/cgi-bin/mjpeg?stream=1
+
+class Panasonic::Camera::HESeries < PlaceOS::Driver
+ include Interface::Camera
+ include Interface::Powerable
+
+ # Discovery Information
+ generic_name :Camera
+ descriptive_name "Panasonic PTZ Camera HE40/50/60"
+ uri_base "http://192.168.0.12"
+
+ default_settings({
+ basic_auth: {
+ username: "admin",
+ password: "12345",
+ },
+ invert_controls: false,
+ presets: {
+ name: {pan: 1, tilt: 1, zoom: 1},
+ },
+ })
+
+ @pan : Int32 = 0
+ @tilt : Int32 = 0
+ @zoom_raw : Int32 = 0
+
+ def on_load
+ # delay between sending commands
+ queue.delay = 130.milliseconds
+ schedule.every(1.minute) { do_poll }
+ on_update
+ end
+
+ @invert : Bool = false
+ @default_movement_speed : Int32 = 12
+ @presets = {} of String => NamedTuple(pan: Int32, tilt: Int32, zoom: Float64)
+
+ def on_update
+ @default_movement_speed = setting?(Int32, :default_movement_speed) || 12
+ self[:inverted] = @invert = setting?(Bool, :invert_controls) || false
+ @presets = setting?(Hash(String, NamedTuple(pan: Int32, tilt: Int32, zoom: Float64)), :presets) || {} of String => NamedTuple(pan: Int32, tilt: Int32, zoom: Float64)
+ self[:presets] = @presets.keys
+ end
+
+ # ===================
+ # Powerable interface
+
+ def power(state : Bool)
+ delay = 6.seconds if state
+ request("O", state ? 1 : 0, delay: delay) { |resp| parse_power resp }
+ end
+
+ def power?
+ parse_power query("O")
+ end
+
+ protected def parse_power(response : String)
+ case response
+ when "p0" then self[:power] = false
+ when "p1", "p3" then self[:power] = true
+ end
+ end
+
+ # ================
+ # Camera interface
+
+ MOVEMENT_STOPPED = 50
+
+ protected def joyspeed(speed : Float64)
+ speed = speed.clamp(-100.0, 100.0)
+ negative = speed < 0.0
+ speed = speed.abs if negative
+
+ percentage = speed / 100.0
+ value = (percentage * 49.0).round.to_i
+ value = -value if negative
+ value
+ end
+
+ def joystick(pan_speed : Float64, tilt_speed : Float64, index : Int32 | String = 0)
+ tilt_speed = -tilt_speed if @invert
+
+ pan = (MOVEMENT_STOPPED + joyspeed(pan_speed)).to_s.rjust(2, '0')
+ tilt = (MOVEMENT_STOPPED + joyspeed(tilt_speed)).to_s.rjust(2, '0')
+
+ # check if we want to stop panning
+ if pan_speed == "50" && tilt_speed == "50"
+ options = {
+ retries: 4,
+ priority: queue.priority + 50,
+ clear_queue: true,
+ name: :joystick,
+ }
+ else
+ options = {
+ retries: 0,
+ priority: queue.priority + 10,
+ clear_queue: false,
+ name: :joystick,
+ }
+ end
+
+ request("PTS", "#{pan}#{tilt}", **options) do |resp|
+ pan, tilt = resp[3..-1].scan(/.{2}/).flat_map(&.to_a)
+ self[:pan_speed] = pan.not_nil!.to_i - MOVEMENT_STOPPED
+ self[:tilt_speed] = tilt.not_nil!.to_i - MOVEMENT_STOPPED
+ end
+ end
+
+ def recall(position : String, index : Int32 | String = 0)
+ preset = @presets[position]?
+ if preset
+ pantilt preset[:pan], preset[:tilt]
+ zoom_to preset[:zoom]
+ else
+ raise "unknown preset #{position}"
+ end
+ end
+
+ def save_position(name : String, index : Int32 | String = 0)
+ do_poll
+ @presets[name] = {pan: @pan, tilt: @tilt, zoom: self[:zoom].as_f}
+ define_setting(:presets, @presets)
+ self[:presets] = @presets.keys
+ end
+
+ def remove_position(name : String, index : Int32 | String = 0)
+ @presets.delete name
+ define_setting(:presets, @presets)
+ self[:presets] = @presets.keys
+ end
+
+ # ================
+ # Moveable interface
+
+ def move(position : MoveablePosition, index : Int32 | String = 0)
+ case position
+ in .open?, .close?
+ # iris not supported
+ in .down?, .up?
+ joystick(
+ pan_speed: 0,
+ tilt_speed: position.down? ? @default_movement_speed : -@default_movement_speed
+ )
+ in .left?, .right?
+ joystick(
+ pan_speed: position.left? ? -@default_movement_speed : @default_movement_speed,
+ tilt_speed: 0
+ )
+ in .in?, .out?
+ zoom(position.in? ? ZoomDirection::In : ZoomDirection::Out)
+ end
+ end
+
+ # ================
+ # Zoomable interface
+
+ ZOOM_MIN = 0x555
+ ZOOM_MAX = 0xFFF
+ ZOOM_RANGE = (ZOOM_MAX - ZOOM_MIN).to_f
+
+ def zoom_to(position : Float64, auto_focus : Bool = true, index : Int32 | String = 0)
+ position = position.clamp(0.0, 100.0)
+ percentage = position / 100.0
+ zoom_value = (percentage * ZOOM_RANGE).to_i + ZOOM_MIN # (zoom range is 0x555 => 0xFFF)
+
+ request("AXZ", zoom_value.to_s(16).upcase.rjust(3, '0')) do |resp|
+ self[:zoom] = resp[3..-1].to_i(16)
+ end
+ end
+
+ def zoom?
+ resp = query("GZ")
+ if resp.includes?("--")
+ message = "camera in standby, operation unavailable"
+ logger.debug { message }
+ message
+ else
+ @zoom_raw = resp[2..-1].to_i(16)
+ self[:zoom] = (@zoom_raw - ZOOM_MIN).to_f * (100.0 / ZOOM_RANGE)
+ end
+ end
+
+ def zoom(direction : ZoomDirection, index : Int32 | String = 0)
+ case direction
+ in .in?
+ move_zoom(@default_movement_speed // 2, priority: queue.priority + 9)
+ in .out?
+ move_zoom(-@default_movement_speed, priority: queue.priority + 9)
+ in .stop?
+ move_zoom(0, priority: queue.priority + 20)
+ end
+ end
+
+ protected def move_zoom(speed : Int32, **options)
+ speed = MOVEMENT_STOPPED + speed
+ request("Z", speed.to_s.rjust(2, '0'), **options) do |resp|
+ self[:zoom_speed] = resp[2..-1].to_i - MOVEMENT_STOPPED
+ end
+ end
+
+ # ================
+ # Stoppable interface
+
+ def stop(index : Int32 | String = 0, emergency : Bool = false)
+ joystick(0, 0)
+ move_zoom(0, priority: queue.priority + 20)
+ end
+
+ # ======================
+ # Other camera functions
+
+ enum Installation
+ Desk
+ Ceiling
+ end
+
+ def installation(position : Installation)
+ request("INS", position.desk? ? 0 : 1) { |resp| parse_installation resp }
+ end
+
+ def installation?
+ parse_installation query("INS")
+ end
+
+ protected def parse_installation(response : String)
+ case response
+ when "ins0" then self[:installation] = Installation::Desk
+ when "ins1" then self[:installation] = Installation::Ceiling
+ end
+ end
+
+ def pantilt(pan : Int32, tilt : Int32)
+ pan_val = pan.to_s(16).upcase.rjust(4, '0')
+ tilt_val = tilt.to_s(16).upcase.rjust(4, '0')
+ request("APC", "#{pan_val}#{tilt_val}", name: :pantilt) { |resp| parse_pantilt resp }
+ end
+
+ def pantilt?
+ parse_pantilt query("APC")
+ end
+
+ protected def parse_pantilt(response : String)
+ pan, tilt = response[3..-1].scan(/.{4}/).flat_map(&.to_a).compact_map(&.try &.to_i(16))
+ self[:pan] = @pan = pan
+ self[:tilt] = @tilt = tilt
+ end
+
+ def do_poll
+ if power?
+ zoom?
+ pantilt?
+ end
+ end
+
+ protected def request(cmd : String, data, **options, &callback : String -> _)
+ request_string = "/cgi-bin/aw_ptz?cmd=%23#{cmd}#{data}&res=1"
+
+ queue.add(**options) do |task|
+ logger.debug { "requesting #{options[:name]?}: #{request_string}" }
+ response = get(request_string)
+
+ if response.success?
+ body = response.body.downcase
+ if body.starts_with?("er")
+ case body[2]
+ when '1' then task.abort("unsupported command #{cmd}: #{body}")
+ when '2'
+ logger.warn { "camera was busy, attempting retry on #{cmd}" }
+ task.retry("camera busy, requested #{cmd}: #{body}")
+ when '3' then task.abort("query outside acceptable range, requested #{cmd}: #{body}")
+ end
+ else
+ begin
+ logger.debug { "received: #{body}" }
+ task.success callback.call(body)
+ rescue error
+ logger.error(exception: error) { "error processing response" }
+ task.abort error.message
+ end
+ end
+ else
+ logger.error { "request failed with #{response.status_code}: #{response.body}" }
+ task.abort "request failed"
+ end
+ end
+ end
+
+ protected def query(cmd : String)
+ request_string = "/cgi-bin/aw_ptz?cmd=%23#{cmd}&res=1"
+ logger.debug { "querying: #{request_string}" }
+ response = get(request_string)
+ raise "request failed with #{response.status_code}: #{response.body}" unless response.success?
+ body = response.body.downcase
+ if body.starts_with?("er")
+ case body[2]
+ when '1' then raise "unsupported command #{cmd}: #{body}"
+ when '2' then raise "camera busy, requested #{cmd}: #{body}"
+ when '3' then raise "query outside acceptable range, requested #{cmd}: #{body}"
+ end
+ end
+ body
+ end
+end
diff --git a/drivers/panasonic/camera/he_series_spec.cr b/drivers/panasonic/camera/he_series_spec.cr
new file mode 100644
index 00000000000..a3856ad439f
--- /dev/null
+++ b/drivers/panasonic/camera/he_series_spec.cr
@@ -0,0 +1,21 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Panasonic::Camera::HESeries" do
+ # Send the request
+ retval = exec(:zoom?)
+
+ # sms should send a HTTP request
+ expect_http_request do |request, response|
+ cmd = request.query_params["cmd"]
+ if cmd == "#GZ"
+ response.status_code = 200
+ response.write "gZFFF".to_slice
+ else
+ raise "expected request: #{cmd}"
+ end
+ end
+
+ # What the sms function should return
+ retval.get.should eq(100.0)
+ status[:zoom].should eq 100
+end
diff --git a/drivers/panasonic/display/protocol2.cr b/drivers/panasonic/display/protocol2.cr
new file mode 100644
index 00000000000..852ab2d1d89
--- /dev/null
+++ b/drivers/panasonic/display/protocol2.cr
@@ -0,0 +1,282 @@
+require "digest/md5"
+require "placeos-driver"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/switchable"
+
+# Based off the very similar https://github.com/PlaceOS/drivers/blob/master/drivers/panasonic/display/nt_control.cr
+
+# How the display expects you interact with it:
+# ===============================================
+# 1. New connection required for each command sent (hence makebreak!)
+# 2. On connect, the display sends you a string of characters to use as a password salt
+# 3. Encode your message using the salt and send it to the display
+# 4. Display responds with a value
+# 5. You have to disconnect explicitly, display won't close the connection
+
+class Panasonic::Display::Protocol2 < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Muteable
+
+ enum Inputs
+ HDMI
+ HDMI2
+ VGA
+ DVI
+ end
+
+ include Interface::InputSelection(Inputs)
+
+ # Discovery Information
+ tcp_port 1024
+ descriptive_name "Panasonic Display Protocol 2"
+ generic_name :Display
+
+ default_settings({
+ username: "admin1",
+ password: "panasonic",
+ })
+
+ makebreak!
+
+ def on_load
+ # Communication settings
+ transport.tokenizer = Tokenizer.new("\r")
+
+ schedule.every(60.seconds) { do_poll }
+
+ on_update
+ end
+
+ def disconnected
+ @channel.close unless @channel.closed?
+ end
+
+ @username : String = "admin1"
+ @password : String = "panasonic"
+
+ # used to coordinate the display password hash
+ @channel : Channel(String) = Channel(String).new
+ @power_target : Bool? = nil
+
+ def on_update
+ @username = setting?(String, :username) || "dispadmin"
+ @password = setting?(String, :password) || "@Panasonic"
+ end
+
+ COMMANDS = {
+ power_on: "PON",
+ power_off: "POF",
+ power_query: "QPW",
+ input: "IMS",
+ volume: "AVL",
+ volume_query: "QAV",
+ audio_mute: "AMT",
+ }
+ RESPONSES = COMMANDS.to_h.invert
+
+ def power(state : Bool)
+ @power_target = state
+
+ if state
+ logger.debug { "requested to power on" }
+ do_send(:power_on, retries: 10, name: :power, delay: 8.seconds)
+ else
+ logger.debug { "requested to power off" }
+ do_send(:power_off, retries: 10, name: :power, delay: 8.seconds)
+ end
+ power?
+ end
+
+ def power?(**options) : Bool
+ do_send(:power_query, **options).get
+ !!self[:power]?.try(&.as_bool)
+ end
+
+ INPUTS = {
+ Inputs::HDMI => "HM1",
+ Inputs::HDMI2 => "HM2",
+ Inputs::VGA => "PC1",
+ Inputs::DVI => "DVI",
+ }
+ INPUT_LOOKUP = INPUTS.invert
+
+ def switch_to(input : Inputs)
+ logger.debug { "requested to switch to: #{input}" }
+ do_send(:input, INPUTS[input], delay: 2.seconds)
+ self[:input] = input # for a responsive UI
+ end
+
+ # There is no input query command
+ def input?
+ self[:input]?
+ end
+
+ # There is no video mute command so this only mutes audio
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ if layer == MuteLayer::Video
+ logger.warn { "requested to mute video which is unsupported" }
+ else
+ logger.debug { "requested audio mute state: #{state}" }
+ do_send(:audio_mute, state ? 1 : 0)
+ end
+ end
+
+ def mute? : Bool
+ do_send(:audio_mute).get
+ !!self[:audio_mute]?.try(&.as_bool)
+ end
+
+ def volume(val : Int32 | Float64)
+ val = val.to_f.clamp(0.0, 100.0).round_away.to_i
+
+ # Unable to query current volume
+ do_send(:volume, val.to_s.rjust(3, '0')).get
+ self[:volume] = val
+ end
+
+ def volume? : Int32?
+ do_send(:volume_query).get
+ self[:volume]?.try(&.as_i)
+ end
+
+ def volume_up
+ current_volume = status?(Float64, :volume) || 50.0
+ volume(current_volume + 5.0)
+ end
+
+ def volume_down
+ current_volume = status?(Float64, :volume) || 50.0
+ volume(current_volume - 5.0)
+ end
+
+ def do_poll
+ if power?(priority: 0)
+ mute?
+ volume?
+ end
+ end
+
+ ERRORS = {
+ "ERR1" => "1: Undefined control command",
+ "ERR2" => "2: Out of parameter range",
+ "ERR3" => "3: Busy state or no-acceptable period",
+ "ERR4" => "4: Timeout or no-acceptable period",
+ "ERR5" => "5: Wrong data length",
+ "ERRA" => "A: Password mismatch",
+ "ER401" => "401: Command cannot be executed",
+ "ER402" => "402: Invalid parameter is sent",
+ }
+
+ def received(data, task)
+ data = String.new(data).strip
+ logger.debug { "Panasonic display sent: #{data} for #{task.try(&.name) || "unknown"}" }
+
+ # This is sent by the display on initial connection
+ # the channel is used to send the hash salt to the task sending a command
+ if data.starts_with?("NTCONTROL")
+ # check for protected mode
+ if @channel && !@channel.closed?
+ # 1 == protected mode
+ @channel.send(data[10] == '1' ? data[12..-1] : "")
+ else
+ transport.disconnect
+ end
+ return
+ end
+
+ # we no longer need the connection to be open , the display expects
+ # us to close it and a new connection is required per-command
+ transport.disconnect
+
+ # remove the leading 00
+ data = data[2..-1]
+
+ # Check for error response
+ if data[0] == 'E'
+ self[:last_error] = error_msg = ERRORS[data]
+
+ if {"ERR3", "ERR4"}.includes?(data)
+ logger.info { "display busy: #{error_msg} (#{data})" }
+ task.try(&.retry)
+ else
+ logger.error { "display error: #{error_msg} (#{data})" }
+ task.try(&.abort(error_msg))
+ end
+ return
+ end
+
+ # We can't interpret this message without a task reference
+ # This also makes sure it is no longer nil
+ return unless task
+
+ # Process the response
+ resp = data.split(':')
+ cmd = RESPONSES[resp[0]]?
+ val = resp[1]?
+
+ case cmd
+ when :power_on, :power_off, :power_query
+ self[:power] = cmd == :power_on if cmd == :power_on || cmd == :power_off
+ self[:power] = val.not_nil!.to_i == 1 if cmd == :power_query
+
+ # Ensure selected power state is achieved
+ if power_target = @power_target
+ if self[:power] == power_target
+ @power_target = nil
+ else
+ power(power_target)
+ end
+ end
+ when :input
+ self[:input] = INPUT_LOOKUP[val]
+ when :volume, :volume_query
+ self[:volume] = val.not_nil!.to_f
+ when :audio_mute
+ self[:audio_mute] = val.not_nil!.to_i == 1
+ end
+
+ task.success
+ end
+
+ protected def do_send(command, param = nil, **options)
+ # prepare the command
+ cmd = if param.nil?
+ "00#{COMMANDS[command]}\r"
+ else
+ "00#{COMMANDS[command]}:#{param}\r"
+ end
+
+ logger.debug { "queuing #{command}: #{cmd}" }
+
+ # queue the request
+ queue(**({
+ name: command,
+ }.merge(options))) do
+ # prepare channel and connect to the display (which will then send the random key)
+ @channel = Channel(String).new
+ transport.connect
+ # wait for the random key to arrive
+ random_key = @channel.receive
+ # build the password hash
+ password_hash = if random_key.empty?
+ # An empty key indicates unauthenticated mode
+ ""
+ else
+ Digest::MD5.hexdigest("#{@username}:#{@password}:#{random_key}")
+ end
+
+ message = "#{password_hash}#{cmd}"
+ logger.debug { "Sending: #{message}" }
+
+ # send the request
+ # NOTE:: the built in `send` function has implicit queuing, but we are
+ # in a task callback here so should be calling transport send directly
+ transport.send(message)
+ end
+ end
+end
diff --git a/drivers/panasonic/display/protocol2_spec.cr b/drivers/panasonic/display/protocol2_spec.cr
new file mode 100644
index 00000000000..2bda8681e56
--- /dev/null
+++ b/drivers/panasonic/display/protocol2_spec.cr
@@ -0,0 +1,75 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Panasonic::Display::Protocol2" do
+ password = "d4a58eaea919558fb54a33a2effa8b94"
+
+ # Execute a command (triggers the connection)
+ exec(:power?)
+ # Once connected the projector will send a password salt
+ expect_reconnect
+ responds("NTCONTROL 1 09b075be\r")
+ # Check the request was sent with the correct password
+ should_send("#{password}00QPW\r")
+ # Respond with the status then check the state updated
+ responds("00QPW:0\r")
+ status[:power].should eq(false)
+
+ exec(:power, true)
+ expect_reconnect
+ responds("NTCONTROL 1 09b075be\r")
+ should_send("#{password}00PON\r")
+ responds("00PON\r")
+ sleep 8.seconds
+ expect_reconnect
+ responds("NTCONTROL 1 09b075be\r")
+ should_send("#{password}00QPW\r")
+ responds("00QPW:1\r")
+ status[:power].should eq(true)
+
+ exec(:switch_to, "hdmi")
+ expect_reconnect
+ responds("NTCONTROL 1 09b075be\r")
+ should_send("#{password}00IMS:HM1\r")
+ responds("00IMS:HM1\r")
+ status[:input].should eq("HDMI")
+
+ exec(:mute?)
+ expect_reconnect
+ responds("NTCONTROL 1 09b075be\r")
+ should_send("#{password}00AMT\r")
+ responds("00AMT:0\r")
+ status[:audio_mute].should eq(false)
+
+ exec(:mute)
+ expect_reconnect
+ responds("NTCONTROL 1 09b075be\r")
+ should_send("#{password}00AMT:1\r")
+ responds("00AMT:1\r")
+ status[:audio_mute].should eq(true)
+
+ exec(:volume?)
+ expect_reconnect
+ responds("NTCONTROL 1 09b075be\r")
+ should_send("#{password}00QAV\r")
+ responds("00QAV:100\r")
+ status[:volume].should eq(100)
+
+ exec(:volume, 20)
+ expect_reconnect
+ responds("NTCONTROL 1 09b075be\r")
+ should_send("#{password}00AVL:020\r")
+ responds("00AVL:020\r")
+ status[:volume].should eq(20)
+
+ exec(:power, false)
+ expect_reconnect
+ responds("NTCONTROL 1 09b075be\r")
+ should_send("#{password}00POF\r")
+ responds("00POF\r")
+ sleep 8.seconds
+ expect_reconnect
+ responds("NTCONTROL 1 09b075be\r")
+ should_send("#{password}00QPW\r")
+ responds("00QPW:0\r")
+ status[:power].should eq(false)
+end
diff --git a/drivers/panasonic/projector/nt_control.cr b/drivers/panasonic/projector/nt_control.cr
new file mode 100644
index 00000000000..0d6bb14757f
--- /dev/null
+++ b/drivers/panasonic/projector/nt_control.cr
@@ -0,0 +1,287 @@
+require "digest/md5"
+require "placeos-driver"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/switchable"
+
+# Documentation: https://aca.im/driver_docs/Panasonic/panasonic_pt-vw535n_manual.pdf
+# also https://aca.im/driver_docs/Panasonic/pt-ez580_en.pdf
+
+# How the projector expects you interact with it
+# ===============================================
+# 1. New connection required for each command sent (hence makebreak!)
+# 2. On connect, the projector sends you a string of characters to use as a password salt
+# 3. Encode your message using the salt and send it to the projector
+# 4. Projector responds with a value
+# 5. You have to disconnect explicitly, projector won't close the connection
+
+class Panasonic::Projector::NTControl < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Muteable
+
+ enum Inputs
+ HDMI
+ HDMI2
+ VGA
+ VGA2
+ Miracast
+ DVI
+ DisplayPort
+ HDBaseT
+ Composite
+ end
+
+ include PlaceOS::Driver::Interface::InputSelection(Inputs)
+
+ # Discovery Information
+ tcp_port 1024
+ descriptive_name "Panasonic Projector"
+ generic_name :Display
+ default_settings({
+ username: "admin1",
+ password: "panasonic",
+ query_lamp_hours: false
+ })
+ makebreak!
+
+ def on_load
+ # Communication settings
+ transport.tokenizer = Tokenizer.new("\r")
+ on_update
+ end
+
+ def disconnected
+ @channel.close unless @channel.closed?
+ end
+
+ @username : String = "admin1"
+ @password : String = "panasonic"
+ getter query_lamp_hours
+ @query_lamp_hours : Bool = false
+
+ # used to coordinate the projector password hash
+ @channel : Channel(String) = Channel(String).new
+ @stable_power : Bool = true
+
+ def on_update
+ @username = setting?(String, :username) || "admin1"
+ @password = setting?(String, :password) || "panasonic"
+ @query_lamp_hours = setting?(Bool, :query_lamp_hours) || false
+
+ schedule.clear
+ schedule.every(40.seconds) do
+ power?(priority: 0)
+ lamp_hours?(priority: 0, retries: 0) if @query_lamp_hours
+ end
+ end
+
+ COMMANDS = {
+ power_on: "PON",
+ power_off: "POF",
+ power_query: "QPW",
+ freeze: "OFZ",
+ input: "IIS",
+ mute: "OSH",
+ lamp: "Q$S",
+ lamp_hours: "Q$L",
+ }
+ RESPONSES = COMMANDS.to_h.invert
+
+ def power(state : Bool)
+ self[:stable_power] = @stable_power = false
+ self[:power_target] = state
+
+ if state
+ logger.debug { "requested to power on" }
+ do_send(:power_on, retries: 10, name: :power, delay: 8.seconds)
+ do_send(:lamp)
+ else
+ logger.debug { "requested to power off" }
+ do_send(:power_off, retries: 10, name: :power, delay: 8.seconds).get
+
+ # Schedule this after we have a result for the power function
+ # As the projector does not even update to cooling for awhile
+ schedule.in(10.seconds) { do_send(:lamp) }
+ end
+ end
+
+ def power?(**options)
+ do_send(:lamp, **options)
+ end
+
+ def lamp_hours?(**options)
+ do_send(:lamp_hours, 1, **options)
+ end
+
+ INPUTS = {
+ Inputs::HDMI => "HD1",
+ Inputs::HDMI2 => "HD2",
+ Inputs::VGA => "RG1",
+ Inputs::VGA2 => "RG2",
+ Inputs::Miracast => "MC1",
+ Inputs::DVI => "DVI",
+ Inputs::DisplayPort => "DP1",
+ Inputs::HDBaseT => "DL1",
+ Inputs::Composite => "VID",
+ }
+ INPUT_LOOKUP = INPUTS.invert
+
+ def switch_to(input : Inputs)
+ # Projector doesn't automatically unmute
+ unmute if self[:mute]?
+
+ do_send(:input, INPUTS[input], delay: 2.seconds)
+ logger.debug { "requested to switch to: #{input}" }
+
+ self[:input] = input # for a responsive UI
+ end
+
+ # Mutes audio + video
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ logger.debug { "requested mute state: #{state}" }
+
+ # TODO:: remote seems to support audio mute and AV mute
+ # but I can't find an audio mute command
+
+ actual = state ? 1 : 0
+ do_send(:mute, actual)
+ end
+
+ ERRORS = {
+ "ERR1" => "1: Undefined control command",
+ "ERR2" => "2: Out of parameter range",
+ "ERR3" => "3: Busy state or no-acceptable period",
+ "ERR4" => "4: Timeout or no-acceptable period",
+ "ERR5" => "5: Wrong data length",
+ "ERRA" => "A: Password mismatch",
+ "ER401" => "401: Command cannot be executed",
+ "ER402" => "402: Invalid parameter is sent",
+ }
+
+ def received(data, task)
+ data = String.new(data).strip
+ logger.debug { "Panasonic sent: #{data}" }
+
+ # This is sent by the projector on initial connection
+ # the channel is used to send the hash salt to the task sending a command
+ if data.starts_with? "NTCONTROL"
+ # check for protected mode
+ if @channel && !@channel.closed?
+ # 1 == protected mode
+ @channel.send(data[10] == '1' ? data[12..-1] : "")
+ else
+ transport.disconnect
+ end
+ return
+ end
+
+ # we no longer need the connection to be open , the projector expects
+ # us to close it and a new connection is required per-command
+ transport.disconnect
+
+ # Check for error response
+ if data[0] == 'E'
+ self[:last_error] = error_msg = ERRORS[data]
+
+ if {"ERR3", "ERR4"}.includes? data
+ logger.info { "projector busy: #{error_msg} (#{data})" }
+ task.try &.retry
+ else
+ logger.error { "projector error: #{error_msg} (#{data})" }
+ task.try &.abort(error_msg)
+ end
+ return
+ end
+
+ # We can't interpret this message without a task reference
+ # This also makes sure it is no longer nil
+ return unless task
+
+ # Process the response
+ data = data[2..-1]
+ resp = data.split(':')
+ cmd = RESPONSES[resp[0]]?
+ val = resp[1]?
+
+ case cmd
+ when :power_on
+ self[:power] = true
+ when :power_off
+ self[:power] = false
+ when :power_query
+ self[:power] = val.not_nil!.to_i == 1
+ when :freeze
+ self[:frozen] = val.not_nil!.to_i == 1
+ when :input
+ self[:input] = INPUT_LOOKUP[val]
+ when :mute
+ state = self[:mute] = val.not_nil!.to_i == 1
+ self[:mute0] = state
+ self[:mute0_video] = state
+ self[:mute0_audio] = state
+ else
+ case task.name
+ when "lamp"
+ ival = resp[0].to_i
+ self[:power] = {1, 2}.includes?(ival)
+ self[:warming] = ival == 1
+ self[:cooling] = ival == 3
+
+ # check target states here
+ if !@stable_power
+ if self[:power] == self[:power_target]
+ self[:stable_power] = @stable_power = true
+ else
+ power self[:power_target].as_bool
+ end
+ end
+ when "lamp_hours"
+ # Resp looks like: "001682"
+ self[:lamp_usage] = data.to_i
+ end
+ end
+
+ task.success
+ end
+
+ protected def do_send(command, param = nil, **options)
+ # prepare the command
+ cmd = if param.nil?
+ "00#{COMMANDS[command]}\r"
+ else
+ "00#{COMMANDS[command]}:#{param}\r"
+ end
+
+ logger.debug { "queuing #{command}: #{cmd}" }
+
+ # queue the request
+ queue(**({
+ name: command,
+ }.merge(options))) do
+ # prepare channel and connect to the projector (which will then send the random key)
+ @channel = Channel(String).new
+ transport.connect
+ # wait for the random key to arrive
+ random_key = @channel.receive
+ # build the password hash
+ password_hash = if random_key.empty?
+ # An empty key indicates unauthenticated mode
+ ""
+ else
+ Digest::MD5.hexdigest("#{@username}:#{@password}:#{random_key}")
+ end
+
+ message = "#{password_hash}#{cmd}"
+ logger.debug { "Sending: #{message}" }
+
+ # send the request
+ # NOTE:: the built in `send` function has implicit queuing, but we are
+ # in a task callback here so should be calling transport send directly
+ transport.send(message)
+ end
+ end
+end
diff --git a/drivers/panasonic/projector/nt_control_spec.cr b/drivers/panasonic/projector/nt_control_spec.cr
new file mode 100644
index 00000000000..33e4d098039
--- /dev/null
+++ b/drivers/panasonic/projector/nt_control_spec.cr
@@ -0,0 +1,25 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Panasonic::Projector::NTControl" do
+ # Execute a command (triggers the connection)
+ exec(:power?)
+
+ # Once connected the projector will send a password salt
+ expect_reconnect
+ transmit "NTCONTROL 1 09b075be\r"
+
+ # Check the request was sent with the correct password
+ password = "d4a58eaea919558fb54a33a2effa8b94"
+ should_send("#{password}00Q$S\r")
+
+ # Respond with the status then check the state updated
+ transmit("00PON\r")
+ status[:power].should be_true
+
+ exec(:lamp_hours?)
+ expect_reconnect
+ transmit "NTCONTROL 1 09b075be\r"
+ should_send("#{password}00Q$L:1\r")
+ transmit("001682\r")
+ status[:lamp_usage].should eq(1682)
+end
diff --git a/drivers/pattr/chat_bot.cr b/drivers/pattr/chat_bot.cr
new file mode 100644
index 00000000000..0eaedc8f3a2
--- /dev/null
+++ b/drivers/pattr/chat_bot.cr
@@ -0,0 +1,102 @@
+require "placeos-driver"
+require "./chat_bot_models"
+
+class Pattr::ChatBot < PlaceOS::Driver
+ descriptive_name "Pattr Chat Bot"
+ generic_name :ChatBot
+ description %(provides data based on context provided by the chat bot)
+
+ default_settings({
+ debug_webhook: false,
+ # building location services, defualts to the current system
+ buildings: ["system_id1"],
+ })
+
+ @debug_webhook : Bool = false
+ @buildings : Array(PlaceOS::Driver::Proxy::System) = [] of PlaceOS::Driver::Proxy::System
+
+ accessor staff_api : StaffAPI_1
+
+ protected getter zones : Hash(String, String) = {} of String => String
+ protected getter systems : Hash(String, String) = {} of String => String
+
+ def on_load
+ @zones = Hash(String, String).new do |hash, key|
+ zone = staff_api.zone(key).get.as_h
+ hash[key] = zone["display_name"]?.try(&.as_s?.try(&.presence)) || zone["name"].as_s
+ end
+
+ @systems = Hash(String, String).new do |hash, key|
+ zone = staff_api.get_system(key).get.as_h
+ hash[key] = zone["display_name"]?.try(&.as_s?.try(&.presence)) || zone["name"].as_s
+ end
+
+ on_update
+ end
+
+ def on_update
+ @debug_webhook = setting?(Bool, :debug_webhook) || false
+
+ # Convert the building system IDs to system proxies
+ buildings = setting?(Array(String), :buildings) || [config.control_system.not_nil!.id]
+ @buildings = buildings.map { |id| system(id) }
+ end
+
+ def chat_data_request(method : String, headers : Hash(String, Array(String)), body : String)
+ logger.debug { "webhook received: #{method},\nheaders #{headers},\nbody size #{body.size}" }
+ logger.debug { body } if @debug_webhook
+
+ request = Request.from_json(body)
+ response = case request
+ in Location
+ locate(request.referencing)
+ end
+
+ payload = response.to_json
+ logger.debug { payload } if @debug_webhook
+ {HTTP::Status::OK.to_i, {"Content-Type" => "application/json"}, payload}
+ end
+
+ # map reduce search for the users across all buildings
+ def locate(staff : Array(String))
+ # kick off the searches
+ searches = staff.map do |username|
+ email = username.includes?('@') ? username : nil
+ queries = @buildings.map { |building| building[:LocationServices].locate_user(email, username) }
+ {username, queries}
+ end
+
+ # wait for the responses to flow in
+ response = {} of String => PlaceLocationResult
+ searches.each do |(username, queries)|
+ locations = {} of String => PlaceLocationResult
+ queries.each do |results|
+ Array(PlaceLocationResult).from_json(results.get.to_json).map do |location|
+ locations[location.location] = location
+ end
+ end
+
+ # Grab the location they are most likely to be
+ if location = locations["meeting"]? || locations["wireless"]? || locations["desk"]?
+ response[username] = location
+ end
+ end
+
+ # build the response
+ response.transform_values do |location|
+ case location.location
+ when "meeting"
+ {
+ building: zones[location.building],
+ level: zones[location.level],
+ room: systems[location.sys_id.not_nil!],
+ }
+ else
+ {
+ building: zones[location.building],
+ level: zones[location.level],
+ }
+ end
+ end
+ end
+end
diff --git a/drivers/pattr/chat_bot_models.cr b/drivers/pattr/chat_bot_models.cr
new file mode 100644
index 00000000000..2fd7ce30df5
--- /dev/null
+++ b/drivers/pattr/chat_bot_models.cr
@@ -0,0 +1,35 @@
+require "json"
+
+module Pattr
+ abstract class Request
+ include JSON::Serializable
+
+ # request type hint
+ use_json_discriminator "request", {
+ "location" => Location,
+ }
+
+ getter user : String
+ end
+
+ class Location < Request
+ getter request : String = "location"
+
+ # user emails / usernames of users we want to locate
+ getter referencing : Array(String)
+ end
+
+ class PlaceLocationResult
+ include JSON::Serializable
+
+ # wireless, desk, meeting, booking
+ getter location : String
+
+ # zone ids
+ getter building : String
+ getter level : String
+
+ # system id (if it's a meeting room)
+ getter sys_id : String?
+ end
+end
diff --git a/drivers/pattr/chat_bot_spec.cr b/drivers/pattr/chat_bot_spec.cr
new file mode 100644
index 00000000000..900b83d4d24
--- /dev/null
+++ b/drivers/pattr/chat_bot_spec.cr
@@ -0,0 +1,45 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Pattr::ChatBot" do
+ system({
+ LocationServices: {LocationServicesMock},
+ StaffAPI: {StaffAPIMock},
+ })
+ settings({
+ buildings: [DriverSpecs::SYSTEM_ID],
+ })
+
+ exec(:locate, ["user@org.com"]).get.should eq({"user@org.com" => {
+ "building" => "The Zone",
+ "level" => "The Zone",
+ "room" => "Room 1234",
+ }})
+end
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ def get_system(id : String)
+ {
+ name: "Some System",
+ display_name: "Room 1234",
+ }
+ end
+
+ def zone(zone_id : String)
+ {
+ name: "The Zone",
+ }
+ end
+end
+
+# :nodoc:
+class LocationServicesMock < DriverSpecs::MockDriver
+ def locate_user(email : String? = nil, username : String? = nil)
+ [{
+ location: "meeting",
+ building: "zone-id",
+ level: "zone-id",
+ sys_id: "sys-123",
+ }]
+ end
+end
diff --git a/drivers/philips/dynalite.cr b/drivers/philips/dynalite.cr
new file mode 100644
index 00000000000..63ee6a7090b
--- /dev/null
+++ b/drivers/philips/dynalite.cr
@@ -0,0 +1,242 @@
+require "placeos-driver"
+require "placeos-driver/interface/lighting"
+
+# Documentation: https://aca.im/driver_docs/Philips/Dynet%20Integrators%20hand%20book%20for%20the%20DNG232%20V2.pdf
+# also https://aca.im/driver_docs/Philips/DyNet%201%20Opcode%20Master%20List%20-%202012-08-29.xls
+
+class Philips::Dynalite < PlaceOS::Driver
+ include Interface::Lighting::Scene
+ include Interface::Lighting::Level
+ alias Area = Interface::Lighting::Area
+
+ # Discovery Information
+ descriptive_name "Philips Dynalite Lighting"
+ generic_name :Lighting
+ tcp_port 50000
+
+ default_settings({
+ disable_tokenizer: false,
+ wait_for_replies: true,
+ num_retries: 3,
+ })
+
+ def on_load
+ queue.delay = 35.milliseconds
+ on_update
+ end
+
+ def on_update
+ case setting?(Bool, :wait_for_replies)
+ when false
+ queue.wait = false
+ when true, nil
+ queue.wait = true
+ end
+
+ queue.retries = setting?(Int32, :num_retries) || 3
+
+ if !(setting?(Bool, :disable_tokenizer) || false)
+ # 8 bytes starting with 1C
+ transport.tokenizer ||= Tokenizer.new(8, Bytes[0x1C])
+ else
+ transport.tokenizer = nil
+ end
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ def connected
+ # maintain the connection
+ schedule.every(1.minute) do
+ logger.debug { "maintaining connection" }
+ get_current_preset(1)
+ end
+ end
+
+ # fade_time in millisecond
+ def trigger(area : Int32, scene : Int32, fade : Int32 = 1000)
+ # convert to centiseconds
+ fade_centi = fade // 10
+
+ # No response so we should update status here
+ self[Area.new(area.to_u32)] = scene
+
+ # Crazy scene encoding
+ # Supports presets: 1 - 24 (0 indexed)
+ # Presets are in 1 of 3 banks (0 indexed)
+ # Presets in a bank are encoded: 0 = P1, 1 = P2, 2 = P3, 3 = P4, A = P5, B = P6, C = P7, D = P8
+ scene = scene - 1 # zero index
+ bank = scene // 8 # calculate bank this preset resides in
+ scene = scene - (bank * 8) # select the scene in the current bank
+ scene += 6 if scene >= 4 # encode the upper bank presets (P5 -> P8)
+
+ command = Bytes[0x1c, area & 0xFF, fade_centi & 0xFF, scene & 0xFF, (fade_centi >> 8) & 0xFF, bank, 0xFF]
+ schedule.in((fade + 200).milliseconds) { get_light_level(area) }
+
+ do_send(command, name: "preset_#{area}_#{scene}")
+ end
+
+ def get_current_preset(area : UInt8)
+ command = Bytes[0x1c, area, 0, 0x63, 0, 0, 0xFF]
+ do_send(command, wait: true)
+ end
+
+ @[Security(Level::Administrator)]
+ def save_preset(area : UInt8, scene : UInt8)
+ num = (scene - 1) & 0xFF
+ command = Bytes[0x1c, area, num, 0x09, 0, 0, 0xFF]
+ do_send(command)
+ end
+
+ def lighting(area : Int32, state : Bool, fade : Int32 = 1000)
+ level = state ? 100.0 : 0.0
+ light_level(area, level, fade)
+ end
+
+ LEVEL_PERCENTAGE = 0xFE / 100
+
+ def light_level(area : Int32, level : Float64, fade : Int32 = 1000, channel : Int32 = 0xFF)
+ cmd = 0x71
+
+ # Command changes based on the length of the fade time
+ fade = if fade <= 25500
+ fade // 100
+ elsif fade < 255000
+ cmd = 0x72
+ fade // 1000
+ else
+ cmd = 0x73
+ (fade // 60000).clamp(1, 22)
+ end
+
+ # Ensure status values are valid
+ area_key = Area.new(area.to_u32, channel: channel == 0xFF ? nil : channel.to_u32).append("level").to_s
+ self[area_key] = level
+
+ # Levels are percentage based (on the PlaceOS side)
+ # 0x01 == 100%
+ # 0xFF == 0%
+ level = (level.clamp(0.0, 100.0) * LEVEL_PERCENTAGE).to_u8
+ level = 0xFF_u8 - level # Invert
+
+ command = Bytes[0x1c, area & 0xFF, channel & 0xFF, cmd, level, fade & 0xFF, 0xFF]
+ do_send(command, name: "level_#{area}_#{channel}")
+ end
+
+ def stop_fading(area : UInt8, channel : UInt8 = 0xFF_u8)
+ command = Bytes[0x1c, area, channel, 0x76, 0, 0, 0xFF]
+ do_send(command, name: "level_#{area}_#{channel}")
+ end
+
+ def stop_all_fading(area : UInt8)
+ command = Bytes[0x1c, area, 0, 0x7A, 0, 0, 0xFF]
+ do_send(command)
+ end
+
+ def get_light_level(area : Int32, channel : Int32 = 0xFF)
+ do_send(Bytes[0x1c, area & 0xFF, channel & 0xFF, 0x61, 0, 0, 0xFF], wait: true)
+ end
+
+ def increment_area_level(area : UInt8)
+ do_send(Bytes[0x1c, area, 0x64, 6, 0, 0, 0xFF])
+ end
+
+ def decrement_area_level(area : UInt8)
+ do_send(Bytes[0x1c, area, 0x64, 5, 0, 0, 0xFF])
+ end
+
+ def unlink_area(area : UInt8)
+ # 0x1c, area, unlink_bitmap, 0x21, unlink_bitmap, unlink_bitmap, join (0xFF)
+ # do_send(Bytes[0x1c, area & 0xFF, 0xFF, 0x21, 0xFF, 0xFF, 0xFF])
+ link_area area, 0_u8
+ end
+
+ def link_area(area : UInt8, join : UInt8)
+ do_send(Bytes[0x1c, area, join, 0x14, 0x00, 0x00, 0xFF])
+ end
+
+ def received(data, task)
+ logger.debug { "received 0x#{data.hexstring}" }
+
+ case data[3]
+ # current preset selected response
+ when 0, 1, 2, 3, 10, 11, 12, 13
+ # 0-3, A-D == preset 1..8
+ number = data[3]
+ number -= 0x0A + 4 if number > 3
+
+ # Data 4 represets the preset offset or bank
+ number += data[5] * 8 + 1
+ self[Area.new(data[1].to_u32)] = number
+ task.try &.success(number)
+
+ # alternative preset response
+ when 0x62
+ number = data[2] + 1
+ self[Area.new(data[1].to_u32)] = number
+ task.try &.success(number)
+ # level response (area or channel)
+ when 0x60
+ level = data[4]
+
+ # 0x01 == 100%
+ # 0xFF == 0%
+ level = 0xFF - level
+ level = level / LEVEL_PERCENTAGE
+ channel = data[2].to_u32
+ area_key = Area.new(data[1].to_u32, channel: channel == 0xFF_u32 ? nil : channel).append("level").to_s
+ self[area_key] = level
+
+ task.try &.success(level)
+ else
+ task.try &.success
+ end
+ end
+
+ protected def do_send(command : Bytes, **options)
+ # 2's compliment checksum (i.e. negative of the sum and the least significant byte of that result)
+ check = (-command.reduce(0) { |acc, i| acc + i }) & 0xFF
+ data = IO::Memory.new(command.size + 1)
+ data.write command
+ data.write_byte check.to_u8
+
+ command = data.to_slice
+ logger.debug { "sending: 0x#{command.hexstring}" }
+
+ send(command, **options)
+ end
+
+ # ==================
+ # Lighting Interface
+ # ==================
+ protected def check_arguments(area : Area?)
+ area_id = area.try(&.id)
+ # area_join = area.try(&.join) || 0xFF_u32
+ raise ArgumentError.new("area.id required") unless area_id
+ area_id.to_i
+ end
+
+ def set_lighting_scene(scene : UInt32, area : Area? = nil, fade_time : UInt32 = 1000_u32)
+ area_id = check_arguments area
+ trigger(area_id, scene.to_i, fade_time.to_i)
+ end
+
+ def lighting_scene?(area : Area? = nil)
+ area_id = check_arguments area
+ get_current_preset(area_id.to_u8)
+ end
+
+ def set_lighting_level(level : Float64, area : Area? = nil, fade_time : UInt32 = 1000_u32)
+ area_id = check_arguments area
+ area_channel = area.try(&.channel) || 0xFF_u32
+ light_level(area_id, level, fade_time.to_i, area_channel.to_i)
+ end
+
+ def lighting_level?(area : Area? = nil)
+ area_id = check_arguments area
+ area_channel = area.try(&.channel) || 0xFF_u32
+ get_light_level(area_id, area_channel.to_i)
+ end
+end
diff --git a/drivers/philips/dynalite_spec.cr b/drivers/philips/dynalite_spec.cr
new file mode 100644
index 00000000000..e324a5ea8a6
--- /dev/null
+++ b/drivers/philips/dynalite_spec.cr
@@ -0,0 +1,40 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Philips::Dynalite" do
+ exec :trigger, 1, 4, 320
+ should_send Bytes[0x1c, 0x01, 0x20, 0x03, 0x00, 0x00, 0xff, 0xc1]
+ status["area1"].should eq(4)
+
+ # 5 second fade
+ exec :light_level, area: 2, level: 49.5, fade: 5000, channel: 3
+ should_send Bytes[0x1c, 0x02, 0x03, 0x71, 0x82, 0x32, 0xff, 0xbb]
+ status["area2_3_level"].should eq(49.5)
+
+ # 50 second fade
+ exec :light_level, area: 2, level: 49.5, fade: 50000, channel: 3
+ should_send Bytes[0x1c, 0x02, 0x03, 0x72, 0x82, 0x32, 0xff, 0xba]
+ status["area2_3_level"].should eq(49.5)
+
+ # 15 minute fade
+ exec :light_level, area: 2, level: 49.5, fade: 900000, channel: 3
+ should_send Bytes[0x1c, 0x02, 0x03, 0x73, 0x82, 0x0f, 0xff, 0xdc]
+ status["area2_3_level"].should eq(49.5)
+
+ exec :stop_fading, area: 4, channel: 6
+ should_send Bytes[0x1c, 0x04, 0x06, 0x76, 0x00, 0x00, 0xff, 0x65]
+
+ exec :stop_all_fading, area: 4
+ should_send Bytes[0x1c, 0x04, 0x00, 0x7A, 0x00, 0x00, 0xff, 0x67]
+
+ response = exec :get_current_preset, area: 4
+ should_send Bytes[0x1c, 0x04, 0x00, 0x63, 0x00, 0x00, 0xff, 0x7e]
+ responds Bytes[0x1c, 0x04, 0x05, 0x62, 0x00, 0x00, 0xff, 0x7A]
+ response.get.should eq(6)
+ status["area4"].should eq(6)
+
+ response = exec :get_light_level, area: 2, channel: 5
+ should_send Bytes[0x1c, 0x02, 0x05, 0x61, 0x00, 0x00, 0xff, 0x7d]
+ responds Bytes[0x1c, 0x02, 0x05, 0x60, 0x70, 0x70, 0xff, 0x9f]
+ response.get.not_nil!.as_f.to_i.should eq(56)
+ status["area2_5_level"].not_nil!.as_f.to_i.should eq(56)
+end
diff --git a/drivers/philips/dynet_text.cr b/drivers/philips/dynet_text.cr
new file mode 100644
index 00000000000..6b2049ed070
--- /dev/null
+++ b/drivers/philips/dynet_text.cr
@@ -0,0 +1,223 @@
+require "placeos-driver"
+require "placeos-driver/interface/lighting"
+require "telnet"
+
+# Documentation: https://aca.im/driver_docs/Philips/DYN_CG_INT_EnvisionGateway_R05.pdf
+# See page 58
+
+class Philips::DyNetText < PlaceOS::Driver
+ include Interface::Lighting::Scene
+ include Interface::Lighting::Level
+ alias Area = Interface::Lighting::Area
+
+ # Discovery Information
+ descriptive_name "Philips DyNet Text Protocol"
+ generic_name :Lighting
+ tcp_port 23
+
+ @ready : Bool = false
+
+ protected getter! telnet : Telnet
+
+ def on_load
+ new_telnet_client
+ transport.pre_processor { |bytes| telnet.buffer(bytes) }
+ transport.tokenizer = Tokenizer.new("\r\n")
+ end
+
+ def connected
+ @ready = false
+ self[:ready] = false
+
+ schedule.every(60.seconds) do
+ logger.debug { "-- polling gateway" }
+ get_date
+ end
+ end
+
+ def disconnected
+ # Ensures the buffer is cleared
+ new_telnet_client
+ schedule.clear
+ end
+
+ protected def new_telnet_client
+ @telnet = Telnet.new { |data| puts "neg: #{data.hexstring}"; transport.send(data) }
+ end
+
+ def received(data, task)
+ data = String.new(data).strip("\x00\r\n\t ")
+ return if data.empty?
+
+ logger.debug { "Dynalite sent: #{data}" }
+
+ if @ready
+ # Extract response
+ components = data.split(", ").map { |component|
+ parts = component.downcase.split
+ value = parts.pop
+ key = parts.join(' ')
+ {key, value}
+ }.to_h
+ process_response data, components, task
+ elsif data =~ /Connection Established/i
+ @ready = true
+ self[:ready] = true
+
+ # Turn off echo
+ do_send "Echo 0", name: "echo"
+ # ensure verbose messages
+ do_send "Verbose", name: "verbose"
+ # Reply with OK
+ do_send "ReplyOK 1", name: "replies"
+ # default join is FF
+ do_send "Join 255", name: "join"
+ end
+ end
+
+ protected def process_response(message : String, parts : Hash(String, String), task)
+ task_name = task.try(&.name)
+ success = task_name.nil?
+
+ # For execute commands we consider complete once we get the OK message
+ if message == "OK"
+ if task && task_name
+ # We want to process replies completely (return the value)
+ # however we don't want to retry in case the target doesn't exist
+ if task_name.starts_with?("get_")
+ task.retries = 0
+ else
+ logger.debug { "execute #{task_name} success!" }
+ task.success
+ end
+ end
+ return
+ end
+
+ check_key = parts.first_key
+ case check_key
+ when "preset"
+ area = parts["area"]?
+ # return here if we are just getting the echo of our request
+ return unless area
+ join = get_join parts["join"]
+ area_key = Area.new(area.to_u32, join: join == 255_u32 ? nil : join)
+ self[area_key] = parts.first_value.to_i
+ when "channel level channel"
+ area = parts["area"].to_u32
+ self[Area.new(area).append("level")] = parts["level"].to_i(strict: false)
+ when .starts_with?("date")
+ success = true if task_name == "date"
+ when .starts_with?("time")
+ success = true if task_name == "time"
+ when .starts_with?("reply")
+ case check_key
+ when .ends_with?("current preset")
+ preset = parts.first_value.to_i
+ area = parts["area"].to_u32
+ join = get_join parts["join"]
+ area_key = Area.new(area, join: join == 255_u32 ? nil : join).to_s
+
+ self[area_key] = preset
+ task.not_nil!.success(preset) if task_name == "get_#{area_key}"
+ when .ends_with?("level ch")
+ area = parts["area"].to_u32
+ join = get_join parts["join"]
+ area_key = Area.new(area, join: join == 255_u32 ? nil : join).append("level").to_s
+ level = parts["targlev"].to_i(strict: false)
+
+ self[area_key] = level
+ task.not_nil!.success(level) if task_name == "get_#{area_key}"
+ end
+ when "channellevel", "stopfade", .starts_with?("requestcurrentpreset"), .starts_with?("requestchannellevel")
+ # we ignore this echo
+ else
+ logger.debug { "ignorning message: #{message}, key: #{check_key.inspect}" }
+ end
+
+ # ignore unless sucess
+ task.try(&.success) if success
+ end
+
+ protected def do_send(command, **options)
+ send telnet.prepare(command), **options
+ end
+
+ protected def get_join(value : String)
+ value = value.rchop("hex")
+ value = value.lchop("0x")
+ value.to_u32(16)
+ end
+
+ def get_date
+ do_send "RequestDate", name: :date
+ end
+
+ def get_time
+ do_send "RequestTime", name: :time
+ end
+
+ def trigger(area : UInt16, scene : UInt16, join : UInt8 = 0xFF_u8, fade : UInt32 = 1000_u32)
+ do_send "Preset #{scene} #{area} #{fade} #{join}", name: "preset#{area}_#{join}"
+ end
+
+ @[Security(Level::Support)]
+ def send_custom(data : String)
+ do_send data
+ end
+
+ def get_current_preset(area : UInt16, join : UInt8 = 0xFF_u8)
+ do_send "RequestCurrentPreset #{area} #{join}", name: (join == 255_u8 ? "get_area#{area}" : "get_area#{area}_#{join}")
+ end
+
+ def lighting(area : UInt16, state : Bool, join : UInt8 = 0xFF_u8, fade : UInt32 = 1000_u32)
+ light_level(area, state ? 100.0 : 0.0, join, fade)
+ end
+
+ def light_level(area : UInt16, level : Float64, join : UInt8 = 0xFF_u8, fade : UInt32 = 1000_u32, channel : UInt16 = 0_u16)
+ # channel 0 is all channels
+ level = level.round_away.to_i
+ do_send "ChannelLevel #{channel} #{level.clamp(0, 100)} #{area} #{fade} #{join}", name: "level#{area}_#{channel}_#{join}"
+ end
+
+ def get_light_level(area : UInt16, join : UInt8 = 0xFF_u8, channel : UInt16 = 1_u16)
+ # can't request level of channel 0 (all channels) so we default to channel 1 which should always exist
+ do_send "RequestChannelLevel #{channel} #{area} #{join}", name: (join == 255_u8 ? "get_area#{area}_level" : "get_area#{area}_#{join}_level")
+ end
+
+ def stop_fading(area : UInt16, join : UInt8 = 0xFF_u8, channel : UInt16 = 0_u16)
+ do_send "StopFade #{channel} #{area} #{join}", name: "stopfade#{area}_#{join}_#{channel}"
+ end
+
+ # ==================
+ # Lighting Interface
+ # ==================
+ protected def check_arguments(area : Area?)
+ area_id = area.try(&.id)
+ area_join = area.try(&.join) || 0xFF_u32
+ raise ArgumentError.new("area.id required, area.join defaults to 0xFF") unless area_id
+ {area_id.to_u16, area_join.to_u8}
+ end
+
+ def set_lighting_scene(scene : UInt32, area : Area? = nil, fade_time : UInt32 = 1000_u32)
+ area_id, area_join = check_arguments area
+ trigger(area_id, scene.to_u16, area_join, fade_time)
+ end
+
+ def lighting_scene?(area : Area? = nil)
+ area_id, area_join = check_arguments area
+ get_current_preset(area_id, area_join)
+ end
+
+ def set_lighting_level(level : Float64, area : Area? = nil, fade_time : UInt32 = 1000_u32)
+ area_id, area_join = check_arguments area
+ area_channel = area.try(&.channel) || 0_u32
+ light_level(area_id, level, area_join, fade_time, area_channel.to_u16)
+ end
+
+ def lighting_level?(area : Area? = nil)
+ area_id, area_join = check_arguments area
+ area_channel = area.try(&.channel) || 1_u32
+ get_light_level(area_id, area_join, area_channel.to_u16)
+ end
+end
diff --git a/drivers/philips/dynet_text_spec.cr b/drivers/philips/dynet_text_spec.cr
new file mode 100644
index 00000000000..71d95e385ae
--- /dev/null
+++ b/drivers/philips/dynet_text_spec.cr
@@ -0,0 +1,101 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Philips::DyNetText" do
+ # Telnet establishment
+ transmit "fffb01".hexbytes
+ should_send "fffd01".hexbytes
+
+ transmit "fffd01".hexbytes
+ should_send "fffc01".hexbytes
+
+ transmit "fffb03".hexbytes
+ should_send "fffd03".hexbytes
+
+ transmit "fffd03".hexbytes
+ should_send "fffc03".hexbytes
+
+ transmit "fffb05".hexbytes
+ should_send "fffe05".hexbytes
+
+ transmit "fffd05".hexbytes
+ should_send "fffc05".hexbytes
+
+ transmit "Telnet Connection Established ...\r\n\r\n"
+ sleep 100.milliseconds
+
+ # Configure protocol
+ status[:ready].should eq true
+
+ should_send "Echo 0\r\x00"
+ responds "OK\r\n"
+ should_send "Verbose\r\x00"
+ responds "OK\r\n"
+ should_send "ReplyOK 1\r\x00"
+ responds "OK\r\n"
+ should_send "Join 255\r\x00"
+ responds "OK\r\n"
+
+ # Process some data
+ transmit "Preset 2, Area 103, Fade 0, Join 0xff\r\n"
+ sleep 100.milliseconds
+ status["area103"].should eq(2)
+
+ # WTF philips, why are there multiple hex representations
+ transmit "Channel Level Channel 43, Level 100%, Area 137, Fade 0, Join ffhex\r\n"
+ sleep 100.milliseconds
+ status["area137_level"].should eq(100)
+
+ # This is a good ping request
+ transmit "Date Wed 8 Jun 2022\r\n"
+ transmit "Time 13:35:51 Standard Time\r\n"
+
+ # NOTE:: Tests here respond with echos even though we turn this off
+ # just for in case the request is ignored
+
+ # Execute some query requests
+ resp = exec :get_current_preset, 58
+ should_send "RequestCurrentPreset 58 255\r\x00"
+ responds "RequestCurrentPreset 58 255\r\n"
+ responds "OK\r\n"
+ # yep, it sometimes replies with a leading null byte, just to screw up anyone dealing with this protocol in C
+ responds "\x00Reply with Current Preset 2, Area 58, Join ffhex\r\n"
+
+ resp.get.should eq 2
+ status["area58"].should eq(2)
+
+ resp = exec :get_light_level, 58
+ should_send "RequestChannelLevel 1 58 255\r\x00"
+ responds "RequestChannelLevel 1 58 255\r\n"
+ responds "OK\r\n"
+ responds "Reply with Current Level Ch 1, Area 58, TargLev 100%, CurrLev 100%, Join ffhex\r\n"
+
+ resp.get.should eq 100
+ status["area58_level"].should eq(100)
+
+ # Execute some update requests
+ resp = exec :trigger, 70, 2
+ should_send "Preset 2 70 1000 255\r\x00"
+ responds "Preset 2 70 1000 255\r\n"
+ responds "OK\r\n"
+ responds "Preset 2, Area 70, Fade 1000, Join 0xff\r\n"
+ resp.get
+ sleep 100.milliseconds
+ status["area70"].should eq(2)
+
+ resp = exec :light_level, 70, 90.1
+ should_send "ChannelLevel 0 90 70 1000 255\r\x00"
+ responds "ChannelLevel 0 100 70 1000 255\r\n"
+ responds "OK\r\n"
+ responds "Channel Level Channel 0, Level 90%, Area 70, Fade 1000, Join ffhex\r\n"
+ resp.get
+ sleep 100.milliseconds
+ status["area70_level"].should eq(90)
+
+ resp = exec :stop_fading, 70
+ should_send "StopFade 0 70 255\r\x00"
+ responds "StopFade 0 70 255\r\n"
+ responds "OK\r\n"
+ resp.get
+
+ puts "Test passed!"
+end
diff --git a/drivers/philips/hue.cr b/drivers/philips/hue.cr
new file mode 100644
index 00000000000..087407c1785
--- /dev/null
+++ b/drivers/philips/hue.cr
@@ -0,0 +1,193 @@
+require "placeos-driver"
+require "placeos-driver/interface/lighting"
+
+# documentation: https://developers.meethue.com/develop/hue-api-v2/api-reference/
+
+class Philips::Hue < PlaceOS::Driver
+ include Interface::Lighting::Scene
+ include Interface::Lighting::Level
+
+ # component == resource
+ # id == id
+ alias Area = Interface::Lighting::Area
+
+ # Discovery Information
+ generic_name :Hue
+ descriptive_name "Philips Hue Lighting"
+ uri_base "https://192.168.4.31"
+
+ default_settings({
+ app_key: "",
+ client_key: "",
+
+ scenes: [""],
+ })
+
+ def on_update
+ @app_key = setting(String, :app_key)
+ @client_key = setting(String, :client_key)
+ @scenes = setting?(Array(String), :scenes) || [] of String
+ end
+
+ @[Security(Level::Administrator)]
+ getter app_key : String = ""
+
+ @[Security(Level::Administrator)]
+ getter client_key : String = ""
+
+ getter scenes : Array(String) = [] of String
+
+ record HueError, type : Int32, address : String, description : String do
+ include JSON::Serializable
+ end
+
+ record RegSuccess, username : String, clientkey : String do
+ include JSON::Serializable
+ end
+
+ record RegResponse, success : RegSuccess?, error : HueError? do
+ include JSON::Serializable
+ end
+
+ def register
+ response = post("/api", body: {
+ devicetype: "placeos##{module_id}",
+ generateclientkey: true,
+ }.to_json)
+
+ raise "unknown error: #{response.body}" unless response.success?
+
+ resp = Array(RegResponse).from_json(response.body)[0]
+ if success = resp.success
+ @app_key = success.username
+ @client_key = success.clientkey
+ define_setting(:app_key, @app_key)
+ define_setting(:client_key, @client_key)
+ @app_key
+ else
+ error = resp.error.as(HueError)
+ logger.error { "type #{error.type}: #{error.description}" }
+ error.description
+ end
+ end
+
+ enum Resource
+ Light
+ Scene
+ Room
+ Zone
+ GroupedLight
+ Device
+ Motion
+ GroupedMotion
+ GroupedLightLevel
+ CameraMotion
+ Temperature
+ end
+
+ def resource_details(resource : Resource, id : String? = nil)
+ # NOTE:: HUE does not like trailing slashes, hence the weird check below
+ response = get("/clip/v2/resource/#{resource.to_s.underscore}#{id.presence ? "/#{id}" : ""}", headers: HTTP::Headers{
+ "hue-application-key" => app_key,
+ })
+ JSON.parse response.body
+ end
+
+ def device_list
+ resource_details(Resource::Device)
+ end
+
+ def scene_list
+ resource_details(Resource::Scene)
+ end
+
+ # convert RGB to CIE which is used by Hue
+ def rgb_to_cie(r : UInt8, g : UInt8, b : UInt8) : Tuple(Float64, Float64)
+ # Normalize RGB values
+ r_norm = r / 255.0
+ g_norm = g / 255.0
+ b_norm = b / 255.0
+
+ # Apply gamma correction
+ r_lin = (r_norm > 0.04045) ? ((r_norm + 0.055) / 1.055) ** 2.4 : r_norm / 12.92
+ g_lin = (g_norm > 0.04045) ? ((g_norm + 0.055) / 1.055) ** 2.4 : g_norm / 12.92
+ b_lin = (b_norm > 0.04045) ? ((b_norm + 0.055) / 1.055) ** 2.4 : b_norm / 12.92
+
+ # Convert to XYZ
+ x = r_lin * 0.4124 + g_lin * 0.3576 + b_lin * 0.1805
+ y = r_lin * 0.2126 + g_lin * 0.7152 + b_lin * 0.0722
+ z = r_lin * 0.0193 + g_lin * 0.1192 + b_lin * 0.9505
+
+ # Convert to xy
+ xy_x = x / (x + y + z)
+ xy_y = y / (x + y + z)
+
+ {xy_x, xy_y}
+ end
+
+ def set_light_colour(light_id : Int32, r : UInt8 = 0_u8, g : UInt8 = 0_u8, b : UInt8 = 0_u8)
+ x, y = rgb_to_cie(r, g, b)
+ response = put("/clip/v2/resource/light/#{light_id}", headers: HTTP::Headers{
+ "hue-application-key" => app_key,
+ }, body: {color: {xy: {x: x, y: y}}}.to_json)
+ raise "error controlling light (#{response.status})\n#{response.body}" unless response.success?
+ JSON.parse response.body
+ end
+
+ def set_light_level(light_id : String, level : UInt32, resource : Resource = Resource::Light)
+ level = level.clamp(0, 100)
+
+ if level == 0
+ response = put("/clip/v2/resource/#{resource.to_s.underscore}/#{light_id}", headers: HTTP::Headers{
+ "hue-application-key" => app_key,
+ }, body: {on: {on: false}}.to_json)
+ else
+ response = put("/clip/v2/resource/#{resource.to_s.underscore}/#{light_id}", headers: HTTP::Headers{
+ "hue-application-key" => app_key,
+ }, body: {on: {on: true}, dimming: {brightness: level}}.to_json)
+ end
+
+ raise "error controlling light (#{response.status})\n#{response.body}" unless response.success?
+ level
+ end
+
+ def set_scene(scene_id : String)
+ response = put("/clip/v2/resource/scene/#{scene_id}", headers: HTTP::Headers{
+ "hue-application-key" => app_key,
+ }, body: {recall: {action: :active}}.to_json)
+ raise "error activating scene (#{response.status})\n#{response.body}" unless response.success?
+ response.body
+ end
+
+ # ==================
+ # Lighting Interface
+ # ==================
+ def set_lighting_scene(scene : UInt32, area : Area? = nil, fade_time : UInt32 = 1000_u32)
+ scene_id = @scenes[scene]
+ set_scene scene_id
+ end
+
+ def lighting_scene?(area : Area? = nil)
+ raise "not really a thing"
+ end
+
+ def set_lighting_level(level : Float64, area : Area? = nil, fade_time : UInt32 = 1000_u32)
+ level_int = level.round_away.to_u32
+ area = area.as(Area)
+ area_id = area.id.as(String)
+ resource = Resource.parse(area.component || "light")
+
+ # TODO:: fade_time is possible using signaling duration
+ set_light_level(area_id, level_int, resource)
+ end
+
+ def lighting_level?(area : Area? = nil)
+ raise "no area provided" unless area
+ area_id = area.id.as(String)
+ resource = Resource.parse(area.component || "light")
+
+ json = resource_details(resource, area_id)
+ state = json["on"]["on"].as_bool
+ state ? json["dimming"]["brightness"].as_i : 0
+ end
+end
diff --git a/drivers/philips/hue_spec.cr b/drivers/philips/hue_spec.cr
new file mode 100644
index 00000000000..fbcdcc6cbfd
--- /dev/null
+++ b/drivers/philips/hue_spec.cr
@@ -0,0 +1,23 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "MessageMedia::SMS" do
+ # Connect response (both return a 200 success response)
+ success_json = "[{\"success\":{\"username\":\"KrSPjVbcROQj4MIhQ1U2XZ2hgi-jznfhBL8eBZIt\",\"clientkey\":\"26CE9D1876E8570DA1C6A56F2A08F4AA\"}}]"
+ error_json = "[{\"error\":{\"type\":101,\"address\":\"\",\"description\":\"link button not pressed\"}}]"
+
+ # Fail a registration request
+ retval = exec(:register)
+ expect_http_request do |_request, response|
+ response.status_code = 200
+ response << error_json
+ end
+ retval.get.should eq("link button not pressed")
+
+ # succeed at registration
+ retval = exec(:register)
+ expect_http_request do |_request, response|
+ response.status_code = 200
+ response << success_json
+ end
+ retval.get.should eq("KrSPjVbcROQj4MIhQ1U2XZ2hgi-jznfhBL8eBZIt")
+end
diff --git a/drivers/place/area_config.cr b/drivers/place/area_config.cr
new file mode 100644
index 00000000000..7c4df5385ed
--- /dev/null
+++ b/drivers/place/area_config.cr
@@ -0,0 +1,70 @@
+require "json"
+require "./area_polygon"
+
+module Place
+ class Geometry
+ include JSON::Serializable
+
+ def initialize(@coordinates, @geo_type = "Polygon")
+ end
+
+ @[JSON::Field(key: "type")]
+ property geo_type : String
+ property coordinates : Array(Tuple(Float64, Float64))
+ end
+
+ class AreaConfig
+ include JSON::Serializable
+
+ def initialize(@id, name, coordinates, building_id = nil, @area_type = "Feature", @feature_type = "section", capacity = nil)
+ @geometry = Geometry.new(coordinates)
+ @properties = Hash(String, JSON::Any::Type | Hash(String, JSON::Any)).new
+ @properties["name"] = name
+ @properties["building_id"] = building_id if building_id
+ @properties["capacity"] = capacity if capacity
+ end
+
+ @[JSON::Field(ignore: true)]
+ @polygon : Polygon? = nil
+
+ property id : String
+
+ @[JSON::Field(key: "type")]
+ property area_type : String
+ property feature_type : String
+
+ property geometry : Geometry
+ property properties : Hash(String, JSON::Any::Type)
+
+ @[JSON::Field(ignore: true)]
+ @adjusted_coords : Array(Tuple(Float64, Float64))? = nil
+
+ def name : String
+ self.properties["name"].as(String)
+ end
+
+ def building : String?
+ self.properties["building_id"]?.as?(String)
+ end
+
+ def capacity : Int32?
+ self.properties["capacity"]?.as?(Int64 | Float64).try &.to_i
+ end
+
+ def coordinates
+ if coords = @adjusted_coords
+ coords
+ else
+ self.geometry.coordinates
+ end
+ end
+
+ def coordinates(map_width : Float64, map_height : Float64)
+ @adjusted_coords = self.geometry.coordinates.map { |(x, y)| {x * map_width, y * map_height} }
+ end
+
+ def polygon : Polygon
+ @polygon ||= Polygon.new(coordinates.map { |coords| Point.new(*coords) })
+ end
+ end
+end
diff --git a/drivers/place/area_management.cr b/drivers/place/area_management.cr
new file mode 100644
index 00000000000..a634086c728
--- /dev/null
+++ b/drivers/place/area_management.cr
@@ -0,0 +1,686 @@
+require "set"
+require "placeos"
+require "placeos-driver"
+require "./area_config"
+require "./area_polygon"
+require "placeos-driver/interface/sensor"
+
+::PlaceOS::Driver::Interface::Sensor.include_unit_conversions
+
+class Place::AreaManagement < PlaceOS::Driver
+ descriptive_name "PlaceOS Area Management"
+ generic_name :AreaManagement
+ description %(counts trackable objects, such as laptops, in building areas)
+
+ accessor staff_api : StaffAPI_1
+
+ default_settings({
+ # time in seconds
+ poll_rate: 20,
+
+ # How many decimal places area summaries should be rounded to
+ rounding_precision: 2,
+
+ # How many wireless devices should we ignore
+ duplication_factor: 0.8,
+
+ # Driver to query
+ location_service: "LocationServices",
+ include_sensors: true,
+
+ _areas: {
+ "zone-1234" => [
+ {
+ id: "lobby1",
+ name: "George St Lobby",
+ building: "building-zone-id",
+ coordinates: [{3, 5}, {5, 6}, {6, 1}],
+ },
+ ],
+ },
+
+ # If another systems has different desk IDs configured you can add them to
+ # desk metadata and then specify the alternative field names here
+ # desk_id_mappings: ["floorsensedeskid", "vergesensedeskid"]
+
+ units: {
+ "Temperature" => "Cel",
+ },
+
+ is_campus: false,
+ })
+
+ alias AreaSetting = NamedTuple(
+ id: String,
+ name: String,
+ building: String?,
+ coordinates: Array(Tuple(Float64, Float64)))
+
+ alias LevelCapacity = NamedTuple(
+ total_desks: Int32,
+ total_capacity: Int32,
+ desk_ids: Array(String),
+ desk_mappings: Hash(String, String))
+
+ alias RawLevelDetails = NamedTuple(
+ wireless_devices: Int32,
+ desk_bookings: Int32,
+ desk_usage: Int32,
+ capacity: LevelCapacity,
+ sensors: Hash(String, Float64),
+ )
+
+ getter? campus : Bool = false
+
+ # level_zone_id => building_zone_id
+ getter level_buildings : Hash(String, String) = {} of String => String
+ # zone_id => sensors
+ getter level_sensors : Hash(String, Hash(String, SensorMeta)) = {} of String => Hash(String, SensorMeta)
+ # zone_id => areas
+ getter level_areas : Hash(String, Array(AreaConfig)) = {} of String => Array(AreaConfig)
+ # area_id => area
+ getter areas : Hash(String, AreaConfig) = {} of String => AreaConfig
+
+ # zone_id => desk_ids
+ @duplication_factor : Float64 = 0.8
+ getter level_details : Hash(String, LevelCapacity) = {} of String => LevelCapacity
+
+ # PlaceOS client config
+ getter building_id : String { get_building_id.as(String) }
+
+ @poll_rate : Time::Span = 60.seconds
+ @location_service : String = "LocationServices"
+
+ @rate_limit : Channel(Nil) = Channel(Nil).new
+ @update_lock : Mutex = Mutex.new
+ @include_sensors : Bool = false
+
+ # Building => sensor_id => sensor meta
+ getter sensor_discovery = Hash(String, Hash(String, SensorMeta)).new
+
+ @desk_id_mappings = [] of String
+
+ @rounding_precision : UInt32 = 2
+
+ @units = {} of SensorType => String
+
+ def on_load
+ spawn { rate_limiter }
+ spawn { update_scheduler }
+
+ on_update
+ end
+
+ def on_unload
+ @rate_limit.close
+ end
+
+ def on_update
+ @include_sensors = setting?(Bool, :include_sensors) || false
+ @campus = setting?(Bool, :is_campus) || false
+ @desk_id_mappings = setting?(Array(String), :desk_id_mappings) || [] of String
+
+ @poll_rate = (setting?(Int32, :poll_rate) || 60).seconds
+ @location_service = setting?(String, :location_service).presence || "LocationServices"
+ @duplication_factor = setting?(Float64, :duplication_factor) || 0.8
+ @sensor_discovery = Hash(String, Hash(String, SensorMeta)).new { |hash, key| hash[key] = {} of String => SensorMeta }
+
+ @rounding_precision = setting?(UInt32, :rounding_precision) || 2_u32
+
+ # Areas are defined in metadata, this is mainly here so we can write specs
+ if building_areas = setting?(Hash(String, Array(AreaSetting)), :areas)
+ @level_areas.clear
+ building_areas.each do |zone_id, areas|
+ @level_areas[zone_id] = areas.map do |area|
+ config = AreaConfig.new(area[:id], area[:name], area[:coordinates], area[:building])
+ @areas[config.id] = config
+ config
+ end
+ end
+ end
+
+ schedule.clear
+ schedule.every(@poll_rate) { synchronize_all_levels }
+
+ if @include_sensors
+ schedule.in(@poll_rate * 3) do
+ # sync the sensor discovery data for map placement
+ schedule.every(2.hours + rand(300).seconds, immediate: true) { write_sensor_discovery }
+ end
+ end
+
+ units = setting?(Hash(String, String), :units) || {} of String => String
+ @units = units.transform_keys { |key| SensorType.parse(key) }
+ end
+
+ # The location services provider
+ protected def location_service
+ system[@location_service]
+ end
+
+ # Finds the building ID for the current location services object
+ def get_building_id
+ building_setting = setting?(String, :building_zone_override)
+ return building_setting if building_setting.presence
+ zone_ids = staff_api.zones(tags: "building").get.as_a.map(&.[]("id").as_s)
+ (zone_ids & system.zones).first
+ rescue error
+ logger.warn(exception: error) { "unable to determine building zone id" }
+ nil
+ end
+
+ # ===============================
+ # SENSOR DETAILS
+ # ===============================
+
+ alias SensorDetail = Interface::Sensor::Detail
+ alias SensorType = Interface::Sensor::SensorType
+
+ struct SensorMeta
+ include JSON::Serializable
+
+ def initialize(@name, @type, @level, @x, @y)
+ end
+
+ property type : SensorType?
+ property name : String?
+ property level : String?
+ property x : Float64?
+ property y : Float64?
+ end
+
+ def write_sensor_discovery
+ sensor_discovery.each do |b_id, sensors|
+ staff_api.write_metadata(b_id, "sensor-discovered", sensors)
+ end
+ end
+
+ # returns the sensor location data that has been configured
+ def sensor_locations(level_id : String? = nil)
+ if level_id
+ @level_sensors[level_id]? || {} of String => SensorMeta
+ else
+ @level_sensors.values.reduce({} of String => SensorMeta) { |acc, i| acc.merge!(i) }
+ end
+ end
+
+ # Queries all the sensors in a building and exposes the data
+ def request_sensor_data(level_id : String) : Array(SensorDetail)
+ level_sensors = @level_sensors[level_id]?
+ sensors = location_service.sensors(zone_id: level_id).get.as_a
+
+ return [] of SensorDetail if sensors.empty?
+ details = Array(SensorDetail).from_json(sensors.to_json)
+
+ building_id_local = level_buildings[level_id]? || building_id
+ locs = sensor_locations(level_id)
+
+ details = details.select! do |sensor|
+ id = sensor.id ? "#{sensor.mac}-#{sensor.id}" : sensor.mac
+ @sensor_discovery[building_id_local][id] = SensorMeta.new(
+ sensor.name,
+ sensor.type,
+ sensor.level,
+
+ # TODO:: calculate x, y if a loc is given
+ sensor.x,
+ sensor.y
+ )
+
+ sensor.module_id = sensor.binding = sensor.loc = nil
+
+ # check if this sensor has a user defined location
+ if location = locs[id]?
+ sensor.x = location.x
+ sensor.y = location.y
+ sensor.level = location.level
+ sensor.building = building_id_local
+ end
+
+ # If a sensor has been added to the map, add the level details
+ if sensor.level.nil? && level_sensors
+ if level_sensors[sensor.id ? "#{sensor.mac}-#{sensor.id}" : sensor.mac]?
+ sensor.level = level_id
+ end
+ end
+
+ if sensor.x && sensor.level
+ # TODO:: calulate the lat, lon and s2 cell id
+
+ # transform different sensor units to a common unit
+ if (curr_unit = sensor.unit) && (desired_unit = @units[sensor.type]?) && curr_unit != desired_unit
+ begin
+ sensor.value = Units::Measurement.new(sensor.value, curr_unit).convert_to(desired_unit).to_f
+ sensor.unit = desired_unit
+ rescue error
+ logger.warn(exception: error) { "failed to convert #{sensor.value} #{curr_unit} => #{desired_unit}" }
+ end
+ end
+
+ # only select sensors that have a location
+ sensor
+ end
+ end
+
+ self["#{level_id}:sensors"] = {
+ value: details,
+ ts_hint: "complex",
+ ts_map: {
+ x: "xloc",
+ y: "yloc",
+ },
+ ts_tag_keys: {"s2_cell_id"},
+ ts_tags: {
+ pos_building: building_id_local,
+ pos_level: level_id,
+ },
+ }
+
+ details
+ end
+
+ # ===============================
+ # LOCATION DETAILS
+ # ===============================
+
+ # Updates a single zone, syncing the metadata
+ protected def update_level_details(level_details, zone, metadata)
+ return unless zone.tags.includes?("level")
+
+ if desks = metadata["desks"]?
+ desk_map = {} of String => String
+
+ if @desk_id_mappings.empty?
+ ids = desks.details.as_a.map { |desk| desk["id"].as_s }
+ else
+ desk_details = desks.details.as_a
+ ids = Array(String).new(desk_details.size)
+
+ desk_details.each do |desk|
+ desk_id = desk["id"].as_s
+ ids << desk_id
+ @desk_id_mappings.each do |mapping|
+ if alt_id = desk[mapping]?
+ desk_map[alt_id.as_s] = desk_id
+ end
+ end
+ end
+ end
+
+ ids = desks.details.as_a.map { |desk| desk["id"].as_s }
+ level_details[zone.id] = {
+ total_desks: ids.size,
+ total_capacity: zone.capacity,
+ desk_ids: ids,
+ desk_mappings: desk_map,
+ }
+ else
+ level_details[zone.id] = {
+ total_desks: zone.count,
+ total_capacity: zone.capacity,
+ desk_ids: [] of String,
+ desk_mappings: {} of String => String,
+ }
+ end
+
+ if regions = metadata["map_regions"]?
+ area_data = Array(AreaConfig).from_json(regions.details["areas"].to_json)
+ @level_areas[zone.id] = area_data
+ area_data.each { |area| @areas[area.id] = area }
+ else
+ @level_areas.delete(zone.id)
+ end
+
+ if sensors = metadata["sensor-locations"]?
+ sensor_data = Hash(String, SensorMeta).from_json(sensors.details.to_json)
+ zone_id = zone.id
+ sensor_data.transform_values! { |sensor| sensor.level = zone_id; sensor }
+ @level_sensors[zone_id] = sensor_data
+ else
+ @level_sensors.delete(zone.id)
+ end
+ end
+
+ alias Zone = PlaceOS::Client::API::Models::Zone
+ alias Metadata = Hash(String, PlaceOS::Client::API::Models::Metadata)
+ alias ChildMetadata = Array(NamedTuple(zone: Zone, metadata: Metadata))
+
+ # Grabs all the level zones in the building and syncs the metadata
+ protected def sync_level_details
+ buildings = if campus?
+ # building_id here is actually the campus id
+ Array(Zone).from_json(staff_api.zones(parent: building_id).get.to_json).map(&.id)
+ else
+ [building_id]
+ end
+
+ level_details = {} of String => LevelCapacity
+ level_buildings = {} of String => String
+
+ buildings.each do |b_id|
+ # Attempt to obtain the latest version of the metadata
+ response = ChildMetadata.from_json(staff_api.metadata_children(b_id).get.to_json)
+ response.each do |meta|
+ level_buildings[meta[:zone].id] = b_id
+ update_level_details(level_details, meta[:zone], meta[:metadata])
+ end
+ end
+
+ @level_details = level_details
+ @level_buildings = level_buildings
+ rescue error
+ logger.error(exception: error) { "obtaining level metadata" }
+ end
+
+ protected def update_level_locations(level_counts, level_id, details, sensor_data)
+ areas = @level_areas[level_id]? || [] of AreaConfig
+ unsorted_sensors = sensor_data || [] of SensorDetail
+ sensors = Hash(String, Array(SensorDetail)).new { |h, k| h[k] = [] of SensorDetail }
+ unsorted_sensors.each { |sensor| sensors[sensor.modified_type.underscore] << sensor }
+
+ # Provide the frontend with the list of all known desk ids on a level
+ self["#{level_id}:desk_ids"] = details[:desk_ids]
+
+ # Get location data for the level
+ locations = location_service.device_locations(level_id).get.as_a
+
+ # Apply any map id transformations
+ desk_mappings = details[:desk_mappings]
+ locations = locations.map do |loc|
+ loc = loc.as_h
+ if location_type = loc["location"]?
+ # measurement name for simplified querying in influxdb
+ loc["measurement"] = location_type
+ case location_type
+ when "desk"
+ if maps_to = desk_mappings[loc["map_id"].as_s]?
+ loc["map_id"] = JSON::Any.new(maps_to)
+ end
+ when "booking"
+ if (has_map_id = loc["map_id"]?.try(&.as_s)) && loc["type"].as_s == "desk" && (maps_to = desk_mappings[has_map_id]?)
+ loc["map_id"] = JSON::Any.new(maps_to)
+ end
+ end
+ end
+ loc
+ end
+
+ # Provide to the frontend
+ self[level_id] = {
+ value: locations,
+ ts_hint: "complex",
+ ts_map: {
+ x: "xloc",
+ y: "yloc",
+ },
+ ts_tag_keys: {"s2_cell_id"},
+ ts_tags: {
+ pos_building: level_buildings[level_id]? || building_id,
+ pos_level: level_id,
+ },
+ }
+
+ # Grab the x,y locations
+ wireless_count = 0
+ desk_count = 0
+ desk_bookings = 0
+ xy_locs = locations.select do |loc|
+ case loc["location"].as_s
+ when "wireless"
+ wireless_count += 1
+
+ # Keep if x, y coords are present
+ !loc["x"].raw.nil?
+ when "desk"
+ desk_count += 1 if (loc["at_location"]?.try(&.as_i?) || 0) > 0
+ false
+ when "booking"
+ desk_bookings += 1 if loc["type"].as_s == "desk"
+ false
+ else
+ false
+ end
+ end
+
+ people_counts = sensors["people_count"]?
+ sensor_summary = sensors.transform_values do |values|
+ if values.size > 0
+ (values.sum(&.value) / values.size).round(@rounding_precision)
+ else
+ 0.0
+ end
+ end
+ if people_counts
+ sensor_summary["people_count_sum"] = people_counts.sum(&.value)
+ end
+
+ # build the level overview
+ level_counts[level_id] = {
+ wireless_devices: wireless_count,
+ desk_bookings: desk_bookings,
+ desk_usage: desk_count,
+ capacity: details,
+ sensors: sensor_summary,
+ }
+
+ # we need to know the map dimensions to be able to count people in areas
+ map_width = 100.0
+ map_height = 100.0
+
+ if tmp_loc = xy_locs[0]?
+ # ensure map width and height are known
+ map_width_raw = tmp_loc["map_width"]?.try(&.raw)
+ case map_width_raw
+ when Int64, Float64
+ map_width = map_width_raw.to_f
+ end
+
+ map_height_raw = tmp_loc["map_height"]?.try(&.raw)
+ case map_height_raw
+ when Int64, Float64
+ map_height = map_height_raw.to_f
+ end
+ end
+
+ # Calculate the device counts for each area
+ area_counts = [] of Hash(String, String | Int32 | Float64)
+ if map_width != -1.0
+ # adjust sensor x,y so we check if they are in areas
+ sensors.each do |_type, array|
+ array.map! do |sensor|
+ sensor.x = sensor.x.as(Float64) * map_width
+ sensor.y = sensor.y.as(Float64) * map_height
+ sensor
+ end
+ end
+
+ areas.each do |area|
+ count = 0
+
+ # Ensure the area is configured
+ area.coordinates(map_width, map_height)
+ polygon = area.polygon
+
+ # Calculate counts, our config uses browser coordinate systems,
+ # so need to adjust any x,y values being received for this
+ xy_locs.each do |loc|
+ case loc["coordinates_from"]?.try(&.raw)
+ when "bottom-left"
+ count += 1 if polygon.contains(loc["x"].as_f, map_height - loc["y"].as_f)
+ else
+ count += 1 if polygon.contains(loc["x"].as_f, loc["y"].as_f)
+ end
+ end
+
+ # build sensor summary for the area
+ area_sensors = Hash(String, Array(SensorDetail)).new { |h, k| h[k] = [] of SensorDetail }
+ sensors.each do |type, array|
+ array.each do |sensor|
+ area_sensors[type] << sensor if polygon.contains(sensor.x.as(Float64), sensor.y.as(Float64))
+ end
+ end
+
+ people_counts = area_sensors["people_count"]?
+ sensor_summary = area_sensors.transform_values do |values|
+ if values.size > 0
+ (values.sum(&.value) / values.size).round(@rounding_precision)
+ else
+ 0.0
+ end
+ end
+ if people_counts
+ sensor_summary["people_count_sum"] = people_counts.sum(&.value)
+ end
+
+ if capacity = area.capacity
+ sensor_summary["capacity"] = capacity
+ end
+
+ area_counts << {
+ "area_id" => area.id,
+ "name" => area.name,
+ "count" => (count * @duplication_factor).to_i,
+ }.merge(sensor_summary)
+ end
+ end
+
+ # Provide the frontend the area details
+ self["#{level_id}:areas"] = {
+ value: area_counts,
+ measurement: "area_summary",
+ ts_hint: "complex",
+ ts_tags: {
+ pos_building: level_buildings[level_id]? || building_id,
+ pos_level: level_id,
+ },
+ }
+ rescue error
+ logger.debug(exception: error) { "while parsing #{level_id}" }
+ sleep 200.milliseconds
+ end
+
+ @level_counts : Hash(String, RawLevelDetails) = {} of String => RawLevelDetails
+
+ def request_level_locations(level_id : String, sensor_data : Array(SensorDetail)? = nil, overview : Bool = true) : Nil
+ @update_lock.synchronize do
+ zone = Zone.from_json(staff_api.zone(level_id).get.to_json)
+ if !zone.tags.includes?("level")
+ logger.warn { "attempted to update location for #{zone.name} (#{level_id}) which is not tagged as a level" }
+ return
+ end
+ metadata = Metadata.from_json(staff_api.metadata(level_id).get.to_json)
+
+ update_level_details @level_details, zone, metadata
+ update_level_locations @level_counts, level_id, @level_details[level_id], sensor_data
+ update_overview if overview
+ end
+ end
+
+ protected def update_overview
+ self[:overview] = @level_counts.transform_values { |details| build_level_stats(**details) }
+ end
+
+ def is_inside?(x : Float64, y : Float64, area_id : String) : Bool
+ area = @areas[area_id]
+ area.polygon.contains(x, y)
+ end
+
+ protected def build_level_stats(wireless_devices, desk_bookings, desk_usage, capacity, sensors)
+ # raw data
+ total_desks = capacity[:total_desks]
+ total_capacity = capacity[:total_capacity]
+
+ # normalised data
+ adjusted_devices = wireless_devices * @duplication_factor
+
+ if total_capacity <= 0
+ percentage_use = 100.0
+ individual_impact = 100.0
+ else
+ percentage_use = (adjusted_devices / total_capacity) * 100.0
+ individual_impact = 100.0 / total_capacity
+ end
+ remaining_capacity = total_capacity - adjusted_devices
+ recommendation = remaining_capacity + remaining_capacity * individual_impact
+
+ {
+ "measurement" => "level_summary",
+ "desk_count" => total_desks,
+ "desk_bookings" => desk_bookings, # booked desks
+ "desk_usage" => desk_usage, # sensor detected someone at a desk
+ "device_capacity" => total_capacity,
+ "device_count" => wireless_devices,
+ "estimated_people" => adjusted_devices.to_i,
+ "percentage_use" => percentage_use,
+
+ # higher the number, better the recommendation
+ "recommendation" => recommendation,
+ }.merge(sensors)
+ end
+
+ # ===============================
+ # RATE LIMITER
+ # ===============================
+
+ # This is to limit the number of "real-time" updates
+ # batching operations to provide fast updates that don't waste CPU cycles
+ protected def rate_limiter
+ sleep 3
+
+ loop do
+ begin
+ break if @rate_limit.closed?
+ @rate_limit.send(nil)
+ rescue error
+ logger.error(exception: error) { "issue with rate limiter" }
+ ensure
+ sleep 3
+ end
+ end
+ rescue
+ # Possible error with logging exception, restart rate limiter silently
+ spawn { rate_limiter } unless terminated?
+ end
+
+ @update_levels : Set(String) = Set.new([] of String)
+ @update_all : Bool = true
+ @schedule_lock : Mutex = Mutex.new
+
+ def update_available(level_ids : Array(String))
+ @schedule_lock.synchronize { @update_levels.concat level_ids }
+ end
+
+ def synchronize_all_levels
+ @schedule_lock.synchronize { @update_all = true }
+ end
+
+ protected def update_scheduler
+ loop do
+ @rate_limit.receive
+ @schedule_lock.synchronize do
+ begin
+ sensor_data = [] of SensorDetail
+ if @update_all
+ @update_lock.synchronize { sync_level_details }
+ @level_buildings.each_key do |level_id|
+ sensor_data = request_sensor_data(level_id) if @include_sensors
+ request_level_locations level_id, sensor_data, false
+ end
+ @update_lock.synchronize { update_overview }
+ else
+ @update_levels.each do |level_id|
+ sensor_data = request_sensor_data(level_id) if @include_sensors
+ request_level_locations level_id, sensor_data, false
+ end
+ @update_lock.synchronize { update_overview }
+ end
+ rescue error
+ logger.error(exception: error) { "error updating floors" }
+ ensure
+ @update_levels.clear
+ @update_all = false
+ end
+ end
+ end
+ end
+end
diff --git a/drivers/place/area_management_spec.cr b/drivers/place/area_management_spec.cr
new file mode 100644
index 00000000000..1bddc0a43d2
--- /dev/null
+++ b/drivers/place/area_management_spec.cr
@@ -0,0 +1,31 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::AreaCount" do
+ settings({
+ areas: {
+ "zone-1234" => [
+ {
+ id: "lobby1",
+ name: "George St Lobby",
+ building: "building-zone-id",
+ coordinates: [{3, 5}, {5, 6}, {6, 1}],
+ },
+ ],
+ },
+ })
+
+ # Used this tool to work out coordinates: https://www.mathsisfun.com/geometry/polygons-interactive.html
+ exec(:is_inside?, 4, 5, "lobby1").get.should eq(true)
+ exec(:is_inside?, 4, 4, "lobby1").get.should eq(true)
+ exec(:is_inside?, 5, 5, "lobby1").get.should eq(true)
+ exec(:is_inside?, 5, 4, "lobby1").get.should eq(true)
+ exec(:is_inside?, 5, 3, "lobby1").get.should eq(true)
+ exec(:is_inside?, 3.1, 5, "lobby1").get.should eq(true)
+
+ exec(:is_inside?, 3, 6, "lobby1").get.should eq(nil)
+ exec(:is_inside?, 4, 6, "lobby1").get.should eq(nil)
+ exec(:is_inside?, 4.6, 5.9, "lobby1").get.should eq(nil)
+ exec(:is_inside?, 5.2, 5.4, "lobby1").get.should eq(nil)
+ exec(:is_inside?, 5.5, 1.5, "lobby1").get.should eq(nil)
+ exec(:is_inside?, 5.9, 2, "lobby1").get.should eq(nil)
+end
diff --git a/drivers/place/area_polygon.cr b/drivers/place/area_polygon.cr
new file mode 100644
index 00000000000..bdc55b15611
--- /dev/null
+++ b/drivers/place/area_polygon.cr
@@ -0,0 +1,71 @@
+require "math"
+
+# Crystal lang point in a polygon, based on
+# https://wrf.ecse.rpi.edu/Research/Short_Notes/pnpoly.html
+
+# 1. The polygon may contain multiple separate components, and/or holes, which may be concave, provided that you separate the components and holes with a (0,0) vertex, as follows.
+# First, include a (0,0) vertex.
+# Then include the first component' vertices, repeating its first vertex after the last vertex.
+# Include another (0,0) vertex.
+# Include another component or hole, repeating its first vertex after the last vertex.
+# Repeat the above two steps for each component and hole.
+# Include a final (0,0) vertex.
+# 2. For example, let three components' vertices be A1, A2, A3, B1, B2, B3, and C1, C2, C3. Let two holes be H1, H2, H3, and I1, I2, I3. Let O be the point (0,0). List the vertices thus:
+# O, A1, A2, A3, A1, O, B1, B2, B3, B1, O, C1, C2, C3, C1, O, H1, H2, H3, H1, O, I1, I2, I3, I1, O.
+# 3. Each component or hole's vertices may be listed either clockwise or counter-clockwise.
+# 4. If there is only one connected component, then it is optional to repeat the first vertex at the end. It's also optional to surround the component with zero vertices.
+
+struct Point
+ def initialize(@x : Float64, @y : Float64)
+ end
+
+ property x : Float64
+ property y : Float64
+
+ # pythagoras
+ def distance_to(point : Point)
+ # lengths of triangles edge
+ a = point.x - @x
+ b = point.y - @y
+
+ Math.sqrt((a * a) + (b * b))
+ end
+end
+
+class Polygon
+ def initialize(@points : Array(Point))
+ @xmax = @xmin = @points[0].x
+ @ymax = @ymin = @points[0].y
+
+ @points[1..-1].each do |point|
+ @xmax = point.x if point.x > @xmax
+ @ymax = point.y if point.y > @ymax
+ @xmin = point.x if point.x < @xmin
+ @ymin = point.y if point.y < @ymin
+ end
+ end
+
+ getter points : Array(Point)
+ getter xmin : Float64
+ getter ymin : Float64
+ getter xmax : Float64
+ getter ymax : Float64
+
+ def contains(testx : Float64, testy : Float64)
+ # definitely not within the polygon, quick check
+ return false if testx < @xmin || testx > @xmax || testy < @ymin || testy > @ymax
+
+ inside = false
+ previous_index = @points.size - 1
+
+ @points.each_with_index do |point, index|
+ previous = @points[previous_index]
+ if ((point.y > testy) != (previous.y > testy)) && (testx < (previous.x - point.x) * (testy - point.y) / (previous.y - point.y) + point.x)
+ inside = !inside
+ end
+ previous_index = index
+ end
+
+ inside
+ end
+end
diff --git a/drivers/place/at_capacity_mailer.cr b/drivers/place/at_capacity_mailer.cr
new file mode 100644
index 00000000000..4c9c9cea31b
--- /dev/null
+++ b/drivers/place/at_capacity_mailer.cr
@@ -0,0 +1,225 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+require "place_calendar"
+require "./bookings/asset_name_resolver"
+
+class Place::AtCapacityMailer < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+ include Place::AssetNameResolver
+
+ descriptive_name "PlaceOS At Capacity Mailer"
+ generic_name :AtCapacityMailer
+ description %(sends a notification when the specified type is at capacity)
+
+ default_settings({
+ timezone: "Australia/Sydney",
+ booking_type: "desk", # desk, locker, parking, etc
+ zones: [] of String, # The zones to check for bookings
+ notify_email: ["concierge@place.com"],
+ email_schedule: "*/5 * * * *", # the frequency to check for bookings
+ time_window_hours: 1, # the number of hours to check for bookings
+ debounce_time_minutes: 60, # the time to wait before sending another email
+ email_template: "at_capacity",
+ unique_templates: false, # this appends the booking type to the template name
+ asset_cache_timeout: 3600_i64, # 1 hour
+ })
+
+ accessor staff_api : StaffAPI_1
+
+ def mailer
+ system.implementing(Interface::Mailer)[0]
+ end
+
+ # used by AssetNameResolver and LockerMetadataParser
+ accessor locations : LocationServices_1
+ getter building_id : String do
+ locations.building_id.get.as_s
+ end
+ getter levels : Array(String) do
+ staff_api.systems_in_building(building_id).get.as_h.keys
+ end
+
+ def on_load
+ on_update
+ end
+
+ @time_zone : Time::Location = Time::Location.load("Australia/Sydney")
+
+ @booking_type : String = "desk"
+ @zones : Array(String) = [] of String
+
+ @notify_email : Array(String) = [] of String
+ @email_schedule : String = "*/5 * * * *"
+ @time_window_hours : Int32 = 1
+ @debounce_time_minutes : Int32 = 60
+ @last_email_sent : Hash(String, Time) = {} of String => Time
+
+ @email_template : String = "at_capacity"
+ @unique_templates : Bool = false
+ @template_suffix : String = ""
+ @template_fields_suffix : String = ""
+
+ @zone_cache : Hash(String, Zone) = {} of String => Zone
+
+ def on_update
+ @building_id = nil
+ @levels = nil
+
+ time_zone = setting?(String, :calendar_time_zone).presence || "Australia/Sydney"
+ @time_zone = Time::Location.load(time_zone)
+
+ @booking_type = setting?(String, :booking_type).presence || "desk"
+ @zones = setting?(Array(String), :zones) || [] of String
+
+ @notify_email = setting?(Array(String), :notify_email) || [] of String
+ @email_schedule = setting?(String, :email_schedule).presence || "*/5 * * * *"
+ @time_window_hours = setting?(Int32, :time_window_hours) || 1
+ @debounce_time_minutes = setting?(Int32, :debounce_time_minutes) || 60
+
+ @email_template = setting?(String, :email_template) || "at_capacity"
+ @unique_templates = setting?(Bool, :unique_templates) || false
+ @template_suffix = @unique_templates ? "_#{@booking_type}" : ""
+ @template_fields_suffix = @unique_templates ? " (#{@booking_type})" : ""
+
+ @asset_cache_timeout = setting?(Int64, :asset_cache_timeout) || 3600_i64
+ clear_asset_cache
+
+ schedule.clear
+
+ # find assets
+ schedule.every(60.minutes) { get_asset_ids }
+
+ if emails = @email_schedule
+ schedule.cron(emails, @time_zone) { check_capacity }
+ end
+ end
+
+ @[Security(Level::Support)]
+ def check_capacity
+ asset_ids = self[:assets_ids]? ? Hash(String, Array(String)).from_json(self[:assets_ids].to_json) : get_asset_ids
+
+ booked_asset_ids = get_booked_asset_ids
+
+ @zones.each do |zone_id|
+ next unless (zone_asset_ids = asset_ids[zone_id]?) && !zone_asset_ids.empty?
+
+ if (zone_asset_ids - booked_asset_ids).empty?
+ logger.debug { "zone #{zone_id} is at capacity" }
+ send_email(zone_id)
+ end
+ end
+ end
+
+ def get_asset_ids : Hash(String, Array(String))
+ assets_ids = {} of String => Array(String)
+
+ @zones.each do |zone_id|
+ assets_ids[zone_id] = lookup_assets(zone_id, @booking_type).map { |asset| asset.id }.uniq!
+ end
+
+ self[:assets_ids] = assets_ids
+ end
+
+ def get_booked_asset_ids : Array(String)
+ asset_ids = Array(String).from_json staff_api.booked(
+ type: @booking_type,
+ period_start: Time.utc.to_unix,
+ period_end: (Time.utc + @time_window_hours.hours).to_unix,
+ zones: @zones,
+ ).get.to_json
+
+ logger.debug { "found #{asset_ids.size} booked assets" }
+
+ self[:booked_assets] = asset_ids
+ rescue error
+ logger.warn(exception: error) { "unable to obtain list of booked assets" }
+ self[:booked_assets] = [] of String
+ end
+
+ @[Security(Level::Support)]
+ def send_email(zone_id : String)
+ if (last = @last_email_sent[zone_id]?) && Time.utc - last < @debounce_time_minutes.minutes
+ logger.debug { "skipping email for #{zone_id} due to debounce timer" }
+ return
+ end
+
+ zone = fetch_zone(zone_id)
+ args = {
+ booking_type: @booking_type,
+ zone_id: zone_id,
+ zone_name: zone.name,
+ zone_description: zone.description,
+ zone_location: zone.location,
+ zone_display_name: zone.display_name,
+ zone_timezone: zone.timezone,
+ }
+
+ begin
+ mailer.send_template(
+ to: @notify_email,
+ template: {"at_capacity", "#{@email_template}#{@template_suffix}"},
+ args: args)
+ @last_email_sent[zone_id] = Time.utc
+ rescue error
+ logger.warn(exception: error) { "failed to send at capacity email for zone #{zone_id}" }
+ end
+ end
+
+ def template_fields : Array(TemplateFields)
+ [
+ TemplateFields.new(
+ trigger: {@email_template, "at_capacity#{@template_suffix}"},
+ name: "At capacity#{@template_fields_suffix}",
+ description: "Notification when the assets of a zone is at capacity",
+ fields: [
+ {name: "booking_type", description: "Type of booking that is at capacity"},
+ {name: "zone_id", description: "Identifier of the zone that is at capacity"},
+ {name: "zone_name", description: "Name of the zone that is at capacity"},
+ {name: "zone_description", description: "Description of the zone that is at capacity"},
+ {name: "zone_location", description: "Location of the zone that is at capacity"},
+ {name: "zone_display_name", description: "Display name of the zone that is at capacity"},
+ {name: "zone_timezone", description: "Timezone of the zone that is at capacity"},
+ ]
+ ),
+ ]
+ end
+
+ def fetch_zone(zone_id : String) : Zone
+ @zone_cache[zone_id] ||= Zone.from_json staff_api.zone(zone_id).get.to_json
+ rescue error
+ logger.warn(exception: error) { "unable to find zone #{zone_id}" }
+ Zone.new(id: zone_id)
+ end
+
+ struct Zone
+ include JSON::Serializable
+
+ property id : String
+
+ property name : String = ""
+ property description : String = ""
+ property tags : Set(String) = Set(String).new
+ property location : String?
+ property display_name : String?
+ property timezone : String?
+
+ property parent_id : String?
+
+ def initialize(@id : String)
+ end
+
+ @[JSON::Field(ignore: true)]
+ @time_location : Time::Location?
+
+ def time_location? : Time::Location?
+ if tz = timezone.presence
+ @time_location ||= Time::Location.load(tz)
+ end
+ end
+
+ def time_location! : Time::Location
+ time_location?.not_nil!
+ end
+ end
+end
diff --git a/drivers/place/at_capacity_mailer_spec.cr b/drivers/place/at_capacity_mailer_spec.cr
new file mode 100644
index 00000000000..83949b20f58
--- /dev/null
+++ b/drivers/place/at_capacity_mailer_spec.cr
@@ -0,0 +1,247 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/mailer"
+
+class StaffAPI < DriverSpecs::MockDriver
+ ZONES = [
+ {
+ created_at: 1660537814,
+ updated_at: 1681800971,
+ id: "level-1",
+ name: "Level 1",
+ display_name: "Level 1",
+ location: "",
+ description: "",
+ code: "",
+ type: "",
+ count: 0,
+ capacity: 0,
+ map_id: "",
+ tags: [
+ "level",
+ ],
+ triggers: [] of String,
+ parent_id: "zone-0000",
+ timezone: "Australia/Sydney",
+ },
+ {
+ created_at: 1660537814,
+ updated_at: 1681800971,
+ id: "level-2",
+ name: "Level 2",
+ display_name: "Level 2",
+ location: "",
+ description: "",
+ code: "",
+ type: "",
+ count: 0,
+ capacity: 0,
+ map_id: "",
+ tags: [
+ "level",
+ ],
+ triggers: [] of String,
+ parent_id: "zone-0000",
+ timezone: "Australia/Sydney",
+ },
+ ]
+
+ def zone(zone_id : String)
+ zones = ZONES.select { |z| z["id"] == zone_id }
+ JSON.parse(zones.to_json)
+ end
+
+ def metadata(id : String, key : String? = nil)
+ zone = ZONES.find! { |z| z["id"] == id }
+ key = key.not_nil!
+
+ details = case key
+ when "desks"
+ [
+ {
+ "id": "desk-1",
+ "name": "Desk 1",
+ "images": [] of String,
+ "bookable": true,
+ "features": [] of String,
+ },
+ {
+ "id": "desk-2",
+ "name": "Desk 2",
+ "images": [] of String,
+ "bookable": true,
+ "features": [] of String,
+ },
+ ]
+ when "parking-spaces"
+ [
+ {
+ "id": "park-1",
+ "name": "Bay 1",
+ "zone": zone[:id],
+ "notes": "",
+ "map_id": "",
+ "zone_id": zone[:id],
+ "assigned_to": nil,
+ "map_rotation": 0,
+ "assigned_name": nil,
+ "assigned_user": nil,
+ },
+ {
+ "id": "park-2",
+ "name": "Bay 2",
+ "zone": zone[:id],
+ "notes": "",
+ "map_id": "",
+ "zone_id": zone[:id],
+ "assigned_to": nil,
+ "map_rotation": 0,
+ "assigned_name": nil,
+ "assigned_user": nil,
+ },
+ ]
+ end
+
+ JSON.parse(
+ {key => {
+ name: key,
+ description: "#{key} for zone #{id}",
+ details: details,
+ parent_id: zone[:parent_id],
+ editors: [] of String,
+ modified_by_id: "user-1234",
+ }}.to_json)
+ end
+
+ def booked(
+ type : String? = nil,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ checked_in : Bool? = nil,
+ include_checked_out : Bool? = nil,
+ include_booked_by : Bool? = nil,
+ department : String? = nil,
+ limit : Int32? = nil,
+ offset : Int32? = nil,
+ permission : String? = nil,
+ extension_data : JSON::Any? = nil,
+ )
+ assets = case type
+ when "desk"
+ ["desk-1", "desk-2"]
+ when "parking"
+ ["park-1"]
+ end
+ JSON.parse(assets.to_json)
+ end
+end
+
+class Mailer < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Mailer
+
+ def on_load
+ self[:sent] = 0
+ end
+
+ def send_template(
+ to : String | Array(String),
+ template : Tuple(String, String),
+ args : TemplateItems,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ )
+ self[:sent] = self[:sent].as_i + 1
+ end
+
+ def send_mail(
+ to : String | Array(String),
+ subject : String,
+ message_plaintext : String? = nil,
+ message_html : String? = nil,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ ) : Bool
+ true
+ end
+end
+
+DriverSpecs.mock_driver "Place::AtCapacityMailer" do
+ system({
+ StaffAPI: {StaffAPI},
+ Mailer: {Mailer},
+ })
+
+ # Start of tests for: #get_booked_asset_ids
+ ###########################################
+
+ settings({
+ booking_type: "parking",
+ zones: ["level-1"],
+ })
+
+ resp = exec(:get_booked_asset_ids).get
+ resp.not_nil!.as_a.should eq ["park-1"]
+
+ ###########################################
+ # End of tests for: #get_booked_asset_ids
+
+ # Start of tests for: #get_asset_ids
+ ####################################
+
+ settings({
+ booking_type: "desk",
+ zones: ["level-1"],
+ })
+
+ resp = exec(:get_asset_ids).get
+ resp.not_nil!.as_h.should eq Hash{"level-1" => ["desk-1", "desk-2"]}
+
+ ####################################
+ # End of tests for: #get_asset_ids
+
+ # Start of tests for: #check_capacity
+ #####################################
+
+ # Not fully booked
+ settings({
+ booking_type: "parking",
+ zones: ["level-1"],
+ })
+ _resp = exec(:get_asset_ids).get # asset_ids are cached
+
+ resp = exec(:check_capacity).get
+ system(:Mailer_1)[:sent].should eq 0
+
+ # Fully booked
+ settings({
+ booking_type: "desk",
+ zones: ["level-1"],
+ })
+ _resp = exec(:get_asset_ids).get # asset_ids are cached
+
+ resp = exec(:check_capacity).get
+ system(:Mailer_1)[:sent].should eq 1
+
+ # spam protection
+ resp = exec(:check_capacity).get
+ system(:Mailer_1)[:sent].should eq 1
+
+ #####################################
+ # End of tests for: #check_capacity
+end
diff --git a/drivers/place/attendee_scanner.cr b/drivers/place/attendee_scanner.cr
new file mode 100644
index 00000000000..48c999461e4
--- /dev/null
+++ b/drivers/place/attendee_scanner.cr
@@ -0,0 +1,193 @@
+require "placeos-driver"
+require "place_calendar"
+
+class Place::AttendeeScanner < PlaceOS::Driver
+ descriptive_name "PlaceOS Attendee scanner"
+ generic_name :AttendeeScanner
+ description %(Scans for attendees that don't have a visitor invite and creates one)
+
+ accessor staff_api : StaffAPI_1
+ accessor locations : LocationServices_1
+
+ default_settings({
+ attendee_scan_every_minutes: 5,
+ _internal_domains: ["comment.out", "use authority / domain email_domains by preference"],
+ })
+
+ def on_update
+ @internal_domains = nil
+ @building_id = nil
+ @timezone = nil
+ @systems = nil
+ @org_id = nil
+
+ period = setting?(Int32, :attendee_scan_every_minutes) || 5
+ schedule.clear
+ schedule.every(period.minutes) { invite_external_guests }
+ end
+
+ getter building_id : String do
+ locations.building_id.get.as_s
+ end
+
+ # Grabs the list of systems in the building
+ getter systems : Hash(String, Array(String)) do
+ staff_api.systems_in_building(building_id).get.as_h.transform_values(&.as_a.map(&.as_s))
+ end
+
+ getter org_id : String do
+ building_details = staff_api.zone(building_id).get
+
+ if tz = building_details["timezone"].as_s?
+ @timezone = Time::Location.load(tz)
+ end
+
+ building_details["parent_id"].as_s
+ end
+
+ protected getter timezone : Time::Location do
+ building_details = staff_api.zone(building_id).get
+ @org_id = building_details["parent_id"].as_s?
+
+ tz = building_details["timezone"]?.try(&.as_s?).presence || config.control_system.try(&.timezone)
+ Time::Location.load(tz.as(String))
+ end
+
+ getter internal_domains : Array(String) do
+ # use authority email_domains so this setting isn't required
+ domains = (setting?(Array(String), :internal_domains) || [] of String).map!(&.strip.downcase)
+ if domains.empty?
+ staff_api.auth_authority.get["email_domains"].as_a?.try(&.map(&.as_s.strip.downcase)) || domains
+ else
+ domains
+ end
+ end
+
+ alias Event = PlaceCalendar::Event
+ alias Attendee = PlaceCalendar::Event::Attendee
+
+ record Guest, zones : Tuple(String, String, String), system_id : String, details : Attendee, event : Event do
+ include JSON::Serializable
+ end
+
+ # extract the list of externals invited to meetings in the building today
+ def externals_in_events
+ building = building_id
+ externals = [] of Guest
+
+ # get the current time
+ now = Time.local(timezone)
+ end_of_day = now.at_end_of_day
+
+ # Find all the guests
+ systems.each do |level_id, system_ids|
+ zones = {org_id, building, level_id}
+
+ system_ids.each do |system_id|
+ sys = system(system_id)
+ if sys.exists?("Bookings", 1)
+ events = sys.get("Bookings", 1).status(Array(Event), :bookings) rescue [] of Event
+ events.each do |event|
+ # all bookings are sorted in this array
+ event_end = event.event_end || end_of_day
+ next if event_end <= now
+ break if event.event_start >= end_of_day
+
+ externals.concat(event.attendees.reject { |attendee|
+ internal_domains.find { |domain| attendee.email.downcase.ends_with? domain }
+ }.map { |attendee|
+ Guest.new(zones, system_id, attendee, event)
+ })
+ end
+ end
+ end
+ end
+
+ externals
+ end
+
+ record Booking, visitor_email : String, booking_start : Time, booking_end : Time do
+ include JSON::Serializable
+ end
+
+ # Find the list of external guests expected in the building today
+ def externals_booked_to_visit
+ building = building_id
+ now = Time.local(timezone)
+ end_of_day = now.at_end_of_day
+
+ staff_api.query_bookings(now.to_unix, end_of_day.to_unix, zones: {building}, type: "visitor").get.as_a.map do |booking|
+ Booking.new(booking["asset_id"].as_s.downcase, Time.unix(booking["booking_start"].as_i64), Time.unix(booking["booking_end"].as_i64))
+ end
+ end
+
+ # invite missing guests
+ def invite_external_guests
+ bookings = externals_booked_to_visit
+ externals = externals_in_events
+ checked = externals.size
+ failed = 0
+
+ logger.debug { "found bookings #{bookings.size} and #{externals.size} externals" }
+
+ externals.reject! do |guest|
+ guest_email = guest.details.email.downcase
+ bookings.find { |booking| booking.visitor_email == guest_email }
+ end
+
+ logger.debug { "found #{externals.size} guests without bookings" }
+
+ now = Time.local(timezone)
+ end_of_day = now.at_end_of_day
+
+ externals.each do |guest|
+ begin
+ event = guest.event
+ host_email = event.host.as(String).downcase
+ host = guest.event.attendees.find! { |attend| attend.email.downcase == host_email }
+ guest_email = guest.details.email.downcase
+ guest_name = guest.details.name
+
+ sys_info = staff_api.get_system(guest.system_id).get
+
+ staff_api.create_booking(
+ booking_type: "visitor",
+ asset_id: guest_email,
+ user_id: host_email,
+ user_email: host_email,
+ user_name: host.name,
+ zones: guest.zones,
+ booking_start: event.event_start.to_unix,
+ booking_end: event.event_end.try(&.to_unix) || end_of_day.to_unix,
+ checked_in: false,
+ approved: true,
+ title: guest_name,
+ description: event.title,
+ time_zone: timezone.name,
+ extension_data: {
+ name: guest_name,
+ parent_id: event.id,
+ location_id: sys_info["name"].as_s,
+ },
+ utm_source: "attendee_scanner",
+ limit_override: 999,
+ event_id: event.id,
+ ical_uid: event.ical_uid,
+ attendees: [{
+ name: guest_name,
+ email: guest_email,
+ }]
+ ).get
+ rescue error
+ failed += 1
+ logger.warn(exception: error) { "failed to invite guest: #{guest.details.email}" }
+ end
+ end
+
+ {
+ invited: externals.size - failed,
+ checked: checked,
+ failure: failed,
+ }
+ end
+end
diff --git a/drivers/place/attendee_scanner_spec.cr b/drivers/place/attendee_scanner_spec.cr
new file mode 100644
index 00000000000..c1a7ea3600d
--- /dev/null
+++ b/drivers/place/attendee_scanner_spec.cr
@@ -0,0 +1,157 @@
+require "placeos-driver/spec"
+
+# :nodoc:
+class LocationServices < DriverSpecs::MockDriver
+ def on_load
+ self[:building_id_requested] = false
+ end
+
+ def building_id
+ self[:building_id_requested] = true
+ "zone-building"
+ end
+end
+
+# :nodoc:
+class StaffAPI < DriverSpecs::MockDriver
+ def zone(zone_id : String)
+ raise "unexpected zone requested #{zone_id}" unless zone_id == "zone-building"
+
+ {
+ id: "zone-building",
+ timezone: "Australia/Sydney",
+ parent_id: "zone-org",
+ }
+ end
+
+ def systems_in_building(zone_id : String, ids_only : Bool = true)
+ self[:systems_requested] = zone_id
+ {
+ "zone-level1": [
+ "spec_runner_system",
+ ],
+ }
+ end
+
+ def get_system(id : String, complete : Bool = false)
+ raise "unexpected system requested #{id}" unless id == "spec_runner_system"
+
+ {
+ name: "Test Room 1",
+ }
+ end
+
+ def query_bookings(
+ type : String? = nil,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ rejected : Bool? = nil,
+ checked_in : Bool? = nil,
+ include_checked_out : Bool? = nil,
+ extension_data : JSON::Any? = nil
+ )
+ [] of Nil
+ end
+
+ def create_booking(
+ booking_type : String,
+ asset_id : String,
+ user_id : String,
+ user_email : String,
+ user_name : String,
+ zones : Array(String),
+ booking_start : Int64? = nil,
+ booking_end : Int64? = nil,
+ checked_in : Bool = false,
+ approved : Bool? = nil,
+ title : String? = nil,
+ description : String? = nil,
+ time_zone : String? = nil,
+ extension_data : JSON::Any? = nil,
+ utm_source : String? = nil,
+ limit_override : Int64? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ attendees : Array(JSON::Any)? = nil
+ )
+ true
+ end
+end
+
+# :nodoc:
+class Bookings < DriverSpecs::MockDriver
+ def on_load
+ self[:bookings] = [{
+ "event_start": 1.hour.ago.to_unix,
+ "event_end": 1.hour.from_now.to_unix,
+ "id": "AAkALgAAAAAAHYQDEapmEc2byACqAC-EWg0AVrOjSWJ0R0_lv6HqEl72fQABnPXAjwAA",
+ "host": "IsaiahL@email.com",
+ "title": "Test Meeting",
+ "body": "\r\n\r\n\r\n\r\n\r\n
\r\n\r\n\r\n",
+ "attendees": [
+ {
+ "name": "Isaiah Langer",
+ "email": "isaiahl@email.com",
+ "response_status": "needsAction",
+ "resource": false,
+ },
+ {
+ "name": "steve@vontaka.ch",
+ "email": "steve@vontaka.ch",
+ "response_status": "needsAction",
+ "resource": false,
+ },
+ {
+ "name": "Test Room 1",
+ "email": "testroom1@email.com",
+ "response_status": "accepted",
+ "resource": true,
+ },
+ ],
+ "hide_attendees": false,
+ "location": "Test Room 1",
+ "private": false,
+ "all_day": false,
+ "timezone": "Australia/Sydney",
+ "recurring": false,
+ "created": "2024-12-03T08:59:00Z",
+ "updated": "2024-12-03T08:59:56Z",
+ "attachments": [] of Nil,
+ "status": "confirmed",
+ "creator": "IsaiahL@email.com",
+ "ical_uid": "040000008200E00074C5B7101A82E00800000000B5C273946145DB01000000000000000010000000651007D546B31E4EB651ED0F73A0CDB6",
+ "online_meeting_provider": "teamsForBusiness",
+ "online_meeting_phones": [] of Nil,
+ "online_meeting_url": "https://teams.microsoft.com/l/meetup-join/19%3ameeting_ZjRkMTM2ZTYtZGIxNi00NDFkLWI5NGYtNDA3Mjg1NDg0YzA2%40thread.v2/0?context=%7b%22Tid%22%3a%22bc9d5ad8-7518-422b-ac8d-b69429ca4cb9%22%2c%22Oid%22%3a%22905b5cbc-ac57-4159-98a7-9b9d8e%22%7d",
+ "mailbox": "testroom1@email.com",
+ }]
+ end
+end
+
+DriverSpecs.mock_driver "Place::AttendeeScanner" do
+ settings({
+ internal_domains: ["email.com"],
+ })
+
+ system({
+ StaffAPI: {StaffAPI},
+ LocationServices: {LocationServices},
+ Bookings: {Bookings},
+ })
+
+ resp = exec(:invite_external_guests).get
+ resp.should eq({
+ "invited" => 1,
+ "checked" => 1,
+ "failure" => 0,
+ })
+end
diff --git a/drivers/place/auto_release.cr b/drivers/place/auto_release.cr
new file mode 100644
index 00000000000..d80f0cd796c
--- /dev/null
+++ b/drivers/place/auto_release.cr
@@ -0,0 +1,563 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+require "place_calendar"
+require "./booking_model"
+require "./bookings/asset_name_resolver"
+
+class Place::AutoRelease < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+ include Place::AssetNameResolver
+
+ descriptive_name "PlaceOS Auto Release"
+ generic_name :AutoRelease
+ description %(emails visitors to confirm automatic release of their booking when they have indicated they are not on-site and releases the booking if they do not confirm)
+
+ default_settings({
+ date_time_format: "%c",
+ time_format: "%l:%M%p",
+ date_format: "%A, %-d %B",
+ email_schedule: "*/5 * * * *",
+ email_template: "auto_release",
+ unique_templates: false,
+ time_window_hours: 4, # The number of hours to check for bookings pending release
+ release_locations: ["wfh", "aol"], # Locations to release bookings for
+ # available locations:
+ # - wfh: Work From Home
+ # - aol: Away on Leave
+ # - wfo: Work From Office
+ skip_created_after_start: true, # Skip bookings created after the start time
+ skip_same_day: false, # Skip bookings created on the same day as the booking
+ skip_all_day: false, # Skip all day bookings
+ asset_cache_timeout: 3600_i64, # 1 hour
+ })
+
+ accessor staff_api : StaffAPI_1
+
+ getter building_zone : Zone { get_building_zone?.not_nil! }
+
+ # used by AssetNameResolver and LockerMetadataParser
+ getter building_id : String { building_zone.id }
+ getter levels : Array(String) do
+ staff_api.systems_in_building(building_id).get.as_h.keys
+ end
+
+ protected getter timezone : Time::Location do
+ tz = config.control_system.try(&.timezone) || building_zone.timezone.presence || "UTC"
+ Time::Location.load(tz)
+ end
+
+ def mailer
+ system.implementing(Interface::Mailer)[0]
+ end
+
+ @date_time_format : String = "%c"
+ @time_format : String = "%l:%M%p"
+ @date_format : String = "%A, %-d %B"
+
+ @auto_release_emails_sent : UInt64 = 0_u64
+ @auto_release_email_errors : UInt64 = 0_u64
+
+ @email_template : String = "auto_release"
+ @unique_templates : Bool = false
+ @email_schedule : String? = nil
+
+ @time_window_hours : Int32 = 1
+ @release_locations : Array(String) = ["wfh", "aol"]
+ @auto_release : AutoReleaseConfig = AutoReleaseConfig.new
+ @skip_created_after_start : Bool = true
+ @skip_same_day : Bool = true
+ @skip_all_day : Bool = false
+
+ def on_update
+ @building_zone = nil
+ @building_id = nil
+ @levels = nil
+ @timezone = nil
+
+ @email_schedule = setting?(String, :email_schedule).presence
+ @email_template = setting?(String, :email_template) || "auto_release"
+ @unique_templates = setting?(Bool, :unique_templates) || false
+
+ @date_time_format = setting?(String, :date_time_format) || "%c"
+ @time_format = setting?(String, :time_format) || "%l:%M%p"
+ @date_format = setting?(String, :date_format) || "%A, %-d %B"
+
+ @time_window_hours = setting?(Int32, :time_window_hours) || 1
+ @release_locations = setting?(Array(String), :release_locations) || ["wfh", "aol"]
+ @auto_release = setting?(AutoReleaseConfig, :auto_release) || AutoReleaseConfig.new
+ @skip_created_after_start = setting?(Bool, :skip_created_after_start).nil? || setting(Bool, :skip_created_after_start)
+ @skip_same_day = setting?(Bool, :skip_same_day) || false
+ @skip_all_day = setting?(Bool, :skip_all_day) || false
+
+ @asset_cache_timeout = setting?(Int64, :asset_cache_timeout) || 3600_i64
+ clear_asset_cache
+
+ schedule.clear
+
+ # find bookins pending release
+ schedule.every(5.minutes) { pending_release }
+
+ # release bookings
+ schedule.every(1.minute) { release_bookings }
+
+ if emails = @email_schedule
+ schedule.cron(emails, timezone) { send_release_emails }
+ end
+ end
+
+ # Explain why a booking was released or not released
+ @[Security(Level::Support)]
+ def explain_state
+ pending_bookings = self[:pending_bookings]? ? Array(Booking).from_json(self[:pending_bookings].to_json) : [] of Booking
+ pending_release = self[:pending_release]? ? Array(Booking).from_json(self[:pending_release].to_json) : [] of Booking
+ emailed_booking_ids = self[:emailed_booking_ids]? ? Array(Int64).from_json(self[:emailed_booking_ids].to_json) : [] of Int64
+ released_booking_ids = self[:released_booking_ids]? ? Array(Int64).from_json(self[:released_booking_ids].to_json) : [] of Int64
+
+ counters = {:bookings => pending_bookings.size}
+ counters[:pending_release] = pending_release.size
+ counters[:emails_sent] = emailed_booking_ids.size
+ counters[:released] = released_booking_ids.size
+
+ bookings = Hash(Int64, Array(String)).new
+
+ # Add booking information details
+ pending_bookings.each do |booking|
+ bookings[booking.id] ||= Array(String).new
+ bookings[booking.id] << "checked_in: #{booking.checked_in}, booking_start: #{booking.booking_start}, booking_type: #{booking.booking_type}, all_day: #{booking.all_day}, user_id: #{booking.user_id}, asset_ids: #{booking.asset_ids}"
+ end
+
+ # Add reasons from explain_pending_release
+ explain_pending_release = self[:explain_pending_release]? ? Hash(Int64, String).from_json(self[:explain_pending_release].to_json) : Hash(Int64, String).new
+ explain_pending_release.each do |booking_id, reason|
+ bookings[booking_id] ||= Array(String).new
+ bookings[booking_id] << reason
+ end
+
+ # Add reasons from explain_release_bookings
+ explain_release_bookings = self[:explain_release_bookings]? ? Hash(Int64, String).from_json(self[:explain_release_bookings].to_json) : Hash(Int64, String).new
+ explain_release_bookings.each do |booking_id, reason|
+ bookings[booking_id] ||= Array(String).new
+ bookings[booking_id] << reason
+ end
+
+ {enabled: enabled?, counters: counters, bookings: bookings}
+ end
+
+ # Finds the building zone for the current location services object
+ def get_building_zone? : Zone?
+ zones = Array(Zone).from_json staff_api.zones(tags: "building").get.to_json
+ zone_ids = zones.map(&.id)
+ zone_id = (zone_ids & system.zones).first
+ zones.find { |zone| zone.id == zone_id }
+ rescue error
+ logger.error(exception: error) { "unable to determine building zone" }
+ nil
+ end
+
+ @[Security(Level::Support)]
+ def enabled? : Bool
+ if !@auto_release.resources.empty? &&
+ !building_zone.time_location?.nil?
+ true
+ else
+ logger.notice { "auto release is not enabled on zone #{building_zone.id}" }
+ logger.debug { "auto release is not enabled on zone #{building_zone.id} due to auto_release.resources being empty" } if @auto_release.resources.empty?
+ logger.debug { "auto release is not enabled on zone #{building_zone.id} due to building_zone.time_location being nil" } if building_zone.time_location?.nil?
+ false
+ end
+ end
+
+ @[Security(Level::Support)]
+ def get_pending_bookings : Array(Booking)
+ results = [] of Booking
+
+ @auto_release.resources.each do |type|
+ bookings = Array(Booking).from_json staff_api.query_bookings(
+ type: type,
+ period_start: Time.utc.to_unix,
+ period_end: (Time.utc + @time_window_hours.hours).to_unix,
+ zones: [building_zone.id],
+ ).get.to_json
+ results += bookings.select { |booking| !booking.checked_in }
+ end
+
+ logger.debug { "found #{results.size} pending bookings" }
+
+ self[:pending_bookings] = results
+ rescue error
+ logger.error(exception: error) { "unable to obtain list of bookings" }
+ self[:pending_bookings] = [] of Booking
+ end
+
+ @[Security(Level::Support)]
+ def get_user_preferences?(user_id : String)
+ user = User.from_json staff_api.user(user_id).get.to_json
+
+ work_preferences = user.work_preferences
+ work_preferences = @auto_release.default_work_preferences if work_preferences.empty?
+
+ {work_preferences: work_preferences, work_overrides: user.work_overrides}
+ rescue
+ logger.debug { "unable to obtain work location for user #{user_id}" }
+ nil
+ end
+
+ @[Security(Level::Support)]
+ def get_user_preferences(user_id : String)
+ get_user_preferences?(user_id) || {work_preferences: @auto_release.default_work_preferences, work_overrides: Hash(String, WorktimePreference).new}
+ end
+
+ def in_preference_hours?(start_time : Float64, end_time : Float64, event_time : Float64) : Bool
+ if start_time < end_time
+ start_time < event_time && end_time > event_time
+ else
+ start_time < event_time || end_time > event_time
+ end
+ end
+
+ def in_preference?(preference : WorktimePreference, event_time : Float64, locations : Array(String), match_locations : Bool = true) : Bool
+ if match_locations
+ preference.blocks.any? do |block|
+ in_preference_hours?(block.start_time, block.end_time, event_time) &&
+ locations.includes? block.location
+ end
+ else
+ preference.blocks.any? do |block|
+ in_preference_hours?(block.start_time, block.end_time, event_time) &&
+ !locations.includes?(block.location)
+ end
+ end
+ end
+
+ @[Security(Level::Support)]
+ def pending_release
+ results = [] of Booking
+ return results unless enabled?
+
+ explain = Hash(Int64, String).new
+
+ bookings = get_pending_bookings
+
+ bookings.each do |booking|
+ if @skip_created_after_start && (created_at = booking.created) && created_at >= booking.booking_start
+ explain[booking.id] = "skipped due to created after start time"
+ next
+ end
+ if @skip_same_day && (created_at = booking.created) &&
+ Time.unix(created_at).in(building_zone.time_location!).day == Time.unix(booking.booking_start).in(building_zone.time_location!).day
+ explain[booking.id] = "skipped due to same day booking"
+ next
+ end
+ if @skip_all_day && booking.all_day
+ explain[booking.id] = "skipped due to all day booking"
+ next
+ end
+
+ preferences = get_user_preferences(booking.user_id)
+
+ # get the booking start time in the building timezone
+ booking_start = Time.unix(booking.booking_start).in building_zone.time_location!
+
+ day_of_week = booking_start.day_of_week.value
+ day_of_week = 0 if day_of_week == 7 # Crystal uses 7 for Sunday, but we use 0 (all other days match up)
+
+ # convert unix timestamp to float hours/minutes
+ # e.g. 7:30AM = 7.5
+ event_time = booking_start.hour + (booking_start.minute / 60.0)
+
+ # use all_day_start for all day bookings
+ event_time = @auto_release.all_day_start if booking.all_day
+
+ # exclude overrides with empty time blocks
+ overrides = preferences[:work_overrides].select { |_, pref| pref.blocks.size > 0 }
+
+ if (override = overrides[booking_start.to_s(format: "%F")]?) &&
+ in_preference?(override, event_time, @release_locations)
+ explain[booking.id] = "pending release due to override matching time and location"
+ results << booking
+ elsif (override = overrides[booking_start.to_s(format: "%F")]?) &&
+ in_preference?(override, event_time, @release_locations, false)
+ explain[booking.id] = "skipped due to override matching time but not location"
+ elsif (preference = preferences[:work_preferences].find { |pref| pref.day_of_week == day_of_week }) &&
+ in_preference?(preference, event_time, @release_locations)
+ explain[booking.id] = "pending release due to matching time and location"
+ results << booking
+ elsif (preference = preferences[:work_preferences].find { |pref| pref.day_of_week == day_of_week }) &&
+ in_preference?(preference, event_time, @release_locations, false)
+ explain[booking.id] = "skipped due to matching time but not location"
+ elsif @auto_release.release_outside_hours
+ explain[booking.id] = "pending release due to outside work hours"
+ results << booking
+ end
+ end
+
+ logger.debug { "found #{results.size} bookings pending release" }
+
+ self[:explain_pending_release] = explain
+ self[:pending_release] = results
+ end
+
+ def skip_release?(cached_booking : Booking) : Bool
+ if (booking_json_any = staff_api.get_booking(cached_booking.id).get) &&
+ (booking = Booking.from_json(booking_json_any.to_json))
+ booking.checked_in || booking.booking_start != cached_booking.booking_start
+ else
+ true
+ end
+ end
+
+ def release_bookings
+ released_booking_ids = [] of Int64
+ return released_booking_ids unless enabled?
+
+ bookings = self[:pending_release]? ? Array(Booking).from_json(self[:pending_release].to_json) : [] of Booking
+
+ previously_released = self[:released_booking_ids]? ? Array(Int64).from_json(self[:released_booking_ids].to_json) : [] of Int64
+ # remove previously released bookings that are no longer pending release
+ previously_released -= previously_released - bookings.map(&.id)
+ # add previously released bookings that are still pending release
+ released_booking_ids += previously_released
+
+ previously_explained = self[:explain_release_bookings]? ? Hash(Int64, String).from_json(self[:explain_release_bookings].to_json) : Hash(Int64, String).new
+ explain = previously_explained.select { |key, _| released_booking_ids.includes?(key) }
+
+ bookings.each do |booking|
+ next if previously_released.includes? booking.id
+
+ # get the booking start time in the building timezone
+ booking_start = Time.unix(booking.booking_start).in building_zone.time_location!
+
+ # convert hours (all_day_start) to seconds
+ booking_start = booking.all_day ? all_day_start_time(booking_start).to_unix : booking.booking_start
+
+ # convert minutes (time_after) to seconds for comparison with unix timestamps (booking_start)
+ if Time.utc.to_unix - booking_start > @auto_release.time_after(booking.booking_type) * 60
+ # skip if there's been changes to the cached bookings checked_in status or booking_start time
+ if skip_release?(booking)
+ explain[booking.id] = "skip release due to changes to checked_in status or booking_start time"
+ next
+ end
+
+ explain[booking.id] = "rejecting booking as it is within the time_after window"
+ logger.debug { "rejecting booking #{booking.id} as it is within the time_after window" }
+ staff_api.reject(booking.id, "auto_release", booking.instance).get
+ released_booking_ids << booking.id
+ end
+ end
+
+ logger.debug { "released #{released_booking_ids.size} bookings" }
+
+ self[:explain_release_bookings] = explain
+ self[:released_booking_ids] = released_booking_ids
+ rescue error
+ logger.error(exception: error) { "unable to release bookings" }
+ self[:released_booking_ids] = [] of Int64
+ end
+
+ private def all_day_start_time(booking_start : Time) : Time
+ # Convert float hours/minutes to time
+ # e.g. 7.5 = 7:30AM in the specified timezone
+ hours = @auto_release.all_day_start.to_i
+ minutes = ((@auto_release.all_day_start - hours) * 60).to_i
+ time_in_zone = Time.local(booking_start.year, booking_start.month, booking_start.day, hours, minutes, location: building_zone.time_location!)
+ end
+
+ @[Security(Level::Support)]
+ def send_release_emails
+ emailed_booking_ids = [] of Int64
+ bookings = self[:pending_release]? ? Array(Booking).from_json(self[:pending_release].to_json) : [] of Booking
+ previously_released = self[:released_booking_ids]? ? Array(Int64).from_json(self[:released_booking_ids].to_json) : [] of Int64
+
+ previously_emailed = self[:emailed_booking_ids]? ? Array(Int64).from_json(self[:emailed_booking_ids].to_json) : [] of Int64
+ # remove previously emailed bookings that are no longer pending release
+ previously_emailed -= previously_emailed - bookings.map(&.id)
+ # add previously emailed bookings that are still pending release
+ emailed_booking_ids += previously_emailed
+
+ bookings.each do |booking|
+ next if previously_released.includes? booking.id
+ next if previously_emailed.includes? booking.id
+
+ # convert minutes (time_after) to seconds for comparison with unix timestamps (booking_start)
+ if enabled? &&
+ (booking.booking_start - Time.utc.to_unix < @auto_release.time_before(booking.booking_type) * 60) &&
+ (Time.utc.to_unix - booking.booking_start < @auto_release.time_after(booking.booking_type) * 60)
+ logger.debug { "sending release email to #{booking.user_email} for booking #{booking.id} as it is withing the time_before window" }
+
+ location = Time::Location.load(booking.timezone.presence || timezone.name)
+ starting = Time.unix(booking.booking_start).in(location)
+ ending = Time.unix(booking.booking_end).in(location)
+
+ args = {
+ booking_id: booking.id,
+ booking_start: booking.booking_start,
+ booking_end: booking.booking_end,
+
+ start_time: starting.to_s(@time_format),
+ start_date: starting.to_s(@date_format),
+ start_datetime: starting.to_s(@date_time_format),
+ end_time: ending.to_s(@time_format),
+ end_date: ending.to_s(@date_format),
+ end_datetime: ending.to_s(@date_time_format),
+
+ asset_id: booking.asset_id,
+ asset_name: lookup_asset(asset_id: booking.asset_id, type: booking.booking_type, zones: booking.zones),
+ user_id: booking.user_id,
+ user_email: booking.user_email,
+ user_name: booking.user_name,
+ reason: booking.title,
+
+ approver_name: booking.approver_name,
+ approver_email: booking.approver_email,
+
+ booked_by_name: booking.booked_by_name,
+ booked_by_email: booking.booked_by_email,
+ }
+
+ begin
+ mailer.send_template(
+ to: booking.user_email,
+ template: {@email_template, "auto_release#{template_suffix(booking.booking_type)}"},
+ args: args)
+ emailed_booking_ids << booking.id
+ rescue error
+ logger.warn(exception: error) { "failed to send release email to #{booking.user_email}" }
+ end
+ end
+ end
+ self[:emailed_booking_ids] = emailed_booking_ids
+ end
+
+ def template_fields : Array(TemplateFields)
+ if @unique_templates && !@auto_release.resources.empty?
+ @auto_release.resources.map { |type| unique_template_fields(type) }
+ else
+ [unique_template_fields]
+ end
+ end
+
+ private def unique_template_fields(booking_type : String = "") : TemplateFields
+ time_now = Time.utc.in(timezone)
+
+ TemplateFields.new(
+ trigger: {@email_template, "auto_release#{template_suffix(booking_type)}"},
+ name: "Auto release booking#{template_fields_suffix(booking_type)}",
+ description: "Notification when a booking is pending automatic release due to user's work location preferences",
+ fields: [
+ {name: "booking_id", description: "Unique identifier for the booking that may be released"},
+ {name: "booking_start", description: "Unix timestamp of when the booking begins"},
+ {name: "booking_end", description: "Unix timestamp of when the booking ends"},
+ {name: "start_time", description: "Formatted start time (e.g., #{time_now.to_s(@time_format)})"},
+ {name: "start_date", description: "Formatted start date (e.g., #{time_now.to_s(@date_format)})"},
+ {name: "start_datetime", description: "Formatted start date and time (e.g., #{time_now.to_s(@date_time_format)})"},
+ {name: "end_time", description: "Formatted end time (e.g., #{time_now.to_s(@time_format)})"},
+ {name: "end_date", description: "Formatted end date (e.g., #{time_now.to_s(@date_format)})"},
+ {name: "end_datetime", description: "Formatted end date and time (e.g., #{time_now.to_s(@date_time_format)})"},
+ {name: "asset_id", description: "Identifier of the booked resource"},
+ {name: "asset_name", description: "Name of the booked resource"},
+ {name: "user_id", description: "Identifier of the person who has the booking"},
+ {name: "user_email", description: "Email address of the person who has the booking"},
+ {name: "user_name", description: "Full name of the person who has the booking"},
+ {name: "reason", description: "Title or purpose of the booking"},
+ {name: "approver_name", description: "Name of the person who approved the booking"},
+ {name: "approver_email", description: "Email of the person who approved the booking"},
+ {name: "booked_by_name", description: "Name of the person who made the booking"},
+ {name: "booked_by_email", description: "Email of the person who made the booking"},
+ ]
+ )
+ end
+
+ private def template_suffix(booking_type : String) : String
+ @unique_templates && !@auto_release.resources.empty? ? "_#{booking_type}" : ""
+ end
+
+ private def template_fields_suffix(booking_type : String) : String
+ @unique_templates && !@auto_release.resources.empty? ? " (#{booking_type})" : ""
+ end
+
+ struct AutoReleaseConfig
+ include JSON::Serializable
+ include JSON::Serializable::Unmapped
+
+ getter time_before : Int64 = 0 # Notification time before booking start in minutes
+ getter time_after : Int64 = 0 # Release time after booking start in minutes
+ getter resources : Array(String) = [] of String # Resources to release bookings for
+ getter default_work_preferences : Array(WorktimePreference) = [] of WorktimePreference # Default work preferences for users
+ getter release_outside_hours : Bool = false # Release bookings outside of work hours
+ getter all_day_start : Float64 = 8.0 # Start time used for all day bookings
+
+ def initialize
+ end
+
+ def time_before(resource : String) : Int64
+ if resource_time_before = json_unmapped["#{resource}_time_before"]?
+ resource_time_before.as_i64
+ else
+ time_before
+ end
+ end
+
+ def time_after(resource : String) : Int64
+ if resource_time_after = json_unmapped["#{resource}_time_after"]?
+ resource_time_after.as_i64
+ else
+ time_after
+ end
+ end
+ end
+
+ record User,
+ id : String,
+ work_preferences : Array(WorktimePreference) = [] of WorktimePreference,
+ work_overrides : Hash(String, WorktimePreference) = Hash(String, WorktimePreference).new do
+ include JSON::Serializable
+ end
+
+ # start_time: Start time of work hours. e.g. `7.5` being 7:30AM
+ # end_time: End time of work hours. e.g. `18.5` being 6:30PM
+ # location: Name of the location the work is being performed at
+ struct WorktimeBlock
+ include JSON::Serializable
+
+ property start_time : Float64
+ property end_time : Float64
+ property location : String = ""
+ end
+
+ # day_of_week: Index of the day of the week. `0` being Sunday
+ struct WorktimePreference
+ include JSON::Serializable
+
+ property day_of_week : Int32
+ property blocks : Array(WorktimeBlock) = [] of WorktimeBlock
+ end
+
+ struct Zone
+ include JSON::Serializable
+
+ property id : String
+
+ property name : String
+ property description : String
+ property tags : Set(String)
+ property location : String?
+ property display_name : String?
+ property timezone : String?
+
+ property parent_id : String?
+
+ @[JSON::Field(ignore: true)]
+ @time_location : Time::Location?
+
+ def time_location? : Time::Location?
+ if tz = timezone.presence
+ @time_location ||= Time::Location.load(tz)
+ end
+ end
+
+ def time_location! : Time::Location
+ time_location?.not_nil!
+ end
+ end
+end
diff --git a/drivers/place/auto_release_locker.cr b/drivers/place/auto_release_locker.cr
new file mode 100644
index 00000000000..066541dd95e
--- /dev/null
+++ b/drivers/place/auto_release_locker.cr
@@ -0,0 +1,86 @@
+require "placeos-driver"
+require "./booking_model"
+
+class Place::AutoReleaseLocker < PlaceOS::Driver
+ descriptive_name "PlaceOS Auto Release Locker"
+ generic_name :AutoReleaseLocker
+ description %(automatic release locker on specified interval)
+
+ default_settings({
+ booking_type: "locker",
+ release_schedule: "0 23 * * 5",
+ time_window_hours: 1,
+ })
+
+ accessor staff_api : StaffAPI_1
+
+ @booking_type : String = "locker"
+ @release_schedule : String = "0 23 * * 5"
+ @time_window_hours : Int32 = 1
+
+ def on_update
+ @timezone = nil
+ @building_id = nil
+ @booking_type = setting?(String, :booking_type).presence || "locker"
+ @time_window_hours = setting?(Int32, :time_window_hours) || 1
+ @release_schedule = setting(String, :release_schedule)
+
+ schedule.clear
+ schedule_cron
+ end
+
+ protected def schedule_cron : Nil
+ schedule.cron(@release_schedule, timezone) { release_lockers }
+ rescue error
+ logger.warn(exception: error) { "failed to schedule cron job" }
+ schedule.in(1.minute) { schedule_cron }
+ end
+
+ # Finds the building ID for the current location services object
+ getter building_id : String do
+ zone_ids = staff_api.zones(tags: "building").get.as_a.map(&.[]("id").as_s)
+ (zone_ids & system.zones).first
+ rescue error
+ logger.warn(exception: error) { "unable to determine building zone id" }
+ raise error
+ end
+
+ protected getter timezone : Time::Location do
+ tz = config.control_system.try(&.timezone) || staff_api.zone(building_id).get["timezone"].as_s
+ Time::Location.load(tz)
+ end
+
+ def get_bookings : Array(Booking)
+ bookings = Array(Booking).from_json staff_api.query_bookings(
+ type: @booking_type,
+ period_start: Time.utc.to_unix,
+ period_end: (Time.utc + @time_window_hours.hours).to_unix,
+ zones: [building_id],
+ ).get.to_json
+ logger.debug { "found #{bookings.size} #{@booking_type} bookings" }
+
+ bookings
+ rescue error
+ logger.warn(exception: error) { "unable to obtain list of #{@booking_type} bookings" }
+ [] of Booking
+ end
+
+ @[Security(Level::Support)]
+ def release_lockers
+ bookings = get_bookings
+ released = 0
+ bookings.each do |booking|
+ logger.debug { "releasing booking #{booking.id} as it is within the time_after window" }
+ begin
+ staff_api.update_booking(booking.id, recurrence_end: booking.booking_end).get if booking.instance
+ staff_api.booking_check_in(booking.id, false, "auto-release", instance: booking.instance).get
+ released += 1
+ rescue error
+ logger.warn(exception: error) { "unable to release #{@booking_type} with booking id #{booking.id} (inst: #{booking.instance})" }
+ end
+ end
+ results = {total: bookings.size, released: released}
+ logger.debug { results.inspect }
+ results
+ end
+end
diff --git a/drivers/place/auto_release_locker_spec.cr b/drivers/place/auto_release_locker_spec.cr
new file mode 100644
index 00000000000..51463fdbfe0
--- /dev/null
+++ b/drivers/place/auto_release_locker_spec.cr
@@ -0,0 +1,181 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::BookingCheckInHelper" do
+ system({
+ StaffAPI: {StaffAPIMock},
+ })
+ resp = exec(:get_bookings).get
+ resp.should_not be_nil
+ resp.not_nil!.as_a.size.should eq 4
+ resp = exec(:release_lockers).get
+ resp.not_nil!.as_h["total"].should eq 4
+ resp.not_nil!.as_h["released"].should eq 4
+end
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ BOOKINGS = [
+ {
+ id: 1,
+ user_id: "user-one",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "locker_001",
+ zones: ["zone-1234"],
+ booking_type: "locker",
+ booking_start: (Time.utc - 10.hour).to_unix,
+ booking_end: (Time.utc + 5.hours).to_unix,
+ timezone: "Australia/Darwin",
+ title: "ignore",
+ description: "",
+ checked_in: true,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-one",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: Time.utc.to_unix,
+ created: Time.utc.to_unix,
+ },
+ {
+ id: 2,
+ user_id: "user-one",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "locker_002",
+ zones: ["zone-1234"],
+ booking_type: "locker",
+ booking_start: (Time.utc - 5.minutes).to_unix,
+ booking_end: (Time.utc + 1.hour).to_unix,
+ timezone: "Australia/Darwin",
+ title: "notify",
+ description: "",
+ checked_in: true,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-one",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: Time.utc.to_unix,
+ created: Time.utc.to_unix,
+ },
+ {
+ id: 3,
+ user_id: "user-one",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "locker_003",
+ zones: ["zone-1234"],
+ booking_type: "locker",
+ booking_start: (Time.utc - 11.minutes).to_unix,
+ booking_end: (Time.utc + 1.hour).to_unix,
+ timezone: "Australia/Darwin",
+ title: "reject",
+ description: "",
+ checked_in: true,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-one",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: Time.utc.to_unix,
+ created: Time.utc.to_unix,
+ },
+ {
+ id: 4,
+ user_id: "user-one",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "locker_004",
+ zones: ["zone-1234"],
+ booking_type: "locker",
+ booking_start: (Time.utc - 5.hours).to_unix,
+ booking_end: (Time.utc + 1.hours).to_unix,
+ timezone: "Australia/Darwin",
+ title: "ignore_after_hours",
+ description: "",
+ checked_in: true,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-one",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: Time.utc.to_unix,
+ created: Time.utc.to_unix,
+ },
+ ]
+
+ def query_bookings(
+ type : String,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ rejected : Bool? = nil,
+ checked_in : Bool? = nil
+ )
+ BOOKINGS
+ end
+
+ def zones(q : String? = nil,
+ limit : Int32 = 1000,
+ offset : Int32 = 0,
+ parent : String? = nil,
+ tags : Array(String) | String? = nil)
+ zones = [
+ {
+ created_at: 1660537814,
+ updated_at: 1681800971,
+ id: "zone-1234",
+ name: "Test Zone",
+ display_name: "Test Zone",
+ location: "",
+ description: "",
+ code: "",
+ type: "",
+ count: 0,
+ capacity: 0,
+ map_id: "",
+ tags: [
+ "building",
+ ],
+ triggers: [] of String,
+ parent_id: "zone-0000",
+ timezone: "Australia/Sydney",
+ },
+ ]
+
+ zones
+ end
+
+ def update_booking(
+ booking_id : String | Int64,
+ booking_start : Int64? = nil,
+ booking_end : Int64? = nil,
+ asset_id : String? = nil,
+ title : String? = nil,
+ description : String? = nil,
+ timezone : String? = nil,
+ extension_data : JSON::Any? = nil,
+ approved : Bool? = nil,
+ checked_in : Bool? = nil,
+ limit_override : Int64? = nil,
+ instance : Int64? = nil,
+ recurrence_end : Int64? = nil,
+ )
+ true
+ end
+
+ def booking_check_in(booking_id : String | Int64, state : Bool = true, utm_source : String? = nil, instance : Int64? = nil)
+ true
+ end
+end
diff --git a/drivers/place/auto_release_readme.md b/drivers/place/auto_release_readme.md
new file mode 100644
index 00000000000..d1b499c5ddb
--- /dev/null
+++ b/drivers/place/auto_release_readme.md
@@ -0,0 +1,266 @@
+# Auto Release Readme
+
+Docs on how to configure the Auto Release driver.
+This driver automatically releases bookings when users have indicated they are not on-site (work from home or away on leave) and haven't checked in to their booking.
+
+* The driver monitors bookings for configured resource types (e.g., desks)
+* Checks user work location preferences and overrides against release locations
+* Sends notification emails to users before automatically releasing their bookings
+* Releases bookings after a configurable time period if users don't confirm attendance
+
+
+## Requirements
+
+Requires the following drivers in the system:
+
+* StaffAPI - for querying bookings and user preferences
+* Mailer - for sending notification emails, this also will be where the templates are configured
+
+**CRITICAL:** The building zone must have its timezone configured. The Auto Release driver always operates using the building's timezone for all time-based calculations and evaluations.
+
+
+## Auto Release Configuration
+
+```yaml
+ # How do we want dates to be formatted in the email template
+ date_time_format: "%c"
+ time_format: "%l:%M%p"
+ date_format: "%A, %-d %B"
+
+ # Cron schedule for sending notification emails (default every 5 minutes)
+ email_schedule: "*/5 * * * *"
+
+ # Email template name to use for notifications
+ email_template: "auto_release"
+
+ # Use unique templates per booking type (e.g. auto_release_desk, auto_release_parking)
+ unique_templates: false
+
+ # Hours ahead to check for bookings that may need to be released
+ time_window_hours: 4
+
+ # User work locations that trigger auto-release
+ # Available locations: wfh (Work From Home), aol (Away on Leave), wfo (Work From Office)
+ release_locations: ["wfh", "aol"]
+
+ # Skip bookings created after their start time
+ skip_created_after_start: true
+
+ # Skip bookings created on the same day as the booking
+ skip_same_day: false
+
+ # Skip all-day bookings from auto-release
+ skip_all_day: false
+
+ # Cache timeout for asset name lookups (in seconds)
+ asset_cache_timeout: 3600
+```
+
+## Zone Configuration Requirements
+
+**CRITICAL:** The `auto_release` configuration must be set on the building zone as an **Unencrypted** setting. This is absolutely required for both the driver to function properly and for the Concierge UI to manage auto-release settings.
+
+**STRONGLY RECOMMENDED:** Use the Concierge UI to configure auto-release settings. The UI provides a user-friendly interface for managing all auto-release configuration options and ensures proper validation of settings.
+
+The building zone configuration should look like this:
+
+```yaml
+# This must be configured as Unencrypted on the building zone
+auto_release:
+ # Time before booking start to send notification email (minutes)
+ # Can be negative to send notifications after booking start
+ time_before: 10
+
+ # Time after booking start to automatically release booking (minutes)
+ time_after: 15
+
+ # Resource types to monitor for auto-release
+ resources: ["desk", "parking"]
+
+ # Default work preferences for users without configured preferences
+ default_work_preferences: []
+
+ # Release bookings outside of configured work hours
+ # Set to true for 24/7 automatic release capability
+ release_outside_hours: false
+
+ # Start time for all-day bookings (24-hour format, e.g. 8.0 = 8:00 AM)
+ # See detailed explanation below
+ all_day_start: 8.0
+
+ # Per-resource timing overrides (optional)
+ # desk_time_before: 5 # Override time_before for desk bookings
+ # desk_time_after: 20 # Override time_after for desk bookings
+```
+
+### Important Configuration Notes
+
+- **Negative time_before values**: When `time_before` is negative, notification emails are sent AFTER the booking has started. For example, `time_before: -5` means emails are sent 5 minutes after the booking start time.
+
+- **24/7 Release**: For buildings that need automatic release at any time of day, set `release_outside_hours: true`. This is particularly useful for flexible workspaces.
+
+- **Resource-specific timing**: You can override `time_before` and `time_after` for specific resource types by adding `{resource}_time_before` and `{resource}_time_after` settings.
+
+- **All-day booking start time (`all_day_start`)**: All-day bookings technically start at midnight (00:00), but checking work preferences against midnight doesn't make practical sense. The `all_day_start` setting defines a virtual "work day start time" that is used ONLY for evaluating whether an all-day booking should be released based on the user's work location preferences.
+
+ For example, if `all_day_start: 8.0` (8:00 AM) and a user has work preferences indicating they work from home from 8:00 AM to 5:00 PM, the system will check the user's 8:00 AM work location preference to determine if the all-day booking should be released. This makes the evaluation meaningful in the context of a normal work day rather than checking against midnight when most people wouldn't be expected to be at work anyway.
+
+ The actual booking times remain unchanged - this setting only affects the work preference evaluation logic for all-day bookings.
+
+
+## Default Work Preferences Configuration
+
+The `default_work_preferences` setting provides fallback work location preferences for users who haven't configured their preferences in the Workplace app. This is particularly useful during initial rollout or for users who haven't yet set up their work schedules.
+
+**RECOMMENDED:** Use the Concierge UI to configure default work preferences. The UI provides validation and makes it easier to set up complex schedules without manually writing YAML.
+
+```yaml
+auto_release:
+ default_work_preferences:
+ # Monday (day 1) - User works from home 9 AM to 5 PM
+ - day_of_week: 1
+ blocks:
+ - start_time: 9.0 # 9:00 AM
+ end_time: 17.0 # 5:00 PM
+ location: "wfh" # Work From Home
+
+ # Tuesday (day 2) - User works from office 8:30 AM to 4:30 PM
+ - day_of_week: 2
+ blocks:
+ - start_time: 8.5 # 8:30 AM
+ end_time: 16.5 # 4:30 PM
+ location: "wfo" # Work From Office
+
+ # Wednesday (day 3) - Split day: morning WFH, afternoon WFO
+ - day_of_week: 3
+ blocks:
+ - start_time: 9.0 # 9:00 AM
+ end_time: 13.0 # 1:00 PM
+ location: "wfh"
+ - start_time: 14.0 # 2:00 PM
+ end_time: 18.0 # 6:00 PM
+ location: "wfo"
+
+ # Thursday (day 4) - Away on leave all day
+ - day_of_week: 4
+ blocks:
+ - start_time: 0.0 # All day
+ end_time: 24.0
+ location: "aol" # Away on Leave
+
+ # Friday through Sunday can be omitted if no default schedule needed
+```
+
+### Day of Week Values
+- `0` = Sunday
+- `1` = Monday
+- `2` = Tuesday
+- `3` = Wednesday
+- `4` = Thursday
+- `5` = Friday
+- `6` = Saturday
+
+### Time Format
+Times are specified in 24-hour format as decimal numbers:
+- `9.0` = 9:00 AM
+- `9.5` = 9:30 AM
+- `17.0` = 5:00 PM
+- `17.75` = 5:45 PM
+
+### Location Values
+- `"wfh"` = Work From Home (triggers auto-release)
+- `"wfo"` = Work From Office (prevents auto-release)
+- `"aol"` = Away on Leave (triggers auto-release)
+
+**Note**: These defaults are only used for users who haven't set their own preferences in the Workplace app. Once a user configures their preferences, these defaults are ignored for that user.
+
+**Important**: If `release_outside_hours: true` is set, configuring `default_work_preferences` may be unnecessary. When `release_outside_hours` is enabled, any booking that doesn't match the user's configured work preferences (or default preferences) will automatically be flagged for release anyway. This makes `default_work_preferences` primarily useful when you want more granular control over release timing rather than blanket 24/7 release behavior.
+
+
+## Template Configuration on Mailer
+
+The driver expects an email template for notifying users about pending releases:
+
+* `auto_release` (default template name, configurable via email_template setting)
+* `auto_release_desk` (if unique_templates is true and desk is a configured resource)
+* `auto_release_parking` (if unique_templates is true and parking is a configured resource)
+
+```yaml
+email_templates:
+ bookings:
+ auto_release:
+ subject: "Your booking may be released - %{asset_name} on %{start_date}"
+ html: >
+
+ Hello %{user_name},
+ Your booking for %{asset_name} on %{start_datetime} may be automatically released
+ because your work location preferences indicate you are working from home or away on leave.
+
+ If you plan to use this booking, please check in when you arrive.
+
+ Booking Details:
+
+ - Resource: %{asset_name}
+ - Date: %{start_date}
+ - Time: %{start_time} - %{end_time}
+ - Reason: %{reason}
+
+
+```
+
+## Template Variables
+
+The following variables are available for use in email templates:
+
+* `booking_id` - Unique identifier for the booking that may be released
+* `booking_start` - Unix timestamp of when the booking begins
+* `booking_end` - Unix timestamp of when the booking ends
+* `start_time` - Formatted start time (e.g., "9:00AM")
+* `start_date` - Formatted start date (e.g., "Monday, 15 January")
+* `start_datetime` - Formatted start date and time (e.g., "Mon Jan 15 09:00:00 2024")
+* `end_time` - Formatted end time (e.g., "5:00PM")
+* `end_date` - Formatted end date (e.g., "Monday, 15 January")
+* `end_datetime` - Formatted end date and time (e.g., "Mon Jan 15 17:00:00 2024")
+* `asset_id` - Identifier of the booked resource
+* `asset_name` - Name of the booked resource
+* `user_id` - Identifier of the person who has the booking
+* `user_email` - Email address of the person who has the booking
+* `user_name` - Full name of the person who has the booking
+* `reason` - Title or purpose of the booking
+* `approver_name` - Name of the person who approved the booking
+* `approver_email` - Email of the person who approved the booking
+* `booked_by_name` - Name of the person who made the booking
+* `booked_by_email` - Email of the person who made the booking
+
+
+## How It Works
+
+1. **Monitoring**: The driver periodically checks for bookings in the configured time window that haven't been checked in
+2. **User Preferences**: For each booking, it retrieves the user's work location preferences and any daily overrides
+3. **Location Matching**: If the user's work location preference matches a release location (e.g., "wfh", "aol") during the booking time, the booking is flagged for potential release
+4. **Notification**: An email is sent to the user before the booking start time (configurable via `time_before`)
+5. **Release**: If the user doesn't check in after the booking start time, the booking is automatically rejected after the configured delay (`time_after`)
+
+The driver respects user work preferences and overrides, only releasing bookings when users have indicated they will be working from home or away on leave during the booking period.
+
+
+## User Work Preferences
+
+Users can set their work location preferences through the **Workplace app**. These preferences are stored in the Staff API and include:
+
+* **Work Preferences**: Regular weekly schedule indicating work location by day and time
+* **Work Overrides**: Specific date overrides for the regular schedule (e.g., working from office on a normally WFH day)
+
+The driver checks both preferences and overrides to determine if a user will be on-site for their booking. Users should ensure their work location preferences are kept up-to-date in the Workplace app to avoid unnecessary booking releases.
+
+
+## Debugging and Monitoring
+
+The driver provides a `explain_state` function that returns detailed information about:
+
+* Current pending bookings and why they are or aren't flagged for release
+* Bookings that have been emailed
+* Bookings that have been released
+* Detailed reasoning for each booking's status
+
+This can be helpful for troubleshooting why certain bookings are or aren't being processed.
\ No newline at end of file
diff --git a/drivers/place/auto_release_spec.cr b/drivers/place/auto_release_spec.cr
new file mode 100644
index 00000000000..8297bf3b09e
--- /dev/null
+++ b/drivers/place/auto_release_spec.cr
@@ -0,0 +1,1293 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/mailer"
+
+class StaffAPI < DriverSpecs::MockDriver
+ def on_load
+ self[:rejected] = 0
+ end
+
+ def reject(booking_id : String | Int64, utm_source : String? = nil, instance : Int64? = nil)
+ self[:rejected] = self[:rejected].as_i + 1
+ end
+
+ TIMEZONE = "Australia/Sydney"
+ TIME_LOCAL = Time.local(location: Time::Location.load(TIMEZONE))
+ TIME_YESTERDAY = TIME_LOCAL - 1.day
+ TIME_START_OF_DAY = TIME_LOCAL - TIME_LOCAL.hour.hours - TIME_LOCAL.minute.minutes - TIME_LOCAL.second.seconds
+ TIME_END_OF_DAY = TIME_START_OF_DAY + 1.day - 1.seconds
+ DATE = TIME_LOCAL.to_s(format: "%F")
+ DAY_OF_WEEK = TIME_LOCAL.day_of_week.value == 0 ? 7 : TIME_LOCAL.day_of_week.value
+
+ # Using a constant for bookings to ensure the times don't change during tests
+ BOOKINGS = [
+ {
+ id: 1,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_001",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL + 1.hour).to_unix,
+ booking_end: (TIME_LOCAL + 2.hours).to_unix,
+ timezone: TIMEZONE,
+ title: "ignore",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: TIME_LOCAL.to_unix,
+ created: TIME_LOCAL.to_unix,
+ },
+ {
+ id: 2,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_002",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL + 5.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "notify",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: TIME_LOCAL.to_unix,
+ created: TIME_LOCAL.to_unix,
+ },
+ {
+ id: 3,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_003",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 11.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "reject",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: (TIME_LOCAL - 20.minutes).to_unix,
+ created: (TIME_LOCAL - 20.minutes).to_unix,
+ },
+ {
+ id: 4,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_004",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL + 5.hours).to_unix,
+ booking_end: (TIME_LOCAL + 6.hours).to_unix,
+ timezone: TIMEZONE,
+ title: "ignore_after_hours",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: TIME_LOCAL.to_unix,
+ created: TIME_LOCAL.to_unix,
+ },
+ {
+ id: 5,
+ user_id: "user-wfo",
+ user_email: "user_two@example.com",
+ user_name: "User Two",
+ asset_id: "desk_005",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 11.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "ignore_wfo",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfo",
+ booked_by_email: "user_two@example.com",
+ booked_by_name: "User Two",
+ process_state: "approved",
+ last_changed: (TIME_LOCAL - 20.minutes).to_unix,
+ created: (TIME_LOCAL - 20.minutes).to_unix,
+ },
+ {
+ id: 6,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_006",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 11.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "ignore_last_minute_checkin",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: (TIME_LOCAL - 20.minutes).to_unix,
+ created: (TIME_LOCAL - 20.minutes).to_unix,
+ },
+ {
+ id: 7,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_007",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 11.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "ignore_last_minute_schedule_change",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: (TIME_LOCAL - 20.minutes).to_unix,
+ created: (TIME_LOCAL - 20.minutes).to_unix,
+ },
+ {
+ id: 8,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_008",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 2.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "reject_on_start",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: (TIME_LOCAL - 20.minutes).to_unix,
+ created: (TIME_LOCAL - 20.minutes).to_unix,
+ },
+ {
+ id: 9,
+ user_id: "user-aol",
+ user_email: "user_three@example.com",
+ user_name: "User Three",
+ asset_id: "desk_009",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 11.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "release_override_aol",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-aol",
+ booked_by_email: "user_three@example.com",
+ booked_by_name: "User Three",
+ process_state: "approved",
+ last_changed: (TIME_LOCAL - 20.minutes).to_unix,
+ created: (TIME_LOCAL - 20.minutes).to_unix,
+ },
+ {
+ id: 10,
+ user_id: "user-wfh-override",
+ user_email: "user_four@example.com",
+ user_name: "User Four",
+ asset_id: "desk_010",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 11.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "ignore_override",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfo-override",
+ booked_by_email: "user_four@example.com",
+ booked_by_name: "User Four",
+ process_state: "approved",
+ last_changed: (TIME_LOCAL - 20.minutes).to_unix,
+ created: (TIME_LOCAL - 20.minutes).to_unix,
+ },
+ {
+ id: 11,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_011",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 11.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "ignore_checked_in",
+ description: "",
+ checked_in: true,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: (TIME_LOCAL - 20.minutes).to_unix,
+ created: (TIME_LOCAL - 20.minutes).to_unix,
+ },
+ {
+ id: 12,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_012",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 1.seconds).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "ignore_created_after_start",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: TIME_LOCAL.to_unix,
+ created: TIME_LOCAL.to_unix,
+ },
+ {
+ id: 13,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_013",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: TIME_LOCAL.to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "ignore_same_created_and_start",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: TIME_LOCAL.to_unix,
+ created: TIME_LOCAL.to_unix,
+ },
+ {
+ id: 14,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_014",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL + 5.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "notify_created_yesterday",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: TIME_YESTERDAY.to_unix,
+ created: TIME_YESTERDAY.to_unix,
+ },
+ {
+ id: 15,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_015",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 11.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "reject_created_yesterday",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: TIME_YESTERDAY.to_unix,
+ created: TIME_YESTERDAY.to_unix,
+ },
+ {
+ id: 16,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_016",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 6.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 1.hour).to_unix,
+ timezone: TIMEZONE,
+ title: "notify_after_start",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: (TIME_LOCAL - 20.minutes).to_unix,
+ created: (TIME_LOCAL - 20.minutes).to_unix,
+ },
+ {
+ id: 17,
+ user_id: "user-wfh",
+ user_email: "user_one@example.com",
+ user_name: "User One",
+ asset_id: "desk_017",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: TIME_START_OF_DAY.to_unix,
+ booking_end: TIME_END_OF_DAY.to_unix,
+ timezone: TIMEZONE,
+ all_day: true,
+ title: "all_day",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-wfh",
+ booked_by_email: "user_one@example.com",
+ booked_by_name: "User One",
+ process_state: "approved",
+ last_changed: (TIME_LOCAL - 2.days).to_unix,
+ created: (TIME_LOCAL - 2.days).to_unix,
+ },
+ {
+ id: 18,
+ user_id: "user-after-hours",
+ user_email: "user_five@example.com",
+ user_name: "User Five",
+ asset_id: "desk_018",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL - 20.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 40.minutes).to_unix,
+ timezone: TIMEZONE,
+ all_day: false,
+ title: "outside_hours",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-after-hours",
+ booked_by_email: "user_five@example.com",
+ booked_by_name: "User Five",
+ process_state: "approved",
+ last_changed: TIME_YESTERDAY.to_unix,
+ created: TIME_YESTERDAY.to_unix,
+ },
+ {
+ id: 19,
+ user_id: "user-no-preferences",
+ user_email: "user_six@example.com",
+ user_name: "User Six",
+ asset_id: "desk_019",
+ zones: ["zone-1234"],
+ booking_type: "desk",
+ booking_start: (TIME_LOCAL + 5.minutes).to_unix,
+ booking_end: (TIME_LOCAL + 25.minutes).to_unix,
+ timezone: TIMEZONE,
+ all_day: false,
+ title: "no_preferences",
+ description: "",
+ checked_in: false,
+ rejected: false,
+ approved: true,
+ booked_by_id: "user-no-preferences",
+ booked_by_email: "user_six@example.com",
+ booked_by_name: "User Six",
+ process_state: "approved",
+ last_changed: TIME_YESTERDAY.to_unix,
+ created: TIME_YESTERDAY.to_unix,
+ },
+ ]
+
+ def query_bookings(
+ type : String? = nil,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ rejected : Bool? = nil,
+ checked_in : Bool? = nil,
+ )
+ JSON.parse(BOOKINGS.to_json)
+ end
+
+ def get_booking(booking_id : String | Int64)
+ booking = query_bookings.as_a.find { |b| b.as_h["id"] == booking_id }
+ return unless booking
+
+ case booking_id
+ when 6
+ booking.as_h["checked_in"] = JSON.parse(true.to_json)
+ when 7
+ booking.as_h["booking_start"] = JSON.parse((Time.utc + 1.hour).to_unix.to_json)
+ booking.as_h["booking_end"] = JSON.parse((Time.utc + 2.hours).to_unix.to_json)
+ end
+ booking
+ end
+
+ def user(id : String)
+ user_wfh = {
+ created_at: Time.utc.to_unix,
+ id: id,
+ email_digest: "not_real_digest",
+ name: "User One",
+ first_name: "User",
+ last_name: "One",
+ groups: [] of String,
+ country: "Australia",
+ building: "",
+ image: "",
+ authority_id: "authority-wfh",
+ deleted: false,
+ department: "",
+ work_preferences: 7.times.map do |i|
+ {
+ day_of_week: i,
+ blocks: [
+ {
+ start_time: (TIME_LOCAL - 4.hours).hour,
+ end_time: (TIME_LOCAL + 4.hours).hour,
+ location: "wfh",
+ },
+ ],
+ }
+ end,
+ sys_admin: false,
+ support: false,
+ email: "user_one@example.com",
+ phone: "",
+ ui_theme: "light",
+ login_name: "",
+ staff_id: "",
+ card_number: "",
+ }
+
+ user_wfo = {
+ created_at: Time.utc.to_unix,
+ id: id,
+ email_digest: "not_real_digest",
+ name: "User Two",
+ first_name: "User",
+ last_name: "Two",
+ groups: [] of String,
+ country: "Australia",
+ building: "",
+ image: "",
+ authority_id: "authority-wfo",
+ deleted: false,
+ department: "",
+ work_preferences: 7.times.map do |i|
+ {
+ day_of_week: i,
+ blocks: [
+ {
+ start_time: (TIME_LOCAL - 4.hours).hour,
+ end_time: (TIME_LOCAL + 4.hours).hour,
+ location: "wfo",
+ },
+ ],
+ }
+ end,
+ sys_admin: false,
+ support: false,
+ email: "user_two@example.com",
+ phone: "",
+ ui_theme: "light",
+ login_name: "",
+ staff_id: "",
+ card_number: "",
+ }
+
+ user_aol = {
+ created_at: Time.utc.to_unix,
+ id: id,
+ email_digest: "not_real_digest",
+ name: "User Three",
+ first_name: "User",
+ last_name: "Three",
+ groups: [] of String,
+ country: "Australia",
+ building: "",
+ image: "",
+ authority_id: "authority-aol",
+ deleted: false,
+ department: "",
+ work_preferences: 7.times.map do |i|
+ {
+ day_of_week: i,
+ blocks: [
+ {
+ start_time: (TIME_LOCAL - 4.hours).hour,
+ end_time: (TIME_LOCAL + 4.hours).hour,
+ location: "wfo",
+ },
+ ],
+ }
+ end,
+ work_overrides: {
+ DATE => {
+ day_of_week: DAY_OF_WEEK,
+ blocks: [
+ {
+ start_time: (TIME_LOCAL - 4.hours).hour,
+ end_time: (TIME_LOCAL + 4.hours).hour,
+ location: "aol",
+ },
+ ],
+ },
+ },
+ sys_admin: false,
+ support: false,
+ email: "user_three@example.com",
+ phone: "",
+ ui_theme: "light",
+ login_name: "",
+ staff_id: "",
+ card_number: "",
+ }
+
+ user_wfh_override = {
+ created_at: Time.utc.to_unix,
+ id: id,
+ email_digest: "not_real_digest",
+ name: "User Four",
+ first_name: "User",
+ last_name: "Four",
+ groups: [] of String,
+ country: "Australia",
+ building: "",
+ image: "",
+ authority_id: "authority-wfo-override",
+ deleted: false,
+ department: "",
+ work_preferences: 7.times.map do |i|
+ {
+ day_of_week: i,
+ blocks: [
+ {
+ start_time: (TIME_LOCAL - 4.hours).hour,
+ end_time: (TIME_LOCAL + 4.hours).hour,
+ location: "wfh",
+ },
+ ],
+ }
+ end,
+ work_overrides: {
+ DATE => {
+ day_of_week: DAY_OF_WEEK,
+ blocks: [
+ {
+ start_time: (TIME_LOCAL - 4.hours).hour,
+ end_time: (TIME_LOCAL + 4.hours).hour,
+ location: "wfo",
+ },
+ ],
+ },
+ },
+ sys_admin: false,
+ support: false,
+ email: "user_four@example.com",
+ phone: "",
+ ui_theme: "light",
+ login_name: "",
+ staff_id: "",
+ card_number: "",
+ }
+
+ user_after_hours = {
+ created_at: Time.utc.to_unix,
+ id: id,
+ email_digest: "not_real_digest",
+ name: "User Five",
+ first_name: "User",
+ last_name: "Five",
+ groups: [] of String,
+ country: "Australia",
+ building: "",
+ image: "",
+ authority_id: "authority-after-hours",
+ deleted: false,
+ department: "",
+ work_preferences: 7.times.map do |i|
+ {
+ day_of_week: i,
+ blocks: [
+ {
+ start_time: (TIME_LOCAL - 6.hours).hour,
+ end_time: (TIME_LOCAL - 2.hours).hour,
+ location: "wfo",
+ },
+ ],
+ }
+ end,
+ sys_admin: false,
+ support: false,
+ email: "user_five@example.com",
+ phone: "",
+ ui_theme: "light",
+ login_name: "",
+ staff_id: "",
+ card_number: "",
+ }
+
+ user_no_preferences = {
+ created_at: Time.utc.to_unix,
+ id: id,
+ email_digest: "not_real_digest",
+ name: "User Six",
+ first_name: "User",
+ last_name: "Six",
+ groups: [] of String,
+ country: "Australia",
+ building: "",
+ image: "",
+ authority_id: "authority-no-preferences",
+ deleted: false,
+ department: "",
+ sys_admin: false,
+ support: false,
+ email: "user_six@example.com",
+ phone: "",
+ ui_theme: "light",
+ login_name: "",
+ staff_id: "",
+ card_number: "",
+ }
+
+ case id
+ when "user-wfh"
+ JSON.parse(user_wfh.to_json)
+ when "user-wfo"
+ JSON.parse(user_wfo.to_json)
+ when "user-aol"
+ JSON.parse(user_aol.to_json)
+ when "user-wfh-override"
+ JSON.parse(user_wfh_override.to_json)
+ when "user-after-hours"
+ JSON.parse(user_after_hours.to_json)
+ when "user-no-preferences"
+ JSON.parse(user_no_preferences.to_json)
+ else
+ JSON.parse(user_wfh.to_json)
+ end
+ end
+
+ def zones(q : String? = nil,
+ limit : Int32 = 1000,
+ offset : Int32 = 0,
+ parent : String? = nil,
+ tags : Array(String) | String? = nil)
+ zones = [
+ {
+ created_at: 1660537814,
+ updated_at: 1681800971,
+ id: "zone-1234",
+ name: "Test Zone",
+ display_name: "Test Zone",
+ location: "",
+ description: "",
+ code: "",
+ type: "",
+ count: 0,
+ capacity: 0,
+ map_id: "",
+ tags: [
+ "building",
+ ],
+ triggers: [] of String,
+ parent_id: "zone-0000",
+ timezone: TIMEZONE,
+ },
+ ]
+
+ JSON.parse(zones.to_json)
+ end
+end
+
+class Mailer < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Mailer
+
+ def on_load
+ self[:sent] = 0
+ end
+
+ def send_template(
+ to : String | Array(String),
+ template : Tuple(String, String),
+ args : TemplateItems,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil,
+ )
+ self[:sent] = self[:sent].as_i + 1
+ end
+
+ def send_mail(
+ to : String | Array(String),
+ subject : String,
+ message_plaintext : String? = nil,
+ message_html : String? = nil,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil,
+ ) : Bool
+ true
+ end
+end
+
+DriverSpecs.mock_driver "Place::AutoRelease" do
+ system({
+ StaffAPI: {StaffAPI},
+ Mailer: {Mailer},
+ })
+
+ timezone = "Australia/Sydney"
+ time_local = Time.local(location: Time::Location.load(timezone))
+
+ settings({
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ },
+ release_locations: ["wfh", "aol"],
+ })
+
+ resp = exec(:get_building_zone?).get
+ resp.not_nil!.as_h["id"].should eq "zone-1234"
+
+ resp = exec(:get_pending_bookings).get
+ resp.not_nil!.as_a.size.should eq 18
+
+ resp = exec(:get_user_preferences?, "user-wfh").get
+ resp.not_nil!.as_h.keys.should eq ["work_preferences", "work_overrides"]
+
+ # Start of tests for: #pending_release
+ #######################################
+
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: false,
+ skip_all_day: true,
+ })
+
+ resp = exec(:pending_release).get
+ pending_release = resp.not_nil!.as_a.map(&.as_h["title"])
+ pending_release.should eq [
+ "ignore",
+ "notify",
+ "reject",
+ "ignore_last_minute_checkin",
+ "ignore_last_minute_schedule_change",
+ "reject_on_start",
+ "release_override_aol",
+ "notify_created_yesterday",
+ "reject_created_yesterday",
+ "notify_after_start",
+ ]
+
+ # skip_same_day: true
+ #####################
+
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: true,
+ skip_all_day: true,
+ })
+
+ resp = exec(:pending_release).get
+ pending_release = resp.not_nil!.as_a.map(&.as_h["title"])
+ pending_release.should eq [
+ "notify_created_yesterday",
+ "reject_created_yesterday",
+ ]
+
+ # all_day_start:
+ ################
+
+ # all_day_start: 20 minutes in the future
+ all_day_start_in_20_minutes = (time_local + 20.minutes).hour + ((time_local + 20.minutes).minute / 60.0)
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ all_day_start: all_day_start_in_20_minutes,
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: true,
+ skip_all_day: false,
+ })
+
+ resp = exec(:pending_release).get
+ pending_release = resp.not_nil!.as_a.map(&.as_h["title"])
+ pending_release.should eq [
+ "notify_created_yesterday",
+ "reject_created_yesterday",
+ "all_day",
+ ]
+
+ # release_outside_hours: true
+ #############################
+
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ release_outside_hours: true,
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: true,
+ skip_all_day: true,
+ })
+
+ resp = exec(:pending_release).get
+ pending_release = resp.not_nil!.as_a.map(&.as_h["title"])
+ pending_release.should eq [
+ "notify_created_yesterday",
+ "reject_created_yesterday",
+ "outside_hours",
+ "no_preferences",
+ ]
+
+ # when release_outside_hours is false (the default)
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ release_outside_hours: false,
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: true,
+ skip_all_day: true,
+ })
+
+ resp = exec(:pending_release).get
+ pending_release = resp.not_nil!.as_a.map(&.as_h["title"])
+ pending_release.should eq [
+ "notify_created_yesterday",
+ "reject_created_yesterday",
+ ]
+
+ # default_work_preferences
+ ##########################
+
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ release_outside_hours: false,
+ default_work_preferences: 7.times.map do |i|
+ {
+ day_of_week: i,
+ blocks: [
+ {
+ start_time: (time_local - 4.hours).hour,
+ end_time: (time_local + 4.hours).hour,
+ location: "wfh",
+ },
+ ],
+ }
+ end,
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: true,
+ skip_all_day: true,
+ })
+
+ resp = exec(:pending_release).get
+ pending_release = resp.not_nil!.as_a.map(&.as_h["title"])
+ pending_release.should eq [
+ "notify_created_yesterday",
+ "reject_created_yesterday",
+ "no_preferences",
+ ]
+
+ #####################################
+ # End of tests for: #pending_release
+
+ # Start of tests for: #release_bookings
+ #######################################
+
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: false,
+ })
+
+ # Ensure self[:pending_release] holds the correct bookings for the settings before testing #release_bookings
+ resp = exec(:pending_release).get
+ pending_release = resp.not_nil!.as_a.map(&.as_h["title"])
+ pending_release.should eq [
+ "ignore",
+ "notify",
+ "reject",
+ "ignore_last_minute_checkin",
+ "ignore_last_minute_schedule_change",
+ "reject_on_start",
+ "release_override_aol",
+ "notify_created_yesterday",
+ "reject_created_yesterday",
+ "notify_after_start",
+ ]
+
+ # Should reject 3 bookings
+ # booking_id: 3, title: reject
+ # booking_id: 9, title: release_override_aol
+ # booking_id: 15, title: reject_created_yesterday
+ resp = exec(:release_bookings).get
+ resp.should eq [3, 9, 15]
+ system(:StaffAPI_1)[:rejected].should eq 3
+
+ # Don't try to reject bookings that have already been rejected
+ resp = exec(:release_bookings).get
+ resp.should eq [3, 9, 15]
+ system(:StaffAPI_1)[:rejected].should eq 3
+
+ # Reject bookings immidiatly on start
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 0,
+ resources: ["desk"],
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: false,
+ })
+
+ # Should reject 5 bookings
+ # booking_id: [3, 9, 15, 8, 16], title: ["reject", "release_override_aol", "reject_created_yesterday", "reject_on_start", "notify_after_start"]
+ resp = exec(:release_bookings).get
+ resp.should eq [3, 9, 15, 8, 16]
+ system(:StaffAPI_1)[:rejected].should eq 5
+
+ # all_day_start:
+ ################
+
+ # all_day_start: 20 minutes in the future
+ all_day_start_in_20_minutes = (time_local + 20.minutes).hour + ((time_local + 20.minutes).minute / 60.0)
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ all_day_start: all_day_start_in_20_minutes,
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: true,
+ skip_all_day: false,
+ })
+
+ # Ensure self[:pending_release] holds the correct bookings for the settings before testing #release_bookings
+ resp = exec(:pending_release).get
+ pending_release = resp.not_nil!.as_a.map(&.as_h["title"])
+ pending_release.should eq [
+ "notify_created_yesterday",
+ "reject_created_yesterday",
+ "all_day",
+ ]
+
+ resp = exec(:release_bookings).get
+ resp.should eq [15]
+ system(:StaffAPI_1)[:rejected].should eq 5
+
+ # all_day_start: 20 minutes in the past
+ all_day_start_20_minutes_ago = (time_local - 20.minutes).hour + ((time_local - 20.minutes).minute / 60.0)
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ all_day_start: all_day_start_20_minutes_ago,
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: true,
+ skip_all_day: false,
+ })
+
+ resp = exec(:release_bookings).get
+ resp.should eq [15, 17]
+ system(:StaffAPI_1)[:rejected].should eq 6
+
+ # release_outside_hours: true
+ #############################
+
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ release_outside_hours: true,
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: true,
+ skip_all_day: true,
+ })
+
+ # Ensure self[:pending_release] holds the correct bookings for the settings before testing #release_bookings
+ resp = exec(:pending_release).get
+ pending_release = resp.not_nil!.as_a.map(&.as_h["title"])
+ pending_release.should eq [
+ "notify_created_yesterday",
+ "reject_created_yesterday",
+ "outside_hours",
+ "no_preferences",
+ ]
+
+ resp = exec(:release_bookings).get
+ resp.should eq [15, 18]
+ system(:StaffAPI_1)[:rejected].should eq 7
+
+ #####################################
+ # End of tests for: #release_bookings
+
+ # Start of tests for: #send_release_emails
+ ##########################################
+
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: 10,
+ time_after: 0,
+ resources: ["desk"],
+ },
+ release_locations: ["wfh", "aol"],
+ skip_created_after_start: true,
+ skip_same_day: false,
+ skip_all_day: true,
+ })
+
+ # Ensure self[:pending_release] holds the correct bookings for the settings before testing #release_bookings
+ resp = exec(:pending_release).get
+ pending_release = resp.not_nil!.as_a.map(&.as_h["title"])
+ pending_release.should eq [
+ "ignore",
+ "notify",
+ "reject",
+ "ignore_last_minute_checkin",
+ "ignore_last_minute_schedule_change",
+ "reject_on_start",
+ "release_override_aol",
+ "notify_created_yesterday",
+ "reject_created_yesterday",
+ "notify_after_start",
+ ]
+
+ # Ensure self[:released_booking_ids] holds the correct bookings for the settings before testing #send_release_emails
+ resp = exec(:release_bookings).get
+ resp.should eq [15, 3, 8, 9, 16]
+
+ # Send email once booking is past the time_before window,
+ # but before the time_after window
+ # (booking_id: 2, title: notify)
+ # (booking_id: 14, title: notify_created_yesterday)
+ resp = exec(:send_release_emails).get
+ resp.should eq [2, 14]
+ system(:Mailer_1)[:sent].should eq 2
+
+ # Spam protection, should not send email again
+ resp = exec(:send_release_emails).get
+ resp.should eq [2, 14]
+ system(:Mailer_1)[:sent].should eq 2
+
+ # Notify after start
+ ####################
+
+ settings({
+ time_window_hours: 8,
+ auto_release: {
+ time_before: -5,
+ time_after: 40,
+ resources: ["desk"],
+ },
+ })
+ status[:released_booking_ids] = [2, 14, 3, 6, 7, 9, 15]
+ status[:emailed_booking_ids] = nil
+
+ # (booking_id: 16, title: notify_after_start)
+ resp = exec(:send_release_emails).get
+ resp.should eq [16]
+ system(:Mailer_1)[:sent].should eq 3
+
+ ########################################
+ # End of tests for: #send_release_emails
+
+ # Start of tests for: #in_preference_hours?
+ ###########################################
+
+ # normal work hours, event in range
+ # start at 8am, end at 4pm, event at 3pm
+ resp = exec(:in_preference_hours?, 8.0, 16.0, 15.0).get
+ resp.should be_true
+
+ # normal work hours, event out of range (after)
+ # start at 8am, end at 4pm, event at 5pm
+ resp = exec(:in_preference_hours?, 8.0, 16.0, 17.0).get
+ resp.should be_false
+
+ # normal work hours, event out of range (before)
+ # start at 8am, end at 4pm, event at 6am
+ resp = exec(:in_preference_hours?, 8.0, 16.0, 6.0).get
+ resp.should be_false
+
+ # work hours crosses midnight, event in range
+ # start at 10pm, end at 6am, event at 3am
+ resp = exec(:in_preference_hours?, 22.0, 6.0, 3.0).get
+ resp.should be_true
+
+ # work hours crosses midnight, event out of range (after)
+ # start at 10pm, end at 6am, event at 7am
+ resp = exec(:in_preference_hours?, 22.0, 6.0, 7.0).get
+ resp.should be_false
+
+ # work hours crosses midnight, event out of range (before)
+ # start at 10pm, end at 6am, event at 8pm
+ resp = exec(:in_preference_hours?, 22.0, 6.0, 20.0).get
+ resp.should be_false
+
+ #########################################
+ # End of tests for: #in_preference_hours?
+
+ # Start of tests for: #enabled?
+ ###############################
+
+ # enabled when there are resources
+ settings({
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: ["desk"],
+ },
+ })
+ resp = exec(:enabled?).get
+ resp.should be_true
+
+ # disabled when resources is empty
+ resp = exec(:enabled?).get
+ resp.should be_true
+ settings({
+ auto_release: {
+ time_before: 10,
+ time_after: 10,
+ resources: [] of String,
+ },
+ })
+ resp = exec(:enabled?).get
+ resp.should be_false
+
+ #############################
+ # End of tests for: #enabled?
+end
diff --git a/drivers/place/booking_approval_workflows.cr b/drivers/place/booking_approval_workflows.cr
new file mode 100644
index 00000000000..30e7ae19467
--- /dev/null
+++ b/drivers/place/booking_approval_workflows.cr
@@ -0,0 +1,807 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+require "digest/md5"
+require "placeos"
+require "file"
+
+require "./booking_model"
+
+class Place::BookingApprovalWorkflows < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+
+ descriptive_name "Desk Booking Approval Workflows"
+ generic_name :BookingApproval
+ description %(picks an approval strategy based on configuration)
+
+ default_settings({
+ timezone: "Australia/Sydney",
+ date_time_format: "%c",
+ time_format: "%l:%M%p",
+ date_format: "%A, %-d %B",
+
+ booking_type: "desk",
+ unique_templates: false, # This appends the booking type to the template name
+ remind_after: 24,
+ escalate_after: 48,
+ disable_attachments: true,
+
+ approval_type: {
+ zone_id1: {
+ name: "Sydney Building 1",
+ approval: :notify,
+ support_email: "support@place.com",
+ },
+ zone_id2: {
+ name: "Melb Building",
+ approval: :manager_approval,
+ attachments: {"file-name.pdf" => "https://s3/your_file.pdf"},
+ support_email: "msupport@place.com",
+ },
+ },
+
+ reminders: {
+ crons: ["0 10 * * *", "0 14 * * *"],
+ zones: {
+ "Australia/Sydney" => ["zone_id1", "zone_id2"],
+ "Australia/Perth" => ["zone_id3"],
+ },
+ },
+ })
+
+ # bookings states:
+ # * manager_contacted = manager has been emailed to approve
+ # * manager_reminded = manager has been emailed a second time to approve
+ # * managers_manager = managers manager has been emailed to approve
+
+ accessor staff_api : StaffAPI_1
+
+ def mailer
+ system.implementing(Interface::Mailer)[0]
+ end
+
+ def on_load
+ # Some form of asset booking has occured
+ monitor("staff/booking/changed") { |_subscription, payload| parse_booking(payload) }
+
+ on_update
+ end
+
+ # See: https://crystal-lang.org/api/0.35.1/Time/Format.html
+ @date_time_format : String = "%c"
+ @time_format : String = "%l:%M%p"
+ @date_format : String = "%A, %-d %B"
+ @time_zone : Time::Location = Time::Location.load("Australia/Sydney")
+
+ @booking_type : String = "desk"
+ @unique_templates : Bool = false
+ @template_suffix : String = ""
+ @template_fields_suffix : String = ""
+ @bookings_checked : UInt64 = 0_u64
+ @error_count : UInt64 = 0_u64
+
+ @remind_after : Time::Span = 24.hours
+ @escalate_after : Time::Span = 48.hours
+ @disable_attachments : Bool = true
+ @notify_managers : Bool = false
+
+ alias SiteDetails = NamedTuple(approval: String, name: String, support_email: String, attachments: Hash(String, String)?)
+ alias Reminders = NamedTuple(crons: Array(String), zones: Hash(String, Array(String)))
+
+ # Zone_id => approval type
+ @approval_lookup : Hash(String, SiteDetails) = {} of String => SiteDetails
+
+ def on_update
+ @booking_type = setting?(String, :booking_type).presence || "desk"
+ @unique_templates = setting?(Bool, :unique_templates) || false
+ @template_suffix = @unique_templates ? "_#{@booking_type}" : ""
+ @template_fields_suffix = @unique_templates ? " (#{@booking_type})" : ""
+
+ time_zone = setting?(String, :calendar_time_zone).presence || "Australia/Sydney"
+ @time_zone = Time::Location.load(time_zone)
+ @date_time_format = setting?(String, :date_time_format) || "%c"
+ @time_format = setting?(String, :time_format) || "%l:%M%p"
+ @date_format = setting?(String, :date_format) || "%A, %-d %B"
+
+ @remind_after = (setting?(Int32, :remind_after) || 24).hours
+ @escalate_after = (setting?(Int32, :escalate_after) || 48).hours
+ @notify_managers = setting?(Bool, :notify_managers) || false
+
+ @approval_lookup = setting(Hash(String, SiteDetails), :approval_type)
+ attach = setting?(Bool, :disable_attachments)
+ @disable_attachments = attach.nil? ? true : !!attach
+
+ schedule.clear
+ schedule.every(5.minutes) { check_bookings }
+
+ reminders = setting?(Reminders, :reminders) || {crons: [] of String, zones: {} of String => Array(String)}
+ reminders[:crons].each do |cron|
+ reminders[:zones].each do |timezone, zones|
+ begin
+ schedule.cron(cron, Time::Location.load(timezone)) { send_checkin_reminder(zones) }
+ rescue error
+ logger.warn(exception: error) { "failed to schedule reminder: #{zones} => #{timezone} : #{cron}" }
+ end
+ end
+ end
+ end
+
+ def template_fields : Array(TemplateFields)
+ time_now = Time.utc.in(@time_zone)
+
+ common_fields = [
+ {name: "booking_id", description: "Unique identifier for the booking"},
+ {name: "start_time", description: "Booking start time (e.g., #{time_now.to_s(@time_format)})"},
+ {name: "start_date", description: "Booking start date (e.g., #{time_now.to_s(@date_format)})"},
+ {name: "start_datetime", description: "Booking start date and time (e.g., #{time_now.to_s(@date_time_format)})"},
+ {name: "end_time", description: "Booking end time (e.g., #{time_now.to_s(@time_format)})"},
+ {name: "end_date", description: "Booking end date (e.g., #{time_now.to_s(@date_format)})"},
+ {name: "end_datetime", description: "Booking end date and time (e.g., #{time_now.to_s(@date_time_format)})"},
+ {name: "starting_unix", description: "Booking start time as Unix timestamp"},
+ {name: "desk_id", description: "Identifier of the booked desk"},
+ {name: "user_id", description: "Identifier of the person the booking is for"},
+ {name: "user_email", description: "Email of the person the booking is for"},
+ {name: "user_name", description: "Name of the person the booking is for"},
+ {name: "reason", description: "Purpose or title of the booking"},
+ {name: "level_zone", description: "Zone identifier for the specific floor level"},
+ {name: "building_zone", description: "Zone identifier for the building"},
+ {name: "building_name", description: "Name of the building"},
+ {name: "support_email", description: "Contact email for booking support"},
+ {name: "approver_name", description: "Name of the person who approved/rejected the booking"},
+ {name: "approver_email", description: "Email of the person who approved/rejected the booking"},
+ {name: "booked_by_name", description: "Name of the person who made the booking"},
+ {name: "booked_by_email", description: "Email of the person who made the booking"},
+ {name: "attachment_name", description: "Name of any attached files"},
+ {name: "attachment_url", description: "URL to download any attachments"},
+ ]
+
+ [
+ TemplateFields.new(
+ trigger: {"bookings", "group_booking_sent#{@template_suffix}"},
+ name: "Group booking sent#{@template_fields_suffix}",
+ description: "Notification when a group booking has been created",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "approved_by#{@template_suffix}"},
+ name: "Booking approved by#{@template_fields_suffix}",
+ description: "Notification when booking is approved by someone other than the requester",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "approved#{@template_suffix}"},
+ name: "Booking approved#{@template_fields_suffix}",
+ description: "Notification when booking is approved",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "rejected#{@template_suffix}"},
+ name: "Booking rejected#{@template_fields_suffix}",
+ description: "Notification when booking is rejected",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "checked_in#{@template_suffix}"},
+ name: "Booking checked in#{@template_fields_suffix}",
+ description: "Notification when user checks in to their booking",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "cancelled_by#{@template_suffix}"},
+ name: "Booking cancelled by#{@template_fields_suffix}",
+ description: "Notification when booking is cancelled by someone other than the booker",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "cancelled#{@template_suffix}"},
+ name: "Booking cancelled#{@template_fields_suffix}",
+ description: "Notification when booking is cancelled by the booker",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "manager_notify_cancelled#{@template_suffix}"},
+ name: "Booking cancelled manager notification#{@template_fields_suffix}",
+ description: "Notification to manager when their team member's booking is cancelled",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "manager_approval#{@template_suffix}"},
+ name: "Booking manager approval#{@template_fields_suffix}",
+ description: "Request for manager to approve a booking#{@template_suffix}",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "manager_contacted#{@template_suffix}"},
+ name: "Booking manager contacted#{@template_fields_suffix}",
+ description: "Notification to user that their manager has been contacted for approval",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "notify_manager#{@template_suffix}"},
+ name: "Booking manager notification#{@template_fields_suffix}",
+ description: "Notification to manager about their team member's booking",
+ fields: common_fields
+ ),
+ ]
+ end
+
+ # Booking id => event, timestamp
+ @debounce = {} of Int64 => {String?, Int64}
+
+ # Booker has been informed of the group booking email
+ @group_email_notifications = {} of String => Int64
+
+ protected def parse_booking(payload)
+ logger.debug { "received booking event payload: #{payload}" }
+ booking_details = Booking.from_json payload
+
+ # Only process booking types of interest
+ return unless booking_details.booking_type == @booking_type
+
+ # Ignore when a bookings state is updated
+ return if {"process_state", "metadata_changed"}.includes?(booking_details.action)
+
+ # Ignore the same event in a short period of time
+ previous = @debounce[booking_details.id]?
+ return if previous && previous[0] == booking_details.action
+ @debounce[booking_details.id] = {booking_details.action, Time.utc.to_unix}
+
+ approval_details = get_building_name(booking_details.zones)
+ return unless approval_details
+ building_zone, building_name, approval_type, support_email, attachments = approval_details
+ building_key = building_name.downcase.gsub(' ', '_')
+
+ timezone = booking_details.timezone.presence || @time_zone.name
+ location = Time::Location.load(timezone)
+
+ # https://crystal-lang.org/api/0.35.1/Time/Format.html
+ # date and time (Tue Apr 5 10:26:19 2016)
+ starting = Time.unix(booking_details.booking_start).in(location)
+ ending = Time.unix(booking_details.booking_end).in(location)
+
+ # Ignore changes to meetings that have already ended
+ return if Time.utc > ending
+
+ attach = attachments.first?
+
+ args = {
+ booking_id: booking_details.id,
+ start_time: starting.to_s(@time_format),
+ start_date: starting.to_s(@date_format),
+ start_datetime: starting.to_s(@date_time_format),
+ end_time: ending.to_s(@time_format),
+ end_date: ending.to_s(@date_format),
+ end_datetime: ending.to_s(@date_time_format),
+ starting_unix: booking_details.booking_start,
+
+ desk_id: booking_details.asset_id,
+ user_id: booking_details.user_id,
+ user_email: booking_details.user_email,
+ user_name: booking_details.user_name,
+ reason: booking_details.title,
+
+ level_zone: booking_details.zones.reject { |z| z == building_zone }.first?,
+ building_zone: building_zone,
+ building_name: building_name,
+ support_email: support_email,
+
+ approver_name: booking_details.approver_name,
+ approver_email: booking_details.approver_email,
+
+ booked_by_name: booking_details.booked_by_name,
+ booked_by_email: booking_details.booked_by_email,
+
+ attachment_name: attach.try &.[](:file_name),
+ attachment_url: attach.try &.[](:uri),
+ }
+
+ attachments.clear if @disable_attachments
+
+ case booking_details.action
+ when "create", "changed"
+ group_id = booking_details.extension_data["group_id"]?.try &.to_s
+ if group_id && !@group_email_notifications.has_key?(group_id)
+ @group_email_notifications[group_id] = Time.utc.to_unix
+
+ mailer.send_template(
+ to: booking_details.booked_by_email,
+ template: {"bookings", "group_booking_sent#{@template_suffix}"},
+ args: args
+ )
+ end
+
+ check_approval(
+ booking_details,
+ approval_type,
+ building_key,
+ attachments,
+ args
+ )
+ when "approved"
+ return if booking_details.process_state == "approval_sent"
+
+ third_party = approval_type == "manager_approval" && booking_details.user_email != booking_details.booked_by_email
+ mailer.send_template(
+ to: booking_details.user_email,
+ template: {"bookings", third_party ? "approved_by#{@template_suffix}" : "approved#{@template_suffix}"},
+ args: args,
+ attachments: attachments
+ ).get
+
+ staff_api.booking_state(booking_details.id, "approval_sent", booking_details.instance).get
+ when "rejected", "checked_in"
+ # no attachment for rejection email
+ user_email = booking_details.user_email
+ mailer.send_template(
+ to: user_email,
+ template: {"bookings", "#{booking_details.action}#{@template_suffix}"},
+ args: args
+ )
+ when "cancelled"
+ third_party = booking_details.approver_email && booking_details.approver_email != booking_details.user_email.downcase
+
+ # no attachment for rejection email
+ user_email = booking_details.user_email
+ mailer.send_template(
+ to: user_email,
+ template: {"bookings", third_party ? "cancelled_by#{@template_suffix}" : "cancelled#{@template_suffix}"},
+ args: args
+ )
+
+ if @notify_managers && (manager_email = get_manager(user_email).try(&.at(0)))
+ mailer.send_template(
+ to: manager_email,
+ template: {"bookings", "manager_notify_cancelled#{@template_suffix}"},
+ args: args
+ )
+ end
+ end
+
+ @bookings_checked += 1
+ self[:bookings_checked] = @bookings_checked
+ rescue error
+ logger.error { error.inspect_with_backtrace }
+ self[:last_error] = {
+ error: error.message,
+ time: Time.local.to_s,
+ user: payload,
+ }
+ @error_count += 1
+ self[:error_count] = @error_count
+ end
+
+ def get_building_name(zones : Array(String))
+ zones.each do |zone_id|
+ details = @approval_lookup[zone_id]?
+ if details
+ attachments = (details[:attachments] || {} of String => String).compact_map { |n, l| get_attachment(n, l) }
+ logger.debug { "attaching #{attachments.size} files" }
+ return {zone_id, details[:name], details[:approval], details[:support_email], attachments}
+ end
+ end
+ nil
+ end
+
+ protected def check_approval(
+ booking_details,
+ approval_type,
+ building_key,
+ attachments,
+ args
+ )
+ user_email = booking_details.user_email
+ state = booking_details.process_state
+
+ logger.debug { "checking status of #{approval_type} booking #{booking_details.id} for #{booking_details.user_name}\ncurrent state: #{state}" }
+
+ case approval_type
+ when "manager_approval"
+ logger.debug { "checking manager approval state: #{state}" }
+
+ case state
+ # manager needs to approve this bookings
+ when nil || state.try(&.empty?)
+ manager_email, manager_name = get_manager(user_email)
+ if manager_email && manager_name
+ logger.debug { "requesting manager approval..." }
+
+ mailer.send_template(
+ to: manager_email,
+ template: {"bookings", "manager_approval#{@template_suffix}"},
+ args: args
+ ).get
+
+ # set the booking state
+ staff_api.booking_state(booking_details.id, "manager_contacted", booking_details.instance).get
+
+ mailer.send_template(
+ to: user_email,
+ template: {"bookings", "manager_contacted#{@template_suffix}"},
+ args: args.merge({
+ manager_email: manager_email,
+ manager_name: manager_name,
+ })
+ )
+ else
+ logger.debug { "manager not found, approving booking!" }
+ # approve automatically if no manager to approve
+ staff_api.approve(booking_details.id, booking_details.instance).get
+ end
+ # we might need to remind this manager to approve or reject a booking
+ when "manager_contacted"
+ if booking_details.changed < @remind_after.ago
+ logger.debug { "sending manager reminder email" }
+
+ if manager_email = get_manager(user_email).try(&.at(0))
+ mailer.send_template(
+ to: manager_email,
+ template: {"bookings", "manager_approval#{@template_suffix}"},
+ args: args
+ ).get
+
+ # set the booking state
+ staff_api.booking_state(booking_details.id, "manager_reminded", booking_details.instance).get
+ else
+ logger.debug { "manager not found, approving booking!" }
+ # approve automatically if no manager to approve
+ staff_api.approve(booking_details.id, booking_details.instance).get
+ end
+ end
+ # do we need to escalate the approval?
+ when "manager_reminded"
+ if booking_details.changed < @escalate_after.ago
+ if manager_email = get_manager(user_email).try(&.at(0))
+ if manager_email = get_manager(manager_email).try(&.at(0))
+ logger.debug { "sending managers manager an email" }
+
+ mailer.send_template(
+ to: manager_email,
+ template: {"bookings", "manager_approval#{@template_suffix}"},
+ args: args
+ ).get
+
+ # set the booking state
+ staff_api.booking_state(booking_details.id, "managers_manager", booking_details.instance).get
+ else
+ # approve automatically if no manager to approve
+ logger.debug { "managers manager not found, approving booking!" }
+ staff_api.approve(booking_details.id, booking_details.instance).get
+ end
+ else
+ # approve automatically if no manager to approve
+ logger.debug { "manager not found, approving booking!" }
+ staff_api.approve(booking_details.id, booking_details.instance).get
+ end
+ end
+ when "managers_manager"
+ if booking_details.changed > 5.days.ago
+ # approve automatically if no manager approves in over 4 days
+ logger.debug { "approving booking as managers have failed to approve" }
+ staff_api.approve(booking_details.id, booking_details.instance).get
+ end
+ end
+ when "notify"
+ logger.debug { "approving booking and notifing manager = #{@notify_managers}" }
+
+ # manager needs to be notified of approval
+ staff_api.approve(booking_details.id, booking_details.instance).get
+ # NOTE:: user will be sent email via the approval event
+
+ if @notify_managers && (manager_email = get_manager(user_email).try(&.at(0)))
+ mailer.send_template(
+ to: manager_email,
+ template: {"bookings", "notify_manager#{@template_suffix}"},
+ args: args
+ )
+ end
+ else
+ # Auto approval
+ logger.debug { "approving booking as unknown approval type: #{approval_type.inspect}" }
+ staff_api.approve(booking_details.id, booking_details.instance).get
+ # NOTE:: user will be sent email via the approval event
+ end
+ end
+
+ protected def get_attachment(filename : String, uri : String)
+ return {file_name: filename, content: "", uri: uri} if @disable_attachments
+
+ ext = filename.split('.')[-1]
+ file = Digest::MD5.base64digest(uri).gsub(/[^0-9a-zA-Z\.]/, "") + ext
+
+ # Local cache is pre-encoded
+ if File.exists?(file)
+ content = File.read(file)
+ logger.debug { "attachment saved locally #{filename} - #{content.bytesize}" }
+ return {file_name: filename, content: content, uri: uri}
+ end
+
+ # Download the file from the internet
+ buffer = IO::Memory.new
+ begin
+ buf = Bytes.new(64)
+ HTTP::Client.get(uri) do |response|
+ raise "HTTP request failed with #{response.status_code}" unless response.success?
+ body_io = response.body_io
+ while ((bytes = body_io.read(buf)) > 0)
+ buffer.write(buf[0, bytes])
+ end
+ end
+ rescue error
+ logger.warn(exception: error) { "unable to download attachment: #{uri}" }
+ return nil
+ end
+
+ encoded = Base64.strict_encode(buffer)
+ File.write file, encoded
+
+ logger.debug { "attachment downloaded #{filename} - #{encoded.bytesize}" }
+
+ {file_name: filename, content: encoded, uri: uri}
+ end
+
+ @check_bookings_mutex = Mutex.new
+
+ @[Security(Level::Support)]
+ def check_bookings(months_from_now : Int32 = 2)
+ # Clean up old debounce data
+ expired = 5.minutes.ago.to_unix
+ @debounce.reject! { |_, (_event, entered)| expired > entered }
+
+ expired = 1.hour.ago.to_unix
+ @group_email_notifications.reject! { |_, entered| expired > entered }
+
+ @check_bookings_mutex.synchronize do
+ @approval_lookup.each do |building_zone, details|
+ building_name = details[:name]
+ approval_type = details[:approval]
+ support_email = details[:support_email]
+ attachments = (details[:attachments] || {} of String => String).compact_map { |n, l| get_attachment(n, l) }
+ building_key = building_name.downcase.gsub(' ', '_')
+
+ perform_booking_check(building_zone, approval_type, building_name, building_key, support_email, attachments, months_from_now)
+ end
+ end
+ end
+
+ protected def perform_booking_check(building_zone, approval_type, building_name, building_key, support_email, attachments, months_from_now = 2)
+ now = Time.utc.to_unix
+ later = months_from_now.months.from_now.to_unix
+
+ bookings = staff_api.query_bookings(
+ type: @booking_type,
+ period_start: now,
+ period_end: later,
+ zones: [building_zone],
+ approved: false,
+ rejected: false,
+ created_before: 2.minutes.ago.to_unix
+ ).get.as_a
+
+ bookings = bookings + staff_api.query_bookings(
+ type: @booking_type,
+ period_start: now,
+ period_end: later,
+ zones: [building_zone],
+ approved: true,
+ rejected: false,
+ created_before: 2.minutes.ago.to_unix
+ ).get.as_a
+
+ bookings = Array(Booking).from_json(bookings.to_json)
+ logger.debug { "checking #{bookings.size} requested bookings in #{building_name}" }
+ bookings.each do |booking_details|
+ timezone = booking_details.timezone.presence || @time_zone.name
+ location = Time::Location.load(timezone)
+
+ starting = Time.unix(booking_details.booking_start).in(location)
+ ending = Time.unix(booking_details.booking_end).in(location)
+
+ attach = attachments.first?
+
+ args = {
+ booking_id: booking_details.id,
+ start_time: starting.to_s(@time_format),
+ start_date: starting.to_s(@date_format),
+ start_datetime: starting.to_s(@date_time_format),
+ end_time: ending.to_s(@time_format),
+ end_date: ending.to_s(@date_format),
+ end_datetime: ending.to_s(@date_time_format),
+ starting_unix: booking_details.booking_start,
+
+ desk_id: booking_details.asset_id,
+ user_id: booking_details.user_id,
+ user_email: booking_details.user_email,
+ user_name: booking_details.user_name,
+ reason: booking_details.title,
+
+ level_zone: booking_details.zones.reject { |z| z == building_zone }.first?,
+ building_zone: building_zone,
+ building_name: building_name,
+ support_email: support_email,
+
+ booked_by_name: booking_details.booked_by_name,
+ booked_by_email: booking_details.booked_by_email,
+
+ attachment_name: attach.try &.[](:file_name),
+ attachment_url: attach.try &.[](:uri),
+ }
+
+ attachments.clear if @disable_attachments
+
+ begin
+ if booking_details.approved
+ if booking_details.process_state != "approval_sent"
+ third_party = booking_details.user_email != booking_details.booked_by_email
+
+ mailer.send_template(
+ to: booking_details.user_email,
+ template: {"bookings", third_party ? "approved_by#{@template_suffix}" : "approved#{@template_suffix}"},
+ args: args,
+ attachments: attachments
+ )
+ staff_api.booking_state(booking_details.id, "approval_sent", booking_details.instance).get
+ end
+ else
+ check_approval(
+ booking_details,
+ approval_type,
+ building_key,
+ attachments,
+ args
+ )
+ end
+ rescue error
+ logger.error(exception: error) { "while processing booking id #{booking_details.id}" }
+ end
+ end
+ end
+
+ @[Security(Level::Support)]
+ def get_manager(staff_email : String)
+ manager = mailer.get_user_manager(staff_email).get
+ {(manager["email"]? || manager["username"]).as_s, manager["name"].as_s}
+ rescue error
+ logger.warn { "failed to email manager of #{staff_email}\n#{error.inspect_with_backtrace}" }
+ {nil, nil}
+ end
+
+ @[Security(Level::Support)]
+ def users_with_invalid_desk_bookings(building_zone : String, ending : Int64)
+ # [] of {zone: {id:}, metadata: {desks: {details: [{id:, groups: [] of String}]}}}
+ meta_raw = staff_api.metadata_children(building_zone, "desks").get.as_a
+
+ # Zone => Desk_id => Groups
+ metadata = {} of String => Hash(String, Array(String))
+ meta_raw.each do |zone|
+ desks = {} of String => Array(String)
+ zone_id = zone["zone"]["id"].as_s
+ zone["metadata"]["desks"]["details"].as_a.each do |desk|
+ desks[desk["id"].as_s] = desk["groups"].as_a.map(&.as_s.downcase)
+ end
+ metadata[zone_id] = desks
+ end
+
+ # User email, Desk ID, zone, booking id, starting, starting friendly
+ users = [] of Tuple(String, String, String, Int64, Int64, String)
+
+ # [] of {user_email:, zones:, asset_id:}
+ bookings = staff_api.query_bookings(type: "desk", period_end: ending, zones: [building_zone], rejected: false).get.as_a
+ bookings.each do |booking|
+ user_email = booking["user_email"].as_s
+ level_id = booking["zones"].as_a.map(&.as_s).reject(building_zone).first
+ desk_id = booking["asset_id"].as_s
+ booking_id = booking["id"].as_i64
+ starting = booking["booking_start"].as_i64
+
+ if desks = metadata[level_id]?
+ if groups = desks[desk_id]?
+ next if groups.empty?
+
+ users_groups = mailer.get_groups(user_email).get.as_a.map { |g| g["name"].as_s.downcase }
+ overlap = users_groups & groups
+ if overlap.empty?
+ date_friendly = Time.unix(starting).to_s(@date_format)
+ users << {user_email, desk_id, level_id, booking_id, starting, date_friendly}
+ end
+ end
+ end
+ end
+
+ logger.debug { "Email,Desk ID,Zone,Booking id,Starting,Start date\n#{users.map { |u| "#{u[0]},#{u[1]},#{u[2]},#{u[3]},#{u[4]},#{u[5]}" }.join("\n")}" }
+
+ nil
+ end
+
+ @[Security(Level::Support)]
+ def send_checkin_reminder(zones : Array(String)? = nil, timezone : String? = nil)
+ time_now = Time.utc.in(timezone ? Time::Location.load(timezone) : @time_zone)
+ time_now = time_now.at_beginning_of_day + 12.hours
+ time_now = time_now.to_local_in(Time::Location::UTC)
+
+ query_start = time_now.to_unix
+ query_end = (time_now + 30.minutes).to_unix
+
+ @check_bookings_mutex.synchronize do
+ @approval_lookup.each do |building_zone, details|
+ next if zones && !zones.includes?(building_zone)
+
+ building_name = details[:name]
+ support_email = details[:support_email]
+ attachments = (details[:attachments] || {} of String => String).compact_map { |n, l| get_attachment(n, l) }
+ building_key = building_name.downcase.gsub(' ', '_')
+
+ perform_checkin_reminder(building_zone, building_name, building_key, support_email, attachments, query_start, query_end)
+ end
+ end
+ end
+
+ protected def perform_checkin_reminder(
+ building_zone,
+ building_name,
+ building_key,
+ support_email,
+ attachments,
+ start_of_day,
+ time_now
+ )
+ bookings = staff_api.query_bookings(
+ type: @booking_type,
+ period_start: start_of_day,
+ period_end: time_now,
+ zones: [building_zone],
+ approved: true,
+ rejected: false,
+ checked_in: false
+ ).get.as_a
+
+ logger.debug { "querying for bookings requiring a reminder, start time: #{start_of_day}, end time #{time_now}" }
+ bookings = Array(Booking).from_json(bookings.to_json)
+ logger.debug { "found #{bookings.size} bookings in #{building_name} requiring a reminder" }
+
+ bookings.each do |booking_details|
+ timezone = booking_details.timezone.presence || @time_zone.name
+ location = Time::Location.load(timezone)
+
+ starting = Time.unix(booking_details.booking_start).in(location)
+ ending = Time.unix(booking_details.booking_end).in(location)
+
+ attach = attachments.first?
+
+ args = {
+ booking_id: booking_details.id,
+ start_time: starting.to_s(@time_format),
+ start_date: starting.to_s(@date_format),
+ start_datetime: starting.to_s(@date_time_format),
+ end_time: ending.to_s(@time_format),
+ end_date: ending.to_s(@date_format),
+ end_datetime: ending.to_s(@date_time_format),
+ starting_unix: booking_details.booking_start,
+
+ desk_id: booking_details.asset_id,
+ user_id: booking_details.user_id,
+ user_email: booking_details.user_email,
+ user_name: booking_details.user_name,
+ reason: booking_details.title,
+
+ level_zone: booking_details.zones.reject { |z| z == building_zone }.first?,
+ building_zone: building_zone,
+ building_name: building_name,
+ support_email: support_email,
+
+ booked_by_name: booking_details.booked_by_name,
+ booked_by_email: booking_details.booked_by_email,
+
+ attachment_name: attach.try &.[](:file_name),
+ attachment_url: attach.try &.[](:uri),
+ }
+
+ attachments.clear if @disable_attachments
+ mailer.send_template(
+ to: booking_details.user_email,
+ template: {"bookings", "checkin_reminder#{@template_suffix}"},
+ args: args,
+ attachments: attachments
+ )
+ end
+ end
+end
diff --git a/drivers/place/booking_approver.cr b/drivers/place/booking_approver.cr
new file mode 100644
index 00000000000..7430cc0aa22
--- /dev/null
+++ b/drivers/place/booking_approver.cr
@@ -0,0 +1,100 @@
+require "placeos-driver"
+require "./booking_model"
+
+class Place::BookingApprover < PlaceOS::Driver
+ descriptive_name "Booking Auto Approver"
+ generic_name :BookingApprover
+ description %(Automatically approves all PlaceOS bookings)
+
+ accessor staff_api : StaffAPI_1
+
+ default_settings({
+ approve_booking_types: ["desk"],
+ approve_zones: ["zone-12345"],
+ })
+
+ def on_load
+ monitor("staff/booking/changed") do |_subscription, payload|
+ logger.debug { "received booking changed event #{payload}" }
+ approve_booking(Booking.from_json payload)
+ end
+ on_update
+ end
+
+ @bookings_approved : Int32 = 0u32
+ @approve_zones : Array(String) = [] of String
+ @approve_booking_types : Array(String) = [] of String
+
+ def on_update
+ @approve_zones = setting?(Array(String), :approve_zones) || [] of String
+ @approve_booking_types = setting?(Array(String), :approve_booking_types) || [] of String
+
+ schedule.clear
+ schedule.every(10.minutes) { approve_missed }
+ end
+
+ # Finds the building ID for the current location services object
+ def get_building_id
+ zone_ids = staff_api.zones(tags: "building").get.as_a.map(&.[]("id").as_s)
+ (zone_ids & system.zones).first
+ rescue error
+ logger.warn(exception: error) { "unable to determine building zone id" }
+ nil
+ end
+
+ private def approve_booking(booking : Booking)
+ return if booking.action == "cancelled" || booking.rejected
+
+ if booking.action != "create"
+ booking = Booking.from_json(staff_api.get_booking(booking.id).get.to_json)
+ end
+
+ if !@approve_zones.empty?
+ if (booking.zones & @approve_zones).empty?
+ logger.debug { "Ignoring booking as no booking zone matches #{booking.id}" }
+ return false
+ end
+ end
+
+ if !@approve_booking_types.empty?
+ if !@approve_booking_types.includes?(booking.booking_type)
+ logger.debug { "Ignoring booking as booking_type #{booking.booking_type} doesn't match #{booking.id}" }
+ return false
+ end
+ end
+
+ if !booking.approved
+ # approving booking instances isn't a thing
+ staff_api.approve(booking.id).get
+ logger.debug { "Approved Booking #{booking.id}" }
+ @bookings_approved += 1
+ true
+ else
+ false
+ end
+ rescue error
+ logger.warn(exception: error) { "failed to approve booking #{booking.id}" }
+ end
+
+ def approve_missed
+ booking_type = @approve_booking_types[0]? || "desk"
+
+ bookings = Array(Booking).from_json staff_api.query_bookings(
+ type: booking_type,
+ zones: [get_building_id],
+ approved: false,
+ period_end: 8.weeks.from_now.to_unix
+ ).get.to_json
+
+ bookings.each do |booking|
+ booking.action = "create"
+ approve_booking booking
+ end
+
+ "found #{bookings.size} missed"
+ end
+
+ def status
+ {bookings_approved: @bookings_approved}
+ end
+end
diff --git a/drivers/place/booking_check_in_helper.cr b/drivers/place/booking_check_in_helper.cr
new file mode 100644
index 00000000000..6655e85a0d3
--- /dev/null
+++ b/drivers/place/booking_check_in_helper.cr
@@ -0,0 +1,417 @@
+require "placeos-driver"
+require "place_calendar"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+require "set"
+
+class Place::BookingCheckInHelper < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+
+ descriptive_name "PlaceOS Check-in helper"
+ generic_name :CheckInHelper
+ description "works in conjunction with the Bookings driver to help automate check-in"
+
+ accessor bookings : Bookings_1
+ accessor calendar : Calendar_1
+
+ def mailer
+ sys_id = @mailer_system.presence
+ sys = sys_id ? system(sys_id) : system
+ sys.implementing(Interface::Mailer)[0]
+ end
+
+ default_settings({
+ # how many minutes until we want to prompt the user
+ prompt_after: 10,
+ auto_cancel: false,
+ decline_message: "optionally use this instead of a custom email template",
+
+ # notify 3rd parties of meetings that are not used
+ _notify_staff: {
+ cc: ["email@address"],
+ mailbox: ["email@address"],
+ },
+
+ # how many minutes to wait before we enable auto-check-in
+ present_from: 5,
+ ignore_longer_than: 120,
+
+ time_zone: "Australia/Sydney",
+ date_time_format: "%c",
+ time_format: "%l:%M%p",
+ date_format: "%A, %-d %B",
+
+ # URIs for confirming or denying a meeting
+ check_in_url: "https://domain.com/meeting/check-in",
+ no_show_url: "https://domain.com/meeting/no-show",
+
+ _mailer_system: "sys-12345",
+
+ jwt_private_key: <<-STRING
+-----BEGIN RSA PRIVATE KEY-----
+MIIEpAIBAAKCAQEAt01C9NBQrA6Y7wyIZtsyur191SwSL3MjR58RIjZ5SEbSyzMG
+3r9v12qka4UtpB2FmON2vwn0fl/7i3Jgh1Xth/s+TqgYXMebdd123wodrbex5pi3
+Q7PbQFT6hhNpnsjBh9SubTf+IeTIFeXUyqtqcDBmEoT5GxU6O+Wuch2GtbfEAmaD
+roy+uyB7P5DxpKLEx8nlVYgpx5g2mx2LufHvykVnx4bFzLezU93SIEW6yjPwUmv9
+R+wDM/AOg60dIf3hCh1DO+h22aKT8D8ysuFodpLTKCToI/AbK4IYOOgyGHZ7xizX
+HYXZdsqX5/zBFXu/NOVrSd/QBYYuCxbqe6tz4wIDAQABAoIBAQCEIRxXrmXIcMlK
+36TfR7h8paUz6Y2+SGew8/d8yvmH4Q2HzeNw41vyUvvsSVbKC0HHIIfzU3C7O+Lt
+9OeiBo2vTKrwNflBv9zPDHHoerlEBLsnNwQ7uEUeTWM9DHdBLwNaLzQApLD6q5iT
+OFW4NfIGpsydIt8R565PiNPDjIcTKwhbVdlsSbI87cLkQ9UuYIMRkvXSD1Q2cg3I
+VsC0SpE4zmfTe7YTZQ5yTxtsoLKPBXrSxhhGuhdayeN7A4YHFYVD39RuQ6/T2w2a
+W/0UaGOk8XWgydDpD5w9wiBdH2I4i6D35IynCcodc5JvmTajzJT+xj6aGjjvMSyq
+q5ZdwJ4JAoGBAOPdZgjbOCf3ONUoiZ5Qw/a4b4xJgMokgqZ5QGBF5GqV1Xsphmk1
+apYmgC7fmab/EOdycrQMS0am2FmtwX1f7gYgJoyWtK4TVkUc5rf+aoWi0ieIsegv
+rjhuiIAc12+vVIbegRgnq8mOI5icrwm6OkwdqHkwTt6VRYdJGEmu67n/AoGBAM3v
+RAd5uIjVwVDLXqaOpvF3pxWfl+cf6PJtAE5y+nbabeTmrw//fJMank3o7qCXkFZR
+F0OJ2tmENwV+LPM8Gy3So8YP2nkOz4bryaGrxQ4eMA+K9+RiACVaKv+tNx/NbyMS
+e9gg504u0cwa60XjM5KUKrmT3RXpY4YIfUPZ1J4dAoGAB6jalDOiSJ2j2G57acn3
+PGTowwN5g9IEXko3IsVWr0qIGZLExOaZxaBXsLutc5KhY9ZSCsFbCm3zWdhgZ7GA
+083i3dj3C970iHA3RToVJJbbj56ltFNd/OGiTwQpLcTsB3iVSFWVDbpsceXacG5F
+JWfd0O0RyaOk6a5IVbm+jMsCgYBglxAOfY4LSE8y6SCM+K3e5iNNZhymgHYPdwbE
+xPMrWgpfab/Evi2dBcgofM+oLU663bAOspMeoP/5qJPGxnNtC7ZbSMZNL6AxBVj+
+ZoW3uHsMXz8kNL8ixecTIxiO5xlwltPVrKExL46hsCKYFhfzcWGUx4DULTLMBCFU
++M/cFQKBgQC+Ite962yJOnE+bjtSReOrvR9+I+YNGqt7vyRa2nGFxL7ZNIqHss5T
+VjaMgjzVJqqYozNT/74pE/b9UjYyMzO/EhrjUmcwriMMan/vTbYoBMYWvGoy536r
+4n455vizig2c4/sxU5yu9AF9Dv+qNsGCx2e9uUOTDUlHM9NXwxU9rQ==
+-----END RSA PRIVATE KEY-----
+STRING
+ })
+
+ @sensor_stale : Bool = false
+ @mailer_system : String? = nil
+
+ # See: https://crystal-lang.org/api/latest/Time/Format.html
+ @date_time_format : String = "%c"
+ @time_format : String = "%l:%M%p"
+ @date_format : String = "%A, %-d %B"
+ @timezone : Time::Location = Time::Location::UTC
+
+ @ignore_longer_than : Time::Span? = nil
+ protected getter! prompt_after : Time::Span
+ protected getter! present_from : Time::Span
+ @auto_cancel : Bool = false
+
+ getter? meeting_pending : Bool = false
+ getter? people_present : Bool = false
+ getter current_meeting : PlaceCalendar::Event? = nil
+
+ # This last meeting id we prompted
+ @prompted : String = ""
+
+ # The URLS we want to send to the user
+ @check_in_url : String = ""
+ @no_show_url : String = ""
+ @domain : String = ""
+
+ @jwt_private_key : String = ""
+ @decline_message : String? = nil
+ @notify_staff : Hash(String, Array(String)) = {} of String => Array(String)
+
+ def on_update
+ @jwt_private_key = setting?(String, :jwt_private_key) || ""
+ @decline_message = setting?(String, :decline_message)
+ @mailer_system = setting?(String, :mailer_system)
+
+ @notify_staff = setting?(Hash(String, Array(String)), :notify_staff) || {} of String => Array(String)
+
+ @ignore_longer_than = setting?(Int32, :ignore_longer_than).try &.minutes
+ @prompt_after = (setting?(Int32, :prompt_after) || 10).minutes
+ @present_from = (setting?(Int32, :present_from) || 5).minutes
+ @auto_cancel = setting?(Bool, :auto_cancel) || false
+
+ @check_in_url = setting?(String, :check_in_url) || ""
+ @no_show_url = setting?(String, :no_show_url) || ""
+ if @check_in_url.presence
+ @domain = URI.parse(@check_in_url).host.not_nil!
+ end
+
+ subscriptions.clear
+ bookings.subscribe(:current_booking) do |_sub, pending|
+ event = PlaceCalendar::Event?.from_json(pending)
+ update_current event
+ end
+ bookings.subscribe(:current_pending) { |_sub, pending| update_pending(pending == "true") }
+ bookings.subscribe(:sensor_stale) { |_sub, sensor_stale| update_stale_state(sensor_stale == "true") }
+ bookings.subscribe(:presence) { |_sub, presence| update_presence(presence == "true") }
+
+ monitor("#{config.control_system.not_nil!.id}/guest/bookings/prompted") do |_sub, response|
+ checkin_or_end_meeting(**NamedTuple(id: String, check_in: Bool).from_json(response))
+ end
+
+ timezone = setting?(String, :time_zone) || config.control_system.not_nil!.timezone.presence
+ @timezone = Time::Location.load(timezone) if timezone
+
+ @date_time_format = setting?(String, :date_time_format) || "%c"
+ @time_format = setting?(String, :time_format) || "%l:%M%p"
+ @date_format = setting?(String, :date_format) || "%A, %-d %B"
+ end
+
+ def ignore_long_meeting? : Bool
+ meeting = current_meeting
+ return false unless meeting
+
+ # we always want to ignore all day events
+ event_end = meeting.event_end
+ return true unless event_end
+
+ # don't ignore meetings if ignore longer than isn't set
+ ignore_length = @ignore_longer_than
+ return false unless ignore_length
+
+ # check if we're over the limit
+ meeting_length = event_end - meeting.event_start
+ meeting_length >= ignore_length
+ end
+
+ protected def update_current(meeting : PlaceCalendar::Event?)
+ logger.debug { "> checking current meeting: #{!!meeting}" }
+
+ @current_meeting = meeting
+ self[:current_meeting] = !!meeting
+ meeting ? apply_state_changes : cleanup_state
+ end
+
+ protected def update_pending(state : Bool)
+ logger.debug { "> meeting pending: #{state}" }
+ self[:meeting_pending] = @meeting_pending = state
+ state ? apply_state_changes : cleanup_state
+ end
+
+ protected def update_presence(state : Bool)
+ logger.debug { "> people present: #{state}" }
+ self[:people_present] = @people_present = state
+ apply_state_changes
+ end
+
+ protected def update_stale_state(stale : Bool)
+ @sensor_stale = stale
+ apply_state_changes
+ end
+
+ protected def cleanup_state
+ logger.debug { "cleaning up state, pending: #{@meeting_pending}, meeting: #{!!@current_meeting}" }
+ schedule.clear
+
+ meeting = current_meeting
+ if meeting.try(&.id) != @prompted
+ self[:prompted] = false
+ self[:no_show] = false
+ self[:checked_in] = false
+ self[:responded] = false
+ end
+ end
+
+ protected def apply_state_changes
+ meeting = self.current_meeting
+ return unless meeting && meeting_pending?
+
+ logger.debug { "applying state changes" }
+ schedule.clear
+
+ time_now = Time.utc
+ start_time = meeting.event_start
+ prompt_at = start_time + prompt_after
+ check_presence_from = start_time + present_from
+
+ # Schedule an auto check-in check if the sensor is stale
+ if @sensor_stale
+ logger.debug { "stale sensor detected... Scheduling meeting start" }
+ schedule.at(check_presence_from) do
+ logger.debug { "starting meeting with stale sensor" }
+ bookings.start_meeting(start_time.to_unix)
+ end
+ return
+ end
+
+ # Can we auto check-in?
+ logger.debug { "people_present? #{people_present?}" }
+ if people_present?
+ if time_now >= check_presence_from
+ logger.debug { "starting meeting!" }
+ bookings.start_meeting(start_time.to_unix)
+ else
+ # Schedule an auto check-in check as people_present? might remain high
+ logger.debug { "scheduling meeting start" }
+ schedule.at(check_presence_from) do
+ logger.debug { "starting meeting!" }
+ bookings.start_meeting(start_time.to_unix)
+ end
+ end
+ return
+ end
+
+ # don't prompt if a long meeting
+ if ignore_long_meeting?
+ logger.debug { "> ignoring meeting due to length" }
+ else
+ # should we be scheduling a prompt email?
+ if time_now >= prompt_at
+ logger.debug { "no show, prompting user" }
+ send_prompt_or_auto_cancel meeting
+ else
+ logger.debug { "scheduling no show" }
+ schedule.at(prompt_at) do
+ logger.debug { "scheduled no show, prompting user" }
+ send_prompt_or_auto_cancel meeting
+ end
+ end
+ end
+ end
+
+ def template_fields : Array(TemplateFields)
+ time_now = Time.utc.in(@timezone)
+ [
+ TemplateFields.new(
+ trigger: {"bookings", "check_in_prompt"},
+ name: "Check in prompt",
+ description: "Email template for prompting meeting hosts to check in or cancel their booking",
+ fields: [
+ {name: "jwt", description: "Authentication token for secure responses"},
+ {name: "host_email", description: "Email address of the meeting organizer"},
+ {name: "host_name", description: "Full name of the meeting organizer"},
+ {name: "event_id", description: "Unique identifier for the calendar event"},
+ {name: "system_id", description: "Unique identifier for the room/space"},
+ {name: "meeting_room_name", description: "Display name of the meeting room"},
+ {name: "meeting_summary", description: "Title or subject of the meeting"},
+ {name: "meeting_datetime", description: "Formatted date and time (e.g., #{time_now.to_s(@date_time_format)})"},
+ {name: "meeting_time", description: "Formatted time (e.g., #{time_now.to_s(@time_format)})"},
+ {name: "meeting_date", description: "Formatted date (e.g., #{time_now.to_s(@date_format)})"},
+ {name: "check_in_url", description: "URL for confirming attendance"},
+ {name: "no_show_url", description: "URL for cancelling the booking"},
+ ]
+ ),
+ ]
+ end
+
+ # decides whether to decline the event now or sends the templated email to the host asking them to end or keep it
+ protected def send_prompt_or_auto_cancel(meeting : PlaceCalendar::Event)
+ if @prompted == meeting.id
+ logger.debug { "user has already been prompted" }
+ return
+ end
+
+ present = (Float64 | Nil).from_json(bookings.people_present?.get.to_json)
+ if present.nil? || present > 0.0
+ logger.debug { "not prompting as people present or presence is unknown: #{present.inspect}" }
+ return
+ end
+
+ unless @decline_message && @auto_cancel
+ logger.debug { "prompting user about meeting room booking #{meeting.id}" }
+ begin
+ cc_list = Set(String).new(@notify_staff["cc"]? || [] of String)
+ begin
+ meeting.attendees.each do |attendee|
+ cc_list << attendee.email.downcase if attendee.organizer
+ end
+ if additional = @notify_staff[meeting.mailbox]?
+ cc_list.concat additional
+ end
+ rescue error
+ logger.warn(exception: error) { "checking for additional staff to notify" }
+ end
+ host_email = meeting.host.not_nil!.downcase
+ cc_list.delete(host_email)
+ params = generate_guest_jwt
+ mailer.send_template(host_email, {"bookings", "check_in_prompt"}, params, cc: cc_list.to_a)
+ rescue error
+ logger.warn(exception: error) { "failed to notify user" }
+ end
+ end
+
+ @prompted = meeting.id.not_nil!
+ self[:no_show] = false
+ self[:checked_in] = false
+ self[:responded] = false
+ self[:prompted] = true
+
+ checkin_or_end_meeting(meeting.id.not_nil!, false) if @auto_cancel
+ end
+
+ # actually decline the meeting now or processes the response if the user clicks one of the links in the email
+ protected def checkin_or_end_meeting(id : String, check_in : Bool)
+ meeting = current_meeting
+ unless meeting
+ logger.warn { "received response but no current meeting" }
+ return
+ end
+
+ if @prompted == meeting.id && @prompted == id
+ self[:responded] = true
+ logger.info { "host has responded with #{check_in}" }
+
+ if check_in
+ bookings.start_meeting(meeting.event_start.to_unix)
+ self[:checked_in] = true
+ elsif @decline_message
+ bookings.end_meeting(meeting.event_start.to_unix, notify: true, comment: @decline_message)
+ self[:no_show] = true
+ else
+ bookings.end_meeting(meeting.event_start.to_unix)
+ self[:no_show] = true
+ end
+ else
+ logger.warn { "received response for another meeting #{id} != #{meeting.id} or #{@prompted}" }
+ end
+ end
+
+ record FallbackUser, name : String
+
+ # generates the parameters that can be mixed into the template email
+ protected def generate_guest_jwt
+ meeting = current_meeting
+ raise "expected current meeting" unless meeting
+
+ ctrl_system = config.control_system.not_nil!
+ system_id = ctrl_system.id
+ event_id = meeting.id
+ host_email = meeting.host.not_nil!.downcase
+
+ user = meeting.attendees.find { |attendee| attendee.email.downcase == host_email }
+ begin
+ user ||= PlaceCalendar::User.from_json(calendar.get_user(host_email).get.to_json)
+ rescue
+ end
+ user ||= FallbackUser.new(host_email.split('@').first.split(/\.|_/).map(&.capitalize).join(' '))
+
+ now = Time.utc
+ starting = meeting.event_start.in(@timezone)
+ end_of_meeting = (meeting.event_end || starting.at_end_of_day).in(@timezone)
+
+ if @jwt_private_key.presence
+ payload = {
+ iss: "POS",
+ iat: now.to_unix,
+ exp: end_of_meeting.to_unix,
+ jti: UUID.random.to_s,
+ aud: @domain,
+ scope: ["guest"],
+ sub: host_email,
+ u: {
+ n: user.name,
+ e: host_email,
+ p: 0,
+ r: [event_id, system_id],
+ },
+ }
+
+ jwt = JWT.encode(payload, @jwt_private_key, JWT::Algorithm::RS256)
+ end
+
+ {
+ jwt: jwt,
+ host_email: host_email,
+ host_name: user.name,
+ event_id: event_id,
+ system_id: system_id,
+ meeting_room_name: ctrl_system.display_name.presence || ctrl_system.name,
+ meeting_summary: meeting.title,
+ meeting_datetime: starting.to_s(@date_time_format),
+ meeting_time: starting.to_s(@time_format),
+ meeting_date: starting.to_s(@date_format),
+ check_in_url: @check_in_url,
+ no_show_url: @no_show_url,
+ }
+ end
+end
diff --git a/drivers/place/booking_check_in_helper_readme.md b/drivers/place/booking_check_in_helper_readme.md
new file mode 100644
index 00000000000..04ac537113b
--- /dev/null
+++ b/drivers/place/booking_check_in_helper_readme.md
@@ -0,0 +1,66 @@
+# Booking Checkin Helper Readme
+
+Docs on how to configure the booking check-in helper.
+This helper provides a simple method for asking users if they intend to attend their meeting.
+
+* Bookings driver tracks room schedule and looks for sensors indicating if there is presence in the room
+* Sensor driver like Vergesense Room Sensor exposes room presence
+* Booking checkin helper monitors `Booking.current_pending` and `Booking.presence`
+ * auto checks in if presence found
+ * emails the host about the booking if they have not checked in
+* configuring `auto_cancel: true` will have the system decline the meeting with the `decline_message` instead of asking the host if they still intend to attend.
+
+
+## Requirements
+
+Requires the following drivers in the system
+
+* Booking - for room state
+* StaffAPI - for peoples names
+* Mailer - for querying the host if they will be using the room
+* (some sensor driver for Booking driver to obtain presence state from)
+
+Note:: to avoid having to add Mailer and StaffAPI to each system you can define a `mailer_system` setting.
+This will delegate to that system for StaffAPI and Mailers.
+
+
+## Usage
+
+The driver generates a guest JWT and listens for a signal on path `"#{control_system.id}/guest/bookings/prompted"`
+You signal via `POST /api/engine/v2/signal?channel=control_system_id/guest/bookings/prompted`
+That signal is expected to have a payload of
+```json
+{"id": "event_id", "check_in": true / false}
+```
+
+To build the email with the links to your frontend interfaces you need to create an email template:
+(email templates live on the mailer driver, this can be a dedicated SMTP driver or the Calendar driver, depending on Suncorp preferences)
+
+```yaml
+email_templates:
+ bookings:
+ check_in_prompt:
+ subject: Reminder about your meeting: %{meeting_summary}
+ html: >
+
+ click here to release your booking
+
+ click here to check-in your booking
+
+```
+
+The variables available to mix into the email template are:
+ jwt
+ host_email
+ host_name
+ event_id
+ system_id
+ meeting_room_name
+ meeting_summary
+ meeting_datetime
+ meeting_time
+ meeting_date
+ check_in_url
+ no_show_url
+
+The urls above are optional, i.e. https://corp.com/booking-confirmation from the template, if you want to configure this as a driver setting vs in the template.
diff --git a/drivers/place/booking_check_in_helper_spec.cr b/drivers/place/booking_check_in_helper_spec.cr
new file mode 100644
index 00000000000..523ccd9a89e
--- /dev/null
+++ b/drivers/place/booking_check_in_helper_spec.cr
@@ -0,0 +1,30 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::BookingCheckInHelper" do
+ system({
+ Bookings: {BookingsMock},
+ })
+
+ sleep 1
+
+ system(:Bookings_1)[:current_pending].should eq(false)
+end
+
+# :nodoc:
+class BookingsMock < DriverSpecs::MockDriver
+ def on_load
+ self[:current_booking] = {
+ event_start: 6.minutes.ago.to_unix,
+ attendees: [] of String,
+ private: false,
+ all_day: false,
+ attachments: [] of String,
+ }
+ self[:current_pending] = true
+ self[:presence] = true
+ end
+
+ def start_meeting(time : Int64)
+ self[:current_pending] = false
+ end
+end
diff --git a/drivers/place/booking_model.cr b/drivers/place/booking_model.cr
new file mode 100644
index 00000000000..14f6f0bb122
--- /dev/null
+++ b/drivers/place/booking_model.cr
@@ -0,0 +1,149 @@
+require "json"
+
+class Place::Booking
+ include JSON::Serializable
+
+ # This is to support events
+ property action : String? = nil
+
+ property id : Int64
+ property instance : Int64? = nil
+ property booking_type : String
+ property booking_start : Int64
+ property booking_end : Int64
+ property timezone : String?
+
+ # events use resource_id instead of asset_id
+ property asset_id : String?
+ property asset_ids : Array(String) = [] of String
+ property resource_id : String?
+
+ def asset_id : String
+ (@asset_id || @resource_id).as(String)
+ end
+
+ property user_id : String
+ property user_email : String
+ property user_name : String
+
+ property zones : Array(String)
+
+ property rejected : Bool?
+ property rejected_at : Int64? = nil
+ property approved : Bool?
+ property process_state : String?
+ property last_changed : Int64?
+ property created : Int64?
+
+ property approver_id : String?
+ property approver_name : String?
+ property approver_email : String?
+
+ property booked_by_id : String?
+ property booked_by_name : String
+ property booked_by_email : String
+
+ property checked_out_at : Int64? = nil
+ property deleted : Bool? = nil
+ property checked_in : Bool { false }
+ property title : String?
+ property description : String?
+
+ property extension_data : Hash(String, JSON::Any) { {} of String => JSON::Any }
+ getter recurrence_type : String? = nil
+
+ property all_day : Bool = false
+
+ def recurring?
+ @recurrence_type != "none"
+ end
+
+ def recurring_master?
+ recurring? && instance.nil?
+ end
+
+ def in_progress?
+ now = Time.utc.to_unix
+ now >= @booking_start && now < @booking_end
+ end
+
+ def changed
+ Time.unix(last_changed.not_nil!)
+ end
+
+ def expand
+ return {self}.each if asset_ids.size < 2
+
+ asset_ids.map do |aid|
+ Place::Booking.new(
+ id: id,
+ booking_type: booking_type,
+ booking_start: booking_start,
+ booking_end: booking_end,
+ user_id: user_id,
+ user_email: user_email,
+ user_name: user_name,
+ zones: zones,
+ booked_by_name: booked_by_name,
+ booked_by_email: booked_by_email,
+ action: action,
+ timezone: timezone,
+ asset_id: aid,
+ resource_id: resource_id,
+ checked_in: checked_in,
+ rejected: rejected,
+ approved: approved,
+ process_state: process_state,
+ last_changed: last_changed,
+ approver_name: approver_name,
+ approver_email: approver_email,
+ title: title,
+ description: description,
+ asset_ids: [aid],
+ created: created,
+ approver_id: approver_id,
+ booked_by_id: booked_by_id,
+ extension_data: extension_data,
+ )
+ end
+ end
+
+ def initialize(
+ @id,
+ @booking_type,
+ @booking_start,
+ @booking_end,
+ @user_id,
+ @user_email,
+ @user_name,
+ @zones,
+ @booked_by_name,
+ @booked_by_email,
+ @action = nil,
+ @timezone = nil,
+ @asset_id = nil,
+ @resource_id = nil,
+ @checked_in = nil,
+ @rejected = nil,
+ @approved = nil,
+ @process_state = nil,
+ @last_changed = nil,
+ @approver_name = nil,
+ @approver_email = nil,
+ @title = nil,
+ @description = nil,
+ @asset_ids = [] of String,
+ @created = nil,
+ @approver_id = nil,
+ @booked_by_id = nil,
+ @instance = nil,
+ @extension_data = nil,
+ )
+ asset = asset_id.presence
+ if @asset_ids.empty?
+ @asset_ids << asset if asset
+ elsif asset.nil?
+ @asset_id = @asset_ids.first
+ end
+ end
+end
diff --git a/drivers/place/booking_notifier.cr b/drivers/place/booking_notifier.cr
new file mode 100644
index 00000000000..ba301dad770
--- /dev/null
+++ b/drivers/place/booking_notifier.cr
@@ -0,0 +1,513 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+require "digest/md5"
+require "placeos"
+require "file"
+require "uuid"
+
+require "./booking_model"
+require "./password_generator_helper"
+
+class Place::BookingNotifier < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+
+ descriptive_name "Booking Notifier"
+ generic_name :BookingNotifier
+ description %(notifies users when a booking takes place)
+
+ default_settings({
+ timezone: "Australia/Sydney",
+ date_time_format: "%c",
+ time_format: "%l:%M%p",
+ date_format: "%A, %-d %B",
+ debug: false,
+
+ booking_type: "desk",
+ unique_templates: false, # This appends the booking type to the template name
+ disable_attachments: true,
+ poll_bookings: false,
+ poll_every_minutes: 5,
+
+ notify: {
+ zone_id1: {
+ name: "Sydney Building 1",
+ email: ["concierge@place.com"],
+ notify_manager: true,
+ notify_booking_owner: true,
+ include_network_credentials: false,
+ network_password_length: DEFAULT_PASSWORD_LENGTH,
+ network_password_exclude: DEFAULT_PASSWORD_EXCLUDE,
+ network_password_minimum_lowercase: DEFAULT_PASSWORD_MINIMUM_LOWERCASE,
+ network_password_minimum_uppercase: DEFAULT_PASSWORD_MINIMUM_UPPERCASE,
+ network_password_minimum_numbers: DEFAULT_PASSWORD_MINIMUM_NUMBERS,
+ network_password_minimum_symbols: DEFAULT_PASSWORD_MINIMUM_SYMBOLS,
+ network_group_ids: [] of String,
+ },
+ zone_id2: {
+ name: "Melb Building",
+ attachments: {"file-name.pdf" => "https://s3/your_file.pdf"},
+ notify_booking_owner: true,
+ },
+ },
+ })
+
+ accessor staff_api : StaffAPI_1
+ accessor network_provider : NetworkAccess_1 # Written for Cisco ISE Driver, but ideally compatible with others
+
+ # We want to use the first driver in the system that is a mailer
+
+ def mailer
+ system.implementing(Interface::Mailer)[0]
+ end
+
+ def calendar
+ system[:Calendar]
+ end
+
+ def on_load
+ # Some form of asset booking has occured
+ monitor("staff/booking/changed") { |_subscription, payload| parse_booking(payload) }
+ on_update
+ end
+
+ # See: https://crystal-lang.org/api/latest/Time/Format.html
+ @date_time_format : String = "%c"
+ @time_format : String = "%l:%M%p"
+ @date_format : String = "%A, %-d %B"
+ @time_zone : Time::Location = Time::Location.load("Australia/Sydney")
+ @debug : Bool = false
+
+ @booking_type : String = "desk"
+ @unique_templates : Bool = false
+ @template_suffix : String = ""
+ @template_fields_suffix : String = ""
+ @bookings_checked : UInt64 = 0_u64
+ @error_count : UInt64 = 0_u64
+
+ @disable_attachments : Bool = true
+ @poll_bookings : Bool = false
+ @poll_every_minutes : Int32 = 5
+
+ # Zone_id => notify settings
+ @notify_lookup : Hash(String, SiteDetails) = {} of String => SiteDetails
+
+ class SiteDetails
+ include JSON::Serializable
+
+ getter name : String
+ getter email : Array(String) { [] of String }
+ getter attachments : Hash(String, String) { {} of String => String }
+ getter notify_manager : Bool?
+ getter notify_booking_owner : Bool?
+ getter include_network_credentials : Bool?
+ getter network_password_length : Int32?
+ getter network_password_exclude : String?
+ getter network_password_minimum_lowercase : Int32?
+ getter network_password_minimum_uppercase : Int32?
+ getter network_password_minimum_numbers : Int32?
+ getter network_password_minimum_symbols : Int32?
+ getter network_group_ids : Array(String) { [] of String }
+ end
+
+ def on_update
+ @booking_type = setting?(String, :booking_type).presence || "desk"
+ @unique_templates = setting?(Bool, :unique_templates) || false
+ @template_suffix = @unique_templates ? "_#{@booking_type}" : ""
+ @template_fields_suffix = @unique_templates ? " (#{@booking_type})" : ""
+
+ time_zone = setting?(String, :calendar_time_zone).presence || "Australia/Sydney"
+ @time_zone = Time::Location.load(time_zone)
+ @date_time_format = setting?(String, :date_time_format) || "%c"
+ @time_format = setting?(String, :time_format) || "%l:%M%p"
+ @date_format = setting?(String, :date_format) || "%A, %-d %B"
+ @debug = setting?(Bool, :debug) || false
+
+ @notify_lookup = setting(Hash(String, SiteDetails), :notify)
+ attach = setting?(Bool, :disable_attachments)
+ @disable_attachments = attach.nil? ? true : !!attach
+ @poll_bookings = setting(Bool, :poll_bookings)
+ @poll_every_minutes = setting(Int32, :poll_every_minutes)
+
+ schedule.clear
+ schedule.every(@poll_every_minutes.minutes) { check_bookings } if @poll_bookings
+ end
+
+ def template_fields : Array(TemplateFields)
+ time_now = Time.utc.in(@time_zone)
+ common_fields = [
+ {name: "booking_id", description: "Unique identifier for the booking"},
+ {name: "start_time", description: "Booking start time (e.g., #{time_now.to_s(@time_format)})"},
+ {name: "start_date", description: "Booking start date (e.g., #{time_now.to_s(@date_format)})"},
+ {name: "start_datetime", description: "Booking start date and time (e.g., #{time_now.to_s(@date_time_format)})"},
+ {name: "end_time", description: "Booking end time (e.g., #{time_now.to_s(@time_format)})"},
+ {name: "end_date", description: "Booking end date (e.g., #{time_now.to_s(@date_format)})"},
+ {name: "end_datetime", description: "Booking end date and time (e.g., #{time_now.to_s(@date_time_format)})"},
+ {name: "starting_unix", description: "Booking start time as Unix timestamp"},
+ {name: "asset_id", description: "Identifier of the booked asset (e.g., desk)"},
+ {name: "user_id", description: "Identifier of the person the booking is for"},
+ {name: "user_email", description: "Email of the person the booking is for"},
+ {name: "user_name", description: "Name of the person the booking is for"},
+ {name: "reason", description: "Purpose or title of the booking"},
+ {name: "level_zone", description: "Zone identifier for the specific floor level"},
+ {name: "building_zone", description: "Zone identifier for the building"},
+ {name: "building_name", description: "Name of the building"},
+ {name: "approver_name", description: "Name of the person who approved/rejected the booking"},
+ {name: "approver_email", description: "Email of the person who approved/rejected the booking"},
+ {name: "booked_by_name", description: "Name of the person who made the booking"},
+ {name: "booked_by_email", description: "Email of the person who made the booking"},
+ {name: "attachment_name", description: "Name of any attached files"},
+ {name: "attachment_url", description: "URL to download any attachments"},
+ {name: "network_username", description: "Network access username (if configured)"},
+ {name: "network_password", description: "Generated network access password (if configured)"},
+ ]
+
+ [
+ TemplateFields.new(
+ trigger: {"bookings", "booked_by_notify#{@template_suffix}"},
+ name: "Booking booked by notification#{@template_fields_suffix}",
+ description: "Notification when someone books on behalf of another person",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "booking_notify#{@template_suffix}"},
+ name: "Booking booked notification#{@template_fields_suffix}",
+ description: "Notification when a booking is created for yourself",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"bookings", "cancelled#{@template_suffix}"},
+ name: "Booking cancelled#{@template_fields_suffix}",
+ description: "Notification when a booking is cancelled",
+ fields: common_fields
+ ),
+ ]
+ end
+
+ # Booking id => event, timestamp
+ @debounce = {} of Int64 => {String?, Int64}
+
+ protected def parse_booking(payload)
+ logger.debug { "received booking event payload: #{payload}" }
+ booking_details = Booking.from_json payload
+
+ # Only process booking types of interest
+ return unless booking_details.booking_type == @booking_type
+
+ # Ignore when a bookings state is updated
+ return unless {"approved", "cancelled"}.includes?(booking_details.action)
+
+ # Ignore the same event in a short period of time
+ previous = @debounce[booking_details.id]?
+ return if previous && previous[0] == booking_details.action
+ @debounce[booking_details.id] = {booking_details.action, Time.utc.to_unix}
+
+ building_zone, notify_details, attachments = get_building_name(booking_details.zones)
+ return unless notify_details && building_zone && attachments
+
+ building_key = notify_details.name.downcase.gsub(' ', '_')
+
+ timezone = booking_details.timezone.presence || @time_zone.name
+ location = Time::Location.load(timezone)
+
+ # https://crystal-lang.org/api/0.35.1/Time/Format.html
+ # date and time (Tue Apr 5 10:26:19 2016)
+ starting = Time.unix(booking_details.booking_start).in(location)
+ ending = Time.unix(booking_details.booking_end).in(location)
+
+ # Ignore changes to meetings that have already ended
+ return if Time.utc > ending
+
+ attach = attachments.first?
+
+ network_username = network_password = nil
+ if notify_details.include_network_credentials
+ network_username, network_password = update_network_user_password(
+ booking_details.user_email,
+ generate_password(
+ length: notify_details.network_password_length,
+ exclude: notify_details.network_password_exclude,
+ minimum_lowercase: notify_details.network_password_minimum_lowercase,
+ minimum_uppercase: notify_details.network_password_minimum_uppercase,
+ minimum_numbers: notify_details.network_password_minimum_numbers,
+ minimum_symbols: notify_details.network_password_minimum_symbols
+ ),
+ notify_details.network_group_ids
+ )
+ end
+
+ args = {
+ booking_id: booking_details.id,
+ start_time: starting.to_s(@time_format),
+ start_date: starting.to_s(@date_format),
+ start_datetime: starting.to_s(@date_time_format),
+ end_time: ending.to_s(@time_format),
+ end_date: ending.to_s(@date_format),
+ end_datetime: ending.to_s(@date_time_format),
+ starting_unix: booking_details.booking_start,
+
+ asset_id: booking_details.asset_id,
+ user_id: booking_details.user_id,
+ user_email: booking_details.user_email,
+ user_name: booking_details.user_name,
+ reason: booking_details.title,
+
+ level_zone: booking_details.zones.reject { |z| z == building_zone }.first?,
+ building_zone: building_zone,
+ building_name: notify_details.name,
+
+ approver_name: booking_details.approver_name,
+ approver_email: booking_details.approver_email,
+
+ booked_by_name: booking_details.booked_by_name,
+ booked_by_email: booking_details.booked_by_email,
+
+ attachment_name: attach.try &.[](:file_name),
+ attachment_url: attach.try &.[](:uri),
+
+ network_username: network_username,
+ network_password: network_password,
+ }
+
+ attachments.clear if @disable_attachments
+ third_party = booking_details.user_email != booking_details.booked_by_email
+
+ send_to = notify_details.email.dup
+ send_to << booking_details.user_email if notify_details.notify_booking_owner
+
+ if notify_details.notify_manager
+ email = get_manager(booking_details.user_email)
+ send_to << email if email
+ end
+
+ if booking_details.action == "approved"
+ mailer.send_template(
+ to: send_to,
+ template: {"bookings", third_party ? "booked_by_notify#{@template_suffix}" : "booking_notify#{@template_suffix}"},
+ args: args,
+ attachments: attachments
+ )
+ else
+ mailer.send_template(
+ to: send_to,
+ template: {"bookings", "cancelled#{@template_suffix}"},
+ args: args,
+ attachments: attachments
+ )
+ end
+ staff_api.booking_state(booking_details.id, "notified", booking_details.instance).get
+
+ @bookings_checked += 1
+ self[:bookings_checked] = @bookings_checked
+ rescue error
+ logger.error { error.inspect_with_backtrace }
+ self[:last_error] = {
+ error: error.message,
+ time: Time.local.to_s,
+ user: payload,
+ }
+ @error_count += 1
+ self[:error_count] = @error_count
+ end
+
+ def get_building_name(zones : Array(String))
+ zones.each do |zone_id|
+ details = @notify_lookup[zone_id]?
+ if details
+ attachments = details.attachments.compact_map { |n, l| get_attachment(n, l) }
+ logger.debug { "attaching #{attachments.size} files" }
+ return {zone_id, details, attachments}
+ end
+ end
+ {nil, nil, nil}
+ end
+
+ protected def get_attachment(filename : String, uri : String)
+ return {file_name: filename, content: "", uri: uri} if @disable_attachments
+
+ ext = filename.split('.')[-1]
+ file = Digest::MD5.base64digest(uri).gsub(/[^0-9a-zA-Z\.]/, "") + ext
+
+ # Local cache is pre-encoded
+ if File.exists?(file)
+ content = File.read(file)
+ logger.debug { "attachment saved locally #{filename} - #{content.bytesize}" }
+ return {file_name: filename, content: content, uri: uri}
+ end
+
+ # Download the file from the internet
+ buffer = IO::Memory.new
+ begin
+ buf = Bytes.new(64)
+ HTTP::Client.get(uri) do |response|
+ raise "HTTP request failed with #{response.status_code}" unless response.success?
+ body_io = response.body_io
+ while ((bytes = body_io.read(buf)) > 0)
+ buffer.write(buf[0, bytes])
+ end
+ end
+ rescue error
+ logger.warn(exception: error) { "unable to download attachment: #{uri}" }
+ return nil
+ end
+
+ encoded = Base64.strict_encode(buffer)
+ File.write file, encoded
+
+ logger.debug { "attachment downloaded #{filename} - #{encoded.bytesize}" }
+
+ {file_name: filename, content: encoded, uri: uri}
+ end
+
+ @check_bookings_mutex = Mutex.new
+
+ @[Security(Level::Support)]
+ def check_bookings(months_from_now : Int32 = 2)
+ # Clean up old debounce data
+ expired = 5.minutes.ago.to_unix
+ @debounce.reject! { |_, (_event, entered)| expired > entered }
+
+ @check_bookings_mutex.synchronize do
+ @notify_lookup.each do |building_zone, details|
+ building_name = details.name
+ email = details.email
+ attachments = details.attachments.compact_map { |n, l| get_attachment(n, l) }
+ building_key = building_name.downcase.gsub(' ', '_')
+
+ perform_booking_check(building_zone, building_name, building_key, email, details.notify_booking_owner, details.notify_manager, attachments, months_from_now)
+ end
+ end
+ end
+
+ protected def perform_booking_check(building_zone, building_name, building_key, emails, notify_owner, notify_manager, attachments, months_from_now = 2)
+ now = Time.utc.to_unix
+ later = months_from_now.months.from_now.to_unix
+
+ bookings = staff_api.query_bookings(
+ type: @booking_type,
+ period_start: now,
+ period_end: later,
+ zones: [building_zone],
+ approved: false,
+ rejected: false,
+ created_before: 2.minutes.ago.to_unix
+ ).get.as_a
+
+ bookings = bookings + staff_api.query_bookings(
+ type: @booking_type,
+ period_start: now,
+ period_end: later,
+ zones: [building_zone],
+ approved: true,
+ rejected: false,
+ created_before: 2.minutes.ago.to_unix
+ ).get.as_a
+
+ bookings = Array(Booking).from_json(bookings.to_json)
+ logger.debug { "checking #{bookings.size} requested bookings in #{building_name}" }
+ bookings.each do |booking_details|
+ next unless booking_details.process_state.nil?
+ timezone = booking_details.timezone.presence || @time_zone.name
+ location = Time::Location.load(timezone)
+ starting = Time.unix(booking_details.booking_start).in(location)
+ ending = Time.unix(booking_details.booking_end).in(location)
+
+ attach = attachments.first?
+ attachments.clear if @disable_attachments
+
+ notify_details = @notify_lookup[building_zone]
+ network_username = network_password = nil
+ if notify_details.include_network_credentials
+ network_username, network_password = update_network_user_password(
+ booking_details.user_email,
+ generate_password(
+ length: notify_details.network_password_length,
+ exclude: notify_details.network_password_exclude,
+ minimum_lowercase: notify_details.network_password_minimum_lowercase,
+ minimum_uppercase: notify_details.network_password_minimum_uppercase,
+ minimum_numbers: notify_details.network_password_minimum_numbers,
+ minimum_symbols: notify_details.network_password_minimum_symbols
+ )
+ )
+ end
+
+ args = {
+ booking_id: booking_details.id,
+ start_time: starting.to_s(@time_format),
+ start_date: starting.to_s(@date_format),
+ start_datetime: starting.to_s(@date_time_format),
+ end_time: ending.to_s(@time_format),
+ end_date: ending.to_s(@date_format),
+ end_datetime: ending.to_s(@date_time_format),
+ starting_unix: booking_details.booking_start,
+
+ asset_id: booking_details.asset_id,
+ user_id: booking_details.user_id,
+ user_email: booking_details.user_email,
+ user_name: booking_details.user_name,
+ reason: booking_details.title,
+
+ level_zone: booking_details.zones.reject { |z| z == building_zone }.first?,
+ building_zone: building_zone,
+ building_name: building_name,
+
+ booked_by_name: booking_details.booked_by_name,
+ booked_by_email: booking_details.booked_by_email,
+
+ attachment_name: attach.try &.[](:file_name),
+ attachment_url: attach.try &.[](:uri),
+
+ network_username: network_username,
+ network_password: network_password,
+ }
+
+ send_to = emails.dup
+ send_to << booking_details.user_email if notify_owner
+
+ begin
+ if notify_manager
+ email = get_manager(booking_details.user_email)
+ send_to << email if email
+ end
+
+ third_party = booking_details.user_email != booking_details.booked_by_email
+
+ mailer.send_template(
+ to: send_to,
+ template: {"bookings", third_party ? "booked_by_notify#{@template_suffix}" : "booking_notify#{@template_suffix}"},
+ args: args,
+ attachments: attachments
+ )
+ staff_api.booking_state(booking_details.id, "notified", booking_details.instance).get
+ rescue error
+ logger.error(exception: error) { "while processing booking id #{booking_details.id}" }
+ end
+ end
+ end
+
+ @[Security(Level::Support)]
+ def get_manager(staff_email : String)
+ manager = calendar.get_user_manager(staff_email).get
+ (manager["email"]? || manager["username"]).as_s
+ rescue error
+ logger.warn { "failed to email manager of #{staff_email}\n#{error.inspect_with_backtrace}" }
+ nil
+ end
+
+ def update_network_user_password(user_email : String, password : String, network_group_ids : Array(String) = [] of String)
+ # Check if they already exist
+ response = network_provider.update_internal_user_password_by_name(user_email, password).get
+ logger.debug { "Response from Network Identity provider for lookup of #{user_email} was:\n#{response}" } if @debug
+ rescue # todo: catch the specific error where the user already exists, instead of any error. Catch other errors in seperate rescue
+ # Create them if they don't already exist
+ create_network_user(user_email, password, network_group_ids)
+ else
+ {user_email, password}
+ end
+
+ def create_network_user(user_email : String, password : String, group_ids : Array(String) = [] of String)
+ response = network_provider.create_internal_user(email: user_email, name: user_email, password: password, identity_groups: group_ids).get
+ logger.debug { "Response from Network Identity provider for creating user #{user_email} was:\n #{response}\n\nDetails:\n#{response.inspect}" } if @debug
+ {response["name"], password}
+ end
+end
diff --git a/drivers/place/booking_notifier_readme.md b/drivers/place/booking_notifier_readme.md
new file mode 100644
index 00000000000..be0c6104ac5
--- /dev/null
+++ b/drivers/place/booking_notifier_readme.md
@@ -0,0 +1,97 @@
+# Booking Notifier Readme
+
+Docs on how to configure the booking notifier helper.
+This helper provides a simple way to notify users of bookings.
+
+* The notifier monitors for new asset bookings (defaults to desks)
+* periodically checks for new bookings
+* for buildings or floors, it notifies a selection of: pre-defined email addresses, the owner of the booking and / or the manager of the booking owner
+
+
+## Requirements
+
+Requires the following drivers in the system
+
+* StaffAPI - for querying bookings
+* Mailer - for sending emails, this also will be where the templates are configured
+* Calendar - for querying a users manager (only if manager notification is desired)
+
+
+## Booking Notifier Configuration
+
+```yaml
+ # How do we want dates to be formatted in the email template
+ timezone: "Australia/Sydney"
+ date_time_format: "%c"
+ time_format: "%l:%M%p"
+ date_format: "%A, %-d %B"
+
+ # What type of asset are we notifying people about
+ booking_type: "desk"
+
+ # Do we want to be emailing out attachments?
+ disable_attachments: true
+
+ # what zones are we notifying about?
+ notify: {
+ # You can configure notification settings for building and floor zones
+ zone_id1: {
+ # name of the building or floor that will be in the email template
+ name: "Sydney Building 1",
+ # optional list of emails you always want to be notified of bookings in this zone
+ email: ["concierge@place.com"],
+ # do we want to notify the booking owners manager?
+ notify_manager: true,
+ # do we want to notify the booking owner?
+ notify_booking_owner: true,
+ },
+ zone_id2: {
+ name: "Melb Building",
+ attachments: {"file-name.pdf" => "https://s3/your_file.pdf"},
+ notify_booking_owner: true,
+ },
+ }
+```
+
+
+## Template configuration on Mailer
+
+There are two templates that are expected:
+
+* `booking_notify` (the booking owner booked the asset)
+* `booked_by_notify` (someone booked on the owners behalf)
+
+```yaml
+email_templates:
+ bookings:
+ booking_notify:
+ subject: Thank you for booking a desk
+ html: >
+
+ your desk %{asset_id} has been booked for %{start_date}
+
+```
+
+The variables available to mix into the email template are:
+ booking_id
+ start_time (formatted as per Booking Notifier Configuration)
+ start_date
+ start_datetime
+ end_time
+ end_date
+ end_datetime
+ starting_unix
+ asset_id
+ user_id (where user is the booking owner)
+ user_email
+ user_name
+ reason (or booking title)
+ level_zone
+ building_zone
+ building_name
+ approver_name
+ approver_email
+ booked_by_name
+ booked_by_email
+ attachment_name
+ attachment_url
diff --git a/drivers/place/booking_notifier_spec.cr b/drivers/place/booking_notifier_spec.cr
new file mode 100644
index 00000000000..90d5759ae4f
--- /dev/null
+++ b/drivers/place/booking_notifier_spec.cr
@@ -0,0 +1,113 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/mailer"
+
+DriverSpecs.mock_driver "Place::BookingCheckInHelper" do
+ system({
+ Mailer: {MailerMock},
+ Calendar: {CalendarMock},
+ StaffAPI: {StaffAPIMock},
+ })
+
+ exec(:check_bookings).get
+
+ system(:StaffAPI)[:queries].should eq 4
+ system(:StaffAPI)[:booking_state].should eq "1--notified"
+ system(:Mailer)[:template].should eq ["bookings", "booking_notify"]
+ system(:Mailer)[:to].should eq ["concierge@place.com", "user1234@org.com", "manager@site.com"]
+end
+
+# :nodoc:
+class MailerMock < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Mailer
+
+ # need this for the interface
+ def send_mail(
+ to : String | Array(String),
+ subject : String,
+ message_plaintext : String? = nil,
+ message_html : String? = nil,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ )
+ true
+ end
+
+ # we don't have templates defined so we'll override this for testing
+ def send_template(
+ to : String | Array(String),
+ template : Tuple(String, String),
+ args : TemplateItems,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ )
+ self[:template] = template
+ self[:to] = to
+ end
+end
+
+# :nodoc:
+class CalendarMock < DriverSpecs::MockDriver
+ def get_user_manager(staff_email : String)
+ {
+ email: "manager@site.com",
+ }
+ end
+end
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ @called : Int32 = 0
+
+ def query_bookings(
+ type : String,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ rejected : Bool? = nil,
+ checked_in : Bool? = nil
+ )
+ logger.debug { "Querying desk bookings!" }
+
+ @called += 1
+ self[:queries] = @called
+ return [] of String if @called >= 2
+
+ now = Time.local
+ start = now.at_beginning_of_day.to_unix
+ ending = now.at_end_of_day.to_unix
+ [{
+ id: 1,
+ booking_type: type,
+ booking_start: start,
+ booking_end: ending,
+ asset_id: "desk-123",
+ user_id: "user-1234",
+ user_email: "user1234@org.com",
+ user_name: "Bob Jane",
+ zones: zones + ["zone-building"],
+ checked_in: true,
+ rejected: false,
+ booked_by_name: "Bob Jane",
+ booked_by_email: "user1234@org.com",
+ }]
+ end
+
+ def booking_state(booking_id : String | Int64, state : String, instance : Int64? = nil)
+ self[:booking_state] = "#{booking_id}--#{state}"
+ true
+ end
+end
diff --git a/drivers/place/bookings.cr b/drivers/place/bookings.cr
new file mode 100644
index 00000000000..ef8f14350a6
--- /dev/null
+++ b/drivers/place/bookings.cr
@@ -0,0 +1,939 @@
+require "placeos-driver"
+require "place_calendar"
+require "placeos-driver/interface/locatable"
+require "placeos-driver/interface/sensor"
+
+class Place::Bookings < PlaceOS::Driver
+ include Interface::Locatable
+
+ descriptive_name "PlaceOS Room Events"
+ generic_name :Bookings
+
+ default_settings({
+ calendar_id: nil,
+ calendar_ids: [] of String,
+ calendar_time_zone: "Australia/Sydney",
+ book_now_default_title: "Ad Hoc booking",
+ disable_book_now_host: false,
+ disable_book_now: false,
+ disable_end_meeting: true,
+ pending_period: 5,
+ pending_before: 5,
+ cache_polling_period: 5,
+ cache_days: 30,
+
+ # consider sensor data older than this unreliable.
+ sensor_stale_minutes: 8,
+
+ # as graph API is eventually consistent we want to delay syncing for a moment
+ change_event_sync_delay: 5,
+
+ control_ui: "https://if.panel/to_be_used_for_control",
+ catering_ui: "https://if.panel/to_be_used_for_catering",
+
+ application_permissions: true,
+ include_cancelled_bookings: false,
+ show_qr_code: false,
+ custom_qr_url: "https://domain.com/path",
+ custom_qr_color: "black",
+
+ # This image is displayed along with the capacity when the room is not bookable
+ room_image: "https://domain.com/room_image.svg",
+ _sensor_mac: "device-mac",
+
+ hide_meeting_details: false,
+ hide_meeting_title: false,
+ enable_end_meeting_button: false,
+ max_user_search_results: 20,
+ poll_x_seconds_after_booking: 2,
+
+ # use this to expose arbitrary fields to influx
+ # expose_for_analytics: {"binding" => "key->subkey"},
+
+ # use these for enabling push notifications
+ _push_authority: "authority-GAdySsf05",
+ # push_notification_url: "https://your.domain/api/engine/v2/notifications/google"
+ _push_notification_url: "https://your.domain/api/engine/v2/notifications/office365",
+ })
+
+ accessor calendar : Calendar_1
+
+ getter calendar_id : String = ""
+ getter calendar_ids : Array(String) = [] of String
+ @time_zone : Time::Location = Time::Location.load("Australia/Sydney")
+ @default_title : String = "Ad Hoc booking"
+ @disable_book_now : Bool = false
+ @disable_end_meeting : Bool = false
+ @pending_period : Time::Span = 5.minutes
+ @pending_before : Time::Span = 5.minutes
+ @change_event_sync_delay : UInt32 = 5_u32
+ @cache_days : Time::Span = 30.days
+ @include_cancelled_bookings : Bool = false
+ @application_permissions : Bool = false
+ @disable_book_now_host : Bool = false
+ @max_user_search_results : UInt32 = 20
+ @poll_x_seconds_after_booking : UInt32 = 2
+
+ @current_meeting_id : String = ""
+ @current_pending : Bool = false
+ @next_pending : Bool = false
+ @expose_for_analytics : Hash(String, String) = {} of String => String
+
+ @sensor_stale_minutes : Time::Span = 8.minutes
+ @perform_sensor_search : Bool = true
+ @sensor_mac : String? = nil
+
+ def on_update
+ schedule.clear
+ @calendar_id = (setting?(String, :calendar_id).presence || system.email.not_nil!).downcase
+ ids = (setting?(Array(String), :calendar_ids) || [] of String).map!(&.downcase)
+ ids.unshift @calendar_id
+ @calendar_ids = ids.uniq!
+
+ @perform_sensor_search = true
+ schedule.in(Random.rand(30).seconds + Random.rand(30_000).milliseconds) { poll_events }
+
+ cache_polling_period = (setting?(UInt32, :cache_polling_period) || 2_u32).minutes.total_milliseconds.to_i
+ cache_polling_period += Random.rand(5_000)
+ cache_random_period = cache_polling_period // 3
+ schedule.every(cache_polling_period.milliseconds) do
+ schedule.in(Random.rand(cache_random_period).milliseconds) { poll_events }
+ end
+
+ time_zone = setting?(String, :calendar_time_zone).presence || config.control_system.not_nil!.timezone.presence
+ @time_zone = Time::Location.load(time_zone) if time_zone
+
+ @default_title = setting?(String, :book_now_default_title).presence || "Ad Hoc booking"
+
+ book_now = setting?(Bool, :disable_book_now)
+ not_bookable = setting?(Bool, :not_bookable) || false
+ self[:bookable] = bookable = not_bookable ? false : system.bookable
+ @disable_book_now = book_now.nil? ? !bookable : !!book_now
+ @disable_end_meeting = !!setting?(Bool, :disable_end_meeting)
+ @disable_book_now_host = setting?(Bool, :disable_book_now_host) || false
+ @max_user_search_results = setting?(UInt32, :max_user_search_results) || 20_u32
+ @poll_x_seconds_after_booking = setting?(UInt32, :poll_x_seconds_after_booking) || 2_u32
+
+ pending_period = setting?(UInt32, :pending_period) || 5_u32
+ @pending_period = pending_period.minutes
+
+ pending_before = setting?(UInt32, :pending_before) || 5_u32
+ @pending_before = pending_before.minutes
+
+ cache_days = setting?(UInt32, :cache_days) || 30_u32
+ @cache_days = cache_days.days
+
+ @change_event_sync_delay = setting?(UInt32, :change_event_sync_delay) || 5_u32
+
+ # ensure we don't load any millisecond timestamps
+ last_started = setting?(Int64, :last_booking_started) || 0_i64
+ @last_booking_started = last_started > 30.minutes.from_now.to_unix ? 0_i64 : last_started
+
+ @include_cancelled_bookings = setting?(Bool, :include_cancelled_bookings) || false
+ @application_permissions = setting?(Bool, :application_permissions) || false
+
+ @sensor_stale_minutes = (setting?(Int32, :sensor_stale_minutes) || 8).minutes
+ @expose_for_analytics = setting?(Hash(String, String), :expose_for_analytics) || {} of String => String
+
+ # ensure current booking is updated at the start of every minute
+ # rand spreads the load placed on redis
+ schedule.cron("* * * * *") do
+ schedule.in(rand(1000).milliseconds) do
+ if list = self[:bookings]?
+ check_current_booking(list.as_a)
+ end
+ end
+ end
+
+ # configure push notifications
+ push_notificaitons_configure
+
+ # Write to redis last on the off chance there is a connection issue
+ control_sys = config.control_system.not_nil!
+ self[:room_name] = setting?(String, :room_name).presence || control_sys.display_name.presence || control_sys.name
+ self[:room_capacity] = setting?(Int32, :room_capacity) || control_sys.capacity
+ self[:default_title] = @default_title
+ self[:disable_book_now_host] = @disable_book_now_host
+ self[:disable_book_now] = @disable_book_now
+ self[:disable_end_meeting] = @disable_end_meeting
+ self[:pending_period] = pending_period
+ self[:pending_before] = pending_before
+ self[:control_ui] = setting?(String, :control_ui)
+ self[:catering_ui] = setting?(String, :catering_ui)
+ self[:room_image] = setting?(String, :room_image) || control_sys.images.try(&.first?)
+ self[:hide_meeting_details] = setting?(Bool, :hide_meeting_details) || false
+ self[:hide_meeting_title] = setting?(Bool, :hide_meeting_title) || false
+
+ self[:offline_color] = setting?(String, :offline_color)
+ self[:offline_image] = setting?(String, :offline_image)
+
+ self[:custom_qr_color] = setting?(String, :custom_qr_color)
+ self[:custom_qr_url] = setting?(String, :custom_qr_url).try do |custom_url|
+ url = custom_url.gsub("{system_id}", control_sys.id)
+ url = url.gsub("{system_email}", @calendar_id)
+ url = url.gsub("{system_email_prefix}", @calendar_id.split('@', 2)[0])
+ url = url.gsub("{system_map_id}", control_sys.map_id.as(String)) if control_sys.map_id
+ url = url.gsub("{system_code}", control_sys.code.as(String)) if control_sys.code
+ url = url.gsub("{system_type}", control_sys.type.as(String)) if control_sys.type
+ url
+ end
+
+ hide_qr_code = setting?(Bool, :hide_qr_code) || false
+ show_qr_code = setting?(Bool, :show_qr_code)
+
+ self[:show_qr_code] = show_qr_code.nil? ? !hide_qr_code : show_qr_code
+
+ self[:sensor_mac] = @sensor_mac = setting?(String, :sensor_mac)
+
+ # min and max meeting duration
+ self[:min_duration] = setting?(Int32, :min_duration) || 15
+ self[:max_duration] = setting?(Int32, :max_duration) || 480
+
+ self[:enable_end_meeting_button] = setting?(Bool, :enable_end_meeting_button) || false
+ end
+
+ # This is how we check the rooms status
+ @last_booking_started : Int64 = 0_i64
+
+ # we no longer accept user specified values
+ def start_meeting(meeting_start_time : Int64) : Nil
+ logger.warn { "deprecated function call to start_meeting, please use checkin" }
+ checkin
+ end
+
+ def checkin : Nil
+ if booking = pending || current
+ check_in_actual booking.event_start.to_unix
+ end
+ end
+
+ private def check_in_actual(meeting_start_time : Int64, check_bookings : Bool = true)
+ logger.debug { "starting meeting @ #{meeting_start_time}" }
+ @last_booking_started = meeting_start_time
+ define_setting(:last_booking_started, meeting_start_time)
+ self[:last_booking_started] = meeting_start_time
+ check_current_booking(self[:bookings].as_a) if check_bookings
+ end
+
+ # End either the current meeting early, or the pending meeting
+ def end_meeting(meeting_start_time : Int64, notify : Bool = true, comment : String = "cancelled at booking panel") : Nil
+ cmeeting = current
+ result = if cmeeting && cmeeting.event_start.to_unix == meeting_start_time
+ logger.debug { "deleting event #{cmeeting.title}, from #{@calendar_id}" }
+ calendar.decline_event(@calendar_id, cmeeting.id, notify: notify, comment: comment)
+ else
+ nmeeting = upcoming
+ if nmeeting && nmeeting.event_start.to_unix == meeting_start_time
+ logger.debug { "declining event #{nmeeting.title}, from #{@calendar_id}" }
+ calendar.decline_event(@calendar_id, nmeeting.id, notify: notify, comment: comment)
+ else
+ raise "only the current or pending meeting can be cancelled"
+ end
+ end
+ result.get
+
+ # Update booking info after creating event
+ schedule.in(1.seconds) { poll_events } unless (subscription = @subscription) && !subscription.expired?
+ end
+
+ # Allow apps to search for attendees (to add to new bookings) via driver instead of via staff-api (as some role based accounts may not have MS Graph access)
+ def list_users(query : String? = nil, limit : UInt32? = 20_u32)
+ calendar.list_users(query, limit)
+ end
+
+ def book_now(period_in_seconds : Int64, title : String? = nil, owner : String? = nil)
+ title ||= @default_title
+ starting = Time.utc.to_unix
+ ending = starting + period_in_seconds
+
+ # is the room about to be used?
+ raise "the room is currently in use" if @next_pending || status?(Bool, "in_use")
+
+ # will the next booking overlap with the room?
+ if next_booking = upcoming
+ raise "unable to book due to clash" if next_booking.event_start.to_unix < ending
+ end
+
+ logger.debug { "booking event #{title}, from #{starting}, to #{ending}, in #{@time_zone.name}, on #{@calendar_id}" }
+
+ room_email = system.email.not_nil!
+
+ if @application_permissions
+ host_calendar = @calendar_id
+ attendees = [::PlaceCalendar::Event::Attendee.new(room_email, room_email, "accepted", true, true)]
+ attendees << ::PlaceCalendar::Event::Attendee.new(owner, owner) if owner && !owner.empty?
+ else
+ host_calendar = owner.presence || @calendar_id
+ room_is_organizer = host_calendar == room_email
+ attendees = [
+ ::PlaceCalendar::Event::Attendee.new(room_email, room_email, "accepted", true, room_is_organizer),
+ ]
+ end
+
+ event = calendar.create_event(
+ title: title,
+ event_start: starting,
+ event_end: ending,
+ description: "",
+ attendees: attendees,
+ location: status?(String, "room_name"),
+ timezone: @time_zone.name,
+ calendar_id: host_calendar
+ ).get
+ # Update booking info after creating event
+ schedule.in(@poll_x_seconds_after_booking.seconds) { poll_events } unless (subscription = @subscription) && !subscription.expired?
+
+ self[:bookings] = self[:bookings].as_a << event
+ check_in_actual starting, check_bookings: true
+ event
+ end
+
+ @polling : Bool = false
+
+ def poll_events : Nil
+ return if @polling
+ @polling = true
+ check_for_sensors if @perform_sensor_search
+
+ now = Time.local @time_zone
+ start_of_day = now.at_beginning_of_day.to_unix
+ cache_period = start_of_day + @cache_days.to_i
+
+ events = @calendar_ids.flat_map { |cal_id|
+ logger.debug { "polling events #{cal_id}, from #{start_of_day}, to #{cache_period}, in #{@time_zone.name}" }
+
+ calendar.list_events(
+ cal_id,
+ start_of_day,
+ cache_period,
+ @time_zone.name,
+ include_cancelled: @include_cancelled_bookings
+ ).get.as_a.map do |evt|
+ visibility = if evt["private"].as_bool?
+ "private"
+ else
+ evt["visibility"]?.try &.as_s?.try &.downcase || "normal"
+ end
+ if visibility == "private"
+ evt.as_h["title"] = JSON::Any.new("Private")
+ evt.as_h["host"] = JSON::Any.new("Private")
+ elsif visibility == "personal"
+ evt.as_h["title"] = evt["host"]
+ elsif visibility == "confidential"
+ evt.as_h["title"] = JSON::Any.new("Confidential")
+ evt.as_h["host"] = JSON::Any.new("Confidential")
+ end
+ evt
+ end
+ }.sort { |a, b| a["event_start"].as_i64 <=> b["event_start"].as_i64 }
+
+ self[:bookings] = events
+ check_current_booking(events)
+ events
+ ensure
+ @polling = false
+ end
+
+ protected def check_current_booking(bookings) : Nil
+ now = Time.utc.to_unix
+ previous_booking = nil
+ current_booking = nil
+ next_booking = Int32::MAX
+
+ bookings.each_with_index do |event, index|
+ starting = event["event_start"].as_i64
+
+ # All meetings are in the future
+ if starting > now
+ next_booking = index
+ previous_booking = index - 1 if index > 0
+ break
+ end
+
+ # Calculate event end time
+ ending_unix = if ending = event["event_end"]?
+ ending.as_i64
+ else
+ starting + 24.hours.to_i
+ end
+
+ # Event ended in the past
+ next if ending_unix < now
+
+ # We've found the current event
+ if starting <= now && ending_unix > now
+ current_booking = index
+ previous_booking = index - 1 if index > 0
+ next_booking = index + 1
+ break
+ end
+ end
+
+ self[:previous_booking] = previous_booking ? bookings[previous_booking] : nil
+
+ # Configure room status (free, pending, in-use)
+ current_pending = false
+ next_pending = false
+ booked = false
+
+ if current_booking
+ booking = bookings[current_booking]
+ start_time = booking["event_start"].as_i64
+ ending_at = booking["event_end"]?
+ booked = true
+
+ # Up to the frontend to delete pending bookings that have past their start time
+ if !@disable_end_meeting
+ if start_time > @last_booking_started
+ if sensor_stale? || status?(Bool, "presence")
+ check_in_actual(start_time, check_bookings: false)
+ else
+ current_pending = true
+ end
+ end
+ elsif @pending_period.to_i > 0_i64
+ pending_limit = (Time.unix(start_time) + @pending_period).to_unix
+ current_pending = true if start_time < pending_limit && start_time > @last_booking_started
+ end
+
+ self[:current_booking] = booking
+ self[:host_email] = booking["extension_data"]?.try(&.[]?("host_override")) || booking["host"]?
+ self[:started_at] = start_time
+ self[:ending_at] = ending_at ? ending_at.as_i64 : (start_time + 24.hours.to_i)
+ self[:all_day_event] = !ending_at
+ self[:event_id] = booking["id"]?
+
+ @expose_for_analytics.each do |binding, path|
+ begin
+ binding_keys = path.split("->")
+ data = booking
+ binding_keys.each do |key|
+ data = data.dig? key
+ break unless data
+ end
+ self[binding] = data
+ rescue error
+ logger.warn(exception: error) { "failed to expose #{binding}: #{path} for analytics" }
+ self[binding] = nil
+ end
+ end
+
+ previous_booking_id = @current_meeting_id
+ new_booking_id = booking["id"].as_s
+ schedule.in(1.second) { check_for_sensors } unless new_booking_id == previous_booking_id
+ @current_meeting_id = new_booking_id
+ else
+ self[:current_booking] = nil
+ self[:host_email] = nil
+ self[:started_at] = nil
+ self[:ending_at] = nil
+ self[:all_day_event] = nil
+ self[:event_id] = nil
+
+ @expose_for_analytics.each_key do |binding|
+ self[binding] = nil
+ end
+ end
+
+ # We haven't checked the index of `next_booking` exists, hence the `[]?`
+ if booking = bookings[next_booking]?
+ start_time = booking["event_start"].as_i64
+
+ # is the next meeting pending?
+ if start_time <= @pending_before.from_now.to_unix
+ # if start time is greater than last started, then no one has checked in yet
+ if start_time > @last_booking_started
+ next_pending = true
+ else
+ booked = true
+ end
+ end
+
+ # don't display upcoming bookings if they are a long way off
+ if start_time < 10.hours.from_now.to_unix
+ self[:next_booking] = booking
+ self[:next_host] = booking["extension_data"]?.try(&.[]?("host_override")) || booking["host"]?
+ else
+ self[:next_booking] = nil
+ self[:next_host] = nil
+ end
+ else
+ self[:next_booking] = nil
+ self[:next_host] = nil
+ end
+
+ self[:booked] = booked
+
+ # Check if pending is enabled
+ if @pending_period.to_i > 0_i64 || @pending_before.to_i > 0_i64
+ self[:current_pending] = @current_pending = current_pending
+ self[:next_pending] = @next_pending = next_pending
+ self[:pending] = current_pending || next_pending
+
+ self[:in_use] = booked && !current_pending
+ else
+ self[:current_pending] = @current_pending = current_pending = false
+ self[:next_pending] = @next_pending = next_pending = false
+ self[:pending] = false
+
+ self[:in_use] = booked
+ end
+
+ # TODO:: set video_conference_url if found in the event details
+
+ self[:status] = (current_pending || next_pending) ? "pending" : (booked ? "busy" : "free")
+ end
+
+ protected def current : ::PlaceCalendar::Event?
+ status?(::PlaceCalendar::Event, :current_booking)
+ end
+
+ protected def upcoming : ::PlaceCalendar::Event?
+ status?(::PlaceCalendar::Event, :next_booking)
+ end
+
+ protected def pending : ::PlaceCalendar::Event?
+ if @current_pending
+ current
+ elsif @next_pending
+ upcoming
+ end
+ end
+
+ # ===================================
+ # Locatable Interface functions
+ # ===================================
+ protected def to_location_format(events : Enumerable(::PlaceCalendar::Event))
+ sys = system.config
+ events.map do |event|
+ event_ends = event.all_day? ? event.event_start.in(@time_zone).at_end_of_day : event.event_end.not_nil!
+ {
+ location: :meeting,
+ mac: @calendar_id,
+ event_id: event.id,
+ map_id: sys.map_id,
+ sys_id: sys.id,
+ ends_at: event_ends.to_unix,
+ started_at: event.event_start.to_unix,
+ private: !!event.private?,
+ }
+ end
+ end
+
+ def locate_user(email : String? = nil, username : String? = nil)
+ logger.debug { "searching for #{email}, #{username}" }
+
+ email = email.to_s.downcase
+ username = username.to_s.downcase
+ matching_events = [] of ::PlaceCalendar::Event
+
+ if event = current
+ emails = event.attendees.map(&.email.downcase)
+ if host = event.host
+ emails << host.downcase
+ end
+
+ if emails.includes?(email) || emails.includes?(username)
+ logger.debug { "found user {#{email}, #{username}} in list of attendees" }
+ matching_events << event
+ elsif !username.empty? && emails.find(&.starts_with?(username))
+ logger.debug { "found email starting with username '#{username}' in list of attendees" }
+ matching_events << event
+ end
+ end
+
+ to_location_format matching_events
+ end
+
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ locate_user(email, username).map(&.[](:mac))
+ end
+
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ logger.debug { "searching for owner of #{mac_address}" }
+ sys_email = @calendar_id.downcase
+ if sys_email == mac_address.downcase && (host = current.try &.host)
+ {
+ location: "meeting",
+ assigned_to: host,
+ mac_address: sys_email,
+ }
+ end
+ end
+
+ def device_locations(zone_id : String, location : String? = nil)
+ logger.debug { "searching devices in zone #{zone_id}" }
+ [] of Nil
+ end
+
+ def people_count? : Float64?
+ drivers = system.implementing(Interface::Sensor)
+ count_data = drivers.sensors("people_count", @sensor_mac).get.flat_map(&.as_a).first?
+
+ return nil unless count_data
+ return nil if is_stale?(count_data["last_seen"]?.try &.as_i64)
+
+ data = count_data["value"]
+ (data.as_f? || data.as_i).to_f
+ rescue error
+ logger.warn(exception: error) { "error checking people count" }
+ nil
+ end
+
+ def people_present? : Float64?
+ count = people_count?
+ return count > 0.0 ? 1.0 : 0.0 if count
+
+ drivers = system.implementing(Interface::Sensor)
+ presence_data = drivers.sensors("presence", @sensor_mac).get.flat_map(&.as_a).first?
+
+ return nil unless presence_data
+ return nil if is_stale?(presence_data["last_seen"]?.try &.as_i64)
+
+ data = presence_data["value"]
+ (data.as_f? || data.as_i).to_f > 0.0 ? 1.0 : 0.0
+ rescue error
+ logger.warn(exception: error) { "error checking people presence" }
+ nil
+ end
+
+ @sensor_subscription : PlaceOS::Driver::Subscriptions::Subscription? = nil
+
+ protected def check_for_sensors
+ @perform_sensor_search = true
+ drivers = system.implementing(Interface::Sensor)
+
+ if sub = @sensor_subscription
+ subscriptions.unsubscribe(sub)
+ @sensor_subscription = nil
+ end
+
+ # Prefer people count data in a space
+ count_data = drivers.sensors("people_count", @sensor_mac).get.flat_map(&.as_a).first?
+
+ if count_data && count_data["module_id"]?.try(&.raw.is_a?(String))
+ if !is_stale?(count_data["last_seen"]?.try &.as_i64)
+ self[:sensor_name] = count_data["name"].as_s
+
+ # the binding might be multiple layers deep
+ binding_keys = count_data["binding"].as_s.split("->")
+ binding = binding_keys.shift
+ @sensor_subscription = subscriptions.subscribe(count_data["module_id"].as_s, binding) do |_sub, payload|
+ data = JSON.parse payload
+ binding_keys.each do |key|
+ data = data.dig? key
+ break unless data
+ end
+ value = data ? (data.as_f? || data.as_i).to_f : nil
+ if value
+ self[:people_count] = value
+ self[:presence] = value > 0.0
+ else
+ self[:people_count] = self[:presence] = nil
+ end
+ end
+ @perform_sensor_search = false
+ end
+ end
+
+ # a people count sensor was stale or not found
+ if @perform_sensor_search
+ self[:people_count] = nil
+
+ # Fallback to checking for presence
+ presence = drivers.sensors("presence", @sensor_mac).get.flat_map(&.as_a).first?
+ if presence && presence["module_id"]?.try(&.raw.is_a?(String))
+ if !is_stale?(presence["last_seen"]?.try &.as_i64)
+ self[:sensor_name] = presence["name"].as_s
+
+ # the binding might be multiple layers deep
+ binding_keys = presence["binding"].as_s.split("->")
+ binding = binding_keys.shift
+ @sensor_subscription = subscriptions.subscribe(presence["module_id"].as_s, binding) do |_sub, payload|
+ data = JSON.parse payload
+ binding_keys.each do |key|
+ data = data.dig? key
+ break unless data
+ end
+ value = data ? (data.as_f? || data.as_i).to_f : nil
+ self[:presence] = value ? value > 0.0 : nil
+ end
+ @perform_sensor_search = false
+ else
+ self[:sensor_name] = self[:presence] = nil
+ @perform_sensor_search = true
+ end
+ end
+ end
+ rescue error
+ @perform_sensor_search = true
+ logger.error(exception: error) { "checking for sensors" }
+ self[:people_count] = nil
+ self[:presence] = nil
+ self[:sensor_name] = nil
+ self[:sensor_stale] = true
+ end
+
+ protected def is_stale?(timestamp : Int64?) : Bool
+ if timestamp.nil?
+ return self[:sensor_stale] = false
+ end
+
+ sensor_time = Time.unix(timestamp)
+ stale_time = @sensor_stale_minutes.ago
+
+ if sensor_time > stale_time
+ self[:sensor_stale] = false
+ else
+ @perform_sensor_search = true
+ self[:sensor_stale] = true
+ end
+ end
+
+ def sensor_stale? : Bool
+ status?(Bool, "sensor_stale") || false
+ end
+
+ enum ServiceName
+ Google
+ Office365
+ end
+
+ enum NotifyType
+ # resource event changes
+ Created # a resource was created (MS only)
+ Updated # a resource was updated (in Google this could also mean created)
+ Deleted # a resource was deleted
+
+ # subscription lifecycle event (MS only)
+ Renew # subscription was deleted
+ Missed # MS sends this to mean resource event changes were not sent
+ Reauthorize # subscription needs reauthorization
+ end
+
+ struct NotifyEvent
+ include JSON::Serializable
+
+ getter event_type : NotifyType
+ getter resource_id : String?
+ getter resource_uri : String
+ getter subscription_id : String
+ getter client_secret : String
+
+ @[JSON::Field(converter: Time::EpochConverter)]
+ getter expiration_time : Time
+ end
+
+ # TODO:: remove in the future
+ struct ::PlaceCalendar::Subscription
+ @client_secret : String | Int64?
+
+ def client_secret
+ @client_secret.to_s
+ end
+
+ def expired?
+ if time = expires_at
+ 1.hour.from_now >= time
+ else
+ false
+ end
+ end
+ end
+
+ @subscription : ::PlaceCalendar::Subscription? = nil
+ @push_notification_url : String? = nil
+ @push_authority : String? = nil
+ @push_service_name : ServiceName? = nil
+ @push_monitoring : PlaceOS::Driver::Subscriptions::ChannelSubscription? = nil
+ @push_mutex : Mutex = Mutex.new(:reentrant)
+
+ # the API reports that 6 days is the max:
+ # Subscription expiration can only be 10070 minutes in the future.
+ SUBSCRIPTION_LENGTH = 3.hours
+
+ protected def push_notificaitons_configure
+ @push_notification_url = setting?(String, :push_notification_url).presence
+ @push_authority = setting?(String, :push_authority).presence
+
+ # load any existing subscriptions
+ subscription = setting?(::PlaceCalendar::Subscription, :push_subscription)
+
+ if @push_notification_url
+ # clear the monitoring if authority changed
+ if subscription && subscription.try(&.id) != @subscription.try(&.id) && (monitor = @push_monitoring)
+ subscriptions.unsubscribe(monitor)
+ @push_monitoring = nil
+ end
+ @subscription = subscription
+ schedule.every(5.minutes + rand(120).seconds) { push_notificaitons_maintain }
+ schedule.in(rand(30).seconds) { push_notificaitons_maintain(true) }
+ elsif subscription
+ push_notificaitons_cleanup(subscription)
+ end
+ end
+
+ # delete a subscription
+ protected def push_notificaitons_cleanup(sub)
+ @push_mutex.synchronize do
+ logger.debug { "removing subscription" }
+
+ calendar.delete_notifier(sub) if sub
+ @subscription = nil
+ define_setting(:push_subscription, nil)
+ end
+ end
+
+ getter sub_renewed_at : Time = 21.minutes.ago
+
+ # creates and maintains a subscription
+ protected def push_notificaitons_maintain(force_renew = false) : Nil
+ should_force = force_renew && @sub_renewed_at < 20.minutes.ago
+
+ @push_mutex.synchronize do
+ subscription = @subscription
+
+ logger.debug { "maintaining push subscription, monitoring: #{!!@push_monitoring}, subscription: #{subscription ? !subscription.expired? : "none"}" }
+
+ return create_subscription unless subscription
+
+ if should_force || subscription.expired?
+ # renew subscription
+ begin
+ logger.debug { "renewing subscription" }
+ expires = SUBSCRIPTION_LENGTH.from_now
+ sub = calendar.renew_notifier(subscription, expires.to_unix).get
+ @subscription = ::PlaceCalendar::Subscription.from_json(sub.to_json)
+
+ # save the subscription details for processing
+ define_setting(:push_subscription, @subscription)
+ @sub_renewed_at = Time.local
+ rescue error
+ logger.error(exception: error) { "failed to renew expired subscription, creating new subscription" }
+ @subscription = nil
+ schedule.in(1.second) { push_notificaitons_maintain; nil }
+ end
+
+ configure_push_monitoring
+ return
+ end
+
+ configure_push_monitoring if @push_monitoring.nil?
+ end
+ end
+
+ protected def configure_push_monitoring
+ subscription = @subscription.as(::PlaceCalendar::Subscription)
+ channel_path = "#{subscription.id}/event"
+
+ if old = @push_monitoring
+ subscriptions.unsubscribe old
+ end
+
+ @push_monitoring = monitor(channel_path) { |_subscription, payload| push_event_occured(payload) }
+ logger.debug { "monitoring channel: #{channel_path}" }
+ end
+
+ protected def push_event_occured(payload : String)
+ logger.debug { "push notification received! #{payload}" }
+
+ notification = NotifyEvent.from_json payload
+
+ secret = @subscription.try &.client_secret
+ unless secret && secret == notification.client_secret
+ logger.warn { "ignoring notify event with mismatched secret: #{notification.inspect}" }
+ return
+ end
+
+ case notification.event_type
+ in .created?, .updated?, .deleted?
+ logger.debug { "polling events as received #{notification.event_type} notification" }
+ if resource_id = notification.resource_id
+ self[:last_event_notification] = {notification.event_type, resource_id, Time.utc.to_unix}
+ end
+
+ # fetch the event from the calendar and signal to staff API
+ # staff-api will:
+ # * notify change
+ # * which will link_master_metadata
+ begin
+ event = calendar.get_event(
+ @calendar_id,
+ notification.resource_id
+ ).get unless notification.event_type.deleted?
+
+ publish("#{@push_authority}/bookings/event", {
+ event_id: notification.resource_id,
+ change: notification.event_type,
+ system_id: system.id,
+ event: event,
+ }.to_json)
+ rescue error
+ logger.warn(exception: error) { "fetching booking event on change notification" }
+ nil
+ end
+
+ poll_events
+ in .missed?
+ # we don't know the exact event id that changed
+ logger.debug { "polling events as a notification was previously missed" }
+ poll_events
+ in .renew?
+ # we need to create a new subscription as the old one has expired
+ logger.debug { "a subscription renewal is required" }
+ create_subscription
+ in .reauthorize?
+ logger.debug { "a subscription reauthorization is required" }
+ expires = SUBSCRIPTION_LENGTH.from_now
+ calendar.reauthorize_notifier(@subscription, expires.to_unix)
+ end
+ rescue error
+ logger.error(exception: error) { "error processing push notification" }
+ end
+
+ protected def create_subscription
+ @push_mutex.synchronize do
+ @push_service_name = service_name = @push_service_name || ServiceName.parse(calendar.calendar_service_name.get.as_s)
+
+ # different resource routes for the different services
+ case service_name
+ in .google?
+ resource = "/calendars/#{calendar_id}/events"
+ in .office365?
+ resource = "/users/#{calendar_id}/events"
+ in Nil
+ raise "service name not known, waiting for "
+ end
+
+ logger.debug { "registering for push notifications! #{resource}" }
+
+ # create a new secret and subscription
+ expires = SUBSCRIPTION_LENGTH.from_now
+ push_secret = "a#{Random.new.hex(4)}"
+ sub = calendar.create_notifier(resource, @push_notification_url, expires.to_unix, push_secret, @push_notification_url).get
+ @subscription = ::PlaceCalendar::Subscription.from_json(sub.to_json)
+
+ # save the subscription details for processing
+ define_setting(:push_subscription, @subscription)
+ @sub_renewed_at = Time.local
+
+ configure_push_monitoring
+ end
+ end
+
+ # =======================================
+ # Helper for detecting invalid config
+ # =======================================
+
+ def syllabus_plus_resource_check
+ sleep rand(10_000).milliseconds
+ @calendar_ids.each do |cal_id|
+ resource_id = cal_id.split('@')[0]
+ begin
+ calendar.resource_lookup(resource_id).get
+ rescue error
+ logger.error(exception: error) { "invalid syllabus plus resource id #{resource_id} in #{config.control_system.not_nil!.name}" }
+ end
+ end
+ end
+end
diff --git a/drivers/place/bookings/asset_name_resolver.cr b/drivers/place/bookings/asset_name_resolver.cr
new file mode 100644
index 00000000000..717e85463cc
--- /dev/null
+++ b/drivers/place/bookings/asset_name_resolver.cr
@@ -0,0 +1,85 @@
+require "json"
+require "./locker_models"
+
+module Place::AssetNameResolver
+ include Place::LockerMetadataParser
+
+ @asset_cache : AssetCache = AssetCache.new
+ @asset_cache_timeout : Int64 = 3600_i64 # 1 hour
+
+ private getter asset_cache : AssetCache
+
+ private def clear_asset_cache
+ @asset_cache = AssetCache.new
+ end
+
+ private def lookup_asset(asset_id : String, type : String, zones : Array(String) = [building_id]) : String
+ if type == "locker"
+ locker = locker_details[asset_id]?
+ return locker.name if locker
+ else
+ zones.each do |zone_id|
+ asset = if (cache = asset_cache[{zone_id, type}]?) && cache[0] > Time.utc.to_unix
+ cache[1].find { |asset| asset.id == asset_id }
+ else
+ assets = lookup_assets(zone_id, type)
+ @asset_cache[{zone_id, type}] = {Time.utc.to_unix + @asset_cache_timeout, assets}
+ assets.find { |asset| asset.id == asset_id }
+ end
+
+ return asset.name if asset
+ end
+ end
+
+ logger.debug { "unable to resolve asset name for #{asset_id}" }
+ asset_id
+ end
+
+ private def lookup_assets(zone_id : String, type : String) : Array(Asset)
+ assets = [] of Asset
+
+ metadata_field = case type
+ when "desk"
+ "desks"
+ when "parking"
+ "parking-spaces"
+ end
+
+ if metadata_field
+ metadata = Metadata.from_json staff_api.metadata(zone_id, metadata_field).get[metadata_field].to_json
+ assets = metadata.details.as_a.map { |asset| Asset.from_json asset.to_json }
+ elsif type == "locker"
+ assets = locker_details.map { |id, locker| Asset.new(id, locker.name) }
+ end
+
+ assets
+ rescue error
+ logger.debug { "unable to get #{metadata_field} from zone #{zone_id} metadata" }
+ [] of Asset
+ end
+
+ # zone_id, type timeout, assets
+ alias AssetCache = Hash(Tuple(String, String), Tuple(Int64, Array(Asset)))
+
+ struct Asset
+ include JSON::Serializable
+
+ property id : String
+ property name : String
+
+ def initialize(@id : String, @name : String)
+ end
+ end
+
+ struct Metadata
+ include JSON::Serializable
+
+ property name : String
+ property description : String = ""
+ property details : JSON::Any
+ property parent_id : String
+ property schema_id : String? = nil
+ property editors : Set(String) = Set(String).new
+ property modified_by_id : String? = nil
+ end
+end
diff --git a/drivers/place/bookings/auto_desk_checkin.cr b/drivers/place/bookings/auto_desk_checkin.cr
new file mode 100644
index 00000000000..37455f289f2
--- /dev/null
+++ b/drivers/place/bookings/auto_desk_checkin.cr
@@ -0,0 +1,49 @@
+require "placeos-driver"
+
+class Place::AutoDeskCheckin < PlaceOS::Driver
+ descriptive_name "Auto Desk Checkin"
+ generic_name :AutoDeskCheckin
+ description %(automatically checks in desks that will be in use in the near future)
+
+ accessor staff_api : StaffAPI_1
+
+ default_settings({
+ check_in_zones: ["zone-id1", "zone-id2"],
+ hours_before_booking_start: 1,
+ booking_category: "desk",
+ })
+
+ @time_period : Time::Span = 1.hour
+ @booking_category : String = "desk"
+ @zones : Array(String) = [] of String
+
+ def on_update
+ @zones = setting(Array(String), :check_in_zones)
+ @time_period = setting(Int32, :hours_before_booking_start).hours
+ @booking_category = setting(String, :booking_category)
+
+ schedule.clear
+ schedule.every(5.minutes) { fetch_and_check_in }
+ end
+
+ def fetch_and_check_in
+ period_start = Time.utc.to_unix
+ period_end = @time_period.from_now.to_unix
+ booking_ids = staff_api.query_bookings(@booking_category, period_start, period_end, @zones, checked_in: false).get.as_a.map { |booking| booking["id"].as_i64 }
+
+ success = 0
+ failed = [] of Int64
+
+ booking_ids.each do |id|
+ begin
+ staff_api.booking_check_in(id, true, "auto-checkin").get
+ success += 1
+ rescue error
+ failed << id
+ logger.debug(exception: error) { "failed to check-in booking #{id}" }
+ end
+ end
+
+ "checked-in #{success} bookings, failed #{failed.size}: #{failed}"
+ end
+end
diff --git a/drivers/place/bookings/auto_desk_checkin_spec.cr b/drivers/place/bookings/auto_desk_checkin_spec.cr
new file mode 100644
index 00000000000..4657f7624a0
--- /dev/null
+++ b/drivers/place/bookings/auto_desk_checkin_spec.cr
@@ -0,0 +1,41 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::EventAttendanceRecorder" do
+ system({
+ StaffAPI: {StaffAPIMock},
+ })
+
+ # Start a new meeting
+ exec(:fetch_and_check_in).get.should eq "checked-in 2 bookings, failed 1: [3]"
+end
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ def query_bookings(
+ type : String,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ rejected : Bool? = nil,
+ checked_in : Bool? = nil
+ )
+ [{id: 1}, {id: 2}, {id: 3}]
+ end
+
+ def booking_check_in(booking_id : String | Int64, state : Bool = true, utm_source : String? = nil)
+ logger.debug { "checking in booking #{booking_id} to: #{state} from #{utm_source}" }
+
+ case booking_id
+ when 3
+ raise "issue updating booking state #{booking_id}: 404"
+ else
+ true
+ end
+ end
+end
diff --git a/drivers/place/bookings/booking_checkin_notifier.cr b/drivers/place/bookings/booking_checkin_notifier.cr
new file mode 100644
index 00000000000..3c9b8949cd3
--- /dev/null
+++ b/drivers/place/bookings/booking_checkin_notifier.cr
@@ -0,0 +1,171 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+require "../booking_model"
+
+class Place::BookingCheckinNotifier < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+
+ descriptive_name "Booking checkin notifier"
+ generic_name :BookingCheckinNotifier
+ description %(notifies information by email when bookings are checked in)
+
+ default_settings({
+ notify_address: "mailing_list@org.com",
+ date_time_format: "%c",
+ time_format: "%l:%M%p",
+ date_format: "%A, %-d %B",
+ determine_host_name_using: "calendar-driver",
+ booking_type: "parking",
+ _zone_override: "booking zone id",
+ })
+
+ accessor calendar : Calendar_1
+ accessor staff_api : StaffAPI_1
+ accessor locations : LocationServices_1
+
+ def mailer
+ system.implementing(Interface::Mailer)[0]
+ end
+
+ def on_load
+ monitor("staff/booking/changed") { |_subscription, payload| parse_booking(payload) }
+ on_update
+ end
+
+ # See: https://crystal-lang.org/api/latest/Time/Format.html
+ @date_time_format : String = "%c"
+ @time_format : String = "%l:%M%p"
+ @date_format : String = "%A, %-d %B"
+ @zone_override : String? = nil
+ @booking_type : String = "parking"
+ @bookings_checked : UInt64 = 0_u64
+ @notify_address : String = ""
+
+ def on_update
+ @building_id = nil
+ @building = nil
+ @building_name = nil
+ @zone_override = setting?(String, :zone_override)
+
+ @notify_address = setting(String, :notify_address)
+ @date_time_format = setting?(String, :date_time_format) || "%c"
+ @time_format = setting?(String, :time_format) || "%l:%M%p"
+ @date_format = setting?(String, :date_format) || "%A, %-d %B"
+ @booking_type = setting?(String, :booking_type).presence || "parking"
+ end
+
+ getter building_id : String do
+ locations.building_id.get.as_s
+ end
+
+ getter building : JSON::Any do
+ staff_api.zone(building_id).get
+ end
+
+ getter building_name : String do
+ building["name"].as_s
+ end
+
+ # system or building timezone
+ protected getter timezone : Time::Location do
+ tz = config.control_system.try(&.timezone) || building["timezone"].as_s
+ Time::Location.load(tz)
+ end
+
+ protected def parse_booking(payload)
+ booking_details = Booking.from_json payload
+
+ # Only process booking types of interest
+ return unless booking_details.booking_type == @booking_type
+
+ # We only care for checked in
+ return unless booking_details.action == "checked_in"
+
+ # in a particular zone
+ return unless booking_details.zones.includes?(@zone_override || building_id)
+
+ logger.debug { "received checked_in event payload:\n#{payload}" }
+ notify_check_in booking_details
+ end
+
+ protected def notify_check_in(booking_details)
+ # https://crystal-lang.org/api/0.35.1/Time/Format.html
+ # date and time (Tue Apr 5 10:26:19 2016)
+ location = timezone
+ starting = Time.unix(booking_details.booking_start).in(location)
+ ending = Time.unix(booking_details.booking_end).in(location)
+
+ # Ignore changes to meetings that have already ended
+ return if Time.utc > ending
+
+ args = {
+ booking_id: booking_details.id,
+ start_time: starting.to_s(@time_format),
+ start_date: starting.to_s(@date_format),
+ start_datetime: starting.to_s(@date_time_format),
+ end_time: ending.to_s(@time_format),
+ end_date: ending.to_s(@date_format),
+ end_datetime: ending.to_s(@date_time_format),
+ starting_unix: booking_details.booking_start,
+
+ asset_id: booking_details.asset_id,
+ user_id: booking_details.user_id,
+ user_email: booking_details.user_email,
+ user_name: booking_details.user_name,
+ reason: booking_details.title,
+
+ building_zone: building_id,
+ building_name: building_name,
+
+ approver_name: booking_details.approver_name,
+ approver_email: booking_details.approver_email,
+
+ booked_by_name: booking_details.booked_by_name,
+ booked_by_email: booking_details.booked_by_email,
+ }
+
+ mailer.send_template(
+ to: @notify_address,
+ template: {"bookings", "check_in_notifier"},
+ args: args
+ )
+
+ @bookings_checked += 1
+ self[:bookings_checked] = @bookings_checked
+ end
+
+ def template_fields : Array(TemplateFields)
+ time_now = Time.utc.in(timezone)
+ common_fields = [
+ {name: "booking_id", description: "Unique identifier for the booking"},
+ {name: "start_time", description: "Booking start time (e.g., #{time_now.to_s(@time_format)})"},
+ {name: "start_date", description: "Booking start date (e.g., #{time_now.to_s(@date_format)})"},
+ {name: "start_datetime", description: "Booking start date and time (e.g., #{time_now.to_s(@date_time_format)})"},
+ {name: "end_time", description: "Booking end time (e.g., #{time_now.to_s(@time_format)})"},
+ {name: "end_date", description: "Booking end date (e.g., #{time_now.to_s(@date_format)})"},
+ {name: "end_datetime", description: "Booking end date and time (e.g., #{time_now.to_s(@date_time_format)})"},
+ {name: "starting_unix", description: "Booking start time as Unix timestamp"},
+ {name: "asset_id", description: "Identifier of the booked asset (e.g., desk)"},
+ {name: "user_id", description: "Identifier of the person the booking is for"},
+ {name: "user_email", description: "Email of the person the booking is for"},
+ {name: "user_name", description: "Name of the person the booking is for"},
+ {name: "reason", description: "Purpose or title of the booking"},
+ {name: "building_zone", description: "Zone identifier for the building"},
+ {name: "building_name", description: "Name of the building"},
+ {name: "approver_name", description: "Name of the person who approved/rejected the booking"},
+ {name: "approver_email", description: "Email of the person who approved/rejected the booking"},
+ {name: "booked_by_name", description: "Name of the person who made the booking"},
+ {name: "booked_by_email", description: "Email of the person who made the booking"},
+ ]
+
+ [
+ TemplateFields.new(
+ trigger: {"bookings", "check_in_notifier"},
+ name: "Booking check in notifier",
+ description: "Notification to a mailing group when a booking is checked in",
+ fields: common_fields
+ ),
+ ]
+ end
+end
diff --git a/drivers/place/bookings/booking_checkin_notifier_spec.cr b/drivers/place/bookings/booking_checkin_notifier_spec.cr
new file mode 100644
index 00000000000..beeb94a835d
--- /dev/null
+++ b/drivers/place/bookings/booking_checkin_notifier_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::BookingCheckinNotifier" do
+end
diff --git a/drivers/place/bookings/event_attendance_recorder.cr b/drivers/place/bookings/event_attendance_recorder.cr
new file mode 100644
index 00000000000..a9c930ddefc
--- /dev/null
+++ b/drivers/place/bookings/event_attendance_recorder.cr
@@ -0,0 +1,157 @@
+require "placeos-driver"
+require "simple_retry"
+
+class Place::EventAttendanceRecorder < PlaceOS::Driver
+ descriptive_name "PlaceOS Event Attendance Recorder"
+ generic_name :EventAttendanceRecorder
+
+ default_settings({
+ metadata_key: "people_count",
+ debounce_seconds: 0,
+ })
+
+ accessor staff_api : StaffAPI_1
+
+ # Staff API metadata key
+ @metadata_key : String = "people_count"
+ @system_id : String = ""
+ getter count : UInt64 = 0_u64
+
+ # Tracking meeting details
+ getter status : String = "free"
+ getter booking_id : String? = nil
+
+ getter should_save : Bool = false
+ getter people_counts : Array(Int32) = [] of Int32
+ getter last_saved_count : Int32 = 0
+ getter last_known_count : Int32 = 0
+
+ @update_mutex = Mutex.new
+ @debounce_seconds : Int32 = 0
+
+ def on_load
+ @system_id = config.control_system.not_nil!.id
+ on_update
+ end
+
+ def on_update
+ @metadata_key = setting?(String, :metadata_key).presence || "people_count"
+ @debounce_seconds = setting?(Int32, :debounce_seconds) || 0
+ end
+
+ bind Bookings_1, :current_booking, :current_booking_changed
+ bind Bookings_1, :people_count, :people_count_changed
+ bind Bookings_1, :status, :status_changed
+
+ class StaffEventChange
+ include JSON::Serializable
+
+ @[JSON::Field(key: "id")]
+ property event_id : String
+ end
+
+ private def current_booking_changed(_subscription, new_value)
+ logger.debug { "booking changed: #{new_value}" }
+ event = (StaffEventChange?).from_json(new_value)
+
+ apply_new_state(event.try(&.event_id), @status)
+ rescue e
+ logger.warn(exception: e) { "failed to parse event" }
+ end
+
+ private def people_count_changed(_subscription, new_value) : Nil
+ logger.debug { "new people count received #{new_value}" }
+ return if new_value == "null"
+ value = (Int32 | Float64).from_json(new_value).to_i
+ value = value < 0 ? 0 : value
+
+ @last_known_count = value
+
+ if @debounce_seconds > 0
+ schedule.clear
+ schedule.in(@debounce_seconds.seconds) { record_new_people value }
+ else
+ record_new_people value
+ end
+ end
+
+ private def record_new_people(count : Int32)
+ @last_saved_count = count
+ if people_counts.last? != count
+ logger.debug { "recording new people count: #{count}" }
+ people_counts << count
+ end
+ end
+
+ private def status_changed(_subscription, new_value)
+ logger.debug { "new room status: #{new_value}" }
+ new_status = (String?).from_json(new_value) rescue new_value.to_s
+
+ apply_new_state(booking_id, new_status)
+ end
+
+ private def apply_new_state(new_booking_id : String?, new_status : String?)
+ @update_mutex.synchronize do
+ logger.debug { "#apply_new_state called with new_booking_id: #{new_booking_id}, new_status: #{new_status}" }
+
+ old_booking_id = @booking_id
+ @booking_id = new_booking_id
+ old_status = @status
+ @status = new_status || "free"
+
+ if old_booking_id && (new_booking_id != old_booking_id || new_status != old_status)
+ save_booking_stats(old_booking_id, people_counts) if @should_save
+ logger.debug { "#apply_new_state event_id: #{new_booking_id}, resetting people counts" }
+ @people_counts = [] of Int32
+ if @debounce_seconds > 0
+ schedule.clear
+ schedule.in(@debounce_seconds.seconds) { record_new_people last_known_count }
+ else
+ record_new_people last_known_count
+ end
+ end
+
+ @should_save = true if @booking_id && @status == "busy"
+ end
+ end
+
+ private def save_booking_stats(event_id : String, counts : Array(Int32))
+ logger.debug { "#save_booking_stats event_id: #{event_id}, counts: #{counts}" }
+
+ if counts.empty?
+ logger.warn { "no counts found for event #{event_id}" }
+ min = 0
+ max = 0
+ median = 0
+ average = 0
+ else
+ min = counts.min
+ max = counts.max
+ total = counts.reduce(0) { |acc, i| acc + i }
+ average = total / counts.size
+ counts.sort!
+ index = (counts.size / 2).round_away.to_i - 1
+ median = counts[index]
+ end
+
+ @count += 1_u64
+ @should_save = false
+
+ SimpleRetry.try_to(
+ max_attempts: 5,
+ base_interval: 10.milliseconds,
+ max_interval: 10.seconds,
+ ) do
+ staff_api.patch_event_metadata(@system_id, event_id, {
+ @metadata_key => {
+ min: min,
+ max: max,
+ median: median,
+ average: average,
+ },
+ }).get
+ end
+ rescue error
+ logger.warn(exception: error) { "failed to save event metadata" }
+ end
+end
diff --git a/drivers/place/bookings/event_attendance_recorder_spec.cr b/drivers/place/bookings/event_attendance_recorder_spec.cr
new file mode 100644
index 00000000000..df713e47eb7
--- /dev/null
+++ b/drivers/place/bookings/event_attendance_recorder_spec.cr
@@ -0,0 +1,69 @@
+require "placeos-driver/spec"
+require "uuid"
+
+DriverSpecs.mock_driver "Place::EventAttendanceRecorder" do
+ system({
+ StaffAPI: {StaffAPIMock},
+ Bookings: {BookingsMock},
+ })
+
+ # Start a new meeting
+ exec(:count).get.should eq 0
+ bookings = system(:Bookings).as(BookingsMock)
+ bookings.new_meeting
+ exec(:count).get.should eq 0
+ bookings.next_people_count
+
+ # Update the people counts
+ bookings.next_people_count
+ bookings.next_people_count
+ bookings.next_people_count
+ bookings.next_people_count
+ exec(:count).get.should eq 0
+
+ # End the meeting
+ bookings.new_meeting
+ sleep 0.1
+
+ exec(:count).get.should eq 1
+
+ # check the update that was applied
+ system(:StaffAPI)[:patched_with][2].should eq({
+ "people_count" => {
+ "min" => 1,
+ "max" => 10,
+ "median" => 2,
+ "average" => 3.4,
+ },
+ })
+end
+
+# :nodoc:
+class BookingsMock < DriverSpecs::MockDriver
+ @people_count_index : Int32 = 0
+ @people_counts : Array(Int32) = [10, 1, 2, 3, 1]
+
+ def next_people_count : Nil
+ self[:status] = "busy"
+ self[:people_count] = @people_counts[@people_count_index]
+ @people_count_index += 1
+ end
+
+ def new_meeting : Nil
+ self[:current_booking] = {
+ id: UUID.random.to_s,
+ }
+ self[:status] = "pending"
+ end
+end
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ @people_count_index : Int32 = 0
+ @people_counts : Array(Int32) = [10, 1, 2, 3, 1]
+
+ def patch_event_metadata(system_id : String, event_id : String, metadata : JSON::Any)
+ self[:patched_with] = {system_id, event_id, metadata}
+ true
+ end
+end
diff --git a/drivers/place/bookings/grant_area_access.cr b/drivers/place/bookings/grant_area_access.cr
new file mode 100644
index 00000000000..7ca38f992ca
--- /dev/null
+++ b/drivers/place/bookings/grant_area_access.cr
@@ -0,0 +1,439 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+require "placeos-driver/interface/zone_access_security"
+require "../booking_model"
+
+class Place::Bookings::GrantAreaAccess < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+
+ descriptive_name "PlaceOS Booking Area Access"
+ generic_name :BookingAreaAccess
+ description "ensures users can access areas they have booked. i.e. a private office allocated to a user"
+
+ default_settings({
+ # the channel id we're looking for events on
+ lookup_using_username: true,
+ _security_zone_whitelist: ["zone_name_or_id"],
+
+ # At 10:00 on every day-of-week from Monday through Friday
+ _email_cron: "0 10 * * 1-5",
+ _email_errors_to: "admin@org.com",
+ })
+
+ accessor calendar : Calendar_1
+ accessor staff_api : StaffAPI_1
+ accessor locations : LocationServices_1
+
+ def security_system
+ system.implementing(Interface::ZoneAccessSecurity).first
+ end
+
+ def on_load
+ monitor("staff/booking/changed") do |_subscription, payload|
+ logger.debug { "received booking changed event #{payload}" }
+ check_access(Booking.from_json payload)
+ end
+
+ on_update
+ end
+
+ @mutex = Mutex.new
+
+ # user_id => Array(special access)
+ getter allocations : Hash(String, Array(String)) = {} of String => Array(String)
+ getter cached_username : Hash(String, String) = {} of String => String
+ getter cached_user_lookups : Hash(String, String | Int64) = {} of String => String | Int64
+ getter cached_zone_lookups : Hash(String, String | Int64) = {} of String => String | Int64
+ getter security_zone_whitelist : Array(String | Int64) = [] of String | Int64
+
+ @lookup_using_username : Bool = false
+ @email_errors_to : String? = nil
+
+ def on_update
+ @building_id = nil
+ @timezone = nil
+ @systems = nil
+
+ @lookup_using_username = setting?(Bool, :lookup_using_username) || false
+ @security_zone_whitelist = setting?(Array(String | Int64), :security_zone_whitelist) || [] of String | Int64
+
+ # we ensure that allocations are recorded so we can unallocate as required
+ @mutex.synchronize do
+ @allocations = setting?(Hash(String, Array(String)), :permissions_allocated) || Hash(String, Array(String)).new
+ end
+
+ schedule.clear
+ schedule.every(30.minutes) { ensure_booking_access }
+
+ @email_errors_to = setting?(String, :email_errors_to)
+ if @email_errors_to && (cron = setting?(String, :email_cron))
+ schedule.cron(cron, timezone) { notify_issues }
+ end
+ end
+
+ getter building_id : String do
+ locations.building_id.get.as_s
+ end
+
+ # Grabs the list of systems in the building
+ getter systems : Hash(String, Array(String)) do
+ staff_api.systems_in_building(building_id).get.as_h.transform_values(&.as_a.map(&.as_s))
+ end
+
+ def levels : Array(String)
+ systems.keys
+ end
+
+ # system or building timezone
+ protected getter timezone : Time::Location do
+ tz = config.control_system.try(&.timezone) || staff_api.zone(building_id).get["timezone"].as_s
+ Time::Location.load(tz)
+ end
+
+ protected def check_access(booking : Booking)
+ now = Time.local(timezone)
+ end_of_day = now.at_end_of_day
+
+ return unless booking.booking_start <= end_of_day.to_unix && booking.booking_end >= now.to_unix
+ ensure_booking_access
+ end
+
+ struct Desk
+ include JSON::Serializable
+
+ getter id : String
+ getter security : String? = nil
+ end
+
+ def username_lookup(email : String) : String
+ email = email.strip.downcase
+ if username = cached_username[email]?
+ username
+ else
+ username = calendar.get_user(email).get["username"]?.try(&.as_s.downcase) || email
+ if username == email
+ cached_username[email] = email
+ else
+ cached_username[email] = username
+ end
+ username
+ end
+ end
+
+ def user_id?(email : String) : String | Int64 | Nil
+ security = security_system
+ lookup_user_id security, email.downcase
+ end
+
+ protected def lookup_user_id(security, email : String) : String | Int64 | Nil
+ id = cached_user_lookups[email]?
+ return id if id
+
+ if @lookup_using_username && (username = username_lookup(email))
+ json = (security.card_holder_id_lookup(username).get rescue nil)
+ if json && json.raw
+ id = (String | Int64).from_json(json.to_json)
+ cached_user_lookups[email] = (String | Int64).from_json(json.to_json)
+ return id
+ end
+ end
+
+ # handle the case where we have a json `null` response
+ json = (security.card_holder_id_lookup(email).get rescue nil)
+ if json && json.raw
+ cached_user_lookups[email] = (String | Int64).from_json(json.to_json)
+ end
+ end
+
+ def zone_id?(name_or_id : String) : String | Int64 | Nil
+ security = security_system
+ lookup_zone_id security, name_or_id
+ end
+
+ protected def lookup_zone_id(security, name_or_id : String) : String | Int64 | Nil
+ id = cached_zone_lookups[name_or_id]?
+ return id if id
+
+ # check if this was a name and lookup the id
+ id_raw = security.zone_access_id_lookup(name_or_id).get
+ if id = id_raw.as_s? || id_raw.as_i64?
+ cached_zone_lookups[name_or_id] = id
+ return id
+ end
+
+ # check if the ID was passed directly
+ if (security.zone_access_lookup(name_or_id).get rescue nil)
+ cached_zone_lookups[name_or_id] = name_or_id
+ return name_or_id
+ end
+
+ # otherwise the id or name is probably incorrect
+ logger.warn { "Zone lookup failed for: #{name_or_id}" }
+ nil
+ end
+
+ # returns desk_id => security zone name / id
+ def desks(level_id : String, blocked : Hash(String, String | Int64) = {} of String => String | Int64) : Hash(String, String)
+ desks = staff_api.metadata(level_id, "desks").get.dig?("desks", "details")
+ security = {} of String => String
+ return security unless desks
+
+ Array(Desk).from_json(desks.to_json).each do |desk|
+ sec = desk.security.presence
+ next unless sec
+
+ if security_zone_whitelist.empty?
+ security[desk.id] = sec
+ elsif security_zone_whitelist.includes?(sec)
+ security[desk.id] = sec
+ else
+ blocked[desk.id] = sec
+ end
+ end
+ security
+ end
+
+ protected def has_access?(security, zone_id, user_id) : Bool
+ has_access = (String | Int64 | Nil).from_json(security.zone_access_member?(zone_id, user_id).get.to_json)
+ !!has_access
+ end
+
+ @check_mutex : Mutex = Mutex.new
+ @performing_check : Bool = false
+ @check_queued : Bool = false
+
+ def ensure_booking_access
+ errors = [] of String
+ # desk id => security zone
+ # where mapping blocked due to not being whitelisted
+ blocked = {} of String => String | Int64
+
+ @check_mutex.synchronize do
+ if @performing_check
+ @check_queued = true
+ return
+ end
+
+ @performing_check = true
+ @check_queued = false
+ end
+
+ @mutex.synchronize do
+ now = Time.local(timezone).at_beginning_of_day
+ end_of_day = 3.days.from_now.in(timezone).at_end_of_day
+
+ access_required = Hash(String, Array(String)).new { |hash, key| hash[key] = [] of String }
+
+ # calculate who needs access
+ levels.each do |level_id|
+ desks = desks(level_id, blocked)
+ next if desks.empty?
+
+ desk_bookings = staff_api.query_bookings(now.to_unix, end_of_day.to_unix, zones: {level_id}, type: "desk").get.as_a
+ next if desk_bookings.empty?
+
+ desk_bookings.each do |booking|
+ desk = booking["asset_id"].as_s
+ if security = desks[desk]?
+ user_access = access_required[booking["user_email"].as_s.downcase]
+ user_access << security
+ user_access.uniq!
+ end
+ end
+ end
+
+ # apply access this access to the system, need to find the differences
+ allocations = @allocations
+ logger.debug { "found #{access_required.size} users that need access" }
+
+ if allocations == access_required
+ logger.debug { "no access changes are required" }
+ return
+ end
+
+ remove = Hash(String, Array(String)).new { |hash, key| hash[key] = [] of String }
+ add = Hash(String, Array(String)).new { |hash, key| hash[key] = [] of String }
+
+ # Collect all keys from both hashes
+ all_keys = allocations.keys.concat(access_required.keys)
+ all_keys.each do |key|
+ current = allocations[key]? || [] of String
+ desired = access_required[key]? || [] of String
+
+ # Calculate elements to remove and add
+ to_remove = current - desired
+ to_add = desired - current
+
+ # Add to `remove` hash if there are elements to remove
+ remove[key] = to_remove unless to_remove.empty?
+
+ # Add to `add` hash if there are elements to add
+ add[key] = to_add unless to_add.empty?
+ end
+
+ logger.debug { "deleting permissions: #{remove.size}" }
+ logger.debug { "granting permissions: #{add.size}" }
+
+ # apply the differences
+ security = security_system
+ remove.each do |user_email, zones|
+ begin
+ user_id = lookup_user_id(security, user_email)
+ raise "unable to find user_id for: #{user_email}" unless user_id
+
+ zones.uniq!.each do |zone|
+ begin
+ zone_id = lookup_zone_id(security, zone)
+ raise "unable to find zone_id for: #{zone}" unless zone_id
+ security.zone_access_remove_member(zone_id, user_id).get if has_access?(security, zone_id, user_id)
+ rescue error
+ # add the user back to the zone so it can be removed in a later sync
+ access_required[user_email] << zone
+ msg = "failed to remove #{user_email} from security zone: #{zone}"
+ errors << msg
+ logger.warn(exception: error) { msg }
+ end
+ end
+ rescue error
+ access_required[user_email] = allocations[user_email]
+ add.delete(user_email)
+ msg = "failed to remove #{user_email} from security zones"
+ errors << msg
+ logger.warn(exception: error) { msg }
+ end
+ end
+
+ add.each do |user_email, zones|
+ begin
+ user_id = lookup_user_id(security, user_email)
+ raise "unable to find user_id for: #{user_email}" unless user_id
+
+ zones.uniq!.each do |zone|
+ begin
+ zone_id = lookup_zone_id(security, zone)
+ raise "unable to find zone_id for: #{zone}" unless zone_id
+ security.zone_access_add_member(zone_id, user_id).get unless has_access?(security, zone_id, user_id)
+ rescue error
+ # remove the user from the recorded zone so it can be added in a later sync
+ access_required[user_email].delete zone
+ msg = "failed to add #{user_email} to security zone: #{zone}"
+ errors << msg
+ logger.warn(exception: error) { msg }
+ end
+ end
+ rescue error
+ access_required.delete(user_email)
+ msg = "failed to add #{user_email} to security zones"
+ errors << msg
+ logger.warn(exception: error) { msg }
+ end
+ end
+
+ # save the newly applied access permissions
+ define_setting(:permissions_allocated, access_required)
+ ensure
+ @check_mutex.synchronize do
+ @performing_check = false
+ spawn { ensure_booking_access } if @check_queued
+ end
+ end
+
+ # expose errors and anything blocked as not on the whitelist
+ self[:sync_errors] = errors
+ self[:sync_blocked] = blocked
+ end
+
+ @[Security(Level::Support)]
+ def security_zone_report
+ # desk id => security id
+ blocked = {} of String => String | Int64
+ found = {} of String => String | Int64
+ levels.each do |level_id|
+ found.merge! desks(level_id, blocked)
+ end
+
+ found_values = found.values.map(&.to_s).uniq!
+ security_groups = found.values + blocked.values
+ in_whitelist_only = security_zone_whitelist - security_groups
+
+ {
+ blocked: blocked,
+ allocated: found_values,
+ in_whitelist_only: in_whitelist_only,
+ }
+ end
+
+ @[Security(Level::Support)]
+ def approve_security_zone_list
+ # save all the security zones to the whitelist
+ details = security_zone_report
+ new_whitelist = details[:in_whitelist_only] + details[:allocated] + details[:blocked].values.uniq!
+ whitelist_strings = new_whitelist.compact_map { |item| item.as(String) if item.is_a?(String) }.sort!
+ whitelist_ints = new_whitelist.compact_map { |item| item.as(Int64) if item.is_a?(Int64) }.sort!
+
+ new_whitelist = [] of String | Int64
+ new_whitelist.concat whitelist_strings
+ new_whitelist.concat whitelist_ints
+
+ define_setting(:security_zone_whitelist, new_whitelist)
+ new_whitelist
+ end
+
+ # =========================
+ # MailerTemplates interface
+ # =========================
+
+ def template_fields : Array(TemplateFields)
+ [
+ TemplateFields.new(
+ trigger: {"security", "area_access_errors"},
+ name: "Booking Area Access Errors",
+ description: "Email sent when there are errors adding users to security groups so they can access the desk they have booked or allocated",
+ fields: [
+ {name: "errors", description: "a formatted list of email addresses to security groups that could not be applied"},
+ {name: "system_id", description: "the system with the BookingAreaAccess driver"},
+ ]
+ ),
+ ]
+ end
+
+ def mailer
+ system.implementing(Interface::Mailer)[0]
+ end
+
+ def notify_issues
+ sync_blocked = status?(Hash(String, String | Int64), :sync_blocked) || Hash(String, String | Int64).new
+ sync_errors = status?(Array(String), :sync_errors) || [] of String
+ return if sync_blocked.empty? && sync_errors.empty?
+
+ issue_list = String.build do |io|
+ if !sync_blocked.empty?
+ io << "security groups not in the whitelist:
\n"
+ io << "=====================================
\n"
+
+ sync_blocked.each do |desk_id, security_zone|
+ io << "desk: #{desk_id}, security group: #{security_zone}
\n"
+ end
+ io << "
\n\n"
+ end
+
+ if !sync_errors.empty?
+ io << "unable to allocate desks for:
\n"
+ io << "=============================
\n"
+
+ sync_errors.each do |error|
+ io << " - "
+ io << error
+ io << "
\n"
+ end
+ io << "
\n\n"
+ end
+ end
+
+ mailer.send_template(@email_errors_to.as(String), {"security", "area_access_errors"}, {
+ errors: issue_list,
+ system_id: config.control_system.try(&.id),
+ })
+ end
+end
diff --git a/drivers/place/bookings/grant_area_access_spec.cr b/drivers/place/bookings/grant_area_access_spec.cr
new file mode 100644
index 00000000000..1d1eee8f9df
--- /dev/null
+++ b/drivers/place/bookings/grant_area_access_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Bookings::GrantAreaAccess" do
+end
diff --git a/drivers/place/bookings/locker_booking_sync.cr b/drivers/place/bookings/locker_booking_sync.cr
new file mode 100644
index 00000000000..1f105989961
--- /dev/null
+++ b/drivers/place/bookings/locker_booking_sync.cr
@@ -0,0 +1,327 @@
+require "placeos-driver"
+require "placeos-driver/interface/lockers"
+require "../booking_model"
+require "./locker_models"
+
+# makes the assumption that there are no future bookings,
+# you can only book a locker now if it's currently free.
+class Place::Bookings::LockerBookingSync < PlaceOS::Driver
+ include Place::LockerMetadataParser
+
+ descriptive_name "PlaceOS Locker Booking Sync"
+ generic_name :LockerBookingSync
+ description "Syncs placeos bookings with a physical lockers system via the placeos locker interface"
+
+ default_settings({
+ authority_id: "auth-1234",
+ end_of_week_bookings: true,
+ })
+
+ # synced == allocation_id in placeos booking.extension_data
+ alias PlaceLocker = PlaceOS::Driver::Interface::Lockers::PlaceLocker
+ alias LockerMetadata = Place::Locker
+
+ accessor staff_api : StaffAPI_1
+ accessor locations : LocationServices_1
+
+ def locker_locations
+ system.implementing(Interface::Lockers)
+ end
+
+ def on_load
+ schedule.every(10.minutes) { ensure_locker_access }
+ on_update
+ end
+
+ @end_of_week_bookings : Bool = false
+
+ def on_update
+ @building_id = nil
+ @timezone = nil
+ @systems = nil
+ @locker_banks = nil
+ @locker_details = nil
+ @end_of_week_bookings = setting?(Bool, :end_of_week_bookings) || false
+
+ authority_id = setting(String, :authority_id)
+ subscriptions.clear
+ monitor("#{authority_id}/staff/booking/changed") do |_subscription, payload|
+ logger.debug { "received booking changed event #{payload}" }
+ check_allocation(Booking.from_json payload)
+ end
+ end
+
+ getter building_id : String do
+ locations.building_id.get.as_s
+ end
+
+ # Grabs the list of systems in the building
+ getter systems : Hash(String, Array(String)) do
+ staff_api.systems_in_building(building_id).get.as_h.transform_values(&.as_a.map(&.as_s))
+ end
+
+ def levels : Array(String)
+ systems.keys
+ end
+
+ # system or building timezone
+ protected getter timezone : Time::Location do
+ tz = config.control_system.try(&.timezone) || staff_api.zone(building_id).get["timezone"].as_s
+ Time::Location.load(tz)
+ end
+
+ # locker_banks included from LockerMetadataParser
+
+ # ===========================
+ # Primary Locker booking sync
+ # ===========================
+
+ @mutex = Mutex.new
+ @sync_busy : Hash(String, Bool) = Hash(String, Bool).new { |hash, key| hash[key] = false }
+ @sync_queue : Hash(String, Int32) = Hash(String, Int32).new { |hash, key| hash[key] = 0 }
+
+ def ensure_locker_access
+ levels.each { |zone_id| sync_level zone_id }
+ end
+
+ def sync_level(zone : String) : Nil
+ @mutex.synchronize do
+ @sync_queue[zone] += 1
+ if !@sync_busy[zone]
+ spawn { queue_sync_level(zone) }
+ :syncing
+ else
+ :queued
+ end
+ end
+ end
+
+ protected def queue_sync_level(zone : String) : Nil
+ # ensure we're not already syncing
+ @mutex.synchronize do
+ return if @sync_busy[zone]
+ @sync_busy[zone] = true
+ end
+
+ begin
+ loop do
+ begin
+ @mutex.synchronize { @sync_queue[zone] = 0 }
+ unique_id = Random::Secure.hex(10)
+ do_sync_level(zone, unique_id)
+ rescue error
+ logger.warn(exception: error) { "syncing #{zone}" }
+ end
+
+ break if @mutex.synchronize { @sync_queue[zone].zero? }
+ Fiber.yield
+ end
+ rescue error
+ logger.warn(exception: error) { "error syncing floor: #{zone}" }
+ ensure
+ @mutex.synchronize { @sync_busy[zone] = false }
+ end
+ end
+
+ protected def do_sync_level(level_id : String, unique_id : String) : Nil
+ logger.debug { "syncing #{level_id} -- id:#{unique_id}" }
+
+ # grab placeos bookings (now to 1 hour from now, including deleted / checked out)
+ starting = Time.local(timezone)
+ end_of_day = starting.at_end_of_day
+ place_bookings_raw = staff_api.query_bookings(starting.to_unix, end_of_day.to_unix, zones: {level_id}, type: "locker", include_checked_out: true).get.as_a
+ place_bookings_raw.concat staff_api.query_bookings(starting.to_unix, end_of_day.to_unix, zones: {level_id}, type: "locker", deleted: true).get.as_a
+ place_bookings = Array(Booking).from_json place_bookings_raw.to_json
+ place_bookings_raw.clear
+
+ # remove older instances of the recurring booking
+ place_bookings.sort! { |a, b| a.booking_start <=> b.booking_start }.uniq! { |book| book.id }
+
+ logger.debug { "found #{place_bookings.size} place bookings -- id:#{unique_id}" }
+
+ # grab current locker allocations
+ locker_systems = locker_locations
+ lockers = locker_systems.flat_map do |locker_system|
+ Array(PlaceLocker).from_json locker_system.device_locations(level_id).get.to_json
+ end
+
+ logger.debug { "found #{lockers.size} locker allocations -- id:#{unique_id}" }
+
+ # match bookings with the allocations
+ allocate_lockers = [] of Booking
+ release_lockers = [] of Booking
+ place_bookings.reject! do |booking|
+ if booking.deleted == true || booking.rejected == true || !booking.checked_out_at.nil?
+ logger.debug { " -- releasing locker #{booking.asset_id} as booking deleted #{booking.deleted.inspect}, rejected #{booking.rejected.inspect}, checked out #{booking.checked_out_at.inspect} -- id:#{unique_id}" }
+ release_lockers << booking
+ elsif has_allocation?(booking).nil?
+ allocate_lockers << booking
+ end
+ end
+
+ # there might be new allocations or valid bookings and we don't want to
+ # release the locker if there are existing bookings
+ release_lockers.reject! do |booking|
+ allocate_lockers.find { |book| book.asset_id == booking.asset_id && (book.user_id == booking.user_id || book.user_email.downcase == booking.user_email.downcase) } ||
+ place_bookings.find { |book| book.asset_id == booking.asset_id && (book.user_id == booking.user_id || book.user_email.downcase == booking.user_email.downcase) }
+ end
+
+ logger.debug { "planning to allocate #{allocate_lockers.size}, release #{release_lockers.size} and check #{place_bookings.size} against #{lockers.size} allocations -- id:#{unique_id}" }
+
+ # remove allocations where a place booking has been checked out
+ # ensure the locker is still allocated to that user
+ allocated = 0
+ release_lockers.each do |place_booking|
+ allocation_id = has_allocation?(place_booking)
+ next unless allocation_id
+
+ if locker = lockers.find { |lock| lock.allocation_id == allocation_id }
+ allocated += 1
+ logger.debug { " -- released #{locker.locker_id} (#{locker.allocation_id}) from #{place_booking.user_id} (#{place_booking.user_email}) -- id:#{unique_id}" }
+ locker_systems.locker_release(locker.bank_id, locker.locker_id, place_booking.user_id.presence || place_booking.user_email) rescue nil
+ lockers.delete locker
+ end
+ end
+
+ logger.debug { "released #{allocated} lockers, checked #{release_lockers.size} bookings -- id:#{unique_id}" }
+
+ # allocate lockers where a place booking has been created
+ allocated = 0
+ skipped = 0
+ alloc_failed = [] of Booking
+ allocate_lockers.each do |place_booking|
+ asset_id = place_booking.asset_id
+ place_user_id = place_booking.user_id.presence || place_booking.user_email
+
+ locker_meta = locker_details[asset_id]?
+ if locker_meta.nil?
+ skipped += 1
+ logger.warn { "unable to find locker details for locker id: #{asset_id}" }
+ next
+ end
+
+ locker = locker_systems.compact_map do |locker_system|
+ if json = (locker_system.locker_allocate(place_user_id, locker_meta.bank_id, locker_meta.id).get rescue nil)
+ PlaceLocker.from_json json.to_json
+ end
+ end.first?
+
+ # check if the locker is allocated to the current user (booking_state update may have failed earlier)
+ if locker.nil? && (found = lockers.find { |lock| lock.locker_id == asset_id })
+ locker = locker_systems.flat_map { |locker_system|
+ Array(PlaceLocker).from_json locker_system.lockers_allocated_to(place_user_id).get.to_json
+ }.select! { |lock| lock.locker_id == asset_id }.first?
+
+ if locker
+ logger.debug { " -- allocated #{found.locker_id} to #{place_user_id} (#{place_booking.user_email}) -- id:#{unique_id}" }
+ lockers.delete(found)
+ end
+ end
+
+ # store the allocation id in placeos, if locker allocate failed then we'll hopefully
+ # resolve this below if this step failed in a previous run
+ if locker
+ logger.debug { " -- update #{locker.locker_id} booking state on #{place_booking.id} to #{locker.allocation_id} -- id:#{unique_id}" }
+ staff_api.booking_extension_data(place_booking.id, {locker_allocation_id: locker.allocation_id}) if place_booking.instance
+ staff_api.booking_extension_data(place_booking.id, {locker_allocation_id: locker.allocation_id}, instance: place_booking.instance)
+ allocated += 1
+ else
+ alloc_failed << place_booking
+ end
+ rescue error
+ logger.warn(exception: error) { "failed to allocate #{place_booking.asset_id}" }
+ end
+
+ logger.debug { "allocated #{allocated} lockers, failed #{alloc_failed.size}, skipped #{skipped} -- id:#{unique_id}" }
+
+ # checkout placeos bookings where a locker has been released
+ # or there is a clash (locker allocated to someone else already)
+ checked_out = 0
+ place_bookings.each do |booking|
+ allocation_id = has_allocation?(booking)
+ if locker = lockers.find { |lock| lock.allocation_id == allocation_id }
+ # we found the locker so we don't need to create a placeos booking
+ lockers.delete(locker)
+ else
+ checked_out += 1
+ logger.debug { " -- booking #{booking.id} checked out of #{booking.asset_id} (#{booking.user_id}: #{booking.user_email}) -- id:#{unique_id}" }
+ # locker has been released so we should free the booking
+ staff_api.update_booking(booking.id, recurrence_end: booking.booking_end) if booking.instance
+ staff_api.booking_check_in(booking.id, false, "locker-sync", instance: booking.instance)
+ end
+ end
+
+ logger.debug { "ended #{checked_out} placeos locker bookings -- id:#{unique_id}" }
+
+ # create placeos bookings where a locker has been allocated
+ start_of_day = starting.at_beginning_of_day
+ end_of_week = starting.at_end_of_week
+ allocated = 0
+ skipped = 0
+ lockers.each do |lock|
+ owner = locker_systems.check_ownership_of(lock.mac).get.first?
+ email = owner["assigned_to"]?.try(&.as_s?).presence if owner
+ if email.nil?
+ logger.warn { "unable to find locker mac #{lock.mac} -- id:#{unique_id}" }
+ skipped += 1
+ next
+ end
+
+ email = email.strip.downcase
+ logger.debug { " -- creating booking for #{lock.locker_id} and #{email} -- id:#{unique_id}" }
+ user = begin
+ staff_api.user(email).get
+ rescue error
+ {
+ "id" => email,
+ "name" => email.split('@', 2)[0].gsub('.', ' '),
+ }
+ end
+ recurrence_end = end_of_week.to_unix if @end_of_week_bookings
+ staff_api.create_booking(
+ booking_type: "locker",
+ asset_id: lock.locker_id,
+ user_id: user["id"],
+ user_email: email,
+ user_name: user["name"],
+ zones: [level_id] + config.control_system.not_nil!.zones,
+ booking_start: start_of_day.to_unix,
+ booking_end: end_of_day.to_unix,
+ time_zone: timezone.name,
+ # checked_in: true, # results in a 422 error
+ title: lock.locker_name,
+ extension_data: {locker_allocation_id: lock.allocation_id},
+ recurrence_type: "DAILY",
+ recurrence_days: 127,
+ recurrence_end: recurrence_end,
+ ).get
+ allocated += 1
+ rescue error
+ logger.warn(exception: error) { "error creating booking for locker mac #{lock.mac} -- id:#{unique_id}" }
+ skipped += 1
+ end
+
+ logger.debug { "created #{allocated} placeos locker bookings. Failed to find #{skipped} users -- id:#{unique_id}" }
+ rescue error
+ logger.error(exception: error) { "unexpected error syncing bookings" }
+ end
+
+ protected def has_allocation?(booking) : String?
+ booking.extension_data["locker_allocation_id"]?.try(&.as_s.presence)
+ end
+
+ # ===========================
+ # Booking change notification
+ # ===========================
+
+ protected def check_allocation(booking : Booking)
+ return unless booking.booking_type == "locker"
+ if zone = (booking.zones & levels).first?
+ booking = Booking.from_json staff_api.get_booking(booking.id, booking.instance).get.to_json
+ # only sync level if the update is a create (unsynced) or the ending of a booking
+ if has_allocation?(booking).nil? || booking.deleted == true || booking.rejected == true || !booking.checked_out_at.nil?
+ queue_sync_level(zone)
+ end
+ end
+ end
+end
diff --git a/drivers/place/bookings/locker_booking_sync_spec.cr b/drivers/place/bookings/locker_booking_sync_spec.cr
new file mode 100644
index 00000000000..630c553cbad
--- /dev/null
+++ b/drivers/place/bookings/locker_booking_sync_spec.cr
@@ -0,0 +1,737 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/lockers"
+require "../booking_model"
+require "./locker_models"
+
+DriverSpecs.mock_driver "Place::Bookings::LockerBookingSync" do
+ system({
+ StaffAPI: {StaffAPIMock},
+ LocationServices: {LocationServicesMock},
+ Lockers: {LockersMock},
+ })
+
+ # Ensure sync works and creates no bookings
+ puts "\n\nEMPTY SYNC\n"
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ staff_api = system(:StaffAPI).as(StaffAPIMock)
+ staff_api.created.should eq 0
+ staff_api.query_calls.should eq 2
+ staff_api.reset
+
+ # create a staff api booking as a locker booking has been made
+ puts "\n\nLOCKER ALLOCATION SYNC\n"
+ lockers = system(:Lockers).as(LockersMock)
+ lockers.locker_allocate("user-1", "bank-1", "locker-2")
+ lockers.total_lockers_allocated.should eq 1
+ staff_api.bookings.size.should eq 0
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ staff_api.bookings.size.should eq 1
+ staff_api.created.should eq 1
+ staff_api.query_calls.should eq 2
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ lockers.total_lockers_allocated.should eq 1
+ staff_api.bookings.size.should eq 1
+ staff_api.created.should eq 1
+ staff_api.checked_out.should eq 0
+ staff_api.updated.should eq 0
+ staff_api.query_calls.should eq 4
+
+ # create a locker allocation if a staff API booking has been made
+ puts "\n\nSTAFF API BOOKING SYNC\n"
+ timezone = Time::Location.load("Australia/Sydney")
+ now = Time.local(timezone)
+ staff_api.create_booking(
+ booking_type: "locker",
+ asset_id: "locker-1",
+ user_id: "user-2",
+ user_email: "user-2@email.com",
+ user_name: "User 2",
+ zones: ["zone-level1", "zone-1234"],
+ booking_start: now.to_unix,
+ booking_end: now.at_end_of_day.to_unix,
+ title: "Lock 2",
+ time_zone: "Australia/Sydney"
+ )
+ staff_api.bookings.size.should eq 2
+ staff_api.created.should eq 2
+ lockers.total_lockers_allocated.should eq 1
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ lockers.total_lockers_allocated.should eq 2
+ staff_api.bookings.size.should eq 2
+ staff_api.created.should eq 2
+ staff_api.checked_out.should eq 0
+ staff_api.updated.should eq 1
+ staff_api.query_calls.should eq 6
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ lockers.total_lockers_allocated.should eq 2
+ staff_api.bookings.size.should eq 2
+ staff_api.created.should eq 2
+ staff_api.checked_out.should eq 0
+ staff_api.updated.should eq 1
+ staff_api.query_calls.should eq 8
+
+ # release a locker if a staff api booking is ended
+ puts "\n\nSTAFF BOOKING ENDED SYNC\n"
+ booking = staff_api.bookings.values.find! { |book| book.user_id == "user-2" }
+ booking.checked_in = false
+ booking.checked_out_at = Time.utc.to_unix
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ lockers.total_lockers_allocated.should eq 1
+ staff_api.bookings.size.should eq 2
+ staff_api.created.should eq 2
+ staff_api.checked_out.should eq 0
+ staff_api.updated.should eq 1
+ staff_api.query_calls.should eq 10
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ lockers.total_lockers_allocated.should eq 1
+ staff_api.bookings.size.should eq 2
+ staff_api.created.should eq 2
+ staff_api.checked_out.should eq 0
+ staff_api.updated.should eq 1
+ staff_api.query_calls.should eq 12
+
+ # end a booking if a locker is released
+ puts "\n\nLOCKER RELEASE SYNC\n"
+ lockers.locker_release_mine("bank-1", "locker-2")
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ lockers.total_lockers_allocated.should eq 0
+ staff_api.bookings.size.should eq 2
+ staff_api.created.should eq 2
+ staff_api.checked_out.should eq 1
+ staff_api.updated.should eq 1
+ staff_api.query_calls.should eq 14
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ lockers.total_lockers_allocated.should eq 0
+ staff_api.bookings.size.should eq 2
+ staff_api.created.should eq 2
+ staff_api.checked_out.should eq 1
+ staff_api.updated.should eq 1
+ staff_api.query_calls.should eq 16
+
+ # ===================================================
+ # create a new booking and ensure bookings are stable
+ # repeating all these previous tasks with old entries
+ # ===================================================
+
+ # create a staff api booking as a locker booking has been made
+ puts "\n\nLOCKER ALLOCATION SYNC\n"
+ lockers = system(:Lockers).as(LockersMock)
+ lockers.locker_allocate("user-1", "bank-1", "locker-2")
+ lockers.total_lockers_allocated.should eq 1
+ staff_api.bookings.size.should eq 2
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ staff_api.bookings.size.should eq 3
+ staff_api.created.should eq 3
+ staff_api.query_calls.should eq 18
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ lockers.total_lockers_allocated.should eq 1
+ staff_api.bookings.size.should eq 3
+ staff_api.created.should eq 3
+ staff_api.checked_out.should eq 1
+ staff_api.updated.should eq 1
+ staff_api.query_calls.should eq 20
+
+ # create a locker allocation if a staff API booking has been made
+ puts "\n\nSTAFF API BOOKING SYNC\n"
+ timezone = Time::Location.load("Australia/Sydney")
+ now = Time.local(timezone)
+ staff_api.create_booking(
+ booking_type: "locker",
+ asset_id: "locker-1",
+ user_id: "user-2",
+ user_email: "user-2@email.com",
+ user_name: "User 2",
+ zones: ["zone-level1", "zone-1234"],
+ booking_start: now.to_unix,
+ booking_end: now.at_end_of_day.to_unix,
+ title: "Lock 2",
+ time_zone: "Australia/Sydney"
+ )
+ staff_api.bookings.size.should eq 4
+ staff_api.created.should eq 4
+ lockers.total_lockers_allocated.should eq 1
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ lockers.total_lockers_allocated.should eq 2
+ staff_api.bookings.size.should eq 4
+ staff_api.created.should eq 4
+ staff_api.checked_out.should eq 1
+ staff_api.updated.should eq 2
+ staff_api.query_calls.should eq 22
+ exec :sync_level, "zone-level1"
+ sleep 300.milliseconds
+ lockers.total_lockers_allocated.should eq 2
+ staff_api.bookings.size.should eq 4
+ staff_api.created.should eq 4
+ staff_api.checked_out.should eq 1
+ staff_api.updated.should eq 2
+ staff_api.query_calls.should eq 24
+end
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ # always requesting the building zone for timezone info
+ def zone(id : String)
+ raise "unexpected id #{id.inspect}, expected zone-building-id" unless id == "zone-building-id"
+ {
+ timezone: "Australia/Sydney",
+ }
+ end
+
+ def systems_in_building(id : String, ids_only : Bool = true)
+ raise "unexpected id #{id.inspect}, expected zone-building-id" unless id == "zone-building-id"
+ raise "only ids supported, unexpected call" unless ids_only
+ {
+ "zone-level1" => [] of String,
+ "zone-level2" => [] of String,
+ }
+ end
+
+ def metadata(id : String, key : String? = nil)
+ raise "unexpected building id: #{id}" unless id == "zone-building-id"
+ case key
+ when "locker_banks"
+ {
+ locker_banks: {
+ details: [
+ {
+ id: "bank-1",
+ name: "Bank 1",
+ zones: ["zone-building-id", "zone-level1"],
+ },
+ {
+ id: "bank-2",
+ name: "Bank 2",
+ zones: ["zone-building-id", "zone-level2"],
+ },
+ ],
+ },
+ }
+ when "lockers"
+ {
+ lockers: {
+ details: [
+ {
+ id: "locker-1",
+ name: "Lock 1",
+ bank_id: "bank-1",
+ bookable: true,
+ },
+ {
+ id: "locker-2",
+ name: "Lock 2",
+ bank_id: "bank-1",
+ bookable: true,
+ },
+ {
+ id: "locker-3",
+ name: "Lock 3",
+ bank_id: "bank-2",
+ bookable: true,
+ },
+ {
+ id: "locker-4",
+ name: "Lock 4",
+ bank_id: "bank-2",
+ bookable: true,
+ },
+ ],
+ },
+ }
+ else
+ {} of Nil => Nil
+ end
+ end
+
+ def reset
+ @query_calls = 0
+ @created = 0
+ @checked_out = 0
+ @updated = 0
+ @bookings = {} of Int64 => Place::Booking
+ end
+
+ # emulate a basic database
+ getter bookings : Hash(Int64, Place::Booking) = {} of Int64 => Place::Booking
+ getter query_calls : Int32 = 0
+ getter created : Int32 = 0
+ getter updated : Int32 = 0
+ getter checked_out : Int32 = 0
+
+ def query_bookings(
+ type : String? = nil,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ rejected : Bool? = nil,
+ checked_in : Bool? = nil,
+ include_checked_out : Bool? = nil,
+ extension_data : JSON::Any? = nil,
+ deleted : Bool? = nil
+ )
+ @query_calls += 1
+ # return the bookings in the database
+ # ignore calls to deleted and return an empty array
+ return [] of Nil if deleted
+ @bookings.values
+ end
+
+ def booking_extension_data(booking_id : String | Int64, extension_data : Hash(String, JSON::Any), instance : Int64? = nil, signal_changes : Bool = false)
+ booking = @bookings[booking_id]?
+ raise "could not find booking #{booking_id}" unless booking
+ @updated += 1
+ booking.extension_data = extension_data
+ booking
+ end
+
+ # we won't test with a booking instance here as it jsut complicates things
+ # def update_booking
+
+ def booking_check_in(booking_id : String | Int64, state : Bool = true, utm_source : String? = nil, instance : Int64? = nil)
+ booking = @bookings[booking_id]?
+ raise "could not find booking #{booking_id}" unless booking
+ booking.checked_in = state
+ booking.checked_out_at = Time.utc.to_unix unless state
+ @checked_out += 1 unless state
+ booking
+ end
+
+ def user(id : String)
+ case id
+ when "user-1", "user-1@email.com"
+ {
+ id: "user-1",
+ email: "user-1@email.com",
+ name: "User 1",
+ }
+ when "user-2", "user-2@email.com"
+ {
+ id: "user-2",
+ email: "user-2@email.com",
+ name: "User 2",
+ }
+ else
+ raise "unexpected user id requested #{id}"
+ end
+ end
+
+ def create_booking(
+ booking_type : String,
+ asset_id : String,
+ user_id : String,
+ user_email : String,
+ user_name : String,
+ zones : Array(String),
+ booking_start : Int64? = nil,
+ booking_end : Int64? = nil,
+ checked_in : Bool = false,
+ approved : Bool? = nil,
+ title : String? = nil,
+ description : String? = nil,
+ time_zone : String? = nil,
+ extension_data : JSON::Any? = nil,
+ utm_source : String? = nil,
+ limit_override : Int64? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ attendees : Array(Nil)? = nil,
+ process_state : String? = nil,
+ recurrence_type : String? = nil,
+ recurrence_days : Int32? = nil,
+ recurrence_nth_of_month : Int32? = nil,
+ recurrence_interval : Int32? = nil,
+ recurrence_end : Int64? = nil
+ )
+ @created += 1
+ id = rand(Int64::MAX)
+ @bookings[id] = Place::Booking.new(
+ id: id,
+ booking_type: booking_type,
+ asset_id: asset_id,
+ user_id: user_id,
+ user_email: user_email,
+ user_name: user_name,
+ zones: zones,
+ booked_by_name: user_name,
+ booked_by_email: user_email,
+ booking_start: booking_start.not_nil!,
+ booking_end: booking_end.not_nil!,
+ timezone: time_zone.not_nil!,
+ extension_data: extension_data.try(&.as_h),
+ )
+ end
+
+ def get_booking(booking_id : String | Int64, instance : Int64? = nil)
+ # this function shouldn't really be called
+ logger.warn { "UNEXPECTED CALL TO staff_api.get_booking(#{booking_id.inspect}, #{instance.inspect})" }
+ @bookings[booking_id.to_i]
+ end
+end
+
+# re-open classes to add some helpers
+class ::Place::Locker
+ def initialize(@id, @name, @bank_id, @bookable, @level_id)
+ end
+
+ # for tracking, not part of metadata
+ property allocated_to : String? = nil
+ property allocated_at : Time? = nil
+ property allocated_until : Time? = nil
+ property shared_with : Array(String) = [] of String
+
+ def release
+ @allocated_to = nil
+ @allocated_at = nil
+ @allocated_until = nil
+ @shared_with = [] of String
+ end
+
+ def allocated? : Bool
+ if time = self.allocated_until
+ if time > Time.utc
+ true
+ else
+ false
+ end
+ elsif self.allocated_to.presence
+ true
+ else
+ false
+ end
+ end
+
+ def not_allocated? : Bool
+ !allocated?
+ end
+end
+
+class ::PlaceOS::Driver::Interface::Lockers::PlaceLocker
+ def initialize(@bank_id, locker : ::Place::Locker, @building = nil)
+ @locker_id = locker.id
+ @locker_name = locker.name
+ @mac = "lb=#{@bank_id}&lk=#{locker.id}"
+ if time = locker.allocated_until
+ if time > Time.utc
+ in_use = true
+ @expires_at = time
+ else
+ in_use = false
+ @expires_at = nil
+ end
+ elsif allocated_to = locker.allocated_to
+ in_use = true
+ @expires_at = nil
+ else
+ in_use = false
+ @expires_at = nil
+ end
+ @allocated = in_use
+ @allocation_id = "#{locker.allocated_to}--#{locker.id}--#{locker.allocated_at.try(&.to_unix_ns)}" if in_use
+ @level = locker.level_id
+ end
+end
+
+class Place::LockerBank
+ def initialize(@id, @name, @zones, @level_id, @lockers)
+ end
+end
+
+# :nodoc:
+class LockersMock < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Lockers
+
+ alias LockerBank = Place::LockerBank
+ alias Locker = Place::Locker
+
+ def reset
+ @locker_banks = nil
+ @locker_details = nil
+ end
+
+ def total_lockers_allocated : Int32
+ allocated = 0
+ locker_details.each_value do |locker|
+ allocated += 1 if locker.allocated?
+ end
+ allocated
+ end
+
+ def invoked_by_user_id
+ "user-1"
+ end
+
+ # implement the locker metadata parser methods
+ getter locker_banks : Hash(String, LockerBank) do
+ {
+ "bank-1" => LockerBank.new("bank-1", "Bank 1", ["zone-building-id", "zone-level1"], "zone-level1", [
+ Locker.new("locker-1", "Lock 1", "bank-1", true, "zone-level1"),
+ Locker.new("locker-2", "Lock 2", "bank-1", true, "zone-level1"),
+ ]),
+ "bank-2" => LockerBank.new("bank-2", "Bank 2", ["zone-building-id", "zone-level2"], "zone-level2", [
+ Locker.new("locker-3", "Lock 3", "bank-2", true, "zone-level2"),
+ Locker.new("locker-4", "Lock 4", "bank-2", true, "zone-level2"),
+ ]),
+ }
+ end
+
+ getter locker_details : Hash(String, Locker) do
+ lockers = {} of String => Locker
+ locker_banks.each_value do |bank|
+ bank.lockers.each do |locker|
+ lockers[locker.id] = locker
+ end
+ end
+ lockers
+ end
+
+ def building_id : String
+ "zone-building-id"
+ end
+
+ def levels : Array(String)
+ ["zone-level1", "zone-level2"]
+ end
+
+ # allocates a locker now, the allocation may expire
+ def locker_allocate(
+ # PlaceOS user id
+ user_id : String,
+
+ # the locker location
+ bank_id : String | Int64,
+
+ # allocates a random locker if this is nil
+ locker_id : String | Int64? = nil,
+
+ # attempts to create a booking that expires at the time specified
+ expires_at : Int64? = nil
+ ) : PlaceLocker
+ bank = locker_banks[bank_id.to_s]
+ locker_id = locker_id ? locker_id : bank.locker_hash.values.select(&.not_allocated?).sample.id
+ locker = bank.locker_hash[locker_id.to_s]
+ locker.allocated_to = user_id
+ locker.allocated_at = Time.utc
+ locker.allocated_until = Time.unix(expires_at) if expires_at
+ PlaceLocker.new(bank_id, locker, building_id)
+ rescue
+ raise "no available lockers"
+ end
+
+ # return the locker to the pool
+ def locker_release(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+
+ # release / unshare just this user - otherwise release the whole locker
+ owner_id : String? = nil
+ ) : Nil
+ locker = locker_banks[bank_id.to_s].locker_hash[locker_id.to_s]
+ if locker.allocated_to == owner_id
+ locker.release
+ else
+ locker.shared_with.delete(owner_id)
+ end
+ end
+
+ # a list of lockers that are allocated to the user
+ def lockers_allocated_to(user_id : String) : Array(PlaceLocker)
+ now = Time.utc
+ building = building_id
+
+ locker_banks.values.flat_map do |bank|
+ bank.locker_hash.values.compact_map do |locker|
+ if locker.allocated_to == user_id
+ if time = locker.allocated_until
+ PlaceLocker.new(bank.id, locker, building) if time > now
+ else
+ PlaceLocker.new(bank.id, locker, building)
+ end
+ end
+ end
+ end
+ end
+
+ def locker_share(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+ owner_id : String,
+ share_with : String
+ ) : Nil
+ locker = locker_banks[bank_id.to_s].locker_hash[locker_id.to_s]
+ perform_share = false
+ if locker.allocated_to == owner_id
+ if time = locker.allocated_until
+ perform_share = time > Time.utc
+ else
+ perform_share = true
+ end
+ end
+
+ if perform_share
+ locker.shared_with << share_with
+ locker.shared_with.uniq!
+ end
+ end
+
+ def locker_unshare(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+ owner_id : String,
+ # the individual you previously shared with (optional)
+ shared_with_id : String? = nil
+ ) : Nil
+ locker = locker_banks[bank_id.to_s].locker_hash[locker_id.to_s]
+ perform_share = false
+ if locker.allocated_to == owner_id
+ if time = locker.allocated_until
+ perform_share = time > Time.utc
+ else
+ perform_share = true
+ end
+ end
+
+ if perform_share
+ if shared_with_id
+ locker.shared_with.delete shared_with_id
+ else
+ locker.shared_with = [] of String
+ end
+ end
+ end
+
+ # a list of user-ids that the locker is shared with.
+ # this can be placeos user ids or emails
+ def locker_shared_with(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+ owner_id : String
+ ) : Array(String)
+ locker = locker_banks[bank_id.to_s].locker_hash[locker_id.to_s]
+ perform_share = false
+ if locker.allocated_to == owner_id
+ if time = locker.allocated_until
+ perform_share = time > Time.utc
+ else
+ perform_share = true
+ end
+ end
+
+ if perform_share
+ locker.shared_with
+ else
+ [] of String
+ end
+ end
+
+ def locker_unlock(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+
+ # sometimes required by locker systems
+ owner_id : String? = nil,
+ # time in seconds the locker should be unlocked
+ # (can be ignored if not implemented)
+ open_time : Int32 = 60,
+ # optional pin code - if user entered from a kiosk
+ pin_code : String? = nil
+ ) : Nil
+ end
+
+ # ===================================
+ # Locatable Interface functions
+ # ===================================
+ def locate_user(email : String? = nil, username : String? = nil)
+ logger.debug { "sensor incapable of locating #{email} or #{username}" }
+ [] of Nil
+ end
+
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ logger.debug { "sensor incapable of tracking #{email} or #{username}" }
+ # we could find the floorsense user, grab the reservations the user has
+ # and list them here, but probably not amazingly useful
+ [] of String
+ end
+
+ USER_EMAILS = {
+ "user-1" => "user-1@email.com",
+ "user-2" => "user-2@email.com",
+ }
+
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ # "lb=#{@bank_id}&lk=#{locker.id}"
+ return nil unless mac_address.starts_with?("lb=")
+ floor_mac = URI::Params.parse mac_address
+ locker_bank = floor_mac["lb"]
+ locker_key = floor_mac["lk"]
+ locker = locker_banks[locker_bank].locker_hash[locker_key]
+
+ has_reservation = false
+ if user_id = locker.allocated_to
+ if time = locker.allocated_until
+ has_reservation = time > Time.utc
+ else
+ has_reservation = true
+ end
+ end
+
+ if has_reservation
+ {
+ location: "locker",
+ assigned_to: USER_EMAILS[locker.allocated_to],
+ mac_address: mac_address,
+ }
+ end
+ rescue
+ nil
+ end
+
+ def device_locations(zone_id : String, location : String? = nil)
+ logger.debug { "searching lockers in zone #{zone_id}" }
+ return [] of Nil if location && location != "locker"
+
+ building = building_id
+ level_zone = zone_id == building ? nil : zone_id
+ return [] of Nil if level_zone && !level_zone.in?(levels)
+
+ now = Time.utc
+ locker_banks.values.flat_map do |bank|
+ next [] of PlaceLocker if level_zone && bank.level_id != level_zone
+
+ bank.locker_hash.values.compact_map do |locker|
+ if locker.allocated_to
+ if time = locker.allocated_until
+ PlaceLocker.new(bank.id, locker, building) if time > now
+ else
+ PlaceLocker.new(bank.id, locker, building)
+ end
+ end
+ end
+ end
+ end
+end
+
+# :nodoc:
+class LocationServicesMock < DriverSpecs::MockDriver
+ def building_id : String
+ "zone-building-id"
+ end
+end
diff --git a/drivers/place/bookings/locker_models.cr b/drivers/place/bookings/locker_models.cr
new file mode 100644
index 00000000000..ff3fc461da9
--- /dev/null
+++ b/drivers/place/bookings/locker_models.cr
@@ -0,0 +1,90 @@
+require "json"
+
+class Place::Locker
+ include JSON::Serializable
+
+ getter id : String
+ getter name : String { id }
+ getter bank_id : String
+ getter bookable : Bool { false }
+
+ # for tracking, not part of metadata
+ property level_id : String? = nil
+end
+
+class Place::LockerBank
+ include JSON::Serializable
+
+ getter id : String
+ getter name : String { id }
+ getter zones : Array(String)
+
+ # for tracking, not part of metadata
+ property level_id : String? = nil
+ getter lockers : Array(Locker) = [] of Locker
+ getter locker_hash : Hash(String, Locker) do
+ lookup = {} of String => Locker
+ level = self.level_id
+ lockers.each do |locker|
+ locker.level_id = level
+ lookup[locker.id] = locker
+ end
+ lookup
+ end
+end
+
+module Place::LockerMetadataParser
+ getter locker_banks : Hash(String, LockerBank) do
+ # Grab bank details
+ banks = staff_api.metadata(building_id, "locker_banks").get.dig?("locker_banks", "details")
+ return Hash(String, LockerBank).new unless banks
+
+ banks = begin
+ Array(LockerBank).from_json(banks.to_json)
+ rescue error
+ message = "error parsing banks json on building #{building_id}:\n#{banks.to_pretty_json}"
+ logger.warn(exception: error) { message }
+ raise message
+ end
+
+ lookup = {} of String => LockerBank
+ banks.each do |bank|
+ bank.level_id = (levels & bank.zones).first?
+ lookup[bank.id] = bank
+ end
+
+ # Grab locker details:
+ lockers = staff_api.metadata(building_id, "lockers").get.dig?("lockers", "details")
+ return lookup unless lockers
+
+ lockers = begin
+ Array(Locker).from_json(lockers.to_json)
+ rescue error
+ message = "error parsing locker json on building #{building_id}:\n#{lockers.to_pretty_json}"
+ logger.warn(exception: error) { message }
+ raise message
+ end
+
+ lockers.each do |locker|
+ begin
+ bank = lookup[locker.bank_id]
+ locker.level_id = bank.level_id
+ bank.lockers << locker
+ rescue error
+ logger.warn(exception: error) { "config issue with locker #{locker.id} on bank #{locker.bank_id}" }
+ end
+ end
+
+ lookup
+ end
+
+ getter locker_details : Hash(String, Locker) do
+ lockers = {} of String => Locker
+ locker_banks.each_value do |bank|
+ bank.lockers.each do |locker|
+ lockers[locker.id] = locker
+ end
+ end
+ lockers
+ end
+end
diff --git a/drivers/place/bookings/security_booking_check_in.cr b/drivers/place/bookings/security_booking_check_in.cr
new file mode 100644
index 00000000000..fd5241fa63c
--- /dev/null
+++ b/drivers/place/bookings/security_booking_check_in.cr
@@ -0,0 +1,81 @@
+require "placeos-driver"
+require "place_calendar"
+require "placeos-driver/interface/door_security"
+
+class Place::SecurityBookingCheckin < PlaceOS::Driver
+ descriptive_name "Security based Booking Checkin"
+ generic_name :SecurityBookingCheckin
+ description %(Checks in users to bookings based on swipe card events in the security system)
+
+ default_settings({
+ # the channel id we're looking for events on
+ organization_id: "event",
+
+ # booking types we want to check in
+ booking_types: ["desk"],
+ })
+
+ def on_update
+ @booking_types = setting(Array(String), :booking_types)
+ time_zone_string = setting?(String, :time_zone).presence || config.control_system.not_nil!.timezone.presence || "GMT"
+ @time_zone = Time::Location.load(time_zone_string)
+ @building_id = nil
+
+ subscriptions.clear
+ org_id = setting?(String, :organization_id) || "event"
+ monitor("security/#{org_id}/door") { |_subscription, payload| door_event(payload) }
+ end
+
+ @booking_types : Array(String) = [] of String
+ @time_zone : Time::Location = Time::Location.load("GMT")
+
+ accessor staff_api : StaffAPI_1
+
+ getter building_id : String { get_building_id.not_nil! }
+
+ def get_building_id : String
+ building_setting = setting?(String, :building_zone_override)
+ return building_setting if building_setting && building_setting.presence
+ zone_ids = staff_api.zones(tags: "building").get.as_a.map(&.[]("id").as_s)
+ (zone_ids & system.zones).first
+ end
+
+ getter event_count : UInt64 = 0_u64
+ getter check_ins : UInt64 = 0_u64
+ getter matched_users : UInt64 = 0_u64
+
+ @[Security(Level::Administrator)]
+ def door_event(json : String)
+ logger.debug { "new door event detected: #{json}" }
+ event = Interface::DoorSecurity::DoorEvent.from_json(json)
+ @event_count += 1_u64
+
+ now = Time.local(@time_zone).at_beginning_of_day
+ end_of_day = now.in(@time_zone).at_end_of_day - 2.hours
+ building = building_id
+
+ @booking_types.each do |booking_type|
+ if email = event.user_email.presence
+ staff_user = staff_api.user(email.strip.downcase).get rescue nil
+ if staff_user
+ email = staff_user["email"].as_s
+ @matched_users += 1_u64
+ end
+
+ # find any bookings that user may have
+ bookings = staff_api.query_bookings(now.to_unix, end_of_day.to_unix, zones: {building}, type: booking_type, email: email).get.as_a
+ logger.debug { "found #{bookings.size} of #{booking_type} for #{email}" }
+
+ bookings.each do |booking|
+ if !booking["checked_in"].as_bool?
+ logger.debug { " -- checking in #{booking_type} for #{email}" }
+ @check_ins += 1_u64
+ staff_api.booking_check_in(booking["id"], true, "security-access", instance: booking["instance"]?)
+ else
+ logger.debug { " -- skipping #{booking_type} for #{email} as already checked-in" }
+ end
+ end
+ end
+ end
+ end
+end
diff --git a/drivers/place/bookings/security_booking_check_in_spec.cr b/drivers/place/bookings/security_booking_check_in_spec.cr
new file mode 100644
index 00000000000..be1d9c7c1f1
--- /dev/null
+++ b/drivers/place/bookings/security_booking_check_in_spec.cr
@@ -0,0 +1,73 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::SecurityBookingCheckin" do
+ system({
+ StaffAPI: {StaffAPIMock},
+ })
+
+ exec(:door_event, {
+ module_id: "mod-123",
+ security_system: "gallagher",
+ door_id: "door 123",
+ timestamp: 0,
+ action: "Granted",
+ user_email: "user@email.com",
+ }.to_json).get
+
+ exec(:event_count).get.should eq 1
+ exec(:check_ins).get.should eq 1
+end
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ def user(id : String)
+ raise "unknown user #{id}" unless id == "user@email.com"
+ {
+ email: "user@email.com",
+ login_name: "user@email.com",
+ }
+ end
+
+ def query_bookings(
+ type : String? = nil,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ rejected : Bool? = nil,
+ checked_in : Bool? = nil,
+ include_checked_out : Bool? = nil,
+ extension_data : JSON::Any? = nil,
+ deleted : Bool? = nil
+ )
+ raise "unexpected bookings query" unless type == "desk" && zones.includes?("zone-building") && email == "user@email.com"
+
+ [{
+ id: 2345,
+ checked_in: false,
+ }]
+ end
+
+ def booking_check_in(booking_id : String | Int64, state : Bool = true, utm_source : String? = nil, instance : Int64? = nil)
+ raise "unexpected booking id" unless booking_id == 2345 && state
+ true
+ end
+
+ def zones(q : String? = nil,
+ limit : Int32 = 1000,
+ offset : Int32 = 0,
+ parent : String? = nil,
+ tags : Array(String) | String? = nil)
+ raise "unexpected tag" unless tags == "building"
+ [{
+ "id" => "zone-building",
+ }]
+ end
+end
diff --git a/drivers/place/bookings_spec.cr b/drivers/place/bookings_spec.cr
new file mode 100644
index 00000000000..30d1b15473f
--- /dev/null
+++ b/drivers/place/bookings_spec.cr
@@ -0,0 +1,292 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/sensor"
+
+DriverSpecs.mock_driver "Place::Bookings" do
+ system({
+ Calendar: {CalendarMock},
+ Sensor: {SensorMock},
+ })
+
+ sleep 200.milliseconds
+
+ # Check it calculates state properly
+ exec(:poll_events).get
+
+ sleep 200.milliseconds
+
+ bookings = status[:bookings].as_a
+ bookings.size.should eq(4)
+
+ sleep 200.milliseconds
+
+ status[:booked].should eq(true)
+ status[:in_use].should eq(false)
+ status[:pending].should eq(true)
+ status[:current_pending].should eq(true)
+ status[:next_pending].should eq(false)
+ status[:status].should eq("pending")
+
+ current_start = bookings[0]["event_start"]
+
+ # Start a meeting
+ exec(:start_meeting, current_start).get
+ sleep 200.milliseconds
+
+ bookings = status[:bookings].as_a
+ bookings.size.should eq(4)
+ status[:booked].should eq(true)
+ status[:in_use].should eq(true)
+ status[:pending].should eq(false)
+ status[:current_pending].should eq(false)
+ status[:next_pending].should eq(false)
+ status[:status].should eq("busy")
+
+ # End a meeting
+ exec(:end_meeting, current_start).get
+ sleep 2200.milliseconds # polls after 2 seconds
+
+ bookings = status[:bookings].as_a
+ bookings.size.should eq(3)
+
+ status[:booked].should eq(false)
+ status[:in_use].should eq(false)
+ status[:pending].should eq(false)
+ status[:current_pending].should eq(false)
+ status[:next_pending].should eq(false)
+ status[:status].should eq("free")
+
+ status[:people_count].should eq(12.0)
+ status[:sensor_name].should eq("Mock People Count")
+ status[:presence].should eq(true)
+end
+
+# :nodoc:
+class SensorMock < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Sensor
+
+ alias Interface = PlaceOS::Driver::Interface
+
+ def on_load
+ self[:people_count] = 12.0
+ end
+
+ def sensors(type : String? = nil, mac : String? = nil, zone_id : String? = nil) : Array(Interface::Sensor::Detail)
+ if type == "people_count"
+ [Interface::Sensor::Detail.new(
+ type: Interface::Sensor::SensorType::PeopleCount,
+ value: 12.0,
+ last_seen: Time.utc.to_unix,
+ mac: "mock-people-count",
+ id: nil,
+ name: "Mock People Count",
+ module_id: "mod-Sensor/1",
+ binding: "people_count"
+ )]
+ else
+ [] of Interface::Sensor::Detail
+ end
+ end
+
+ def sensor(mac : String, id : String? = nil) : Interface::Sensor::Detail?
+ nil
+ end
+end
+
+# :nodoc:
+class CalendarMock < DriverSpecs::MockDriver
+ def on_load
+ self[:checked_calendar] = nil
+ self[:deleted_event] = nil
+ end
+
+ def decline_event(calendar_id : String, event_id : String, user_id : String? = nil, notify : Bool = false, comment : String? = nil)
+ self[:deleted_event] = {calendar_id, event_id}
+ @events = @events.reject { |event| event["id"] == event_id }
+ nil
+ end
+
+ def delete_event(calendar_id : String, event_id : String, user_id : String? = nil, notify : Bool = false, comment : String? = nil)
+ self[:deleted_event] = {calendar_id, event_id}
+ @events = @events.reject { |event| event["id"] == event_id }
+ nil
+ end
+
+ def list_events(
+ calendar_id : String,
+ period_start : Int64,
+ period_end : Int64,
+ time_zone : String? = nil,
+ user_id : String? = nil,
+ include_cancelled : Bool = false
+ )
+ self[:checked_calendar] = calendar_id
+ @events
+ end
+
+ @events : Array(Hash(String, Array(Hash(String, String)) | Bool | Int64 | String | Array(Nil))) = [
+ {
+ "event_start" => 10.minutes.ago.to_unix,
+ "event_end" => 20.minutes.from_now.to_unix,
+ "id" => "2hg6c13j9ko8hiugmuj8n3jtap_20200804T000000Z",
+ "host" => "jeremy@place.nology",
+ "title" => "A Standup",
+ "description" => "",
+ "attendees" => [
+ {
+ "name" => "alexandre@place.nology",
+ "email" => "alexandre@place.nology",
+ },
+ {
+ "name" => "candy@place.nology",
+ "email" => "candy@place.nology",
+ },
+ {
+ "name" => "viv@place.nology",
+ "email" => "viv@place.nology",
+ },
+ {
+ "name" => "steve@place.nology",
+ "email" => "steve@place.nology",
+ },
+ {
+ "name" => "jeremy@place.nology",
+ "email" => "jeremy@place.nology",
+ },
+ ],
+ "private" => false,
+ "recurring" => false,
+ "all_day" => false,
+ "timezone" => "UTC",
+ "attachments" => [] of Nil,
+ },
+ {
+ "event_start" => 40.minutes.from_now.to_unix,
+ "event_end" => 1.hour.from_now.to_unix,
+ "id" => "2hg6c13j9ko8hiugmuj8n3jtap_20200806T000000Z",
+ "host" => "jeremy@place.nology",
+ "title" => "A Standup",
+ "description" => "",
+ "attendees" => [
+ {
+ "name" => "alexandre@place.nology",
+ "email" => "alexandre@place.nology",
+ },
+ {
+ "name" => "candy@place.nology",
+ "email" => "candy@place.nology",
+ },
+ {
+ "name" => "viv@place.nology",
+ "email" => "viv@place.nology",
+ },
+ {
+ "name" => "steve@place.nology",
+ "email" => "steve@place.nology",
+ },
+ {
+ "name" => "jeremy@place.nology",
+ "email" => "jeremy@place.nology",
+ },
+ ],
+ "private" => false,
+ "recurring" => false,
+ "all_day" => false,
+ "timezone" => "UTC",
+ "attachments" => [] of Nil,
+ },
+ {
+ "event_start" => 4.hour.from_now.to_unix,
+ "event_end" => 5.hour.from_now.to_unix,
+ "id" => "0e1f5n6a898n85eo9gsj169kh1_20200806T010000Z",
+ "host" => "shreya@external.com",
+ "title" => "Place weekly catchup",
+ "description" => "",
+ "attendees" => [
+ {
+ "name" => "Michael",
+ "email" => "michael@external.com",
+ },
+ {
+ "name" => "Glenn",
+ "email" => "glenn@external.com",
+ },
+ {
+ "name" => "Shreya",
+ "email" => "shreya@external.com",
+ },
+ {
+ "name" => "jeremy@place.nology",
+ "email" => "jeremy@place.nology",
+ },
+ {
+ "name" => "Lisa",
+ "email" => "lisa@external.com",
+ },
+ {
+ "name" => "Sheshank",
+ "email" => "sheshank@external.com",
+ },
+ {
+ "name" => "steve@place.nology",
+ "email" => "steve@place.nology",
+ },
+ {
+ "name" => "Zinoca",
+ "email" => "zain@external.com",
+ },
+ {
+ "name" => "Aymie",
+ "email" => "aymie@external.com",
+ },
+ ],
+ "private" => false,
+ "recurring" => false,
+ "all_day" => false,
+ "timezone" => "UTC",
+ "attachments" => [] of Nil,
+ },
+ {
+ "event_start" => 10.hours.from_now.to_unix,
+ "event_end" => 11.hours.from_now.to_unix,
+ "id" => "d8n8u5a5u8j45jgm5248ir49qs_20200806T010000Z",
+ "host" => "jeremy@place.nology",
+ "title" => "PlaceOS Standup",
+ "description" => "Regular Standup to discuss Engine2 Development and Product Requirements.",
+ "attendees" => [
+ {
+ "name" => "caspian@place.nology",
+ "email" => "caspian@place.nology",
+ },
+ {
+ "name" => "viv@place.nology",
+ "email" => "viv@place.nology",
+ },
+ {
+ "name" => "Kim",
+ "email" => "kim@place.nology",
+ },
+ {
+ "name" => "William",
+ "email" => "w.le@place.nology",
+ },
+ {
+ "name" => "jeremy@place.nology",
+ "email" => "jeremy@place.nology",
+ },
+ {
+ "name" => "Shane",
+ "email" => "shane@place.nology",
+ },
+ {
+ "name" => "steve@place.nology",
+ "email" => "steve@place.nology",
+ },
+ ],
+ "private" => false,
+ "recurring" => false,
+ "all_day" => false,
+ "timezone" => "UTC",
+ "attachments" => [] of Nil,
+ },
+ ]
+end
diff --git a/drivers/place/calendar.cr b/drivers/place/calendar.cr
new file mode 100644
index 00000000000..145b0698e08
--- /dev/null
+++ b/drivers/place/calendar.cr
@@ -0,0 +1,39 @@
+require "./calendar_common"
+
+class Place::Calendar < PlaceOS::Driver
+ include Place::CalendarCommon
+
+ # update to trigger build.
+ descriptive_name "PlaceOS Calendar"
+ generic_name :Calendar
+
+ uri_base "https://staff.api.com"
+
+ default_settings({
+ calendar_service_account: "service_account@email.address",
+ calendar_config: {
+ scopes: ["https://www.googleapis.com/auth/calendar", "https://www.googleapis.com/auth/admin.directory.user.readonly"],
+ domain: "primary.domain.com",
+ sub: "default.service.account@google.com",
+ issuer: "placeos@organisation.iam.gserviceaccount.com",
+ signing_key: "PEM encoded private key",
+ },
+ calendar_config_office: {
+ _note_: "rename to 'calendar_config' for use",
+ tenant: "",
+ client_id: "",
+ client_secret: "",
+ conference_type: nil, # This can be set to "teamsForBusiness" to add a Teams link to EVERY created Event
+ },
+
+ # only applies to google
+ rate_limit: 5,
+
+ # defaults to calendar_service_account if not configured
+ mailer_from: "email_or_office_userPrincipalName",
+ email_templates: {visitor: {checkin: {
+ subject: "%{name} has arrived",
+ text: "for your meeting at %{time}",
+ }}},
+ })
+end
diff --git a/drivers/place/calendar_common.cr b/drivers/place/calendar_common.cr
new file mode 100644
index 00000000000..a30f10c8490
--- /dev/null
+++ b/drivers/place/calendar_common.cr
@@ -0,0 +1,448 @@
+require "placeos-driver"
+require "place_calendar"
+require "placeos-driver/interface/mailer"
+require "qr-code"
+require "qr-code/export/png"
+
+module Place::CalendarCommon
+ include PlaceOS::Driver::Interface::Mailer
+
+ alias GoogleParams = NamedTuple(
+ scopes: String | Array(String),
+ domain: String,
+ sub: String,
+ issuer: String,
+ signing_key: String,
+ )
+
+ alias OfficeParams = NamedTuple(
+ tenant: String,
+ client_id: String,
+ client_secret: String,
+ conference_type: String | Nil,
+ )
+
+ macro included
+ @client : ::PlaceCalendar::Client? = nil
+ @service_account : String? = nil
+ @rate_limit : Int32 = 10
+ @channel : Channel(Nil) = Channel(Nil).new(9)
+ @in_flight : Channel(Nil) = Channel(Nil).new(10)
+
+ @queue_lock : Mutex = Mutex.new
+ @queue_size = 0
+ @flight_size = 0
+ @wait_time : Time::Span = 300.milliseconds
+
+ @mailer_from : String? = nil
+ end
+
+ def on_unload
+ @in_flight.close
+ @channel.close
+ end
+
+ def on_update
+ if proxy_config = setting?(NamedTuple(host: String, port: Int32, auth: NamedTuple(username: String, password: String)?), :proxy)
+ ConnectProxy.proxy_uri = "http://#{proxy_config[:host]}:#{proxy_config[:port]}"
+ if proxy_auth = proxy_config[:auth]
+ ConnectProxy.username = proxy_auth[:username]
+ ConnectProxy.password = proxy_auth[:password]
+ end
+ end
+
+ ConnectProxy.verify_tls = !!setting?(Bool, :proxy_verify_tls)
+ ConnectProxy.disable_crl_checks = !!setting?(Bool, :proxy_disable_crl)
+
+ @service_account = setting?(String, :calendar_service_account).presence
+ @rate_limit = setting?(Int32, :rate_limit) || 10
+ @wait_time = 1.second / @rate_limit
+
+ @mailer_from = setting?(String, :mailer_from).presence || @service_account
+ @templates = setting?(Templates, :email_templates) || Templates.new
+
+ @in_flight.close
+ @channel.close
+
+ # Work around crystal limitation of splatting a union
+ @client = begin
+ config = setting(GoogleParams, :calendar_config)
+ cli = ::PlaceCalendar::Client.new(**config)
+
+ # only google uses the rate limiter
+ @channel = Channel(Nil).new(9)
+ @in_flight = Channel(Nil).new(10)
+ spawn { rate_limiter }
+ cli
+ rescue
+ config = setting(OfficeParams, :calendar_config)
+ ::PlaceCalendar::Client.new(**config)
+ end
+ end
+
+ protected def client
+ # office365 execute queries against the users mailbox and hence doesn't require rate limiting
+ if @client.not_nil!.client_id == :office365
+ return yield(@client.not_nil!)
+ end
+
+ if (@wait_time * @queue_size) > 90.seconds
+ raise "wait time would be exceeded for API request, #{@queue_size} requests already queued"
+ end
+
+ @queue_lock.synchronize { @queue_size += 1 }
+ @channel.receive
+ @in_flight.send(nil)
+
+ begin
+ @queue_lock.synchronize { @queue_size -= 1; @flight_size += 1 }
+ result = yield @client.not_nil!
+ result
+ ensure
+ @in_flight.receive
+ @queue_lock.synchronize { @flight_size -= 1 }
+ end
+ end
+
+ def queue_size
+ @queue_size
+ end
+
+ def in_flight_size
+ @flight_size
+ end
+
+ def generate_svg_qrcode(text : String) : String
+ QRCode.new(text).as_svg
+ end
+
+ def generate_png_qrcode(text : String, size : Int32 = 128) : String
+ Base64.strict_encode QRCode.new(text).as_png(size: size)
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def send_mail(
+ to : String | Array(String),
+ subject : String,
+ message_plaintext : String? = nil,
+ message_html : String? = nil,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ )
+ sender = case from
+ in String
+ from
+ in Array(String)
+ from.first? || @mailer_from.not_nil!
+ in Nil
+ @mailer_from.not_nil!
+ end
+
+ logger.debug { "an email was sent from: #{sender}, to: #{to}" }
+
+ client &.calendar.send_mail(
+ sender,
+ to,
+ subject,
+ message_plaintext,
+ message_html,
+ resource_attachments,
+ attachments,
+ cc,
+ bcc
+ )
+ end
+
+ @[PlaceOS::Driver::Security(Level::Administrator)]
+ def access_token(user_id : String? = nil)
+ logger.info { "access token requested #{user_id}" }
+ client &.access_token(user_id)
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def get_groups(user_id : String)
+ logger.debug { "getting group membership for user: #{user_id}" }
+ client &.get_groups(user_id)
+ end
+
+ class ::PlaceCalendar::Member
+ property next_page : String? = nil
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def get_members(
+ group_id : String,
+ next_page : String? = nil
+ )
+ logger.debug { "listing members of group: #{group_id}" }
+
+ if group_id.includes?('@')
+ client do |_client|
+ if _client.client_id == :office365
+ logger.warn { "inefficient group members request. Recommended obtaining group.id versus using email" }
+ end
+ end
+ end
+ members = client &.get_members(group_id, next_link: next_page)
+
+ if member = members.first?
+ member.next_page = member.next_link
+ end
+ members
+ end
+
+ class ::PlaceCalendar::User
+ property next_page : String? = nil
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def list_users(
+ query : String? = nil,
+ limit : Int32? = nil,
+ filter : String? = nil,
+ next_page : String? = nil
+ )
+ logger.debug { "listing user details, query #{query || filter}, limit #{limit} (next: #{!!next_page})" }
+ users = client &.list_users(query, limit, filter: filter, next_link: next_page)
+ # next link is not returned to reduce payload size and used
+ # in the staff API for setting a header
+ if user = users.first?
+ user.next_page = user.next_link
+ end
+ users
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def get_user(user_id : String)
+ logger.debug { "getting user details for #{user_id}" }
+ client &.get_user_by_email(user_id)
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def list_calendars(user_id : String)
+ logger.debug { "listing calendars for #{user_id}" }
+ client &.list_calendars(user_id)
+ end
+
+ # NOTE:: GraphAPI Only!
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def get_user_manager(user_id : String)
+ logger.debug { "getting manager details for #{user_id}, note: graphAPI only" }
+ client do |_client|
+ if _client.client_id == :office365
+ _client.calendar.as(PlaceCalendar::Office365).client.get_user_manager(user_id).to_place_calendar
+ end
+ end
+ end
+
+ # NOTE:: GraphAPI Only! - here for use with configuration
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def list_groups(
+ query : String? = nil,
+ filter : String? = nil
+ )
+ logger.debug { "listing groups, filtering by #{filter || query}, note: graphAPI only" }
+ client do |_client|
+ if _client.client_id == :office365
+ _client.calendar.as(PlaceCalendar::Office365).client.list_groups(query, filter: filter).value.map(&.to_place_group)
+ end
+ end
+ end
+
+ # NOTE:: GraphAPI Only!
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def get_group(group_id : String)
+ logger.debug { "getting group #{group_id}, note: graphAPI only" }
+ client do |_client|
+ if _client.client_id == :office365
+ office_client = _client.calendar.as(PlaceCalendar::Office365).client
+ if group_id.includes?('@')
+ group = office_client.list_groups(filter: "mail eq '#{group_id}'").value.first?
+ return group.to_place_group if group
+ end
+ office_client.get_group(group_id).to_place_group
+ end
+ end
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def list_events(calendar_id : String, period_start : Int64, period_end : Int64, time_zone : String? = nil, user_id : String? = nil, include_cancelled : Bool = false, ical_uid : String? = nil)
+ location = time_zone ? Time::Location.load(time_zone) : Time::Location.local
+ period_start = Time.unix(period_start).in location
+ period_end = Time.unix(period_end).in location
+ user_id = user_id || @service_account.presence || calendar_id
+
+ logger.debug { "listing events for #{calendar_id}" }
+
+ _client = @client.not_nil!
+ events = if _client.client_id == :google
+ _client.calendar.as(PlaceCalendar::Google).list_events(user_id, calendar_id,
+ period_start: period_start,
+ period_end: period_end,
+ showDeleted: include_cancelled,
+ ical_uid: ical_uid,
+ # https://cloud.google.com/apis/docs/system-parameters (avoid hitting request quotas in common driver usage)
+ quotaUser: calendar_id[0..39]
+ )
+ else
+ _client.list_events(user_id, calendar_id,
+ period_start: period_start,
+ period_end: period_end,
+ showDeleted: include_cancelled,
+ ical_uid: ical_uid
+ )
+ end
+ # FFS MS doesn't always filter for icaluid correctly
+ events = events.select { |e| e.ical_uid == ical_uid } if ical_uid
+ events
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def get_event(calendar_id : String, event_id : String, user_id : String? = nil)
+ logger.debug { "fetching event #{event_id} on #{calendar_id}" }
+ user_id = user_id || @service_account.presence || calendar_id
+ client &.get_event(user_id, id: event_id, calendar_id: calendar_id)
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def decline_event(calendar_id : String, event_id : String, user_id : String? = nil, notify : Bool = false, comment : String? = nil)
+ user_id = user_id || @service_account.presence || calendar_id
+
+ logger.debug { "declining event #{event_id} on #{calendar_id}" }
+
+ client &.decline_event(user_id, event_id, calendar_id: calendar_id, notify: notify, comment: comment)
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def delete_event(calendar_id : String, event_id : String, user_id : String? = nil, notify : Bool = false, comment : String? = nil)
+ user_id = user_id || @service_account.presence || calendar_id
+
+ logger.debug { "deleting event #{event_id} on #{calendar_id}" }
+
+ client &.delete_event(user_id, event_id, calendar_id: calendar_id, notify: notify)
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def accept_event(calendar_id : String, event_id : String, user_id : String? = nil, notify : Bool = false, comment : String? = nil)
+ user_id = user_id || @service_account.presence || calendar_id
+
+ logger.debug { "accepting event #{event_id} on #{calendar_id}" }
+
+ client &.accept_event(user_id, event_id, calendar_id: calendar_id, notify: notify, comment: comment)
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def create_event(
+ title : String,
+ event_start : Int64,
+ event_end : Int64? = nil,
+ description : String = "",
+ attendees : Array(::PlaceCalendar::Event::Attendee) = [] of ::PlaceCalendar::Event::Attendee,
+ location : String? = nil,
+ timezone : String? = nil,
+ user_id : String? = nil,
+ calendar_id : String? = nil,
+ online_meeting_id : String? = nil,
+ online_meeting_provider : String? = nil,
+ online_meeting_url : String? = nil,
+ online_meeting_sip : String? = nil,
+ online_meeting_phones : Array(String)? = nil,
+ online_meeting_pin : String? = nil
+ )
+ user_id = (user_id || @service_account.presence || calendar_id).not_nil!
+ calendar_id = calendar_id || user_id
+
+ logger.debug { "creating event on #{calendar_id}" }
+
+ event = ::PlaceCalendar::Event.new(
+ host: calendar_id,
+ title: title,
+ body: description,
+ location: location,
+ timezone: timezone,
+ attendees: attendees,
+ online_meeting_id: online_meeting_id,
+ online_meeting_url: online_meeting_url,
+ online_meeting_sip: online_meeting_sip,
+ online_meeting_pin: online_meeting_pin,
+ online_meeting_phones: online_meeting_phones,
+ online_meeting_provider: online_meeting_provider,
+ )
+
+ tz = Time::Location.load(timezone) if timezone
+ event.event_start = timezone ? Time.unix(event_start).in tz.not_nil! : Time.unix(event_start)
+ event.event_end = timezone ? Time.unix(event_end).in tz.not_nil! : Time.unix(event_end) if event_end
+
+ event.all_day = true unless event_end
+
+ client &.create_event(user_id, event, calendar_id)
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def update_event(event : ::PlaceCalendar::Event, user_id : String? = nil, calendar_id : String? = nil)
+ user_id = (user_id || @service_account.presence || calendar_id).not_nil!
+ calendar_id = calendar_id || user_id
+
+ logger.debug { "updating event #{event.id} on #{event.host}" }
+
+ client &.update_event(user_id: user_id, event: event, calendar_id: calendar_id)
+ end
+
+ # returns: google or office365
+ def calendar_service_name
+ @client.not_nil!.client_id
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def create_notifier(resource : String, notification_url : String, expiration_time : Int64, client_secret : String? = nil, lifecycle_notification_url : String? = nil) : ::PlaceCalendar::Subscription
+ expires = Time.unix expiration_time
+ client &.create_notifier(resource, notification_url, expires, client_secret, lifecycle_notification_url: lifecycle_notification_url)
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def renew_notifier(subscription : ::PlaceCalendar::Subscription, new_expiration_time : Int64) : ::PlaceCalendar::Subscription
+ expires = Time.unix new_expiration_time
+ client &.renew_notifier(subscription, expires)
+ end
+
+ # NOTE:: GraphAPI Only!
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def reauthorize_notifier(subscription : ::PlaceCalendar::Subscription, new_expiration_time : Int64? = nil) : ::PlaceCalendar::Subscription
+ expires = new_expiration_time ? Time.unix(new_expiration_time) : nil
+ client &.reauthorize_notifier(subscription, expires)
+ end
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def delete_notifier(subscription : ::PlaceCalendar::Subscription) : Nil
+ client &.delete_notifier(subscription)
+ end
+
+ protected def rate_limiter
+ in_flight = @in_flight
+ channel = @channel
+ begin
+ loop do
+ break if channel.closed? || in_flight.closed?
+ begin
+ # ensure there is an available slot before allowing more requests
+ in_flight.send(nil)
+ in_flight.receive
+
+ # allow more requests through
+ channel.send(nil)
+ rescue error
+ logger.error(exception: error) { "issue with rate limiter" }
+ ensure
+ sleep @wait_time
+ end
+ end
+ rescue
+ # Possible error with logging exception, restart rate limiter silently
+ spawn { rate_limiter } unless terminated? || channel.closed? || in_flight.closed?
+ end
+ end
+end
diff --git a/drivers/place/calendar_delegated.cr b/drivers/place/calendar_delegated.cr
new file mode 100644
index 00000000000..59566589be5
--- /dev/null
+++ b/drivers/place/calendar_delegated.cr
@@ -0,0 +1,288 @@
+require "placeos-driver"
+require "place_calendar"
+require "rate_limiter"
+
+class Place::CalendarDelegated < PlaceOS::Driver
+ descriptive_name "PlaceOS Calendar (delegating to Staff API)"
+ generic_name :Calendar
+
+ uri_base "https://staff.app.api.com"
+
+ default_settings({
+ # PlaceOS X-API-key
+ api_key: "key-here",
+ rate_limit: 5,
+
+ jwt_private_key: <<-STRING
+-----BEGIN RSA PRIVATE KEY-----
+MIIEpAIBAAKCAQEAt01C9NBQrA6Y7wyIZtsyur191SwSL3MjR58RIjZ5SEbSyzMG
+3r9v12qka4UtpB2FmON2vwn0fl/7i3Jgh1Xth/s+TqgYXMebdd123wodrbex5pi3
+Q7PbQFT6hhNpnsjBh9SubTf+IeTIFeXUyqtqcDBmEoT5GxU6O+Wuch2GtbfEAmaD
+roy+uyB7P5DxpKLEx8nlVYgpx5g2mx2LufHvykVnx4bFzLezU93SIEW6yjPwUmv9
+R+wDM/AOg60dIf3hCh1DO+h22aKT8D8ysuFodpLTKCToI/AbK4IYOOgyGHZ7xizX
+HYXZdsqX5/zBFXu/NOVrSd/QBYYuCxbqe6tz4wIDAQABAoIBAQCEIRxXrmXIcMlK
+36TfR7h8paUz6Y2+SGew8/d8yvmH4Q2HzeNw41vyUvvsSVbKC0HHIIfzU3C7O+Lt
+9OeiBo2vTKrwNflBv9zPDHHoerlEBLsnNwQ7uEUeTWM9DHdBLwNaLzQApLD6q5iT
+OFW4NfIGpsydIt8R565PiNPDjIcTKwhbVdlsSbI87cLkQ9UuYIMRkvXSD1Q2cg3I
+VsC0SpE4zmfTe7YTZQ5yTxtsoLKPBXrSxhhGuhdayeN7A4YHFYVD39RuQ6/T2w2a
+W/0UaGOk8XWgydDpD5w9wiBdH2I4i6D35IynCcodc5JvmTajzJT+xj6aGjjvMSyq
+q5ZdwJ4JAoGBAOPdZgjbOCf3ONUoiZ5Qw/a4b4xJgMokgqZ5QGBF5GqV1Xsphmk1
+apYmgC7fmab/EOdycrQMS0am2FmtwX1f7gYgJoyWtK4TVkUc5rf+aoWi0ieIsegv
+rjhuiIAc12+vVIbegRgnq8mOI5icrwm6OkwdqHkwTt6VRYdJGEmu67n/AoGBAM3v
+RAd5uIjVwVDLXqaOpvF3pxWfl+cf6PJtAE5y+nbabeTmrw//fJMank3o7qCXkFZR
+F0OJ2tmENwV+LPM8Gy3So8YP2nkOz4bryaGrxQ4eMA+K9+RiACVaKv+tNx/NbyMS
+e9gg504u0cwa60XjM5KUKrmT3RXpY4YIfUPZ1J4dAoGAB6jalDOiSJ2j2G57acn3
+PGTowwN5g9IEXko3IsVWr0qIGZLExOaZxaBXsLutc5KhY9ZSCsFbCm3zWdhgZ7GA
+083i3dj3C970iHA3RToVJJbbj56ltFNd/OGiTwQpLcTsB3iVSFWVDbpsceXacG5F
+JWfd0O0RyaOk6a5IVbm+jMsCgYBglxAOfY4LSE8y6SCM+K3e5iNNZhymgHYPdwbE
+xPMrWgpfab/Evi2dBcgofM+oLU663bAOspMeoP/5qJPGxnNtC7ZbSMZNL6AxBVj+
+ZoW3uHsMXz8kNL8ixecTIxiO5xlwltPVrKExL46hsCKYFhfzcWGUx4DULTLMBCFU
++M/cFQKBgQC+Ite962yJOnE+bjtSReOrvR9+I+YNGqt7vyRa2nGFxL7ZNIqHss5T
+VjaMgjzVJqqYozNT/74pE/b9UjYyMzO/EhrjUmcwriMMan/vTbYoBMYWvGoy536r
+4n455vizig2c4/sxU5yu9AF9Dv+qNsGCx2e9uUOTDUlHM9NXwxU9rQ==
+-----END RSA PRIVATE KEY-----
+STRING
+ })
+
+ @api_key : String = ""
+ @host : String = ""
+ @jwt_private_key : String = ""
+
+ private getter! limiter : RateLimiter::Limiter
+
+ def on_update
+ rate_limit = setting?(Float64, :rate_limit) || 3.0
+ @limiter = RateLimiter.new(rate: rate_limit, max_burst: rate_limit.to_i)
+
+ @api_key = api_key = setting(String, :api_key)
+ transport.before_request do |request|
+ request.headers["X-API-Key"] = api_key unless request.headers["Authorization"]?
+ end
+
+ @host = URI.parse(config.uri.not_nil!).host.not_nil!
+ @debug_payload = setting?(Bool, :debug_payload) || false
+ @jwt_private_key = setting?(String, :jwt_private_key) || ""
+ end
+
+ protected def client(skip_limiter)
+ limiter.get!(max_wait: 90.seconds) unless skip_limiter
+ self
+ end
+
+ protected def process(response)
+ raise "request failed with #{response.status_code} (#{response.body})" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ @[Security(Level::Support)]
+ def get_groups(user_id : String, act_as_user : String? = nil)
+ logger.debug { "getting group membership for user: #{user_id}" }
+ process client(act_as_user).get("/api/staff/v1/people/#{user_id}/groups", headers: act_as(act_as_user))
+ end
+
+ @[Security(Level::Support)]
+ def get_members(group_id : String, act_as_user : String? = nil)
+ logger.debug { "listing members of group: #{group_id}" }
+ process client(act_as_user).get("/api/staff/v1/groups/#{group_id}/members", headers: act_as(act_as_user))
+ end
+
+ @[Security(Level::Support)]
+ def list_users(query : String? = nil, limit : Int32? = nil, act_as_user : String? = nil)
+ logger.debug { "listing user details, query #{query}" }
+ params = query ? {"q" => query} : {} of String => String?
+ process client(act_as_user).get("/api/staff/v1/people", params: params, headers: act_as(act_as_user))
+ end
+
+ @[Security(Level::Support)]
+ def get_user(user_id : String, act_as_user : String? = nil)
+ logger.debug { "getting user details for #{user_id}" }
+ process client(act_as_user).get("/api/staff/v1/people/#{user_id}", headers: act_as(act_as_user))
+ end
+
+ @[Security(Level::Support)]
+ def list_calendars(user_id : String, act_as_user : String? = nil)
+ logger.debug { "listing calendars for #{user_id}" }
+ process client(act_as_user).get("/api/staff/v1/people/#{user_id}/calendars", headers: act_as(act_as_user))
+ end
+
+ # NOTE:: GraphAPI Only!
+ @[Security(Level::Support)]
+ def get_user_manager(user_id : String, act_as_user : String? = nil)
+ logger.debug { "getting manager details for #{user_id}, note: graphAPI only" }
+ process client(act_as_user).get("/api/staff/v1/people/#{user_id}/manager", headers: act_as(act_as_user))
+ end
+
+ # NOTE:: GraphAPI Only! - here for use with configuration
+ @[Security(Level::Support)]
+ def list_groups(query : String? = nil, act_as_user : String? = nil)
+ logger.debug { "listing groups, filtering by #{query}, note: graphAPI only" }
+ params = query ? {"q" => query} : {} of String => String?
+ process client(act_as_user).get("/api/staff/v1/groups", params: params, headers: act_as(act_as_user))
+ end
+
+ # NOTE:: GraphAPI Only!
+ @[Security(Level::Support)]
+ def get_group(group_id : String, act_as_user : String? = nil)
+ logger.debug { "getting group #{group_id}, note: graphAPI only" }
+ process client(act_as_user).get("/api/staff/v1/groups/#{group_id}", headers: act_as(act_as_user))
+ end
+
+ protected def check_if_resource(email)
+ # attempt get the system the requested email is in
+ # assuming we are using this driver for resource calendars
+ email = email.downcase
+ response = get("/api/engine/v2/systems/", params: {
+ "email" => email,
+ "limit" => "1000",
+ })
+ if response.success?
+ result = Array(NamedTuple(id: String, email: String?)).from_json(response.body)
+ result.find { |sys| sys[:email].try(&.downcase) == email }.try &.[](:id)
+ end
+ end
+
+ @[Security(Level::Support)]
+ def list_events(
+ calendar_id : String,
+ period_start : Int64,
+ period_end : Int64,
+ time_zone : String? = nil,
+ user_id : String? = nil,
+ include_cancelled : Bool = false,
+ act_as_user : String? = nil
+ )
+ logger.debug { "listing events for #{calendar_id}" }
+
+ # Query the calendar
+ if system_id = check_if_resource(calendar_id)
+ params = {
+ "system_ids" => system_id,
+ }
+ else
+ params = {
+ "calendars" => calendar_id,
+ }
+ end
+
+ params["period_start"] = period_start.to_s
+ params["period_end"] = period_end.to_s
+ params["include_cancelled"] = "true" if include_cancelled
+ process client(act_as_user).get("/api/staff/v1/events", params: params, headers: act_as(act_as_user))
+ end
+
+ @[Security(Level::Support)]
+ def delete_event(
+ calendar_id : String,
+ event_id : String,
+ user_id : String? = nil,
+ notify : Bool = false,
+ act_as_user : String? = nil
+ )
+ logger.debug { "deleting event #{event_id} on #{calendar_id}" }
+
+ # Query the calendar
+ if system_id = check_if_resource(calendar_id)
+ params = {
+ "system_ids" => system_id,
+ }
+ else
+ params = {
+ "calendars" => calendar_id,
+ }
+ end
+
+ if notify
+ begin
+ process client(act_as_user).post("/api/staff/v1/events/#{event_id}/decline", params: params, headers: act_as(act_as_user))
+ rescue
+ process client(act_as_user).delete("/api/staff/v1/events/#{event_id}", params: params, headers: act_as(act_as_user))
+ end
+ else
+ params["notify"] = "false"
+ process client(act_as_user).delete("/api/staff/v1/events/#{event_id}", params: params, headers: act_as(act_as_user))
+ end
+ end
+
+ @[Security(Level::Support)]
+ def create_event(
+ title : String,
+ event_start : Int64,
+ event_end : Int64? = nil,
+ description : String = "",
+ attendees : Array(PlaceCalendar::Event::Attendee) = [] of PlaceCalendar::Event::Attendee,
+ location : String? = nil,
+ timezone : String? = nil,
+ user_id : String? = nil,
+ calendar_id : String? = nil,
+ online_meeting_id : String? = nil,
+ online_meeting_provider : String? = nil,
+ online_meeting_url : String? = nil,
+ online_meeting_sip : String? = nil,
+ online_meeting_phones : Array(String)? = nil,
+ online_meeting_pin : String? = nil,
+ act_as_user : String? = nil
+ )
+ calendar_id = calendar_id || user_id
+ logger.debug { "creating event on #{calendar_id}" }
+
+ event = PlaceCalendar::Event.new(
+ host: calendar_id,
+ title: title,
+ body: description,
+ location: location,
+ timezone: timezone,
+ attendees: attendees,
+ online_meeting_id: online_meeting_id,
+ online_meeting_url: online_meeting_url,
+ online_meeting_sip: online_meeting_sip,
+ online_meeting_pin: online_meeting_pin,
+ online_meeting_phones: online_meeting_phones,
+ online_meeting_provider: online_meeting_provider,
+ )
+
+ tz = Time::Location.load(timezone) if timezone
+ event.event_start = timezone ? Time.unix(event_start).in tz.not_nil! : Time.unix(event_start)
+ event.event_end = timezone ? Time.unix(event_end).in tz.not_nil! : Time.unix(event_end) if event_end
+ event.all_day = true unless event_end
+
+ process client(act_as_user).post("/api/staff/v1/events", body: event.to_json, headers: act_as(act_as_user))
+ end
+
+ struct User
+ include JSON::Serializable
+
+ getter name : String
+ getter email : String
+ getter id : String
+ end
+
+ protected def act_as(user_id : String?)
+ return ::HTTP::Headers.new unless user_id
+ return ::HTTP::Headers.new if @jwt_private_key.empty?
+
+ response = get("/api/engine/v2/users/#{user_id}")
+ raise "error fetching user details: #{response.status} (response.status_code)\n#{response.body}" unless response.success?
+ user = User.from_json(response.body)
+
+ logger.debug { "generating JWT for #{user.email}" }
+
+ payload = {
+ iss: "POS",
+ iat: 5.minutes.ago.to_unix,
+ exp: 10.minutes.from_now.to_unix,
+ jti: UUID.random.to_s,
+ aud: @host,
+ scope: ["public"],
+ sub: user.id,
+ u: {
+ n: user.name,
+ e: user.email,
+ p: 0,
+ r: [] of String,
+ },
+ }
+
+ jwt = JWT.encode(payload, @jwt_private_key, JWT::Algorithm::RS256)
+ HTTP::Headers{"Authorization" => "Bearer #{jwt}"}
+ end
+end
diff --git a/drivers/place/calendar_delegated_spec.cr b/drivers/place/calendar_delegated_spec.cr
new file mode 100644
index 00000000000..aa19c28f26e
--- /dev/null
+++ b/drivers/place/calendar_delegated_spec.cr
@@ -0,0 +1,23 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::CalendarDelegated" do
+ resp = exec(:list_groups)
+
+ expect_http_request do |request, response|
+ headers = request.headers
+ if headers["X-API-Key"]? == "key-here"
+ response.status_code = 200
+ response << %([{
+ "id": "1234",
+ "name": "Some Group"
+ }])
+ else
+ response.status_code = 401
+ end
+ end
+
+ resp.get.should eq(JSON.parse(%([{
+ "id": "1234",
+ "name": "Some Group"
+ }])))
+end
diff --git a/drivers/place/calendar_spec.cr b/drivers/place/calendar_spec.cr
new file mode 100644
index 00000000000..1b667f8b050
--- /dev/null
+++ b/drivers/place/calendar_spec.cr
@@ -0,0 +1,11 @@
+require "placeos-driver/spec"
+
+# this spec isn't implemented as this driver wraps an independently tested library
+# however sometimes it is useful to run tests here.
+#
+# To run specs, add proper credentials to the drivers settings
+# then you can check the responses here
+DriverSpecs.mock_driver "Place::Calendar" do
+ # exec(:get_members, "SalesandMarketing@0cbfs.onmicrosoft.com").get
+ # sleep 1
+end
diff --git a/drivers/place/chat/health_notification_models.cr b/drivers/place/chat/health_notification_models.cr
new file mode 100644
index 00000000000..0cf39ce4d1c
--- /dev/null
+++ b/drivers/place/chat/health_notification_models.cr
@@ -0,0 +1,143 @@
+require "json"
+require "./health_rooms_models"
+
+module Place::Chat
+ # room defaults are at: settings -> notifications
+ # Metadata stored on the user model:
+ # notifications = {
+ # general => NotificationSettings, (defaults)
+ # system_id => NotificationSettings (per-room override)
+ # }
+
+ struct NotifyEventSettings
+ include JSON::Serializable
+
+ def initialize
+ end
+
+ getter? enabled : Bool = true
+ getter? browser : Bool = true
+ getter? email : Bool = true
+ getter? sms : Bool = true
+
+ # minutes before notification
+ getter delay : Int32 = 3
+ end
+
+ struct NotificationSettings
+ include JSON::Serializable
+
+ def initialize
+ end
+
+ # only alert if the user selected me
+ getter? chosen_provider : Bool = false
+ getter? enabled : Bool = true
+
+ getter on_enter : NotifyEventSettings = NotifyEventSettings.new
+ # how often should it send notifications
+ getter on_recurr : NotifyEventSettings = NotifyEventSettings.new
+ # do we only notify if the user has been waiting for a certain amount of time
+ getter on_waiting : NotifyEventSettings = NotifyEventSettings.new
+ # settings if the patient has been waiting for a long time
+ getter on_escalate : NotifyEventSettings = NotifyEventSettings.new
+ end
+
+ class RoomMember
+ include JSON::Serializable
+
+ getter? available : Bool
+ property email : String
+ getter id : String
+ property name : String
+ property phone : String?
+ getter roles : Array(String)
+
+ @[JSON::Field(ignore: true)]
+ property! notifications : NotificationSettings
+
+ def coordinator?
+ roles.includes? "coordinator"
+ end
+
+ def clinician?
+ roles.includes? "clinician"
+ end
+
+ def admin?
+ roles.includes? "admin"
+ end
+ end
+
+ struct OpeningHours
+ def initialize(opening_times : Tuple(String, String, Bool))
+ @opens = parse_time opening_times[0]
+ @closes = parse_time opening_times[1]
+ @enabled = opening_times[2]
+ end
+
+ protected def parse_time(time : String)
+ hours, minutes = time.split(':').map(&.strip)
+ hours.to_i.hours + minutes.to_i.minutes
+ end
+
+ getter opens : Time::Span
+ getter closes : Time::Span
+ getter enabled : Bool
+
+ def is_open?(now : Time)
+ return false unless enabled
+ start_of_day = now.at_beginning_of_day
+ opening = start_of_day + opens
+ return false unless now >= opening
+ closing = start_of_day + closes
+ now < closing
+ end
+ end
+
+ # Room metadata => settings key
+ class RoomSettings
+ include JSON::Serializable
+
+ def initialize
+ end
+
+ getter available : Bool = true
+ getter open_24_7 : Bool = true
+ getter notifications : NotificationSettings do
+ NotificationSettings.new
+ end
+
+ property members : Array(RoomMember) = [] of RoomMember
+
+ @[JSON::Field(ignore: true)]
+ property! timezone : Time::Location
+
+ # 0 index == Monday
+ # open time, close time, enabled
+ getter opening_hours : Array(Tuple(String, String, Bool)) do
+ [] of Tuple(String, String, Bool)
+ end
+
+ @[JSON::Field(ignore: true)]
+ getter opening : Hash(Time::DayOfWeek, OpeningHours) do
+ times = {} of Time::DayOfWeek => OpeningHours
+ opening_hours.each_with_index do |times, index|
+ index += 1
+ times[Time::DayOfWeek.from_value(index)] = OpeningHours.new(times)
+ end
+ times
+ end
+
+ def is_open?(timezone : Time::Location)
+ return false unless available
+ return true if open_24_7
+ now = Time.local timezone
+
+ # more efficient version of
+ # opening[now.day_of_week].is_open? now
+ index = now.day_of_week.to_i - 1
+ OpeningHours.new(opening_hours[index]).is_open? now
+ end
+ end
+end
diff --git a/drivers/place/chat/health_rooms.cr b/drivers/place/chat/health_rooms.cr
new file mode 100644
index 00000000000..e9854970145
--- /dev/null
+++ b/drivers/place/chat/health_rooms.cr
@@ -0,0 +1,963 @@
+require "placeos-driver"
+require "placeos-driver/interface/sms"
+require "placeos-driver/interface/mailer"
+require "./health_rooms_models.cr"
+require "./health_notification_models.cr"
+
+class Place::Chat::HealthRooms < PlaceOS::Driver
+ descriptive_name "Health Chat Rooms"
+ generic_name :ChatRoom
+
+ EXAMPLE_SMS_TEMPLATE = "patient %{patient_name} is waiting in %{room_name} for an appointment at %{appointment_time}"
+
+ default_settings({
+ is_spec: true,
+ domain_id: "domain",
+ pool_size: 10,
+ # disconnect time in minutes
+ disconnect_timeout: 3,
+
+ sms_source: "Health",
+ sms_template: EXAMPLE_SMS_TEMPLATE,
+ notify_no_time: "no time specified",
+ })
+
+ def on_load
+ spawn { meeting_state_perform_save }
+ on_update
+ end
+
+ @disconnect_timeout : Time::Span = 3.minutes
+ @sms_source : String? = nil
+ @sms_template : String = ""
+ @notify_no_time : String = "no time specified"
+
+ def on_update
+ @update_mutex.synchronize do
+ if @update_expected > 0
+ @update_expected -= 1
+ logger.debug { "[admin] updating settings..." }
+ return
+ end
+ end
+
+ logger.debug { "[admin] updating settings..." }
+ is_spec = setting?(Bool, :is_spec) || false
+
+ domain = setting(String, :domain_id)
+ @sms_source = setting?(String, :sms_source)
+ @sms_template = setting?(String, :sms_template) || EXAMPLE_SMS_TEMPLATE
+ @notify_no_time = setting?(String, :notify_no_time) || "no time specified"
+ @pool_target_size = setting?(Int32, :pool_size) || 10
+ system_id = config.control_system.not_nil!.id
+
+ @disconnect_timeout = (setting?(Int32, :disconnect_timeout) || 3).minutes
+ @timezone_default = nil
+
+ schedule.clear
+ schedule.every(@disconnect_timeout / 3) { cleanup_disconnected }
+ schedule.every(5.minutes) { pool_cleanup }
+ schedule.in(1.second) { pool_cleanup } unless is_spec
+
+ monitoring = "#{domain}/chat/#{system_id}/guest/entry"
+ self[:monitoring] = monitoring
+
+ subscriptions.clear
+ meeting_state_restore
+ monitor(monitoring) { |_subscription, payload| new_guest(payload) }
+ monitor("#{domain}/chat/user/joined") { |_subscription, payload| user_joined(payload) }
+ monitor("#{domain}/chat/user/exited") do |_subscription, payload|
+ logger.debug { "[signal] user exited: #{payload}" }
+ user_id = NamedTuple(user_id: String).from_json(payload)[:user_id]
+ user_exited(user_id)
+ end
+ monitor("#{domain}/chat/user/left") { |_subscription, payload| user_left(payload) }
+ logger.debug { "[admin] settings update success!" }
+ end
+
+ # ================================================
+ # Save and restore meeting details
+ # ================================================
+
+ # logic to ensure we trigger saving as few times as possible
+ @save_requested : Channel(Nil) = Channel(Nil).new(10)
+ @state_save_mutex : Mutex = Mutex.new
+ @state_save_requested : Int32 = 0
+
+ # use this to trigger a save
+ def meeting_state_request_save
+ @save_requested.send nil
+ end
+
+ # ensures only a single save is ever queued
+ protected def meeting_state_perform_save
+ loop do
+ begin
+ @save_requested.receive
+ @state_save_mutex.synchronize do
+ if @state_save_requested >= 2
+ next
+ else
+ @state_save_requested += 1
+ end
+ end
+ spawn { meeting_state_save }
+ rescue error
+ logger.warn(exception: error) { "[state] performing save" }
+ end
+ break if terminated?
+ end
+ end
+
+ # ensures we ignore updates due to state save
+ @update_mutex : Mutex = Mutex.new
+ @update_expected : Int32 = 0
+
+ # ensures only one state save occurs at any one time
+ @meeting_state_save_mutex : Mutex = Mutex.new
+
+ protected def meeting_state_save
+ @meeting_state_save_mutex.synchronize do
+ begin
+ rooms = uninitialized Hash(SystemId, Array(SessionId))
+ meetings = uninitialized Hash(SessionId, Meeting)
+
+ # grab the data
+ @meeting_mutex.synchronize do
+ @room_mutex.synchronize do
+ rooms = @rooms.dup
+ meetings = @meetings.dup
+ end
+ end
+
+ logger.debug { "[state] performing state save" }
+
+ # save the state
+ @update_mutex.synchronize { @update_expected += 1 }
+ define_setting(:last_known_rooms, rooms)
+ @update_mutex.synchronize { @update_expected += 1 }
+ define_setting(:last_known_meetings, meetings)
+ ensure
+ @state_save_mutex.synchronize { @state_save_requested -= 1 }
+ end
+ end
+ end
+
+ protected def meeting_state_restore
+ restored = false
+ sessions = [] of String
+ @meeting_mutex.synchronize do
+ @room_mutex.synchronize do
+ return unless @meetings.empty?
+
+ if rooms = setting?(Hash(SystemId, Array(SessionId)), :last_known_rooms)
+ if meetings = setting?(Hash(SessionId, Meeting), :last_known_meetings)
+ @rooms = rooms
+ @meetings = meetings
+ sessions = meetings.keys
+ restored = true
+ end
+ end
+ end
+ end
+
+ return unless restored
+
+ logger.warn { "[state] last known meeting state restored" }
+ sessions.each { |session_id| update_meeting_state(session_id) }
+ check_disconnected
+ end
+
+ # ================================================
+ # Expose meeting details via bindings
+ # ================================================
+
+ protected def update_meeting_state(session_id, system_id = nil, old_system_id = nil) : Nil
+ self[session_id] = @meeting_mutex.synchronize { @meetings[session_id]?.try(&.dup) }
+ if old_system_id
+ self[old_system_id] = @room_mutex.synchronize { @rooms[old_system_id]?.try(&.dup) } || [] of String
+ end
+ if system_id
+ self[system_id] = @room_mutex.synchronize { @rooms[system_id]?.try(&.dup) } || [] of String
+ end
+
+ # update the overview of all the meetings
+ # NOTE:: locks must be obtained in the same order as other places
+ # in code to prevent deadlocks / invalid state
+ summary = Array(MeetingSummary).new(@rooms.size)
+ @meeting_mutex.synchronize do
+ @room_mutex.synchronize do
+ time_now = Time.utc.to_unix
+
+ @rooms.each do |sys_id, sessions|
+ total_participants = 0
+ waiting = 0
+ longest_wait = 0_i64
+ number_calls = sessions.size
+
+ sessions.each do |sesh_id|
+ call_details = @meetings[sesh_id]
+ num_participants = call_details.participants.size
+ total_participants += num_participants
+ initiator = call_details.participants[call_details.created_by_user_id]?
+ if num_participants == 1 && initiator && !initiator.contacted
+ waiting += 1
+ waiting_time = call_details.updated_at.to_unix
+ longest_wait = waiting_time if longest_wait == 0_i64 || waiting_time < longest_wait
+ end
+ end
+
+ summary << MeetingSummary.new(sys_id, number_calls, total_participants, waiting, longest_wait)
+ end
+ end
+ end
+
+ meeting_state_request_save
+
+ self[:chat_summary] = {
+ value: summary,
+ ts_hint: "complex",
+ ts_tag_keys: {"pos_system"},
+ measurement: "chat_summary",
+ }
+ end
+
+ # ================================================
+ # CHAT ENTRY SIGNAL
+ # ================================================
+
+ accessor staff_api : StaffAPI_1
+
+ protected def new_guest(payload : String)
+ logger.debug { "[signal] new guest arrived: #{payload}" }
+ room_guest = Hash(String, Participant).from_json payload
+ system_id, guest = room_guest.first
+ begin
+ conference = pool_checkout_conference
+ # guest JWT's are not needed
+ # webex_guest_jwt = video_conference.create_guest_bearer(guest.user_id, guest.name).get.as_s
+
+ register_new_guest(system_id, guest, conference)
+ rescue error
+ logger.error(exception: error) { "[meet] failed to obtain meeting details, kicking guest #{guest.name} (#{guest.user_id})" }
+ staff_api.kick_user(guest.user_id, guest.session_id, "failed to allocate meeting")
+ end
+ end
+
+ protected def register_new_guest(system_id, guest, conference)
+ meeting = Meeting.new(system_id, conference, guest)
+ meeting.timezone = timezone_system(system_id)
+ session_id = meeting.session_id
+ logger.info { "[meet] new guest has entered chat: #{guest.name}, user_id: #{guest.user_id}, session: #{session_id}" }
+
+ # update the session hash
+ @meeting_mutex.synchronize { @meetings[session_id] = meeting }
+
+ # update the room
+ sessions = [] of SessionId
+ @room_mutex.synchronize do
+ sessions = @rooms[system_id]? || sessions
+ sessions << meeting.session_id
+ @rooms[system_id] = sessions
+ end
+
+ # send the meeting details to the user
+ schedule.in(2.seconds) do
+ staff_api.transfer_user(guest.user_id, session_id, {
+ space_id: conference.space_id,
+ guest_pin: conference.guest_pin,
+ })
+ end
+
+ # notify that the user has joined
+ spawn { notify_entry(meeting) }
+
+ # update status
+ update_meeting_state(session_id, system_id)
+ rescue error
+ logger.fatal(exception: error) { "[meet] failure to setup guest conference" }
+
+ # remove the user at from the chat
+ session_id = guest.session_id.not_nil!
+ staff_api.kick_user(guest.user_id, session_id, "failed to allocate meeting")
+
+ # remove the user from the UI
+ meeting_remove_user(guest.user_id, session_id)
+ end
+
+ # chat user id unique => disconnect time
+ @recent_lock = Mutex.new
+ @concurrent_flag = false
+ @recently_disconnected = {} of String => Int64
+
+ # if we missed a signal we want to check twice, to avoid race conditions
+ # user => session_id
+ @missed_connections = {} of String => String
+
+ # in case we missed any signals from the backend (i.e. service crash)
+ # and the users have not re-connected
+ protected def check_disconnected
+ # grab the current state of meetings
+ connected = {} of String => Array(String)
+ disconnected = {} of String => Array(String)
+
+ @meeting_mutex.synchronize do
+ @meetings.each do |session_id, meeting|
+ conn = [] of String
+ disc = [] of String
+ meeting.participants.values.each do |par|
+ if par.connected
+ conn << par.user_id
+ else
+ disc << par.user_id
+ end
+ end
+ connected[session_id] = conn
+ disconnected[session_id] = disc
+ end
+ end
+
+ # ensure we haven't missed any signals, compare API to our state
+ new_missed = {} of String => String
+ old_missed = @missed_connections.dup
+
+ connected.each do |session_id, connected_users|
+ disconnected_users = disconnected[session_id]
+
+ begin
+ actual_users = staff_api.chat_members(session_id).get.as_a.map(&.as_s)
+
+ # reject any users that have actually just moved
+ connected_not_found = connected_users - actual_users
+ disconnected_found = disconnected_users & actual_users
+
+ # build a new not found list
+ @recent_lock.synchronize do
+ connected_not_found.each do |user_id|
+ new_missed[user_id] = session_id
+ end
+ end
+
+ disconnected_found.each do |user_id|
+ old_missed.delete(user_id)
+ mark_user_as_connected(session_id, user_id)
+ end
+ rescue error
+ logger.warn(exception: error) { "[cleanup] failed to obtain member list for #{session_id}" }
+ end
+ end
+
+ # mark as disconnected users that are not connected
+ disconnected = new_missed.keys & old_missed.keys
+ disconnected.each do |user_id|
+ # remove from new missed as it was found missing a second time
+ new_missed.delete user_id
+
+ # mark the user as deleted
+ begin
+ mark_user_as_disconnected(old_missed[user_id], user_id)
+ rescue
+ end
+ end
+
+ logger.debug { "[cleanup] complete, #{disconnected.size} disconnections, #{new_missed.size} pending disconnect" }
+
+ # update missed connections
+ @missed_connections = new_missed
+ end
+
+ protected def cleanup_disconnected : Nil
+ logger.debug { "[cleanup] removing disconnected clients from meetings..." }
+
+ # prevent concurrent running of this function
+ @recent_lock.synchronize do
+ return if @concurrent_flag
+ @concurrent_flag = true
+ end
+
+ # find disconnected users who have timed out
+ remove = [] of String
+ expired = @disconnect_timeout.ago.to_unix
+ @recent_lock.synchronize do
+ @recently_disconnected.each do |user_id, disconnected|
+ remove << user_id if disconnected <= expired
+ end
+ remove.each do |user_id|
+ @recently_disconnected.delete user_id
+ end
+ end
+
+ # find the sessions the users who are to be removed
+ remove.each { |user_id| user_exited(user_id) }
+ logger.debug { "[cleanup] removed #{remove.size} users who have timed out" }
+ check_disconnected
+ ensure
+ @recent_lock.synchronize { @concurrent_flag = false }
+ end
+
+ # finds all the session_ids that includes the specified user_id
+ def sessions_with_user(user_id : String) : Array(String)
+ sessions = [] of String
+ @meeting_mutex.synchronize do
+ @meetings.each do |session_id, meeting|
+ sessions << session_id if meeting.participants.has_key? user_id
+ end
+ end
+ sessions
+ end
+
+ protected def user_joined(payload : String) : Nil
+ logger.debug { "[signal] user joined: #{payload}" }
+ session_user = Hash(String, String).from_json payload
+ mark_user_as_connected *session_user.first
+ end
+
+ protected def mark_user_as_connected(session_id, user_id)
+ # check if we have seen this user and re-instate the user
+ @recent_lock.synchronize do
+ @missed_connections.delete(user_id)
+ @recently_disconnected.delete(user_id)
+ end
+
+ system_id = @meeting_mutex.synchronize do
+ @meetings[session_id]?.try &.mark_participant_connected(user_id, true)
+ end
+
+ # update the state
+ if system_id
+ update_meeting_state(session_id, system_id)
+ end
+ end
+
+ protected def user_left(payload : String)
+ logger.debug { "[signal] user left: #{payload}" }
+ session_user = Hash(String, String).from_json payload
+ mark_user_as_disconnected *session_user.first
+ end
+
+ protected def user_exited(user_id : String)
+ @recent_lock.synchronize do
+ @missed_connections.delete(user_id)
+ @recently_disconnected.delete(user_id)
+ end
+
+ sessions_with_user(user_id).each do |session_id|
+ begin
+ meeting_remove_user(user_id, session_id)
+ rescue error
+ logger.warn(exception: error) { "failed to remove user #{user_id} from #{session_id}" }
+ end
+ end
+ end
+
+ protected def mark_user_as_disconnected(session_id, user_id)
+ # check if the user is related to this system
+ system_id = @meeting_mutex.synchronize do
+ @meetings[session_id]?.try &.mark_participant_connected(user_id, false)
+ end
+
+ # update the state
+ if system_id
+ now = Time.utc.to_unix
+ @recent_lock.synchronize { @recently_disconnected[user_id] = now }
+ update_meeting_state(session_id, system_id)
+ end
+ end
+
+ # ================================================
+ # NOTIFICATIONS
+ # ================================================
+
+ getter timezone_default : String { system.timezone.presence || "UTC" }
+
+ def timezone_system(system_id : String)
+ staff_api.get_system(system_id).get["timezone"]?.try(&.as_s.presence) || timezone_default
+ rescue error
+ logger.error(exception: error) { "[notify] failed to obtain timezone information for #{system_id}" }
+ timezone_default
+ end
+
+ @[Security(Level::Support)]
+ def notify_inspect_meeting(session_id : String)
+ meeting = @meeting_mutex.synchronize { @meetings[session_id]?.try &.dup }
+ raise "meeting #{session_id} not found" unless meeting
+ system_info, room_settings = notify_load_notifications(meeting)
+ members = room_settings.try &.members.map do |member|
+ {member: member, notifications: member.notifications}
+ end
+ {settings: room_settings, members: members}
+ end
+
+ def notify_config(system_id : String, timezone : String)
+ timezone = Time::Location.load timezone
+
+ # system metadata settings => notifications
+ raw_settings = staff_api.metadata(system_id, "settings").get["settings"]?.try(&.to_json)
+ settings = raw_settings ? RoomSettings.from_json(raw_settings, root: "details") : RoomSettings.new
+ default_notifications = settings.notifications
+
+ # Grab the user notification settings
+ room_users = settings.members.compact_map do |member|
+ next unless member.available?
+ begin
+ user_data = staff_api.user(member.id).get.as_h
+ member.name = (user_data["nickname"]? || user_data["name"]).as_s
+ member.email = user_data["email"].as_s
+ member.phone = user_data["phone"]?.try &.as_s
+ notify_settings = if user_settings = staff_api.metadata(member.id, "settings").get["settings"]?.try(&.[]?("details")).try(&.to_json)
+ begin
+ NotificationSettings.from_json(user_settings, root: "notifications")
+ rescue parse_error
+ logger.warn(exception: parse_error) { "failed to parse user #{member.id} notification settings" }
+ # defaults if there is an error parsing settings
+ default_notifications
+ end
+ else
+ # defaults if the user hasn't explicitily configured any
+ default_notifications
+ end
+ next unless notify_settings.enabled?
+
+ # notify_settings.member = member
+ member.notifications = notify_settings
+ member
+ rescue error
+ logger.error(exception: error) { "[notify] failed to obtain user #{member.id} metadata" }
+ nil
+ end
+ end
+
+ settings.members = room_users
+ settings.timezone = timezone
+ settings
+ end
+
+ protected def notify_load_notifications(meeting)
+ system_info = meeting.system || PlaceOS::Driver::DriverModel::ControlSystem.from_json(staff_api.get_system(meeting.system_id).get.to_json)
+ room_settings = meeting.room_settings || notify_config(meeting.system_id, meeting.timezone)
+ meeting.room_settings = room_settings
+ meeting.system = system_info
+ {system_info, room_settings}
+ end
+
+ protected def notify_entry(meeting, delay = true)
+ system_info, room_settings = notify_load_notifications(meeting)
+ contact_members = meeting.notify_members_on_entry
+ participant = meeting.created_by_participant
+
+ contacted = @meeting_mutex.synchronize { meeting.creator_contacted? }
+ if contacted
+ logger.debug { "[notify] ignoring entry event as user has been contacted" }
+ return
+ end
+
+ sys = system
+ sms = sys.implementing(PlaceOS::Driver::Interface::SMS).first?
+ mailer = sys.implementing(PlaceOS::Driver::Interface::SMS).first?
+
+ logger.debug { "[notify] entry event found #{contact_members.size} members to contact. SMS #{!!sms}, email #{!!mailer}" }
+
+ contact_members.each do |member|
+ notify = member.notifications.on_enter
+ args = {
+ member_name: member.name,
+ member_email: member.email,
+ member_phone: member.phone,
+ member_id: member.id,
+ patient_name: participant.name,
+ patient_email: participant.email,
+ patient_phone: participant.phone,
+ patient_chat_only: participant.text_chat_only,
+ room_name: system_info.display_name,
+ room_code: system_info.code,
+ room_id: system_info.id,
+ appointment_time: participant.appointment_time.presence || @notify_no_time,
+ }
+
+ # sms
+ if sms && (phone = member.phone.presence) && notify.sms?
+ string = @sms_template
+ args.each { |key, value| string = string.gsub("%{#{key}}", value) }
+ sms.send_sms(phone, string, source: @sms_source)
+ end
+
+ # email
+ if mailer && (email = member.email.presence) && notify.email?
+ mailer.send_template(
+ to: {member.email},
+ template: {"chat_rooms", "notify_entry"},
+ args: args
+ )
+ end
+ end
+ rescue error
+ logger.error(exception: error) { "[notify] error notifying entry" }
+ end
+
+ # ================================================
+ # MEETING MANAGEMENT
+ # ================================================
+
+ # session id == the webrtc session id
+ alias SessionId = String
+
+ # system id == room
+ alias SystemId = String
+
+ # session_id => connection_details
+ @meetings : Hash(SessionId, Meeting) = {} of SessionId => Meeting
+ @meeting_mutex = Mutex.new
+
+ # system ids => session ids
+ @rooms = Hash(SystemId, Array(SessionId)).new { |hash, key| hash[key] = [] of SessionId }
+ @room_mutex = Mutex.new
+
+ def meeting_move_room(session_id : String, system_id : String) : Bool
+ old_system_id = nil
+ moved = false
+
+ @meeting_mutex.synchronize do
+ # grab the room id from the meeting details
+ if meeting = @meetings[session_id]?
+ old_system_id = meeting.system_id
+ meeting.system_id = system_id
+ moved = true
+
+ @room_mutex.synchronize do
+ # move the meeting to a new room
+ if room_sessions = @rooms[old_system_id]?
+ room_sessions.delete(session_id)
+
+ if room_sessions.empty?
+ @rooms.delete(old_system_id)
+ self[old_system_id] = nil
+ end
+
+ sessions = @rooms[system_id]? || [] of SessionId
+ sessions << session_id
+ @rooms[system_id] = sessions
+ end
+ end
+ end
+ end
+
+ logger.debug { "[meet] moving session: #{session_id} to system #{system_id} from #{old_system_id}" }
+
+ # update the system state
+ update_meeting_state(session_id, system_id, old_system_id) if moved
+ moved
+ end
+
+ # this is how staff members create a meeting room
+ # or join an existing meeting
+ def meeting_join(rtc_user_id : String, session_id : String, type : String? = nil, system_id : String? = nil, text_chat_only : Bool? = nil) : ConferenceDetails
+ placeos_user_id = invoked_by_user_id
+ user_details = staff_api.user(placeos_user_id).get
+ user_name = user_details["name"].as_s
+
+ participant = Participant.new(
+ user_id: rtc_user_id,
+ name: user_name,
+ email: user_details["email"].as_s,
+ type: type,
+ staff_user_id: placeos_user_id,
+ text_chat_only: text_chat_only
+ )
+
+ # TODO:: ensure the user has left any other room they might be in
+ @recent_lock.synchronize { @recently_disconnected.delete(rtc_user_id) }
+
+ # check we have the information we need
+ meeting = nil
+ @meeting_mutex.synchronize do
+ # check if we're joining an existing session
+ if meeting = @meetings[session_id]?
+ system_id = meeting.system_id
+ end
+ end
+
+ raise "must provide a system id if there is not an existing session" unless system_id
+ system_id = system_id.as(String)
+ timezone = meeting.try(&.timezone) || timezone_system(system_id)
+
+ logger.debug do
+ if meeting
+ "[meet] joining existing meeting: staff #{placeos_user_id}, session: #{session_id} in #{system_id}"
+ else
+ "[meet] creating new meeting: staff #{placeos_user_id}, session: #{session_id} in #{system_id}"
+ end
+ end
+
+ # guest JWT's are not needed
+ # webex_guest_jwt = video_conference.create_guest_bearer(placeos_user_id, user_name).get.as_s
+ conference = pool_checkout_conference unless meeting
+
+ @meeting_mutex.synchronize do
+ # create a new meeting if required
+ meeting = if meet = @meetings[session_id]?
+ system_id = meet.system_id
+ meet.add participant
+ meet
+ else
+ # most likely won't have to checkout a conference here
+ conference = conference || pool_checkout_conference
+ meet = Meeting.new(system_id.as(String), session_id, conference, participant)
+ meet.timezone = timezone
+ meet
+ end
+ @meetings[session_id] = meeting
+ conference = meeting.conference
+
+ @room_mutex.synchronize do
+ sessions = @rooms[system_id]? || [] of SessionId
+ sessions << session_id unless sessions.includes?(session_id)
+ @rooms[system_id] = sessions
+ end
+ end
+
+ # update status
+ update_meeting_state(session_id, system_id.as(String))
+ conference.as(ConferenceDetails)
+ end
+
+ protected def meeting_remove_user(rtc_user_id : String, session_id : String, placeos_user_id : String? = nil)
+ system_id = nil
+
+ @recent_lock.synchronize { @recently_disconnected.delete(rtc_user_id) }
+ @meeting_mutex.synchronize do
+ # grab the meeting details
+ meeting = @meetings[session_id]?
+ raise "meeting not found" unless meeting
+ system_id = meeting.system_id
+
+ # ensure the current place user is the rtc_user_id
+ if placeos_user_id
+ participant = meeting.participants[rtc_user_id]
+ owner_user_id = participant.staff_user_id
+ raise "user #{placeos_user_id} attempting to leave on behalf of #{owner_user_id}" unless owner_user_id == placeos_user_id
+ end
+
+ # remove the participant
+ meeting.remove rtc_user_id
+ if meeting.empty?
+ @meetings.delete session_id
+ @room_mutex.synchronize do
+ if sessions = @rooms[system_id]?
+ sessions.delete(session_id)
+ @rooms.delete(system_id) if sessions.empty?
+ end
+ end
+ end
+ end
+
+ # update status
+ update_meeting_state(session_id, system_id.as(String))
+ end
+
+ # the user is planning of leaving the meeting or has left
+ def meeting_leave(rtc_user_id : String, session_id : String) : Nil
+ placeos_user_id = invoked_by_user_id
+ logger.debug { "[meet] user leaving #{rtc_user_id} (#{placeos_user_id}) session #{session_id}" }
+
+ meeting_remove_user(rtc_user_id, session_id, placeos_user_id)
+ end
+
+ # kicks an individual from a meeting
+ def meeting_kick(rtc_user_id : String, session_id : String)
+ placeos_user_id = invoked_by_user_id
+ logger.warn { "[meet] kicking user #{rtc_user_id} from session #{session_id}, kicked by: #{placeos_user_id}" }
+
+ # remove the user at from the chat
+ staff_api.kick_user(rtc_user_id, session_id, "kicked by host")
+
+ # remove the user from the UI
+ user_exited(rtc_user_id)
+ end
+
+ # removes the meeting from the list and kicks anyone left in the meeting
+ def meeting_end(session_id : String)
+ placeos_user_id = invoked_by_user_id
+ system_id = nil
+ meeting = nil
+ logger.debug { "[meet] ending meeting #{session_id} ended by #{placeos_user_id}" }
+
+ # remove the meeting
+ @meeting_mutex.synchronize do
+ # grab the meeting details
+ meeting = @meetings.delete session_id
+ raise "meeting not found" unless meeting
+ system_id = meeting.system_id
+
+ @room_mutex.synchronize do
+ if sessions = @rooms[system_id]?
+ sessions.delete(session_id)
+ @rooms.delete(system_id) if sessions.empty?
+ end
+ end
+ end
+
+ # kick the users to notify them that the meeting has ended
+ meeting.not_nil!.participants.keys.each do |rtc_user_id|
+ staff_api.kick_user(rtc_user_id, session_id, "meeting ended")
+ end
+
+ # update status
+ update_meeting_state(session_id, system_id.as(String))
+ end
+
+ def guest_mark_as_contacted(rtc_user_id : String, session_id : String, contacted : Bool = true) : Bool
+ found = false
+ @meeting_mutex.synchronize do
+ if meeting = @meetings[session_id]?
+ if participant = meeting.participants[rtc_user_id]?
+ found = true
+ participant.contacted = contacted
+ end
+ end
+ end
+ logger.debug { "[meet] marking guest #{rtc_user_id} as contacted: #{contacted} in session #{session_id}" }
+ update_meeting_state(session_id) if found
+ found
+ end
+
+ def guest_move_session(rtc_user_id : String, session_id : String, new_session_id : String) : Bool
+ system_id = nil
+ new_meeting = nil
+
+ if @recent_lock.synchronize { @recently_disconnected[rtc_user_id]? }
+ logger.warn { "[meet] failed to move guest #{rtc_user_id} as disconnected" }
+ raise "can't move disconnected users, please wait for reconnection or kick"
+ end
+
+ # move the meeting
+ @meeting_mutex.synchronize do
+ if (meeting = @meetings[session_id]?) && (new_meeting = @meetings[new_session_id]?)
+ if participant = meeting.remove(rtc_user_id)
+ system_id = meeting.system_id
+ new_meeting.add participant
+
+ if meeting.empty?
+ @meetings.delete session_id
+ @room_mutex.synchronize { @rooms[system_id].try(&.delete(session_id)) }
+ end
+ end
+ end
+ end
+
+ # update state if the meeting was moved
+ if system_id && new_meeting
+ logger.debug { "[meet] moving user #{rtc_user_id} into #{new_session_id} from #{session_id}" }
+ update_meeting_state(session_id, system_id)
+ update_meeting_state(new_session_id)
+
+ # POST the update so the guest is aware of the new meeting details
+ conference = new_meeting.conference
+ staff_api.transfer_user(rtc_user_id, new_session_id, {
+ space_id: conference.space_id,
+ guest_pin: conference.guest_pin,
+ })
+ else
+ logger.warn { "[meet] failed to move guest #{rtc_user_id} as could not find session" }
+ end
+ !!system_id
+ end
+
+ # ================================================
+ # MEETING POOL
+ # ================================================
+ accessor video_conference : InstantConnect_1
+
+ @pool_lock : Mutex = Mutex.new
+ @pool_meet : Array(ConferenceDetails) = [] of ConferenceDetails
+ getter pool_size : Int32 = 0
+ getter pool_target_size : Int32 = 10
+
+ # how many new meetings do we need in the pool?
+ # set the pool size counter eagerly and then get to work
+ # this way concurrent calls to this function can occur
+ # and we don't block anything with the fiber.
+ #
+ # if a new user joins and they don't have meeting details then we can
+ # create them on the fly and not update the pool
+ protected def new_conference
+ logger.debug { "[pool] Creating new conference..." }
+ room_id = UUID.random.to_s
+ details = video_conference.create_meeting(room_id).get
+ ConferenceDetails.new room_id, details["space_id"].as_s, details["host_token"].as_s, details["guest_token"].as_s
+ end
+
+ protected def pool_cleanup
+ logger.debug { "[pool] Checking for expired meetings..." }
+ expired = 4.hours.ago
+ @pool_lock.synchronize do
+ @pool_meet = @pool_meet.reject do |meeting|
+ rejected = meeting.created_at < expired
+ # we reduce the size of the pool here as technically we
+ # could be running pool_ensure_size at the same time
+ if rejected
+ @pool_size -= 1
+ new_size = @pool_size
+ logger.debug { "[pool] --> Cleaning up expired meeting, pool size #{new_size}" }
+ end
+ rejected
+ end
+ end
+
+ pool_ensure_size
+ end
+
+ def pool_ensure_size : Nil
+ # calculate the number of meetings required
+ required = 0
+ @pool_lock.synchronize do
+ required = @pool_target_size - @pool_size
+ @pool_size = @pool_target_size
+ end
+
+ logger.debug { "[pool] Maintaining meeting pool size, #{required} new meetings required" }
+ return if required <= 0
+
+ # create the desired number of meetings
+ created = 0
+ begin
+ required.times do
+ meeting = new_conference
+ @pool_lock.synchronize { @pool_meet << meeting }
+ created += 1
+ end
+ rescue error
+ logger.error(exception: error) { "[pool] error creating pool meetings" }
+
+ # adjust size if pool update failed
+ if created != required
+ diff = required - created
+ @pool_lock.synchronize { @pool_size = @pool_size - diff }
+ end
+ end
+ end
+
+ def pool_checkout_conference : ConferenceDetails
+ meeting = @pool_lock.synchronize do
+ if @pool_meet.size > 0
+ @pool_size -= 1
+ @pool_meet.shift
+ end
+ end
+
+ logger.debug { "[pool] Checking out meeting, available in pool? #{!meeting.nil?}" }
+ spawn { pool_ensure_size }
+
+ meeting || new_conference
+ end
+
+ def pool_clear_conferences : Nil
+ logger.debug { "[pool] Clearing #{@pool_size} meetings from pool" }
+
+ @pool_lock.synchronize do
+ @pool_size = 0
+ @pool_meet = [] of ConferenceDetails
+ end
+
+ pool_ensure_size
+ end
+end
diff --git a/drivers/place/chat/health_rooms_models.cr b/drivers/place/chat/health_rooms_models.cr
new file mode 100644
index 00000000000..679ffef234e
--- /dev/null
+++ b/drivers/place/chat/health_rooms_models.cr
@@ -0,0 +1,185 @@
+require "json"
+require "./health_notification_models"
+
+module Place::Chat
+ struct ConferenceDetails
+ include JSON::Serializable
+
+ getter place_id : String
+ getter space_id : String
+ getter host_pin : String
+ getter guest_pin : String
+
+ @[JSON::Field(converter: Time::EpochConverter)]
+ getter created_at : Time
+
+ def initialize(@place_id, @space_id, @host_pin, @guest_pin)
+ @created_at = Time.utc
+ end
+ end
+
+ class Participant
+ include JSON::Serializable
+ include JSON::Serializable::Unmapped
+
+ property name : String
+ property email : String?
+ property phone : String?
+
+ # the type of guest (additional information)
+ @[JSON::Field(key: "role")]
+ property type : String?
+ property text_chat_only : Bool? = false
+
+ # the placeos user id we would like to notify if we have the user details
+ @[JSON::Field(key: "staff_id")]
+ property chat_to_user_id : String?
+ getter appointment_time : String? = nil
+
+ # the users chat id. This purely generated on the frontend
+ # not a placeos user_id, we use it to track browser instances
+ property user_id : String
+
+ # the chat session id the user is planning to use, the initial chat room
+ property session_id : String? = nil
+ property contacted : Bool = false
+ property staff_user_id : String? = nil
+
+ # as we don't care about this field anymore and don't want it saved in unmapped
+ @[JSON::Field(ignore: true)]
+ property captcha : String? = nil
+
+ property connected : Bool = true
+
+ def initialize(@user_id, @name, @email = nil, @phone = nil, @type = nil, @staff_user_id = nil, @text_chat_only = nil)
+ end
+ end
+
+ struct MeetingSummary
+ include JSON::Serializable
+
+ getter pos_system : String
+ getter call_count : Int32
+ getter waiting_count : Int32
+ getter participant_count : Int32
+ getter longest_wait_time : Int64
+
+ def initialize(@pos_system, @call_count, @participant_count, @waiting_count, @longest_wait_time)
+ end
+ end
+
+ class Meeting
+ include JSON::Serializable
+
+ # webrtc_user_id => participant
+ getter participants : Hash(String, Participant)
+ getter session_id : String
+ property system_id : String
+ property! timezone : String
+
+ # webrtc_user_id that created the meeting
+ getter created_by_user_id : String
+
+ @[JSON::Field(converter: Time::EpochConverter)]
+ getter created_at : Time = Time.utc
+
+ @[JSON::Field(converter: Time::EpochConverter)]
+ getter updated_at : Time
+
+ property conference : ConferenceDetails
+
+ @[JSON::Field(ignore: true)]
+ property room_settings : RoomSettings? = nil
+
+ @[JSON::Field(ignore: true)]
+ property system : PlaceOS::Driver::DriverModel::ControlSystem? = nil
+
+ protected def filter_members(clinician_selected : String?)
+ room_settings.not_nil!.members.compact_map do |member|
+ begin
+ next unless (member.clinician? || member.coordinator?) && member.notifications.enabled?
+ next if clinician_selected && member.notifications.chosen_provider? && member.id != clinician_selected
+ member
+ rescue error
+ # logger.warn(exception: error) { "checking user #{member.id} notification settings" }
+ member
+ end
+ end
+ end
+
+ def notify_members_on_entry : Array(RoomMember)
+ settings = room_settings
+ return [] of RoomMember unless settings
+
+ patient = participants[created_by_user_id]
+
+ # check for clinicians with on_enter notifications
+ clinician_selected = patient.chat_to_user_id.presence
+ contact = filter_members(clinician_selected)
+
+ # the clinician might not be in today
+ contact = filter_members(nil) if contact.empty? && clinician_selected
+
+ # contact the admin if there are no clinicians or coordinators
+ contact = settings.members if contact.empty?
+ contact
+ end
+
+ def initialize(@system_id, @conference, participant : Participant)
+ session_id = participant.session_id
+ raise "no session id provided for participant" unless session_id
+ @session_id = session_id
+ @created_at = @updated_at = Time.utc
+ @created_by_user_id = participant.user_id
+ @participants = {
+ participant.user_id => participant,
+ }
+ end
+
+ def initialize(@system_id, @session_id, @conference, participant : Participant)
+ @created_at = @updated_at = Time.utc
+ @created_by_user_id = participant.user_id
+ @participants = {
+ participant.user_id => participant,
+ }
+ end
+
+ def add(participant : Participant) : Participant
+ @participants[participant.user_id] = participant
+ @participants[@created_by_user_id]?.try(&.contacted=(true))
+ @updated_at = Time.utc
+ participant
+ end
+
+ def remove(webrtc_user_id : String) : Participant?
+ if participant = @participants.delete(webrtc_user_id)
+ @updated_at = Time.utc
+ participant
+ end
+ end
+
+ def created_by_participant
+ @participants[created_by_user_id]
+ end
+
+ def creator_contacted?
+ @participants[created_by_user_id]?.try &.contacted
+ end
+
+ def has_participant?(webrtc_user_id : String) : Participant?
+ @participants[webrtc_user_id]?
+ end
+
+ def mark_participant_connected(webrtc_user_id : String, state : Bool) : String?
+ if participant = has_participant?(webrtc_user_id)
+ old_state = participant.connected
+ participant.connected = state
+ return system_id unless old_state == state
+ end
+ end
+
+ def empty? : Bool
+ @participants.empty?
+ end
+ end
+end
diff --git a/drivers/place/chat/health_rooms_spec.cr b/drivers/place/chat/health_rooms_spec.cr
new file mode 100644
index 00000000000..08fed882df4
--- /dev/null
+++ b/drivers/place/chat/health_rooms_spec.cr
@@ -0,0 +1,35 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Chat::HealthRooms" do
+ system({
+ InstantConnect: {InstantConnectMock},
+ })
+
+ exec(:pool_size).get.should eq 0
+ exec(:pool_target_size).get.should eq 10
+
+ meeting = exec(:pool_checkout_conference).get
+ raise "no meeting returned" unless meeting
+
+ meeting["host_pin"].should eq "host-1234"
+ meeting["guest_pin"].should eq "guest-1234"
+
+ sleep 0.5
+
+ system(:InstantConnect_1)[:created].should eq(11)
+end
+
+# :nodoc:
+class InstantConnectMock < DriverSpecs::MockDriver
+ @called = 0
+
+ def create_meeting(room_id : String)
+ @called += 1
+ self[:created] = @called
+ {
+ space_id: room_id,
+ host_token: "host-1234",
+ guest_token: "guest-1234",
+ }
+ end
+end
diff --git a/drivers/place/demo/camera.cr b/drivers/place/demo/camera.cr
new file mode 100644
index 00000000000..aa620f5bea6
--- /dev/null
+++ b/drivers/place/demo/camera.cr
@@ -0,0 +1,179 @@
+require "placeos-driver"
+require "placeos-driver/interface/camera"
+require "placeos-driver/interface/powerable"
+
+class Place::Demo::Camera < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Camera
+
+ # Discovery Information.
+ generic_name :Camera
+ descriptive_name "Demo Camera"
+ udp_port 52381
+
+ alias Presets = Hash(String, Tuple(Int32, Int32, Int32))
+ @presets : Presets = {} of String => Tuple(Int32, Int32, Int32)
+
+ def on_update
+ @presets = setting?(Presets, :camera_presets) || @presets
+ self[:presets] = @presets.keys
+ end
+
+ # ====== Powerable Interface ======
+
+ def power(state : Bool)
+ self[:power] = state
+ end
+
+ def power?
+ case status?(Bool, :power)
+ when true
+ true
+ when false
+ false
+ when nil
+ self[:power] = false
+ end
+ end
+
+ # ====== Camera Interface ======
+
+ def home
+ logger.debug { "camera moved to home" }
+ end
+
+ def joystick(pan_speed : Float64, tilt_speed : Float64, index : Int32 | String = 0)
+ if pan_speed.zero? && tilt_speed.zero?
+ self[:moving] = false
+ else
+ self[:moving] = true
+ end
+ end
+
+ # moves to an absolute position
+ def pantilt(pan : Int32, tilt : Int32, speed : UInt8)
+ logger.debug { "moved to position pan #{pan}, tilt #{tilt}" }
+ end
+
+ def recall(position : String, index : Int32 | String = 0)
+ if pos = @presets[position]?
+ pan_pos, tilt_pos, zoom_pos = pos
+ pantilt(pan_pos, tilt_pos, 8_u8)
+ zoom_to(zoom_pos)
+ else
+ raise "unknown preset #{position}"
+ end
+ end
+
+ def save_position(name : String, index : Int32 | String = 0)
+ @presets[name] = {1, 2, zoom?}
+ save_presets
+ end
+
+ def remove_position(name : String, index : Int32 | String = 0)
+ @presets.delete(name)
+ save_presets
+ end
+
+ protected def save_presets
+ define_setting(:camera_presets, @presets)
+ self[:presets] = @presets.keys
+ end
+
+ # ====== Moveable Interface ======
+
+ def move(position : MoveablePosition, index : Int32 | String = 0)
+ @mutex.synchronize do
+ logger.debug { "move called: #{position}" }
+ case position
+ in .up?
+ joystick(pan_speed: 0.0, tilt_speed: 50.0)
+ in .down?
+ joystick(pan_speed: 0.0, tilt_speed: -50.0)
+ in .left?
+ joystick(pan_speed: -50.0, tilt_speed: 0.0)
+ in .right?
+ joystick(pan_speed: 50.0, tilt_speed: 0.0)
+ in .in?
+ zoom(:in)
+ in .out?
+ zoom(:out)
+ in .open?, .close?
+ # not supported
+ end
+ end
+ end
+
+ # ====== Zoomable Interface ======
+
+ # Zooms to an absolute position
+ def zoom_to(position : Float64, auto_focus : Bool = true, index : Int32 | String = 0)
+ position = position.clamp(0.0, 100.0).to_i
+ self[:zoom] = position
+ end
+
+ @zoom_task : PlaceOS::Driver::Proxy::Scheduler::TaskWrapper? = nil
+ @mutex : Mutex = Mutex.new
+
+ def zoom(direction : ZoomDirection, index : Int32 | String = 0)
+ @mutex.synchronize do
+ logger.debug { "zoom called: #{direction}" }
+ @zoom_task.try &.cancel
+ @zoom_task = nil
+
+ case direction
+ in .in?
+ self[:zooming] = true
+ @zoom_task = schedule.every(250.milliseconds) do
+ level = zoom? + 1
+ level = level.clamp(0, 100)
+ self[:zoom] = level
+
+ if level == 100
+ @zoom_task.try &.cancel
+ @zoom_task = nil
+ end
+ end
+ in .out?
+ self[:zooming] = true
+ @zoom_task = schedule.every(250.milliseconds) do
+ level = zoom? - 1
+ level = level.clamp(0, 100)
+ self[:zoom] = level
+
+ if level == 0
+ @zoom_task.try &.cancel
+ @zoom_task = nil
+ end
+ end
+ in .stop?
+ self[:zooming] = false
+ end
+ end
+ end
+
+ def zoom?
+ case (zoom = status?(Int32, :zoom))
+ in Int32
+ zoom
+ in Nil
+ self[:zoom] = 0
+ end
+ end
+
+ def pantilt?
+ logger.debug { "query pantilt" }
+ end
+
+ # ====== Stoppable Interface ======
+
+ def stop(index : Int32 | String = 0, emergency : Bool = false)
+ self[:moving] = false
+ end
+
+ # should be no incoming data
+ def received(data, task, sequence : UInt32? = nil) : Nil
+ logger.debug { "Camera sent: 0x#{data.hexstring}" }
+ task.try &.success
+ end
+end
diff --git a/drivers/place/demo/camera_spec.cr b/drivers/place/demo/camera_spec.cr
new file mode 100644
index 00000000000..a20aa9b7508
--- /dev/null
+++ b/drivers/place/demo/camera_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Demo::Camera" do
+end
diff --git a/drivers/place/demo/display.cr b/drivers/place/demo/display.cr
new file mode 100644
index 00000000000..1afe119c0ff
--- /dev/null
+++ b/drivers/place/demo/display.cr
@@ -0,0 +1,60 @@
+require "placeos-driver"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/switchable"
+
+class Place::Demo::Display < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Muteable
+
+ udp_port 6137
+
+ enum Input
+ DVI = 1
+ HDMI = 10
+ HDMI2 = 13
+ HDMI3 = 18
+ DisplayPort = 14
+ VGA = 2
+ VGA2 = 16
+ Component = 3
+ end
+
+ include Interface::InputSelection(Input)
+
+ descriptive_name "PlaceOS Demo Display"
+ generic_name :Display
+
+ def power(state : Bool)
+ self[:power] = state
+ end
+
+ def power?(**options)
+ self[:power].as_bool
+ end
+
+ def switch_to(input : Input)
+ self[:input] = input
+ end
+
+ getter? volume : Float64 = 0.0
+
+ def volume(level : Int32 | Float64)
+ self[:volume] = @volume = level.to_f64
+ end
+
+ def test_setting(key : String, payload : JSON::Any)
+ define_setting(key, payload)
+ payload
+ end
+
+ # There seems to only be audio mute available
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo,
+ )
+ self[:audio_mute] = state
+ self[:volume] = state ? 0 : @volume
+ end
+end
diff --git a/drivers/place/demo/location_services.cr b/drivers/place/demo/location_services.cr
new file mode 100644
index 00000000000..af959439f05
--- /dev/null
+++ b/drivers/place/demo/location_services.cr
@@ -0,0 +1,58 @@
+require "placeos-driver"
+
+class Place::Demo::LocationServices < PlaceOS::Driver
+ descriptive_name "Demo Location Services"
+ generic_name :LocationServices
+ description %(a mock version of location services for demos and testing)
+
+ default_settings({
+ building_zone: "zone_123",
+ level_zone: "zone_456",
+ system_id: "sys-123",
+ })
+
+ @building_zone : String = ""
+ @level_zone : String = ""
+ @system_id : String = ""
+
+ def on_update
+ @building_zone = setting(String, :building_zone)
+ @level_zone = setting(String, :level_zone)
+ @system_id = setting(String, :system_id)
+ end
+
+ def locate_user(email : String? = nil, username : String? = nil)
+ case rand(3)
+ when 0
+ [{
+ location: "wireless",
+ coordinates_from: "bottom-left",
+ x: 27.113065326953013,
+ y: 36.85052447328469,
+ lon: 55.27498749637098,
+ lat: 25.20090608906493,
+ mac: "66e0fd1279ce",
+ variance: 4.5194575835650745,
+ last_seen: 1601555879,
+ building: @building_zone,
+ level: @level_zone,
+ map_width: 1234.2,
+ map_height: 123.8,
+ }]
+ when 1
+ [{
+ location: "meeting",
+ mac: "meeting.room@resource.org.com",
+ event_id: "meet-1234567",
+ map_id: "map-1234",
+ sys_id: @system_id,
+ ends_at: 1.hour.from_now,
+ private: false,
+ level: @level_zone,
+ building: @building_zone,
+ }]
+ else
+ [] of String
+ end
+ end
+end
diff --git a/drivers/place/demo/lockers.cr b/drivers/place/demo/lockers.cr
new file mode 100644
index 00000000000..d1e7ab3170a
--- /dev/null
+++ b/drivers/place/demo/lockers.cr
@@ -0,0 +1,317 @@
+require "placeos-driver"
+require "placeos-driver/interface/lockers"
+require "../bookings/locker_models"
+
+class Place::Demo::Lockers < PlaceOS::Driver
+ include Interface::Lockers
+ include Place::LockerMetadataParser
+ alias PlaceLocker = PlaceOS::Driver::Interface::Lockers::PlaceLocker
+
+ descriptive_name "Locker Testing"
+ generic_name :DemoLockers
+ description %(used for end to end testing of locker interfaces)
+
+ accessor staff_api : StaffAPI_1
+ accessor locations : LocationServices_1
+
+ getter building_id : String do
+ locations.building_id.get.as_s
+ end
+
+ getter levels : Array(String) do
+ staff_api.systems_in_building(building_id).get.as_h.keys
+ end
+
+ # re-open class to add some helpers
+ class ::Place::Locker
+ # for tracking, not part of metadata
+ property allocated_to : String? = nil
+ property allocated_at : Time? = nil
+ property allocated_until : Time? = nil
+ property shared_with : Array(String) = [] of String
+
+ def release
+ @allocated_to = nil
+ @allocated_at = nil
+ @allocated_until = nil
+ @shared_with = [] of String
+ end
+
+ def allocated? : Bool
+ if time = self.allocated_until
+ if time > Time.utc
+ true
+ else
+ false
+ end
+ elsif self.allocated_to.presence
+ true
+ else
+ false
+ end
+ end
+
+ def not_allocated? : Bool
+ !allocated?
+ end
+ end
+
+ class ::PlaceOS::Driver::Interface::Lockers::PlaceLocker
+ def initialize(@bank_id, locker : ::Place::Locker, @building = nil)
+ @locker_id = locker.id
+ @locker_name = locker.name
+ @mac = "lb=#{@bank_id}&lk=#{locker.id}"
+ if time = locker.allocated_until
+ if time > Time.utc
+ in_use = true
+ @expires_at = time
+ else
+ in_use = false
+ @expires_at = nil
+ end
+ elsif allocated_to = locker.allocated_to
+ in_use = true
+ @expires_at = nil
+ else
+ in_use = false
+ @expires_at = nil
+ end
+ @allocated = in_use
+ @allocation_id = "#{locker.allocated_to}--#{locker.id}--#{locker.allocated_at.try(&.to_unix_ns)}" if in_use
+ @level = locker.level_id
+ end
+ end
+
+ # allocates a locker now, the allocation may expire
+ @[Security(Level::Support)]
+ def locker_allocate(
+ # PlaceOS user id
+ user_id : String,
+
+ # the locker location
+ bank_id : String | Int64,
+
+ # allocates a random locker if this is nil
+ locker_id : String | Int64? = nil,
+
+ # attempts to create a booking that expires at the time specified
+ expires_at : Int64? = nil,
+ ) : PlaceLocker
+ bank = locker_banks[bank_id.to_s]
+ locker_id = locker_id ? locker_id : bank.locker_hash.values.select(&.not_allocated?).sample.id
+ locker = bank.locker_hash[locker_id.to_s]
+ locker.allocated_to = user_id
+ locker.allocated_at = Time.utc
+ locker.allocated_until = Time.unix(expires_at) if expires_at
+ PlaceLocker.new(bank_id, locker, building_id)
+ rescue
+ raise "no available lockers"
+ end
+
+ # return the locker to the pool
+ @[Security(Level::Support)]
+ def locker_release(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+
+ # release / unshare just this user - otherwise release the whole locker
+ owner_id : String? = nil,
+ ) : Nil
+ locker = locker_banks[bank_id.to_s].locker_hash[locker_id.to_s]
+ if locker.allocated_to == owner_id
+ locker.release
+ else
+ locker.shared_with.delete(owner_id)
+ end
+ end
+
+ # a list of lockers that are allocated to the user
+ @[Security(Level::Support)]
+ def lockers_allocated_to(user_id : String) : Array(PlaceLocker)
+ now = Time.utc
+ building = building_id
+
+ locker_banks.values.flat_map do |bank|
+ bank.locker_hash.values.compact_map do |locker|
+ if locker.allocated_to == user_id
+ if time = locker.allocated_until
+ PlaceLocker.new(bank.id, locker, building) if time > now
+ else
+ PlaceLocker.new(bank.id, locker, building)
+ end
+ end
+ end
+ end
+ end
+
+ @[Security(Level::Support)]
+ def locker_share(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+ owner_id : String,
+ share_with : String,
+ ) : Nil
+ locker = locker_banks[bank_id.to_s].locker_hash[locker_id.to_s]
+ perform_share = false
+ if locker.allocated_to == owner_id
+ if time = locker.allocated_until
+ perform_share = time > Time.utc
+ else
+ perform_share = true
+ end
+ end
+
+ if perform_share
+ locker.shared_with << share_with
+ locker.shared_with.uniq!
+ end
+ end
+
+ @[Security(Level::Support)]
+ def locker_unshare(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+ owner_id : String,
+ # the individual you previously shared with (optional)
+ shared_with_id : String? = nil,
+ ) : Nil
+ locker = locker_banks[bank_id.to_s].locker_hash[locker_id.to_s]
+ perform_share = false
+ if locker.allocated_to == owner_id
+ if time = locker.allocated_until
+ perform_share = time > Time.utc
+ else
+ perform_share = true
+ end
+ end
+
+ if perform_share
+ if shared_with_id
+ locker.shared_with.delete shared_with_id
+ else
+ locker.shared_with = [] of String
+ end
+ end
+ end
+
+ # a list of user-ids that the locker is shared with.
+ # this can be placeos user ids or emails
+ @[Security(Level::Support)]
+ def locker_shared_with(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+ owner_id : String,
+ ) : Array(String)
+ locker = locker_banks[bank_id.to_s].locker_hash[locker_id.to_s]
+ perform_share = false
+ if locker.allocated_to == owner_id
+ if time = locker.allocated_until
+ perform_share = time > Time.utc
+ else
+ perform_share = true
+ end
+ end
+
+ if perform_share
+ locker.shared_with
+ else
+ [] of String
+ end
+ end
+
+ @[Security(Level::Support)]
+ def locker_unlock(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+
+ # sometimes required by locker systems
+ owner_id : String? = nil,
+ # time in seconds the locker should be unlocked
+ # (can be ignored if not implemented)
+ open_time : Int32 = 60,
+ # optional pin code - if user entered from a kiosk
+ pin_code : String? = nil,
+ ) : Nil
+ end
+
+ # ===================================
+ # Locatable Interface functions
+ # ===================================
+ def locate_user(email : String? = nil, username : String? = nil)
+ logger.debug { "sensor incapable of locating #{email} or #{username}" }
+ [] of Nil
+ end
+
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ logger.debug { "sensor incapable of tracking #{email} or #{username}" }
+ # we could find the floorsense user, grab the reservations the user has
+ # and list them here, but probably not amazingly useful
+ [] of String
+ end
+
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ # "lb=#{@bank_id}&lk=#{locker.id}"
+ return nil unless mac_address.starts_with?("lb=")
+ floor_mac = URI::Params.parse mac_address
+ locker_bank = floor_mac["lb"]
+ locker_key = floor_mac["lk"]
+ locker = locker_banks[locker_bank].locker_hash[locker_key]
+
+ has_reservation = false
+ if user_id = locker.allocated_to
+ if time = locker.allocated_until
+ has_reservation = time > Time.utc
+ else
+ has_reservation = true
+ end
+ end
+
+ if has_reservation
+ {
+ location: "locker",
+ assigned_to: staff_api.user(locker.allocated_to).get["email"].as_s,
+ mac_address: mac_address,
+ }
+ end
+ rescue
+ nil
+ end
+
+ def device_locations(zone_id : String, location : String? = nil)
+ logger.debug { "searching lockers in zone #{zone_id}" }
+ return [] of Nil if location && location != "locker"
+
+ building = building_id
+ level_zone = zone_id == building ? nil : zone_id
+ return [] of Nil if level_zone && !level_zone.in?(levels)
+
+ now = Time.utc
+ locker_banks.values.flat_map do |bank|
+ next [] of PlaceLocker if level_zone && bank.level_id != level_zone
+
+ bank.locker_hash.values.compact_map do |locker|
+ if locker.allocated_to
+ if time = locker.allocated_until
+ PlaceLocker.new(bank.id, locker, building) if time > now
+ else
+ PlaceLocker.new(bank.id, locker, building)
+ end
+ end
+ end
+ end
+ end
+
+ @[Security(Level::Support)]
+ def release_all_lockers : Int32
+ released = 0
+ locker_banks.values.flat_map do |bank|
+ bank.locker_hash.values.compact_map do |locker|
+ if locker.allocated_to
+ locker.release
+ released += 1
+ end
+ end
+ end
+ released
+ end
+end
diff --git a/drivers/place/demo/lockers_spec.cr b/drivers/place/demo/lockers_spec.cr
new file mode 100644
index 00000000000..de880250e72
--- /dev/null
+++ b/drivers/place/demo/lockers_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Demo::Lockers" do
+end
diff --git a/drivers/place/demo/room_sensor.cr b/drivers/place/demo/room_sensor.cr
new file mode 100644
index 00000000000..391e70a9c08
--- /dev/null
+++ b/drivers/place/demo/room_sensor.cr
@@ -0,0 +1,169 @@
+require "placeos-driver"
+require "placeos-driver/interface/sensor"
+require "placeos-driver/interface/locatable"
+
+class Place::Demo::RoomSensor < PlaceOS::Driver
+ include Interface::Sensor
+ include Interface::Locatable
+
+ # Discovery Information
+ descriptive_name "Demo Room Sensor"
+ generic_name :Sensor
+
+ default_settings({
+ sensor_id: "1234",
+ capacity: 2,
+ default_count: 0,
+ })
+
+ @sensor_id : String = "1234"
+ @capacity : Int32 = 2
+ getter! count : Int32
+ @timestamp : Int64 = 0_i64
+
+ def on_update
+ @capacity = setting?(Int32, :capacity) || 2
+ @count ||= setting?(Int32, :default_count) || 0
+ @sensor_id = setting?(String, :sensor_id) || module_id
+ @timestamp = Time.utc.to_unix
+ update_state
+ end
+
+ def set_sensor(new_count : Int32)
+ @timestamp = Time.utc.to_unix
+ @count = new_count
+ update_state
+ end
+
+ protected def update_state
+ self["people"] = count
+ self["presence"] = count > 0
+ end
+
+ # Finds the building ID for the current location services object
+ getter building_id : String do
+ zone_ids = system["StaffAPI"].zones(tags: "building").get.as_a.map(&.[]("id").as_s)
+ (zone_ids & system.zones).first
+ rescue error
+ logger.warn(exception: error) { "unable to determine building zone id" }
+ raise error
+ end
+
+ # Finds the level ID for the current location services object
+ getter level_id : String do
+ zone_ids = system["StaffAPI"].zones(tags: "level").get.as_a.map(&.[]("id").as_s)
+ (zone_ids & system.zones).first
+ rescue error
+ logger.warn(exception: error) { "unable to determine building zone id" }
+ raise error
+ end
+
+ # ======================
+ # Sensor interface
+ # ======================
+
+ SENSOR_TYPES = {SensorType::PeopleCount, SensorType::Presence}
+ NO_MATCH = [] of Interface::Sensor::Detail
+
+ def sensors(type : String? = nil, mac : String? = nil, zone_id : String? = nil) : Array(Interface::Sensor::Detail)
+ logger.debug { "sensors of type: #{type}, mac: #{mac}, zone_id: #{zone_id} requested" }
+
+ return NO_MATCH if mac && mac != "demo-#{@sensor_id}"
+ if type
+ sensor_type = SensorType.parse(type)
+ return NO_MATCH unless SENSOR_TYPES.includes?(sensor_type)
+ end
+ return NO_MATCH if zone_id && !system.zones.includes?(zone_id)
+
+ if sensor_type
+ sensor = build_sensor_details(sensor_type)
+ return NO_MATCH unless sensor
+ [sensor]
+ else
+ space_sensors
+ end
+ end
+
+ def sensor(mac : String, id : String? = nil) : Interface::Sensor::Detail?
+ logger.debug { "sensor mac: #{mac}, id: #{id} requested" }
+ return nil unless id
+ return nil unless mac == "demo-#{@sensor_id}"
+
+ case id
+ when "people"
+ build_sensor_details(:people_count)
+ when "presence"
+ build_sensor_details(:presence)
+ end
+ end
+
+ protected def build_sensor_details(sensor : SensorType) : Detail?
+ time = @timestamp
+ id = "people"
+
+ value = case sensor
+ when .people_count?
+ count.to_f64
+ when .presence?
+ id = "presence"
+ count > 0 ? 1.0 : 0.0
+ else
+ raise "sensor type unavailable: #{sensor}"
+ end
+ return nil unless value
+
+ Detail.new(
+ type: sensor,
+ value: value,
+ last_seen: time,
+ mac: "demo-#{@sensor_id}",
+ id: id,
+ name: "Demo Sensor (#{@sensor_id})",
+ module_id: module_id,
+ binding: id
+ )
+ end
+
+ protected def space_sensors
+ [
+ build_sensor_details(:people_count),
+ build_sensor_details(:presence),
+ ].compact
+ end
+
+ # ===================================
+ # Locatable Interface functions
+ # ===================================
+ def locate_user(email : String? = nil, username : String? = nil)
+ logger.debug { "sensor incapable of locating #{email} or #{username}" }
+ [] of Nil
+ end
+
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ logger.debug { "sensor incapable of tracking #{email} or #{username}" }
+ [] of String
+ end
+
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ logger.debug { "sensor incapable of tracking #{mac_address}" }
+ nil
+ end
+
+ def device_locations(zone_id : String, location : String? = nil)
+ logger.debug { "searching locatable in zone #{zone_id}" }
+ return [] of Nil unless {building_id, level_id}.includes?(zone_id)
+ return [] of Nil if location && location != "area"
+
+ [{
+ location: "area",
+ at_location: count,
+ map_id: system.map_id,
+ level: level_id,
+ building: building_id,
+ capacity: @capacity,
+
+ module_id: module_id,
+
+ }]
+ end
+end
diff --git a/drivers/place/demo/room_sensor_spec.cr b/drivers/place/demo/room_sensor_spec.cr
new file mode 100644
index 00000000000..ff5ad5af668
--- /dev/null
+++ b/drivers/place/demo/room_sensor_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Demo::RoomSensor" do
+end
diff --git a/drivers/place/demo/switcher.cr b/drivers/place/demo/switcher.cr
new file mode 100644
index 00000000000..725a15ccb8b
--- /dev/null
+++ b/drivers/place/demo/switcher.cr
@@ -0,0 +1,39 @@
+require "placeos-driver"
+require "placeos-driver/interface/switchable"
+
+# This is a mock switch for demoing AV interfaces
+
+class Place::Demo::Switcher < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::Switchable(Int32, Int32)
+
+ descriptive_name "PlaceOS Demo Switcher"
+ generic_name :Switcher
+
+ default_settings({
+ inputs: 6,
+ outputs: 6,
+ })
+
+ getter inputs : Int32 { setting(Int32, :inputs) }
+ getter outputs : Int32 { setting(Int32, :outputs) }
+
+ def on_update
+ @inputs = nil
+ @outputs = nil
+ end
+
+ def switch_to(input : Int32)
+ raise "invalid input #{input}, supported values 0 -> #{inputs}" if input < 0 || input > inputs
+ logger.debug { "switching all outputs to input #{input}" }
+ (1..outputs).each { |outp| self["output#{outp}"] = input }
+ true
+ end
+
+ def switch(map : Hash(Input, Array(Output)), layer : SwitchLayer? = nil)
+ logger.debug { "switching #{map} on layer #{layer || SwitchLayer::All}" }
+ map.each do |input, outputs|
+ outputs.each { |outp| self["output#{outp}"] = input }
+ end
+ true
+ end
+end
diff --git a/drivers/place/demo/test_ssh.cr b/drivers/place/demo/test_ssh.cr
new file mode 100644
index 00000000000..0446806a3d4
--- /dev/null
+++ b/drivers/place/demo/test_ssh.cr
@@ -0,0 +1,30 @@
+require "placeos-driver"
+
+class Place::Demo::TestSSH < PlaceOS::Driver
+ # Discovery Information
+ descriptive_name "SSH Testing Tool"
+ generic_name :TestSSH
+ tcp_port 22
+
+ default_settings({
+ ssh: {
+ username: :root,
+ password: :password,
+ },
+ })
+
+ def ls(dir : String = "./", modifiers : String = "")
+ exec("ls -#{modifiers} #{dir}").gets_to_end
+ end
+
+ def run(command : String, wait : Bool = true)
+ logger.debug { "SSH command:\n#{command}" }
+ send "#{command}\n", wait: wait
+ end
+
+ def received(data, task)
+ data = String.new(data)
+ logger.debug { "SSH response:\n#{data}" }
+ task.try &.success(data)
+ end
+end
diff --git a/drivers/place/demo/test_ssh_spec.cr b/drivers/place/demo/test_ssh_spec.cr
new file mode 100644
index 00000000000..23aa904cb4e
--- /dev/null
+++ b/drivers/place/demo/test_ssh_spec.cr
@@ -0,0 +1,8 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Demo::TestSSH" do
+ resp = exec(:run, "ls")
+ should_send "ls\n"
+ responds "bin docker-compose.yml examples lib\n"
+ resp.get.should eq "bin docker-compose.yml examples lib\n"
+end
diff --git a/drivers/place/desk/allocations.cr b/drivers/place/desk/allocations.cr
new file mode 100644
index 00000000000..8c04ece3d1e
--- /dev/null
+++ b/drivers/place/desk/allocations.cr
@@ -0,0 +1,433 @@
+require "placeos-driver"
+require "http"
+require "csv"
+
+class Place::Desk::Allocations < PlaceOS::Driver
+ descriptive_name "PlaceOS Desk Allocations"
+ generic_name :DeskAllocations
+ description %(helper for exporting and importing desk allocations)
+
+ accessor staff_api : StaffAPI_1
+ accessor calendar : Calendar_1
+
+ default_settings({
+ allocation_list_url: "http://org.com/desk/allocations",
+ polling_cron: "*/15 * * * *",
+ testing: false,
+ })
+
+ @allocation_list_url : String = "http://org.com/desk/allocations"
+
+ getter testing : Bool = false
+
+ def on_update
+ @allocation_list_url = setting(String, :allocation_list_url)
+ @testing = setting?(Bool, :testing) || false
+ schedule.clear
+ schedule.cron(setting(String, :polling_cron)) { pull_and_sync_desk_allocations(testing) }
+ end
+
+ struct Zone
+ include JSON::Serializable
+
+ getter id : String
+ getter name : String
+ getter display_name : String?
+ getter tags : Array(String)
+ getter timezone : String?
+
+ property code : String?
+ property parent_id : String?
+ end
+
+ getter buildings : Hash(String, Zone) do
+ Array(Zone).from_json(staff_api.zones(tags: {"building"}).get.to_json).sort_by(&.name).to_h { |zone| {zone.id, zone} }
+ end
+
+ getter all_levels : Array(Zone) do
+ Array(Zone).from_json(staff_api.zones(tags: {"level"}).get.to_json).sort_by(&.name)
+ end
+
+ struct Desk
+ include JSON::Serializable
+
+ getter id : String
+ getter name : String
+ getter level_code : String
+ getter building_code : String
+ getter allocation_email : String?
+
+ getter building_id : String
+ getter level_id : String
+
+ # TODO:: dont think I need this
+ # getter org : String
+ # getter campus : String
+
+ def initialize(@id, @name, @level_code, @building_code, @allocation_email, @building_id, @level_id)
+ end
+ end
+
+ def desks : Hash(String, Desk)
+ logger.debug { "getting list of all desks" }
+ response = {} of String => Desk
+
+ l = all_levels
+ l.each do |level|
+ logger.debug { " - processing level #{level.name}" }
+
+ all_desks = staff_api.metadata(level.id, "desks").get.dig?("desks", "details")
+ if all_desks && (building = buildings[level.parent_id]?)
+ desks = all_desks.as_a
+
+ building_code = building.code.presence || building.display_name.presence || building.name
+ level_code = level.code.presence || level.display_name.presence || level.name
+
+ desks.each do |desk|
+ desk_id = desk["id"].as_s
+ response[desk_id] = Desk.new(
+ desk_id,
+ desk["name"].as_s?.presence || desk["id"].as_s,
+ level_code,
+ building_code,
+ desk["assigned_to"]?.try(&.as_s?.presence),
+ building.id,
+ level.id
+ )
+ end
+ end
+ end
+
+ logger.debug { "found #{response.size} desks" }
+ response
+ end
+
+ # Provides a list of desk information to a desk management tool
+ def get_desks(method : String, headers : Hash(String, Array(String)), body : String)
+ logger.debug { "webhook received: #{method},\nheaders #{headers},\nbody size #{body.size}" }
+
+ payload = CSV.build do |csv|
+ csv.row "desk_id", "desk_name", "building", "level", "allocation_email"
+ desks.values.each do |desk|
+ csv.row desk.id, desk.name, desk.building_code, desk.level_code, desk.allocation_email
+ end
+ end
+
+ {HTTP::Status::OK.to_i, {"Content-Type" => "text/csv"}, payload}
+ end
+
+ struct Allocation
+ include JSON::Serializable
+
+ getter desk_id : String
+ getter desk_name : String
+ getter email : String?
+
+ def initialize(@desk_id, @desk_name, allocation : String?)
+ @email = allocation.try(&.strip.downcase)
+ end
+ end
+
+ def pull_and_sync_desk_allocations(test : Bool = true)
+ # pulls the allocations from the remote server
+ pull_allocations(test)
+
+ # syncs the recurring meetings associated with the allocations
+ # deleting old and adding in the new
+ sync_allocations(test)
+ end
+
+ def pull_allocations(test : Bool = true)
+ # get the list of desks
+ # TODO:: check if the desks
+ all_desks = desks
+
+ # fetch the allocation CSV
+ response = HTTP::Client.get(@allocation_list_url)
+ raise "failed to fetch desk allocations with #{response.status}\n#{response.body}" unless response.success?
+
+ # parse the CSV and check each allocation and for any name updates
+ # "PlaceOS ID","Name","Assigned To"
+ # "desk-6.43.19","6.43.19","Roopali.Misra@cdu.edu.au"
+ csv = CSV.new(response.body, headers: true, strip: true)
+ csv_allocations = {} of String => Allocation
+
+ loop do
+ break unless csv.next
+ row = csv.row
+ desk_id = row[0]
+ csv_allocations[desk_id] = Allocation.new(desk_id, row[1], row[2])
+ end
+
+ level_allocations = Hash(String, Array(Allocation)).new do |hash, level_id|
+ hash[level_id] = [] of Allocation
+ end
+
+ # find new allocations
+ new_allocations = 0
+ csv_allocations.each do |desk_id, allocation|
+ desk = all_desks[desk_id]?
+ if desk.nil?
+ logger.warn { "desk #{desk_id} not configured in metadata" }
+ next
+ end
+
+ next if desk.allocation_email == allocation.email
+
+ level_allocations[desk.level_id] << allocation
+ new_allocations += 1
+ end
+ logger.debug { "found #{new_allocations} new allocations" }
+
+ # find any desks whos allocation has been removed
+ # (the CSV only returns the current allocations)
+ removed_allocations = 0
+ all_desks.each do |desk_id, desk|
+ allocation = csv_allocations[desk_id]?
+ next if allocation
+
+ # skip unless there is an email presence
+ allocated_email = desk.allocation_email
+ next unless allocated_email
+
+ removed_allocations += 1
+ level_allocations[desk.level_id] << Allocation.new(desk_id, desk.name, nil)
+ end
+ logger.debug { "found #{removed_allocations} allocations to be removed" }
+
+ # update the allocation metadata
+ return if test
+ level_allocations.each do |level_id, allocations|
+ update_allocation_metadata(level_id, allocations)
+ end
+ end
+
+ # set the users in the metadata
+ protected def update_allocation_metadata(level_zone : String, allocations : Array(Allocation))
+ # fetch the level metadata
+ all_desks = staff_api.metadata(level_zone, "desks").get.dig?("desks", "details").try(&.as_a?)
+ return unless all_desks
+
+ allocation_hash = allocations.to_h { |alloc| {alloc.desk_id, alloc} }
+
+ # update the json with allocation changes
+ updated_desks = all_desks.map do |desk|
+ desk_id = desk["id"].as_s
+ allocation = allocation_hash[desk_id]?
+ desk = desk.as_h
+ next desk unless allocation
+
+ if email = allocation.email.presence
+ # look up users name
+ user_name = begin
+ staff_api.calendar(email).get["name"].as_s
+ rescue error
+ logger.error(exception: error) { "failed to find allocation name for #{allocation.email}" }
+ email.split("@")[0].split(' ').map(&.capitalize).join(' ')
+ end
+ else
+ user_name = ""
+ end
+
+ desk["name"] = JSON::Any.new(allocation.desk_name)
+ desk["assigned_to"] = JSON::Any.new(email)
+ desk["assigned_name"] = JSON::Any.new(user_name)
+ desk
+ end
+
+ # update the level metadata
+ begin
+ staff_api.write_metadata(level_zone, "desks", updated_desks).get
+ rescue error
+ logger.error(exception: error) { "failed to write metadata for level: #{level_zone}" }
+ end
+ end
+
+ # Syncs all the allocations
+ def sync_allocations(test : Bool = true)
+ buildings.keys.each do |building_id|
+ sync_allocations_in(building_id, test)
+ end
+ end
+
+ # ==============================
+ # Desk allocation syncronisation
+ # ==============================
+
+ protected def building_details(building_id : String) : Tuple(Time::Location, Array(String))
+ building_details = buildings[building_id]
+ logger.debug { "syncing allocations in: #{building_details.name}\n====================" }
+
+ if building_parent = building_details.parent_id.presence
+ parent_details = staff_api.zone(building_parent).get
+ parent_parent = parent_details["parent_id"]?.try(&.as_s?)
+ end
+
+ tz = building_details.timezone.presence || config.control_system.try(&.timezone)
+ {Time::Location.load(tz.as(String)), [parent_parent, building_parent].compact}
+ end
+
+ record AssignmentDetails, desk_id : String, assigned_email : String, assigned_name : String, level_zone : String, desk_name : String
+
+ protected def sync_allocations_in(building_zone : String, test : Bool)
+ # find the parent zones for the building
+ timezone, parent_zones = building_details(building_zone)
+
+ # sync code as per the script
+ desk_ids = Set(String).new
+
+ # email => [] of desks
+ assigned_to = Hash(String, Array(AssignmentDetails)).new do |hash, key|
+ hash[key] = [] of AssignmentDetails
+ end
+
+ # desk_id => DeskDetails
+ assignments = {} of String => AssignmentDetails
+
+ # get the desk assignments
+ json = staff_api.metadata_children(building_zone, "desks").get
+ json.as_a.each do |level|
+ level_zone = level["zone"]["id"].as_s
+
+ if desks = level["metadata"]["desks"]?
+ desks["details"].as_a.each do |desk|
+ assigned_email = desk["assigned_to"]?.try(&.as_s?).presence
+ next unless assigned_email
+ assigned_email = assigned_email.strip.downcase
+ assigned_name = desk["assigned_name"]?.try(&.as_s?)
+
+ if assigned_name.nil?
+ logger.warn { "no assigned name for desk #{assigned_email}" }
+ assigned_name = assigned_email.split('@')[0].gsub('.', ' ')
+ end
+
+ desk_id = desk["id"].as_s
+ desk_name = desk["name"]?.try(&.as_s?) || desk_id
+ details = AssignmentDetails.new(desk_id, assigned_email, assigned_name, level_zone, desk_name)
+
+ assignments[desk_id] = details
+ assigned_to[assigned_email] << details
+ end
+ end
+ end
+
+ # find all the booking allocation ids
+ starting = Time.local(timezone)
+ ending = 2.hours.from_now
+
+ booking_start = starting.at_beginning_of_day
+ booking_end = starting.at_end_of_day
+
+ bookings = staff_api.query_bookings(
+ type: "desk",
+ zones: {building_zone},
+ limit: 10_000,
+ period_start: starting.to_unix,
+ period_end: ending.to_unix
+ ).get.as_a
+
+ bookings.select! { |booking| booking["recurrence_type"].as_s? == "daily" && booking["recurrence_end"]?.try(&.as_i64?).nil? && booking["booking_type"].as_s == "desk" }
+
+ # find all the missing assignments or incorrect assignments
+ missing = {} of String => AssignmentDetails
+ deleted = {} of Int64 => String
+ failed = 0
+ assignments.each do |desk_id, details|
+ booking = bookings.find { |book| book["asset_id"].as_s == desk_id }
+ if booking.nil?
+ missing[desk_id] = details
+ next
+ end
+
+ booking_email = booking["user_email"].as_s.strip.downcase
+ if booking_email != details.assigned_email
+ booking_id = booking["id"].as_i64
+
+ # this is an incorrect booking, we should delete it
+ # then we can add the current assignment to missing
+ staff_api.booking_delete(booking_id).get unless test
+
+ deleted[booking_id] = booking_email
+ missing[desk_id] = details
+ end
+ end
+
+ # remove bookings that shouldn't exist
+ removed_dangling = 0
+ bookings.each do |booking|
+ asset_id = booking["asset_id"].as_s
+ if assignments[asset_id]?.nil?
+ booking_id = booking["id"].as_i64
+ booking_email = booking["user_email"].as_s.strip.downcase
+
+ # this is an incorrect booking, we should delete it
+ # then we can add the current assignment to missing
+ staff_api.booking_delete(booking_id).get unless test
+
+ removed_dangling += 1
+ deleted[booking_id] = booking_email
+ end
+ end
+
+ # log the results
+ logger.debug do
+ String.build do |io|
+ io << "found #{removed_dangling} dangling bookings\n" unless removed_dangling.zero?
+ io << "checked #{assignments.size} assignments against #{bookings.size} bookings\n"
+ io << "failed to remove #{failed} bookings\n" unless failed.zero?
+ io << "removed #{deleted.size} incorrect assignments\n"
+ deleted.each do |booking_id, email|
+ io << " - #{email}: #{booking_id}\n"
+ end
+ io << "found #{missing.size} missing assignments"
+ end
+ end
+
+ logger.debug { "creating missing bookings..." } unless missing.size.zero?
+
+ # update the bookings with the new ids
+ fixed = 0
+ no_applied = {} of String => String
+ missing.each do |desk_id, details|
+ logger.debug { " - assigning #{desk_id} => #{details.assigned_email}" }
+
+ staff_api.create_booking(
+ asset_id: desk_id,
+ asset_ids: {desk_id},
+ asset_name: details.desk_name,
+ zones: parent_zones + [
+ building_zone,
+ details.level_zone,
+ ],
+ booking_start: booking_start.to_unix,
+ booking_end: booking_end.to_unix,
+ booking_type: "desk",
+ time_zone: timezone.name,
+ user_email: details.assigned_email,
+ user_id: details.assigned_email,
+ user_name: details.assigned_email,
+ title: "Desk Booking",
+ extension_data: {
+ "asset_name" => details.desk_name,
+ "is_assigned" => true,
+ "assets" => [] of String,
+ "tags" => [] of String,
+ },
+ recurrence_type: "daily",
+ recurrence_days: 127
+ ).get unless test
+
+ fixed += 1
+ end
+
+ logger.debug do
+ String.build do |io|
+ io << "added #{fixed} missing bookings\n" unless missing.size.zero?
+ if !no_applied.size.zero?
+ io << "failed to apply #{no_applied.size} bookings\n"
+ end
+ io << "done!"
+ end
+ end
+ end
+end
diff --git a/drivers/place/desk/allocations_spec.cr b/drivers/place/desk/allocations_spec.cr
new file mode 100644
index 00000000000..b9b5e06f3e0
--- /dev/null
+++ b/drivers/place/desk/allocations_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Desk::Allocations" do
+end
diff --git a/drivers/place/desk/control.cr b/drivers/place/desk/control.cr
new file mode 100644
index 00000000000..5d836494b06
--- /dev/null
+++ b/drivers/place/desk/control.cr
@@ -0,0 +1,123 @@
+require "placeos-driver"
+require "placeos-driver/interface/desk_control"
+require "placeos"
+require "json"
+
+class Place::Desk::Control < PlaceOS::Driver
+ descriptive_name "PlaceOS Desk Control"
+ generic_name :DeskControl
+ description %(helper for handling desk control)
+
+ default_settings({
+ desk_id_key: "id",
+ })
+
+ accessor area_manager : AreaManagement_1
+ accessor staff_api : StaffAPI_1
+
+ METADATA_KEY = "desks"
+
+ def on_load
+ # cache desk ids periodically
+ schedule.every(1.hour) { @desk_ids = nil }
+ on_update
+ end
+
+ def on_update
+ @desk_id_key = setting?(String, :desk_id_key) || "id"
+ end
+
+ getter desk_id_key : String = "id"
+
+ def desk_lookup(desk_id : String) : String
+ # if it's not id, then there is a mapping to another id
+ if desk_id_key != "id"
+ mapped_id = desk_ids[desk_id]?
+ raise "mapped id not found" unless mapped_id
+ mapped_id
+ else
+ desk_id
+ end
+ end
+
+ protected def desk_control
+ system.implementing(PlaceOS::Driver::Interface::DeskControl)
+ end
+
+ # ===================================
+ # Desk control functions
+ # ===================================
+
+ def set_desk_height(desk_key : String, desk_height : Int32)
+ desk_key = desk_lookup(desk_key)
+ desk_control.set_desk_height(desk_key, desk_height).get
+ end
+
+ def get_desk_height(desk_key : String)
+ desk_control.get_desk_height(desk_key).get
+ end
+
+ def set_desk_power(desk_key : String, desk_power : Bool?)
+ desk_key = desk_lookup(desk_key)
+ desk_control.set_desk_power(desk_key, desk_power).get
+ end
+
+ def get_desk_power(desk_key : String)
+ desk_control.get_desk_power(desk_key).get
+ end
+
+ # ===================================
+ # Desk zone queries
+ # ===================================
+
+ struct DeskId
+ include JSON::Serializable
+ include JSON::Serializable::Unmapped
+
+ getter id : String
+ end
+
+ struct Details
+ include JSON::Serializable
+
+ property details : Array(DeskId)
+ end
+
+ alias Zone = PlaceOS::Client::API::Models::Zone
+ alias Metadata = Hash(String, Details)
+ alias ChildMetadata = Array(NamedTuple(zone: Zone, metadata: Metadata))
+
+ getter desk_ids : Hash(String, String) do
+ metadatas = level_buildings.values.uniq.map do |zone_id|
+ ChildMetadata.from_json(staff_api.metadata_children(
+ zone_id,
+ METADATA_KEY
+ ).get.to_json)
+ end
+
+ desks = {} of String => String
+ key = desk_id_key
+
+ metadatas.each do |metadata|
+ metadata.each do |level|
+ zone = level[:zone]
+ if ids = level[:metadata][METADATA_KEY]?.try(&.details)
+ ids.each do |desk_details|
+ if mapped_id = desk_details.json_unmapped[key]?.try(&.as_s?)
+ desks[desk_details.id] = mapped_id
+ end
+ end
+ end
+ end
+ end
+
+ desks
+ end
+
+ # level_zone_id => building_zone_id
+ getter level_buildings : Hash(String, String) do
+ hash = area_manager.level_buildings.get.as_h.transform_values(&.as_s)
+ raise "level cache not loaded yet" unless hash.size > 0
+ hash
+ end
+end
diff --git a/drivers/place/desk/control_spec.cr b/drivers/place/desk/control_spec.cr
new file mode 100644
index 00000000000..25c31035af3
--- /dev/null
+++ b/drivers/place/desk/control_spec.cr
@@ -0,0 +1,116 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Desk::Control" do
+ system({
+ StaffAPI: {StaffAPIMock},
+ AreaManagement: {AreaManagementMock},
+ })
+
+ settings({
+ desk_id_key: "map_id",
+ })
+
+ exec(:desk_ids).get.should eq({
+ "desk_77123" => "desk-77123",
+ "desk_006-17" => "desk-006-17",
+ })
+
+ exec(:desk_lookup, "desk_77123").get.should eq("desk-77123")
+end
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ def metadata_children(id : String, key : String? = nil)
+ logger.info { "requesting zone #{id} and key #{key}" }
+
+ [
+ {
+ "zone": {
+ "created_at": 1668744303,
+ "updated_at": 1668744303,
+ "id": "zone-FlWVOXv9yY",
+ "name": "PlaceOS Dev Sydney Catering Enabled",
+ "display_name": "Catering ",
+ "location": "",
+ "description": "",
+ "code": "",
+ "type": "",
+ "count": 0,
+ "capacity": 0,
+ "map_id": "",
+ "tags": [] of String,
+ "triggers": [] of String,
+ "parent_id": "zone-DnTcV5ZeEq",
+ },
+ "metadata": {} of String => String,
+ },
+ {
+ "zone": {
+ "created_at": 1691972553,
+ "updated_at": 1701398359,
+ "id": "zone-EYEnrhbaQz",
+ "name": "LEVEL Parking",
+ "display_name": "Parking",
+ "location": "",
+ "description": "",
+ "code": "",
+ "type": "",
+ "count": 0,
+ "capacity": 0,
+ "map_id": "https://s3-ap-southeast-2.amazonaws.com/os.place.tech/placeos-dev.aca.im/169197263162476823.svg",
+ "tags": [
+ "level",
+ "parking",
+ ],
+ "triggers": [] of String,
+ "parent_id": "zone-DnTcV5ZeEq",
+ },
+ "metadata": {
+ "desks": {
+ "name": "desks",
+ "description": "List of available desks",
+ "details": [
+ {
+ "id": "desk_77123",
+ "name": "test2",
+ "groups": [] of String,
+ "images": [] of String,
+ "map_id": "desk-77123",
+ "bookable": false,
+ "features": [
+ "test",
+ ],
+ },
+ {
+ "id": "desk_006-17",
+ "name": "test3",
+ "groups": [] of String,
+ "images": [] of String,
+ "map_id": "desk-006-17",
+ "bookable": true,
+ "features": [] of String,
+ },
+ ],
+ "parent_id": "zone-FlWVOXv9yY",
+ "editors": [] of String,
+ "modified_by_id": "user-DGLTbVU8eqiSRn",
+ },
+ },
+ },
+ ]
+ end
+end
+
+# :nodoc:
+class AreaManagementMock < DriverSpecs::MockDriver
+ def update_available(zones : Array(String))
+ logger.info { "requested update to #{zones}" }
+ nil
+ end
+
+ def level_buildings
+ {
+ "zone-EYEnrhbaQz": "zone-DnTcV5ZeEq",
+ }
+ end
+end
diff --git a/drivers/place/desk_booking_webhook.cr b/drivers/place/desk_booking_webhook.cr
new file mode 100644
index 00000000000..78f653cb40a
--- /dev/null
+++ b/drivers/place/desk_booking_webhook.cr
@@ -0,0 +1,69 @@
+require "placeos-driver"
+require "http/client"
+
+class Place::DeskBookingWebhook < PlaceOS::Driver
+ descriptive_name "Desk Booking Webhook"
+ generic_name :DeskBookingWebhook
+ description %(sends a webhook with booking information as it changes)
+
+ accessor staff_api : StaffAPI_1
+
+ default_settings({
+ post_uri: "https://remote-server/path",
+ building: "zone-id",
+
+ custom_headers: {
+ "API_KEY" => "123456",
+ },
+
+ # how many days from now do we want to send
+ days_from_now: 14,
+
+ booking_category: "desk",
+
+ debug: false,
+ })
+
+ def on_load
+ monitor("staff/booking/changed") do |_subscription, payload|
+ logger.debug { "received booking changed event #{payload}" }
+ fetch_and_post
+ end
+ schedule.every(24.hours) { fetch_and_post }
+ on_update
+ end
+
+ @time_period : Time::Span = 14.days
+ @booking_category : String = "desk"
+ @custom_headers = {} of String => String
+ @building = ""
+ @post_uri = ""
+ @debug : Bool = false
+
+ def on_update
+ @post_uri = setting(String, :post_uri)
+ @building = setting(String, :building)
+ @custom_headers = setting(Hash(String, String), :custom_headers)
+ @time_period = setting(Int32, :days_from_now).days
+ @booking_category = setting(String, :booking_category)
+ @debug = setting(Bool, :debug)
+
+ fetch_and_post
+ end
+
+ def fetch_and_post
+ period_start = Time.utc.to_unix
+ period_end = @time_period.from_now.to_unix
+ zones = [@building]
+ payload = staff_api.query_bookings(@booking_category, period_start, period_end, zones).get.to_json
+
+ headers = HTTP::Headers.new
+ @custom_headers.each { |key, value| headers[key] = value }
+ headers["Content-Type"] = "application/json; charset=UTF-8"
+
+ logger.debug { "Posting: #{payload} \n with Headers: #{headers}" } if @debug
+ response = HTTP::Client.post @post_uri, headers, body: payload
+ raise "Request failed with #{response.status_code}: #{response.body}" unless response.status_code < 300
+ "#{response.status_code}: #{response.body}"
+ end
+end
diff --git a/drivers/place/desk_bookings_locations.cr b/drivers/place/desk_bookings_locations.cr
new file mode 100644
index 00000000000..0b81ff31236
--- /dev/null
+++ b/drivers/place/desk_bookings_locations.cr
@@ -0,0 +1,270 @@
+require "placeos-driver"
+require "placeos-driver/interface/locatable"
+require "./booking_model"
+require "json"
+require "set"
+
+class Place::DeskBookingsLocations < PlaceOS::Driver
+ include Interface::Locatable
+
+ descriptive_name "PlaceOS Desk Bookings Locations"
+ generic_name :DeskBookings
+ description %(collects desk booking data from the staff API for visualising on a map)
+
+ accessor area_manager : AreaManagement_1
+ accessor staff_api : StaffAPI_1
+ accessor location_service : LocationServices_1
+
+ default_settings({
+ zone_filter: [] of String,
+
+ # time in seconds
+ poll_rate: 20,
+ booking_type: "desk",
+
+ _expose_for_analytics: {"output_key" => "booking_key->subkey"},
+ })
+
+ @expose_for_analytics : Hash(String, String) = {} of String => String
+ @zone_filter : Array(String) = [] of String
+ @poll_rate : Time::Span = 60.seconds
+ @booking_type : String = "desk"
+
+ def on_load
+ monitor("staff/booking/changed") do |_subscription, payload|
+ logger.debug { "received booking changed event #{payload}" }
+ booking = Booking.from_json(payload)
+ booking.user_email = booking.user_email.downcase
+ booking_changed(booking)
+ end
+ on_update
+ end
+
+ def on_update
+ @zone_filter = setting?(Array(String), :zone_filter) || [] of String
+ @zones = nil
+ @building_id = nil
+ @map_ids = nil
+ @poll_rate = (setting?(Int32, :poll_rate) || 60).seconds
+
+ @booking_type = setting?(String, :booking_type).presence || "desk"
+ @expose_for_analytics = setting?(Hash(String, String), :expose_for_analytics) || {} of String => String
+
+ map_zones
+ schedule.clear
+ schedule.every(@poll_rate) { query_desk_bookings }
+ schedule.in(5.seconds) { query_desk_bookings }
+ end
+
+ getter zones : Array(String) do
+ filtered = @zone_filter
+ if filtered.empty?
+ location_service.systems.get.as_h.keys
+ else
+ filtered
+ end
+ end
+
+ getter building_id : String { location_service.building_id.get.as_s }
+
+ # asset_id => map_id
+ getter map_ids : Hash(String, String) do
+ levels = staff_api.metadata_children(building_id, "desks").get.as_a
+ id_map = {} of String => String
+
+ levels.each do |level|
+ if desks = level["metadata"]["desks"]?
+ desks["details"].as_a.each do |desk|
+ if map_id = desk["map_id"]?.try(&.as_s?).presence
+ id_map[desk["id"].as_s] = map_id
+ end
+ end
+ end
+ end
+ id_map
+ end
+
+ # ===================================
+ # Monitoring desk bookings
+ # ===================================
+ protected def booking_changed(event)
+ return unless event.booking_type == @booking_type
+ matching_zones = zones & event.zones
+ return if matching_zones.empty?
+
+ logger.debug { "booking event is in a matching zone" }
+
+ case event.action
+ when "create"
+ return unless event.in_progress?
+ # Check if this event is happening now
+ logger.debug { "adding new booking" }
+ @bookings[event.user_email] << event
+ when "cancelled", "rejected"
+ # delete the booking from the levels
+ found = false
+ @bookings[event.user_email].reject! { |booking| found = true if booking.id == event.id }
+ return unless found
+ when "check_in"
+ return unless event.in_progress?
+ @bookings[event.user_email].each { |booking| booking.checked_in = true if booking.id == event.id }
+ when "changed"
+ # Check if this booking is for today and update as required
+ @bookings[event.user_email].reject! { |booking| booking.id == event.id }
+ @bookings[event.user_email] << event if event.in_progress?
+ else
+ # ignore the update (approve)
+ logger.debug { "booking event was ignored" }
+ return
+ end
+
+ area_manager.update_available(matching_zones)
+ end
+
+ # ===================================
+ # Locatable Interface functions
+ # ===================================
+ def locate_user(email : String? = nil, username : String? = nil)
+ logger.debug { "searching for #{email}, #{username}" }
+ bookings = @bookings[email]? || [] of Booking
+ map_bookings(bookings)
+ end
+
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ logger.debug { "listing MAC addresses assigned to #{email}, #{username}" }
+ found = [] of String
+ @known_users.each { |user_id, (user_email, _name)|
+ found << user_id if email == user_email
+ }
+ found
+ end
+
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ logger.debug { "searching for owner of #{mac_address}" }
+ if user_details = @known_users[mac_address]?
+ email, _name = user_details
+ {
+ location: "booking",
+ assigned_to: email,
+ mac_address: mac_address,
+ }
+ end
+ end
+
+ def device_locations(zone_id : String, location : String? = nil)
+ logger.debug { "searching devices in zone #{zone_id}" }
+ return [] of Nil if location && location != "booking"
+
+ bookings = [] of Booking
+ @bookings.each_value(&.each { |booking|
+ next unless zone_id.in?(booking.zones)
+ bookings << booking
+ })
+ map_bookings(bookings)
+ end
+
+ protected def map_bookings(bookings)
+ map_mappings = map_ids rescue {} of String => String
+ bookings.map do |booking|
+ level = nil
+ building = nil
+ booking.zones.each do |zone_id|
+ tags = @zone_mappings[zone_id]
+ level = zone_id if tags.includes? "level"
+ building = zone_id if tags.includes? "building"
+ break if level && building
+ end
+
+ # We specify location as JSON::Any so we don't have to
+ # explicitly define the type of this object
+ payload = {
+ "location" => JSON::Any.new("booking"),
+ "type" => @booking_type,
+ "checked_in" => booking.checked_in,
+ "asset_id" => booking.asset_id,
+ "booking_id" => booking.id,
+ "building" => building,
+ "level" => level,
+ "ends_at" => booking.booking_end,
+ "started_at" => booking.booking_start,
+ "duration" => booking.booking_end - booking.booking_start,
+ "mac" => booking.user_id,
+ "staff_email" => booking.user_email,
+ "staff_name" => booking.user_name,
+ "map_id" => map_mappings[booking.asset_id]?
+ }.compact!
+
+ # check for any custom data we want to include
+ if !booking.extension_data.empty? && (init_data = JSON::Any.new(booking.extension_data))
+ @expose_for_analytics.each do |binding, path|
+ begin
+ binding_keys = path.split("->")
+ data = init_data
+ binding_keys.each do |key|
+ next if key == "extension_data"
+
+ data = data.dig? key
+ break unless data
+ end
+ payload[binding] = data
+ rescue error
+ logger.warn(exception: error) { "failed to expose #{binding}: #{path} for analytics" }
+ end
+ end
+ end
+
+ payload
+ end
+ end
+
+ # ===================================
+ # DESK AND ZONE QUERIES
+ # ===================================
+ # zone id => tags
+ @zone_mappings = {} of String => Array(String)
+
+ protected def map_zones
+ @zone_mappings = Hash(String, Array(String)).new do |hash, zone_id|
+ # Map zones_ids to tags (level, building etc)
+ hash[zone_id] = staff_api.zone(zone_id).get["tags"].as_a.map(&.as_s)
+ end
+ end
+
+ # Email => Array of bookings
+ @bookings : Hash(String, Array(Booking)) = Hash(String, Array(Booking)).new
+
+ # UserID => {Email, Name}
+ @known_users : Hash(String, Tuple(String, String)) = Hash(String, Tuple(String, String)).new
+
+ def query_desk_bookings : Nil
+ ids = Set(Int64).new
+ bookings = [] of JSON::Any
+ zones.each do |zone|
+ bookings.concat staff_api.query_bookings(type: @booking_type, zones: {zone}).get.as_a
+ rescue error
+ logger.warn(exception: error) { "failed to query bookings in zone: #{zone}" }
+ end
+ bookings = bookings.flat_map do |booking|
+ booking = Booking.from_json(booking.to_json)
+ next [] of Booking if ids.includes?(booking.id)
+ ids << booking.id
+
+ booking.user_email = booking.user_email.downcase
+ booking.expand
+ end
+
+ logger.debug { "queried desk bookings, found #{bookings.size}" }
+
+ new_bookings = Hash(String, Array(Booking)).new do |hash, key|
+ hash[key] = [] of Booking
+ end
+
+ bookings.each do |booking|
+ next if booking.rejected
+ new_bookings[booking.user_email] << booking
+ @known_users[booking.user_id] = {booking.user_email, booking.user_name}
+ end
+
+ @bookings = new_bookings
+ end
+end
diff --git a/drivers/place/desk_bookings_locations_spec.cr b/drivers/place/desk_bookings_locations_spec.cr
new file mode 100644
index 00000000000..7c83616fd12
--- /dev/null
+++ b/drivers/place/desk_bookings_locations_spec.cr
@@ -0,0 +1,91 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::DeskBookingsLocations" do
+ system({
+ StaffAPI: {StaffAPIMock},
+ AreaManagement: {AreaManagementMock},
+ })
+
+ settings({
+ zone_filter: ["placeos-zone-id"],
+ })
+
+ now = Time.local
+ start = now.at_beginning_of_day.to_unix
+ ending = now.at_end_of_day.to_unix
+
+ exec(:query_desk_bookings).get
+ resp = exec(:device_locations, "placeos-zone-id").get
+ puts resp
+ resp.should eq([
+ {"location" => "booking", "type" => "desk", "checked_in" => true, "asset_id" => "desk-123", "booking_id" => 1, "building" => "zone-building", "level" => "placeos-zone-id", "ends_at" => ending, "started_at" => start, "duration" => 86399, "mac" => "user-1234", "staff_email" => "user1234@org.com", "staff_name" => "Bob Jane"},
+ {"location" => "booking", "type" => "desk", "checked_in" => false, "asset_id" => "desk-456", "booking_id" => 2, "building" => "zone-building", "level" => "placeos-zone-id", "ends_at" => ending, "started_at" => start, "duration" => 86399, "mac" => "user-456", "staff_email" => "zdoo@org.com", "staff_name" => "Zee Doo"},
+ ])
+end
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ def query_bookings(type : String, zones : Array(String))
+ logger.debug { "Querying desk bookings!" }
+
+ now = Time.local
+ start = now.at_beginning_of_day.to_unix
+ ending = now.at_end_of_day.to_unix
+ [
+ {
+ id: 1,
+ booking_type: type,
+ booking_start: start,
+ booking_end: ending,
+ asset_id: "desk-123",
+ user_id: "user-1234",
+ user_email: "user1234@org.com",
+ user_name: "Bob Jane",
+ zones: zones + ["zone-building"],
+ checked_in: true,
+ rejected: false,
+ booked_by_name: "Bob Jane",
+ booked_by_email: "user1234@org.com",
+ },
+ {
+ id: 2,
+ booking_type: type,
+ booking_start: start,
+ booking_end: ending,
+ asset_id: "desk-456",
+ user_id: "user-456",
+ user_email: "zdoo@org.com",
+ user_name: "Zee Doo",
+ zones: zones + ["zone-building"],
+ checked_in: false,
+ rejected: false,
+ booked_by_name: "Zee Doo",
+ booked_by_email: "zdoo@org.com",
+ },
+ ]
+ end
+
+ def zone(zone_id : String)
+ logger.info { "requesting zone #{zone_id}" }
+
+ if zone_id == "placeos-zone-id"
+ {
+ id: zone_id,
+ tags: ["level"],
+ }
+ else
+ {
+ id: zone_id,
+ tags: ["building"],
+ }
+ end
+ end
+end
+
+# :nodoc:
+class AreaManagementMock < DriverSpecs::MockDriver
+ def update_available(zones : Array(String))
+ logger.info { "requested update to #{zones}" }
+ nil
+ end
+end
diff --git a/drivers/place/event_mailer.cr b/drivers/place/event_mailer.cr
new file mode 100644
index 00000000000..772eb7d9a38
--- /dev/null
+++ b/drivers/place/event_mailer.cr
@@ -0,0 +1,232 @@
+require "placeos-driver"
+require "place_calendar"
+require "placeos-driver/interface/mailer_templates"
+
+require "./password_generator_helper"
+
+class Place::EventMailer < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+
+ descriptive_name "PlaceOS Event Mailer"
+ generic_name :EventMailer
+ description %(Subscribe to Events and send emails to attendees)
+
+ default_settings({
+ zone_ids_to_target: ["zone-id-here"],
+ module_to_target: "Bookings_1",
+ module_status_to_scrape: "bookings",
+ event_filter: "occurs_today",
+ email_template_group: "events",
+ email_template: "welcome",
+ send_network_credentials: false,
+ network_password_length: DEFAULT_PASSWORD_LENGTH,
+ network_password_exclude: DEFAULT_PASSWORD_EXCLUDE,
+ network_password_minimum_lowercase: DEFAULT_PASSWORD_MINIMUM_LOWERCASE,
+ network_password_minimum_uppercase: DEFAULT_PASSWORD_MINIMUM_UPPERCASE,
+ network_password_minimum_numbers: DEFAULT_PASSWORD_MINIMUM_NUMBERS,
+ network_password_minimum_symbols: DEFAULT_PASSWORD_MINIMUM_SYMBOLS,
+ network_group_ids: [] of String,
+ date_time_format: "%c",
+ time_format: "%l:%M%p",
+ date_format: "%A, %-d %B",
+ debug: false,
+ })
+
+ accessor staff_api : StaffAPI_1
+ accessor mailer : Mailer_1
+ accessor network_provider : NetworkAccess_1 # Written for Cisco ISE Driver, but ideally compatible with others
+
+ @target_zones = [] of String
+ @target_module = "Bookings_1"
+ @target_status = "bookings"
+ @event_filter = "occurs_today"
+ @email_template_group = "events"
+ @email_template = "welcome"
+ @send_network_credentials = false
+ @network_password_length : Int32 = DEFAULT_PASSWORD_LENGTH
+ @network_password_exclude : String = DEFAULT_PASSWORD_EXCLUDE
+ @network_password_minimum_lowercase : Int32 = DEFAULT_PASSWORD_MINIMUM_LOWERCASE
+ @network_password_minimum_uppercase : Int32 = DEFAULT_PASSWORD_MINIMUM_UPPERCASE
+ @network_password_minimum_numbers : Int32 = DEFAULT_PASSWORD_MINIMUM_NUMBERS
+ @network_password_minimum_symbols : Int32 = DEFAULT_PASSWORD_MINIMUM_SYMBOLS
+ @network_group_ids = [] of String
+
+ # See: https://crystal-lang.org/api/0.35.1/Time/Format.html
+ @date_time_format : String = "%c"
+ @time_format : String = "%l:%M%p"
+ @date_format : String = "%A, %-d %B"
+
+ @debug = false
+ @events = {} of String => Array(PlaceCalendar::Event) # {sys_id: [event]}
+
+ def on_update
+ @target_zones = setting?(Array(String), :zone_ids_to_target) || [] of String
+ @target_module = setting?(String, :module_to_target) || "Bookings_1"
+ @target_status = setting?(String, :module_status_to_target) || "bookings"
+ @event_filter = setting?(String, :event_filter) || ""
+ @email_template_group = setting?(String, :email_template_group) || "events"
+ @email_template = setting?(String, :email_template) || "welcome"
+
+ @send_network_credentials = setting?(Bool, :send_network_credentials) || false
+ @network_password_length = setting?(Int32, :password_length) || DEFAULT_PASSWORD_LENGTH
+ @network_password_exclude = setting?(String, :password_exclude) || DEFAULT_PASSWORD_EXCLUDE
+ @network_password_minimum_lowercase = setting?(Int32, :password_minimum_lowercase) || DEFAULT_PASSWORD_MINIMUM_LOWERCASE
+ @network_password_minimum_uppercase = setting?(Int32, :password_minimum_uppercase) || DEFAULT_PASSWORD_MINIMUM_UPPERCASE
+ @network_password_minimum_numbers = setting?(Int32, :password_minimum_numbers) || DEFAULT_PASSWORD_MINIMUM_NUMBERS
+ @network_password_minimum_symbols = setting?(Int32, :password_minimum_symbols) || DEFAULT_PASSWORD_MINIMUM_SYMBOLS
+ @network_group_ids = setting?(Array(String), :network_group_ids) || [] of String
+
+ @date_time_format = setting?(String, :date_time_format) || "%c"
+ @time_format = setting?(String, :time_format) || "%l:%M%p"
+ @date_format = setting?(String, :date_format) || "%A, %-d %B"
+ @debug = setting?(Bool, :debug) || false
+
+ self[:events] = @events.clear
+
+ subscribe_to_all_modules
+ end
+
+ private def subscribe_to_all_modules
+ # Subscribe to the targetted state of all matching modules and update our state when they change
+ subscriptions.clear
+ list_target_systems.map do |sys|
+ sys_id = sys["id"].to_s
+ system(sys_id).subscribe(@target_module, @target_status) do |_subscription, new_value|
+ process_updated_events(sys_id, Array(PlaceCalendar::Event).from_json(new_value))
+ end
+ end
+ end
+
+ def list_target_systems
+ @target_zones.flat_map { |zone_id| list_systems_in_zone(zone_id) }
+ end
+
+ def list_systems_in_zone(zone_id : String)
+ staff_api.systems(zone_id: zone_id).get.as_a
+ end
+
+ def inspect_event_store
+ @events
+ end
+
+ private def process_updated_events(system_id : String, events : Array(PlaceCalendar::Event))
+ logger.debug { "Detected #{events.size} new Events in #{system_id}" } if @debug
+ selected_events = apply_filter(events)
+ logger.debug { "Filtered to #{selected_events.size} events with filter #{@event_filter}" } if @debug
+
+ new_events = selected_events
+ # new_events = selected_events - @events[system_id] # Don't process events we've already seen in the past
+ # @events[system_id] = new_events # Store the updated list of events
+ # self[:events] = @events
+
+ logger.debug { "Sending emails for #{new_events.size} events in #{system_id}" }
+ new_events.each { |event| send_event_email(event, system_id) }
+ end
+
+ def template_fields : Array(TemplateFields)
+ time_now = Time.utc.in(Time::Location.local)
+ [
+ TemplateFields.new(
+ trigger: {@email_template_group, @email_template},
+ name: "Event welcome",
+ description: "Welcome email sent to event organizers when their event is coming up today",
+ fields: [
+ {name: "host_name", description: "Name of the event organizer"},
+ {name: "host_email", description: "Email address of the event organizer"},
+ {name: "room_name", description: "Location or room where the event is being held"},
+ {name: "event_title", description: "Title or subject of the event"},
+ {name: "event_start", description: "Start time of the event (e.g., #{time_now.to_s(@time_format)})"},
+ {name: "event_date", description: "Date of the event (e.g., #{time_now.to_s(@date_format)})"},
+ {name: "network_username", description: "Username for network access (only if network credentials enabled)"},
+ {name: "network_password", description: "Generated password for network access (only if network credentials enabled)"},
+ ]
+ ),
+ ]
+ end
+
+ private def send_event_email(event : PlaceCalendar::Event, system_id : String)
+ # Don't send welcome email more than once
+ # Surely there's a tidier way to do these 2 lines?
+ extension_data = event.extended_properties # https://github.com/PlaceOS/calendar/blob/master/src/models/event.cr#L38
+ return "Event email was already sent at #{extension_data[:event_mailer_email_sent_at]}" if extension_data && extension_data.not_nil![:event_mailer_email_sent_at]
+
+ organizer_email = event.host
+ organizer_name = event.attendees.find { |a| a.email == organizer_email }.try &.name || "Name Unknown"
+ network_username = network_password = ""
+ network_username, network_password = update_network_user_password(
+ organizer_email.not_nil!,
+ generate_password(
+ length: @network_password_length,
+ exclude: @network_password_exclude,
+ minimum_lowercase: @network_password_minimum_lowercase,
+ minimum_uppercase: @network_password_minimum_uppercase,
+ minimum_numbers: @network_password_minimum_numbers,
+ minimum_symbols: @network_password_minimum_symbols
+ ),
+ @network_group_ids
+ ) if @send_network_credentials
+
+ email_data = {
+ host_name: organizer_name,
+ host_email: organizer_email,
+ room_name: event.location,
+ event_title: event.title,
+ event_start: event.event_start.to_s(@time_format),
+ event_date: event.event_end.not_nil!.to_s(@date_format),
+ network_username: network_username,
+ network_password: network_password,
+ }
+ begin
+ logger.debug { "SENDING welcome email: #{email_data}" }
+ mailer.send_template(
+ to: [organizer_email],
+ template: {@email_template_group, @email_template},
+ args: email_data
+ ).get
+ rescue
+ logger.error { "ERROR when attempting to send welcome email" }
+ else
+ staff_api.patch_event_metadata(system_id, event.id, {"event_mailer_email_sent_at": Time.local}).get
+ end
+ end
+
+ private def apply_filter(events : Array(PlaceCalendar::Event))
+ # Additional event filters can be added in the future
+ case @event_filter
+ when "occurs_today"
+ logger.debug { "Event filter: occurs today" } if @debug
+ select_todays_events(events)
+ else
+ logger.debug { "Event filter: NONE" } if @debug
+ events
+ end
+ end
+
+ private def select_todays_events(events : Array(PlaceCalendar::Event))
+ events.select do |event|
+ logger.debug { "Processing event #{event.inspect}" } if @debug
+ timezone = event.timezone ? Time::Location.load(event.timezone.not_nil!) : Time::Location.local
+ now = Time.local(location: timezone)
+ event.event_start >= now.at_beginning_of_day && event.event_start <= now.at_end_of_day
+ end
+ end
+
+ # # For Cisco ISE network credentials
+
+ def update_network_user_password(user_email : String, password : String, network_group_ids : Array(String) = [] of String)
+ # Check if they already exist
+ response = network_provider.update_internal_user_password_by_name(user_email, password).get
+ logger.debug { "Response from Network Identity provider for lookup of #{user_email} was:\n#{response}" } if @debug
+ rescue # todo: catch the specific error where the user already exists, instead of any error. Catch other errors in seperate rescue
+ # Create them if they don't already exist
+ create_network_user(user_email, password, network_group_ids)
+ else
+ {user_email, password}
+ end
+
+ def create_network_user(user_email : String, password : String, group_ids : Array(String) = [] of String)
+ response = network_provider.create_internal_user(email: user_email, name: user_email, password: password, identity_groups: group_ids).get
+ logger.debug { "Response from Network Identity provider for creating user #{user_email} was:\n #{response}\n\nDetails:\n#{response.inspect}" } if @debug
+ {response["name"], password}
+ end
+end
diff --git a/drivers/place/event_setup_breakdown_time.cr b/drivers/place/event_setup_breakdown_time.cr
new file mode 100644
index 00000000000..e56aa66fe09
--- /dev/null
+++ b/drivers/place/event_setup_breakdown_time.cr
@@ -0,0 +1,220 @@
+require "placeos-driver"
+require "place_calendar"
+
+class Place::EventSetupBreakdownTime < PlaceOS::Driver
+ descriptive_name "PlaceOS Event Setup/Breakdown Time"
+ generic_name :EventSetupBreakdownTime
+ description %(Manages setup/breakdown time before/after events)
+
+ accessor staff_api : StaffAPI_1
+ accessor calendar : Calendar_1
+
+ @event_change_mutex : Mutex = Mutex.new
+
+ def on_load
+ monitor("staff/event/changed") do |_subscription, payload|
+ begin
+ logger.debug { "received event changed signal #{payload}" }
+
+ @event_change_mutex.synchronize do
+ event_changed(EventChangedSignal.from_json(payload))
+ end
+ rescue error
+ logger.warn(exception: error) { "error processing event changed signal" }
+ end
+ end
+
+ on_update
+ end
+
+ def on_update
+ end
+
+ private def event_changed(signal : EventChangedSignal)
+ system_id = signal.system_id
+ event = signal.event
+ calendar_id = signal.resource
+ cancelled = event.status == "cancelled" || signal.action == "cancelled"
+
+ # delete setup/breakdown events if event is cancelled
+ if cancelled
+ if setup_event_id = event.setup_event_id
+ calendar.delete_event(
+ calendar_id: calendar_id,
+ event_id: setup_event_id,
+ )
+ logger.debug { "deleted setup event #{setup_event_id}" }
+ end
+ if breakdown_event_id = event.breakdown_event_id
+ calendar.delete_event(
+ calendar_id: calendar_id,
+ event_id: breakdown_event_id,
+ )
+ logger.debug { "deleted breakdown event #{breakdown_event_id}" }
+ end
+ return
+ end
+
+ # skip if no changes
+ if meta = Array(EventMetadata).from_json(staff_api.query_metadata(system_id: system_id, event_ref: [signal.event_id, signal.event_ical_uid]).get.to_json).first?
+ if meta.setup_time == event.setup_time &&
+ meta.setup_event_id == event.setup_event_id &&
+ (
+ (meta.setup_time > 0 && meta.setup_event_id) ||
+ (meta.setup_time == 0 && !meta.setup_event_id.presence)
+ ) &&
+ meta.breakdown_time == event.breakdown_time &&
+ meta.breakdown_event_id == event.breakdown_event_id &&
+ (
+ (meta.breakdown_time > 0 && meta.breakdown_event_id) ||
+ (meta.breakdown_time == 0 && !meta.breakdown_event_id.presence)
+ )
+ logger.debug { "skipping event #{signal.event_id} on #{calendar_id} as no changes" }
+ return
+ end
+ end
+
+ raise "missing event_start time" unless event_start = event.event_start
+ raise "missing event_end time" unless event_end = event.event_end
+
+ linked_events = LinkedEvents.new(main_event_ical: event.ical_uid, main_event_id: event.id)
+ linked_events.setup_event_id = event.setup_event_id if event.setup_event_id
+ linked_events.breakdown_event_id = event.breakdown_event_id if event.breakdown_event_id
+
+ linked_events = LinkedEvents.new(main_event_ical: event.ical_uid, main_event_id: event.id)
+ linked_events.setup_event_id = event.setup_event_id if event.setup_event_id
+ linked_events.breakdown_event_id = event.breakdown_event_id if event.breakdown_event_id
+
+ # create/update setup event
+ if (setup_time = event.setup_time) && setup_time > 0
+ if setup_event_id = event.setup_event_id
+ setup_event = PlaceCalendar::Event.from_json calendar.get_event(calendar_id: calendar_id, event_id: setup_event_id).get.to_json
+ setup_event.event_start = event_start - setup_time.minutes
+ setup_event.event_end = event_start
+ setup_event.body = "<<<#{linked_events.to_json}}>>>"
+ calendar.update_event(event: setup_event, calendar_id: calendar_id)
+ logger.debug { "updated setup event #{setup_event_id} on #{calendar_id}" }
+ else
+ setup_event = PlaceCalendar::Event.from_json calendar.create_event(
+ calendar_id: calendar_id,
+ title: "Setup for #{event.title}",
+ event_start: (event_start - setup_time.minutes).to_unix,
+ event_end: event_start.to_unix,
+ description: "<<<#{linked_events.to_json}}>>>",
+ attendees: [PlaceCalendar::Event::Attendee.new(name: calendar_id, email: calendar_id, response_status: "accepted", resource: true, organizer: true)],
+ ).get.to_json
+
+ linked_events.setup_event_id = setup_event.id
+ logger.debug { "created setup event #{setup_event.id} on #{calendar_id}" }
+ event.setup_event_id = setup_event.id
+ end
+ elsif (setup_time = event.setup_time) && (setup_event_id = event.setup_event_id) && setup_time == 0
+ calendar.delete_event(
+ calendar_id: calendar_id,
+ event_id: setup_event_id,
+ )
+ logger.debug { "deleted setup event #{setup_event_id} on #{calendar_id}" }
+ event.setup_event_id = ""
+ end
+
+ # create/update breakdown event
+ if (breakdown_time = event.breakdown_time) && breakdown_time > 0
+ if breakdown_event_id = event.breakdown_event_id
+ breakdown_event = PlaceCalendar::Event.from_json calendar.get_event(calendar_id: calendar_id, event_id: breakdown_event_id).get.to_json
+ breakdown_event.event_start = event_end
+ breakdown_event.event_end = event_end + breakdown_time.minutes
+ breakdown_event.body = "<<<#{linked_events.to_json}}>>>"
+ calendar.update_event(event: breakdown_event, calendar_id: calendar_id)
+ logger.debug { "updated breakdown event #{breakdown_event_id} on #{calendar_id}" }
+ else
+ breakdown_event = PlaceCalendar::Event.from_json calendar.create_event(
+ calendar_id: calendar_id,
+ title: "Breakdown for #{event.title}",
+ event_start: event_end.to_unix,
+ event_end: (event_end + breakdown_time.minutes).to_unix,
+ description: "<<<#{linked_events.to_json}}>>>",
+ attendees: [PlaceCalendar::Event::Attendee.new(name: calendar_id, email: calendar_id, response_status: "accepted", resource: true, organizer: true)],
+ ).get.to_json
+
+ logger.debug { "created breakdown event #{breakdown_event.id} on #{calendar_id}" }
+ event.breakdown_event_id = breakdown_event.id
+ end
+ elsif (breakdown_time = event.breakdown_time) && (breakdown_event_id = event.breakdown_event_id) && breakdown_time == 0
+ calendar.delete_event(
+ calendar_id: calendar_id,
+ event_id: breakdown_event_id,
+ )
+ logger.debug { "deleted breakdown event #{breakdown_event_id} on #{calendar_id}" }
+ event.breakdown_event_id = ""
+ end
+
+ # save metadata
+ staff_api.patch_event_metadata(system_id: system_id, event_id: signal.event_id, metadata: NamedTuple.new, ical_uid: signal.event_ical_uid, setup_time: event.setup_time, breakdown_time: event.breakdown_time, setup_event_id: event.setup_event_id, breakdown_event_id: event.breakdown_event_id).get
+ end
+
+ class PlaceCalendar::Event
+ property setup_time : Int64? = nil
+ property breakdown_time : Int64? = nil
+ property setup_event_id : String? = nil
+ property breakdown_event_id : String? = nil
+ end
+
+ struct LinkedEvents
+ include JSON::Serializable
+
+ property main_event_ical : String?
+ property main_event_id : String?
+ property setup_event_id : String?
+ property breakdown_event_id : String?
+
+ def initialize(@main_event_ical : String?, @main_event_id : String?)
+ end
+ end
+
+ struct LinkedEvents
+ include JSON::Serializable
+
+ property main_event_ical : String?
+ property main_event_id : String?
+ property setup_event_id : String?
+ property breakdown_event_id : String?
+
+ def initialize(@main_event_ical : String?, @main_event_id : String?)
+ end
+ end
+
+ struct EventChangedSignal
+ include JSON::Serializable
+
+ property action : String
+ property system_id : String
+ property event_id : String
+ property event_ical_uid : String
+ property host : String?
+ property resource : String
+ property event : PlaceCalendar::Event
+ property ext_data : JSON::Any?
+ end
+
+ struct EventMetadata
+ include JSON::Serializable
+
+ property system_id : String
+ property event_id : String
+ property recurring_master_id : String?
+ property ical_uid : String
+
+ property host_email : String
+ property resource_calendar : String
+ property event_start : Int64
+ property event_end : Int64
+ property cancelled : Bool = false
+
+ property ext_data : JSON::Any?
+
+ property setup_time : Int64 = 0
+ property breakdown_time : Int64 = 0
+ property setup_event_id : String?
+ property breakdown_event_id : String?
+ end
+end
diff --git a/drivers/place/event_setup_breakdown_time_spec.cr b/drivers/place/event_setup_breakdown_time_spec.cr
new file mode 100644
index 00000000000..0b274bc8510
--- /dev/null
+++ b/drivers/place/event_setup_breakdown_time_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::EventSetupBreakdownTime" do
+end
diff --git a/drivers/place/http_pinger.cr b/drivers/place/http_pinger.cr
new file mode 100644
index 00000000000..14659bb7b0a
--- /dev/null
+++ b/drivers/place/http_pinger.cr
@@ -0,0 +1,84 @@
+require "placeos-driver"
+
+class Place::HTTPPinger < PlaceOS::Driver
+ # Discovery Information
+ generic_name :Ping
+ descriptive_name "Service Status Check"
+ uri_base "https://192.168.0.2/api/healthcheck"
+
+ default_settings({
+ basic_auth: {
+ username: "srvc_acct",
+ password: "password!",
+ },
+ ping_every: 60,
+ expected_response_code: 200,
+ http_max_requests: 0,
+ request_verb: "GET",
+ request_headers: {
+ "Accept" => "application/json",
+ },
+ })
+
+ getter response_mismatch_count : UInt64 = 0_u64
+ getter response_failure_count : UInt64 = 0_u64
+
+ getter expected_response_code : Int32 = 200
+ getter request_verb : String = "GET"
+ @request_headers : HTTP::Headers = HTTP::Headers.new
+ alias HeaderJSON = Hash(String, Array(String) | String)
+
+ def on_load
+ transport.before_request do |request|
+ logger.debug { "using proxy #{!!transport.proxy_in_use} #{transport.proxy_in_use.inspect}\nconnecting to host: #{config.uri}\nperforming request: #{request.method} #{request.path}\nheaders: #{request.headers}\n#{!request.body.nil? ? String.new(request.body.as(IO::Memory).to_slice) : nil}" }
+ end
+
+ on_update
+ end
+
+ def on_update
+ schedule.clear
+ schedule.every((setting?(Int32, :ping_every) || 60).seconds) { check_status }
+ @request_verb = setting?(String, :request_verb) || "GET"
+ @expected_response_code = setting?(Int32, :expected_response_code) || 200
+
+ request_headers = HTTP::Headers.new
+ headers = setting?(HeaderJSON, :request_headers) || {} of String => Array(String) | String
+ headers.each { |key, value| request_headers.add(key, value) }
+ @request_headers = request_headers
+ end
+
+ def connected
+ check_status
+ end
+
+ def check_status : Bool
+ response = http(@request_verb, "/", headers: @request_headers)
+
+ if response.status_code == expected_response_code
+ self[:last_successful_check] = Time.utc.to_unix
+ self[:last_response_code] = response.status_code
+ true
+ else
+ self[:last_response_code] = response.status_code
+ @response_mismatch_count += 1
+ self[:response_mismatch_count] = @response_mismatch_count
+ queue.online = false
+ false
+ end
+ rescue error
+ logger.warn(exception: error) { "HTTP service not responding" }
+ @response_failure_count += 1
+ self[:response_failure_count] = @response_failure_count
+ self[:last_error] = error.message
+ false
+ end
+
+ DUMMY_CALLBACK = Proc(Task, Nil).new { nil }
+
+ @[Security(Level::Administrator)]
+ def curl(verb : String, path : String, headers : Hash(String, String) = {} of String => String, body : String? = nil)
+ response = http(verb, path, body, headers: headers)
+ logger.debug { "response #{response.status}: #{response.status_message}\nheaders: #{response.headers}\n#{response.body}" }
+ end
+end
diff --git a/drivers/place/http_pinger_spec.cr b/drivers/place/http_pinger_spec.cr
new file mode 100644
index 00000000000..f1e5362c086
--- /dev/null
+++ b/drivers/place/http_pinger_spec.cr
@@ -0,0 +1,22 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::HTTPPinger" do
+ expect_http_request do |request, response|
+ response.status_code = 200
+ end
+
+ sleep 1
+
+ status[:last_response_code]?.should eq 200
+ status[:connected]?.should eq true
+
+ retval = exec(:check_status)
+ expect_http_request do |request, response|
+ response.status_code = 400
+ end
+ retval.get
+
+ status[:last_response_code]?.should eq 400
+ status[:response_mismatch_count]?.should eq 1
+ status[:connected]?.should eq false
+end
diff --git a/drivers/place/llm/llm.cr b/drivers/place/llm/llm.cr
new file mode 100644
index 00000000000..66e11088f53
--- /dev/null
+++ b/drivers/place/llm/llm.cr
@@ -0,0 +1,64 @@
+require "placeos-driver"
+require "placeos-driver/interface/chat_functions"
+
+class Place::LLM < PlaceOS::Driver
+ descriptive_name "PlaceOS LLM Interface"
+ generic_name :LLM
+ description %(an interface for LLMs such as ChatGPT for discovering capabilities)
+
+ default_settings({
+ prompt: %(you are an AI assistant in a smart building.
+Helping a staff member with every day tasks.
+Don't disclose that you're an AI
+Skip language that implies regret or apology
+say 'I don't know' for unknowns
+skip expert disclaimers
+no repetitive answers
+don't direct to other sources
+focus on key points in questions
+simplify complex issues with steps
+clarify unclear questions before answering
+request any missing details before running functions, such as meeting title etc
+bookings cannot be made in the past
+correct errors in previous answers
+end with follow up questions where applicable),
+
+ user_hint: "Hi! I'm your workplace assistant.\n" +
+ "I can get you instant answers for almost anything as well as perform actions such as booking a meeting room.\n" +
+ "How can I help?",
+ })
+
+ def on_update
+ @prompt = setting(String, :prompt)
+ @user_hint = setting?(String, :user_hint) || "Hi! I'm your workplace assistant."
+
+ schedule.clear
+ schedule.in(5.seconds) { update_prompt }
+ schedule.every(5.minutes) { update_prompt }
+ end
+
+ getter! user_hint : String
+ getter! prompt : String
+
+ def capabilities
+ system.implementing(Interface::ChatFunctions).map do |driver|
+ {
+ id: driver.module_name,
+ capability: driver[:capabilities].as_s,
+ }
+ end
+ end
+
+ def new_chat
+ {
+ prompt: @prompt,
+ capabilities: capabilities,
+ system_id: system.id,
+ }
+ end
+
+ protected def update_prompt
+ self[:prompt] = new_chat
+ self[:user_hint] = @user_hint
+ end
+end
diff --git a/drivers/place/llm/llm_spec.cr b/drivers/place/llm/llm_spec.cr
new file mode 100644
index 00000000000..525f5aabf56
--- /dev/null
+++ b/drivers/place/llm/llm_spec.cr
@@ -0,0 +1,94 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/chat_functions"
+
+DriverSpecs.mock_driver "Place::LLM" do
+ system({
+ DeskBookings: {DeskMock},
+ RoomBookings: {RoomMock},
+ })
+
+ sleep 200.milliseconds
+
+ exec(:capabilities).get.should eq [
+ {
+ "id" => "DeskBookings",
+ "capability" => "provides methods listing current desk bookings and booking or allocating a new desk booking",
+ },
+ {
+ "id" => "RoomBookings",
+ "capability" => "provides methods listing current meeting room bookings or events and booking new meetings or events",
+ },
+ ]
+
+ system(:DeskBookings_1).function_schemas.should eq([
+ {
+ function: "list_of_levels",
+ description: "returns the list of levels with available desks",
+ parameters: {} of String => JSON::Any,
+ },
+ {
+ function: "book",
+ description: "books a desk, you can optionally provide a preferred level or how many days from now if the booking is for tomorrow etc",
+ parameters: {
+ "level" => {
+ "anyOf" => [{"type" => "null"}, {"type" => "string"}],
+ "title" => "(String | Nil)",
+ "default" => nil,
+ },
+ "days_in_future" => {
+ "type" => "integer",
+ "format" => "Int32",
+ "title" => "Int32",
+ "default" => 0,
+ },
+ },
+ },
+ ])
+end
+
+# :nodoc:
+class DeskMock < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::ChatFunctions
+
+ def capabilities : String
+ "provides methods listing current desk bookings and booking or allocating a new desk booking"
+ end
+
+ @[Description("returns the list of levels with available desks")]
+ def list_of_levels
+ {"level 1", "level 2"}
+ end
+
+ @[Description("books a desk, you can optionally provide a preferred level or how many days from now if the booking is for tomorrow etc")]
+ def book(level : String? = nil, days_in_future : Int32 = 0)
+ "you've been allocated desk 123 on #{level || "level 2"}"
+ end
+end
+
+# :nodoc:
+class RoomMock < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::ChatFunctions
+
+ def capabilities : String
+ "provides methods listing current meeting room bookings or events and booking new meetings or events"
+ end
+
+ def my_bookings(days_in_future : Int32 = 0)
+ [{
+ room: "room@site.com",
+ booking_id: "12345",
+ title: "Blah",
+ organizer: "Janis",
+ }]
+ end
+
+ @[Description("returns the list of levels with available rooms")]
+ def list_of_levels(number_of_attendees : Int32)
+ {"level 1", "level 2"}
+ end
+
+ @[Description("books a room, you can optionally provide a preferred level or how many days from now if the booking is for tomorrow etc")]
+ def book(number_of_attendees : Int32, level : String? = nil, days_in_future : Int32 = 0)
+ "you've been allocated room studio 2 on #{level || "level 2"}"
+ end
+end
diff --git a/drivers/place/llm/schedule.cr b/drivers/place/llm/schedule.cr
new file mode 100644
index 00000000000..196c7e3b71b
--- /dev/null
+++ b/drivers/place/llm/schedule.cr
@@ -0,0 +1,393 @@
+require "placeos-driver"
+require "placeos-driver/interface/chat_functions"
+require "place_calendar"
+
+class Place::Schedule < PlaceOS::Driver
+ include Interface::ChatFunctions
+
+ descriptive_name "LLM Users Schedule"
+ generic_name :Schedule
+ description %(provides calendaring functions to a LLM)
+
+ default_settings({
+ platform: "office365", # or "google"
+ email_domain: "org.com",
+ conference_type: "teamsForBusiness",
+
+ # fallback if there isn't one on the zone
+ time_zone: "Australia/Sydney",
+ })
+
+ @platform : String = "office365"
+ @email_domain : String = "org.com"
+ @conference_type : String? = "teamsForBusiness"
+ @fallback_timezone : Time::Location = Time::Location::UTC
+
+ def on_update
+ timezone = config.control_system.not_nil!.timezone.presence || setting?(String, :time_zone).presence || "Australia/Sydney"
+ @fallback_timezone = Time::Location.load(timezone)
+ @platform = setting?(String, :platform) || "office365"
+ @email_domain = setting?(String, :email_domain) || "org.com"
+ @conference_type = setting?(String, :conference_type)
+ end
+
+ # =========================
+ # The LLM Interface
+ # =========================
+
+ getter capabilities : String do
+ String.build do |str|
+ str << "lookup or search for the email and phone numbers of other staff members if you haven't been provided their details. Do not guess.\n"
+ str << "provides details of my daily schedule, meeting room bookings and events I'm attending.\n"
+ str << "meeting room bookings must have a resource as an attendee.\n"
+ str << "my meeting room bookings will have me as the host or creator.\n"
+ str << "meeting rooms are the attendees marked as resources.\n"
+ str << "all day events may not have an ending time.\n"
+ str << "internal staff have the following email domain: #{@email_domain}. We can only obtain the schedules of internal staff\n"
+ str << "check schedules before booking or moving meetings to ensure no one is busy at that time\n"
+ end
+ end
+
+ @[Description("returns my schedule with event details with attendees and their response status. day_offset: 0 will return todays schedule, day_offset: 1 will return tomorrows schedule etc. If you provide a date, in ISO 8601 format and the correct timezone, the date will be used.")]
+ def my_schedule(day_offset : Int32 = 0, date : Time? = nil)
+ cal_client = place_calendar_client
+ me = current_user
+
+ if date
+ starting = date.in(timezone).at_beginning_of_day
+ else
+ now = Time.local(timezone)
+ days = day_offset.days
+ starting = now.at_beginning_of_day + days
+ end
+ ending = starting.at_end_of_day
+
+ logger.debug { "requesting events for #{me.name} (#{me.email}) @ #{starting} -> #{ending}" }
+
+ events = cal_client.list_events(me.email, period_start: starting, period_end: ending)
+ events = Array(Event).from_json(events.to_json)
+ events.each { |event| event.configure_times(timezone) }
+
+ events
+ end
+
+ @[Description("search for a staff members phone and email addresses using odata filter queries, don't include `$filter=`, for example: `givenName eq 'mary' or startswith(surname,'smith')`, confrim with the user when there are multiple results, search for both givenName and surname using `or` if there is ambiguity")]
+ def search_staff_member(filter : String)
+ logger.debug { "searching for staff member: #{filter}" }
+ cal_client = place_calendar_client
+ cal_client.list_users(filter: filter)
+ end
+
+ @[Description("look up a staff members name and phone number by providing their email address. Use search if you only have their name")]
+ def lookup_staff_member(email : String)
+ logger.debug { "looking up staff member: #{email}" }
+ cal_client = place_calendar_client
+ user = cal_client.get_user_by_email(email)
+ return "could not find a staff member with email #{email}. Try searching for their name?" unless user
+ user
+ end
+
+ @[Description("returns busy periods of the emails specified. Search for staff first if you haven't been given their email address. This can be a person or a resource like a room. An empty schedules array means they are available")]
+ def get_schedules(emails : Array(String), day_offset : Int32 = 0, date : Time? = nil)
+ cal_client = place_calendar_client
+ me = current_user
+
+ if date
+ starting = date.in(timezone).at_beginning_of_day
+ else
+ now = Time.local(timezone)
+ days = day_offset.days
+ starting = now.at_beginning_of_day + days
+ end
+ ending = starting.at_end_of_day
+ return "past schedules are not useful" if ending < Time.utc
+
+ duration = ending - starting
+
+ logger.debug { "getting schedules for #{emails} @ #{starting} -> #{ending}" }
+
+ availability_view_interval = {duration, 30.minutes}.min.total_minutes.to_i!
+
+ # format the data that helps the LLM make sense of it
+ tz = timezone
+ cal_client.get_availability(me.email, emails, starting, ending, view_interval: availability_view_interval).map do |avail|
+ {
+ email: avail.calendar,
+ schedule: avail.availability.map do |sched|
+ {
+ status: sched.status,
+ starting: sched.starts_at.in(tz),
+ ending: sched.ends_at.in(tz),
+ }
+ end,
+ }
+ end
+ end
+
+ @[Description("create a calendar entry with the provided event details. Make sure the attendees are available by getting their schedules first, remember to include the host in the attendees list. An ending time is required except for all day bookings. You can specify an alternate host if booking on behalf of someone else. Don't provide a response_status for attendees when using this function. Starting and ending date times must be ISO 8601 formatted with the timezone")]
+ def create(event : CreateEvent)
+ cal_client = place_calendar_client
+ me = current_user
+ my_email = me.email.downcase
+ host_email = (event.host.presence || me.email).downcase
+ i_am_host = host_email == my_email
+ host_name = host_email
+
+ attendees = event.attendees.uniq.reject do |attendee|
+ attend_email = attendee.email.downcase
+ if attend_email == host_email
+ host_name = attendee.name
+ true
+ elsif attend_email == my_email
+ attendee.organizer = true
+ false
+ end
+ end
+ attendees << PlaceCalendar::Event::Attendee.new(name: i_am_host ? me.name : host_name, email: host_email, response_status: "accepted", organizer: i_am_host)
+
+ return "error: ending time required unless this is an all_day event" if event.ending.nil? && event.all_day == false
+
+ # create the calendar event
+ new_event = PlaceCalendar::Event.new
+ new_event.attendees = attendees
+ new_event.title = event.title
+ new_event.location = event.location
+ new_event.all_day = event.all_day
+ new_event.event_start = event.starting.in(timezone)
+ new_event.event_end = event.ending.try &.in(timezone)
+ new_event.body = event.title
+ new_event.timezone = timezone.name
+ new_event.creator = my_email
+ new_event.host = host_email
+
+ logger.debug { "creating booking: #{new_event.inspect}" }
+
+ # convert to the simplified view
+ created_event = cal_client.create_event(user_id: my_email, event: new_event, calendar_id: host_email)
+ Event.from_json(created_event.to_json).configure_times(timezone)
+ end
+
+ @[Description("update the details of an existing event. The original id is required, otherwise you only need to provide the changes. You must provide the complete list of attendees if that list is being modified. Don't provide a response_status for attendees when using this function. You can't modify events where the start time is in the past")]
+ def modify(event : UpdateEvent)
+ cal_client = place_calendar_client
+ me = current_user
+
+ # fetch existing event
+ existing = cal_client.get_event(me.email, id: event.id)
+ return "error: could not find event with id '#{event.id}', it may have been cancelled?" unless existing
+
+ # update with these new details
+ {% for param in %w(title location host attendees) %}
+ existing.{{param.id}} = event.{{param.id}}.nil? ? existing.{{param.id}} : event.{{param.id}}.not_nil!
+ {% end %}
+
+ existing.event_start = event.starting.nil? ? existing.event_start.in(timezone) : event.starting.not_nil!.in(timezone)
+ if event.all_day
+ existing.all_day = true
+ existing.event_end = nil
+ else
+ existing.all_day = false
+ existing.event_end = event.ending.nil? ? existing.event_end.try(&.in(timezone)) : event.ending.not_nil!.in(timezone)
+ return "error: ending time required unless this is an all_day event" if event.ending.nil? && event.all_day == false
+ end
+
+ logger.debug { "updating event: #{existing.inspect}" }
+
+ # update the event
+ updated_event = cal_client.update_event(user_id: me.email, event: existing, calendar_id: existing.host)
+ Event.from_json(updated_event.to_json).configure_times(timezone)
+ end
+
+ @[Description("cancels an event with an optional reason")]
+ def cancel(event_id : String, reason : String? = nil)
+ cal_client = place_calendar_client
+ me = current_user
+
+ logger.debug { "declining event: #{event_id}" }
+
+ cal_client.decline_event(
+ user_id: me.email,
+ id: event_id,
+ notify: !!reason,
+ comment: reason
+ )
+
+ "cancelled"
+ end
+
+ enum Attendance
+ Attend
+ Decline
+ end
+
+ @[Description("use to confirm your attendance at a meeting this will update your attendee response_status in the specified meeting from your schedule. You should probably provide a reason when declining, however this is optional")]
+ def update_attending_status(event_id : String, attendance : Attendance, reason : String? = nil)
+ cal_client = place_calendar_client
+ me = current_user
+
+ logger.debug { "updating attendance: #{attendance} #{reason} -> #{event_id}" }
+
+ case attendance
+ in .decline?
+ cal_client.decline_event(
+ user_id: me.email,
+ id: event_id,
+ notify: true,
+ comment: reason
+ )
+
+ "declined"
+ in .attend?
+ cal_client.accept_event(
+ user_id: me.email,
+ id: event_id,
+ notify: true,
+ comment: reason
+ )
+
+ "attending"
+ end
+ end
+
+ # =========================
+ # Support functions
+ # =========================
+
+ struct CreateEvent
+ include JSON::Serializable
+
+ getter title : String
+ getter location : String?
+ getter host : String?
+ getter attendees : Array(PlaceCalendar::Event::Attendee) = [] of PlaceCalendar::Event::Attendee
+ getter starting : Time
+ getter ending : Time?
+ getter all_day : Bool = false
+ end
+
+ struct UpdateEvent
+ include JSON::Serializable
+
+ getter id : String
+ getter title : String?
+ getter location : String?
+ getter host : String?
+ getter attendees : Array(PlaceCalendar::Event::Attendee)?
+ getter starting : Time?
+ getter ending : Time?
+ getter all_day : Bool?
+ end
+
+ class Event
+ include JSON::Serializable
+
+ getter id : String?
+ getter title : String?
+ getter location : String?
+ getter status : String?
+ getter host : String?
+ getter creator : String?
+ getter all_day : Bool
+ getter attendees : Array(PlaceCalendar::Event::Attendee)
+ getter online_meeting_url : String?
+
+ # We convert unix time into something more readable for a human or AI
+ @[JSON::Field(converter: Time::EpochConverter, type: "integer", format: "Int64", ignore_serialize: true)]
+ getter event_start : Time
+
+ @[JSON::Field(converter: Time::EpochConverter, type: "integer", format: "Int64", ignore_serialize: true)]
+ getter event_end : Time?
+
+ getter starting : Time?
+ getter ending : Time?
+
+ # these are used to configure the JSON times correctly
+ @[JSON::Field(ignore_serialize: true)]
+ getter timezone : String?
+
+ @[JSON::Field(ignore: true)]
+ getter! time_zone : Time::Location
+
+ def configure_times(tz : Time::Location)
+ @time_zone = tz
+ @starting = event_start.in(tz)
+ @ending = event_end.try &.in(tz)
+ self
+ end
+ end
+
+ struct User
+ include JSON::Serializable
+
+ getter name : String
+ getter email : String
+ end
+
+ protected def staff_api
+ system["StaffAPI_1"]
+ end
+
+ def current_user : User
+ User.from_json staff_api.user(invoked_by_user_id).get.to_json
+ end
+
+ getter timezone : Time::Location do
+ building.time_zone || @fallback_timezone
+ end
+
+ struct Zone
+ include JSON::Serializable
+
+ getter id : String
+ getter name : String
+ getter display_name : String?
+
+ @[JSON::Field(key: "timezone")]
+ getter tz : String?
+
+ @[JSON::Field(ignore: true)]
+ getter time_zone : Time::Location? do
+ if tz = @tz.presence
+ Time::Location.load(tz)
+ end
+ end
+ end
+
+ getter building : Zone { get_building }
+
+ # Finds the building ID for the current location services object
+ def get_building : Zone
+ zones = staff_api.zones(tags: "building").get.as_a
+ zone_ids = zones.map(&.[]("id").as_s)
+ building_id = (zone_ids & system.zones).first
+
+ building = zones.find! { |zone| zone["id"].as_s == building_id }
+ Zone.from_json building.to_json
+ rescue error
+ msg = "unable to determine building zone"
+ logger.warn(exception: error) { msg }
+ raise msg
+ end
+
+ record AccessToken, token : String, expires : Int64? { include JSON::Serializable }
+
+ protected def get_users_access_token
+ AccessToken.from_json staff_api.user_resource_token.get.to_json
+ end
+
+ protected def place_calendar_client : ::PlaceCalendar::Client
+ token = get_users_access_token
+
+ case @platform
+ when "office365"
+ cal = ::PlaceCalendar::Office365.new(token.token, @conference_type, delegated_access: true)
+ ::PlaceCalendar::Client.new(cal)
+ when "google"
+ auth = ::Google::TokenAuth.new(token.token, token.expires || 5.hours.from_now.to_unix)
+ cal = ::PlaceCalendar::Google.new(auth, @email_domain, conference_type: @conference_type, delegated_access: true)
+ ::PlaceCalendar::Client.new(cal)
+ else
+ raise "unknown platform: #{@platform}, expecting google or office365"
+ end
+ end
+end
diff --git a/drivers/place/llm/schedule_spec.cr b/drivers/place/llm/schedule_spec.cr
new file mode 100644
index 00000000000..2d9133076c6
--- /dev/null
+++ b/drivers/place/llm/schedule_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Schedule" do
+end
diff --git a/drivers/place/llm/todo_list.cr b/drivers/place/llm/todo_list.cr
new file mode 100644
index 00000000000..2e60fd4d338
--- /dev/null
+++ b/drivers/place/llm/todo_list.cr
@@ -0,0 +1,38 @@
+require "placeos-driver"
+require "placeos-driver/interface/chat_functions"
+
+class Place::TODOs < PlaceOS::Driver
+ include Interface::ChatFunctions
+
+ descriptive_name "PlaceOS TODO list"
+ generic_name :TODO
+ description %(an example driver providing functions to a LLM)
+
+ @todos = [] of NamedTuple(complete: Bool, task: String)
+
+ def on_load
+ self[:loaded] = true
+ end
+
+ def capabilities : String
+ "manages the list of tasks a user needs to complete throughout the day"
+ end
+
+ @[Description("returns the list of tasks and their current status")]
+ def list_tasks
+ @todos
+ end
+
+ @[Description("adds a new task to the list")]
+ def add_task(description : String)
+ task = {complete: false, task: description}
+ @todos << task
+ task
+ end
+
+ @[Description("marks a task as completed")]
+ def complete_task(index : Int32)
+ task = @todos[index]
+ @todos[index] = {complete: true, task: task[:task]}
+ end
+end
diff --git a/drivers/place/llm/todo_list_spec.cr b/drivers/place/llm/todo_list_spec.cr
new file mode 100644
index 00000000000..a7770d24d3e
--- /dev/null
+++ b/drivers/place/llm/todo_list_spec.cr
@@ -0,0 +1,50 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::TODOs" do
+ exec(:add_task, "my task").get.should eq({
+ "complete" => false,
+ "task" => "my task",
+ })
+
+ exec(:list_tasks).get.should eq([{
+ "complete" => false,
+ "task" => "my task",
+ }])
+
+ exec(:complete_task, 0).get.should eq({
+ "complete" => true,
+ "task" => "my task",
+ })
+
+ exec(:list_tasks).get.should eq([{
+ "complete" => true,
+ "task" => "my task",
+ }])
+
+ exec(:function_schemas).get.should eq([
+ {
+ "function" => "list_tasks",
+ "description" => "returns the list of tasks and their current status",
+ "parameters" => {} of String => JSON::Any,
+ },
+ {
+ "function" => "add_task",
+ "description" => "adds a new task to the list",
+ "parameters" => {
+ "description" => {"type" => "string", "title" => "String"},
+ },
+ },
+ {
+ "function" => "complete_task",
+ "description" => "marks a task as completed",
+ "parameters" => {
+ "index" => {"type" => "integer", "format" => "Int32", "title" => "Int32"},
+ },
+ },
+ ])
+
+ # Test the interface
+ status[:capabilities].should eq exec(:capabilities).get
+ status[:function_schemas].should eq exec(:function_schemas).get
+ status[:loaded].should eq(true)
+end
diff --git a/drivers/place/llm/workplace.cr b/drivers/place/llm/workplace.cr
new file mode 100644
index 00000000000..a17684e38c1
--- /dev/null
+++ b/drivers/place/llm/workplace.cr
@@ -0,0 +1,501 @@
+require "placeos-driver"
+require "placeos-driver/interface/chat_functions"
+require "set"
+
+# metadata class
+require "placeos"
+
+class Place::Workplace < PlaceOS::Driver
+ include Interface::ChatFunctions
+
+ descriptive_name "LLM Workplace interface"
+ generic_name :Workplace
+ description %(provides workplace introspection functions to a LLM)
+
+ default_settings({
+ # fallback if there isn't one on the zone
+ time_zone: "Australia/Sydney",
+ })
+
+ @fallback_timezone : Time::Location = Time::Location::UTC
+
+ def on_update
+ timezone = config.control_system.not_nil!.timezone.presence || setting?(String, :time_zone).presence || "Australia/Sydney"
+ @fallback_timezone = Time::Location.load(timezone)
+ end
+
+ # =========================
+ # The LLM Interface
+ # =========================
+
+ getter capabilities : String do
+ String.build do |str|
+ str << "functions for listing building levels to obtain level names and level ids\n"
+ str << "find meeting rooms, filtering by capacity and or level id\n"
+ str << "my current desk, car parking and guest visitor bookings\n"
+ str << "Note: when booking a meeting room, preference one on the same level or closest level to my desk booking, if I have one, unless I specify a specific level. Also try to pick a room with an appropriate capacity.\n"
+ str << "once candidate meeting rooms have been found, you can include the list of resource emails when getting schedules to see which rooms are available\n"
+ str << "this capability also supports managing desk bookings and inviting visitors to the building\n"
+ str << "please cancel any bookings made on the incorrect day"
+ end
+ end
+
+ @[Description("returns desks, car parking spaces and visitors I have booked. day_offset: 0 will return todays schedule, day_offset: 1 will return tomorrows schedule etc. If you provide a date, in ISO 8601 format and the correct timezone, the date will be used.")]
+ def my_bookings(day_offset : Int32 = 0, date : Time? = nil)
+ me = current_user
+
+ if date
+ starting = date.in(timezone).at_beginning_of_day
+ logger.debug { "listing bookings for #{current_user.email}, on day #{starting}" }
+ else
+ logger.debug { "listing bookings for #{current_user.email}, day offset #{day_offset}" }
+ now = Time.local(timezone)
+ days = day_offset.days
+ starting = now.at_beginning_of_day + days
+ end
+ ending = starting.at_end_of_day
+
+ {"desk", "visitor", "parking", "asset-request"}.flat_map do |booking_type|
+ staff_api.query_bookings(
+ type: booking_type,
+ period_start: starting.to_unix,
+ period_end: ending.to_unix,
+ zones: {building.id},
+ user: invoked_by_user_id,
+ email: me.email
+ ).get.as_a.compact_map { |b| to_friendly_booking(b) }
+ end
+ end
+
+ @[Description("returns the building details and list of levels. Use this to obtain level_ids")]
+ def levels : Array(Zone)
+ logger.debug { "getting list of levels" }
+ l = all_levels
+ l.each do |level|
+ all_desks = staff_api.metadata(level.id, "desks").get.dig?("desks", "details")
+ if all_desks
+ desks = all_desks.as_a
+ level.bookable_desk_count = desks.size
+ features = Set(String).new
+ desks.each do |desk|
+ if feat = desk["features"]?
+ feat.as_a.each { |f| features << f.as_s.downcase }
+ end
+ end
+ level.desk_features = features.to_a unless features.empty?
+ else
+ level.bookable_desk_count = 0
+ end
+ end
+ l
+ end
+
+ getter all_levels : Array(Zone) do
+ [building] + Array(Zone).from_json(staff_api.zones(parent: building.id, tags: {"level"}).get.to_json).sort_by(&.name)
+ end
+
+ @[Description("returns the list of meeting rooms in the building filtering by capacity or level")]
+ def meeting_rooms(minimum_capacity : Int32 = 1, level_id : String? = nil)
+ logger.debug { "listing meeting rooms on level #{level_id} with capacity #{minimum_capacity}" }
+
+ # ensure the level id exists if provided
+ if level_id
+ level = levels.find { |l| l.id == level_id }
+ raise "could not find level_id #{level_id} in the building. Make sure you've obtained the list of levels." unless level
+ end
+
+ zone_id = level_id || building.id
+ staff_api.systems(zone_id: zone_id, capacity: minimum_capacity, bookable: true).get.as_a.compact_map { |s| to_friendly_system(s) }
+ end
+
+ alias PlaceZone = PlaceOS::Client::API::Models::Zone
+ alias Metadata = Hash(String, PlaceOS::Client::API::Models::Metadata)
+ alias ChildMetadata = Array(NamedTuple(zone: PlaceZone, metadata: Metadata))
+
+ @[Description("returns the list of desks available for booking on the level and day specified. If the level has desk features then you can also filter by features.")]
+ def desks(level_id : String, day_offset : Int32 = 0, date : Time? = nil, feature : String? = nil)
+ logger.debug { "listing desks on level #{level_id}, day offset #{day_offset}" }
+
+ # ensure the level id exists
+ level = levels.find { |l| l.id == level_id }
+ raise "could not find level_id #{level_id} in the building. Make sure you've obtained the list of levels." unless level
+
+ # get the list of desks for the level
+ all_desks = staff_api.metadata(level.id, "desks").get.dig?("desks", "details")
+ raise "no bookable desks on this level, please try another." unless all_desks
+ desks = Array(Desk).from_json(all_desks.to_json)
+
+ # calculate the offset time
+ if date
+ starting = date.in(timezone).at_beginning_of_day
+ else
+ now = Time.local(timezone)
+ days = day_offset.days
+ starting = now.at_beginning_of_day + days
+ end
+ ending = starting.at_end_of_day
+
+ # need current user so we can filter out desks limited to certain groups
+ me = current_user
+
+ # get the current bookings for the level
+ bookings = staff_api.query_bookings(type: "desk", period_start: starting.to_unix, period_end: ending.to_unix, zones: {level_id}).get.as_a
+ bookings = bookings.map(&.[]("asset_id").as_s)
+
+ # filter out desks that are not available to the user
+ feature = feature.try(&.downcase)
+ desks.reject! do |desk|
+ next true if desk.id.in?(bookings)
+ next true if feature && !desk.features.map!(&.downcase).includes?(feature)
+ if !desk.groups.empty?
+ (desk.groups & me.groups).empty?
+ end
+ end
+
+ # need to limit the results as the LLM runs out of memory
+ logger.debug { "found #{desks.size} available desks" }
+ desks.sample(5)
+ end
+
+ @[Description("books an asset, such as a desk or car parking space, for the number of days specified, starting on the day offset. For desk bookings use booking_type: desk")]
+ def book_relative(booking_type : String, asset_id : String, level_id : String, day_offset : Int32 = 0, number_of_days : Int32 = 1)
+ logger.debug { "booking relative #{booking_type}, asset #{asset_id} on level #{level_id}, day offset #{day_offset} for num days #{number_of_days}" }
+
+ # ensure the level id exists
+ level = levels.find { |l| l.id == level_id }
+ raise "could not find level_id #{level_id} in the building. Make sure you've obtained the list of levels." unless level
+
+ user_id = invoked_by_user_id
+ me = current_user
+ current_time = Time.local(timezone)
+ now = current_time.at_beginning_of_day
+
+ raise "booking in the past is not permitted" unless day_offset > 0 || (day_offset == 0 && current_time.hour < 18)
+
+ # ensure the asset exists if we can check for it
+ case booking_type
+ when "desk"
+ all_desks = staff_api.metadata(level.id, "desks").get.dig?("desks", "details")
+ raise "no desks found on level #{level_id}, ensure this id is correct" unless all_desks
+ desks = Array(Desk).from_json(all_desks.to_json)
+ desk = desks.find { |d| d.id == asset_id }
+
+ raise "could not find a desk with id: #{asset_id}" unless desk
+ end
+
+ ids = (day_offset...(day_offset + number_of_days)).map do |offset|
+ # calculate the offset time
+ days = offset.days
+ starting = now + days + 8.hours
+ ending = now.at_end_of_day + days - 4.hours
+
+ resp = staff_api.create_booking(
+ booking_type: booking_type,
+ asset_id: asset_id,
+ user_id: user_id,
+ user_email: me.email,
+ user_name: me.name,
+ zones: {level_id, building.id},
+ booking_start: starting.to_unix,
+ booking_end: ending.to_unix,
+ time_zone: timezone.to_s,
+ utm_source: "chatgpt"
+ )
+ resp.get["id"].as_i64
+ end
+ starting = now + day_offset.days
+
+ {
+ booking_ids: ids,
+ details: "booking for #{asset_id} created on #{starting.day_of_week}, #{starting.to_s("%F")} for #{number_of_days} #{number_of_days > 1 ? "days" : "day"}",
+ }
+ end
+
+ @[Description("books an asset, such as a desk or car parking space, for the number of days specified, the start date must be in ISO 8601 format with the correct timezone. For desk bookings use booking_type: desk")]
+ def book_on(booking_type : String, asset_id : String, level_id : String, date : Time, number_of_days : Int32 = 1)
+ logger.debug { "booking on #{booking_type}, asset #{asset_id} on level #{level_id}, date #{date} for num days #{number_of_days}" }
+
+ # ensure the level id exists
+ level = levels.find { |l| l.id == level_id }
+ raise "could not find level_id #{level_id} in the building. Make sure you've obtained the list of levels." unless level
+
+ user_id = invoked_by_user_id
+ me = current_user
+ now = date.in(timezone).at_beginning_of_day
+ current_time = Time.local(timezone)
+ raise "booking in the past is not permitted" unless current_time < now || (current_time - now) < 18.hours
+
+ # ensure the asset exists if we can check for it
+ case booking_type
+ when "desk"
+ all_desks = staff_api.metadata(level.id, "desks").get.dig?("desks", "details")
+ raise "no desks found on level #{level_id}, ensure this id is correct" unless all_desks
+ desks = Array(Desk).from_json(all_desks.to_json)
+ desk = desks.find { |d| d.id == asset_id }
+
+ raise "could not find a desk with id: #{asset_id}" unless desk
+ end
+
+ ids = (0...number_of_days).map do |offset|
+ # calculate the offset time
+ days = offset.days
+ starting = now + days + 8.hours
+ ending = now.at_end_of_day + days - 4.hours
+
+ resp = staff_api.create_booking(
+ booking_type: booking_type,
+ asset_id: asset_id,
+ user_id: user_id,
+ user_email: me.email,
+ user_name: me.name,
+ zones: {level_id, building.id},
+ booking_start: starting.to_unix,
+ booking_end: ending.to_unix,
+ time_zone: timezone.to_s,
+ utm_source: "chatgpt"
+ )
+ resp.get["id"].as_i64
+ end
+
+ {
+ booking_ids: ids,
+ details: "booking for #{asset_id} created on #{now.day_of_week}, #{now.to_s("%F")} for #{number_of_days} #{number_of_days > 1 ? "days" : "day"}",
+ }
+ end
+
+ @[Description("cancels the given booking ids")]
+ def cancel_bookings(booking_ids : Array(Int64))
+ logger.debug { "cancel bookings #{booking_ids}" }
+ booking_ids.each do |booking_id|
+ booking = staff_api.get_booking(booking_id).get
+ user_id = invoked_by_user_id
+ me = current_user
+ unless (user_id == booking["user_id"]?.try(&.as_s)) || me.email.downcase.in?({booking["user_email"].as_s, booking["booked_by_email"].as_s})
+ raise "can only cancel bookings owned by #{me.email} - this booking is owned by #{booking["user_email"]}"
+ end
+ staff_api.booking_delete(booking_id, "chatgpt")
+ end
+ "bookings have been removed"
+ end
+
+ @[Description("book a visitor to the building")]
+ def invite(visitor_name : String, visitor_email : String, day_offset : Int32 = 0, date : Time? = nil, number_of_days : Int32 = 1)
+ logger.debug { "inviting visitor to the building #{visitor_name}: #{visitor_email}, day offset #{day_offset} for num days #{number_of_days}" }
+
+ # select a random level
+ level = levels.first
+ user_id = invoked_by_user_id
+ me = current_user
+ current_time = Time.local(timezone)
+ now = current_time.at_beginning_of_day
+
+ # adjust the offset if a date has been selected
+ if date
+ desired_date = date.in(timezone).at_beginning_of_day
+ day_offset = (desired_date - now).total_days.round_away.to_i
+ end
+
+ raise "booking in the past is not permitted" unless day_offset > 0 || (day_offset == 0 && current_time.hour < 16)
+
+ visitor_email = visitor_email.downcase
+
+ ids = (day_offset...(day_offset + number_of_days)).map do |offset|
+ # calculate the offset time
+ days = offset.days
+ starting = now + days + 8.hours
+ ending = now.at_end_of_day + days - 4.hours
+
+ resp = staff_api.create_booking(
+ booking_type: "visitor",
+ asset_id: visitor_email,
+ user_id: user_id,
+ user_email: me.email,
+ user_name: me.name,
+ zones: {level.id, building.id},
+ booking_start: starting.to_unix,
+ booking_end: ending.to_unix,
+ time_zone: timezone.to_s,
+ utm_source: "chatgpt",
+
+ attendees: [{
+ name: visitor_name,
+ email: visitor_email,
+ }]
+ )
+ resp.get["id"].as_i64
+ end
+ starting = now + day_offset.days
+
+ {
+ booking_ids: ids,
+ details: "invited #{visitor_email} to the office on #{starting.day_of_week}, #{starting.to_s("%F")} for #{number_of_days} #{number_of_days > 1 ? "days" : "day"}",
+ }
+ end
+
+ # =========================
+ # Support functions
+ # =========================
+
+ struct Desk
+ include JSON::Serializable
+
+ getter id : String
+ getter groups : Array(String) = [] of String
+ getter features : Array(String) = [] of String
+ end
+
+ protected def to_friendly_system(system : JSON::Any) : System?
+ the_levels = levels
+
+ zone_ids = system["zones"].as_a.map(&.as_s)
+ level = the_levels.find do |l|
+ next nil unless l.tags.includes?("level")
+ zone_ids.find { |z| z == l.id }
+ end
+
+ if level
+ System.new level, system
+ end
+ end
+
+ struct System
+ include JSON::Serializable
+
+ getter id : String? = nil
+ getter name : String
+ getter features : Array(String)
+ getter email : String?
+ getter capacity : Int32 = 0
+
+ getter level_id : String
+ getter level_name : String
+ getter map_id : String? = nil
+
+ # getter images : Array(String)
+
+ def initialize(level : Zone, system : JSON::Any)
+ sys = system.as_h
+ @id = sys["id"].as_s
+ @name = sys["display_name"]?.try(&.as_s?) || sys["name"].as_s
+ # @description = sys["description"]?.try &.as_s? || ""
+ @features = sys["features"].as_a.map(&.as_s)
+ # @images = sys["images"].as_a.map(&.as_s)
+ @email = sys["email"]?.try &.as_s?
+ @capacity = sys["capacity"].as_i
+ @map_id = sys["map_id"]?.try &.as_s?
+ @level_id = level.id
+ @level_name = level.display_name || level.name
+ end
+ end
+
+ protected def to_friendly_booking(booking : JSON::Any) : Booking?
+ the_levels = levels
+
+ zone_ids = booking["zones"].as_a.map(&.as_s)
+ level = the_levels.find do |l|
+ next nil unless l.tags.includes?("level")
+ zone_ids.find { |z| z == l.id }
+ end
+
+ if level
+ Booking.new level, booking, timezone
+ end
+ end
+
+ struct Booking
+ include JSON::Serializable
+
+ getter id : Int64? = nil
+ getter starting : Time
+ getter ending : Time
+
+ getter booking_type : String
+ getter asset_id : String
+ getter user_id : String?
+ getter user_email : String
+ getter user_name : String
+ getter level_id : String
+ getter level_name : String
+
+ # getter booked_by_email : String
+ # getter booked_by_name : String
+
+ getter checked_in : Bool = false
+
+ def initialize(level : Zone, book : JSON::Any, timezone : Time::Location)
+ b = book.as_h
+ @id = b["id"].as_i64
+ @starting = Time.unix(b["booking_start"].as_i64).in(timezone)
+ @ending = Time.unix(b["booking_end"].as_i64).in(timezone)
+ @booking_type = b["booking_type"].as_s
+ @asset_id = b["asset_id"].as_s
+ @user_id = b["user_id"]?.try &.as_s?
+ @user_email = b["user_email"].as_s
+ @user_name = b["user_name"].as_s
+ @checked_in = b["checked_in"].as_bool
+ @level_id = level.id
+ @level_name = level.display_name || level.name
+
+ # @booked_by_email = b["booked_by_email"].as_s
+ # @booked_by_name = b["booked_by_name"].as_s
+ end
+ end
+
+ protected def staff_api
+ system["StaffAPI_1"]
+ end
+
+ def current_user : User
+ User.from_json staff_api.user(invoked_by_user_id).get.to_json
+ end
+
+ getter timezone : Time::Location do
+ building.time_zone || @fallback_timezone
+ end
+
+ struct User
+ include JSON::Serializable
+
+ getter name : String
+ getter email : String
+ getter groups : Array(String)
+ end
+
+ getter building : Zone { get_building }
+
+ class Zone
+ include JSON::Serializable
+
+ getter id : String
+ getter name : String
+ getter display_name : String?
+ getter tags : Array(String)
+
+ property bookable_desk_count : Int32? = nil
+ property desk_features : Array(String)? = nil
+
+ @[JSON::Field(key: "timezone")]
+ getter tz : String?
+
+ @[JSON::Field(ignore: true)]
+ getter time_zone : Time::Location? do
+ if tz = @tz.presence
+ Time::Location.load(tz)
+ end
+ end
+ end
+
+ # Finds the building ID for the current location services object
+ def get_building : Zone
+ zones = staff_api.zones(tags: "building").get.as_a
+ zone_ids = zones.map(&.[]("id").as_s)
+ building_id = (zone_ids & system.zones).first
+
+ building = zones.find! { |zone| zone["id"].as_s == building_id }
+ Zone.from_json building.to_json
+ rescue error
+ msg = "unable to determine building zone"
+ logger.warn(exception: error) { msg }
+ raise msg
+ end
+end
diff --git a/drivers/place/llm/workplace_spec.cr b/drivers/place/llm/workplace_spec.cr
new file mode 100644
index 00000000000..4e62708aeca
--- /dev/null
+++ b/drivers/place/llm/workplace_spec.cr
@@ -0,0 +1,8 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Workplace" do
+end
+
+# :nodoc:
+class StaffMock < DriverSpecs::MockDriver
+end
diff --git a/drivers/place/location_services.cr b/drivers/place/location_services.cr
new file mode 100644
index 00000000000..c21f58e5f7e
--- /dev/null
+++ b/drivers/place/location_services.cr
@@ -0,0 +1,368 @@
+require "set"
+require "json"
+require "placeos-driver"
+require "placeos-driver/interface/locatable"
+require "placeos-driver/interface/sensor"
+
+class Place::LocationServices < PlaceOS::Driver
+ descriptive_name "PlaceOS Location Services"
+ generic_name :LocationServices
+ description %(collects location data from compatible services and combines the data)
+
+ accessor staff_api : StaffAPI_1
+
+ default_settings({
+ debug_webhook: false,
+ search_building: false,
+
+ # various groups of people one might be interested in contacting
+ _emergency_contacts: {
+ "Fire Wardens" => "5542c9f-eaa7-4e74",
+ "First Aid" => "ed9f7608-488f-aeef",
+ },
+ })
+
+ @debug_webhook : Bool = false
+ @emergency_contacts : Hash(String, String) = {} of String => String
+ @search_building : Bool = true
+ @include_room_locations : Bool = false
+
+ getter building_id : String { get_building_id.not_nil! }
+ getter systems : Hash(String, Array(String)) { get_systems_list.not_nil! }
+
+ def on_update
+ @debug_webhook = setting?(Bool, :debug_webhook) || false
+ @emergency_contacts = setting?(Hash(String, String), :emergency_contacts) || Hash(String, String).new
+ @search_building = setting?(Bool, :search_building) || false
+ @include_room_locations = setting?(Bool, :include_room_locations) || false
+ @building_id = nil
+ @systems = nil
+
+ schedule.clear
+
+ # Keep mappings up to date
+ if @search_building || @include_room_locations
+ schedule.every(1.hour) { @systems = get_systems_list.not_nil! if @systems }
+ end
+
+ if !@emergency_contacts.empty?
+ schedule.every(6.hours, immediate: true) { update_contacts_list }
+ end
+ end
+
+ # Finds the building ID for the current location services object
+ def get_building_id
+ building_setting = setting?(String, :building_zone_override)
+ return building_setting if building_setting.presence
+ zone_ids = staff_api.zones(tags: "building").get.as_a.map(&.[]("id").as_s)
+ (zone_ids & system.zones).first
+ rescue error
+ logger.warn(exception: error) { "unable to determine building zone id" }
+ nil
+ end
+
+ # Grabs the list of systems in the building
+ def get_systems_list
+ staff_api.systems_in_building(building_id).get.as_h.transform_values(&.as_a.map(&.as_s))
+ rescue error
+ logger.warn(exception: error) { "unable to obtain list of systems in the building" }
+ nil
+ end
+
+ # Runs through all the services that support the Locatable interface
+ # requests location information on the identifier for all of them
+ # concatenates the results and returns them as a single array
+ def locate_user(email : String? = nil, username : String? = nil)
+ raise ArgumentError.new("must provide either email or username") unless email.presence || username.presence
+
+ email = email.try &.downcase
+ logger.debug { "searching for #{email}, #{username}" }
+ located = [] of JSON::Any
+
+ # check if the user has opted out of being located
+ user = (staff_api.user(email || username).get rescue nil)
+ if user && !user.raw.nil?
+ return located if user["locatable"].as_bool == false
+ end
+
+ system.implementing(Interface::Locatable).locate_user(email, username).get.each do |locations|
+ located.concat locations.as_a
+ end
+
+ if @search_building
+ building = JSON::Any.new building_id
+ results = [] of Tuple(JSON::Any, PlaceOS::Driver::Proxy::Drivers::Responses)
+
+ # Map
+ systems.each do |level_id, system_ids|
+ level_id = JSON::Any.new level_id
+ system_ids.each do |system_id|
+ results << {level_id, system(system_id).implementing(Interface::Locatable).locate_user(email, username)}
+ end
+ end
+
+ # reduce
+ results.each do |(level_id, result)|
+ result.get.each do |locations|
+ located.concat(locations.as_a.tap &.each { |location|
+ location = location.as_h
+ location["level"] = level_id
+ location["building"] = building
+ })
+ end
+ end
+ end
+
+ located
+ end
+
+ # Will return an array of MAC address strings
+ # lowercase with no seperation characters abcdeffd1234 etc
+ def macs_assigned_to(email : String? = nil, username : String? = nil)
+ email = email.try &.downcase
+ logger.debug { "listing MAC addresses assigned to #{email}, #{username}" }
+ macs = [] of String
+ system.implementing(Interface::Locatable).macs_assigned_to(email, username).get.each do |found|
+ macs.concat found.as_a.map(&.as_s)
+ end
+
+ if @search_building
+ results = [] of PlaceOS::Driver::Proxy::Drivers::Responses
+
+ # Map
+ systems.each do |_level_id, system_ids|
+ system_ids.each do |system_id|
+ results << system(system_id).implementing(Interface::Locatable).macs_assigned_to(email, username)
+ end
+ end
+
+ # reduce
+ results.each &.get.each { |found| macs.concat found.as_a.map(&.as_s) }
+ end
+
+ macs
+ end
+
+ # Will return `nil` or `{"location": "wireless", "assigned_to": "bob123", "mac_address": "abcd"}`
+ def check_ownership_of(mac_address : String)
+ logger.debug { "searching for owner of #{mac_address}" }
+ owner = nil
+ system.implementing(Interface::Locatable).check_ownership_of(mac_address).get.each do |result|
+ if result != nil
+ owner = result
+ break
+ end
+ end
+
+ if owner.nil? && @search_building
+ results = [] of PlaceOS::Driver::Proxy::Drivers::Responses
+
+ # Map
+ systems.each do |_level_id, system_ids|
+ system_ids.each do |system_id|
+ results << system(system_id).implementing(Interface::Locatable).check_ownership_of(mac_address)
+ end
+ end
+
+ # reduce
+ results.each do |sys_results|
+ sys_results.get.each do |result|
+ if result != nil
+ owner = result
+ break
+ end
+ end
+ break unless owner.nil?
+ end
+ end
+
+ owner
+ end
+
+ # Will return an array of devices and their x, y coordinates
+ def device_locations(zone_id : String, location : String? = nil)
+ logger.debug { "searching devices in zone #{zone_id}" }
+ located = [] of JSON::Any
+ system.implementing(Interface::Locatable).device_locations(zone_id, location).get.each do |locations|
+ located.concat locations.as_a
+ end
+
+ if @include_room_locations
+ results = [] of PlaceOS::Driver::Proxy::Drivers::Responses
+
+ # Map
+ systems.each do |_level_id, system_ids|
+ system_ids.each do |system_id|
+ results << system(system_id).implementing(Interface::Locatable).device_locations(zone_id, location)
+ end
+ end
+
+ # reduce
+ results.each &.get.each { |locations| located.concat locations.as_a }
+ end
+
+ located
+ end
+
+ # ===============================
+ # Sensor data collection
+ # ===============================
+
+ # sensor search + filtered search
+ def sensors(type : String? = nil, mac : String? = nil, zone_id : String? = nil)
+ logger.debug { "searching sensors of type: #{type.inspect}, mac: #{mac.inspect}, zone_id: #{zone_id}" }
+ located = [] of JSON::Any
+
+ drivers = system.implementing(Interface::Sensor)
+ drivers.sensors(type, mac, zone_id).get.each do |locations|
+ located.concat locations.as_a
+ end
+
+ driver_ids = Set.new drivers.map(&.@module_id)
+
+ if @search_building
+ building = JSON::Any.new building_id
+ results = [] of Tuple(JSON::Any, PlaceOS::Driver::Proxy::Drivers::Responses)
+
+ # Map
+ systems.each do |level_id, system_ids|
+ next if zone_id && zone_id != level_id
+ level_id = JSON::Any.new level_id
+ system_ids.each do |system_id|
+ # ensure we don't query modules more than once
+ drivers = system(system_id).implementing(Interface::Sensor)
+ drivers = PlaceOS::Driver::Proxy::Drivers.new(drivers.reject { |driver| driver.@module_id.in?(driver_ids) })
+ driver_ids.concat drivers.map(&.@module_id)
+
+ results << {level_id, drivers.sensors(type, mac, zone_id)}
+ end
+ end
+
+ # reduce
+ results.each do |(level_id, result)|
+ result.get.each do |locations|
+ located.concat(locations.as_a.tap &.each { |location|
+ location = location.as_h
+ location["level"] = level_id
+ location["building"] = building
+ })
+ end
+ end
+ end
+
+ located
+ end
+
+ def sensor(mac : String, id : String? = nil)
+ logger.debug { "querying sensor with mac: #{mac}, id: #{id.inspect}" }
+ located = [] of JSON::Any
+ drivers = system.implementing(Interface::Sensor)
+ drivers.sensor(mac, id).get.each do |locations|
+ located.concat locations.as_a
+ end
+
+ return located.first unless located.empty?
+
+ driver_ids = Set.new drivers.map(&.@module_id)
+
+ if @search_building
+ building = JSON::Any.new building_id
+ results = [] of Tuple(JSON::Any, PlaceOS::Driver::Proxy::Drivers::Responses)
+
+ # Map
+ systems.each do |level_id, system_ids|
+ level_id = JSON::Any.new level_id
+ system_ids.each do |system_id|
+ # ensure we don't query modules more than once
+ drivers = system(system_id).implementing(Interface::Sensor)
+ drivers = PlaceOS::Driver::Proxy::Drivers.new(drivers.reject { |driver| driver.@module_id.in?(driver_ids) })
+ driver_ids.concat drivers.map(&.@module_id)
+
+ results << {level_id, drivers.sensor(mac, id)}
+ end
+ end
+
+ # reduce
+ results.each do |(level_id, result)|
+ result.get.each do |locations|
+ located.concat(locations.as_a.tap &.each { |location|
+ location = location.as_h
+ location["level"] = level_id
+ location["building"] = building
+ })
+ end
+ end
+ end
+
+ located.first unless located.empty?
+ end
+
+ # ===============================
+ # IP ADDRESS => MAC ADDRESS
+ # ===============================
+ SUCCESS_RESPONSE = {HTTP::Status::OK, {} of String => String, nil}
+
+ # Webhook handler for accepting IP address to username mappings
+ # This data is typically obtained via domain controller logs
+ def ip_mappings(method : String, headers : Hash(String, Array(String)), body : String)
+ logger.debug { "IP mappings webhook received: #{method},\nheaders #{headers},\nbody size #{body.size}" }
+ logger.debug { body } if @debug_webhook
+
+ # ip, username, domain, hostname
+ ip_map = Array(Tuple(String, String, String, String?)).from_json(body)
+ system.implementing(Interface::Locatable).ip_username_mappings(ip_map)
+
+ SUCCESS_RESPONSE
+ end
+
+ def mac_address_mappings(method : String, headers : Hash(String, Array(String)), body : String)
+ logger.debug { "MAC mappings webhook received: #{method},\nheaders #{headers},\nbody size #{body.size}" }
+ logger.debug { body } if @debug_webhook
+
+ # username, macs, domain
+ username, macs, domain = Tuple(String, Array(String), String?).from_json(body)
+ username = username.strip
+ macs = macs.compact_map do |mac|
+ mac = mac.strip.gsub(/(0x|[^0-9A-Fa-f])*/, "").downcase
+ mac if mac.size == 12
+ end
+ return {HTTP::Status::NOT_ACCEPTABLE, {} of String => String, nil} if username.empty? || macs.empty?
+
+ system.implementing(Interface::Locatable).mac_address_mappings(username, macs, domain)
+
+ SUCCESS_RESPONSE
+ end
+
+ @[Security(Level::Support)]
+ def update_contacts_list
+ if @emergency_contacts.empty?
+ self[:emergency_contacts] = nil
+ return
+ end
+
+ if !system.exists?(:Calendar)
+ logger.warn { "contacts requested however no directory service available" }
+ return
+ end
+
+ directory = system[:Calendar]
+ self[:emergency_contacts] = @emergency_contacts.transform_values { |id|
+ directory.get_members(id).get.as(JSON::Any)
+ }
+ end
+
+ # locates all the of the emergency contacts
+ def locate_contacts(list_name : String)
+ contacts = status(Hash(String, Array(NamedTuple(
+ email: String,
+ username: String))), :emergency_contacts)
+
+ list = contacts[list_name]
+ results = {} of String => Array(JSON::Any)
+ list.each do |person|
+ email = person[:email]
+ results[email] = locate_user(email, person[:username])
+ end
+ results
+ end
+end
diff --git a/drivers/place/location_services_spec.cr b/drivers/place/location_services_spec.cr
new file mode 100644
index 00000000000..cfb304cd37c
--- /dev/null
+++ b/drivers/place/location_services_spec.cr
@@ -0,0 +1,86 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/locatable"
+
+WIRELESS_LOC = {
+ "location" => "wireless",
+ "coordinates_from" => "bottom-left",
+ "x" => 16.764784482481577,
+ "y" => 25.435735950388988,
+ "lng" => 55.274935030154325,
+ "lat" => 25.201036346211698,
+ "variance" => 7.944837533996209,
+ "last_seen" => 1601526474,
+ "building" => "zone_1234",
+ "level" => "zone_1234",
+}
+
+DESK_LOC = {
+ "location" => "desk",
+ "at_location" => true,
+ "map_id" => "desk-4-1006",
+ "building" => "zone_1234",
+ "level" => "zone_1234",
+}
+
+DriverSpecs.mock_driver "Place::LocationServices" do
+ system({
+ Dashboard: {WirelessLocation},
+ DeskManagement: {DeskLocation},
+ })
+
+ exec(:locate_user, "Steve").get.should eq([WIRELESS_LOC, DESK_LOC])
+end
+
+# :nodoc:
+class WirelessLocation < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Locatable
+
+ def locate_user(email : String? = nil, username : String? = nil)
+ [WIRELESS_LOC]
+ end
+
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ [] of String
+ end
+
+ alias OwnershipMAC = NamedTuple(
+ location: String,
+ assigned_to: String,
+ mac_address: String,
+ )
+
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ nil
+ end
+
+ def device_locations(zone_id : String, location : String? = nil)
+ nil
+ end
+end
+
+# :nodoc:
+class DeskLocation < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Locatable
+
+ def locate_user(email : String? = nil, username : String? = nil)
+ [DESK_LOC]
+ end
+
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ [] of String
+ end
+
+ alias OwnershipMAC = NamedTuple(
+ location: String,
+ assigned_to: String,
+ mac_address: String,
+ )
+
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ nil
+ end
+
+ def device_locations(zone_id : String, location : String? = nil)
+ nil
+ end
+end
diff --git a/drivers/place/logic_example.cr b/drivers/place/logic_example.cr
new file mode 100644
index 00000000000..f8091791260
--- /dev/null
+++ b/drivers/place/logic_example.cr
@@ -0,0 +1,35 @@
+require "placeos-driver"
+
+# use for testing some basic functionality
+class Place::LogicExample < PlaceOS::Driver
+ descriptive_name "Example Logic"
+ generic_name :ExampleLogic
+
+ accessor main_lcd : Display_1
+
+ def on_update
+ logger.info { "woot! an update #{setting?(String, :name)}" }
+ end
+
+ def power_state?
+ main_lcd[:power]
+ end
+
+ def power(state : Bool)
+ system.all(:Display).power(state)
+ end
+
+ def webhook(method : String, headers : Hash(String, Array(String)), body : String)
+ logger.debug { "webhook executed" }
+ power(true)
+ {HTTP::Status::OK.to_i, {} of String => String, ""}
+ end
+
+ def display_count
+ system.count(:Display)
+ end
+
+ def not_implemented
+ raise "not implemented"
+ end
+end
diff --git a/drivers/place/logic_example_spec.cr b/drivers/place/logic_example_spec.cr
new file mode 100644
index 00000000000..9f55e1183db
--- /dev/null
+++ b/drivers/place/logic_example_spec.cr
@@ -0,0 +1,93 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/switchable"
+
+# :nodoc:
+class Display < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Powerable
+ include PlaceOS::Driver::Interface::Muteable
+
+ enum Inputs
+ HDMI
+ HDMI2
+ VGA
+ VGA2
+ Miracast
+ DVI
+ DisplayPort
+ HDBaseT
+ Composite
+ end
+
+ include PlaceOS::Driver::Interface::InputSelection(Inputs)
+
+ # Configure initial state in on_load
+ def on_load
+ self[:power] = false
+ self[:input] = Inputs::HDMI
+ end
+
+ # implement the abstract methods required by the interfaces
+ def power(state : Bool)
+ self[:power] = state
+ end
+
+ def switch_to(input : Inputs)
+ mute(false)
+ self[:input] = input
+ end
+
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ self[:mute] = state
+ self[:mute0] = state
+ end
+end
+
+# :nodoc:
+class Switcher < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::InputSelection(Int32)
+
+ def switch_to(input : Input)
+ self[:output] = input
+ end
+end
+
+DriverSpecs.mock_driver "Place::LogicExample" do
+ system({
+ Display: {Display, Display},
+ Switcher: {Switcher},
+ })
+
+ exec(:power_state?).get.should eq(false)
+
+ # Should allow updating of settings
+ settings({
+ name: "Steve",
+ })
+
+ # Updating emulated module state
+ system(:Display_1)[:power] = true
+ exec(:power_state?).get.should eq(true)
+
+ # Expecting a function call
+ exec(:power, false)
+ exec(:power_state?).get.should eq(false)
+ system(:Display_1)[:power].should eq(false)
+
+ # Expecting a function call to return a result
+ exec(:power, true).get.should eq(true)
+
+ exec(:display_count).get.should eq(2)
+
+ system({
+ Display: {Display},
+ Switcher: {Switcher},
+ })
+
+ exec(:display_count).get.should eq(1)
+end
diff --git a/drivers/place/meet.cr b/drivers/place/meet.cr
new file mode 100644
index 00000000000..25fd83ccee6
--- /dev/null
+++ b/drivers/place/meet.cr
@@ -0,0 +1,1522 @@
+require "placeos-driver"
+require "placeos-driver/interface/chat_functions"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/lighting"
+require "./meet/qsc_phone_dialing"
+require "./meet/help"
+require "./meet/tab"
+require "./router/core"
+
+class Place::Meet < PlaceOS::Driver
+ include Interface::ChatFunctions
+ include Interface::Muteable
+ include Interface::Powerable
+ include Router::Core
+
+ generic_name :System
+ descriptive_name "Meeting room logic"
+ description <<-DESC
+ Room level state and behaviours.
+
+ This driver provides a high-level API for interaction with devices, systems \
+ and integrations found within common workplace collaboration spaces
+ DESC
+
+ default_settings({
+ help: {
+ "help-id" => {
+ "title" => "Video Conferencing",
+ "content" => "markdown",
+ },
+ },
+ tabs: [
+ {
+ name: "VC",
+ icon: "conference",
+ inputs: ["VidConf_1"],
+ help: "help-id",
+ controls: "vidconf-controls",
+ merge_on_join: false,
+ },
+ ],
+
+ # if we want to display the selected tab on displays meant only for the presenter
+ preview_outputs: ["Display_2"],
+ vc_camera_in: "switch_camera_output_id",
+ join_lockout_secondary: true,
+ unjoin_on_shutdown: false,
+ mute_on_unlink: true,
+ auto_route_on_join: false,
+
+ # only required in joining rooms
+ local_outputs: ["Display_1"],
+ local_cameras: ["Camera_1"],
+
+ screens: {
+ "Projector_1" => "Screen_1",
+ },
+
+ # change to false if there is a joining flag
+ lighting_independent: true,
+ lighting_area: {
+ # see interface/lighting for options
+ id: 34,
+ join: 0x01,
+ },
+ lighting_scenes: [
+ {
+ name: "Full",
+ id: 1,
+ icon: "lightbulb",
+ opacity: 1.0,
+ },
+ {
+ name: "Medium",
+ id: 2,
+ icon: "lightbulb",
+ opacity: 0.5,
+ },
+ {
+ name: "Off",
+ id: 3,
+ icon: "lightbulb_outline",
+ opacity: 0.8,
+ },
+ ],
+ lighting_levels: [
+ {
+ name: "Spot light left",
+ area: {
+ id: 123,
+ },
+ },
+ ],
+ _channel_details: [
+ {
+ name: "Al Jazeera",
+ icon: "https://url-to-svg-or-png",
+ channel: "udp://239.192.10.170:5000?hwchan=0",
+ },
+ ],
+ })
+
+ class ChannelDetail
+ include JSON::Serializable
+
+ getter name : String
+ getter icon : String?
+ getter channel : String
+ end
+
+ # =========================
+ # The LLM Interface
+ # =========================
+
+ getter capabilities : String do
+ String.build do |str|
+ str << "provides meeting room audio visual control such as controlling video source to be presented\n"
+ str << "check for available inputs and outputs before switching to present a source to a display.\n"
+ str << "output volume and microphone fader controls are floats between 0.0 to 100.0\n"
+ str << "query output volume to change it by a relative amount, if asked to increase or decrease volume, change it by 10.0\n"
+ str << "audio can be muted and you unroute video to blank displays.\n"
+ str << "you can also shutdown, startup, power off, power on, start or end the meeting using the set_power_state function available in this capability.\n"
+ str << "some rooms may have lighting control, make sure to check what levels are available before changing state\n"
+ str << "some rooms may have accessories such as blinds or projector screen controls. Check for available accessories when asked about something not explicitly controllable\n"
+ end
+ end
+
+ EXT_INIT = [] of Symbol
+ EXT_POWER = [] of Symbol
+
+ # extensions:
+ include Place::QSCPhoneDialing
+
+ def on_load
+ system.load_complete do
+ init_previous_join_state
+ on_update
+ end
+ end
+
+ @tabs : Array(Tab) = [] of Tab
+ getter local_help : Help = Help.new
+ getter local_tabs : Array(Tab) = [] of Tab
+
+ @outputs : Array(String) = [] of String
+ getter linked_outputs = {} of String => Hash(String, String)
+ getter local_outputs : Array(String) = [] of String
+ getter local_cameras : Array(String) = [] of String
+
+ @preview_outputs : Array(String) = [] of String
+ getter local_preview_outputs : Array(String) = [] of String
+
+ @shutdown_devices : Array(String)? = nil
+ @local_vidconf : String = "VidConf_1"
+ @ignore_update : Int64 = 0_i64
+ @unjoin_on_shutdown : Bool? = nil
+ @mute_on_unlink : Bool = true
+ @auto_route_on_join : Bool = false
+
+ # core includes: 'current_routes' hash
+ # but we override it here for LLM integration
+ @[Description("obtain the current routes, output => input")]
+ getter current_routes : Hash(String, String?) = {} of String => String?
+
+ def on_update
+ return if (Time.utc.to_unix - @ignore_update) < 3
+
+ self[:name] = system.display_name.presence || system.name
+ self[:local_help] = @local_help = setting?(Help, :help) || Help.new
+ self[:local_tabs] = @local_tabs = setting?(Array(Tab), :tabs) || [] of Tab
+ self[:local_outputs] = @local_outputs = setting?(Array(String), :local_outputs) || [] of String
+ self[:local_cameras] = @local_cameras = setting?(Array(String), :local_cameras) || [] of String
+ self[:local_preview_outputs] = @local_preview_outputs = setting?(Array(String), :preview_outputs) || [] of String
+ self[:voice_control] = setting?(Bool, :voice_control) || false
+ self[:channel_details] = setting?(Array(ChannelDetail), :channel_details)
+ @shutdown_devices = setting?(Array(String), :shutdown_devices)
+ @local_vidconf = setting?(String, :local_vidconf) || "VidConf_1"
+ @unjoin_on_shutdown = setting?(Bool, :unjoin_on_shutdown)
+ @mute_on_unlink = setting?(Bool, :mute_on_unlink) || false
+ @auto_route_on_join = setting?(Bool, :auto_route_on_join) || false
+
+ @join_lock.synchronize do
+ subscriptions.clear
+
+ reset_remote_cache
+ init_signal_routing
+ init_projector_screens
+ init_master_audio
+ init_microphones
+ init_accessories
+ init_lighting
+ init_vidconf
+ init_joining
+ end
+
+ # initialize all the extentsions
+ {% for func in EXT_INIT %}
+ begin
+ {{func.id}}
+ rescue error
+ logger.warn(exception: error) { "error in init function: #{ {{func.id.stringify}} }" }
+ end
+ {% end %}
+ end
+
+ # link screen control to power state
+ protected def init_projector_screens
+ screens = setting?(Hash(String, String), :screens) || {} of String => String
+
+ subscribe(:active) do |_sub, active_state|
+ if active_state == "true"
+ sys = system
+ screens.each do |display, screen|
+ system[screen].down if sys[display][:power] == true
+ end
+ end
+ end
+
+ screens.each do |display, screen|
+ system.subscribe(display, :power) do |_sub, power_state|
+ logger.debug { "power-state changed on #{display}: #{power_state.inspect}" }
+ if power_state == "false"
+ logger.debug { "updating screen position: up" }
+ system[screen].up
+ elsif power_state == "true"
+ logger.debug { "updating screen position: down" }
+ system[screen].down
+ end
+ end
+ end
+ end
+
+ @[Description("power on or off the meeting room. Send true for power on (startup) or false for power off (shutdown)")]
+ def set_power_state(state : Bool)
+ power state
+ end
+
+ # Sets the overall room power state.
+ def power(state : Bool, unlink : Bool = false)
+ return if state == status?(Bool, :active)
+ logger.debug { "Powering #{state ? "up" : "down"}" }
+ self[:active] = state
+ unlink = @unjoin_on_shutdown.nil? ? unlink : !!@unjoin_on_shutdown
+
+ remotes_before = remote_rooms
+ sys = system
+
+ if state
+ @local_preview_outputs.each { |device| sys[device].power true } # Power on preview displays
+ apply_master_audio_default
+ apply_camera_defaults
+ apply_default_routes
+ apply_mic_defaults
+
+ if first_output = @tabs.first?.try &.inputs.first
+ selected_input first_output
+ end
+ else
+ unlink_systems if unlink
+ audio_mute(true) rescue nil
+
+ @local_outputs.each { |output| unroute(output) }
+ @local_preview_outputs.each { |output| unroute(output) }
+
+ mute_microphones
+
+ if devices = @shutdown_devices
+ devices.each { |device| sys[device].power false }
+ else
+ sys.implementing(Interface::Powerable).power false
+ end
+ sys[@local_vidconf].hangup if sys.exists?(@local_vidconf)
+ end
+
+ remotes_before.each { |room| room.power(state, unlink) }
+
+ # perform power state actions
+ {% for func in EXT_POWER %}
+ begin
+ {{func.id}}(state, unlink)
+ rescue error
+ logger.warn(exception: error) { "error in power state function: #{ {{func.id.stringify}} }" }
+ end
+ {% end %}
+
+ state
+ end
+
+ @[Description("query the system power state?")]
+ def power? : Bool
+ status?(Bool, :active) || false
+ end
+
+ # =====================
+ # System IO management
+ # ====================
+
+ @default_routes : Hash(String, String) = {} of String => String
+
+ protected def init_signal_routing
+ @default_routes = setting?(Hash(String, String), :default_routes) || {} of String => String
+
+ logger.debug { "loading signal graph..." }
+ load_siggraph
+ logger.debug { "signal graph loaded" }
+ update_available_tabs
+ update_available_help
+ update_available_outputs
+ rescue error
+ logger.warn(exception: error) { "failed to init signal graph" }
+ end
+
+ protected def on_siggraph_loaded(inputs, outputs)
+ outputs.each &.watch { |node| on_output_change node }
+ end
+
+ protected def on_output_change(output)
+ case output.source
+ when Router::SignalGraph::Mute, nil
+ # nothing to do here
+ else
+ output.proxy.power true
+ end
+ end
+
+ def apply_default_routes
+ @default_routes.each { |output, input| route_signal(input, output) }
+ rescue error
+ logger.warn(exception: error) { "error applying default routes" }
+ end
+
+ @[Description("available inputs and outputs. Route using id keys")]
+ def inputs_and_outputs
+ inps = all_inputs
+ outs = all_outputs
+
+ results = [] of NamedTuple(type: Symbol, name: String, id: String)
+ inps.each do |input|
+ name = status?(NamedTuple(name: String), "input/#{input}")
+ if name
+ results << {type: :input, name: name[:name], id: input}
+ end
+ end
+ outs.each do |output|
+ name = status?(NamedTuple(name: String), "output/#{output}")
+ if name
+ results << {type: :output, name: name[:name], id: output}
+ end
+ end
+ results
+ end
+
+ @[Description("route to present an input to an output / display. Don't guess, look up available input and output ids")]
+ def route_input(input_id : String, output_id : String)
+ # obtain input ID
+ keys = all_inputs
+ hash = keys.each_with_object({} of String => String) do |input, memo|
+ memo[input.downcase] = input
+ end
+ input_actual = hash[input_id.downcase]?
+ raise "invalid input #{input_id}, must be one of #{keys.join(", ")}" unless input_actual
+
+ # obtain output ID
+ keys = all_outputs
+ hash = keys.each_with_object({} of String => String) do |output, memo|
+ memo[output.downcase] = output
+ end
+ output_actual = hash[output_id.downcase]?
+ raise "invalid output #{output_id}, must be one of: #{keys.join(", ")}" unless output_actual
+
+ power true
+ selected_input(input_actual)
+ route(input_actual, output_actual)
+ end
+
+ def route(input : String, output : String, max_dist : Int32? = nil, simulate : Bool = false, follow_additional_routes : Bool = true, called_from_join : Bool = false)
+ route_signal(input, output, max_dist, simulate, follow_additional_routes)
+
+ if links = @linked_outputs[output]?
+ links.each { |_sys_id, remote_out| route_signal(input, remote_out, max_dist, simulate, follow_additional_routes) }
+ end
+
+ if !called_from_join
+ remote_systems.each do |remote_system|
+ room = remote_system.room_logic
+ sys_id = remote_system.system_id
+ if links = @linked_outputs[output]?
+ if remote_out = links[sys_id]?
+ room.route(input, remote_out, max_dist, simulate, follow_additional_routes, true)
+ end
+ end
+ end
+ end
+ end
+
+ @[Description("route an input for presentation to all displays. Don't guess, look up available input ids")]
+ def route_all(input_id : String)
+ # obtain input ID
+ keys = all_inputs
+ hash = keys.each_with_object({} of String => String) do |input, memo|
+ memo[input.downcase] = input
+ end
+ input_actual = hash[input_id.downcase]?
+ raise "invalid input #{input_id}, must be one of #{keys.join(", ")}" unless input_actual
+
+ power true
+ selected_input(input_actual)
+ @outputs.each do |output|
+ route(input_actual, output)
+ end
+ end
+
+ # we want to unroute any signal going to the display
+ # or if it's a direct connection, we want to mute the display.
+ @[Description("blank a display / output, sometimes called a video mute")]
+ def unroute(output : String)
+ route("MUTE", output)
+ rescue error
+ logger.debug(exception: error) { "failed to unroute #{output}" }
+ end
+
+ @[Description("blank all displays / outputs")]
+ def unroute_all
+ @outputs.each do |output|
+ route("MUTE", output)
+ end
+ end
+
+ # This is the currently selected input
+ # if the user selects an output then this will be routed to it
+ def selected_input(name : String, simulate : Bool = false) : Nil
+ selected_tab = @tabs.find(&.inputs.includes?(name)).try &.name
+ if selected_tab || !simulate
+ self[:selected_input] = name
+ self[:selected_tab] = selected_tab || @tabs.first
+
+ # ensure inputs are powered on (mostly to bring VC out of standby)
+ sys = system
+ if sys.exists? name
+ mod = sys[name]
+ mod.power(true) if mod.implements? Interface::Powerable
+ end
+ end
+
+ # Perform any desired routing
+ if !simulate
+ if @preview_outputs.empty?
+ route_signal(name, @outputs.first) if @outputs.size == 1
+ else
+ @preview_outputs.each { |output| route_signal(name, output) }
+ end
+
+ remote_rooms.each { |room| room.selected_input(name, true) }
+ end
+ end
+
+ protected def all_outputs
+ status(Array(String), :outputs)
+ end
+
+ protected def all_inputs
+ status(Array(String), :inputs)
+ end
+
+ protected def update_available_help
+ help = @local_help.dup
+
+ # merge in joined room help
+ remote_rooms.each do |room|
+ help.merge! Help.from_json(room.local_help.get.to_json)
+ end
+
+ self[:help] = help
+ end
+
+ protected def update_available_tabs
+ available_cameras = @local_cameras.dup
+ seen_cameras = @local_cameras.dup
+ tabs = @local_tabs.dup.map(&.clone)
+
+ # merge in joined room tabs
+ remote_rooms.each do |room|
+ remote_tabs = Array(Tab).from_json(room.local_tabs.get.to_json)
+ remote_tabs.each do |remote_tab|
+ next if remote_tab.merge_on_join == false
+
+ if local_tab = tabs.find { |loc_tab| loc_tab.name == remote_tab.name }
+ local_tab.merge!(remote_tab)
+ else
+ tabs << remote_tab
+ end
+ end
+
+ remote_cameras = room.local_cameras.get.as_a.map(&.as_s)
+ remote_cameras.each_with_index do |remote_cam, index|
+ next if seen_cameras.includes?(remote_cam)
+ available_cameras << remote_cam
+ seen_cameras << remote_cam
+ end
+ end
+
+ # local_inputs configured for backwards compatibility with older versions of the UI
+ self[:local_inputs] = self[:available_inputs] = tabs.flat_map(&.inputs)
+ self[:tabs] = @tabs = tabs
+
+ if available_cameras.empty? && @join_modes.empty?
+ if inputs_raw = setting?(::Place::Router::Core::Settings::IOMeta, "inputs")
+ available_cameras = inputs_raw.select! { |_key, values| values["type"]?.try(&.as_s?) == "cam" }.keys
+ end
+ end
+ self[:available_cameras] = available_cameras
+ end
+
+ protected def update_available_outputs
+ available_outputs = @local_outputs.dup
+ seen_outputs = @local_outputs.dup
+
+ preview_outputs = @local_preview_outputs.dup
+
+ new_linked_outputs = Hash(String, Hash(String, String)).new { |hash, key| hash[key] = {} of String => String }
+
+ # Grab the join mode if any
+ if join_mode = @join_modes[@join_selected]?
+ # merge in joined room settings
+ remote_systems.each do |remote_system|
+ room = remote_system.room_logic
+ remote_system_id = remote_system.system_id
+ preview_outputs.concat room.local_preview_outputs.get.as_a.map(&.as_s)
+
+ # merge in outputs from remote rooms
+ remote_outputs = room.local_outputs.get.as_a.map(&.as_s)
+ remote_outputs.each_with_index do |remote_out, index|
+ if join_mode.merge_outputs? && (local_out = available_outputs[index]?)
+ seen_outputs << remote_out
+ new_linked_outputs[local_out][remote_system_id] = remote_out
+ end
+
+ next if seen_outputs.includes?(remote_out)
+ available_outputs << remote_out
+ seen_outputs << remote_out
+ end
+ end
+ end
+
+ @linked_outputs = new_linked_outputs
+ self[:preview_outputs] = @preview_outputs = preview_outputs
+
+ if available_outputs.empty?
+ if preview_outputs.empty?
+ self[:available_outputs] = @outputs = all_outputs
+ else
+ self[:available_outputs] = @outputs = all_outputs - preview_outputs
+ end
+ else
+ self[:available_outputs] = @outputs = available_outputs
+ end
+ end
+
+ # =======================
+ # Primary volume controls
+ # =======================
+
+ class RoomMutes
+ include JSON::Serializable
+
+ getter name : String
+ getter binding : String
+ getter control : String | Array(String)? = nil
+ getter falsy_value : String | Bool = false
+
+ # maps ids to commands to send
+ getter route : Array(AccessoryComplex::Exec)? = nil
+ getter unroute : Array(AccessoryComplex::Exec)? = nil
+ end
+
+ class AudioFader
+ include JSON::Serializable
+
+ def initialize
+ end
+
+ getter name : String? = nil
+ property level_id : String | Array(String)? = nil
+ getter mute_id : String | Array(String)? { level_id }
+
+ getter default_muted : Bool? = nil
+ getter default_level : Float64? = nil
+
+ getter level_index : Int32? = nil
+ getter mute_index : Int32? = nil
+
+ getter min_level : Float64 { 0.0 }
+ getter max_level : Float64 { 100.0 }
+
+ property level_feedback : String do
+ id = level_id
+ "fader#{id.is_a?(Array) ? id.first : id}"
+ end
+ property mute_feedback : String do
+ id = mute_id || level_id
+ "fader#{id.is_a?(Array) ? id.first : id}_mute"
+ end
+ property module_id : String { "Mixer_1" }
+
+ getter? level_feedback, mute_feedback
+
+ getter rooms : Array(RoomMutes)? = nil
+
+ def use_defaults?
+ @module_id.nil? && (level_id.nil? || level_id.try &.empty?) && (mute_id.nil? || mute_id.try &.empty?)
+ end
+
+ def implements_volume?
+ level_id == "\e"
+ end
+ end
+
+ @master_audio : AudioFader? = nil
+
+ protected def init_master_audio
+ audio = setting?(AudioFader, :master_audio)
+ output = @outputs.first?
+ unless audio || output
+ logger.warn { "no audio configuration found" }
+ self[:has_master_audio] = false
+ @master_audio = nil
+ return
+ end
+ self[:has_master_audio] = true
+ audio ||= AudioFader.new
+
+ # if nothing defined then we want to use the first output
+ # we might have configured default levels
+ if audio.use_defaults?
+ unless output
+ logger.warn { "audio partially conigured, no output found" }
+ return
+ end
+
+ mod = signal_node(output).ref.mod.not_nil!
+
+ # proxy = (mod.sys == system.id ? system : system mod.sys).get mod.name, mod.idx
+ audio.module_id = "#{mod.name}_#{mod.idx}"
+ audio.level_feedback = "volume" unless audio.level_feedback?
+ audio.mute_feedback = "audio_mute" unless audio.mute_feedback?
+ audio.level_id = "\e"
+ end
+
+ # we can subscribe to feedback before we're sure all the modules are running
+ system.subscribe(audio.module_id, audio.level_feedback) do |_sub, level|
+ raw_level = Float64.from_json(level) if level && level != "null"
+ if raw_level
+ range = audio.min_level..audio.max_level
+ vol_percent = ((raw_level.to_f - range.begin.to_f) / (range.end - range.begin)) * 100.0
+ self[:volume] = vol_percent
+ end
+ end
+
+ system.subscribe(audio.module_id, audio.mute_feedback) do |_sub, muted|
+ self[:mute] = muted == "true" if muted && muted != "null"
+ end
+
+ @master_audio = audio
+ rescue error
+ logger.warn(exception: error) { "failed to init master audio" }
+ end
+
+ protected def apply_master_audio_default
+ audio = @master_audio
+ return unless audio
+ mixer = system[audio.module_id]
+
+ case audio.default_muted
+ in Bool
+ set_master_mute(mixer, audio, audio.default_muted)
+ in Nil
+ mixer.query_mutes(audio.level_id) unless audio.implements_volume?
+ end
+
+ case audio.default_level
+ in Float64
+ set_master_volume(mixer, audio, audio.default_level)
+ in Nil
+ mixer.query_faders(audio.level_id) unless audio.implements_volume?
+ end
+ end
+
+ protected def set_master_volume(mixer, audio, level)
+ if level_index = audio.level_index
+ mixer.fader(audio.level_id, level, level_index)
+ elsif audio.implements_volume?
+ mixer.volume(level)
+ else
+ mixer.fader(audio.level_id, level)
+ end
+ end
+
+ protected def set_master_mute(mixer, audio, state)
+ if mute_index = audio.mute_index
+ mixer.mute(audio.level_id, state, mute_index)
+ elsif audio.implements_volume?
+ mixer.mute_audio(state)
+ else
+ mixer.mute(audio.mute_id, state)
+ end
+ end
+
+ @[Description("change the room volume")]
+ def set_volume(level : Int32 | Float64)
+ power true
+ if level.zero?
+ audio_mute true
+ "audio was muted"
+ else
+ audio_mute false
+ volume level, ""
+ "volume set to #{level.to_f.clamp(0.0, 100.0)}"
+ end
+ end
+
+ @[Description("query the current volume, useful to know when asked to change the volume relatively")]
+ def volume?
+ status?(Float64, :volume) || 0.0
+ end
+
+ @[Description("mute or unmute the room audio")]
+ def audio_mute(state : Bool)
+ mute state
+ state ? "audio is muted" : "audio is unmuted"
+ end
+
+ @[Description("check if the room audio is muted")]
+ def audio_muted?
+ status?(Bool, :mute) || false
+ end
+
+ # Set the volume of a signal node within the system.
+ def volume(level : Int32 | Float64, input_or_output : String, push_to_remotes : Bool = true)
+ audio = @master_audio
+ if audio
+ logger.debug { "setting master volume to #{level}" }
+ else
+ logger.debug { "no master output configured" }
+ return
+ end
+
+ level = level.to_f.clamp(0.0, 100.0)
+ percentage = level / 100.0
+ range = audio.min_level..audio.max_level
+
+ # adjust into range
+ level_actual = percentage * (range.end - range.begin)
+ level_actual = (level_actual + range.begin.to_f).round(1)
+
+ mixer = system[audio.module_id]
+ set_master_volume(mixer, audio, level_actual)
+
+ # We are not using a join mode, so we need to set the lighting scene in joined rooms
+ if push_to_remotes
+ remote_rooms.each { |room| room.volume(level, input_or_output, false) }
+ end
+
+ level
+ end
+
+ # Sets the mute state on a signal node within the system.
+ def mute(state : Bool = true, index : Int32 | String = 0, layer : MuteLayer = MuteLayer::AudioVideo)
+ input_or_output = index
+ audio = @master_audio
+ if audio
+ logger.debug { "setting master mute to #{state}" }
+ else
+ logger.debug { "no master output configured" }
+ return
+ end
+
+ mixer = system[audio.module_id]
+ set_master_mute(mixer, audio, state)
+ end
+
+ # =================
+ # Lighting Controls
+ # =================
+
+ alias LightingArea = Interface::Lighting::Area
+ alias LightingScene = NamedTuple(name: String, id: UInt32, icon: String, opacity: Float64)
+ record LightingLevel, name : String, area : LightingArea, binding : String? = nil do
+ include JSON::Serializable
+ end
+
+ DEFAULT_LIGHT_MOD = "Lighting_1"
+
+ getter local_lighting_area : LightingArea? = nil
+ getter lighting_independent : Bool = false
+ @light_area : LightingArea? = nil
+ @light_scenes : Hash(String, UInt32) = {} of String => UInt32
+ @light_module : String = DEFAULT_LIGHT_MOD
+ getter local_light_levels : Array(LightingLevel)? = nil
+
+ @light_subscription : PlaceOS::Driver::Subscriptions::Subscription? = nil
+ @light_levels_query : PlaceOS::Driver::Proxy::Scheduler::TaskWrapper? = nil
+
+ protected def init_lighting
+ # deal with `false`
+ lights_independent = setting?(Bool, :lighting_independent)
+ @lighting_independent = lights_independent.nil? ? true : lights_independent
+ @light_area = @local_lighting_area = setting?(LightingArea, :lighting_area)
+ light_scenes = setting?(Array(LightingScene), :lighting_scenes)
+ @local_light_levels = setting?(Array(LightingLevel), :lighting_levels)
+ @light_module = setting?(String, :lighting_module) || DEFAULT_LIGHT_MOD
+
+ local_scenes = {} of String => UInt32
+
+ light_scenes.try(&.each { |scene| local_scenes[scene[:name].downcase] = scene[:id] })
+ @light_scenes = local_scenes
+ self[:lighting_scenes] = light_scenes
+
+ # query current light levels if we have faders
+ @light_levels_query.try(&.cancel) rescue nil
+ @light_levels_query = nil
+ if local_levels = @local_light_levels
+ @light_levels_query = schedule.in(10.seconds + rand(2000).milliseconds) do
+ @light_levels_query = nil
+ lighting = system[@light_module]
+ local_levels.each do |level|
+ lighting.lighting_level?(level.area)
+ end
+ end
+ end
+
+ @light_subscription = nil
+ update_available_lighting
+ end
+
+ protected def update_available_lighting
+ if sub = @light_subscription
+ subscriptions.unsubscribe sub
+ @light_subscription = nil
+ end
+
+ return if @light_scenes.empty?
+
+ # Check current join state
+ if light_area = @local_lighting_area
+ unless lighting_independent
+ # merge in joined room mics
+ remote_rooms.each do |room|
+ begin
+ remote_area = LightingArea.from_json(room.local_lighting_area.get.to_json)
+ light_area = light_area.join_with(remote_area)
+ rescue error
+ logger.warn(exception: error) { "ignoring lighting config in room #{room.name} (#{room.id})" }
+ end
+ end
+ end
+
+ # perform lighting linking if it's available
+ @light_area = light_area
+ lighting = system[@light_module]
+ if lighting.implements? "link_area"
+ if remote_rooms.empty?
+ lighting.unlink_area light_area.id
+ else
+ lighting.link_area light_area.id, light_area.join
+ end
+ end
+ end
+
+ @light_subscription = system.subscribe(@light_module, @light_area.to_s) do |_sub, scene|
+ self[:lighting_scene] = scene.to_i if scene && scene != "null"
+ end
+
+ # merge all the faders onto the joined touch panels
+ levels = @local_light_levels.try(&.dup) || [] of LightingLevel
+ remote_systems.each do |remote|
+ if remote_levels = Array(LightingLevel)?.from_json(remote.room_logic.local_light_levels.get.to_json)
+ levels.concat(remote_levels)
+ end
+ end
+ levels.map! { |level| LightingLevel.new(level.name, level.area, level.area.to_s) }
+ self[:lighting_levels] = levels.empty? ? nil : levels
+ end
+
+ def select_lighting_scene(scene : String, push_to_remotes : Bool = true)
+ scene_id = @light_scenes[scene.downcase]?
+ raise ArgumentError.new("invalid scene '#{scene}', valid scenes are: #{@light_scenes.keys.join(", ")}") unless scene_id
+
+ system[@light_module].set_lighting_scene(scene_id, @light_area)
+
+ # We are not using a join mode, so we need to set the lighting scene in joined rooms
+ if push_to_remotes && lighting_independent
+ remote_rooms.each { |room| room.select_lighting_scene(scene, false) }
+ end
+ end
+
+ @[Description("returns the list of available lighting scenes")]
+ def lighting_scenes
+ scenes = status?(Array(NamedTuple(name: String)), :lighting_scenes)
+ raise "no lighting control available" unless scenes
+ scenes.map { |scene| scene[:name].downcase }
+ end
+
+ @[Description("query the current lighting scene")]
+ def lighting_scene?
+ scenes = status?(Array(NamedTuple(name: String, id: Int32)), :lighting_scenes)
+ raise "no lighting control available" unless scenes
+ current = status?(Int32, :lighting_scene)
+ scene = scenes.find { |available| available[:id] == current }
+ scene ? "current lighting scene: #{scene[:name]}" : "lights in unknown state"
+ end
+
+ @[Description("set a new lighting scene. Remember to list available lighting scenes before calling")]
+ def set_lighting_scene(scene : String)
+ scenes = lighting_scenes
+ raise "invalid scene #{scene}, must be one of: #{scenes.join(", ")}" unless scenes.includes?(scene.downcase)
+ select_lighting_scene scene
+ "current lighting scene: #{scene}"
+ end
+
+ # ================
+ # Room Accessories
+ # ================
+
+ struct AccessoryBasic
+ include JSON::Serializable
+
+ struct Control
+ include JSON::Serializable
+
+ getter name : String
+ getter icon : String
+ getter function_name : String
+ getter arguments : Array(JSON::Any) = [] of JSON::Any
+ end
+
+ getter name : String
+ getter module : String
+ getter controls : Array(Control)
+
+ @[JSON::Field(ignore: true)]
+ property remote : String? = nil
+ end
+
+ struct AccessoryComplex
+ include JSON::Serializable
+
+ struct Exec
+ include JSON::Serializable
+
+ getter module : String { "System_1" }
+ getter function_name : String
+ getter arguments : Array(JSON::Any) = [] of JSON::Any
+
+ # used with mic room selection controls, do we want to augment the arguments
+ # with a toggle value? i.e. true / false value
+ getter augment : Bool? = nil
+ end
+
+ struct Control
+ include JSON::Serializable
+
+ getter name : String
+ getter icon : String
+ getter exec : Array(Exec)
+ end
+
+ getter name : String
+ getter controls : Array(Control)
+
+ @[JSON::Field(ignore: true)]
+ property remote : String? = nil
+ end
+
+ alias Accessory = AccessoryBasic | AccessoryComplex
+
+ getter local_accessories : Array(Accessory) = [] of Accessory
+ getter available_accessories : Array(Accessory) = [] of Accessory
+
+ protected def init_accessories
+ @local_accessories = setting?(Array(Accessory), :room_accessories) || [] of Accessory
+ update_available_accessories
+ end
+
+ protected def update_available_accessories
+ accessories = @local_accessories.dup
+ remote_systems.each do |remote|
+ remote_accessories = Array(Accessory).from_json(remote.room_logic.local_accessories.get.to_json)
+ accessories.concat(remote_accessories.map! { |acc|
+ acc.remote = remote.system_id
+ acc
+ })
+ end
+ self[:room_accessories] = @available_accessories = accessories
+ end
+
+ def accessory_exec(accessory : String, control : String) : Bool
+ accessory_inst = @available_accessories.find { |access| access.name == accessory }
+ return false unless accessory_inst
+
+ control_inst = accessory_inst.controls.find { |ctrl| ctrl.name == control }
+ return false unless control_inst
+
+ # execute accessories on the system they came from
+ # some are merged in if a room is joined
+ if system_id = accessory_inst.remote
+ system(system_id).get("System", 1).accessory_exec(accessory, control)
+ return true
+ end
+
+ case control_inst
+ in AccessoryBasic::Control
+ mod_name = accessory_inst.as(AccessoryBasic).module
+ system[mod_name].__send__(control_inst.function_name, control_inst.arguments)
+ in AccessoryComplex::Control
+ control_inst.exec.each do |exec|
+ system[exec.module].__send__(exec.function_name, exec.arguments)
+ end
+ end
+
+ true
+ end
+
+ # ===================
+ # Microphone Controls
+ # ===================
+
+ alias Microphone = AudioFader
+
+ getter local_mics : Array(Microphone) = [] of Microphone
+ @available_mics : Array(Microphone) = [] of Microphone
+
+ protected def init_microphones
+ @local_mics = setting?(Array(Microphone), :local_microphones) || [] of Microphone
+ update_available_mics
+ rescue error
+ logger.warn(exception: error) { "failed to init microphones" }
+ end
+
+ protected def update_available_mics
+ local = @local_mics.dup
+
+ # merge in joined room mics
+ remote_rooms.each do |room|
+ local.concat Array(Microphone).from_json(room.local_mics.get.to_json)
+ end
+
+ # expose the details to the UI
+ @available_mics = local
+ self[:microphones] = @available_mics.map do |mic|
+ level_id = mic.level_id
+ mute_id = mic.mute_id
+ level_array = level_id.is_a?(Array) ? level_id : [level_id]
+ mute_array = mute_id.is_a?(Array) ? mute_id : [mute_id]
+
+ {
+ name: mic.name,
+ level_id: level_array.compact,
+ mute_id: mute_array.compact,
+ level_index: mic.level_index,
+ mute_index: mic.mute_index,
+ level_feedback: mic.level_feedback,
+ mute_feedback: mic.mute_feedback,
+ module_id: mic.module_id,
+ min_level: mic.min_level,
+ max_level: mic.max_level,
+ rooms: mic.rooms,
+ }
+ end
+ end
+
+ protected def apply_mic_defaults
+ @local_mics.each do |mic|
+ mixer = system[mic.module_id]
+
+ case mic.default_muted
+ in Bool
+ if mute_index = mic.mute_index
+ mixer.mute(mic.mute_id, mic.default_muted, mute_index)
+ else
+ mixer.mute(mic.mute_id, mic.default_muted)
+ end
+ in Nil
+ mixer.query_mutes(mic.level_id)
+ end
+
+ case mic.default_level
+ in Float64
+ if level_index = mic.level_index
+ mixer.fader(mic.level_id, mic.default_level, level_index)
+ else
+ mixer.fader(mic.level_id, mic.default_level)
+ end
+ in Nil
+ mixer.query_faders(mic.level_id)
+ end
+ end
+ end
+
+ # level is a percentage 0.0->100.0
+ def set_microphone(level : Float64, mute : Bool = false)
+ @local_mics.each do |mic|
+ mixer = system[mic.module_id]
+
+ if level_index = mic.level_index
+ mixer.fader(mic.level_id, level, level_index)
+ else
+ mixer.fader(mic.level_id, level)
+ end
+
+ if mute_index = mic.mute_index
+ mixer.mute(mic.mute_id, mute, mute_index)
+ else
+ mixer.mute(mic.mute_id, mute)
+ end
+ end
+ end
+
+ def mute_microphones(mute : Bool = true) : Nil
+ @local_mics.each do |mic|
+ begin
+ mixer = system[mic.module_id]
+
+ if mute_index = mic.mute_index
+ mixer.mute(mic.mute_id, mute, mute_index)
+ else
+ mixer.mute(mic.mute_id, mute)
+ end
+ rescue error
+ logger.warn(exception: error) { "failed to mute microphone: #{mic}" }
+ end
+ end
+ end
+
+ # set_string: zone_id, index
+ # 22 for false
+ def mic_room_selection(mic_name : String, room_name : String, selected : Bool)
+ mic = @available_mics.find { |match| match.name == mic_name }
+ raise "no matching mic name: #{mic_name}" unless mic
+
+ rooms = mic.rooms
+ raise "no rooms for mic: #{mic_name}" unless rooms
+
+ room = rooms.find { |match| match.name == room_name }
+ raise "no matching room name for: #{room_name}" unless room
+
+ execs = selected ? room.route : room.unroute
+ if execs
+ execs.each do |action|
+ if action.augment
+ args = action.arguments.dup
+ args << JSON::Any.new(selected)
+ system[action.@module || mic.module_id].__send__(action.function_name, args)
+ else
+ system[action.@module || mic.module_id].__send__(action.function_name, action.arguments)
+ end
+ end
+ else
+ mixer = system[mic.module_id]
+ ctrl = room.control
+ case ctrl
+ in Nil
+ mixer.mute(room.binding, !selected)
+ in String, Array(String)
+ mixer.mute(ctrl, !selected)
+ end
+ end
+ end
+
+ # ====================
+ # VC Camera Management
+ # ====================
+
+ class CamDetails
+ include JSON::Serializable
+
+ getter mod : String
+ getter index : String | Int32? # if multiple cams on the one device (VidConf mod for instance)
+ getter vc_camera_input : String | Int32?
+ end
+
+ @vc_camera_in : String | Array(String)? = nil
+ protected getter vc_camera_module : String { "Camera" }
+
+ def init_vidconf
+ @vc_camera_in = setting?(String | Array(String), :vc_camera_in)
+ @vc_camera_module = setting?(String, :vc_camera_module)
+ end
+
+ # run on system power on
+ def apply_camera_defaults
+ system.all(vc_camera_module).power true
+ end
+
+ # This is the camera input that is currently selected so we can switch between
+ # different cameras
+ def selected_camera(camera : String)
+ self[:selected_camera] = camera
+
+ cam = camera_details(camera)
+ system[cam.mod].power(true)
+
+ # route the camera
+ case camera_in = @vc_camera_in
+ in String
+ route_signal(camera, camera_in)
+ in Array(String)
+ camera_in.each { |cin| route_signal(camera, cin) }
+ in Nil
+ end
+
+ # switch to the correct VC input
+ if camera_vc_in = cam.vc_camera_input
+ system[@local_vidconf].camera_select(camera_vc_in)
+ end
+ end
+
+ def add_preset(preset : String, camera : String)
+ cam = camera_details(camera)
+ system[cam.mod].save_position preset, cam.index || 0
+ end
+
+ def remove_preset(preset : String, camera : String)
+ cam = camera_details(camera)
+ system[cam.mod].remove_position preset, cam.index || 0
+ end
+
+ protected def camera_details(camera : String)
+ status CamDetails, "input/#{camera}"
+ end
+
+ # =========================
+ # Room Joining Coordination
+ # =========================
+ enum JoinType
+ # only rooms part of the join need to be notified
+ Independent
+
+ # even rooms not part of the join, need to be notified
+ FullyAware
+ end
+
+ class JoinAction
+ include JSON::Serializable
+
+ getter module_id : String
+ getter function_name : String
+ getter arguments : Array(JSON::Any) { [] of JSON::Any }
+ getter named_args : Hash(String, JSON::Any) { {} of String => JSON::Any }
+ getter? master_only : Bool { true }
+ end
+
+ class JoinDetail
+ include JSON::Serializable
+
+ getter id : String
+ getter name : String
+ getter room_ids : Array(String)
+ getter join_actions : Array(JoinAction) { [] of JoinAction }
+ getter breakdown : Array(JoinAction) { [] of JoinAction }
+
+ # Do we want to merge the outputs (all outputs on all screens)
+ # or do we want them as seperate displays
+ getter? merge_outputs : Bool = true
+
+ @[JSON::Field(ignore: true)]
+ getter? linked : Bool { !room_ids.empty? }
+ end
+
+ class JoinSetting
+ include JSON::Serializable
+
+ getter type : JoinType { JoinType::Independent }
+ getter lock_remote : Bool { false }
+ getter modes : Array(JoinDetail)
+
+ @[JSON::Field(ignore: true)]
+ getter all_rooms : Set(String) do
+ modes.reduce(Set(String).new) { |rooms, mode| rooms.concat(mode.room_ids) }
+ end
+ end
+
+ @join_lock : Mutex = Mutex.new(:reentrant)
+ @join_selected : String? = nil
+ @join_confirmed : Bool = false
+ @join_settings : JoinSetting? = nil
+ @join_modes : Hash(String, JoinDetail) = {} of String => JoinDetail
+
+ # this is called on_load, before settings are loaded to setup any previous state
+ protected def init_previous_join_state
+ init_joining
+ master = setting?(Bool, :join_master)
+ self[:join_master] = @join_master = master.nil? ? true : master
+ self[:joined] = @join_selected = setting?(String, :join_selected)
+ self[:join_confirmed] = @join_confirmed = true
+
+ if @join_modes[@join_selected]?.nil?
+ self[:join_master] = @join_master = true
+ self[:joined] = @join_selected = nil
+ self[:join_confirmed] = @join_confirmed = true
+ end
+ end
+
+ protected def init_joining
+ @join_settings = join_settings = setting?(JoinSetting, :join_modes)
+ join_lookup = {} of String => JoinDetail
+ join_settings.try &.modes.each { |mode| join_lookup[mode.id] = mode }
+ self[:join_modes] = @join_modes = join_lookup
+
+ self[:join_lockout_secondary] = setting?(Bool, :join_lockout_secondary) || false
+ self[:join_hide_button] = setting?(Bool, :join_hide_button) || false
+ end
+
+ protected def perform_breakdown_actions(old_mode)
+ old_mode.breakdown.each do |action|
+ # dynamic function invocation
+ system[action.module_id].__send__(action.function_name, action.arguments, action.named_args)
+ end
+ rescue error
+ logger.error(exception: error) { "error performing join breakdown actions" }
+ end
+
+ def join_mode(mode_id : String, master : Bool = true)
+ mode = @join_modes[mode_id]
+ old_mode = @join_modes[@join_selected]? if @join_selected
+ join_settings = @join_settings.not_nil!
+ this_room = config.control_system.not_nil!.id
+
+ begin
+ @join_lock.synchronize do
+ # check this room is included in the join
+ if master
+ notify_rooms = join_settings.type.fully_aware? ? join_settings.all_rooms : mode.room_ids
+ if mode.linked?
+ raise "unable to perform join from this system" unless notify_rooms.includes?(this_room)
+ end
+
+ @join_selected = mode.id
+ @join_master = true
+
+ if old_mode && old_mode.linked?
+ # Perform any breakdown actions
+ perform_breakdown_actions(old_mode)
+
+ # unlink independent rooms
+ # find the rooms not incuded in this join and unlink them
+ if join_settings.type.independent?
+ unlink(old_mode.room_ids - mode.room_ids)
+ end
+ end
+
+ # unlink fully aware systems (empty array for independent rooms, unlinked above)
+ return unlink(notify_rooms) if !mode.linked?
+
+ reset_remote_cache
+ self[:join_confirmed] = @join_confirmed = false
+
+ notify_rooms.each do |room_id|
+ next if room_id == this_room
+ system(room_id).get("System", 1).join_mode(mode_id, master: false).get
+ end
+ persist_join_state
+
+ self[:join_master] = master
+ self[:joined] = @join_selected
+ self[:join_confirmed] = @join_confirmed = true
+ else
+ @join_selected = mode.id
+ @join_master = false
+ reset_remote_cache
+
+ persist_join_state
+
+ self[:join_master] = master
+ self[:joined] = mode.id
+ self[:join_confirmed] = @join_confirmed = true
+ end
+ end
+ ensure
+ update_available_ui
+
+ # ensure the system is powered on
+ power(true) if mode.linked? && !power?
+
+ # perform the custom actions
+ mode.join_actions.each do |action|
+ if master || !action.master_only?
+ # dynamic function invocation
+ system[action.module_id].__send__(action.function_name, action.arguments, action.named_args)
+ end
+ end
+
+ # recall the first lighting preset
+ if !@light_scenes.empty? && master
+ select_lighting_scene(@light_scenes.keys.first)
+ end
+
+ # send the current input to the remote rooms
+ if @auto_route_on_join && master
+ begin
+ if selected_inp = status?(String, :selected_input)
+ @outputs.each do |outp|
+ route(selected_inp, outp)
+ end
+ else
+ unroute_all
+ end
+ rescue error
+ logger.error(exception: error) { "error applying routes during join" }
+ end
+ end
+ end
+ end
+
+ def unlink_systems
+ if unlink_mode = @join_modes.find { |_id, mode| !mode.linked? }
+ join_mode(unlink_mode[0])
+ else
+ currrent_selected = @join_selected
+ if currrent_selected && (current_mode = @join_modes[currrent_selected]?)
+ perform_breakdown_actions(current_mode)
+ unlink(current_mode.room_ids)
+ end
+ unlink_internal_use
+ end
+ rescue error
+ logger.warn(exception: error) { "unlink failed" }
+ end
+
+ def unlink_internal_use
+ @join_lock.synchronize do
+ @join_selected = nil unless @join_modes[@join_selected]?.try(&.room_ids.empty?)
+ @join_master = true
+ self[:join_confirmed] = @join_confirmed = false
+ self[:join_master] = true
+ self[:joined] = @join_selected
+ reset_remote_cache
+
+ persist_join_state
+ update_available_ui
+
+ self[:join_confirmed] = @join_confirmed = true
+ end
+
+ # only mute on unlink if we're not powering off
+ if @mute_on_unlink && status?(Bool, :active)
+ @local_outputs.each { |output| unroute(output) }
+ @local_preview_outputs.each { |output| unroute(output) }
+ end
+ rescue error
+ logger.error(exception: error) { "ui state failed to be applied unjoining room" }
+ end
+
+ protected def persist_join_state
+ @ignore_update = Time.utc.to_unix
+ define_setting(:join_master, @join_master)
+ define_setting(:join_selected, @join_selected)
+ rescue error
+ logger.error(exception: error) { "failed to persist join state" }
+ end
+
+ protected def update_available_ui
+ update_available_help
+ # VC tab to not be merged
+ update_available_tabs
+ update_available_outputs
+ update_available_mics
+ update_available_lighting
+ update_available_accessories
+ rescue error
+ logger.error(exception: error) { "ui state failed to be applied in room join" }
+ end
+
+ protected def unlink(rooms : Enumerable(String))
+ this_room = config.control_system.not_nil!.id
+ rooms.each do |room|
+ if room == this_room
+ unlink_internal_use
+ next
+ end
+ system(room).get("System", 1).unlink_internal_use
+ end
+ end
+
+ struct RemoteSystem
+ getter system_id : String
+ getter room_logic : PlaceOS::Driver::Proxy::Driver
+
+ def initialize(@system_id : String, @room_logic : PlaceOS::Driver::Proxy::Driver)
+ end
+ end
+
+ protected getter remote_systems : Array(RemoteSystem) do
+ if selected = @join_selected
+ if mode = @join_modes[selected]
+ this_room = config.control_system.not_nil!.id
+ if mode.room_ids.includes? this_room
+ mode.room_ids.compact_map do |room|
+ next if room == this_room
+ RemoteSystem.new(room, system(room).get("System", 1))
+ end
+ else
+ [] of RemoteSystem
+ end
+ else
+ [] of RemoteSystem
+ end
+ else
+ [] of RemoteSystem
+ end
+ end
+
+ # cache the proxies for performance reasons
+ protected getter remote_rooms : Array(PlaceOS::Driver::Proxy::Driver) do
+ remote_systems.map(&.room_logic)
+ end
+
+ protected def reset_remote_cache
+ @remote_systems = nil
+ @remote_rooms = nil
+ end
+end
diff --git a/drivers/place/meet/help.cr b/drivers/place/meet/help.cr
new file mode 100644
index 00000000000..24c1f812f51
--- /dev/null
+++ b/drivers/place/meet/help.cr
@@ -0,0 +1,14 @@
+require "json"
+
+module Place
+ struct HelpPage
+ include JSON::Serializable
+ include JSON::Serializable::Unmapped
+
+ getter icon : String?
+ getter title : String
+ getter content : String
+ end
+
+ alias Help = Hash(String, HelpPage)
+end
diff --git a/drivers/place/meet/qsc_phone_dialing.cr b/drivers/place/meet/qsc_phone_dialing.cr
new file mode 100644
index 00000000000..386b0deb9aa
--- /dev/null
+++ b/drivers/place/meet/qsc_phone_dialing.cr
@@ -0,0 +1,78 @@
+# Code for handling QSC phone dialing, if available
+module Place::QSCPhoneDialing
+ # This data will be stored in the tab
+ class QscPhone
+ include JSON::Serializable
+
+ getter number_id : String
+ getter dial_id : String
+ getter hangup_id : String
+ getter status_id : String
+ getter ringing_id : String
+ getter offhook_id : String
+ getter dtmf_id : String
+ end
+
+ macro included
+ {% EXT_INIT << :qsc_phone_dialing_init %}
+ {% EXT_POWER << :qsc_phone_dialing_power %}
+ end
+
+ @qsc_dial_settings : QscPhone? = nil
+ @dial_string : String = ""
+
+ protected def qsc_phone_dialing_init
+ @qsc_dial_settings = setting?(QscPhone, :qsc_phone)
+ self[:qsc_dial_number] = @dial_string
+ self[:qsc_dial_bindings] = @qsc_dial_settings
+ end
+
+ protected def qsc_phone_dialing_power(state : Bool, unlink : Bool)
+ if state
+ qsc_dial_pad_clear
+ else
+ qsc_dial_hangup
+ qsc_dial_pad_clear
+ end
+ end
+
+ protected def qsc_dial_pad_sync : Nil
+ dial_settings = @qsc_dial_settings
+ return unless dial_settings
+ system[:Mixer].set_string(dial_settings.number_id, @dial_string)
+ self[:qsc_dial_number] = @dial_string
+ end
+
+ def qsc_dial_pad(number : String)
+ return unless number.size > 0
+ char = number[0]
+
+ case char
+ when '\b'
+ @dial_string = @dial_string[0..-2] unless @dial_string.size == 0
+ when '0', '1', '2', '3', '4', '5', '6', '7', '8', '9', '*', '#'
+ @dial_string = "#{@dial_string}#{char}"
+ else
+ logger.info { "unsupported dial char provided #{char}" }
+ end
+
+ qsc_dial_pad_sync
+ end
+
+ def qsc_dial_pad_clear : Nil
+ @dial_string = ""
+ qsc_dial_pad_sync
+ end
+
+ def qsc_dial_makecall
+ dial_settings = @qsc_dial_settings
+ return unless dial_settings
+ system[:Mixer].trigger(dial_settings.dial_id)
+ end
+
+ def qsc_dial_hangup
+ dial_settings = @qsc_dial_settings
+ return unless dial_settings
+ system[:Mixer].trigger(dial_settings.hangup_id)
+ end
+end
diff --git a/drivers/place/meet/sensor_shutdown.cr b/drivers/place/meet/sensor_shutdown.cr
new file mode 100644
index 00000000000..f85752aebd6
--- /dev/null
+++ b/drivers/place/meet/sensor_shutdown.cr
@@ -0,0 +1,147 @@
+require "placeos-driver"
+
+class Place::SensorShutdown < PlaceOS::Driver
+ descriptive_name "PlaceOS Idle Shutdown"
+ generic_name :IdleShutdown
+ description "works in conjunction with the Bookings driver to decide when a room should shutdown"
+
+ accessor bookings : Bookings_1
+ accessor av_control : System_1
+
+ default_settings({
+ timeout_ad_hoc: 15,
+ timeout_booked: 30,
+ })
+
+ @sensor_stale : Bool = false
+
+ getter? event_in_progress : Bool = false
+ getter? people_present : Bool = false
+ getter? sensor_stale : Bool = false
+ getter? room_powered_on : Bool = false
+
+ getter? timer_active : Bool = false
+ @timer_time : Time::Span? = nil
+ @timer_started : Time::Span = 0.seconds
+ @shutdown_count : Int64 = 0_i64
+
+ @timeout_ad_hoc : Time::Span = 15.minutes
+ @timeout_booked : Time::Span = 30.minutes
+ @state_change_mutex : Mutex = Mutex.new(:reentrant)
+
+ def on_update
+ timeout_ad_hoc = setting?(UInt32, :timeout_ad_hoc) || 15_u32.minutes
+ timeout_booked = setting?(UInt32, :timeout_booked) || 30_u32.minutes
+
+ subscriptions.clear
+ bookings.subscribe(:status) { |_sub, status| update_status(status != "\"free\"") }
+ bookings.subscribe(:sensor_stale) { |_sub, sensor_stale| update_stale_state(sensor_stale == "true") }
+ bookings.subscribe(:presence) { |_sub, presence| update_presence(presence == "true") }
+ av_control.subscribe(:active) { |_sub, active| update_room_power_state(active == "true") }
+ end
+
+ protected def update_status(busy : Bool)
+ return if event_in_progress? == busy
+
+ logger.debug { "> event in progress: #{busy}" }
+ self[:event_in_progress] = @event_in_progress = busy
+ @state_change_mutex.synchronize { apply_state_changes }
+ end
+
+ protected def update_presence(state : Bool)
+ return if people_present? == state
+
+ logger.debug { "> people present: #{state}" }
+ self[:people_present] = @people_present = state
+ @state_change_mutex.synchronize { apply_state_changes }
+ end
+
+ protected def update_stale_state(stale : Bool)
+ return if sensor_stale? == stale
+
+ logger.debug { "> sensor state change: #{stale}" }
+ @sensor_stale = stale
+ @state_change_mutex.synchronize { apply_state_changes }
+ end
+
+ protected def update_room_power_state(powered : Bool)
+ return if room_powered_on? == powered
+
+ logger.debug { "> power state change: #{powered}" }
+ @room_powered_on = powered
+ @state_change_mutex.synchronize { apply_state_changes }
+ end
+
+ protected def clear_timer(update_status : Bool = true)
+ @state_change_mutex.synchronize do
+ @timer_active = false
+ @timer_time = nil
+ schedule.clear
+
+ if update_status
+ self[:timer_active] = false
+ self[:timer_started] = nil
+ end
+ end
+ end
+
+ protected def apply_state_changes
+ if sensor_stale?
+ clear_timer
+ logger.warn { "possible sensor failure, ignoring state" }
+ return
+ end
+
+ if !room_powered_on?
+ clear_timer
+ logger.debug { "room powered off, clearing schedule" }
+ return
+ end
+
+ if people_present?
+ clear_timer
+ logger.debug { "people detected, clearing schedule" }
+ return
+ end
+
+ timeout = if event_in_progress?
+ @timeout_booked
+ else
+ @timeout_ad_hoc
+ end
+
+ if timer_active?
+ if @timer_time == timeout
+ logger.debug { "timer already active, ignoring event" }
+ return
+ else
+ elapsed = Time.monotonic - @timer_started
+ remaining = timeout - elapsed
+
+ if remaining.positive?
+ timeout = remaining
+ else
+ logger.info { "new timeout period and already idle for that amount of time" }
+ return perform_shutdown
+ end
+ end
+ end
+
+ clear_timer(update_status: false)
+ schedule.in(timeout) { perform_shutdown }
+ self[:timer_active] = @timer_active = true
+ self[:timer_started] = Time.utc.to_unix
+ @timer_time = timeout
+ @timer_started = Time.monotonic
+ logger.debug { "timer started, shutdown in #{timeout}" }
+ end
+
+ protected def perform_shutdown
+ clear_timer
+ av_control.power false
+ @shutdown_count += 1_i64
+ self[:last_idle_shutdown] = Time.utc.to_unix
+ self[:idle_shutdowns] = @shutdown_count
+ logger.info { "System ilde timeout, shutdown requested" }
+ end
+end
diff --git a/drivers/place/meet/sensor_shutdown_spec.cr b/drivers/place/meet/sensor_shutdown_spec.cr
new file mode 100644
index 00000000000..4ff71b9a160
--- /dev/null
+++ b/drivers/place/meet/sensor_shutdown_spec.cr
@@ -0,0 +1,40 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::SensorShutdown" do
+ system({
+ Bookings: {BookingsMock},
+ System: {SystemMock},
+ })
+
+ sleep 1
+
+ status[:timer_active].should eq(true)
+ system(:Bookings_1).as(BookingsMock).sensor_stale
+
+ sleep 1
+ status[:timer_active].should eq(false)
+end
+
+# :nodoc:
+class BookingsMock < DriverSpecs::MockDriver
+ def on_load
+ self[:status] = "free"
+ self[:sensor_stale] = false
+ self[:presence] = false
+ end
+
+ def sensor_stale
+ self[:sensor_stale] = true
+ end
+end
+
+# :nodoc:
+class SystemMock < DriverSpecs::MockDriver
+ def on_load
+ self[:active] = true
+ end
+
+ def power(state : Bool)
+ self[:active] = state
+ end
+end
diff --git a/drivers/place/meet/tab.cr b/drivers/place/meet/tab.cr
new file mode 100644
index 00000000000..45a542cd5e8
--- /dev/null
+++ b/drivers/place/meet/tab.cr
@@ -0,0 +1,38 @@
+require "json"
+
+class Place::Tab
+ include JSON::Serializable
+ include JSON::Serializable::Unmapped
+
+ def initialize(@icon, @name, @inputs, @help = nil, @controls = nil, @merge_on_join = nil, @presentation_source = nil, @json_unmapped = Hash(String, JSON::Any).new)
+ end
+
+ getter icon : String
+ getter name : String
+ getter inputs : Array(String)
+
+ getter help : String?
+
+ # such as: vidconf-controls
+ getter controls : String?
+ getter merge_on_join : Bool?
+
+ # For the VC controls
+ getter presentation_source : String?
+
+ def clone : Tab
+ Tab.new(@icon, @name, inputs.dup, @help, @controls, @merge_on_join, @presentation_source, @json_unmapped.dup)
+ end
+
+ def merge(tab : Tab) : Tab
+ input = inputs.dup.concat(tab.inputs).uniq!
+ new_unmapped = tab.json_unmapped.merge json_unmapped
+ Tab.new(@icon, @name, input, @help, @controls, @merge_on_join, @presentation_source, new_unmapped)
+ end
+
+ def merge!(tab : Tab) : Tab
+ @json_unmapped.merge! tab.json_unmapped
+ @inputs.concat(tab.inputs).uniq!
+ self
+ end
+end
diff --git a/drivers/place/meet_readme.md b/drivers/place/meet_readme.md
new file mode 100644
index 00000000000..fb2ad973125
--- /dev/null
+++ b/drivers/place/meet_readme.md
@@ -0,0 +1,620 @@
+# Meet Readme
+
+Docs on how to configure a tabbed control UI
+
+* available icons for controls are: https://fonts.google.com/icons?selected=Material+Icons
+
+## Routing
+
+The router is designed to graph signal paths in a system between devices.
+https://docs.google.com/document/d/1DG2s9jjMVhiW65YGPDkUnOYYpFDeW42SkGvHyp1BEjQ/
+
+* devices can be represented by modules `Display_1`
+* virutal devices can be representated by a `*`: `*Laptop_HDMI`
+
+Connections are then defined by a flat map of Output => Inputs
+There are two styles of switching supported:
+
+* `switch_to`: an output that multiple inputs
+* `switch`: multiple outputs and multiple inputs
+
+NOTE:: when an input is presented to an output via `route("Input_id", "Output_id")`
+if the input and output support the `Powerable` interface, they will be powered on
+
+### Examples
+
+A basic single display system
+
+```yaml
+
+# A switch_to style of output where the inputs are virtual devices
+# virtual devices as no modules in the system represent the inputs
+connections:
+ Display_1:
+ hdmi: '*HDMI_Cable'
+ hdmi2: '*Wireless_Presenter'
+
+```
+
+A switcher and multiple displays
+
+* Switcher outputs are represented by `.` i.e. `Switcher_1.2` (output 2)
+* Switcher inputs can be represented by `:` i.e. `Switcher_1:2` (input 2)
+ * Switcher inputs in this format are only required if chaining multiple switchers
+
+```yaml
+
+# A typical single switcher setup
+connections:
+ # Display 1 is connected to Switcher 1 ouput 1
+ Display_1:
+ hdmi: Switcher_1.1
+ Display_2:
+ hdmi: Switcher_1.2
+
+ # We have a virtual output connected to output 5
+ '*AUX_Output': Switcher_1.5
+
+ # The switcher inputs are hooked up using a hash
+ Switcher_1:
+ '1': '*Wireless_Presenter' # always on, wireless presenter
+ '2': IPTV_1 # set top box or streaming input that can be powered on
+ '5': '*Desk_HDMI_1' # i.e. laptop inputs on a table in the room
+ '6': '*Desk_HDMI_2'
+
+```
+
+If you have a situation where audio and video need to be switched separately then you can also define layers on the switcher outputs.
+
+```yaml
+
+# A weird audio setup
+connections:
+ # Front of house audio split from the camera video input (real world example!)
+ Display_1:
+ hdmi: Switcher_1.12
+ '*VC_Camera_1': Switcher_1.1!video
+ '*FOH_Audio': Switcher_1.1!audio
+
+ # The switcher inputs are hooked up using a hash
+ Switcher_1:
+ '1': '*Wireless_Presenter' # always on, wireless presenter
+ '2': IPTV_1 # set top box or streaming input that can be powered on
+ '5': '*Desk_HDMI_1' # i.e. laptop inputs on a table in the room
+ '6': '*Desk_HDMI_2'
+
+# as we also want the audio to follow anything being presented to the display
+# you can ensure the sources follow one another
+outputs:
+ Display_1:
+ name: Projector
+ followers: ["FOH_Audio"]
+
+```
+
+### Default routes
+
+these are applied at system startup
+
+```yaml
+
+# output id => input id (as defined in the router)
+default_routes:
+ VC_Camera_1: Camera_1
+ VC_Camera_2: Camera_2
+
+```
+
+## Naming Inputs and Outputs
+
+Inputs and outputs are all referenced from their IDs which are either:
+
+* DeviceMod_1
+* Virtual_Device
+
+However you can apply metadata to these inputs and outputs, such as name for display on the user interface. This configuration is split between the inputs and outputs.
+
+```yaml
+
+# Input meta data
+inputs:
+ Desk_HDMI_1:
+ name: Table Box HDMI Cable
+ icon: input
+ Wireless_Presenter:
+ name: Wireless
+ icon: connected_tv
+
+ # Inputs of type cam are collected for camera control
+ # index is optional (only where a single module controls multiple cameras)
+ Camera_1:
+ name: Camera 1
+ icon: video_camera_front
+ type: cam
+ mod: Camera_1
+ index: 1 # only use this index on VC systems, single mod, mutliple cameras
+
+ # Inputs that have `presentable: false` are ignored as possible inputs for VC presenations
+ VidConf_1:
+ name: Video Conference
+ icon: video_camera_front
+ presentable: false
+
+```
+
+Output config is typically less interesting
+
+```yaml
+
+outputs:
+ Display_1:
+ name: Display Left
+ Display_2:
+ name: Display Right
+
+ # this display is hidden on the UI when the room is joined, preventing its use
+ Display_3:
+ name: Middle of room
+ hide_on_join: true
+
+```
+
+## Laying out Tabs
+
+Spaces can have more inputs and outputs defined then you want to display on the panel. Some things are auto switched etc so you need define you tab layouts.
+
+```yaml
+
+# a single tab UI with the optional help link
+tabs:
+ - name: Laptop
+ icon: computer
+ help: laptop-help
+
+ # Multiple inputs can be on a single tab
+ inputs:
+ - HDMI_Cable
+ - Wireless_Presenter
+
+```
+
+### Cisco Video Conferencing
+
+Configuring a tab with Cisco VC controls
+
+```yaml
+
+tabs:
+ - name: Conference
+ icon: video_camera_front
+ # The controls we want to see on the tab
+ controls: vidconf-controls
+ # this defines the switch output representing the presentation input on the VC
+ presentation_source: Virtual_VC_Presentation_Output
+ inputs:
+ - VidConf_1
+
+```
+
+configuring camera switching where cameras are connected via a switcher (single input on the VC unit)
+
+```yaml
+
+connections:
+ # outputs:
+ '*VC_Camera_Input': Switcher_1.1!video
+ '*Recorder_Camera_Input': Switcher_1.2!video
+ Switcher_1: # inputs:
+ '35': Camera_1
+ '36': Camera_2
+
+# specify which input on the VC unit the inputs are connected
+inputs:
+ Camera_1:
+ name: Camera 1
+ icon: video_camera_front
+ type: cam
+ mod: Camera_1
+ presentable: false # don't appear as VC content
+ Camera_2:
+ name: Karijini I Camera 2
+ icon: video_camera_front
+ type: cam # this indicated we want to have this camera manually controllable
+ mod: Camera_2
+ presentable: false # don't appear as VC content
+
+# When camera 1 or 2 is selected, we'll switch it to this output
+vc_camera_in: VC_Camera_Input
+
+# If the camera needs to be switched to multiple sources (i.e. a recording device and a VC system)
+vc_camera_in:
+ - VC_Camera_Input
+ - Recorder_Camera_Input
+
+# where there are joining rooms you must define which cameras are local to the system
+local_cameras:
+ - Camera_1
+ - Camera_2
+```
+
+configuring camera switching where cameras are connected via a switcher but also multiple cameras are connected to the VC at once
+
+```yaml
+
+# Configure the camera inputs and outputs on the switcher
+connections:
+ # outputs:
+ '*VC_Camera_1': Switcher_1.1!video
+ '*VC_Camera_2': Switcher_1.2!video
+ Switcher_1: # inputs:
+ '35': Camera_1
+ '36': Camera_2
+
+# auto switch these these to the VC on startup
+default_routes:
+ VC_Camera_1: Camera_1
+ VC_Camera_2: Camera_2
+
+# specify which input on the VC unit the inputs are connected
+inputs:
+ Camera_1:
+ name: Camera 1
+ icon: video_camera_front
+ type: cam
+ mod: Camera_1
+ presentable: false
+ vc_camera_input: 1 # This is input on the VC codec we want to select
+ Camera_2:
+ name: Karijini I Camera 2
+ icon: video_camera_front
+ type: cam # this indicated we want to have this camera manually controllable
+ mod: Camera_2
+ presentable: false # don't appear as VC content
+ vc_camera_input: 2
+
+```
+
+### IPTV Control
+
+Configuring IPTV controls for a page
+
+```yaml
+
+tabs:
+ - name: TV
+ icon: live_tv
+
+ # the controls we want to show (expects IPTV_1 mod to expose channel details)
+ controls: tv-channels
+ mod: IPTV_1
+ inputs:
+ - IPTV_1
+
+```
+
+example channel detail config (see [Exterity M93xx](https://github.com/PlaceOS/drivers/blob/master/drivers/exterity/avedia_player/m93xx.cr#L15) for an example driver)
+
+```yaml
+channel_details:
+ - name: Al Jazeera
+ channel: 'udp://239.192.10.170:5000?hwchan=0'
+ icon: 'https://os.place.tech/placeos.com/16335767803641925864.svg'
+```
+
+## Help pages
+
+This is custom HTML content that is embedded on the UI.
+The help key (`laptop-help` in the example below) is used to link the help to a tab
+
+* Help pages are inlined onto tabs when there are no controls defined.
+* Where there are controls defined a button is placed on the tab that links to the help pop-up
+
+```yaml
+
+help:
+ laptop-help:
+ title: Swytch
+ icon: computer
+ content: >
+ Follow the instructions below on how to connect your laptop in a meeting
+ room:
+
+ 1. Plug the ‘Y’ shaped connector into the USB-C port on your laptop.
+
+ 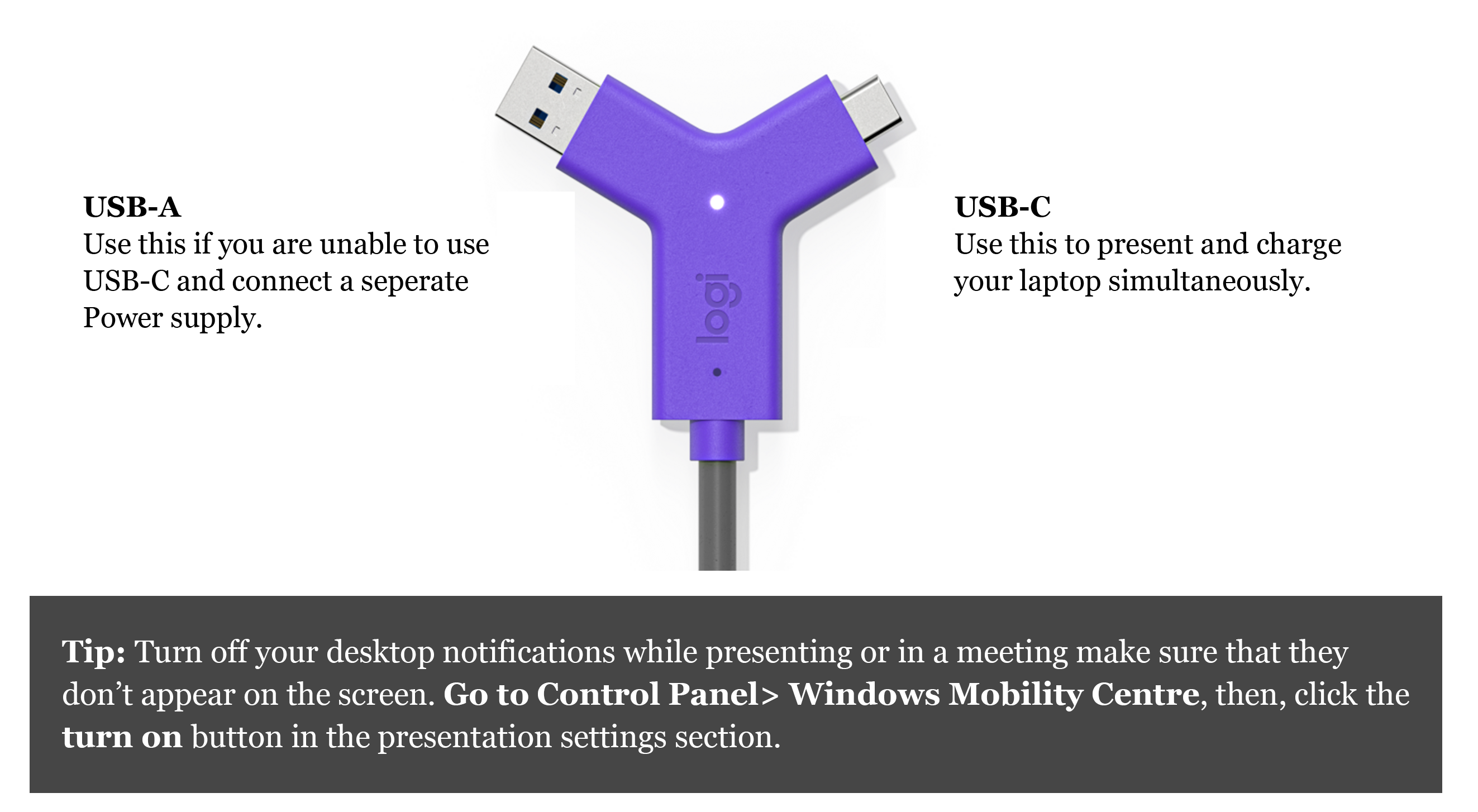 +
+
+```
+
+You can drag and drop images and videos into backoffice so they are available for embedding.
+
+## Defining Outputs to display
+
+You need to define which ouputs will be displayed on the panel.
+
+* when there is a single output, it'll automatically be switched
+* where there are two outputs, the user must manually switch by selecting the output
+
+```yaml
+
+# named local outputs as when joining rooms we'll merge these with joined rooms
+local_outputs:
+ - Display_1
+ - Display_2
+
+```
+
+Where you have Preview Monitor(s) for previewing sources before presenting them, you configure them using:
+
+```yaml
+
+# these will show the currently selected input
+preview_outputs:
+ - Display_3
+
+```
+
+NOTE:: there is a setting `mute_on_unlink: true` that can be set to ensure outputs are muted when rooms are unlinked - ensuring routes are reset
+
+## Front of House Audio
+
+By default the first display in the output list is assumed to be managing audio
+However you may want to configure defaults or use Mixer controls instead of the output device
+
+```yaml
+
+# This is a mixer configuration
+master_audio:
+ name: FOH Speakers
+ level_id: ["FOH-1234", "FOH-1235"]
+ mute_id: 'FOH-123-45-mute'
+
+ level_index: 4,
+ mute_index: 4,
+ level_feedback: 'faderFOH-1234'
+ mute_feedback: 'faderFOH-1234_mute'
+ module_id: 'Mixer_2'
+
+ default_muted: false
+ default_level: 60
+
+ min_level: 40
+ max_level: 90
+
+```
+
+You can just customise defaults if you want to continue using the default output
+
+```yaml
+
+master_audio:
+ default_muted: false
+ default_level: 60
+
+```
+
+## Projector Screen Linking
+
+Linking a projector screen to a displays power state
+
+```yaml
+
+screens:
+ Karijini_IV_Projector_1: Screen_1
+
+```
+
+## QSC Phone Dialing controls
+
+The places a dialing phone icon at the top of the screen that can be used to dial a phone number. Does not effect other aspects of the UI / Switching.
+
+```yaml
+
+phone_settings:
+ module: "Mixer_1",
+ number_id: "Status/Control16-17-VoIPCallControlDialString",
+ dial_id: "Status/Control16-17-VoIPCallControlConnect",
+ hangup_id: "Status/Control16-17-VoIPCallControlDisconnect",
+ status_id: "Status/Control16-17-VoIPCallStatusProgress",
+ ringing_id: "Status/Control16-17-VoIPCallStatusRinging(state)",
+ offhook_id: "Status/Control16-17-VoIPCallStatusOffHook",
+ dtmf_id: "16.17:dtmftx1"
+
+```
+
+Then in the QSC driver you want to define which controls QSC should poll and report changes:
+
+```yaml
+
+# keeps the phone status in sync
+change_groups: {
+ "room123_phone" => {
+ id: 1,
+ controls: ["VoIPCallStatusProgress", "VoIPCallStatusRinging", "VoIPCallStatusOffHook"],
+ },
+},
+
+```
+
+## Microphone configuration
+
+A basic list of fader and mute values that represent the microphones available
+
+```yaml
+
+local_microphones:
+ - name: Hand Held Microphone
+ level_id: ["HH-1234", "HH-1235"]
+ mute_id: 'HH-123-45-mute'
+
+ # optional keys
+ level_index: 4,
+ mute_index: 4,
+ level_feedback: 'faderHH-1234'
+ mute_feedback: 'faderHH-1234_mute'
+ module_id: 'Mixer_2'
+
+ default_muted: true
+ default_level: 55.8
+
+ min_level: 40
+ max_level: 90
+
+```
+
+Where a microphone might be shared between rooms or spill into a lobby, you can add a rooms configuration with mute ids that when unmuted will route the microphone audio to various spaces.
+
+```yaml
+
+local_microphones:
+ - name: Hand Held Microphone
+ # as above
+
+ rooms:
+ - name: "Room 1"
+ binding: "hh_room1_mute_id_mute"
+ control: "hh_room1_mute_id"
+ # this uses the `mute` function
+
+ - name: "Room 2"
+ binding: "hh_room2_mute_id_mute"
+ route:
+ - module_id: Mixer_1
+ function_name: trigger
+ arguments: ["hh_room2_add"]
+ unroute:
+ - module_id: Mixer_1
+ function_name: trigger
+ arguments: ["hh_room2_remove"]
+
+```
+
+## Joining Config
+
+Where systems can be merged you can define the various modes that are supported between the rooms.
+
+* there are two types `fully_aware` or `independent` (default)
+ * fully_aware: (typically something like 4 rooms where you can have independent, 1:3, 2:2 or all 4 etc)
+ * rooms that are not technically part of the join are aware of the join (1:3 combination for example)
+ * this might be because the DSP has a preset for each join combination (to combine microphones)
+ * independent: (typically something like 3 rooms that share a video switcher)
+ * only rooms part of the join are notified of the join
+ * this makes sense where audio and video come off an output of a shared switch
+ * so if room1 wants to present in room2 all it has to do is present to both outputs and keep audio levels in sync
+
+```yaml
+
+join_modes:
+ type: fully_aware
+ # input 1 in both rooms is merged (versus becoming a seperate input)
+ merge_outputs: true # default true
+ modes:
+ # id links mode across rooms.
+ # useful in fully linked where joining room_ids might differ between systems
+ - id: unlinked
+ name: Independent
+ room_ids: []
+ # join actions are optional
+ join_actions:
+ - module_id: Mixer_1
+ function_name: trigger
+ # supports named arguments too
+ arguments: ["UnjoinAll"]
+ - id: join-all
+ name: All Rooms
+ room_ids: ["sys-Cia-PnmTLC", "sys-Cia-ehhm8h", "sys-Cia-_e0jWQ"]
+ join_actions:
+ - module_id: Mixer_1
+ function_name: trigger
+ arguments: ["Join-all"]
+
+ # sometimes you may need to run an action to break a join (typically not required)
+ breakdown:
+ - module_id: Mixer_1
+ function_name: trigger
+ arguments: ["UnjoinAll"]
+
+```
+
+## Lighting Config
+
+There are two lighting modes:
+
+* independent rooms (even when linked, each room controls it's lighting area, we manually sync them)
+* joining rooms (a single request will change the scene in all linked rooms)
+
+```yaml
+
+# scenes are often the same across many rooms, so should be applied to a zone
+lighting_scenes:
+ - id: 1
+ name: "Full"
+ icon: lightbulb
+ opacity: 1.0
+ - id: 2
+ name: "Medium"
+ icon: lightbulb
+ opacity: 0.5
+ - id: 3
+ name: "Off"
+ icon: lightbulb_outline
+ opacity: 0.8
+
+# Each room typically will have its own area or grouping, so apply this at the system level
+lighting_area:
+ id: 23
+ # join: 0xFF (only if required by the driver)
+ # channel: 3 (only if required by the driver)
+ # component: "Lighting" (only if required by the driver)
+
+# Typically set to false if using the `join` field in `lighting_area`
+lighting_independent: true
+```
+
+## Additional Room Accessories
+
+These are things like blinds or air-conditioning that usually have limited controls and obsucre interfaces
+
+```yaml
+
+room_accessories:
+ - name: Shade blind
+ module: Blinds_1
+ controls:
+ - name: Up
+ icon: vertical_align_top
+ function_name: position
+ arguments: [1, "up"]
+ - name: Down
+ icon: vertical_align_bottom
+ function_name: position
+ arguments: [1, "down"]
+
+```
+
+If a control performs multiple actions you can use the `exec` block
+
+```yaml
+
+room_accessories:
+ - name: Projector Screen
+ controls:
+ - name: Up
+ icon: vertical_align_top
+ exec:
+ - module: Screen_1
+ function_name: position
+ arguments: [1, "up"]
+ - module: Projector_1
+ function_name: power
+ arguments: [false]
+ - name: Down
+ icon: vertical_align_bottom
+ exec:
+ - module: Screen_1
+ function_name: position
+ arguments: [1, "down"]
+
+```
diff --git a/drivers/place/meet_spec.cr b/drivers/place/meet_spec.cr
new file mode 100644
index 00000000000..e9a25e0a853
--- /dev/null
+++ b/drivers/place/meet_spec.cr
@@ -0,0 +1,98 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/switchable"
+
+# :nodoc:
+class DisplayMock < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Powerable
+ include PlaceOS::Driver::Interface::Muteable
+
+ enum MockInputs
+ HDMI
+ HDMI2
+ end
+
+ include PlaceOS::Driver::Interface::InputSelection(MockInputs)
+
+ # implement the abstract methods required by the interfaces
+ def power(state : Bool)
+ self[:power] = state
+ end
+
+ def switch_to(input : MockInputs)
+ mute(false)
+ self[:input] = input
+ end
+
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo,
+ )
+ self[:audio_mute] = state
+ end
+
+ def volume(level : Int32 | Float64)
+ self[:volume] = level
+ end
+end
+
+# :nodoc:
+class SwitcherMock < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Switchable(Int32, Int32)
+
+ def switch_to(input : Int32)
+ self[:input] = input
+ end
+
+ def switch(map : Hash(Input, Array(Output)), layer : SwitchLayer? = nil)
+ map.each do |(input, outputs)|
+ outputs.each do |output|
+ self["output#{output}"] = input
+ end
+ end
+ end
+end
+
+DriverSpecs.mock_driver "Place::Meet" do
+ system({
+ Display: {DisplayMock},
+ Switcher: {SwitcherMock},
+ })
+
+ settings({
+ connections: {
+ Display_1: {
+ hdmi: "Switcher_1.1",
+ },
+ Switcher_1: ["*Foo", "*Bar"],
+ },
+ local_outputs: ["Display_1"],
+ })
+
+ # Give the settings time to load
+ sleep 0.5
+
+ status["inputs"].as_a.should contain("Foo")
+ status["inputs"].as_a.should contain("Bar")
+ status["outputs"].as_a.should contain("Display_1")
+ status["output/Display_1"]["inputs"].should eq(["Foo", "Bar"])
+
+ exec(:power, true).get
+ status["active"]?.should eq true
+
+ exec(:route, "Foo", "Display_1").get
+ status["output/Display_1"]["source"].should eq(status["input/Foo"]["ref"])
+ system(:Display_1)["power"].should be_true
+
+ exec(:volume, 50, "Display_1").get
+ system(:Display_1)["volume"].should eq(50)
+ status["volume"]?.should eq(50)
+
+ exec(:mute, true, "Display_1").get
+ system(:Display_1)["audio_mute"].should be_true
+ status["mute"]?.should be_true
+
+ puts "Spec completed successfully"
+end
diff --git a/drivers/place/models/workplace_subscriptions.cr b/drivers/place/models/workplace_subscriptions.cr
new file mode 100644
index 00000000000..46874778f88
--- /dev/null
+++ b/drivers/place/models/workplace_subscriptions.cr
@@ -0,0 +1,201 @@
+require "placeos-driver"
+require "place_calendar"
+
+module Place::WorkplaceSubscription
+ enum NotifyType
+ # resource event changes
+ Created # a resource was created (MS only)
+ Updated # a resource was updated (in Google this could also mean created)
+ Deleted # a resource was deleted
+
+ # subscription lifecycle event (MS only)
+ Renew # subscription was deleted
+ Missed # MS sends this to mean resource event changes were not sent
+ Reauthorize # subscription needs reauthorization
+ end
+
+ struct NotifyEvent
+ include JSON::Serializable
+
+ getter event_type : NotifyType
+ getter resource_id : String?
+ getter resource_uri : String
+ getter subscription_id : String
+ getter client_secret : String
+
+ @[JSON::Field(converter: Time::EpochConverter)]
+ getter expiration_time : Time
+ end
+
+ abstract def subscription_on_crud(notification : NotifyEvent) : Nil
+ abstract def subscription_on_missed : Nil
+
+ enum ServiceName
+ Google
+ Office365
+ end
+
+ # should return the resource URI for monitoring, for example:
+ #
+ # case service_name
+ # in .google?
+ # resource = "/calendars/#{calendar_id}/events"
+ # in .office365?
+ # resource = "/users/#{calendar_id}/events"
+ abstract def subscription_resource(service_name : ServiceName) : String
+
+ @subscription : PlaceCalendar::Subscription? = nil
+ @push_notification_url : String? = nil
+ @push_authority : String? = nil
+ @push_service_name : ServiceName? = nil
+ @push_monitoring : PlaceOS::Driver::Subscriptions::ChannelSubscription? = nil
+ @push_mutex : Mutex = Mutex.new(:reentrant)
+
+ # the API reports that 6 days is the max:
+ # Subscription expiration can only be 10070 minutes in the future.
+ SUBSCRIPTION_LENGTH = 3.hours
+
+ protected def workplace_accessor
+ system["Calendar"]
+ end
+
+ protected def push_notificaitons_configure
+ @push_notification_url = setting?(String, :push_notification_url).presence
+ @push_authority = setting?(String, :push_authority).presence
+
+ # load any existing subscriptions
+ subscription = setting?(PlaceCalendar::Subscription, :push_subscription)
+
+ if @push_notification_url
+ # clear the monitoring if authority changed
+ if subscription && subscription.try(&.id) != @subscription.try(&.id) && (monitor = @push_monitoring)
+ subscriptions.unsubscribe(monitor)
+ @push_monitoring = nil
+ end
+ @subscription = subscription
+ schedule.every(5.minutes + rand(120).seconds) { push_notificaitons_maintain }
+ schedule.in(rand(30).seconds) { push_notificaitons_maintain(true) }
+ elsif subscription
+ push_notificaitons_cleanup(subscription)
+ end
+ end
+
+ # delete a subscription
+ protected def push_notificaitons_cleanup(sub)
+ @push_mutex.synchronize do
+ logger.debug { "removing subscription" }
+
+ workplace_accessor.delete_notifier(sub) if sub
+ @subscription = nil
+ define_setting(:push_subscription, nil)
+ end
+ end
+
+ getter sub_renewed_at : Time = 21.minutes.ago
+
+ # creates and maintains a subscription
+ protected def push_notificaitons_maintain(force_renew = false) : Nil
+ should_force = force_renew && @sub_renewed_at < 20.minutes.ago
+
+ @push_mutex.synchronize do
+ subscription = @subscription
+
+ logger.debug { "maintaining push subscription, monitoring: #{!!@push_monitoring}, subscription: #{subscription ? !subscription.expired? : "none"}" }
+
+ return create_subscription unless subscription
+
+ if should_force || subscription.expired?
+ # renew subscription
+ begin
+ logger.debug { "renewing subscription" }
+ expires = SUBSCRIPTION_LENGTH.from_now
+ sub = workplace_accessor.renew_notifier(subscription, expires.to_unix).get
+ @subscription = PlaceCalendar::Subscription.from_json(sub.to_json)
+
+ # save the subscription details for processing
+ define_setting(:push_subscription, @subscription)
+ @sub_renewed_at = Time.local
+ rescue error
+ logger.error(exception: error) { "failed to renew expired subscription, creating new subscription" }
+ @subscription = nil
+ schedule.in(1.second) { push_notificaitons_maintain; nil }
+ end
+
+ configure_push_monitoring
+ return
+ end
+
+ configure_push_monitoring if @push_monitoring.nil?
+ end
+ end
+
+ protected def configure_push_monitoring
+ subscription = @subscription.as(PlaceCalendar::Subscription)
+ channel_path = "#{subscription.id}/event"
+
+ if old = @push_monitoring
+ subscriptions.unsubscribe old
+ end
+
+ @push_monitoring = monitor(channel_path) { |_subscription, payload| push_event_occured(payload) }
+ logger.debug { "monitoring channel: #{channel_path}" }
+ end
+
+ protected def push_event_occured(payload : String)
+ logger.debug { "push notification received! #{payload}" }
+
+ notification = NotifyEvent.from_json payload
+
+ secret = @subscription.try &.client_secret
+ unless secret && secret == notification.client_secret
+ logger.warn { "ignoring notify event with mismatched secret: #{notification.inspect}" }
+ return
+ end
+
+ case notification.event_type
+ in .created?, .updated?, .deleted?
+ logger.debug { "polling events as received #{notification.event_type} notification" }
+ if resource_id = notification.resource_id
+ self[:last_event_notification] = {notification.event_type, resource_id, Time.utc.to_unix}
+ end
+
+ subscription_on_crud(notification)
+ in .missed?
+ # we don't know the exact event id that changed
+ logger.debug { "polling events as a notification was previously missed" }
+ subscription_on_missed
+ in .renew?
+ # we need to create a new subscription as the old one has expired
+ logger.debug { "a subscription renewal is required" }
+ create_subscription
+ in .reauthorize?
+ logger.debug { "a subscription reauthorization is required" }
+ expires = SUBSCRIPTION_LENGTH.from_now
+ workplace_accessor.reauthorize_notifier(@subscription, expires.to_unix)
+ end
+ rescue error
+ logger.error(exception: error) { "error processing push notification" }
+ end
+
+ protected def create_subscription
+ @push_mutex.synchronize do
+ @push_service_name = service_name = @push_service_name || ServiceName.parse(workplace_accessor.calendar_service_name.get.as_s)
+
+ # different resource routes for the different services
+ resource = subscription_resource(service_name)
+ logger.debug { "registering for push notifications! #{resource}" }
+
+ # create a new secret and subscription
+ expires = SUBSCRIPTION_LENGTH.from_now
+ push_secret = "a#{Random.new.hex(4)}"
+ sub = workplace_accessor.create_notifier(resource, @push_notification_url, expires.to_unix, push_secret, @push_notification_url).get
+ @subscription = PlaceCalendar::Subscription.from_json(sub.to_json)
+
+ # save the subscription details for processing
+ define_setting(:push_subscription, @subscription)
+ @sub_renewed_at = Time.local
+
+ configure_push_monitoring
+ end
+ end
+end
diff --git a/drivers/place/mqtt.cr b/drivers/place/mqtt.cr
new file mode 100644
index 00000000000..42ce6f9ffe7
--- /dev/null
+++ b/drivers/place/mqtt.cr
@@ -0,0 +1,155 @@
+require "placeos-driver"
+require "./mqtt_transport_adaptor"
+
+class Place::MQTT < PlaceOS::Driver
+ descriptive_name "Generic MQTT"
+ generic_name :GenericMQTT
+
+ tcp_port 1883
+ description %(makes MQTT data available to other drivers in PlaceOS, for use with String payloads)
+
+ default_settings({
+ username: "user",
+ password: "pass",
+ keep_alive: 60,
+ client_id: "placeos",
+ subscriptions: ["root/#"],
+
+ # requests per-second
+ rate_limit: 100,
+ queue_size: 1000,
+ })
+
+ @rate_limited : Bool = true
+ @queue_size : Int32 = 1000
+ @queue_count : Int32 = 0
+ @channel : Channel(Nil) = Channel(Nil).new(1)
+ @queue_lock : Mutex = Mutex.new
+ @wait_time : Time::Span = 300.milliseconds
+
+ @keep_alive : Int32 = 60
+ @username : String? = nil
+ @password : String? = nil
+ @client_id : String = "placeos"
+
+ @mqtt : ::MQTT::V3::Client? = nil
+ @subs : Array(String) = [] of String
+ @transport : Place::TransportAdaptor? = nil
+ @sub_proc : Proc(String, Bytes, Nil) = Proc(String, Bytes, Nil).new { |_key, _payload| nil }
+
+ def on_load
+ spawn { rate_limiter }
+ @sub_proc = Proc(String, Bytes, Nil).new { |key, payload| on_message(key, payload) }
+ on_update
+ end
+
+ def on_unload
+ @channel.close
+ end
+
+ def on_update
+ @username = setting?(String, :username)
+ @password = setting?(String, :password)
+ @keep_alive = setting?(Int32, :keep_alive) || 60
+ @client_id = setting?(String, :client_id) || ::MQTT.generate_client_id("placeos_")
+
+ @queue_size = setting?(Int32, :queue_size) || 1000
+ if rate_limit = setting?(Int32, :rate_limit)
+ @rate_limited = true
+ @wait_time = (1.0 / rate_limit.to_f).seconds
+ else
+ @rate_limited = false
+ end
+
+ existing = @subs
+ @subs = setting?(Array(String), :subscriptions) || [] of String
+
+ schedule.clear
+ schedule.every((@keep_alive // 3).seconds) { ping }
+
+ if client = @mqtt
+ unsub = existing - @subs
+ newsub = @subs - existing
+
+ unsub.each do |sub|
+ logger.debug { "unsubscribing to #{sub}" }
+ perform_operation { client.unsubscribe(sub) }
+ end
+
+ newsub.each do |sub|
+ logger.debug { "subscribing to #{sub}" }
+ perform_operation { client.subscribe(sub, &@sub_proc) }
+ end
+ end
+ end
+
+ def connected
+ transp = Place::TransportAdaptor.new(transport, queue)
+ client = ::MQTT::V3::Client.new(transp)
+ @transport = transp
+ @mqtt = client
+
+ logger.debug { "sending connect message" }
+ client.connect(@username, @password, @keep_alive, @client_id)
+ @subs.each do |sub|
+ logger.debug { "subscribing to #{sub}" }
+ perform_operation { client.subscribe(sub, &@sub_proc) }
+ end
+ end
+
+ def disconnected
+ @transport = nil
+ @mqtt = nil
+ end
+
+ protected def on_message(key : String, playload : Bytes) : Nil
+ self[key] = String.new(playload)
+ end
+
+ def publish(key : String, payload : String) : Nil
+ logger.debug { "publishing payload to #{key}" }
+ perform_operation { @mqtt.not_nil!.publish(key, payload) }
+ nil
+ end
+
+ def ping
+ logger.debug { "sending ping" }
+ perform_operation { @mqtt.not_nil!.ping }
+ end
+
+ def received(data, task)
+ logger.debug { "received #{data.size} bytes: 0x#{data.hexstring}" }
+ @transport.try &.process(data)
+ task.try &.success
+ end
+
+ protected def perform_operation
+ return yield unless @rate_limited
+
+ if @queue_count >= @queue_size
+ raise "queue size #{@queue_size} requests already queued, backpressure being applied"
+ end
+
+ @queue_lock.synchronize { @queue_count += 1 }
+ @channel.receive
+ @queue_lock.synchronize { @queue_count -= 1 }
+
+ yield
+ end
+
+ protected def rate_limiter
+ loop do
+ break if @channel.closed?
+ begin
+ @channel.send(nil)
+ rescue error
+ logger.error(exception: error) { "issue with rate limiter" }
+ ensure
+ sleep @wait_time
+ end
+ end
+ rescue
+ # Possible error with logging exception, restart rate limiter silently
+ spawn { rate_limiter } unless @channel.closed?
+ end
+end
diff --git a/drivers/place/mqtt_spec.cr b/drivers/place/mqtt_spec.cr
new file mode 100644
index 00000000000..d658439744d
--- /dev/null
+++ b/drivers/place/mqtt_spec.cr
@@ -0,0 +1,71 @@
+require "placeos-driver/spec"
+require "mqtt"
+
+DriverSpecs.mock_driver "Place::MQTT" do
+ # ============================
+ # CONNECTION
+ # ============================
+ puts "===== CONNECTION NEGOTIATION ====="
+ connect = MQTT::V3::Connect.new
+ connect.id = MQTT::RequestType::Connect
+ connect.keep_alive_seconds = 60_u16
+ connect.client_id = "placeos"
+ connect.clean_start = true
+ connect.username = "user"
+ connect.password = "pass"
+ connect.packet_length = connect.calculate_length
+ should_send(connect.to_slice)
+
+ connack = MQTT::V3::Connack.new
+ connack.id = MQTT::RequestType::Connack
+ connack.packet_length = connack.calculate_length
+ responds(connack.to_slice)
+
+ # ============================
+ # SUBSCRIPTION
+ # ============================
+ puts "===== SUBSCRIPTION REQUESTED ====="
+ packet = MQTT::V3::Subscribe.new
+ packet.id = MQTT::RequestType::Subscribe
+ packet.qos = MQTT::QoS::BrokerReceived
+ packet.message_id = 2_u16
+ packet.topic = "root/#"
+ packet.packet_length = packet.calculate_length
+ should_send(packet.to_slice)
+
+ suback = MQTT::V3::Suback.new
+ suback.id = MQTT::RequestType::Suback
+ suback.message_id = 2_u16
+ suback.return_codes = [MQTT::QoS::FireAndForget]
+ suback.packet_length = suback.calculate_length
+ responds(suback.to_slice)
+
+ # ============================
+ # REMOTE PUBLISH
+ # ============================
+ puts "===== REMOTE PUBLISH ====="
+ publish = MQTT::V3::Publish.new
+ publish.id = MQTT::RequestType::Publish
+ publish.message_id = 3_u16
+ publish.topic = "root/topic"
+ publish.payload = "testing"
+ publish.packet_length = publish.calculate_length
+
+ transmit publish.to_slice
+ sleep 0.1 # wait a bit for processing
+ status["root/topic"].should eq("testing")
+
+ # ============================
+ # DRIVER PUBLISH
+ # ============================
+ puts "===== DRIVER PUBLISH ====="
+ exec(:publish, "root/topic/action", "value")
+
+ publish = MQTT::V3::Publish.new
+ publish.id = MQTT::RequestType::Publish
+ publish.message_id = 3_u16
+ publish.topic = "root/topic/action"
+ publish.payload = "value"
+ publish.packet_length = publish.calculate_length
+ should_send(publish.to_slice)
+end
diff --git a/drivers/place/mqtt_transport_adaptor.cr b/drivers/place/mqtt_transport_adaptor.cr
new file mode 100644
index 00000000000..a3fef439df5
--- /dev/null
+++ b/drivers/place/mqtt_transport_adaptor.cr
@@ -0,0 +1,28 @@
+require "mqtt"
+
+class Place::TransportAdaptor < MQTT::Transport
+ def initialize(@driver, @queue)
+ super()
+ end
+
+ @driver : PlaceOS::Driver::Transport
+ @queue : PlaceOS::Driver::Queue
+
+ def close! : Nil
+ @driver.disconnect
+ end
+
+ def closed? : Bool
+ !@queue.online
+ end
+
+ def send(message) : Nil
+ @driver.send(message)
+ end
+
+ def process(data : Bytes)
+ @tokenizer.extract(data).each do |bytes|
+ spawn { @on_message.try &.call(bytes) }
+ end
+ end
+end
diff --git a/drivers/place/parking/locations.cr b/drivers/place/parking/locations.cr
new file mode 100644
index 00000000000..9cacab24dbf
--- /dev/null
+++ b/drivers/place/parking/locations.cr
@@ -0,0 +1,341 @@
+require "placeos-driver"
+require "placeos-driver/interface/locatable"
+require "../booking_model"
+require "placeos"
+require "json"
+
+# reserved parking spaces
+# check if any of these have been made available
+# fetch the parking bookings
+
+class Place::Parking::Locations < PlaceOS::Driver
+ include Interface::Locatable
+
+ descriptive_name "PlaceOS Parking Locations"
+ generic_name :ParkingLocations
+ description %(helper for handling parking bookings)
+
+ accessor area_manager : AreaManagement_1
+ accessor staff_api : StaffAPI_1
+
+ default_settings({
+ # time in seconds
+ poll_rate: 60,
+
+ # expose_for_analytics: {"output_key" => "booking_key->subkey"},
+ })
+
+ @timezone : Time::Location = Time::Location::UTC
+ @expose_for_analytics : Hash(String, String) = {} of String => String
+ @poll_rate : Time::Span = 60.seconds
+
+ BOOKING_TYPE = "parking"
+ RESERVED_RELEASED = "parking-released"
+ METADATA_KEY = "parking-spaces"
+
+ def on_load
+ monitor("staff/booking/changed") do |_subscription, payload|
+ logger.debug { "received booking changed event #{payload}" }
+ booking = Booking.from_json(payload)
+ booking.user_email = booking.user_email.downcase
+ booking_changed(booking)
+ end
+ on_update
+ end
+
+ def on_update
+ @poll_rate = (setting?(Int32, :poll_rate) || 60).seconds
+ @expose_for_analytics = setting?(Hash(String, String), :expose_for_analytics) || {} of String => String
+
+ timezone = config.control_system.not_nil!.timezone.presence || setting?(String, :time_zone).presence || "Australia/Sydney"
+ @timezone = Time::Location.load(timezone)
+
+ schedule.clear
+ schedule.every(@poll_rate) { query_parking_bookings }
+ schedule.in(5.seconds) { query_parking_bookings }
+ end
+
+ # level_zone_id => building_zone_id
+ getter level_buildings : Hash(String, String) do
+ hash = area_manager.level_buildings.get.as_h.transform_values(&.as_s)
+ raise "level cache not loaded yet" unless hash.size > 0
+ hash
+ end
+
+ getter zone_filter : Array(String) do
+ lvb = level_buildings
+ (lvb.keys + lvb.values).uniq
+ end
+
+ # ===================================
+ # Monitoring desk bookings
+ # ===================================
+ protected def booking_changed(event)
+ return unless event.booking_type == BOOKING_TYPE
+ matching_zones = zone_filter & event.zones
+ return if matching_zones.empty?
+
+ logger.debug { "booking event is in a matching zone" }
+
+ case event.action
+ when "create"
+ return unless event.in_progress?
+ # Check if this event is happening now
+ logger.debug { "adding new booking" }
+ @bookings[event.user_email] << event
+ when "cancelled", "rejected"
+ # delete the booking from the levels
+ found = false
+ @bookings[event.user_email].reject! { |booking| found = true if booking.id == event.id }
+ return unless found
+ when "check_in"
+ return unless event.in_progress?
+ @bookings[event.user_email].each { |booking| booking.checked_in = true if booking.id == event.id }
+ when "changed"
+ # Check if this booking is for today and update as required
+ @bookings[event.user_email].reject! { |booking| booking.id == event.id }
+ @bookings[event.user_email] << event if event.in_progress?
+ else
+ # ignore the update (approve)
+ logger.debug { "booking event was ignored" }
+ return
+ end
+
+ area_manager.update_available(matching_zones)
+ end
+
+ # ===================================
+ # Locatable Interface functions
+ # ===================================
+ def locate_user(email : String? = nil, username : String? = nil)
+ logger.debug { "searching for #{email}, #{username}" }
+ bookings = @bookings[email]? || [] of Booking
+ map_bookings(bookings)
+ end
+
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ logger.debug { "listing MAC addresses assigned to #{email}, #{username}" }
+ found = [] of String
+ @known_users.each { |user_id, (user_email, _name)|
+ found << user_id if email == user_email
+ }
+ found
+ end
+
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ logger.debug { "searching for owner of #{mac_address}" }
+ if user_details = @known_users[mac_address]?
+ email, _name = user_details
+ {
+ location: "booking",
+ assigned_to: email,
+ mac_address: mac_address,
+ }
+ end
+ end
+
+ def device_locations(zone_id : String, location : String? = nil)
+ logger.debug { "searching devices in zone #{zone_id}" }
+ return [] of Nil if location && location != "booking"
+
+ bookings = [] of Booking
+ @bookings.each_value(&.each { |booking|
+ next unless zone_id.in?(booking.zones)
+ bookings << booking
+ })
+ map_bookings(bookings)
+ end
+
+ protected def map_bookings(bookings)
+ level_to_building = level_buildings
+
+ bookings.map do |booking|
+ level = nil
+ building = nil
+ booking.zones.each do |zone_id|
+ if build = level_to_building[zone_id]?
+ building = build
+ level = zone_id
+ break
+ end
+ end
+
+ # We specify location as JSON::Any so we don't have to
+ # explicitly define the type of this object
+ payload = {
+ "location" => JSON::Any.new("booking"),
+ "type" => BOOKING_TYPE,
+ "checked_in" => booking.checked_in,
+ "asset_id" => booking.asset_id,
+ "booking_id" => booking.id,
+ "building" => building,
+ "level" => level,
+ "ends_at" => booking.booking_end,
+ "started_at" => booking.booking_start,
+ "duration" => booking.booking_end - booking.booking_start,
+ "mac" => booking.user_email,
+ "staff_name" => booking.user_name,
+ }
+
+ # check for any custom data we want to include
+ if !booking.extension_data.empty? && (init_data = JSON::Any.new(booking.extension_data))
+ @expose_for_analytics.each do |binding, path|
+ begin
+ binding_keys = path.split("->")
+ data = init_data
+ binding_keys.each do |key|
+ next if key == "extension_data"
+
+ data = data.dig? key
+ break unless data
+ end
+ payload[binding] = data
+ rescue error
+ logger.warn(exception: error) { "failed to expose #{binding}: #{path} for analytics" }
+ end
+ end
+ end
+
+ payload
+ end
+ end
+
+ # ===================================
+ # Parking and zone queries
+ # ===================================
+
+ struct ParkingSpace
+ include JSON::Serializable
+
+ property id : String
+ property name : String
+ property map_id : String
+ property assigned_to : String?
+ property assigned_name : String?
+
+ def reserved?
+ !!@assigned_to
+ end
+ end
+
+ struct Details
+ include JSON::Serializable
+
+ property details : Array(ParkingSpace)
+ end
+
+ alias Zone = PlaceOS::Client::API::Models::Zone
+ alias Metadata = Hash(String, Details)
+ alias ChildMetadata = Array(NamedTuple(zone: Zone, metadata: Metadata))
+
+ # Email => Array of bookings
+ @bookings : Hash(String, Array(Booking)) = Hash(String, Array(Booking)).new
+
+ # UserID => {Email, Name}
+ @known_users : Hash(String, Tuple(String, String)) = Hash(String, Tuple(String, String)).new
+
+ def parking_spaces : Hash(String, Array(ParkingSpace))
+ metadatas = level_buildings.values.uniq.map do |zone_id|
+ ChildMetadata.from_json(staff_api.metadata_children(
+ zone_id,
+ METADATA_KEY
+ ).get.to_json)
+ end
+
+ zone_parking = Hash(String, Array(ParkingSpace)).new
+
+ metadatas.each do |metadata|
+ metadata.each do |level|
+ zone = level[:zone]
+ if spaces = level[:metadata][METADATA_KEY]?.try(&.details)
+ zone_parking[zone.id] = spaces
+ end
+ end
+ end
+
+ zone_parking
+ end
+
+ def query_parking_bookings : Nil
+ # find all the reserved parking
+ reserved_spaces = parking_spaces.tap(&.each_value(&.select!(&.reserved?)))
+
+ logger.debug do
+ count = 0
+ reserved_spaces.each_value { |space| count += space.size }
+ "queried reserved spaces, found #{count}"
+ end
+
+ parking_zones = reserved_spaces.keys
+
+ # bookings for general access spaces
+ bookings = [] of JSON::Any
+ parking_zones.each { |zone| bookings.concat staff_api.query_bookings(type: BOOKING_TYPE, zones: {zone}).get.as_a }
+ bookings = bookings.map do |booking|
+ booking = Booking.from_json(booking.to_json)
+ booking.user_email = booking.user_email.downcase
+ booking
+ end
+
+ logger.debug { "queried parking bookings, found #{bookings.size}" }
+
+ # check if any of the reserved spaces have been made available
+ release_bookings = [] of JSON::Any
+ parking_zones.each { |zone| release_bookings.concat staff_api.query_bookings(type: RESERVED_RELEASED, zones: {zone}).get.as_a }
+ release_bookings = release_bookings.map do |booking|
+ booking = Booking.from_json(booking.to_json)
+ booking.user_email = booking.user_email.downcase
+ booking
+ end
+
+ logger.debug { "queried released spaces, found #{release_bookings.size}" }
+
+ # for all reserved spaces that haven't been released, we need to
+ # create a virtual booking for them
+ release_bookings.each do |booking|
+ parking_space = booking.asset_id
+ reserved_spaces.each_value do |spaces|
+ spaces.reject! { |space| space.id == parking_space }
+ end
+ end
+
+ now = Time.local(@timezone)
+ res_start = now.at_beginning_of_day.to_unix
+ res_end = now.at_end_of_day.to_unix
+ level_to_building = level_buildings
+
+ reserved_spaces.each do |level_zone, reservations|
+ building_zone = level_to_building[level_zone]?
+ next unless building_zone
+
+ reservations.each do |reservation|
+ bookings << Place::Booking.new(
+ id: -1,
+ booking_type: BOOKING_TYPE,
+ booking_start: res_start,
+ booking_end: res_end,
+ user_id: reservation.assigned_to.as(String),
+ user_email: reservation.assigned_to.as(String),
+ user_name: reservation.assigned_name.as(String),
+ zones: [level_zone, building_zone],
+ booked_by_name: reservation.assigned_name.as(String),
+ booked_by_email: reservation.assigned_to.as(String),
+ asset_id: reservation.id,
+ checked_in: true,
+ )
+ end
+ end
+
+ new_bookings = Hash(String, Array(Booking)).new do |hash, key|
+ hash[key] = [] of Booking
+ end
+
+ bookings.each do |booking|
+ next if booking.rejected
+ new_bookings[booking.user_email] << booking
+ @known_users[booking.user_id] = {booking.user_email, booking.user_name}
+ end
+
+ @bookings = new_bookings
+ end
+end
diff --git a/drivers/place/parking/locations_spec.cr b/drivers/place/parking/locations_spec.cr
new file mode 100644
index 00000000000..deddad83165
--- /dev/null
+++ b/drivers/place/parking/locations_spec.cr
@@ -0,0 +1,161 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Parking::Locations" do
+ system({
+ StaffAPI: {StaffAPIMock},
+ AreaManagement: {AreaManagementMock},
+ })
+
+ exec(:parking_spaces).get.should eq({
+ "zone-EYEnrhbaQz" => [
+ {
+ "id" => "park-001",
+ "name" => "Bay 001",
+ "map_id" => "park-001",
+ },
+ {
+ "id" => "parking-zone-FlWVOXv9yY.472179",
+ "name" => "Bay 005 Test",
+ "map_id" => "park-005",
+ "assigned_to" => "AdeleV@0cbfs.onmicrosoft.com",
+ "assigned_name" => "Adele Vance",
+ },
+ ],
+ })
+end
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ def query_bookings(type : String, zones : Array(String))
+ logger.debug { "Querying desk bookings!" }
+
+ now = Time.local
+ start = now.at_beginning_of_day.to_unix
+ ending = now.at_end_of_day.to_unix
+ [
+ {
+ id: 1,
+ booking_type: type,
+ booking_start: start,
+ booking_end: ending,
+ asset_id: "desk-123",
+ user_id: "user-1234",
+ user_email: "user1234@org.com",
+ user_name: "Bob Jane",
+ zones: zones + ["zone-building"],
+ checked_in: true,
+ rejected: false,
+ booked_by_name: "Bob Jane",
+ booked_by_email: "user1234@org.com",
+ },
+ {
+ id: 2,
+ booking_type: type,
+ booking_start: start,
+ booking_end: ending,
+ asset_id: "desk-456",
+ user_id: "user-456",
+ user_email: "zdoo@org.com",
+ user_name: "Zee Doo",
+ zones: zones + ["zone-building"],
+ checked_in: false,
+ rejected: false,
+ booked_by_name: "Zee Doo",
+ booked_by_email: "zdoo@org.com",
+ },
+ ]
+ end
+
+ def metadata_children(id : String, key : String? = nil)
+ logger.info { "requesting zone #{id} and key #{key}" }
+
+ [
+ {
+ "zone": {
+ "created_at": 1668744303,
+ "updated_at": 1668744303,
+ "id": "zone-FlWVOXv9yY",
+ "name": "PlaceOS Dev Sydney Catering Enabled",
+ "display_name": "Catering ",
+ "location": "",
+ "description": "",
+ "code": "",
+ "type": "",
+ "count": 0,
+ "capacity": 0,
+ "map_id": "",
+ "tags": [] of String,
+ "triggers": [] of String,
+ "parent_id": "zone-DnTcV5ZeEq",
+ },
+ "metadata": {} of String => String,
+ },
+ {
+ "zone": {
+ "created_at": 1691972553,
+ "updated_at": 1701398359,
+ "id": "zone-EYEnrhbaQz",
+ "name": "LEVEL Parking",
+ "display_name": "Parking",
+ "location": "",
+ "description": "",
+ "code": "",
+ "type": "",
+ "count": 0,
+ "capacity": 0,
+ "map_id": "https://s3-ap-southeast-2.amazonaws.com/os.place.tech/placeos-dev.aca.im/169197263162476823.svg",
+ "tags": [
+ "level",
+ "parking",
+ ],
+ "triggers": [] of String,
+ "parent_id": "zone-DnTcV5ZeEq",
+ },
+ "metadata": {
+ "parking-spaces": {
+ "name": "parking-spaces",
+ "description": "List of available parking spaces",
+ "details": [
+ {
+ "id": "park-001",
+ "name": "Bay 001",
+ "notes": "notes new",
+ "map_id": "park-001",
+ "assigned_to": nil,
+ "map_rotation": 0,
+ "assigned_name": nil,
+ "assigned_user": nil,
+ },
+ {
+ "id": "parking-zone-FlWVOXv9yY.472179",
+ "name": "Bay 005 Test",
+ "notes": "",
+ "map_id": "park-005",
+ "assigned_to": "AdeleV@0cbfs.onmicrosoft.com",
+ "map_rotation": 0,
+ "assigned_name": "Adele Vance",
+ },
+ ],
+ "parent_id": "zone-FlWVOXv9yY",
+ "editors": [] of String,
+ "modified_by_id": "user-DGLTbVU8eqiSRn",
+ },
+ },
+ },
+ ]
+ end
+end
+
+# :nodoc:
+class AreaManagementMock < DriverSpecs::MockDriver
+ def update_available(zones : Array(String))
+ logger.info { "requested update to #{zones}" }
+ nil
+ end
+
+ def level_buildings
+ {
+ "zone-EYEnrhbaQz": "zone-DnTcV5ZeEq",
+ }
+ end
+end
diff --git a/drivers/place/password_generator_helper.cr b/drivers/place/password_generator_helper.cr
new file mode 100644
index 00000000000..91ac343af92
--- /dev/null
+++ b/drivers/place/password_generator_helper.cr
@@ -0,0 +1,58 @@
+# Password defaults
+DEFAULT_PASSWORD_LENGTH = 6
+DEFAULT_PASSWORD_EXCLUDE = "0Oo1Il`'\\/"
+DEFAULT_PASSWORD_MINIMUM_LOWERCASE = 1
+DEFAULT_PASSWORD_MINIMUM_UPPERCASE = 0
+DEFAULT_PASSWORD_MINIMUM_NUMBERS = 1
+DEFAULT_PASSWORD_MINIMUM_SYMBOLS = 0
+
+PASSWORD_LOWERCASE_CHARACTERS = ('a'..'z').to_a
+PASSWORD_UPPERCASE_CHARACTERS = ('A'..'Z').to_a
+PASSWORD_NUMBER_CHARACTERS = ('0'..'9').to_a
+PASSWORD_SYMBOL_CHARACTERS = ['!', '@', '#', '$', '%', '^', '&', '*', '(', ')', '_', '+', '-', '=', '{', '}', '[', ']', '|', '\\', ':', ';', '"', '\'', '<', '>', ',', '.', '?', '/', '`', '~']
+
+def generate_password(
+ length : Int32? = DEFAULT_PASSWORD_LENGTH,
+ exclude : String? = DEFAULT_PASSWORD_EXCLUDE,
+ minimum_lowercase : Int32? = DEFAULT_PASSWORD_MINIMUM_LOWERCASE,
+ minimum_uppercase : Int32? = DEFAULT_PASSWORD_MINIMUM_UPPERCASE,
+ minimum_numbers : Int32? = DEFAULT_PASSWORD_MINIMUM_NUMBERS,
+ minimum_symbols : Int32? = DEFAULT_PASSWORD_MINIMUM_SYMBOLS
+) : String
+ length ||= DEFAULT_PASSWORD_LENGTH
+ exclude ||= DEFAULT_PASSWORD_EXCLUDE
+ minimum_lowercase ||= DEFAULT_PASSWORD_MINIMUM_LOWERCASE
+ minimum_uppercase ||= DEFAULT_PASSWORD_MINIMUM_UPPERCASE
+ minimum_numbers ||= DEFAULT_PASSWORD_MINIMUM_NUMBERS
+ minimum_symbols ||= DEFAULT_PASSWORD_MINIMUM_SYMBOLS
+
+ # Make sure the lenght is at least the minimums
+ minimums = minimum_lowercase + minimum_uppercase + minimum_numbers + minimum_symbols
+ length = minimums if length < minimums
+
+ characters = [] of Char
+ characters = PASSWORD_LOWERCASE_CHARACTERS if minimum_lowercase > 0
+ characters += PASSWORD_UPPERCASE_CHARACTERS if minimum_uppercase > 0
+ characters += PASSWORD_NUMBER_CHARACTERS if minimum_numbers > 0
+ characters += PASSWORD_SYMBOL_CHARACTERS if minimum_symbols > 0
+ characters = characters - exclude.chars
+
+ # make sure we have some characters to work with
+ if characters.empty?
+ characters = (PASSWORD_LOWERCASE_CHARACTERS + PASSWORD_NUMBER_CHARACTERS) - DEFAULT_PASSWORD_EXCLUDE.chars
+ end
+
+ password = [] of Char
+
+ # Add the minimums
+ minimum_lowercase.times { password << (PASSWORD_LOWERCASE_CHARACTERS - exclude.chars).sample(random: Random::Secure) }
+ minimum_uppercase.times { password << (PASSWORD_UPPERCASE_CHARACTERS - exclude.chars).sample(random: Random::Secure) }
+ minimum_numbers.times { password << (PASSWORD_NUMBER_CHARACTERS - exclude.chars).sample(random: Random::Secure) }
+ minimum_symbols.times { password << (PASSWORD_SYMBOL_CHARACTERS - exclude.chars).sample(random: Random::Secure) }
+
+ # Add the rest
+ (length - minimums).times { password << characters.sample(random: Random::Secure) }
+
+ # Shuffle the password
+ password.shuffle(random: Random::Secure).join
+end
diff --git a/drivers/place/pinger.cr b/drivers/place/pinger.cr
new file mode 100644
index 00000000000..f210ae7041d
--- /dev/null
+++ b/drivers/place/pinger.cr
@@ -0,0 +1,38 @@
+require "placeos-driver"
+require "pinger"
+
+class Place::Pinger < PlaceOS::Driver
+ descriptive_name "Device Pinger"
+ generic_name :Ping
+
+ # Discard port
+ udp_port 9
+ description %(periodically pings a device)
+
+ default_settings({
+ ping_every: 60,
+ })
+
+ def on_update
+ # Use quite a large random value to spread load
+ period = setting?(Int32, :ping_every) || 60
+ period = period * 1000 + rand(1000)
+
+ schedule.clear
+ schedule.every(period.milliseconds) { ping }
+ end
+
+ def ping
+ hostname = config.ip.not_nil!
+ pinger = ::Pinger.new(hostname, count: 3)
+ pinger.ping
+
+ pingable = pinger.pingable
+ if !pingable
+ self[:last_error] = pinger.exception || pinger.warning || "unknown error"
+ end
+
+ set_connected_state pingable
+ self[:pingable] = pingable
+ end
+end
diff --git a/drivers/place/pinger_spec.cr b/drivers/place/pinger_spec.cr
new file mode 100644
index 00000000000..b76080508fb
--- /dev/null
+++ b/drivers/place/pinger_spec.cr
@@ -0,0 +1,6 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Pinger" do
+ exec(:ping).get.should eq(true)
+ status[:pingable].should eq(true)
+end
diff --git a/drivers/place/rbp_remote_logger.cr b/drivers/place/rbp_remote_logger.cr
new file mode 100644
index 00000000000..05905001380
--- /dev/null
+++ b/drivers/place/rbp_remote_logger.cr
@@ -0,0 +1,61 @@
+require "placeos-driver"
+require "json"
+
+class Place::RbpRemoteLogger < PlaceOS::Driver
+ descriptive_name "Log Receiver for Room Booking Panel app"
+ generic_name :Logger
+ description %(Recieve logs streamed from Room Booking Panel app)
+
+ default_settings({
+ enabled: false,
+ max_log_entries: 1000,
+ debug: false,
+ })
+
+ @enabled : Bool = false
+ @max_log_entries : Int32 = 1000
+ @debug : Bool = false
+ @entries : Hash(String, Array(JSON::Any)) = {} of String => Array(JSON::Any)
+
+ def on_update
+ @logging_enabled = setting?(Bool, "enabled") || true
+ @max_log_entries = setting?(Int32, "max_log_entries") || 1000
+ @debug = setting?(Bool, "debug") || false
+
+ self[:enabled] = @logging_enabled
+ end
+
+ def post_event(payload : JSON::Any | String)
+ logger.debug { "Received: #{payload}" } if @debug
+
+ payload = payload.to_json if payload.is_a?(JSON::Any)
+ payload = payload.to_s if payload.is_a?(String)
+
+ entry = Entry.from_json(payload)
+
+ @entries[entry.device_id] ||= [] of JSON::Any
+
+ @entries[entry.device_id] =
+ @entries
+ .[entry.device_id]
+ .unshift(JSON.parse(payload))
+ .truncate(0, @max_log_entries)
+
+ self[:entries] = @entries
+
+ entry
+ end
+
+ class Entry
+ include JSON::Serializable
+
+ property id : String
+ property device_id : String
+ property type : String # Enum 'network' | 'console' | 'dom'
+ property subtype : String
+ property timestamp : Int64
+ property raw : JSON::Any
+ property data : JSON::Any
+ property metadata : JSON::Any
+ end
+end
diff --git a/drivers/place/rbp_remote_logger_spec.cr b/drivers/place/rbp_remote_logger_spec.cr
new file mode 100644
index 00000000000..239d67df95a
--- /dev/null
+++ b/drivers/place/rbp_remote_logger_spec.cr
@@ -0,0 +1,23 @@
+require "placeos-driver/spec"
+require "uuid"
+
+DriverSpecs.mock_driver "Place::RbpRemoteLogger" do
+ subpayload = {"id" => "1"}
+
+ payload = {
+ "id" => "1",
+ "type" => "3",
+ "subtype" => "4",
+ "timestamp" => 5,
+ "raw" => subpayload,
+ "data" => subpayload,
+ "metadata" => subpayload,
+ }
+
+ 5.times do
+ payload.merge!({"device_id" => UUID.random.to_s})
+ entry = exec(:post_event, payload.to_json).get.not_nil!
+ end
+
+ status.[:entries].as_h.keys.size.should eq 5
+end
diff --git a/drivers/place/room_at_capacity_mailer.cr b/drivers/place/room_at_capacity_mailer.cr
new file mode 100644
index 00000000000..3f321161775
--- /dev/null
+++ b/drivers/place/room_at_capacity_mailer.cr
@@ -0,0 +1,148 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+
+class Place::RoomAtCapacityMailer < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+
+ descriptive_name "PlaceOS Room at capacity mailer"
+ generic_name :RoomAtCapacityMailer
+ description %(notifies when a room is at capacity)
+
+ default_settings({
+ notify_email: ["concierge@place.com"],
+ email_template: "room_at_capacity",
+ debounce_time_minutes: 60, # the time to wait before sending another email
+ check_every_minutes: 5, # the frequency to check rooms
+ over_capactity_detected_count: 2, # the number of times over capacity before sending an email
+ })
+
+ accessor staff_api : StaffAPI_1
+ accessor locations : LocationServices_1
+
+ def mailer
+ system.implementing(Interface::Mailer)[0]
+ end
+
+ getter building_id : String do
+ locations.building_id.get.as_s
+ end
+
+ # Grabs the list of systems in the building
+ getter systems : Hash(String, Array(String)) do
+ staff_api.systems_in_building(building_id).get.as_h.transform_values(&.as_a.map(&.as_s))
+ end
+
+ def on_load
+ on_update
+ end
+
+ @notify_email : Array(String) = [] of String
+ @email_template : String = "room_at_capacity"
+ @debounce_time_minutes : Int32 = 60
+ @over_capactity_detected_count : Int32 = 2
+
+ @last_email_sent : Hash(String, Time) = {} of String => Time
+ @over_capacity : Hash(String, Int32) = Hash(String, Int32).new { |hash, sys_id| hash[sys_id] = 0 }
+
+ def on_update
+ @building_id = nil
+ @systems = nil
+
+ @notify_email = setting?(Array(String), :notify_email) || [] of String
+ @email_template = setting?(String, :email_template) || "room_at_capacity"
+ @debounce_time_minutes = setting?(Int32, :debounce_time_minutes) || 60
+ @over_capactity_detected_count = setting?(Int32, :over_capactity_detected_count) || 2
+
+ period = setting?(Int32, :check_every_minutes) || 5
+ schedule.clear
+ schedule.every(period.minutes) { check_capacity }
+ end
+
+ def check_capacity
+ systems.each do |level_id, system_ids|
+ system_ids.each do |system_id|
+ sys = system(system_id)
+ next unless sys.exists?("Bookings", 1)
+ next unless sys.capacity > 0
+
+ if people_count = sys.get("Bookings", 1).status?(Float64, "people_count")
+ logger.debug { "people count for #{system_id}: #{people_count}" }
+
+ if people_count >= sys.capacity
+ @over_capacity[system_id] += 1
+ else
+ @over_capacity[system_id] = 0
+ end
+
+ if (over = @over_capacity[system_id]?) && over == @over_capactity_detected_count
+ send_email(
+ sys.capacity,
+ people_count,
+ system_id,
+ sys.name,
+ sys.display_name,
+ sys.description,
+ sys.email,
+ )
+ end
+ end
+ end
+ end
+ end
+
+ @[Security(Level::Support)]
+ def send_email(
+ capacity : Int32,
+ people_count : Float64,
+ system_id : String,
+ name : String? = nil,
+ display_name : String? = nil,
+ description : String? = nil,
+ system_email : String? = nil,
+ )
+ if (last = @last_email_sent[system_id]?) && Time.utc - last < @debounce_time_minutes.minutes
+ logger.debug { "skipping email for #{system_id} due to debounce timer" }
+ return
+ end
+
+ args = {
+ system_id: system_id,
+ name: name,
+ display_name: display_name,
+ description: description,
+ system_email: system_email,
+ capacity: capacity,
+ people_count: people_count,
+ }
+
+ begin
+ mailer.send_template(
+ to: @notify_email,
+ template: {"room_at_capacity", @email_template},
+ args: args)
+ @last_email_sent[system_id] = Time.utc
+ rescue error
+ logger.warn(exception: error) { "failed to send at capacity email for zone #{system_id}" }
+ end
+ end
+
+ def template_fields : Array(TemplateFields)
+ [
+ TemplateFields.new(
+ trigger: {"room_at_capacity", @email_template},
+ name: "Room at capacity",
+ description: "Notification when a room is at capacity",
+ fields: [
+ {name: "system_id", description: "Identifier of the room/system"},
+ {name: "name", description: "Room name"},
+ {name: "display_name", description: "Room display name"},
+ {name: "description", description: "Room description"},
+ {name: "system_email", description: "System/room email address"},
+ {name: "capacity", description: "Capacity of the room"},
+ {name: "people_count", description: "Number of people in the room"},
+ ]
+ ),
+ ]
+ end
+end
diff --git a/drivers/place/room_booking_approval.cr b/drivers/place/room_booking_approval.cr
new file mode 100644
index 00000000000..d7c7c8d610b
--- /dev/null
+++ b/drivers/place/room_booking_approval.cr
@@ -0,0 +1,72 @@
+require "placeos-driver"
+require "place_calendar"
+
+class Place::RoomBookingApproval < PlaceOS::Driver
+ descriptive_name "PlaceOS Room Booking Approval"
+ generic_name :RoomBookingApproval
+ description %(Room Booking approval for tentative events)
+
+ default_settings({} of String => String)
+
+ accessor calendar : Calendar_1
+
+ getter building_id : String { get_building_id.not_nil! }
+ getter systems : Hash(String, Array(String)) { get_systems_list.not_nil! }
+
+ def on_update
+ @building_id = nil
+ @systems = nil
+
+ schedule.clear
+ # used to detect changes in building configuration
+ schedule.every(1.hour) { @systems = get_systems_list.not_nil! }
+
+ # The search
+ schedule.every(5.minutes) { find_bookings_for_approval }
+ end
+
+ # Finds the building ID for the current location services object
+ def get_building_id
+ zone_ids = system["StaffAPI"].zones(tags: "building").get.as_a.map(&.[]("id").as_s)
+ (zone_ids & system.zones).first
+ rescue error
+ logger.warn(exception: error) { "unable to determine building zone id" }
+ nil
+ end
+
+ # Grabs the list of systems in the building
+ def get_systems_list
+ system["StaffAPI"].systems_in_building(building_id).get.as_h.transform_values(&.as_a.map(&.as_s))
+ rescue error
+ logger.warn(exception: error) { "unable to obtain list of systems in the building" }
+ nil
+ end
+
+ def find_bookings_for_approval : Hash(String, Array(PlaceCalendar::Event))
+ results = {} of String => Array(PlaceCalendar::Event)
+
+ systems.each do |level_id, system_ids|
+ system_ids.each do |system_id|
+ sys = system(system_id)
+ if sys.exists?("Bookings", 1)
+ if bookings = sys.get("Bookings", 1).status?(Array(PlaceCalendar::Event), "bookings")
+ bookings.select! { |event| event.status == "tentative" }
+ results[system_id] = bookings unless bookings.empty?
+ end
+ end
+ end
+ end
+
+ self[:approval_required] = results
+ end
+
+ @[Security(Level::Support)]
+ def accept_event(calendar_id : String, event_id : String, user_id : String? = nil, notify : Bool = false, comment : String? = nil)
+ calendar.accept_event(calendar_id: calendar_id, event_id: event_id, user_id: user_id, notify: notify, comment: comment)
+ end
+
+ @[Security(Level::Support)]
+ def decline_event(calendar_id : String, event_id : String, user_id : String? = nil, notify : Bool = false, comment : String? = nil)
+ calendar.decline_event(calendar_id: calendar_id, event_id: event_id, user_id: user_id, notify: notify, comment: comment)
+ end
+end
diff --git a/drivers/place/room_booking_approval_spec.cr b/drivers/place/room_booking_approval_spec.cr
new file mode 100644
index 00000000000..f87901b0d22
--- /dev/null
+++ b/drivers/place/room_booking_approval_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::RoomBookingApprovalAltnerative" do
+end
diff --git a/drivers/place/router.cr b/drivers/place/router.cr
new file mode 100644
index 00000000000..82a9765bbbe
--- /dev/null
+++ b/drivers/place/router.cr
@@ -0,0 +1,46 @@
+require "placeos-driver"
+
+# this driver only exists to test router functionality
+# please use the meet driver
+
+# :nodoc:
+class Place::RouterTest < PlaceOS::Driver
+ generic_name :Switcher
+ descriptive_name "Signal router"
+ description <<-DESC
+ A virtual matrix switcher for arbitrary signal networks.
+
+ Following configuration, this driver can be used to perform simple input → \
+ output routing, regardless of intermediate hardware. Drivers it interacts \
+ with _must_ implement the `Switchable`, `InputSelection` or `Muteable` \
+ interfaces.
+
+ Configuration is specified as a map of devices and their attached inputs. \
+ This must exist under a top-level `connections` key.
+
+ Inputs can be either named:
+
+ Display_1:
+ hdmi: VidConf_1
+
+ Or, index based:
+
+ Switcher_1:
+ - Camera_1
+ - Camera_2
+
+ If an input is not a device with an associated module, prefix with an \
+ asterisk (`*`) to create a named alias.
+
+ Display_1:
+ hdmi: *Laptop
+
+ DESC
+end
+
+require "./router/core"
+
+# :nodoc:
+class Place::RouterTest < PlaceOS::Driver
+ include Router::Core
+end
diff --git a/drivers/place/router/core.cr b/drivers/place/router/core.cr
new file mode 100644
index 00000000000..56d00cbb0e5
--- /dev/null
+++ b/drivers/place/router/core.cr
@@ -0,0 +1,275 @@
+require "placeos-driver"
+require "levenshtein"
+require "promise"
+
+require "./settings"
+require "./signal_graph"
+
+# Core routing methods and functionality. This exists as module to enable
+# inclusion in other drivers, such as room logic, that provide auxillary
+# functionality to signal distribution.
+module Place::Router::Core
+ alias NodeRef = SignalGraph::Node::Ref
+
+ # Wrapper for providng simple interaction with a signal node and it's
+ # associated driver.
+ struct SignalNode
+ @label : SignalGraph::Node::Label
+ @proxy : Future::Compute(PlaceOS::Driver::Proxy::Driver)
+
+ def initialize(@label, @proxy)
+ end
+
+ forward_missing_to @label
+
+ def proxy
+ @proxy.get
+ end
+
+ def to_s(io)
+ io << ref
+ end
+
+ def watch(&handler : self ->)
+ @label.watch { handler.call self }
+ end
+ end
+
+ private getter! siggraph : SignalGraph
+
+ private getter! resolver : Hash(String, NodeRef)
+
+ getter current_routes : Hash(String, String?) = {} of String => String?
+
+ def on_update
+ load_siggraph
+ end
+
+ protected def load_siggraph
+ logger.debug { "loading signal graph from settings" }
+ connections = setting(Settings::Connections::Map, :connections)
+ load_siggraph connections
+ end
+
+ protected def load_siggraph(connections : Settings::Connections::Map)
+ nodes, links, aliases = Settings::Connections.parse connections, system.id
+ @siggraph = SignalGraph.build nodes, links
+ @resolver = init_resolver aliases
+ on_siggraph_load
+ end
+
+ protected def init_resolver(seed)
+ resolver = Hash(String, NodeRef).new(initial_capacity: seed.size) do |cache, key|
+ if ref = NodeRef.resolve? key, system.id
+ cache[key] = ref
+ else
+ alt = Levenshtein.find key, cache.keys, 3
+ msg = String.build do |err|
+ err << %(unknown signal node "#{key}")
+ err << %( - did you mean "#{alt}"?) if alt
+ end
+ raise KeyError.new msg
+ end
+ end
+ resolver.merge! seed
+ resolver
+ end
+
+ # Reads settings with node metadata into the graph.
+ protected def load_io(key : Symbol) : Enumerable(SignalGraph::Node::Label)?
+ logger.debug { "loading #{key}" }
+ if io = setting?(Settings::IOMeta, key)
+ io.map do |(key, meta)|
+ ref = resolver[key]
+ node = siggraph[ref]
+ node.meta = meta
+ node
+ end
+ else
+ logger.debug { "no #{key} configured" }
+ nil
+ end
+ end
+
+ protected def on_siggraph_load
+ aliases = resolver.invert
+ to_name = ->(ref : NodeRef) { aliases[ref]? || ref.local(system.id) }
+
+ inputs = load_io(:inputs) || siggraph.inputs.to_a
+ outputs = load_io(:outputs) || siggraph.outputs.to_a
+
+ # Persist previous state across module restarts or settings load
+ persist = ->(key : String, node : SignalGraph::Node::Label) do
+ self[key]?.try(&.as_h?).try &.each do |attr, value|
+ case attr
+ when "ref"
+ # Ignore
+ when "source"
+ node.source = signal_node(value.as_s).ref
+ when "locked"
+ node.locked = value.as_bool
+ else
+ node[attr] = value
+ end
+ rescue e
+ logger.info(exception: e) { "when loading previous #{key}/#{attr}" }
+ end
+ end
+
+ # Expose a list of input keys, along with an `input/` with a hash of
+ # metadata and state info for each.
+ self[:inputs] = inputs.map do |node|
+ key = to_name.call node.ref
+ persist.call "input/#{key}", node
+ node["name"] ||= key
+ node.watch { self["input/#{key}"] = node }
+ key
+ end
+
+ # As above, but for the outputs.
+ self[:outputs] = outputs.map do |node|
+ key = to_name.call node.ref
+
+ persist.call "output/#{key}", node
+ source_ref = node.source
+ current_routes[key] = source_ref ? to_name.call(source_ref.as(NodeRef)) : nil
+ node["name"] ||= key
+
+ # Discover inputs available to each output
+ reachable = siggraph.inputs(node.ref).select &.in?(inputs)
+ node["inputs"] = reachable.map(&.ref).map(&to_name).to_a
+
+ node.watch do
+ source_ref = node.source
+ current_routes[key] = source_ref ? to_name.call(source_ref.as(NodeRef)) : nil
+ self["output/#{key}"] = node
+ end
+ key
+ end
+
+ inodes, onodes = {inputs, outputs}.map &.each.map { |n| signal_node n.ref }
+ on_siggraph_loaded inodes, onodes
+ end
+
+ # Optional callback for overriding by driver extending this.
+ protected def on_siggraph_loaded(input, outputs)
+ end
+
+ protected def signal_node(key : String)
+ ref = resolver[key]
+ signal_node ref
+ end
+
+ protected def signal_node(ref : NodeRef)
+ node = siggraph[ref]
+
+ proxy = lazy do
+ case ref
+ when SignalGraph::Device, SignalGraph::Input, SignalGraph::Output
+ proxy_for ref.mod
+ else
+ raise "no device associated with #{ref}"
+ end
+ end
+
+ SignalNode.new node, proxy
+ end
+
+ protected def proxy_for(mod : SignalGraph::Mod)
+ (mod.sys == system.id ? system : system mod.sys).get mod.name, mod.idx
+ end
+
+ # Routes signal from *input* to *output*.
+ #
+ # Performs all intermediate device interaction based on current system
+ # config.
+ def route_signal(input : String, output : String, max_dist : Int32? = nil, simulate : Bool = false, follow_additional_routes : Bool = true)
+ logger.debug { "requesting route from #{input} to #{output}" }
+
+ src, dst = resolver.values_at input, output
+ dst_node = siggraph[dst]
+ src_node = siggraph[src]
+
+ path = siggraph.route(src, dst, max_dist) || raise "no route found"
+
+ execs = path.compact_map do |(node, edge, next_node)|
+ logger.debug { "#{node} → #{next_node}" }
+
+ raise "#{next_node} is locked, aborting" if next_node.locked
+
+ case edge
+ in SignalGraph::Edge::Static
+ nil
+ in SignalGraph::Edge::Active
+ Promise.defer(timeout: 1.second) do
+ next_node.source = siggraph[src].source
+
+ # OPTIMIZE: split this to perform an inital pass to build a hash
+ # from Driver::Proxy => [Edge::Active] then form the minimal set of
+ # execs that satisfies these.
+ if !simulate
+ mod = proxy_for edge.mod
+ case func = edge.func
+ in SignalGraph::Edge::Func::Mute
+ # check if we want to mute a video or audio layer
+ dst_layer = dst_node.ref.layer.downcase
+ case dst_layer
+ when "audio", "video"
+ mod.mute func.state, func.index, dst_layer
+ else
+ mod.mute func.state, func.index
+ end
+ in SignalGraph::Edge::Func::Select
+ mod.switch_to func.input
+
+ # ensure the device is unmuted
+ mod.mute(false, layer: :video) if mod.implements?(::PlaceOS::Driver::Interface::Muteable)
+ in SignalGraph::Edge::Func::Switch
+ mod.switch({func.input => [func.output]}, func.layer)
+ end
+ end
+ nil
+ end
+ end
+ end
+
+ # are there any additional switching actions to perform (combined outputs)
+ if follow_additional_routes
+ routes = {} of String => Tuple(String, String, Int32?, Bool, Bool)
+
+ if following_outputs = dst_node["followers"]?.try(&.as_a)
+ logger.debug { "routing #{following_outputs.size} additional followers" }
+ following_outputs.each { |output_follow| routes[output_follow.as_s] = {input, output_follow.as_s, max_dist, simulate, false} }
+ end
+
+ ignore_source_routes = dst_node["ignore_source_routes"]?.try(&.as_bool) || false
+
+ # perform_routes: {output: input}
+ if !ignore_source_routes && (additional_routes = src_node["perform_routes"]?.try(&.as_h))
+ logger.debug { "perfoming #{additional_routes.size} additional routes" }
+ additional_routes.each { |ad_output, ad_input| routes[ad_output] = {ad_input.as_s, ad_output, max_dist, simulate, false} }
+ end
+
+ spawn {
+ routes.each_value do |route|
+ begin
+ route_signal(*route)
+ rescue error
+ logger.warn(exception: error) { "issue routing: #{route[0]}=>#{route[1]}" }
+ end
+ end
+ }
+ end
+
+ logger.debug { "awaiting responses" }
+ execs.each do |promise|
+ begin
+ promise.get
+ rescue error
+ logger.warn(exception: error) { "processing route" }
+ end
+ end
+
+ :ok
+ end
+end
diff --git a/drivers/place/router/digraph.cr b/drivers/place/router/digraph.cr
new file mode 100644
index 00000000000..455475684f9
--- /dev/null
+++ b/drivers/place/router/digraph.cr
@@ -0,0 +1,224 @@
+# Labelled digraph. Holds node labels of type *N* and edge labels of type *E*.
+#
+# Nodes are stored on UInt64 ID's. This provides an interface that should feel
+# similar to `Indexable` for interacting with nodes labels. Similarly edges can
+# be placed and retrieved by using a dual index of {predescessor, successor}.
+#
+# OPTIMIZE: replace with a sparse matrix and graphBLAS operations.
+class Place::Router::Digraph(N, E)
+ class Error < Exception; end
+
+ record Node(N, E),
+ attr : N,
+ succ : Hash(UInt64, E)
+
+ @nodes : Hash(UInt64, Node(N, E))
+
+ delegate clear, to: @nodes
+
+ def initialize(initial_capacity = nil)
+ @nodes = Hash(UInt64, Node(N, E)).new initial_capacity: initial_capacity
+ end
+
+ private def node(id)
+ node(id) { raise Error.new "Node #{id} does not exist" }
+ end
+
+ private def node(id, &)
+ id = id.to_u64
+ @nodes.fetch(id) { yield id }
+ end
+
+ private def check_node_exists(id)
+ check_node_exists(id) { raise Error.new "Node #{id} does not exist" }
+ end
+
+ private def check_node_exists(id, &)
+ id = id.to_u64
+ @nodes.has_key?(id) ? id : yield id
+ end
+
+ # Retrieves the label attached to node *id*.
+ def [](id)
+ node(id).attr
+ end
+
+ # Retrieves the label attached to node *id*. Yields if it does not exist.
+ def fetch(id, &) : N
+ node = node(id) { return yield id }
+ node.attr
+ end
+
+ # Insert a new node.
+ def []=(id, attr)
+ insert(id, attr) { raise Error.new "Node #{attr.inspect} (#{id}) already exists" }
+ end
+
+ # Inserts a node. Yields if it already exists.
+ def insert(id, attr : N, &)
+ id = id.to_u64
+ if @nodes.has_key? id
+ yield id
+ else
+ @nodes[id] = Node(N, E).new attr, {} of UInt64 => E
+ end
+ end
+
+ # Retrieves the label attached to the edge that joins *pred_id* and *succ_id*.
+ def [](pred_id, succ_id)
+ fetch(pred_id, succ_id) do
+ raise Error.new "Edge #{pred_id} -> #{succ_id} does not exist"
+ end
+ end
+
+ # :ditto:
+ def fetch(pred_id, succ_id, &) : E
+ succ_id = check_node_exists succ_id
+ node(pred_id).succ.fetch(succ_id) { yield pred_id, succ_id }
+ end
+
+ # Inserts an edge.
+ def []=(pred_id, succ_id, attr)
+ insert(pred_id, succ_id, attr) do
+ raise Error.new "Edge #{pred_id} -> #{succ_id} already exists"
+ end
+ end
+
+ # :ditto:
+ def insert(pred_id, succ_id, attr : E, &)
+ succ_id = check_node_exists succ_id
+ pred = node pred_id
+ if pred.succ.has_key? succ_id
+ yield pred_id, succ_id
+ else
+ pred.succ[succ_id] = attr
+ end
+ end
+
+ # Perform a breadth first search across the graph, starting at *from*.
+ #
+ # Each node id is yielded as it's traversed. The search will terminate when
+ # this block returns true. If `nil` is returned the node is skipped, but the
+ # traversal continues.
+ #
+ # Results are provided as a Hash that includes all reached nodes as the keys,
+ # and their predecessor as the associated value.
+ def breadth_first_search(from, & : UInt64 -> Bool?)
+ paths = Hash(UInt64, UInt64).new
+ queue = Deque(UInt64).new 1, from
+
+ while pred_id = queue.shift?
+ node(pred_id).succ.each_key do |succ_id|
+ # Already visited
+ next if paths.has_key? succ_id
+
+ done = yield succ_id
+
+ next if done.nil?
+
+ paths[succ_id] = pred_id
+
+ return paths if done
+
+ queue << succ_id
+ end
+ end
+ end
+
+ # Returns a list of node IDs that form the shortest path between the passed
+ # nodes or `nil` if no path exists.
+ def path(from, to, invert = false) : Enumerable(UInt64)?
+ from = check_node_exists from
+ to = check_node_exists to
+
+ paths = breadth_first_search from, &.== to
+ return if paths.nil?
+
+ # Unwind the path captured in the hash.
+ nodes = [to]
+ until nodes.last == from
+ nodes << paths[nodes.last]
+ end
+
+ invert ? nodes : nodes.reverse!
+ end
+
+ # Provides all nodes present within the graph.
+ #
+ # NOTE: ordering of nodes is _not_ defined.
+ def nodes : Enumerable(UInt64)
+ @nodes.each_key
+ end
+
+ # Checks if a node has incoming edges only.
+ def sink?(id) : Bool
+ outdegree(id).zero? && !indegree(id).zero?
+ end
+
+ # Provides all nodes with incoming edges only.
+ def sinks : Enumerable(UInt64)
+ nodes.select { |id| sink? id }
+ end
+
+ # Checks if a node has outgoing edges only.
+ def source?(id) : Bool
+ !outdegree(id).zero? && indegree(id).zero?
+ end
+
+ # Provides all nodes with outgoing edges only.
+ #
+ # OPTIMIZE: this is _very_ slow [O(V * E)], but works for testing purposes.
+ # Switching the sparse matrix should assist so not worth optimising for this
+ # setup.
+ def sources : Enumerable(UInt64)
+ nodes.select { |id| source? id }
+ end
+
+ # The outgoing edges from *id*.
+ def outdegree(id)
+ node(id).succ.size
+ end
+
+ # The number of incomming edges to *id*.
+ def indegree(id)
+ id = check_node_exists id
+ @nodes.reduce(0) do |count, (_, node)|
+ count += 1 if node.succ.has_key? id
+ count
+ end
+ end
+
+ # Provides all nodes reachable from *id*.
+ def subtree(id) : Enumerable(UInt64)
+ id = check_node_exists id
+ SubtreeIterator.new self, id
+ end
+
+ private class SubtreeIterator
+ include Iterator(UInt64)
+
+ @ch = Channel(UInt64).new
+
+ def initialize(g, id)
+ spawn do
+ g.breadth_first_search id do |node|
+ begin
+ @ch.send node
+ false
+ rescue Channel::ClosedError
+ true
+ end
+ end
+ @ch.close unless @ch.closed?
+ end
+ end
+
+ def finalize
+ @ch.close unless @ch.closed?
+ end
+
+ def next
+ @ch.receive? || stop
+ end
+ end
+end
diff --git a/drivers/place/router/digraph_spec.cr b/drivers/place/router/digraph_spec.cr
new file mode 100644
index 00000000000..11f64f9a7aa
--- /dev/null
+++ b/drivers/place/router/digraph_spec.cr
@@ -0,0 +1,147 @@
+require "spec"
+require "./digraph"
+
+alias Digraph = Place::Router::Digraph
+
+describe Digraph do
+ describe "node insertion / retrieval" do
+ it "inserts a node with the specified ID" do
+ g = Digraph(String, String).new
+ g[42] = "foo"
+ g[42].should eq("foo")
+ end
+
+ it "raises when inserting on ID conflict" do
+ g = Digraph(String, String).new
+ expect_raises(Digraph::Error) do
+ g[42] = "foo"
+ g[42] = "bar"
+ end
+ end
+
+ it "raises when retrieving if node does not exist" do
+ g = Digraph(String, String).new
+ expect_raises(Digraph::Error) do
+ g[123]
+ end
+ end
+ end
+
+ describe "edge insertion / retrieval" do
+ it "inserts between the specified IDs" do
+ g = Digraph(String, String).new
+ g[0] = "foo"
+ g[1] = "bar"
+ g[0, 1] = "foobar"
+ g[0, 1].should eq("foobar")
+ end
+
+ it "raises if setting an edge that already exists" do
+ g = Digraph(String, String).new
+ expect_raises(Digraph::Error) do
+ g.insert(0, "foo") { }
+ g.insert(1, "bar") { }
+ g[0, 1] = "foobar"
+ g[0, 1] = "foobar"
+ end
+ end
+
+ it "raises when reading an edge that does not exist" do
+ g = Digraph(String, String).new
+ expect_raises(Digraph::Error) do
+ g[1, 0]
+ end
+ end
+ end
+
+ describe "#path" do
+ it "works on a trival graph" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[2] = "c"
+ g[0, 1] = "ab"
+ g[1, 2] = "bc"
+ g.path(0, 2).should eq([0, 1, 2])
+ g.path(2, 0).should be_nil
+ end
+
+ it "finds the shortest path" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[2] = "c"
+ g[0, 1] = "ab"
+ g[1, 2] = "bc"
+
+ g[3] = "x"
+ g[4] = "y"
+ g[5] = "z"
+ g[0, 3] = "ax"
+ g[3, 4] = "xy"
+ g[4, 5] = "yz"
+ g[5, 2] = "zc"
+
+ g.path(0, 2).should eq([0, 1, 2])
+ end
+ end
+
+ describe "#nodes" do
+ it "provides all nodes" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[2] = "c"
+ (g.nodes.to_a - [0, 1, 2]).should be_empty
+ end
+ end
+
+ describe "#outdegree" do
+ it "counts outgoing edges" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[0, 1] = "ab"
+ g.outdegree(0).should eq(1)
+ g.outdegree(1).should eq(0)
+ end
+ end
+
+ describe "#indegree" do
+ it "counts incoming edges" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[0, 1] = "ab"
+ g.indegree(0).should eq(0)
+ g.indegree(1).should eq(1)
+ end
+ end
+
+ describe "#subtree" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[2] = "c"
+ g[0, 1] = "ab"
+ g[1, 2] = "bc"
+ g[3] = "x"
+
+ it "returns all reachable nodes" do
+ reachable = g.subtree(0).to_a
+ expected = [1, 2]
+ (expected - reachable).should be_empty
+ end
+
+ it "does not return disconnected nodes" do
+ reachable = g.subtree(0)
+ reachable.should_not contain(3_u64)
+ end
+
+ it "traverses lazilly" do
+ reachable = g.subtree 0
+ g[2, 3] = "cx"
+ reachable.should contain(3_u64)
+ end
+ end
+end
diff --git a/drivers/place/router/settings.cr b/drivers/place/router/settings.cr
new file mode 100644
index 00000000000..c7f1bfe3150
--- /dev/null
+++ b/drivers/place/router/settings.cr
@@ -0,0 +1,176 @@
+require "json"
+require "./signal_graph"
+
+module Place::Router::Core::Settings
+ # Types for representing the settings format for defining connections.
+ module Connections
+ module Deserializable
+ macro extended
+ def self.new(pull : JSON::PullParser)
+ parse?(pull.read_string) || pull.raise("Invalid #{self} (#{pull.string_value.inspect})")
+ end
+ end
+
+ abstract def parse?(raw : String)
+
+ def from_json_object_key?(key : String)
+ parse? key
+ end
+
+ def get_parts(module_id : String) : {String, Int32?}
+ mod_name, match, index = module_id.rpartition('_')
+ if match.empty?
+ {module_id, 1}
+ else
+ # we want the `.to_i` to be able to fail, this indicates it's probably a DeviceOutput
+ {mod_name, index.to_i?}
+ end
+ end
+ end
+
+ # Module name of a device within the local system e.g. `"Switcher_1"`.
+ record Device, mod : String, idx : Int32 do
+ extend Deserializable
+
+ def self.parse?(raw : String)
+ return if name = raw.lchop?('*')
+ mod, idx = get_parts(raw)
+ new mod, idx if idx
+ end
+ end
+
+ # Reference to a specific output on a device that has multiple outputs.
+ # This is a concatenation of the `Device` reference a `.` and the output.
+ # For example, output 3 of Switcher_1 is `"Switcher_1.3"`.
+ record DeviceOutput, mod : String, idx : Int32, output : String | Int32, layer : String? do
+ extend Deserializable
+
+ def self.parse?(raw : String)
+ return if name = raw.lchop?('*')
+ mod_name, match, outp = raw.rpartition(/_\d+\./)
+ if !match.empty?
+ mod, idx = mod_name, match[1..-2].to_i
+ outp_idx, match, layer = outp.rpartition('!')
+ if match.empty?
+ output = outp.to_i? || outp
+ new mod, idx, output, nil
+ else
+ output = outp_idx.to_i? || outp_idx
+ new mod, idx, output, layer
+ end
+ end
+ end
+ end
+
+ # Alias used to refer to a signal node that does not have an accompanying
+ # module. This can be useful for declaring the concept of a device that is
+ # attached to an input (e.g. `"*Laptop"`). All alias' must be prefixed with
+ # an asterisk ('*') within connections settings.
+ record Alias, name : String do
+ extend Deserializable
+
+ def self.parse?(raw : String)
+ if name = raw.lchop?('*')
+ new name
+ end
+ end
+ end
+
+ # The device a signal is originating from.
+ alias Source = Device | DeviceOutput | Alias
+
+ # The device that recieves the signal.
+ alias Sink = Device | Alias
+
+ # Identifier for the input on Sink.
+ alias Input = String
+
+ # Structure for a full connection map.
+ #
+ # ```json
+ # {
+ # "Display_1": {
+ # "hdmi": "Switcher_1.1"
+ # },
+ # "Switcher_1": ["*Foo", "*Bar"],
+ # "*FloorBox": "Switcher_1.2"
+ # }
+ # ```
+ alias Map = Hash(Sink, Hash(Input, Source) | Array(Source) | DeviceOutput)
+
+ # Parses a `Map` containing the system conectivity into a set of nodes and
+ # links that can be used for assembling the `SignalGraph`.
+ def self.parse(map : Map, sys : String)
+ nodes = [] of SignalGraph::Node::Ref
+ links = [] of {SignalGraph::Node::Ref, SignalGraph::Node::Ref}
+ aliases = {} of String => SignalGraph::Node::Ref
+
+ make_alias = ->(name : String, node : SignalGraph::Node::Ref) do
+ if prev = aliases[name]?
+ raise %(invalid configuration: "#{name}" refers to both #{prev} and #{node})
+ end
+ aliases[name] = node
+ end
+
+ map.each do |sink, inputs|
+ if sink.is_a? Alias
+ source = inputs
+ unless source.is_a? DeviceOutput
+ raise %(invalid configuration: "#{sink}" must link to a DeviceOutput)
+ end
+ onode = SignalGraph::Output.new sys, source.mod, source.idx, source.output, source.layer
+ nodes << onode
+ make_alias.call sink.name, onode
+ else
+ # Direct link only supported by output aliases.
+ if inputs.is_a? DeviceOutput
+ raise %(invalid configuration: "#{sink}" must specify inputs as either a hash or array)
+ end
+
+ nodes << SignalGraph::Device.new sys, sink.mod, sink.idx
+
+ # Iterate source arrays as 1-based input id's
+ inputs = inputs.each.with_index(1).map &.reverse if inputs.is_a? Array
+
+ inputs.each do |input, input_source|
+ inode = SignalGraph::Input.new sys, sink.mod, sink.idx, input
+ nodes << inode
+
+ if input_source.is_a? Alias
+ make_alias.call input_source.name, inode
+ next
+ end
+
+ onode = case input_source
+ in Device
+ SignalGraph::Device.new sys, input_source.mod, input_source.idx
+ in DeviceOutput
+ SignalGraph::Output.new sys, input_source.mod, input_source.idx, input_source.output, input_source.layer
+ end
+ nodes << onode
+
+ links << {onode, inode}
+ end
+ end
+ end
+
+ {nodes, links, aliases}
+ end
+ end
+
+ # Input/outputs and their associated metadata. Attributes specified here are
+ # progated to the assocated input status keys. This allows information such as
+ # name, type etc to be exposed to UI's.
+ alias IOMeta = Hash(String, Hash(String, JSON::Any))
+end
+
+# FIXME: submit as PR to crystal standard lib to support this neatly
+struct Union
+ def self.from_json_object_key?(key : String)
+ {% for t in T %}
+ instance = {{t}}.from_json_object_key? key
+ return instance unless instance.nil?
+ {% end %}
+ raise JSON::ParseException.new("Couldn't parse #{self} from #{key}", __LINE__, 0)
+ end
+end
diff --git a/drivers/place/router/settings_spec.cr b/drivers/place/router/settings_spec.cr
new file mode 100644
index 00000000000..78a8c65ddae
--- /dev/null
+++ b/drivers/place/router/settings_spec.cr
@@ -0,0 +1,77 @@
+require "spec"
+require "./settings"
+
+alias Settings = Place::Router::Core::Settings
+alias SignalGraph = Place::Router::SignalGraph
+
+class PlaceOS::Driver::Proxy::System
+ def self.module_id?(sys, name, idx) : String?
+ mock_id = {sys, name, idx}.hash
+ "mod-#{mock_id}"
+ end
+end
+
+describe Settings::Connections do
+ connections = <<-JSON
+ {
+ "Display_1": {
+ "hdmi": "Switcher_1.1"
+ },
+ "Switcher_1": ["*Foo", "*Bar"],
+ "*FloorBox": "Switcher_1.2"
+ }
+ JSON
+
+ describe "Map" do
+ it "deserializes from JSON" do
+ Settings::Connections::Map.from_json connections
+ end
+ end
+
+ describe ".parse" do
+ it "extracts nodes, links, aliases" do
+ map = Settings::Connections::Map.from_json connections
+ nodes, links, aliases = Settings::Connections.parse map, sys: "abc123"
+ nodes.size.should eq(7)
+ links.should contain({
+ SignalGraph::Output.new("abc123", "Switcher", 1, 1, "all"),
+ SignalGraph::Input.new("abc123", "Display", 1, "hdmi"),
+ })
+ aliases.keys.should contain "Foo"
+ aliases.keys.should contain "FloorBox"
+ end
+
+ it "extracts nodes, links, aliases and layers" do
+ connections2 = <<-JSON
+ {
+ "Display_1": {
+ "hdmi": "15.07_Switcher_1.1!video"
+ },
+ "Switcher_1": ["*Foo", "*Bar"],
+ "*FloorBox": "Switcher_1.2"
+ }
+ JSON
+
+ map = Settings::Connections::Map.from_json connections2
+ nodes, links, aliases = Settings::Connections.parse map, sys: "abc123"
+ nodes.size.should eq(7)
+ links.should contain({
+ SignalGraph::Output.new("abc123", "15.07_Switcher", 1, 1, "video"),
+ SignalGraph::Input.new("abc123", "Display", 1, "hdmi"),
+ })
+ aliases.keys.should contain "Foo"
+ aliases.keys.should contain "FloorBox"
+ end
+
+ it "detects alias conflicts" do
+ map = Settings::Connections::Map.from_json <<-JSON
+ {
+ "Switcher_1": ["*Foo", "*Foo"]
+ }
+ JSON
+ expect_raises(Exception) do
+ Settings::Connections.parse map, sys: "abc123"
+ end
+ end
+ end
+end
diff --git a/drivers/place/router/signal_graph.cr b/drivers/place/router/signal_graph.cr
new file mode 100644
index 00000000000..9751b32e67f
--- /dev/null
+++ b/drivers/place/router/signal_graph.cr
@@ -0,0 +1,185 @@
+require "set"
+require "./digraph"
+require "./signal_graph/*"
+
+# Structures and types for mapping between sys,mod,idx,io referencing and the
+# underlying graph structure.
+#
+# The SignalGraph class _does not_ perform any direct interaction with devices,
+# but does provide the ability to discover routes and available connectivity
+# when may then be acted on.
+class Place::Router::SignalGraph
+ alias Input = Node::DeviceInput
+
+ alias Output = Node::DeviceOutput
+
+ alias Device = Node::Device
+
+ Mute = Node::Mute.instance
+
+ private getter g : Digraph(Node::Label, Edge::Label)
+
+ private def initialize(initial_capacity = nil)
+ @g = Digraph(Node::Label, Edge::Label).new initial_capacity
+ end
+
+ # Inserts *node*.
+ protected def insert(node : Node::Ref)
+ g[node.id] = Node::Label.new node
+ end
+
+ # :ditto:
+ protected def insert(node : Node::Mute)
+ mute = Node::Label.new node
+ mute.source = Mute
+ mute.locked = true
+ g[node.id] = mute
+ end
+
+ # Defines a physical connection between two devices.
+ #
+ # *output* and *input* must both already exist within the underlying graph as
+ # signal nodes.
+ protected def connect(output : Node::Ref, input : Node::Ref)
+ g[input.id, output.id] = Edge::Static.instance
+ end
+
+ # Given a *mod* and sets of known *inputs* and *outputs* in use on it, wire up
+ # any active edges between these based on the interfaces available.
+ protected def link(mod : Mod, inputs : Enumerable(Input), outputs : Enumerable(Output))
+ if mod.switchable? && !outputs.empty?
+ inputs.each do |input|
+ outputs.each do |output|
+ func = Edge::Func::Switch.new input.input, output.output, output.layer
+ g[output.id, input.id] = Edge::Active.new mod, func
+ end
+ end
+ elsif mod.selectable?
+ inputs.each do |input|
+ output = Node::Device.new mod
+ func = Edge::Func::Select.new input.input
+ g[output.id, input.id] = Edge::Active.new mod, func
+ end
+ end
+
+ if mod.muteable?
+ if outputs.empty?
+ output = Node::Device.new mod
+ func = Edge::Func::Mute.new true
+ g[output.id, Mute.id] = Edge::Active.new mod, func
+ else
+ # ameba:disable Lint/ShadowingOuterLocalVar
+ outputs.each do |output|
+ func = Edge::Func::Mute.new true, output.output
+ g[output.id, Mute.id] = Edge::Active.new mod, func
+ end
+ end
+ end
+ end
+
+ # Construct a graph from a pre-parsed configuration.
+ #
+ # *nodes* must contain the set of all signal nodes that form the device inputs
+ # and outputs across the system. This includes those at the "edge" of the
+ # signal network (e.g. a input to a switcher) as well as inputs in use on
+ # intermediate devices (e.g. a input on a display, which in turn is attached to
+ # the switcher above).
+ #
+ # *links* declares the interconnections between devices.
+ #
+ # Modules associated with any of these nodes are then introspected for
+ # switching, input selection and mute control based on the interfaces they
+ # expose.
+ def self.build(nodes : Enumerable(Node::Ref), links : Enumerable({Node::Ref, Node::Ref}))
+ mod_io = Hash(Mod, {Set(Input), Set(Output)}).new do |h, k|
+ h[k] = {Set(Input).new, Set(Output).new}
+ end
+
+ siggraph = new initial_capacity: nodes.size
+
+ siggraph.insert Mute
+
+ # Create verticies for each signal node
+ nodes.each do |node|
+ siggraph.insert node
+
+ # Track device IO in use for building active edges
+ case node
+ when Input
+ inputs, _ = mod_io[node.mod]
+ inputs << node
+ when Output
+ _, outputs = mod_io[node.mod]
+ outputs << node
+ end
+ end
+
+ # Insert the static edges.
+ links.each { |source, dest| siggraph.connect source, dest }
+
+ # Wire up the active edges.
+ mod_io.each { |mod, (inputs, outputs)| siggraph.link mod, inputs, outputs }
+
+ # Set a loopback source on all inputs.
+ siggraph.inputs.each { |node| node.source = node.ref }
+
+ siggraph
+ end
+
+ # Retrieves the labelled state for *node*.
+ def [](node : Node::Ref)
+ g[node.id]
+ end
+
+ # Retrieves the labelled state for the signal node at *node_id*.
+ def [](node_id)
+ g[node_id]
+ end
+
+ # Find the signal path that connects *source* to *dest*, or `nil` if this is
+ # not possible.
+ #
+ # Provides an `Iterator` that provides labels across each node, the edge, and
+ # subsequent node.
+ def route(source : Node::Ref, destination : Node::Ref, max_dist = nil)
+ path = g.path destination.id, source.id, invert: true
+
+ return nil unless path
+
+ return nil if max_dist && path.size > max_dist
+
+ path.each_cons(2, true).map do |(succ, pred)|
+ {
+ g[succ], # source
+ g[pred, succ], # edge
+ g[pred], # next node
+ }
+ end
+ end
+
+ # Checks if *node* is a system input.
+ def input?(node : Node::Ref) : Bool
+ g.sink? node.id
+ end
+
+ # Provide the signal nodes that form system inputs.
+ def inputs
+ # Graph connectivity is inverse to signal direction, hence sinks here.
+ g.sinks.compact_map { |id| g[id] unless id == Mute.id }
+ end
+
+ # Provide all signal nodes that can be routed to *destination*.
+ def inputs(destination : Node::Ref)
+ g.subtree(destination.id).map { |id| g[id] }
+ end
+
+ # Checks if *node* is a system output.
+ def output?(node : Node::Ref) : Bool
+ g.source? node.id
+ end
+
+ # Provide the signal nodes that form system outputs.
+ def outputs
+ g.sources.compact_map { |id| g[id] unless id == Mute.id }
+ end
+end
diff --git a/drivers/place/router/signal_graph/edge.cr b/drivers/place/router/signal_graph/edge.cr
new file mode 100644
index 00000000000..cceb5e67a30
--- /dev/null
+++ b/drivers/place/router/signal_graph/edge.cr
@@ -0,0 +1,39 @@
+require "./mod"
+
+class Place::Router::SignalGraph
+ module Edge
+ alias Label = Static | Active
+
+ class Static
+ class_getter instance : self { new }
+
+ protected def initialize; end
+ end
+
+ record Active, mod : Mod, func : Func::Type
+
+ module Func
+ record Mute,
+ state : Bool,
+ index : Int32 | String = 0
+
+ record Select,
+ input : Int32 | String
+
+ record Switch,
+ input : Int32 | String,
+ output : Int32 | String,
+ layer : String
+
+ # NOTE: currently not supported. Requires interaction via
+ # Proxy::RemoteDriver to support dynamic method execution.
+ # record Custom,
+ # func : String,
+ # args : Hash(String, JSON::Any::Type)
+
+ macro finished
+ alias Type = {{ @type.constants.join(" | ").id }}
+ end
+ end
+ end
+end
diff --git a/drivers/place/router/signal_graph/mod.cr b/drivers/place/router/signal_graph/mod.cr
new file mode 100644
index 00000000000..488f5434359
--- /dev/null
+++ b/drivers/place/router/signal_graph/mod.cr
@@ -0,0 +1,60 @@
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/switchable"
+
+class Place::Router::SignalGraph
+ # Reference to a PlaceOS module that provides IO nodes within the graph.
+ class Mod
+ getter sys : String
+ getter name : String
+ getter idx : Int32
+
+ getter id : String
+
+ def initialize(@sys, @name, @idx)
+ id = PlaceOS::Driver::Proxy::System.module_id? sys, name, idx
+ @id = id || raise %("#{name}/#{idx}" does not exist in #{sys})
+ end
+
+ def metadata
+ if meta = PlaceOS::Driver::Proxy::System.driver_metadata?(id)
+ meta
+ else
+ # TODO:: warn about offline device
+ PlaceOS::Driver::DriverModel::Metadata.new(interface: {} of String => Hash(String, JSON::Any))
+ end
+ rescue error
+ raise RuntimeError.new("failed to obtain metadata for #{id}", cause: error)
+ end
+
+ # FIXME: drop if / after renaming InputSelection -> Selectable
+ def selectable?
+ interface = {{PlaceOS::Driver::Interface::InputSelection.name(generic_args: false).stringify}}
+ interface.in? metadata.implements
+ end
+
+ macro finished
+ {% for interface in PlaceOS::Driver::Interface.constants %}
+ {% type = PlaceOS::Driver::Interface.constant(interface) %}
+ def {{interface.underscore}}?
+ {{type.name(generic_args: false).stringify}}.in? metadata.implements
+ end
+ {% end %}
+ end
+
+ def_equals_and_hash @id
+
+ def to_s(io)
+ io << sys << '/' << name << '_' << idx
+ end
+
+ def self.parse?(ref)
+ if m = ref.match /^(.+)\/(.+)\_(\d+)$/
+ sys = m[1]
+ mod = m[2]
+ idx = m[3].to_i
+ new sys, mod, idx
+ end
+ end
+ end
+end
diff --git a/drivers/place/router/signal_graph/node.cr b/drivers/place/router/signal_graph/node.cr
new file mode 100644
index 00000000000..a8da7feab5a
--- /dev/null
+++ b/drivers/place/router/signal_graph/node.cr
@@ -0,0 +1,260 @@
+require "json"
+require "./mod"
+require "./watchable"
+
+class Place::Router::SignalGraph
+ module Node
+ # Metadata tracked against each signal node.
+ class Label
+ include JSON::Serializable
+ include Watchable
+
+ def initialize(@ref)
+ end
+
+ def to_s(io)
+ io << ref
+ end
+
+ # The `Node::Ref` used when creating this node.
+ getter ref : Ref
+
+ # `Ref` of the upstream signal source currently feeding this node.
+ property source : Ref? = nil
+
+ # Locked state. When `true` changes to signal routes that transit this
+ # are blocked.
+ property locked : Bool = false
+
+ # Additional metadata passed in from settings or dynamically applied.
+ # Information here is propogated to exposed state keys. May be used for
+ # any information needed by a user interface or external system.
+ @[JSON::Field(ignore: true)]
+ property meta : Hash(String, JSON::Any) { Hash(String, JSON::Any).new }
+
+ delegate :[], :[]?, to: meta
+
+ # Sets a metadata property of `self`.
+ def []=(key, value : JSON::Any)
+ meta[key] = value
+ self.notify
+ value
+ end
+
+ def []=(key, value)
+ self[key] = JSON::Any.new value
+ end
+
+ def []=(key, value : Int)
+ self[key] = JSON::Any.new value.to_i64
+ end
+
+ def []=(key, value : Float)
+ self[key] = JSON::Any.new value.to_f64
+ end
+
+ def []=(key, value : Array)
+ self[key] = JSON::Any.new value.map { |x| JSON::Any.new x }
+ end
+
+ def []=(key, value : Hash)
+ self[key] = JSON::Any.new value.transform_values { |x| JSON::Any.new x }
+ end
+
+ protected def on_to_json(json)
+ @meta.try &.each do |key, value|
+ json.field(key) { value.to_json(json) }
+ end
+ end
+ end
+
+ # Base structure for referring to a node within the graph.
+ abstract struct Ref
+ # Resolves a string-based node *key* to a fully-qualified reference.
+ #
+ # If a system component is not present within *key*, this is resolved
+ # within the context of *sys*. For example:
+ #
+ # Ref.resolve("Display_1:hdmi", "sys-abc123")
+ # # => DeviceInput(sys: "sys-abc123", mod: {"Display", 1}, input: "hdmi")
+ #
+ def self.resolve?(key : String, sys = nil)
+ ref = key.includes?('/') ? key : "#{sys}/#{key}"
+ {% begin %}
+ {% for type in @type.subclasses %}
+ {{type}}.parse?(ref) || \
+ {% end %}
+ nil
+ {% end %}
+ end
+
+ # Node identifier for usage as the graph ID.
+ def id
+ self.class.hash ^ self.hash
+ end
+
+ abstract def mod
+
+ DEFAULT_LAYER = "all"
+
+ def layer
+ DEFAULT_LAYER
+ end
+
+ def ==(other : Ref)
+ id == other.id
+ end
+
+ def local(sys : String)
+ to_s.lchop "#{sys}/"
+ end
+
+ def to_json(json)
+ json.string to_s
+ end
+
+ private module ClassMethods(T)
+ # Parses a string-based *ref* to {{@type}}.
+ abstract def parse?(ref : String) : T?
+ end
+
+ macro inherited
+ extend ClassMethods(self)
+ end
+ end
+
+ # Reference to the default / central node for a device.
+ #
+ # These take the cannonical string form of:
+ #
+ # sys-abc123/Display_1
+ # │ │ │
+ # │ │ └module index
+ # │ └module name
+ # └system
+ #
+ struct Device < Ref
+ getter mod : Mod
+
+ def initialize(sys, name, idx)
+ @mod = Mod.new sys, name, idx
+ end
+
+ def initialize(@mod)
+ end
+
+ def to_s(io)
+ io << mod
+ end
+
+ def self.parse?(ref) : self?
+ if mod = Mod.parse? ref
+ new mod
+ end
+ end
+ end
+
+ # Reference to a signal output from a device.
+ #
+ # These take the cannonical string form of:
+ #
+ # sys-abc123/Switcher_1.1!video
+ # │ │ │ │ │_layer
+ # │ │ │ └output
+ # │ │ └module index
+ # │ └module namme
+ # └system
+ #
+ struct DeviceOutput < Ref
+ getter mod : Mod
+ getter output : Int32 | String
+ getter layer : String
+
+ def initialize(sys, name, idx, @output, layer)
+ @mod = Mod.new sys, name, idx
+ @layer = layer.try(&.downcase) || DEFAULT_LAYER
+ end
+
+ def initialize(@mod, @output)
+ @layer = DEFAULT_LAYER
+ end
+
+ def to_s(io)
+ io << mod << '.' << output
+ io << '!' << @layer unless @layer == DEFAULT_LAYER
+ end
+
+ def self.parse?(ref) : self?
+ # as match == "_123."
+ mod_name, match, outp = ref.rpartition(/_\d+\./)
+ mod_name = "#{mod_name}_#{match[1..-2]}" if !match.empty?
+
+ if mod = Mod.parse? mod_name
+ output = outp.to_i? || outp
+ new mod, output
+ end
+ end
+ end
+
+ # Reference to a signal input to a device.
+ #
+ # These take the cannonical string form of:
+ #
+ # sys-abc123/Display_1:hdmi
+ # │ │ │ │
+ # │ │ │ └input
+ # │ │ └module index
+ # │ └module namme
+ # └system
+ #
+ struct DeviceInput < Ref
+ getter mod : Mod
+ getter input : Int32 | String
+
+ def initialize(sys, name, idx, @input)
+ @mod = Mod.new sys, name, idx
+ end
+
+ def initialize(@mod, @input)
+ end
+
+ def to_s(io)
+ io << mod << ':' << input
+ end
+
+ def self.parse?(ref) : self?
+ m, _, i = ref.rpartition ':'
+ if mod = Mod.parse? m
+ input = i.to_i? || i
+ new mod, input
+ end
+ end
+ end
+
+ # Virtual node representing (any) mute source.
+ #
+ # This may be refernced simply as `MUTE`.
+ struct Mute < Ref
+ class_getter instance : self { new }
+
+ protected def initialize
+ end
+
+ def id
+ 0_u64
+ end
+
+ def mod
+ end
+
+ def self.parse?(ref) : self?
+ # See Ref#resolve? on line 82 of this file for what is passed here
+ instance if ref.upcase.ends_with?("MUTE")
+ end
+
+ def to_s(io)
+ io << "MUTE"
+ end
+ end
+ end
+end
diff --git a/drivers/place/router/signal_graph/watchable.cr b/drivers/place/router/signal_graph/watchable.cr
new file mode 100644
index 00000000000..d862b5c05d7
--- /dev/null
+++ b/drivers/place/router/signal_graph/watchable.cr
@@ -0,0 +1,29 @@
+class Place::Router::SignalGraph
+ module Watchable
+ # Subscribe to updates.
+ def watch(initial = true, &handler : self ->) : Nil
+ subscribers << handler
+ handler.call(self) if initial
+ end
+
+ # Notify subscribers with current state.
+ def notify : Nil
+ @subscribers.try &.each &.call(self)
+ end
+
+ macro included
+ @[JSON::Field(ignore: true)]
+ private getter subscribers : Array(self ->) { Array(self ->).new }
+
+ {% verbatim do %}
+ macro finished
+ {% for method in @type.methods.select &.name.ends_with? '=' %}
+ def {{method.name}}({{method.args.splat}})
+ previous_def.tap { notify }
+ end
+ {% end %}
+ end
+ {% end %}
+ end
+ end
+end
diff --git a/drivers/place/router/signal_graph_spec.cr b/drivers/place/router/signal_graph_spec.cr
new file mode 100644
index 00000000000..33d73a0e4dd
--- /dev/null
+++ b/drivers/place/router/signal_graph_spec.cr
@@ -0,0 +1,251 @@
+abstract class PlaceOS::Driver; end
+
+require "spec"
+require "placeos-driver/driver_model"
+require "./signal_graph"
+
+alias SigGraph = Place::Router::SignalGraph
+
+abstract class PlaceOS::Driver
+ module Interface
+ module Switchable; end
+
+ module Selectable; end
+
+ module Muteable; end
+
+ # TODO: expand interfaces in `placeos-driver` to cover this
+ module InputMuteable; end
+ end
+
+ class Proxy::System
+ def self.module_id?(sys, name, idx) : String?
+ mock_id = {sys, name, idx}.hash
+ "mod-#{mock_id}"
+ end
+
+ def self.driver_metadata?(id) : DriverModel::Metadata?
+ m = DriverModel::Metadata.new
+ m.implements << {{Interface::Switchable.name(generic_args: false).stringify}}
+ m.implements << {{Interface::Selectable.name(generic_args: false).stringify}}
+ m.implements << {{Interface::Muteable.name(generic_args: false).stringify}}
+ m
+ end
+ end
+end
+
+# Settings:
+#
+# connections = {
+# Display_1: {
+# hdmi: "15.02_Switcher_1.1"
+# },
+# 15.02_Switcher_1: ["*foo", "*bar"],
+# Display_2: {
+# hdmi: "*baz"
+# }
+# }
+#
+# inputs = {
+# foo: "laptop",
+# bar: "pc"
+# }
+
+# Set of inputs in use
+# NOTE: alias are only used in the local system, no impact here
+nodes = [
+ SigGraph::Input.new("sys-123", "Display", 1, "hdmi"),
+ SigGraph::Input.new("sys-123", "Display", 2, "hdmi"),
+ SigGraph::Input.new("sys-123", "15.02_Switcher", 1, 1),
+ SigGraph::Input.new("sys-123", "15.02_Switcher", 1, 2),
+ SigGraph::Output.new("sys-123", "15.02_Switcher", 1, 1, "all"),
+ SigGraph::Device.new("sys-123", "Display", 1),
+ SigGraph::Device.new("sys-123", "Display", 2),
+ SigGraph::Device.new("sys-123", "15.02_Switcher", 1),
+]
+
+connections = [
+ {SigGraph::Output.new("sys-123", "15.02_Switcher", 1, 1, "all"), SigGraph::Input.new("sys-123", "Display", 1, "hdmi")},
+]
+
+inputs = {
+ foo: SigGraph::Input.new("sys-123", "15.02_Switcher", 1, 1),
+ bar: SigGraph::Input.new("sys-123", "15.02_Switcher", 1, 2),
+ baz: SigGraph::Input.new("sys-123", "Display", 2, "hdmi"),
+}
+
+outputs = {
+ display: SigGraph::Device.new("sys-123", "Display", 1),
+ display2: SigGraph::Device.new("sys-123", "Display", 2),
+}
+
+describe SigGraph do
+ describe ".build" do
+ it "builds from config" do
+ SigGraph.build nodes, connections
+ end
+ end
+
+ describe "#[]" do
+ n = SigGraph::Device.new("sys-123", "Display", 1)
+ g = SigGraph.build [n], [] of {SigGraph::Node::Ref, SigGraph::Node::Ref}
+
+ it "provides node details from a Ref" do
+ g[n].should be_a(SigGraph::Node::Label)
+ end
+
+ it "provides nodes details from an ID" do
+ g[n.id].should be_a(SigGraph::Node::Label)
+ end
+
+ it "provides the same label for both accessors" do
+ g[n].should eq(g[n.id])
+ end
+ end
+
+ describe "#route" do
+ g = SigGraph.build nodes, connections
+
+ it "returns nil if no path exists" do
+ path = g.route inputs[:foo], outputs[:display2]
+ path.should be_nil
+ end
+
+ it "provides the path connects a signal source to a destination" do
+ source = inputs[:foo]
+ dest = outputs[:display]
+
+ path = g.route source, dest
+ path = path.not_nil!
+
+ path.each_with_index do |(node, edge, next_node), step|
+ case step
+ when 0
+ node.should eq g[source]
+ edge = edge.as SigGraph::Edge::Active
+ edge.mod.name.should eq "15.02_Switcher"
+ edge.func.should eq SigGraph::Edge::Func::Switch.new 1, 1, "all"
+ when 1
+ edge.should be_a SigGraph::Edge::Static
+ next_node.should eq g[SigGraph::Input.new("sys-123", "Display", 1, "hdmi")]
+ when 2
+ edge = edge.as SigGraph::Edge::Active
+ edge.mod.name.should eq "Display"
+ edge.mod.idx.should eq 1
+ edge.func.should eq SigGraph::Edge::Func::Select.new "hdmi"
+ when 4
+ fail "path iterator did not terminate"
+ end
+ end
+ end
+
+ it "provides mute activation on an output device" do
+ source = SigGraph::Mute
+ dest = outputs[:display]
+
+ path = g.route source, dest
+ path = path.not_nil!
+
+ node, edge, next_node = path.first
+ node.should eq g[source]
+ edge = edge.as SigGraph::Edge::Active
+ edge.mod.name.should eq "Display"
+ edge.func.should eq SigGraph::Edge::Func::Mute.new true
+ next_node.should eq g[dest]
+ end
+
+ it "provide mute activate on an intermediate switcher" do
+ source = SigGraph::Mute
+ dest = SigGraph::Output.new("sys-123", "15.02_Switcher", 1, 1, "all")
+
+ path = g.route source, dest
+ path = path.not_nil!
+
+ node, edge, next_node = path.first
+ node.should eq g[source]
+ edge = edge.as SigGraph::Edge::Active
+ edge.mod.name.should eq "15.02_Switcher"
+ edge.func.should eq SigGraph::Edge::Func::Mute.new true, 1
+ next_node.should eq g[dest]
+ end
+ end
+
+ describe "#input?" do
+ g = SigGraph.build nodes, connections
+
+ it "returns true if the node is an input" do
+ g.input?(inputs.values.sample).should be_true
+ end
+
+ it "returns false otherwise" do
+ g.input?(outputs.values.sample).should be_false
+ end
+ end
+
+ describe "#inputs" do
+ it "provides a list of input nodes within the graph" do
+ g = SigGraph.build nodes, connections
+ expected = inputs.values
+ discovered = g.inputs.map(&.ref).to_a
+ expected.each { |input| discovered.should contain input }
+ end
+ end
+
+ describe "#inputs(destination)" do
+ it "provides a list of inputs nodes accessible to an output" do
+ g = SigGraph.build nodes, connections
+ reachable = g.inputs(outputs[:display]).map(&.ref).to_a
+ expected = {inputs[:foo], inputs[:bar]}
+ expected.each { |input| reachable.should contain input }
+ end
+ end
+
+ describe "#output?" do
+ g = SigGraph.build nodes, connections
+
+ it "returns true if the node is an output" do
+ g.output?(outputs.values.sample).should be_true
+ end
+
+ it "returns false otherwise" do
+ g.output?(inputs.values.sample).should be_false
+ end
+ end
+
+ describe "#outputs" do
+ it "list the output nodes present in the graph" do
+ g = SigGraph.build nodes, connections
+ expected = outputs.values
+ discovered = g.outputs.map(&.ref).to_a
+ expected.each { |output| discovered.should contain output }
+ end
+ end
+
+ pending "#to_json" do
+ end
+ pending ".from_json" do
+ end
+
+ pending "#merge" do
+ end
+
+ describe SigGraph::Node::Label do
+ it "supports change notification" do
+ n = SigGraph::Device.new("sys-123", "Display", 1)
+ g = SigGraph.build [n], [] of {SigGraph::Node::Ref, SigGraph::Node::Ref}
+
+ x = 0
+
+ g[n].watch(initial: false) { x += 1 }
+
+ x.should eq 0
+ g[n].notify
+ x.should eq 1
+
+ g[n].locked.should be_false
+ g[n].locked = true
+ x.should eq 2
+ g[n].locked.should be_true
+ end
+ end
+end
diff --git a/drivers/place/router_spec.cr b/drivers/place/router_spec.cr
new file mode 100644
index 00000000000..08a49570987
--- /dev/null
+++ b/drivers/place/router_spec.cr
@@ -0,0 +1,102 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/switchable"
+
+# :nodoc:
+class RouterDisplay < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Powerable
+ include PlaceOS::Driver::Interface::Muteable
+
+ enum Inputs
+ HDMI
+ HDMI2
+ end
+
+ include PlaceOS::Driver::Interface::InputSelection(Inputs)
+
+ # implement the abstract methods required by the interfaces
+ def power(state : Bool)
+ self[:power] = state
+ end
+
+ def switch_to(input : Inputs)
+ mute(false)
+ self[:input] = input
+ end
+
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ self[:mute] = state
+ end
+end
+
+# :nodoc:
+class RouterSwitcher < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Switchable(Int32, Int32)
+
+ def switch_to(input : Int32)
+ self[:input] = input
+ end
+
+ def switch(map : Hash(Input, Array(Output)), layer : SwitchLayer? = nil)
+ self["last_switched_layer"] = layer.to_s.downcase
+ map.each do |(input, outputs)|
+ outputs.each do |output|
+ self["output#{output}"] = input
+ end
+ end
+ end
+end
+
+DriverSpecs.mock_driver "Place::RouterTest" do
+ system({
+ Display: {RouterDisplay},
+ Switcher: {RouterSwitcher},
+ })
+
+ settings({
+ connections: {
+ Display_1: {
+ hdmi: "Switcher_1.1!video",
+ },
+ Switcher_1: ["*Foo", "*Bar"],
+ "*FloorBox": "Switcher_1.2",
+ },
+ })
+
+ # Give the settings time to load
+ sleep 2
+
+ status["inputs"].as_a.should contain("Foo")
+ status["inputs"].as_a.should contain("Bar")
+ status["outputs"].as_a.should contain("Display_1")
+ status["outputs"].as_a.should contain("FloorBox")
+ status["output/Display_1"]["inputs"].should eq(["Foo", "Bar"])
+
+ exec(:route_signal, "Foo", "Display_1").get
+ status["output/Display_1"]["source"].should eq(status["input/Foo"]["ref"])
+ system(:Switcher_1)["last_switched_layer"].should eq("video")
+
+ expect_raises(
+ PlaceOS::Driver::RemoteException,
+ %(unknown signal node "Baz" - did you mean "Bar"?)
+ ) do
+ exec(:route_signal, "Foo", "Baz").get
+ end
+
+ # Ensure previous status persists settings reloads for continuing nodes
+ settings({
+ connections: {
+ Display_1: {
+ hdmi: "Switcher_1.1",
+ },
+ Switcher_1: ["*Foo", "*Bar"],
+ },
+ })
+ sleep 2
+ status["output/Display_1"]["source"].should eq(status["input/Foo"]["ref"])
+end
diff --git a/drivers/place/smtp.cr b/drivers/place/smtp.cr
new file mode 100644
index 00000000000..6375355f4d4
--- /dev/null
+++ b/drivers/place/smtp.cr
@@ -0,0 +1,161 @@
+require "qr-code"
+require "qr-code/export/png"
+require "base64"
+require "email"
+require "uri"
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+
+class Place::Smtp < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::Mailer
+
+ descriptive_name "SMTP Mailer"
+ generic_name :Mailer
+ uri_base "https://smtp.host.com"
+ description %(sends emails via SMTP)
+
+ default_settings({
+ sender: "support@place.tech",
+ # host: "smtp.host",
+ # port: 587,
+ tls_mode: EMail::Client::TLSMode::STARTTLS.to_s,
+ ssl_verify_ignore: false,
+ username: "", # Username/Password for SMTP servers with basic authorization
+ password: "",
+
+ email_templates: {visitor: {checkin: {
+ subject: "%{name} has arrived",
+ text: "for your meeting at %{time}",
+ }}},
+ })
+
+ private def smtp_client : EMail::Client
+ @smtp_client ||= new_smtp_client
+ end
+
+ @smtp_client : EMail::Client?
+ @sender : String = "support@place.tech"
+ @username : String = ""
+ @password : String = ""
+ @host : String = "smtp.host"
+ @port : Int32 = 587
+ @tls_mode : EMail::Client::TLSMode = EMail::Client::TLSMode::STARTTLS
+ @send_lock : Mutex = Mutex.new
+ @ssl_verify_ignore : Bool = false
+
+ def on_update
+ defaults = URI.parse(config.uri.not_nil!)
+ tls_mode = if scheme = defaults.scheme
+ scheme.ends_with?('s') ? EMail::Client::TLSMode::SMTPS : EMail::Client::TLSMode::STARTTLS
+ else
+ EMail::Client::TLSMode::STARTTLS
+ end
+ port = defaults.port || 587
+ host = defaults.host || "smtp.host"
+
+ @username = setting?(String, :username) || ""
+ @password = setting?(String, :password) || ""
+ @sender = setting?(String, :sender) || "support@place.tech"
+ @host = setting?(String, :host) || host
+ @port = setting?(Int32, :port) || port
+ @tls_mode = setting?(EMail::Client::TLSMode, :tls_mode) || tls_mode
+ @ssl_verify_ignore = setting?(Bool, :ssl_verify_ignore) || false
+
+ @smtp_client = new_smtp_client
+
+ @templates = setting?(Templates, :email_templates) || Templates.new
+ end
+
+ # Create and configure an SMTP client
+ private def new_smtp_client
+ email_config = EMail::Client::Config.new(@host, @port)
+ email_config.log = logger
+ email_config.client_name = "PlaceOS"
+
+ unless @username.empty? || @password.empty?
+ email_config.use_auth(@username, @password)
+ end
+
+ email_config.use_tls(@tls_mode)
+ email_config.tls_context.verify_mode = OpenSSL::SSL::VerifyMode::None if @ssl_verify_ignore
+
+ EMail::Client.new(email_config)
+ end
+
+ def generate_svg_qrcode(text : String) : String
+ QRCode.new(text).as_svg
+ end
+
+ def generate_png_qrcode(text : String, size : Int32 = 128) : String
+ Base64.strict_encode QRCode.new(text).as_png(size: size)
+ end
+
+ def send_mail(
+ to : String | Array(String),
+ subject : String,
+ message_plaintext : String? = nil,
+ message_html : String? = nil,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ ) : Bool
+ to = {to} unless to.is_a?(Array)
+
+ from = {from} unless from.nil? || from.is_a?(Array)
+ cc = {cc} unless cc.nil? || cc.is_a?(Array)
+ bcc = {bcc} unless bcc.nil? || bcc.is_a?(Array)
+ reply_to = {reply_to} unless reply_to.nil? || reply_to.is_a?(Array)
+
+ message = EMail::Message.new
+
+ message.subject(subject)
+
+ message.sender(@sender)
+
+ if from.nil? || from.empty?
+ message.from(@sender)
+ else
+ from.each { |_from| message.from(_from) }
+ end
+
+ to.each { |_to| message.to(_to) }
+ bcc.each { |_bcc| message.bcc(_bcc) }
+ cc.each { |_cc| message.cc(_cc) }
+
+ if reply_to
+ reply_to.each { |_reply| message.reply_to(_reply) }
+ end
+
+ message.message(message_plaintext.as(String)) unless message_plaintext.presence.nil?
+ message.message_html(message_html.as(String)) unless message_html.presence.nil?
+
+ # Traverse all attachments
+ {resource_attachments, attachments}.map(&.each).each.flatten.each do |attachment|
+ # Base64 decode to memory, then attach to email
+ attachment_io = IO::Memory.new
+ Base64.decode(attachment[:content], attachment_io)
+ attachment_io.rewind
+
+ case attachment
+ in Attachment
+ message.attach(io: attachment_io, file_name: attachment[:file_name])
+ in ResourceAttachment
+ message.message_resource(io: attachment_io, file_name: attachment[:file_name], cid: attachment[:content_id])
+ end
+ end
+
+ sent = false
+
+ # Ensure only a single send at a time
+ @send_lock.synchronize do
+ smtp_client.start do
+ sent = send(message)
+ end
+ end
+
+ sent
+ end
+end
diff --git a/drivers/place/smtp_spec.cr b/drivers/place/smtp_spec.cr
new file mode 100644
index 00000000000..989f6ad5218
--- /dev/null
+++ b/drivers/place/smtp_spec.cr
@@ -0,0 +1,41 @@
+require "placeos-driver/spec"
+require "email"
+
+# for local testing use: http://nilhcem.com/FakeSMTP/download.html
+
+DriverSpecs.mock_driver "Place::Smtp" do
+ settings({
+ sender: "support@place.tech",
+ host: ENV["PLACE_SMTP_HOST"]? || "localhost",
+ port: ENV["PLACE_SMTP_PORT"]?.try(&.to_i) || 25,
+ username: ENV["PLACE_SMTP_USER"]? || "", # Username/Password for SMTP servers with basic authorization
+ password: ENV["PLACE_SMTP_PASS"]? || "",
+ tls_mode: ENV["PLACE_SMTP_MODE"]? || "none",
+
+ email_templates: {visitor: {checkin: {
+ subject: "%{name} has arrived",
+ text: "for your meeting at %{time}",
+ }}},
+ })
+
+ response = exec(
+ :send_mail,
+ subject: "Test Email",
+ to: ENV["PLACE_TEST_EMAIL"]? || "support@place.tech",
+ message_plaintext: "Hello!",
+ ).get
+
+ response.should be_true
+
+ response = exec(
+ :send_template,
+ to: "steve@place.tech",
+ template: {"visitor", "checkin"},
+ args: {
+ name: "Bob",
+ time: "1:30pm",
+ }
+ ).get
+
+ response.should be_true
+end
diff --git a/drivers/place/spec_helper.cr b/drivers/place/spec_helper.cr
new file mode 100644
index 00000000000..ac332cfa843
--- /dev/null
+++ b/drivers/place/spec_helper.cr
@@ -0,0 +1,8 @@
+require "placeos-driver"
+
+class Place::SpecHelper < PlaceOS::Driver
+ # This method will be exposed on the module
+ def implemented_in_driver
+ "woot!"
+ end
+end
diff --git a/drivers/place/staff_api.cr b/drivers/place/staff_api.cr
new file mode 100644
index 00000000000..6b3cdd43317
--- /dev/null
+++ b/drivers/place/staff_api.cr
@@ -0,0 +1,1051 @@
+require "json-schema"
+require "placeos-driver"
+require "oauth2"
+require "placeos"
+require "link-header"
+require "simple_retry"
+require "place_calendar"
+require "./booking_model"
+
+# This comment is to force a recompile of the driver with updated models
+
+class Place::StaffAPI < PlaceOS::Driver
+ descriptive_name "PlaceOS Staff API"
+ generic_name :StaffAPI
+ description %(helpers for requesting data held in the staff API.)
+
+ # The PlaceOS API
+ uri_base "https://staff"
+
+ default_settings({
+ # PlaceOS X-API-key, for simpler authentication
+ api_key: "",
+ disable_event_notify: false,
+ query_limit: 100,
+ period_end_default_in_min: 60,
+ })
+
+ @place_domain : URI = URI.parse("https://staff")
+ @host_header : String = ""
+ @api_key : String = ""
+
+ @authority_id : String = ""
+ @event_monitoring : PlaceOS::Driver::Subscriptions::ChannelSubscription? = nil
+ @notify_count : UInt64 = 0_u64
+ @notify_fails : UInt64 = 0_u64
+
+ @query_limit : Int32 = 100
+ @period_end_default_in_min : Int32? = nil
+
+ def on_update
+ # x-api-key is the preferred method for API access
+ @api_key = setting(String, :api_key) || ""
+ @access_expires = 30.years.from_now if @api_key.presence
+
+ @place_domain = URI.parse(config.uri.not_nil!)
+ @host_header = setting?(String, :host_header) || @place_domain.host.not_nil!
+
+ @placeos_client = nil
+ @query_limit = setting?(Int32, :query_limit) || 100
+ @period_end_default_in_min = setting?(Int32, :period_end_default_in_min)
+
+ # skip if not going to work
+ return unless @api_key.presence
+ return if setting?(Bool, :disable_event_notify)
+ schedule.clear
+ schedule.every(1.hour + rand(300).seconds) { lookup_authority_id }
+ schedule.in(1.second) { lookup_authority_id }
+ end
+
+ def lookup_authority_id(retry : Int32 = 0)
+ response = get("/auth/authority")
+ raise "unexpected response for /auth/authority: #{response.status_code}\n#{response.body}" unless response.success?
+
+ old_id = @authority_id
+ @authority_id = NamedTuple(id: String).from_json(response.body)[:id]
+ monitor_event_changes unless old_id == @authority_id
+ @authority_id
+ rescue error
+ logger.warn(exception: error) { "failed to lookup authority id" }
+ sleep rand(3).seconds
+ retry += 1
+ return if retry == 10
+ spawn { lookup_authority_id(retry) }
+ end
+
+ protected def monitor_event_changes
+ if monitor = @event_monitoring
+ subscriptions.unsubscribe(monitor)
+ @event_monitoring = nil
+ end
+
+ @event_monitoring = monitor("#{@authority_id}/bookings/event") { |_subscription, payload| push_event_occured(payload) }
+ end
+
+ struct PushEvent
+ include JSON::Serializable
+
+ getter event_id : String
+ getter change : String
+ getter system_id : String
+ getter event : JSON::Any?
+ end
+
+ protected def push_event_occured(payload)
+ @notify_count += 1
+ logger.debug { "new push event: #{payload}" }
+
+ event = PushEvent.from_json payload
+
+ response = post("/api/staff/v1/events/notify/#{event.change}/#{event.system_id}/#{event.event_id}",
+ body: event.event.to_json,
+ headers: authentication(HTTP::Headers{
+ "Content-Type" => "application/json",
+ })
+ )
+ if !response.success?
+ @notify_fails += 1
+ raise "unexpected response processing push event: #{response.status_code}\n#{payload}"
+ end
+ end
+
+ def push_event_status
+ {
+ authority_id: @authority_id,
+ monitoring: !!@event_monitoring,
+ events: @notify_count,
+ failures: @notify_fails,
+ }
+ end
+
+ def auth_authority
+ response = get("/auth/authority")
+ raise "unexpected response for /auth/authority: #{response.status_code}\n#{response.body}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ def domain : String
+ @place_domain.host.as(String)
+ end
+
+ def get_system(id : String, complete : Bool = false)
+ response = get("/api/engine/v2/systems/#{id}?complete=#{complete}", headers: authentication)
+ raise "unexpected response for system id #{id}: #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing system #{id}:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ def systems(
+ q : String? = nil,
+ zone_id : String? = nil,
+ capacity : Int32? = nil,
+ bookable : Bool? = nil,
+ features : String? = nil,
+ limit : Int32 = 1000,
+ offset : Int32 = 0,
+ )
+ placeos_client.systems.search(
+ q: q,
+ limit: limit,
+ offset: offset,
+ zone_id: zone_id,
+ capacity: capacity,
+ bookable: bookable,
+ features: features
+ )
+ end
+
+ record Setting, keys : Array(String), settings_string : String? do
+ include JSON::Serializable
+ end
+
+ @[Security(Level::Support)]
+ def system_settings(id : String, key : String)
+ response = get("/api/engine/v2/systems/#{id}/settings", headers: authentication)
+ raise "settings request failed for #{id}: #{response.status_code}" unless response.success?
+ setting = Array(Setting).from_json(response.body).select { |sub_setting|
+ sub_setting.settings_string && sub_setting.keys.includes?(key)
+ }.last?
+ return nil unless setting
+ YAML.parse(setting.settings_string.as(String))[key]
+ end
+
+ def systems_in_building(zone_id : String, ids_only : Bool = true)
+ levels = zones(parent: zone_id, tags: ["level"])
+ if ids_only
+ hash = {} of String => Array(String)
+ levels.each { |level| hash[level.id] = systems(zone_id: level.id).map(&.id) }
+ else
+ hash = {} of String => Array(::PlaceOS::Client::API::Models::System)
+ levels.each { |level| hash[level.id] = systems(zone_id: level.id) }
+ end
+ hash
+ end
+
+ # Staff details returns the information from AD
+ def staff_details(email : String)
+ response = get("/api/staff/v1/people/#{email}", headers: authentication)
+ raise "unexpected response for staff #{email}: #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing staff #{email}:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # ===================================
+ # Modules
+ # ===================================
+
+ @[Security(Level::Administrator)]
+ def start_or_stop_module(module_id : String, start : Bool)
+ response = post("/api/engine/v2/modules/#{module_id}/#{start ? "start" : "stop"}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # ===================================
+ # User details
+ # ===================================
+ def user(id : String)
+ placeos_client.users.fetch(id)
+ end
+
+ @[Security(Level::Support)]
+ def create_user(body_json : String)
+ response = post("/api/engine/v2/users", body: body_json, headers: authentication(HTTP::Headers{
+ "Content-Type" => "application/json",
+ }))
+ raise "failed to create user: #{response.status_code}" unless response.success?
+ PlaceOS::Client::API::Models::User.from_json response.body
+ end
+
+ @[Security(Level::Support)]
+ def update_user(id : String, body_json : String) : Nil
+ response = patch("/api/engine/v2/users/#{id}", body: body_json, headers: authentication(HTTP::Headers{
+ "Content-Type" => "application/json",
+ }))
+
+ raise "failed to update user #{id}: #{response.status_code}" unless response.success?
+ end
+
+ @[Security(Level::Support)]
+ def delete_user(id : String, force_removal : Bool = false) : Nil
+ response = delete("/api/engine/v2/users/#{id}?force_removal=#{force_removal}", headers: authentication)
+ raise "failed to delete user #{id}: #{response.status_code}" unless response.success?
+ end
+
+ @[Security(Level::Support)]
+ def revive_user(id : String) : Nil
+ response = post("/api/engine/v2/users/#{id}/revive", headers: authentication)
+ raise "failed to revive user #{id}: #{response.status_code}" unless response.success?
+ end
+
+ @[Security(Level::Support)]
+ def resource_token
+ response = post("/api/engine/v2/users/resource_token", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # NOTE:: this function requires "users" scope to be specified explicity for access
+ @[Security(Level::Administrator)]
+ def user_resource_token
+ response = post("/api/engine/v2/users/#{invoked_by_user_id}/resource_token", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ @[Security(Level::Support)]
+ def query_users(
+ q : String? = nil,
+ limit : Int32 = 20,
+ offset : Int32 = 0,
+ authority_id : String? = nil,
+ include_deleted : Bool = false,
+ )
+ placeos_client.users.search(q: q, limit: limit, offset: offset, authority_id: authority_id, include_deleted: include_deleted)
+ end
+
+ # ===================================
+ # WebRTC Helper functions
+ # ===================================
+
+ @[Security(Level::Support)]
+ def transfer_user(user_id : String, session_id : String, payload : JSON::Any)
+ status = 200
+ payload_str = payload.to_json
+ SimpleRetry.try_to(
+ max_attempts: 5,
+ base_interval: 1.second,
+ max_interval: 10.seconds,
+ ) do
+ response = post("/api/engine/v2/webrtc/transfer/#{user_id}/#{session_id}", headers: authentication, body: payload_str)
+ # 200 == success
+ # 428 == client is not connected to received the message, should be retried
+ status = response.status_code
+ raise "client not yet connected" unless response.success?
+ end
+ status
+ end
+
+ @[Security(Level::Support)]
+ def kick_user(user_id : String, session_id : String, reason : String)
+ response = post("/api/engine/v2/webrtc/kick/#{user_id}/#{session_id}", headers: authentication, body: {
+ reason: reason,
+ }.to_json)
+ response.status_code
+ end
+
+ def chat_members(session_id : String) : Array(String)
+ SimpleRetry.try_to(
+ max_attempts: 3,
+ base_interval: 1.second,
+ max_interval: 5.seconds,
+ ) do
+ response = get("/api/engine/v2/webrtc/members/#{session_id}", headers: authentication)
+ raise "webrtc service possibly unavailable" unless response.success?
+ Array(String).from_json(response.not_nil!.body)
+ end
+ end
+
+ # ===================================
+ # Uploads
+ # ===================================
+
+ def uploads(search : String? = nil, tags : Array(String) = [] of String, limit : Int32? = nil, offset : Int32? = nil)
+ tags_param = tags.join(",")
+
+ params = URI::Params.build do |form|
+ form.add("file_search", search.to_s) if search.presence
+ form.add("tags", tags_param) if tags_param.presence
+ form.add("limit", limit.to_s) if limit
+ form.add("offset", offset.to_s) if offset
+ end
+
+ response = get("/api/engine/v2/uploads?#{params}", headers: authentication)
+ raise "uploads request failed #{response.status_code}\n#{response.body}" unless response.success?
+
+ JSON.parse(response.body)
+ end
+
+ enum UploadPermissions
+ None
+ Admin
+ Support
+ end
+
+ # returns details for a signed URL that can be used to upload the file
+ # obviously this doesn't actually upload the file directly
+ def upload(
+ file_name : String,
+ file_size : Int64,
+ file_md5 : String,
+ file_mime : String? = nil,
+ file_path : String? = nil,
+ permissions : UploadPermissions = UploadPermissions::None,
+ public : Bool = false, # public internet accessible
+ tags : Array(String) = [] of String,
+ cache_etag : String? = nil,
+ cache_modified : Time? = nil,
+ )
+ response = post("/api/engine/v2/uploads", headers: authentication, body: {
+ file_name: file_name,
+ file_size: file_size,
+ file_id: file_md5,
+ file_mime: file_mime,
+ file_path: file_path,
+ permissions: permissions,
+ public: public,
+ tags: tags,
+ cache_etag: cache_etag,
+ cache_modified: cache_modified,
+ }.to_json)
+ raise "upload request failed #{response.status_code}\n#{response.body}" unless response.success?
+
+ # Looks like: {type: "chunked_upload" | "direct_upload", upload_id: "upload-1234", residence: "S3" | "AzureStorage",
+ # signature: {verb: "PUT", url: "https://signed.url/file", headers: {"Content-Type": "image/jpeg"}}}
+ JSON.parse(response.body)
+ end
+
+ # returns a temporary URL where you can download the upload contents
+ def upload_content_url(upload_id : String) : String
+ response = get("/api/engine/v2/uploads/#{upload_id}/url", headers: authentication)
+ raise "uploads request failed #{response.status_code}\n#{response.body}" unless response.status.see_other?
+ response.headers["Location"]
+ end
+
+ def upload_remove(upload_id : String) : Bool
+ response = delete("/api/engine/v2/uploads/#{upload_id}", headers: authentication)
+ raise "upload removal failed #{response.status_code}\n#{response.body}" unless response.success?
+ true
+ end
+
+ # ===================================
+ # Guest details
+ # ===================================
+ @[Security(Level::Support)]
+ def guest_details(guest_id : String)
+ response = get("/api/staff/v1/guests/#{guest_id}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ @[Security(Level::Support)]
+ def update_guest(id : String, body_json : String) : Nil
+ response = patch("/api/staff/v1/guests/#{id}", body: body_json, headers: authentication(HTTP::Headers{
+ "Content-Type" => "application/json",
+ }))
+
+ raise "failed to update guest #{id}: #{response.status_code}" unless response.success?
+ end
+
+ @[Security(Level::Support)]
+ def query_guests(period_start : Int64, period_end : Int64, zones : Array(String))
+ params = URI::Params.build do |form|
+ form.add "period_start", period_start.to_s
+ form.add "period_end", period_end.to_s
+ form.add "zone_ids", zones.join(",")
+ end
+
+ response = get("/api/staff/v1/guests?#{params}", headers: authentication)
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # ===================================
+ # CALENDAR EVENT ACTIONS (via staff api)
+ # ===================================
+ @[Security(Level::Support)]
+ def query_events(
+ period_start : Int64,
+ period_end : Int64,
+ zones : Array(String)? = nil,
+ systems : Array(String)? = nil,
+ capacity : Int32? = nil,
+ features : String? = nil,
+ bookable : Bool? = nil,
+ include_cancelled : Bool? = nil,
+ )
+ params = URI::Params.build do |form|
+ form.add "period_start", period_start.to_s
+ form.add "period_end", period_end.to_s
+ form.add "zone_ids", zones.join(",") if zones && !zones.empty?
+ form.add "system_ids", systems.join(",") if systems && !systems.empty?
+ form.add "capacity", capacity.to_s if capacity
+ form.add "features", features if features
+ form.add "bookable", bookable.to_s if !bookable.nil?
+ form.add "include_cancelled", include_cancelled.to_s if !include_cancelled.nil?
+ end
+
+ response = get("/api/staff/v1/events?#{params}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # gets an event from either the `system_id` or `calendar` if only one is provided
+ # if both are provided, it gets the event from `calendar` and the metadata from `system_id`
+ # NOTE:: the use of `calendar` will typically not work from a driver unless the X-API-Key
+ # has read access to it. From a driver perspective you should probably use a
+ # dedicated Calendar driver with application access and the query_metadata function
+ # below if metadata is required: `query_metadata(system_id: "sys", event_ref: ["id", "uuid"])`
+ def get_event(event_id : String, system_id : String? = nil, calendar : String? = nil)
+ raise ArgumentError.new("requires system_id or calendar param") unless calendar.presence || system_id.presence
+ params = URI::Params.build do |form|
+ form.add "calendar", calendar.to_s if calendar.presence
+ form.add "system_id", system_id.to_s if system_id.presence
+ end
+
+ response = get("/api/staff/v1/events/#{event_id}?#{params}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # NOTE:: https://docs.google.com/document/d/1OaZljpjLVueFitmFWx8xy8BT8rA2lITyPsIvSYyNNW8/edit#
+ # The service account making this request needs delegated access and hence you can only edit
+ # events associated with a resource calendar
+ def update_event(system_id : String, event : PlaceCalendar::Event)
+ response = patch("/api/staff/v1/events/#{event.id}?system_id=#{system_id}", headers: authentication, body: event.to_json)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ PlaceCalendar::Event.from_json(response.body)
+ end
+
+ def create_event(event : PlaceCalendar::Event)
+ response = post("/api/staff/v1/events", headers: authentication, body: event.to_json)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ PlaceCalendar::Event.from_json(response.body)
+ end
+
+ def delete_event(system_id : String, event_id : String)
+ response = delete("/api/staff/v1/events/#{event_id}?system_id=#{system_id}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success? || response.status_code == 404
+ true
+ end
+
+ def patch_event_metadata(system_id : String, event_id : String, metadata : JSON::Any, ical_uid : String? = nil, setup_time : Int64? = nil, breakdown_time : Int64? = nil, setup_event_id : String? = nil, breakdown_event_id : String? = nil)
+ params = URI::Params.build do |form|
+ form.add "ical_uid", ical_uid.to_s if ical_uid.presence
+ form.add "setup_time", setup_time.to_s if setup_time
+ form.add "breakdown_time", breakdown_time.to_s if breakdown_time
+ form.add "setup_event_id", setup_event_id.to_s if setup_event_id
+ form.add "breakdown_event_id", breakdown_event_id.to_s if breakdown_event_id
+ end
+ response = patch("/api/staff/v1/events/#{event_id}/metadata/#{system_id}?#{params}", headers: authentication, body: metadata.to_json)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ JSON::Any.from_json(response.body)
+ end
+
+ def replace_event_metadata(system_id : String, event_id : String, metadata : JSON::Any, ical_uid : String? = nil, setup_time : Int64? = nil, breakdown_time : Int64? = nil, setup_event_id : String? = nil, breakdown_event_id : String? = nil)
+ params = URI::Params.build do |form|
+ form.add "ical_uid", ical_uid.to_s if ical_uid.presence
+ form.add "setup_time", setup_time.to_s if setup_time
+ form.add "breakdown_time", breakdown_time.to_s if breakdown_time
+ form.add "setup_event_id", setup_event_id.to_s if setup_event_id
+ form.add "breakdown_event_id", breakdown_event_id.to_s if breakdown_event_id
+ end
+ response = put("/api/staff/v1/events/#{event_id}/metadata/#{system_id}?#{params}", headers: authentication, body: metadata.to_json)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ JSON::Any.from_json(response.body)
+ end
+
+ # Search for metadata that exists on events to obtain the event information.
+ # For response details see `EventMetadata__Assigner` in the OpenAPI docs
+ # https://editor.swagger.io/?url=https://raw.githubusercontent.com/PlaceOS/staff-api/master/OPENAPI_DOC.yml
+ def query_metadata(
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ field_name : String? = nil,
+ value : String? = nil,
+ system_id : String? = nil,
+ event_ref : Array(String)? = nil,
+ )
+ params = URI::Params.build do |form|
+ form.add "period_start", period_start.to_s if period_start
+ form.add "period_end", period_end.to_s if period_end
+ form.add "field_name", field_name if field_name.presence
+ form.add "value", value if value.presence
+ form.add "event_ref", event_ref.join(",") if event_ref && !event_ref.empty?
+ end
+
+ response = get("/api/staff/v1/events/extension_metadata/#{system_id}?#{params}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # ===================================
+ # ZONE METADATA
+ # ===================================
+ def metadata(id : String, key : String? = nil)
+ placeos_client.metadata.fetch(id, key)
+ end
+
+ def metadata_children(id : String, key : String? = nil)
+ placeos_client.metadata.children(id, key)
+ end
+
+ @[Security(Level::Support)]
+ def write_metadata(id : String, key : String, payload : JSON::Any, description : String = "")
+ placeos_client.metadata.update(id, key, payload, description)
+ end
+
+ @[Security(Level::Support)]
+ def merge_metadata(id : String, key : String, payload : JSON::Any, description : String = "")
+ placeos_client.metadata.merge(id, key, payload, description)
+ end
+
+ # ===================================
+ # ZONE INFORMATION
+ # ===================================
+ def zone(zone_id : String)
+ placeos_client.zones.fetch zone_id
+ end
+
+ def zones(q : String? = nil,
+ limit : Int32 = 1000,
+ offset : Int32 = 0,
+ parent : String? = nil,
+ tags : Array(String) | String? = nil)
+ placeos_client.zones.search(
+ q: q,
+ limit: limit,
+ offset: offset,
+ parent_id: parent,
+ tags: tags
+ )
+ end
+
+ # ===================================
+ # BOOKINGS ACTIONS
+ # ===================================
+ @[Security(Level::Support)]
+ def create_booking(
+ booking_type : String,
+ asset_id : String,
+ user_id : String,
+ user_email : String,
+ user_name : String,
+ zones : Array(String),
+ booking_start : Int64? = nil,
+ booking_end : Int64? = nil,
+ checked_in : Bool = false,
+ approved : Bool? = nil,
+ title : String? = nil,
+ description : String? = nil,
+ time_zone : String? = nil,
+ extension_data : JSON::Any? = nil,
+ utm_source : String? = nil,
+ limit_override : Int64? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ attendees : Array(PlaceCalendar::Event::Attendee)? = nil,
+ process_state : String? = nil,
+ recurrence_type : String? = nil,
+ recurrence_days : Int32? = nil,
+ recurrence_nth_of_month : Int32? = nil,
+ recurrence_interval : Int32? = nil,
+ recurrence_end : Int64? = nil,
+ asset_ids : Array(String)? = nil,
+ asset_name : String? = nil,
+ )
+ now = time_zone ? Time.local(Time::Location.load(time_zone)) : Time.local
+ booking_start ||= now.at_beginning_of_day.to_unix
+ booking_end ||= now.at_end_of_day.to_unix
+
+ checked_in_at = now.to_unix if checked_in
+
+ logger.debug { "creating a #{booking_type} booking, starting #{booking_start}, asset #{asset_id}" }
+
+ params = URI::Params.build do |form|
+ form.add "utm_source", utm_source.to_s unless utm_source.nil?
+ form.add "limit_override", limit_override.to_s unless limit_override.nil?
+ form.add "event_id", event_id.to_s unless event_id.nil?
+ form.add "ical_uid", ical_uid.to_s unless ical_uid.nil?
+ end
+
+ response = post("/api/staff/v1/bookings?#{params}", headers: authentication, body: {
+ "booking_start" => booking_start,
+ "booking_end" => booking_end,
+ "booking_type" => booking_type,
+ "asset_id" => asset_id,
+ "asset_ids" => asset_ids,
+ "asset_name" => asset_name,
+ "user_id" => user_id,
+ "user_email" => user_email,
+ "user_name" => user_name,
+ "zones" => zones,
+ "checked_in" => checked_in,
+ "checked_in_at" => checked_in_at,
+ "approved" => approved,
+ "title" => title,
+ "description" => description,
+ "timezone" => time_zone,
+ "extension_data" => extension_data || JSON.parse("{}"),
+ "attendees" => attendees,
+ "process_state" => process_state,
+ "recurrence_type" => recurrence_type,
+ "recurrence_days" => recurrence_days,
+ "recurrence_nth_of_month" => recurrence_nth_of_month,
+ "recurrence_interval" => recurrence_interval,
+ "recurrence_end" => recurrence_end,
+ }.compact.to_json)
+ raise "issue creating #{booking_type} booking, starting #{booking_start}, asset #{asset_id}: #{response.status_code}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ @[Security(Level::Support)]
+ def update_booking(
+ booking_id : String | Int64,
+ booking_start : Int64? = nil,
+ booking_end : Int64? = nil,
+ asset_id : String? = nil,
+ title : String? = nil,
+ description : String? = nil,
+ timezone : String? = nil,
+ extension_data : JSON::Any? = nil,
+ approved : Bool? = nil,
+ checked_in : Bool? = nil,
+ limit_override : Int64? = nil,
+ instance : Int64? = nil,
+ recurrence_end : Int64? = nil,
+ )
+ logger.debug { "updating booking #{booking_id}" }
+
+ case checked_in
+ in true
+ checked_in_at = Time.utc.to_unix
+ in false
+ checked_out_at = Time.utc.to_unix
+ in nil
+ end
+
+ params = URI::Params.build do |form|
+ form.add "limit_override", limit_override.to_s unless limit_override.nil?
+ end
+
+ response = patch("/api/staff/v1/bookings/#{booking_id}?#{params}", headers: authentication, body: {
+ "booking_start" => booking_start,
+ "booking_end" => booking_end,
+ "checked_in" => checked_in,
+ "checked_in_at" => checked_in_at,
+ "checked_out_at" => checked_out_at,
+ "asset_id" => asset_id,
+ "title" => title,
+ "description" => description,
+ "timezone" => timezone,
+ "extension_data" => extension_data,
+ "instance" => instance,
+ "recurrence_end" => recurrence_end,
+ }.compact.to_json)
+ raise "issue updating booking #{booking_id}: #{response.status_code}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ @[Security(Level::Support)]
+ def reject(booking_id : String | Int64, utm_source : String? = nil, instance : Int64? = nil)
+ logger.debug { "rejecting booking #{booking_id}" }
+
+ params = URI::Params.build do |form|
+ form.add "instance", instance.to_s unless instance.nil?
+ form.add "utm_source", utm_source.to_s unless utm_source.nil?
+ end
+
+ response = post("/api/staff/v1/bookings/#{booking_id}/reject?#{params}", headers: authentication)
+ raise "issue rejecting booking #{booking_id}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ @[Security(Level::Support)]
+ def approve(booking_id : String | Int64, instance : Int64? = nil)
+ logger.debug { "approving booking #{booking_id}" }
+ inst = "/instance/#{instance}" if instance
+ response = post("/api/staff/v1/bookings/#{booking_id}/approve#{inst}", headers: authentication)
+ raise "issue approving booking #{booking_id}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ @[Security(Level::Support)]
+ def booking_state(booking_id : String | Int64, state : String, instance : Int64? = nil)
+ logger.debug { "updating booking #{booking_id}.#{instance} state to: #{state}" }
+ inst = "&instance=#{instance}" if instance
+ response = post("/api/staff/v1/bookings/#{booking_id}/update_state?state=#{state}#{inst}", headers: authentication)
+ raise "issue updating booking state #{booking_id}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ @[Security(Level::Support)]
+ def booking_check_in(booking_id : String | Int64, state : Bool = true, utm_source : String? = nil, instance : Int64? = nil)
+ logger.debug { "checking in booking #{booking_id}.#{instance} to: #{state}" }
+
+ params = URI::Params.build do |form|
+ form.add "instance", instance.to_s unless instance.nil?
+ form.add "utm_source", utm_source.to_s unless utm_source.nil?
+ form.add "state", state.to_s
+ end
+ response = post("/api/staff/v1/bookings/#{booking_id}/check_in?#{params}", headers: authentication)
+ raise "issue checking in booking #{booking_id}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ @[Security(Level::Support)]
+ def booking_delete(booking_id : String | Int64, utm_source : String? = nil, instance : Int64? = nil)
+ logger.debug { "deleting booking #{booking_id}" }
+ params = URI::Params.build do |form|
+ form.add "instance", instance.to_s unless instance.nil?
+ form.add "utm_source", utm_source.to_s unless utm_source.nil?
+ end
+ response = delete("/api/staff/v1/bookings/#{booking_id}?#{params}", headers: authentication)
+ raise "issue updating booking state #{booking_id}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ @[Security(Level::Support)]
+ def booking_extension_data(booking_id : String | Int64, extension_data : Hash(String, JSON::Any), instance : Int64? = nil, signal_changes : Bool = false)
+ logger.debug { "updating booking ext data #{booking_id}.#{instance} with: #{extension_data}" }
+
+ params = URI::Params.build do |form|
+ form.add "signal_changes", signal_changes.to_s
+ end
+
+ response = patch("/api/staff/v1/bookings/#{booking_id}/ext_data/#{instance}?#{params}", headers: authentication, body: extension_data.to_json)
+ raise "issue updating booking #{booking_id}.#{instance}: #{response.status_code}\n#{response.body}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ # ===================================
+ # BOOKINGS QUERY
+ # ===================================
+ def query_bookings(
+ type : String? = nil,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ rejected : Bool? = nil,
+ checked_in : Bool? = nil,
+ include_checked_out : Bool? = nil,
+ extension_data : JSON::Any? = nil,
+ deleted : Bool? = nil,
+ asset_id : String? = nil,
+ limit : Int32? = nil,
+ )
+ default_end = @period_end_default_in_min || 30
+
+ # Assumes occuring now
+ period_start ||= Time.utc.to_unix
+ period_end ||= default_end.minutes.from_now.to_unix
+ limit ||= @query_limit
+
+ params = URI::Params.build do |form|
+ form.add "period_start", period_start.to_s if period_start
+ form.add "period_end", period_end.to_s if period_end
+ form.add "type", type.to_s if type.presence
+
+ form.add "zones", zones.join(",") unless zones.empty?
+ form.add "user", user.to_s if user.presence
+ form.add "email", email.to_s if email.presence
+ form.add "state", state.to_s if state.presence
+ form.add "created_before", created_before.to_s if created_before
+ form.add "created_after", created_after.to_s if created_after
+ form.add "approved", approved.to_s unless approved.nil?
+ form.add "rejected", rejected.to_s unless rejected.nil?
+ form.add "checked_in", checked_in.to_s unless checked_in.nil?
+ form.add "deleted", deleted.to_s unless deleted.nil?
+ form.add "event_id", event_id.to_s if event_id.presence
+ form.add "ical_uid", ical_uid.to_s if ical_uid.presence
+ form.add "include_checked_out", include_checked_out.to_s unless include_checked_out.nil?
+
+ form.add "asset_id", asset_id.to_s unless asset_id.nil?
+ form.add "limit", limit.to_s
+
+ if extension_data
+ value = extension_data.as_h.map { |k, v| "#{k}:#{v}" }.join(",")
+ form.add "extension_data", "{#{value}}"
+ end
+ end
+
+ logger.debug { "requesting staff/v1/bookings: #{params}" }
+
+ # Get the existing bookings from the API to check if there is space
+ bookings = [] of JSON::Any
+ next_request = "/api/staff/v1/bookings?#{params}"
+
+ loop do
+ response = get(next_request, headers: authentication)
+ raise "issue loading list of bookings (zones #{zones}): #{response.status_code}" unless response.success?
+ links = LinkHeader.new(response)
+
+ # Just parse it here instead of using the Bookings object
+ # it will be parsed into an object on the far end
+ new_bookings = JSON.parse(response.body).as_a
+ bookings.concat new_bookings
+
+ last_req = next_request
+ next_request = links["next"]?
+ break if next_request.nil? || new_bookings.empty? || last_req == next_request
+ end
+
+ logger.debug { "bookings count: #{bookings.size}" }
+
+ bookings
+ end
+
+ def get_booking(booking_id : String | Int64, instance : Int64? = nil)
+ logger.debug { "getting booking #{booking_id}" }
+ params = "?instance=#{instance}" if instance
+ response = get("/api/staff/v1/bookings/#{booking_id}#{params}", headers: authentication)
+ raise "issue getting booking #{booking_id}: #{response.status_code}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ # lists asset IDs based on the parameters provided
+ #
+ # booking_type is required unless event_id or ical_uid is present
+ def booked(
+ type : String? = nil,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ checked_in : Bool? = nil,
+ include_checked_out : Bool? = nil,
+ include_booked_by : Bool? = nil,
+ department : String? = nil,
+ limit : Int32? = nil,
+ offset : Int32? = nil,
+ permission : String? = nil,
+ extension_data : JSON::Any? = nil,
+ )
+ params = URI::Params.build do |form|
+ form.add "period_start", period_start.to_s if period_start
+ form.add "period_end", period_end.to_s if period_end
+ form.add "type", type.to_s if type.presence
+
+ form.add "zones", zones.join(",") unless zones.empty?
+ form.add "user", user.to_s if user.presence
+ form.add "email", email.to_s if email.presence
+ form.add "state", state.to_s if state.presence
+ form.add "created_before", created_before.to_s if created_before
+ form.add "created_after", created_after.to_s if created_after
+ form.add "approved", approved.to_s unless approved.nil?
+ form.add "checked_in", checked_in.to_s unless checked_in.nil?
+ form.add "event_id", event_id.to_s if event_id.presence
+ form.add "ical_uid", ical_uid.to_s if ical_uid.presence
+ form.add "include_checked_out", include_checked_out.to_s unless include_checked_out.nil?
+ form.add "include_booked_by", include_booked_by.to_s unless include_booked_by.nil?
+ form.add "department", department.to_s if department.presence
+ form.add "limit", limit.to_s if limit
+ form.add "offset", offset.to_s if offset
+ form.add "permission", permission.to_s if permission.presence
+
+ if extension_data
+ value = extension_data.as_h.map { |k, v| "#{k}:#{v}" }.join(",")
+ form.add "extension_data", "{#{value}}"
+ end
+ end
+
+ logger.debug { "requesting staff/v1/bookings/booked: #{params}" }
+ response = get("/api/staff/v1/bookings/booked?#{params}", headers: authentication)
+ raise "issue getting booked assets: #{response.status_code}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ # ===================================
+ # Driver debugging
+ # ===================================
+
+ def driver_introspection
+ {
+ protocol: PlaceOS::Driver::Stats.protocol_tracking,
+ memory: PlaceOS::Driver::Stats.memory_usage,
+ queue: @__queue__.@queue.size,
+ }
+ end
+
+ # ===================================
+ # SURVEYS
+ # ===================================
+
+ def get_survey_invites(survey_id : Int64? = nil, sent : Bool? = nil)
+ logger.debug { "getting survey_invites (survey #{survey_id}, sent #{sent})" }
+ params = URI::Params.new
+ params["survey_id"] = survey_id.to_s if survey_id
+ params["sent"] = sent.to_s unless sent.nil?
+ response = get("/api/staff/v1/surveys/invitations", params, headers: authentication)
+ raise "issue getting survey invitations (survey #{survey_id}, sent #{sent}): #{response.status_code}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ @[Security(Level::Support)]
+ def update_survey_invite(
+ token : String,
+ email : String? = nil,
+ sent : Bool? = nil,
+ )
+ logger.debug { "updating survey invite #{token}" }
+ response = patch("/api/staff/v1/surveys/invitations/#{token}", headers: authentication, body: {
+ "email" => email,
+ "sent" => sent,
+ }.compact.to_json)
+ raise "issue updating survey invite #{token}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ # ===================================
+
+ @[Security(Level::Support)]
+ def signal(channel : String, payload : JSON::Any? = nil)
+ placeos_client.root.signal(channel, payload)
+ end
+
+ # For accessing PlaceOS APIs
+ protected getter placeos_client : PlaceOS::Client do
+ insecure = setting?(Bool, :https_insecure) || setting?(String, :https_verify) == "none"
+ PlaceOS::Client.new(
+ @place_domain,
+ host_header: @host_header,
+ x_api_key: @api_key,
+ insecure: insecure
+ )
+ end
+
+ # ===================================
+ # PLACEOS AUTHENTICATION:
+ # ===================================
+ protected def authentication(headers : HTTP::Headers = HTTP::Headers.new) : HTTP::Headers
+ headers["Accept"] = "application/json"
+ headers["X-API-Key"] = @api_key.presence || "spec-test"
+ headers
+ end
+end
diff --git a/drivers/place/staff_api_spec.cr b/drivers/place/staff_api_spec.cr
new file mode 100644
index 00000000000..76ede5046fc
--- /dev/null
+++ b/drivers/place/staff_api_spec.cr
@@ -0,0 +1,92 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::StaffAPI" do
+ resp = exec(:query_bookings, "desk")
+
+ expect_http_request do |request, response|
+ headers = request.headers
+ if headers["X-API-Key"]? == "spec-test"
+ response.status_code = 200
+ response << %([{
+ "id": 1234,
+ "user_id": "user-12345",
+ "user_email": "steve@place.tech",
+ "user_name": "Steve T",
+ "asset_id": "desk-2-12",
+ "zones": ["zone-build1", "zone-level2"],
+ "booking_type": "Steve T",
+ "booking_start": 123456,
+ "booking_end": 12345678,
+ "timezone": "Australia/Sydney",
+ "checked_in": true,
+ "rejected": false,
+ "approved": false
+ }])
+ else
+ response.status_code = 401
+ end
+ end
+
+ resp.get.should eq(JSON.parse(%([{
+ "id": 1234,
+ "user_id": "user-12345",
+ "user_email": "steve@place.tech",
+ "user_name": "Steve T",
+ "asset_id": "desk-2-12",
+ "zones": ["zone-build1", "zone-level2"],
+ "booking_type": "Steve T",
+ "booking_start": 123456,
+ "booking_end": 12345678,
+ "timezone": "Australia/Sydney",
+ "checked_in": true,
+ "rejected": false,
+ "approved": false
+ }])))
+
+ sleep 1
+ invites_resp = exec(:get_survey_invites, sent: false)
+
+ expect_http_request do |request, response|
+ headers = request.headers
+ if headers["X-API-Key"]? == "spec-test"
+ response.status_code = 200
+
+ params = request.query_params
+ survey_id = params["survey_id"]? || 1234
+ sent = params["sent"]?
+
+ sent_invite = {
+ id: 123,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user@spec.test",
+ sent: true,
+ }
+ unsent_invite = {
+ id: 123,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user@spec.test",
+ sent: false,
+ }
+
+ if sent == "true"
+ response << [sent_invite].to_json
+ elsif sent == "false"
+ response << [unsent_invite].to_json
+ else
+ response << [sent_invite, unsent_invite].to_json
+ end
+ else
+ response.status_code = 401
+ end
+ end
+
+ invites_resp.get.should eq(JSON.parse(%([{
+ "id": 123,
+ "survey_id": 1234,
+ "token": "QWERTY",
+ "email": "user@spec.test",
+ "sent": false
+ }])))
+end
diff --git a/drivers/place/survey_mailer.cr b/drivers/place/survey_mailer.cr
new file mode 100644
index 00000000000..4f65d195b91
--- /dev/null
+++ b/drivers/place/survey_mailer.cr
@@ -0,0 +1,98 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+
+class Place::SurveyMailer < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+
+ descriptive_name "PlaceOS Survey Mailer"
+ generic_name :SurveyMailer
+ description %(emails survey invites)
+
+ default_settings({
+ timezone: "GMT",
+ send_invites: "*/3 * * * *",
+ email_template: "survey",
+ })
+
+ accessor staff_api : StaffAPI_1
+
+ def mailer
+ system.implementing(Interface::Mailer)[0]
+ end
+
+ @time_zone : Time::Location = Time::Location.load("GMT")
+
+ @visitor_emails_sent : UInt64 = 0_u64
+ @visitor_email_errors : UInt64 = 0_u64
+
+ @email_template : String = "survey"
+ @send_invites : String? = nil
+
+ def on_update
+ @send_invites = setting?(String, :send_invites).presence
+ @email_template = setting?(String, :email_template) || "survey"
+
+ time_zone = setting?(String, :timezone).presence || "GMT"
+ @time_zone = Time::Location.load(time_zone)
+
+ schedule.clear
+ if invites = @send_invites
+ schedule.cron(invites, @time_zone) { send_survey_emails }
+ end
+ end
+
+ def template_fields : Array(TemplateFields)
+ [
+ TemplateFields.new(
+ trigger: {@email_template, "invite"},
+ name: "Survey invite",
+ description: "Email invitation sent to participants to complete a survey",
+ fields: [
+ {name: "email", description: "Email address of the survey recipient"},
+ {name: "token", description: "Unique authentication token for accessing the survey"},
+ {name: "survey_id", description: "Unique identifier of the survey to be completed"},
+ ]
+ ),
+ ]
+ end
+
+ @[Security(Level::Support)]
+ def send_survey_emails
+ invites = Array(SurveyInvite).from_json staff_api.get_survey_invites(sent: false).get.to_json
+ sent_invites : Hash(String, Array(Int64)) = {} of String => Array(Int64)
+
+ invites.each do |invite|
+ next if invite.sent
+ begin
+ if !(sent_surveys = sent_invites[invite.email]?) || !sent_surveys.includes?(invite.survey_id)
+ sent_invites[invite.email] ||= [] of Int64
+ sent_invites[invite.email] << invite.survey_id
+
+ mailer.send_template(
+ to: invite.email,
+ template: {@email_template, "invite"},
+ args: {
+ email: invite.email,
+ token: invite.token,
+ survey_id: invite.survey_id,
+ })
+ end
+
+ staff_api.update_survey_invite(invite.token, sent: true)
+ rescue error
+ logger.warn(exception: error) { "failed to send survey email to #{invite.email}" }
+ end
+ end
+ end
+
+ struct SurveyInvite
+ include JSON::Serializable
+
+ property id : Int64
+ property survey_id : Int64
+ property token : String
+ property email : String
+ property sent : Bool?
+ end
+end
diff --git a/drivers/place/survey_mailer_spec.cr b/drivers/place/survey_mailer_spec.cr
new file mode 100644
index 00000000000..aca455dde19
--- /dev/null
+++ b/drivers/place/survey_mailer_spec.cr
@@ -0,0 +1,99 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/mailer"
+
+class StaffAPI < DriverSpecs::MockDriver
+ def get_survey_invites(survey_id : Int64? = nil, sent : Bool? = nil)
+ survey_id ||= 1
+
+ invites = [
+ {
+ id: 1,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user1@spec.test",
+ sent: false,
+ },
+ {
+ id: 2,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user1@spec.test",
+ sent: false,
+ },
+ {
+ id: 3,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user2@spec.test",
+ sent: false,
+ },
+ {
+ id: 4,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user3@spec.test",
+ sent: nil,
+ },
+ {
+ id: 5,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user4@spec.test",
+ sent: true,
+ },
+ ]
+
+ JSON.parse(invites.to_json)
+ end
+
+ def update_survey_invite(token : String, email : String? = nil, sent : Bool? = nil)
+ true
+ end
+end
+
+class Mailer < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Mailer
+
+ def on_load
+ self[:sent] = 0
+ end
+
+ def send_template(
+ to : String | Array(String),
+ template : Tuple(String, String),
+ args : TemplateItems,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ )
+ self[:sent] = self[:sent].as_i + 1
+ end
+
+ def send_mail(
+ to : String | Array(String),
+ subject : String,
+ message_plaintext : String? = nil,
+ message_html : String? = nil,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ ) : Bool
+ true
+ end
+end
+
+DriverSpecs.mock_driver "Place::StaffAPI" do
+ system({
+ StaffAPI: {StaffAPI},
+ Mailer: {Mailer},
+ })
+
+ _resp = exec(:send_survey_emails).get
+ system(:Mailer_1)[:sent].should eq 3
+end
diff --git a/drivers/place/template_mailer.cr b/drivers/place/template_mailer.cr
new file mode 100644
index 00000000000..abb827cd83c
--- /dev/null
+++ b/drivers/place/template_mailer.cr
@@ -0,0 +1,298 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+
+# This driver uses metadata templates to send emails via the SMTP mailer.
+# It should be configured as Mailer_1 with the next mailer in the chain as Mailer_2.
+#
+# It also updates metadata in the staff API with available fields for use in email templates.
+class Place::TemplateMailer < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::Mailer
+
+ alias TemplateFields = PlaceOS::Driver::Interface::MailerTemplates::TemplateFields
+
+ descriptive_name "Template Mailer"
+ generic_name :Mailer
+ description %(uses metadata templates to send emails via the SMTP mailer)
+
+ default_settings({
+ cache_timeout: 300, # timeout for the template cache
+ keep_if_not_seen: 6, # keep fields for x updates if not seen, -1 to keep forever, 0 to never keep
+ timezone: "Australia/Sydney",
+ update_schedule: "*/20 * * * *", # cron schedule for updating template fields
+ })
+
+ accessor staff_api : StaffAPI_1
+
+ getter org_zone_ids : Array(String) { get_zone_ids?("org").not_nil! }
+ getter region_zone_ids : Array(String) { get_zone_ids?("region").not_nil! }
+ getter building_zone_ids : Array(String) { get_zone_ids?("building").not_nil! }
+ getter level_zone_ids : Array(String) { get_zone_ids?("level").not_nil! }
+
+ getter org_zone_id : String { get_local_zone_id(org_zone_ids).not_nil! }
+ getter building_zone_id : String { get_local_zone_id(building_zone_ids).not_nil! }
+
+ def mailer
+ system.implementing(Interface::Mailer)[1]
+ end
+
+ SEPERATOR = "."
+
+ @template_cache : TemplateCache = TemplateCache.new
+ @cache_timeout : Int64 = 300
+
+ # keep fields for x updates if not seen
+ # -1 to keep forever
+ # 0 to never keep
+ # 1 to keep for 1 update
+ @keep_if_not_seen : Int64 = 6
+ @not_seen_times : Hash(String, Int64) = Hash(String, Int64).new
+
+ @timezone : Time::Location = Time::Location.load("Australia/Sydney")
+ @update_schedule : String? = nil
+
+ def on_update
+ @org_zone_ids = nil
+ @region_zone_ids = nil
+ @building_zone_ids = nil
+ @level_zone_ids = nil
+
+ @org_zone_id = nil
+ @building_zone_id = nil
+
+ @cache_timeout = setting?(Int64, :cache_timeout) || 300_i64
+ @keep_if_not_seen = setting?(Int64, :keep_if_not_seen) || 6_i64
+
+ timezone = setting?(String, :timezone).presence || "Australia/Sydney"
+ @timezone = Time::Location.load(timezone)
+ @update_schedule = setting?(String, :update_schedule).presence
+
+ schedule.clear
+
+ if update_schedule = @update_schedule
+ schedule.cron(update_schedule, @timezone) do
+ update_template_fields(org_zone_id)
+ end
+ end
+
+ update_template_fields(org_zone_id)
+ end
+
+ def get_zone_ids?(tag : String) : Array(String)?
+ staff_api.zones(tags: tag).get.as_a.map(&.[]("id").as_s)
+ rescue error
+ logger.warn(exception: error) { "unable to determine #{tag} zone ids" }
+ nil
+ end
+
+ def get_local_zone_id(zone_ids : Array(String)) : String?
+ (zone_ids & system.zones).first
+ rescue error
+ logger.warn(exception: error) { "unable to determine local zone id" }
+ nil
+ end
+
+ def get_template_fields?(zone_id : String) : Hash(String, MetadataTemplateFields)?
+ metadata = Metadata.from_json staff_api.metadata(zone_id, "email_template_fields").get["email_template_fields"].to_json
+ Hash(String, MetadataTemplateFields).from_json metadata.details.to_json
+ rescue error
+ logger.warn(exception: error) { "unable to get email template fields from zone #{zone_id} metadata" }
+ nil
+ end
+
+ def sticky_template_fields(zone_id : String) : Hash(String, MetadataTemplateFields)
+ # keep nothing
+ return Hash(String, MetadataTemplateFields).new if @keep_if_not_seen == 0
+
+ current_fields = get_template_fields?(zone_id) || Hash(String, MetadataTemplateFields).new
+ return current_fields if current_fields.empty?
+
+ # keep forever
+ return current_fields if @keep_if_not_seen == -1
+
+ sticky_fields = Hash(String, MetadataTemplateFields).new
+
+ current_fields.keys.each do |key|
+ @not_seen_times[key] = @not_seen_times[key]? ? @not_seen_times[key] + 1 : 1_i64
+
+ if @not_seen_times[key] <= @keep_if_not_seen
+ sticky_fields[key] = current_fields[key]
+ end
+ end
+
+ sticky_fields
+ end
+
+ def update_template_fields(zone_id : String)
+ template_fields : Hash(String, MetadataTemplateFields) = sticky_template_fields(zone_id)
+
+ system.implementing(Interface::MailerTemplates).each do |driver|
+ # next if the driver is turned off, or anything else goes wrong
+ begin
+ driver_template_fields = Array(TemplateFields).from_json driver.template_fields.get.to_json
+ rescue error
+ logger.warn(exception: error) { "unable to get template fields from module #{driver.module_id}" }
+ next
+ end
+
+ driver_template_fields = Array(TemplateFields).from_json driver.template_fields.get.to_json
+ driver_template_fields.each do |field_list|
+ template_fields["#{field_list[:trigger].join(SEPERATOR)}"] = MetadataTemplateFields.new(
+ module_name: driver.module_name,
+ name: field_list[:name],
+ description: field_list[:description],
+ fields: field_list[:fields],
+ )
+ end
+ end
+
+ template_fields.keys.each do |key|
+ @not_seen_times[key] = 0_i64
+ end
+
+ self[:template_fields] = template_fields
+
+ unless template_fields.empty?
+ staff_api.write_metadata(id: zone_id, key: "email_template_fields", payload: template_fields, description: "Available fields for use in email templates").get
+ end
+ end
+
+ # fetch templates from cache or metadata
+ def fetch_templates(zone_id : String?) : Array(Template)
+ return [] of Template unless zone_id
+
+ if (cache = @template_cache[zone_id]?) && cache[0] > Time.utc.to_unix
+ cache[1]
+ else
+ templates = get_templates?(zone_id) || [] of Template
+ @template_cache[zone_id] = {Time.utc.to_unix + @cache_timeout, templates}
+ templates
+ end
+ end
+
+ def template_cache
+ @template_cache
+ end
+
+ def clear_template_cache(zone_id : String? = nil)
+ if zone_id && !zone_id.blank?
+ @template_cache.delete(zone_id)
+ else
+ @template_cache = TemplateCache.new
+ end
+ end
+
+ # get templates from metadata
+ def get_templates?(zone_id : String) : Array(Template)?
+ metadata = Metadata.from_json staff_api.metadata(zone_id, "email_templates").get["email_templates"].to_json
+ metadata.details.as_a.map { |template| Template.from_json template.to_json }
+ rescue
+ logger.debug { "unable to get email templates from zone #{zone_id} metadata" }
+ nil
+ end
+
+ def find_template?(template : String, zone_ids : Array(String)) : Template?
+ org_id = (zone_ids & org_zone_ids)[0]?
+ region_id = (zone_ids & region_zone_ids)[0]?
+ building_id = (zone_ids & building_zone_ids)[0]?
+ level_id = (zone_ids & level_zone_ids)[0]?
+
+ # find the requested template
+ # order of precedence: level, building, region, org
+ fetch_templates(level_id).find { |t| t["trigger"] == template } ||
+ fetch_templates(building_id).find { |t| t["trigger"] == template } ||
+ fetch_templates(region_id).find { |t| t["trigger"] == template } ||
+ fetch_templates(org_id).find { |t| t["trigger"] == template } ||
+ nil
+ end
+
+ def generate_svg_qrcode(text : String) : String
+ mailer.generate_svg_qrcode(text).get.as_s
+ end
+
+ def generate_png_qrcode(text : String, size : Int32 = 128) : String
+ mailer.generate_png_qrcode(text, size).get.as_s
+ end
+
+ def send_mail(
+ to : String | Array(String),
+ subject : String,
+ message_plaintext : String? = nil,
+ message_html : String? = nil,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ )
+ mailer.send_mail(to, subject, message_plaintext, message_html, resource_attachments, attachments, cc, bcc, from, reply_to)
+ end
+
+ def send_template(
+ to : String | Array(String),
+ template : Tuple(String, String),
+ args : TemplateItems,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ )
+ zone_ids = if (zones = args["zone_ids"]?) && zones.is_a?(Array(String))
+ zones
+ else
+ [org_zone_id, building_zone_id]
+ end
+
+ metadata_template = find_template?(template.join(SEPERATOR), zone_ids)
+
+ if metadata_template
+ subject = build_template(metadata_template["subject"].to_s, args)
+ text = build_template(metadata_template["text"]?.try &.to_s, args) || ""
+ html = build_template(metadata_template["html"]?.try &.to_s, args) || ""
+ from = metadata_template["from"].to_s if (from_template = metadata_template["from"]?) && from_template.to_s.presence
+ reply_to = metadata_template["reply_to"].to_s if (reply_to_template = metadata_template["reply_to"]?) && reply_to_template.to_s.presence
+
+ mailer.send_mail(to, subject, text, html, resource_attachments, attachments, cc, bcc, from, reply_to)
+ else
+ logger.info { "unable to find template #{template.join(SEPERATOR)} from zones #{zone_ids} metadata, forwarding to Mailer_2" }
+ mailer.send_template(to, template, args, resource_attachments, attachments, cc, bcc, from, reply_to)
+ end
+ end
+
+ alias Template = Hash(String, String | Int64)
+
+ # zone_id, timeout, templates
+ alias TemplateCache = Hash(String, Tuple(Int64, Array(Template)))
+
+ struct Metadata
+ include JSON::Serializable
+
+ property name : String
+ property description : String = ""
+ property details : JSON::Any
+ property parent_id : String
+ property schema_id : String? = nil
+ property editors : Set(String) = Set(String).new
+ property modified_by_id : String? = nil
+ end
+
+ struct MetadataTemplateFields
+ include JSON::Serializable
+
+ property module_name : String = ""
+ property name : String = ""
+ property description : String? = nil
+ property fields : Array(NamedTuple(name: String, description: String)) = [] of NamedTuple(name: String, description: String)
+
+ def initialize(
+ @module_name : String,
+ @name : String,
+ @description : String? = nil,
+ @fields : Array(NamedTuple(name: String, description: String)) = [] of NamedTuple(name: String, description: String)
+ )
+ end
+ end
+end
diff --git a/drivers/place/template_mailer_spec.cr b/drivers/place/template_mailer_spec.cr
new file mode 100644
index 00000000000..b1bd6e50c64
--- /dev/null
+++ b/drivers/place/template_mailer_spec.cr
@@ -0,0 +1,157 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+
+class StaffAPI < DriverSpecs::MockDriver
+ ZONES = [
+ {
+ created_at: 1660537814,
+ updated_at: 1681800971,
+ id: "zone-org-1234",
+ name: "Test Org Zone",
+ display_name: "Test Org Zone",
+ location: "",
+ description: "",
+ code: "",
+ type: "",
+ count: 0,
+ capacity: 0,
+ map_id: "",
+ tags: [
+ "org",
+ ],
+ triggers: [] of String,
+ parent_id: "zone-0000",
+ timezone: "Australia/Sydney",
+ },
+ {
+ created_at: 1660537814,
+ updated_at: 1681800971,
+ id: "zone-bld-1234",
+ name: "Test Building Zone",
+ display_name: "Test Building Zone",
+ location: "",
+ description: "",
+ code: "",
+ type: "",
+ count: 0,
+ capacity: 0,
+ map_id: "",
+ tags: [
+ "building",
+ ],
+ triggers: [] of String,
+ parent_id: "zone-0000",
+ timezone: "Australia/Sydney",
+ },
+ ]
+
+ # METADATA_TEMPLATES = {
+ # email_templates = {
+ # name: "email_templates",
+ # description: "Email Templates for Zone",
+ # details: [
+ # {
+ # id: "template-1",
+ # from: "support@example.com",
+ # html: "
+
+
+```
+
+You can drag and drop images and videos into backoffice so they are available for embedding.
+
+## Defining Outputs to display
+
+You need to define which ouputs will be displayed on the panel.
+
+* when there is a single output, it'll automatically be switched
+* where there are two outputs, the user must manually switch by selecting the output
+
+```yaml
+
+# named local outputs as when joining rooms we'll merge these with joined rooms
+local_outputs:
+ - Display_1
+ - Display_2
+
+```
+
+Where you have Preview Monitor(s) for previewing sources before presenting them, you configure them using:
+
+```yaml
+
+# these will show the currently selected input
+preview_outputs:
+ - Display_3
+
+```
+
+NOTE:: there is a setting `mute_on_unlink: true` that can be set to ensure outputs are muted when rooms are unlinked - ensuring routes are reset
+
+## Front of House Audio
+
+By default the first display in the output list is assumed to be managing audio
+However you may want to configure defaults or use Mixer controls instead of the output device
+
+```yaml
+
+# This is a mixer configuration
+master_audio:
+ name: FOH Speakers
+ level_id: ["FOH-1234", "FOH-1235"]
+ mute_id: 'FOH-123-45-mute'
+
+ level_index: 4,
+ mute_index: 4,
+ level_feedback: 'faderFOH-1234'
+ mute_feedback: 'faderFOH-1234_mute'
+ module_id: 'Mixer_2'
+
+ default_muted: false
+ default_level: 60
+
+ min_level: 40
+ max_level: 90
+
+```
+
+You can just customise defaults if you want to continue using the default output
+
+```yaml
+
+master_audio:
+ default_muted: false
+ default_level: 60
+
+```
+
+## Projector Screen Linking
+
+Linking a projector screen to a displays power state
+
+```yaml
+
+screens:
+ Karijini_IV_Projector_1: Screen_1
+
+```
+
+## QSC Phone Dialing controls
+
+The places a dialing phone icon at the top of the screen that can be used to dial a phone number. Does not effect other aspects of the UI / Switching.
+
+```yaml
+
+phone_settings:
+ module: "Mixer_1",
+ number_id: "Status/Control16-17-VoIPCallControlDialString",
+ dial_id: "Status/Control16-17-VoIPCallControlConnect",
+ hangup_id: "Status/Control16-17-VoIPCallControlDisconnect",
+ status_id: "Status/Control16-17-VoIPCallStatusProgress",
+ ringing_id: "Status/Control16-17-VoIPCallStatusRinging(state)",
+ offhook_id: "Status/Control16-17-VoIPCallStatusOffHook",
+ dtmf_id: "16.17:dtmftx1"
+
+```
+
+Then in the QSC driver you want to define which controls QSC should poll and report changes:
+
+```yaml
+
+# keeps the phone status in sync
+change_groups: {
+ "room123_phone" => {
+ id: 1,
+ controls: ["VoIPCallStatusProgress", "VoIPCallStatusRinging", "VoIPCallStatusOffHook"],
+ },
+},
+
+```
+
+## Microphone configuration
+
+A basic list of fader and mute values that represent the microphones available
+
+```yaml
+
+local_microphones:
+ - name: Hand Held Microphone
+ level_id: ["HH-1234", "HH-1235"]
+ mute_id: 'HH-123-45-mute'
+
+ # optional keys
+ level_index: 4,
+ mute_index: 4,
+ level_feedback: 'faderHH-1234'
+ mute_feedback: 'faderHH-1234_mute'
+ module_id: 'Mixer_2'
+
+ default_muted: true
+ default_level: 55.8
+
+ min_level: 40
+ max_level: 90
+
+```
+
+Where a microphone might be shared between rooms or spill into a lobby, you can add a rooms configuration with mute ids that when unmuted will route the microphone audio to various spaces.
+
+```yaml
+
+local_microphones:
+ - name: Hand Held Microphone
+ # as above
+
+ rooms:
+ - name: "Room 1"
+ binding: "hh_room1_mute_id_mute"
+ control: "hh_room1_mute_id"
+ # this uses the `mute` function
+
+ - name: "Room 2"
+ binding: "hh_room2_mute_id_mute"
+ route:
+ - module_id: Mixer_1
+ function_name: trigger
+ arguments: ["hh_room2_add"]
+ unroute:
+ - module_id: Mixer_1
+ function_name: trigger
+ arguments: ["hh_room2_remove"]
+
+```
+
+## Joining Config
+
+Where systems can be merged you can define the various modes that are supported between the rooms.
+
+* there are two types `fully_aware` or `independent` (default)
+ * fully_aware: (typically something like 4 rooms where you can have independent, 1:3, 2:2 or all 4 etc)
+ * rooms that are not technically part of the join are aware of the join (1:3 combination for example)
+ * this might be because the DSP has a preset for each join combination (to combine microphones)
+ * independent: (typically something like 3 rooms that share a video switcher)
+ * only rooms part of the join are notified of the join
+ * this makes sense where audio and video come off an output of a shared switch
+ * so if room1 wants to present in room2 all it has to do is present to both outputs and keep audio levels in sync
+
+```yaml
+
+join_modes:
+ type: fully_aware
+ # input 1 in both rooms is merged (versus becoming a seperate input)
+ merge_outputs: true # default true
+ modes:
+ # id links mode across rooms.
+ # useful in fully linked where joining room_ids might differ between systems
+ - id: unlinked
+ name: Independent
+ room_ids: []
+ # join actions are optional
+ join_actions:
+ - module_id: Mixer_1
+ function_name: trigger
+ # supports named arguments too
+ arguments: ["UnjoinAll"]
+ - id: join-all
+ name: All Rooms
+ room_ids: ["sys-Cia-PnmTLC", "sys-Cia-ehhm8h", "sys-Cia-_e0jWQ"]
+ join_actions:
+ - module_id: Mixer_1
+ function_name: trigger
+ arguments: ["Join-all"]
+
+ # sometimes you may need to run an action to break a join (typically not required)
+ breakdown:
+ - module_id: Mixer_1
+ function_name: trigger
+ arguments: ["UnjoinAll"]
+
+```
+
+## Lighting Config
+
+There are two lighting modes:
+
+* independent rooms (even when linked, each room controls it's lighting area, we manually sync them)
+* joining rooms (a single request will change the scene in all linked rooms)
+
+```yaml
+
+# scenes are often the same across many rooms, so should be applied to a zone
+lighting_scenes:
+ - id: 1
+ name: "Full"
+ icon: lightbulb
+ opacity: 1.0
+ - id: 2
+ name: "Medium"
+ icon: lightbulb
+ opacity: 0.5
+ - id: 3
+ name: "Off"
+ icon: lightbulb_outline
+ opacity: 0.8
+
+# Each room typically will have its own area or grouping, so apply this at the system level
+lighting_area:
+ id: 23
+ # join: 0xFF (only if required by the driver)
+ # channel: 3 (only if required by the driver)
+ # component: "Lighting" (only if required by the driver)
+
+# Typically set to false if using the `join` field in `lighting_area`
+lighting_independent: true
+```
+
+## Additional Room Accessories
+
+These are things like blinds or air-conditioning that usually have limited controls and obsucre interfaces
+
+```yaml
+
+room_accessories:
+ - name: Shade blind
+ module: Blinds_1
+ controls:
+ - name: Up
+ icon: vertical_align_top
+ function_name: position
+ arguments: [1, "up"]
+ - name: Down
+ icon: vertical_align_bottom
+ function_name: position
+ arguments: [1, "down"]
+
+```
+
+If a control performs multiple actions you can use the `exec` block
+
+```yaml
+
+room_accessories:
+ - name: Projector Screen
+ controls:
+ - name: Up
+ icon: vertical_align_top
+ exec:
+ - module: Screen_1
+ function_name: position
+ arguments: [1, "up"]
+ - module: Projector_1
+ function_name: power
+ arguments: [false]
+ - name: Down
+ icon: vertical_align_bottom
+ exec:
+ - module: Screen_1
+ function_name: position
+ arguments: [1, "down"]
+
+```
diff --git a/drivers/place/meet_spec.cr b/drivers/place/meet_spec.cr
new file mode 100644
index 00000000000..e9a25e0a853
--- /dev/null
+++ b/drivers/place/meet_spec.cr
@@ -0,0 +1,98 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/switchable"
+
+# :nodoc:
+class DisplayMock < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Powerable
+ include PlaceOS::Driver::Interface::Muteable
+
+ enum MockInputs
+ HDMI
+ HDMI2
+ end
+
+ include PlaceOS::Driver::Interface::InputSelection(MockInputs)
+
+ # implement the abstract methods required by the interfaces
+ def power(state : Bool)
+ self[:power] = state
+ end
+
+ def switch_to(input : MockInputs)
+ mute(false)
+ self[:input] = input
+ end
+
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo,
+ )
+ self[:audio_mute] = state
+ end
+
+ def volume(level : Int32 | Float64)
+ self[:volume] = level
+ end
+end
+
+# :nodoc:
+class SwitcherMock < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Switchable(Int32, Int32)
+
+ def switch_to(input : Int32)
+ self[:input] = input
+ end
+
+ def switch(map : Hash(Input, Array(Output)), layer : SwitchLayer? = nil)
+ map.each do |(input, outputs)|
+ outputs.each do |output|
+ self["output#{output}"] = input
+ end
+ end
+ end
+end
+
+DriverSpecs.mock_driver "Place::Meet" do
+ system({
+ Display: {DisplayMock},
+ Switcher: {SwitcherMock},
+ })
+
+ settings({
+ connections: {
+ Display_1: {
+ hdmi: "Switcher_1.1",
+ },
+ Switcher_1: ["*Foo", "*Bar"],
+ },
+ local_outputs: ["Display_1"],
+ })
+
+ # Give the settings time to load
+ sleep 0.5
+
+ status["inputs"].as_a.should contain("Foo")
+ status["inputs"].as_a.should contain("Bar")
+ status["outputs"].as_a.should contain("Display_1")
+ status["output/Display_1"]["inputs"].should eq(["Foo", "Bar"])
+
+ exec(:power, true).get
+ status["active"]?.should eq true
+
+ exec(:route, "Foo", "Display_1").get
+ status["output/Display_1"]["source"].should eq(status["input/Foo"]["ref"])
+ system(:Display_1)["power"].should be_true
+
+ exec(:volume, 50, "Display_1").get
+ system(:Display_1)["volume"].should eq(50)
+ status["volume"]?.should eq(50)
+
+ exec(:mute, true, "Display_1").get
+ system(:Display_1)["audio_mute"].should be_true
+ status["mute"]?.should be_true
+
+ puts "Spec completed successfully"
+end
diff --git a/drivers/place/models/workplace_subscriptions.cr b/drivers/place/models/workplace_subscriptions.cr
new file mode 100644
index 00000000000..46874778f88
--- /dev/null
+++ b/drivers/place/models/workplace_subscriptions.cr
@@ -0,0 +1,201 @@
+require "placeos-driver"
+require "place_calendar"
+
+module Place::WorkplaceSubscription
+ enum NotifyType
+ # resource event changes
+ Created # a resource was created (MS only)
+ Updated # a resource was updated (in Google this could also mean created)
+ Deleted # a resource was deleted
+
+ # subscription lifecycle event (MS only)
+ Renew # subscription was deleted
+ Missed # MS sends this to mean resource event changes were not sent
+ Reauthorize # subscription needs reauthorization
+ end
+
+ struct NotifyEvent
+ include JSON::Serializable
+
+ getter event_type : NotifyType
+ getter resource_id : String?
+ getter resource_uri : String
+ getter subscription_id : String
+ getter client_secret : String
+
+ @[JSON::Field(converter: Time::EpochConverter)]
+ getter expiration_time : Time
+ end
+
+ abstract def subscription_on_crud(notification : NotifyEvent) : Nil
+ abstract def subscription_on_missed : Nil
+
+ enum ServiceName
+ Google
+ Office365
+ end
+
+ # should return the resource URI for monitoring, for example:
+ #
+ # case service_name
+ # in .google?
+ # resource = "/calendars/#{calendar_id}/events"
+ # in .office365?
+ # resource = "/users/#{calendar_id}/events"
+ abstract def subscription_resource(service_name : ServiceName) : String
+
+ @subscription : PlaceCalendar::Subscription? = nil
+ @push_notification_url : String? = nil
+ @push_authority : String? = nil
+ @push_service_name : ServiceName? = nil
+ @push_monitoring : PlaceOS::Driver::Subscriptions::ChannelSubscription? = nil
+ @push_mutex : Mutex = Mutex.new(:reentrant)
+
+ # the API reports that 6 days is the max:
+ # Subscription expiration can only be 10070 minutes in the future.
+ SUBSCRIPTION_LENGTH = 3.hours
+
+ protected def workplace_accessor
+ system["Calendar"]
+ end
+
+ protected def push_notificaitons_configure
+ @push_notification_url = setting?(String, :push_notification_url).presence
+ @push_authority = setting?(String, :push_authority).presence
+
+ # load any existing subscriptions
+ subscription = setting?(PlaceCalendar::Subscription, :push_subscription)
+
+ if @push_notification_url
+ # clear the monitoring if authority changed
+ if subscription && subscription.try(&.id) != @subscription.try(&.id) && (monitor = @push_monitoring)
+ subscriptions.unsubscribe(monitor)
+ @push_monitoring = nil
+ end
+ @subscription = subscription
+ schedule.every(5.minutes + rand(120).seconds) { push_notificaitons_maintain }
+ schedule.in(rand(30).seconds) { push_notificaitons_maintain(true) }
+ elsif subscription
+ push_notificaitons_cleanup(subscription)
+ end
+ end
+
+ # delete a subscription
+ protected def push_notificaitons_cleanup(sub)
+ @push_mutex.synchronize do
+ logger.debug { "removing subscription" }
+
+ workplace_accessor.delete_notifier(sub) if sub
+ @subscription = nil
+ define_setting(:push_subscription, nil)
+ end
+ end
+
+ getter sub_renewed_at : Time = 21.minutes.ago
+
+ # creates and maintains a subscription
+ protected def push_notificaitons_maintain(force_renew = false) : Nil
+ should_force = force_renew && @sub_renewed_at < 20.minutes.ago
+
+ @push_mutex.synchronize do
+ subscription = @subscription
+
+ logger.debug { "maintaining push subscription, monitoring: #{!!@push_monitoring}, subscription: #{subscription ? !subscription.expired? : "none"}" }
+
+ return create_subscription unless subscription
+
+ if should_force || subscription.expired?
+ # renew subscription
+ begin
+ logger.debug { "renewing subscription" }
+ expires = SUBSCRIPTION_LENGTH.from_now
+ sub = workplace_accessor.renew_notifier(subscription, expires.to_unix).get
+ @subscription = PlaceCalendar::Subscription.from_json(sub.to_json)
+
+ # save the subscription details for processing
+ define_setting(:push_subscription, @subscription)
+ @sub_renewed_at = Time.local
+ rescue error
+ logger.error(exception: error) { "failed to renew expired subscription, creating new subscription" }
+ @subscription = nil
+ schedule.in(1.second) { push_notificaitons_maintain; nil }
+ end
+
+ configure_push_monitoring
+ return
+ end
+
+ configure_push_monitoring if @push_monitoring.nil?
+ end
+ end
+
+ protected def configure_push_monitoring
+ subscription = @subscription.as(PlaceCalendar::Subscription)
+ channel_path = "#{subscription.id}/event"
+
+ if old = @push_monitoring
+ subscriptions.unsubscribe old
+ end
+
+ @push_monitoring = monitor(channel_path) { |_subscription, payload| push_event_occured(payload) }
+ logger.debug { "monitoring channel: #{channel_path}" }
+ end
+
+ protected def push_event_occured(payload : String)
+ logger.debug { "push notification received! #{payload}" }
+
+ notification = NotifyEvent.from_json payload
+
+ secret = @subscription.try &.client_secret
+ unless secret && secret == notification.client_secret
+ logger.warn { "ignoring notify event with mismatched secret: #{notification.inspect}" }
+ return
+ end
+
+ case notification.event_type
+ in .created?, .updated?, .deleted?
+ logger.debug { "polling events as received #{notification.event_type} notification" }
+ if resource_id = notification.resource_id
+ self[:last_event_notification] = {notification.event_type, resource_id, Time.utc.to_unix}
+ end
+
+ subscription_on_crud(notification)
+ in .missed?
+ # we don't know the exact event id that changed
+ logger.debug { "polling events as a notification was previously missed" }
+ subscription_on_missed
+ in .renew?
+ # we need to create a new subscription as the old one has expired
+ logger.debug { "a subscription renewal is required" }
+ create_subscription
+ in .reauthorize?
+ logger.debug { "a subscription reauthorization is required" }
+ expires = SUBSCRIPTION_LENGTH.from_now
+ workplace_accessor.reauthorize_notifier(@subscription, expires.to_unix)
+ end
+ rescue error
+ logger.error(exception: error) { "error processing push notification" }
+ end
+
+ protected def create_subscription
+ @push_mutex.synchronize do
+ @push_service_name = service_name = @push_service_name || ServiceName.parse(workplace_accessor.calendar_service_name.get.as_s)
+
+ # different resource routes for the different services
+ resource = subscription_resource(service_name)
+ logger.debug { "registering for push notifications! #{resource}" }
+
+ # create a new secret and subscription
+ expires = SUBSCRIPTION_LENGTH.from_now
+ push_secret = "a#{Random.new.hex(4)}"
+ sub = workplace_accessor.create_notifier(resource, @push_notification_url, expires.to_unix, push_secret, @push_notification_url).get
+ @subscription = PlaceCalendar::Subscription.from_json(sub.to_json)
+
+ # save the subscription details for processing
+ define_setting(:push_subscription, @subscription)
+ @sub_renewed_at = Time.local
+
+ configure_push_monitoring
+ end
+ end
+end
diff --git a/drivers/place/mqtt.cr b/drivers/place/mqtt.cr
new file mode 100644
index 00000000000..42ce6f9ffe7
--- /dev/null
+++ b/drivers/place/mqtt.cr
@@ -0,0 +1,155 @@
+require "placeos-driver"
+require "./mqtt_transport_adaptor"
+
+class Place::MQTT < PlaceOS::Driver
+ descriptive_name "Generic MQTT"
+ generic_name :GenericMQTT
+
+ tcp_port 1883
+ description %(makes MQTT data available to other drivers in PlaceOS, for use with String payloads)
+
+ default_settings({
+ username: "user",
+ password: "pass",
+ keep_alive: 60,
+ client_id: "placeos",
+ subscriptions: ["root/#"],
+
+ # requests per-second
+ rate_limit: 100,
+ queue_size: 1000,
+ })
+
+ @rate_limited : Bool = true
+ @queue_size : Int32 = 1000
+ @queue_count : Int32 = 0
+ @channel : Channel(Nil) = Channel(Nil).new(1)
+ @queue_lock : Mutex = Mutex.new
+ @wait_time : Time::Span = 300.milliseconds
+
+ @keep_alive : Int32 = 60
+ @username : String? = nil
+ @password : String? = nil
+ @client_id : String = "placeos"
+
+ @mqtt : ::MQTT::V3::Client? = nil
+ @subs : Array(String) = [] of String
+ @transport : Place::TransportAdaptor? = nil
+ @sub_proc : Proc(String, Bytes, Nil) = Proc(String, Bytes, Nil).new { |_key, _payload| nil }
+
+ def on_load
+ spawn { rate_limiter }
+ @sub_proc = Proc(String, Bytes, Nil).new { |key, payload| on_message(key, payload) }
+ on_update
+ end
+
+ def on_unload
+ @channel.close
+ end
+
+ def on_update
+ @username = setting?(String, :username)
+ @password = setting?(String, :password)
+ @keep_alive = setting?(Int32, :keep_alive) || 60
+ @client_id = setting?(String, :client_id) || ::MQTT.generate_client_id("placeos_")
+
+ @queue_size = setting?(Int32, :queue_size) || 1000
+ if rate_limit = setting?(Int32, :rate_limit)
+ @rate_limited = true
+ @wait_time = (1.0 / rate_limit.to_f).seconds
+ else
+ @rate_limited = false
+ end
+
+ existing = @subs
+ @subs = setting?(Array(String), :subscriptions) || [] of String
+
+ schedule.clear
+ schedule.every((@keep_alive // 3).seconds) { ping }
+
+ if client = @mqtt
+ unsub = existing - @subs
+ newsub = @subs - existing
+
+ unsub.each do |sub|
+ logger.debug { "unsubscribing to #{sub}" }
+ perform_operation { client.unsubscribe(sub) }
+ end
+
+ newsub.each do |sub|
+ logger.debug { "subscribing to #{sub}" }
+ perform_operation { client.subscribe(sub, &@sub_proc) }
+ end
+ end
+ end
+
+ def connected
+ transp = Place::TransportAdaptor.new(transport, queue)
+ client = ::MQTT::V3::Client.new(transp)
+ @transport = transp
+ @mqtt = client
+
+ logger.debug { "sending connect message" }
+ client.connect(@username, @password, @keep_alive, @client_id)
+ @subs.each do |sub|
+ logger.debug { "subscribing to #{sub}" }
+ perform_operation { client.subscribe(sub, &@sub_proc) }
+ end
+ end
+
+ def disconnected
+ @transport = nil
+ @mqtt = nil
+ end
+
+ protected def on_message(key : String, playload : Bytes) : Nil
+ self[key] = String.new(playload)
+ end
+
+ def publish(key : String, payload : String) : Nil
+ logger.debug { "publishing payload to #{key}" }
+ perform_operation { @mqtt.not_nil!.publish(key, payload) }
+ nil
+ end
+
+ def ping
+ logger.debug { "sending ping" }
+ perform_operation { @mqtt.not_nil!.ping }
+ end
+
+ def received(data, task)
+ logger.debug { "received #{data.size} bytes: 0x#{data.hexstring}" }
+ @transport.try &.process(data)
+ task.try &.success
+ end
+
+ protected def perform_operation
+ return yield unless @rate_limited
+
+ if @queue_count >= @queue_size
+ raise "queue size #{@queue_size} requests already queued, backpressure being applied"
+ end
+
+ @queue_lock.synchronize { @queue_count += 1 }
+ @channel.receive
+ @queue_lock.synchronize { @queue_count -= 1 }
+
+ yield
+ end
+
+ protected def rate_limiter
+ loop do
+ break if @channel.closed?
+ begin
+ @channel.send(nil)
+ rescue error
+ logger.error(exception: error) { "issue with rate limiter" }
+ ensure
+ sleep @wait_time
+ end
+ end
+ rescue
+ # Possible error with logging exception, restart rate limiter silently
+ spawn { rate_limiter } unless @channel.closed?
+ end
+end
diff --git a/drivers/place/mqtt_spec.cr b/drivers/place/mqtt_spec.cr
new file mode 100644
index 00000000000..d658439744d
--- /dev/null
+++ b/drivers/place/mqtt_spec.cr
@@ -0,0 +1,71 @@
+require "placeos-driver/spec"
+require "mqtt"
+
+DriverSpecs.mock_driver "Place::MQTT" do
+ # ============================
+ # CONNECTION
+ # ============================
+ puts "===== CONNECTION NEGOTIATION ====="
+ connect = MQTT::V3::Connect.new
+ connect.id = MQTT::RequestType::Connect
+ connect.keep_alive_seconds = 60_u16
+ connect.client_id = "placeos"
+ connect.clean_start = true
+ connect.username = "user"
+ connect.password = "pass"
+ connect.packet_length = connect.calculate_length
+ should_send(connect.to_slice)
+
+ connack = MQTT::V3::Connack.new
+ connack.id = MQTT::RequestType::Connack
+ connack.packet_length = connack.calculate_length
+ responds(connack.to_slice)
+
+ # ============================
+ # SUBSCRIPTION
+ # ============================
+ puts "===== SUBSCRIPTION REQUESTED ====="
+ packet = MQTT::V3::Subscribe.new
+ packet.id = MQTT::RequestType::Subscribe
+ packet.qos = MQTT::QoS::BrokerReceived
+ packet.message_id = 2_u16
+ packet.topic = "root/#"
+ packet.packet_length = packet.calculate_length
+ should_send(packet.to_slice)
+
+ suback = MQTT::V3::Suback.new
+ suback.id = MQTT::RequestType::Suback
+ suback.message_id = 2_u16
+ suback.return_codes = [MQTT::QoS::FireAndForget]
+ suback.packet_length = suback.calculate_length
+ responds(suback.to_slice)
+
+ # ============================
+ # REMOTE PUBLISH
+ # ============================
+ puts "===== REMOTE PUBLISH ====="
+ publish = MQTT::V3::Publish.new
+ publish.id = MQTT::RequestType::Publish
+ publish.message_id = 3_u16
+ publish.topic = "root/topic"
+ publish.payload = "testing"
+ publish.packet_length = publish.calculate_length
+
+ transmit publish.to_slice
+ sleep 0.1 # wait a bit for processing
+ status["root/topic"].should eq("testing")
+
+ # ============================
+ # DRIVER PUBLISH
+ # ============================
+ puts "===== DRIVER PUBLISH ====="
+ exec(:publish, "root/topic/action", "value")
+
+ publish = MQTT::V3::Publish.new
+ publish.id = MQTT::RequestType::Publish
+ publish.message_id = 3_u16
+ publish.topic = "root/topic/action"
+ publish.payload = "value"
+ publish.packet_length = publish.calculate_length
+ should_send(publish.to_slice)
+end
diff --git a/drivers/place/mqtt_transport_adaptor.cr b/drivers/place/mqtt_transport_adaptor.cr
new file mode 100644
index 00000000000..a3fef439df5
--- /dev/null
+++ b/drivers/place/mqtt_transport_adaptor.cr
@@ -0,0 +1,28 @@
+require "mqtt"
+
+class Place::TransportAdaptor < MQTT::Transport
+ def initialize(@driver, @queue)
+ super()
+ end
+
+ @driver : PlaceOS::Driver::Transport
+ @queue : PlaceOS::Driver::Queue
+
+ def close! : Nil
+ @driver.disconnect
+ end
+
+ def closed? : Bool
+ !@queue.online
+ end
+
+ def send(message) : Nil
+ @driver.send(message)
+ end
+
+ def process(data : Bytes)
+ @tokenizer.extract(data).each do |bytes|
+ spawn { @on_message.try &.call(bytes) }
+ end
+ end
+end
diff --git a/drivers/place/parking/locations.cr b/drivers/place/parking/locations.cr
new file mode 100644
index 00000000000..9cacab24dbf
--- /dev/null
+++ b/drivers/place/parking/locations.cr
@@ -0,0 +1,341 @@
+require "placeos-driver"
+require "placeos-driver/interface/locatable"
+require "../booking_model"
+require "placeos"
+require "json"
+
+# reserved parking spaces
+# check if any of these have been made available
+# fetch the parking bookings
+
+class Place::Parking::Locations < PlaceOS::Driver
+ include Interface::Locatable
+
+ descriptive_name "PlaceOS Parking Locations"
+ generic_name :ParkingLocations
+ description %(helper for handling parking bookings)
+
+ accessor area_manager : AreaManagement_1
+ accessor staff_api : StaffAPI_1
+
+ default_settings({
+ # time in seconds
+ poll_rate: 60,
+
+ # expose_for_analytics: {"output_key" => "booking_key->subkey"},
+ })
+
+ @timezone : Time::Location = Time::Location::UTC
+ @expose_for_analytics : Hash(String, String) = {} of String => String
+ @poll_rate : Time::Span = 60.seconds
+
+ BOOKING_TYPE = "parking"
+ RESERVED_RELEASED = "parking-released"
+ METADATA_KEY = "parking-spaces"
+
+ def on_load
+ monitor("staff/booking/changed") do |_subscription, payload|
+ logger.debug { "received booking changed event #{payload}" }
+ booking = Booking.from_json(payload)
+ booking.user_email = booking.user_email.downcase
+ booking_changed(booking)
+ end
+ on_update
+ end
+
+ def on_update
+ @poll_rate = (setting?(Int32, :poll_rate) || 60).seconds
+ @expose_for_analytics = setting?(Hash(String, String), :expose_for_analytics) || {} of String => String
+
+ timezone = config.control_system.not_nil!.timezone.presence || setting?(String, :time_zone).presence || "Australia/Sydney"
+ @timezone = Time::Location.load(timezone)
+
+ schedule.clear
+ schedule.every(@poll_rate) { query_parking_bookings }
+ schedule.in(5.seconds) { query_parking_bookings }
+ end
+
+ # level_zone_id => building_zone_id
+ getter level_buildings : Hash(String, String) do
+ hash = area_manager.level_buildings.get.as_h.transform_values(&.as_s)
+ raise "level cache not loaded yet" unless hash.size > 0
+ hash
+ end
+
+ getter zone_filter : Array(String) do
+ lvb = level_buildings
+ (lvb.keys + lvb.values).uniq
+ end
+
+ # ===================================
+ # Monitoring desk bookings
+ # ===================================
+ protected def booking_changed(event)
+ return unless event.booking_type == BOOKING_TYPE
+ matching_zones = zone_filter & event.zones
+ return if matching_zones.empty?
+
+ logger.debug { "booking event is in a matching zone" }
+
+ case event.action
+ when "create"
+ return unless event.in_progress?
+ # Check if this event is happening now
+ logger.debug { "adding new booking" }
+ @bookings[event.user_email] << event
+ when "cancelled", "rejected"
+ # delete the booking from the levels
+ found = false
+ @bookings[event.user_email].reject! { |booking| found = true if booking.id == event.id }
+ return unless found
+ when "check_in"
+ return unless event.in_progress?
+ @bookings[event.user_email].each { |booking| booking.checked_in = true if booking.id == event.id }
+ when "changed"
+ # Check if this booking is for today and update as required
+ @bookings[event.user_email].reject! { |booking| booking.id == event.id }
+ @bookings[event.user_email] << event if event.in_progress?
+ else
+ # ignore the update (approve)
+ logger.debug { "booking event was ignored" }
+ return
+ end
+
+ area_manager.update_available(matching_zones)
+ end
+
+ # ===================================
+ # Locatable Interface functions
+ # ===================================
+ def locate_user(email : String? = nil, username : String? = nil)
+ logger.debug { "searching for #{email}, #{username}" }
+ bookings = @bookings[email]? || [] of Booking
+ map_bookings(bookings)
+ end
+
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ logger.debug { "listing MAC addresses assigned to #{email}, #{username}" }
+ found = [] of String
+ @known_users.each { |user_id, (user_email, _name)|
+ found << user_id if email == user_email
+ }
+ found
+ end
+
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ logger.debug { "searching for owner of #{mac_address}" }
+ if user_details = @known_users[mac_address]?
+ email, _name = user_details
+ {
+ location: "booking",
+ assigned_to: email,
+ mac_address: mac_address,
+ }
+ end
+ end
+
+ def device_locations(zone_id : String, location : String? = nil)
+ logger.debug { "searching devices in zone #{zone_id}" }
+ return [] of Nil if location && location != "booking"
+
+ bookings = [] of Booking
+ @bookings.each_value(&.each { |booking|
+ next unless zone_id.in?(booking.zones)
+ bookings << booking
+ })
+ map_bookings(bookings)
+ end
+
+ protected def map_bookings(bookings)
+ level_to_building = level_buildings
+
+ bookings.map do |booking|
+ level = nil
+ building = nil
+ booking.zones.each do |zone_id|
+ if build = level_to_building[zone_id]?
+ building = build
+ level = zone_id
+ break
+ end
+ end
+
+ # We specify location as JSON::Any so we don't have to
+ # explicitly define the type of this object
+ payload = {
+ "location" => JSON::Any.new("booking"),
+ "type" => BOOKING_TYPE,
+ "checked_in" => booking.checked_in,
+ "asset_id" => booking.asset_id,
+ "booking_id" => booking.id,
+ "building" => building,
+ "level" => level,
+ "ends_at" => booking.booking_end,
+ "started_at" => booking.booking_start,
+ "duration" => booking.booking_end - booking.booking_start,
+ "mac" => booking.user_email,
+ "staff_name" => booking.user_name,
+ }
+
+ # check for any custom data we want to include
+ if !booking.extension_data.empty? && (init_data = JSON::Any.new(booking.extension_data))
+ @expose_for_analytics.each do |binding, path|
+ begin
+ binding_keys = path.split("->")
+ data = init_data
+ binding_keys.each do |key|
+ next if key == "extension_data"
+
+ data = data.dig? key
+ break unless data
+ end
+ payload[binding] = data
+ rescue error
+ logger.warn(exception: error) { "failed to expose #{binding}: #{path} for analytics" }
+ end
+ end
+ end
+
+ payload
+ end
+ end
+
+ # ===================================
+ # Parking and zone queries
+ # ===================================
+
+ struct ParkingSpace
+ include JSON::Serializable
+
+ property id : String
+ property name : String
+ property map_id : String
+ property assigned_to : String?
+ property assigned_name : String?
+
+ def reserved?
+ !!@assigned_to
+ end
+ end
+
+ struct Details
+ include JSON::Serializable
+
+ property details : Array(ParkingSpace)
+ end
+
+ alias Zone = PlaceOS::Client::API::Models::Zone
+ alias Metadata = Hash(String, Details)
+ alias ChildMetadata = Array(NamedTuple(zone: Zone, metadata: Metadata))
+
+ # Email => Array of bookings
+ @bookings : Hash(String, Array(Booking)) = Hash(String, Array(Booking)).new
+
+ # UserID => {Email, Name}
+ @known_users : Hash(String, Tuple(String, String)) = Hash(String, Tuple(String, String)).new
+
+ def parking_spaces : Hash(String, Array(ParkingSpace))
+ metadatas = level_buildings.values.uniq.map do |zone_id|
+ ChildMetadata.from_json(staff_api.metadata_children(
+ zone_id,
+ METADATA_KEY
+ ).get.to_json)
+ end
+
+ zone_parking = Hash(String, Array(ParkingSpace)).new
+
+ metadatas.each do |metadata|
+ metadata.each do |level|
+ zone = level[:zone]
+ if spaces = level[:metadata][METADATA_KEY]?.try(&.details)
+ zone_parking[zone.id] = spaces
+ end
+ end
+ end
+
+ zone_parking
+ end
+
+ def query_parking_bookings : Nil
+ # find all the reserved parking
+ reserved_spaces = parking_spaces.tap(&.each_value(&.select!(&.reserved?)))
+
+ logger.debug do
+ count = 0
+ reserved_spaces.each_value { |space| count += space.size }
+ "queried reserved spaces, found #{count}"
+ end
+
+ parking_zones = reserved_spaces.keys
+
+ # bookings for general access spaces
+ bookings = [] of JSON::Any
+ parking_zones.each { |zone| bookings.concat staff_api.query_bookings(type: BOOKING_TYPE, zones: {zone}).get.as_a }
+ bookings = bookings.map do |booking|
+ booking = Booking.from_json(booking.to_json)
+ booking.user_email = booking.user_email.downcase
+ booking
+ end
+
+ logger.debug { "queried parking bookings, found #{bookings.size}" }
+
+ # check if any of the reserved spaces have been made available
+ release_bookings = [] of JSON::Any
+ parking_zones.each { |zone| release_bookings.concat staff_api.query_bookings(type: RESERVED_RELEASED, zones: {zone}).get.as_a }
+ release_bookings = release_bookings.map do |booking|
+ booking = Booking.from_json(booking.to_json)
+ booking.user_email = booking.user_email.downcase
+ booking
+ end
+
+ logger.debug { "queried released spaces, found #{release_bookings.size}" }
+
+ # for all reserved spaces that haven't been released, we need to
+ # create a virtual booking for them
+ release_bookings.each do |booking|
+ parking_space = booking.asset_id
+ reserved_spaces.each_value do |spaces|
+ spaces.reject! { |space| space.id == parking_space }
+ end
+ end
+
+ now = Time.local(@timezone)
+ res_start = now.at_beginning_of_day.to_unix
+ res_end = now.at_end_of_day.to_unix
+ level_to_building = level_buildings
+
+ reserved_spaces.each do |level_zone, reservations|
+ building_zone = level_to_building[level_zone]?
+ next unless building_zone
+
+ reservations.each do |reservation|
+ bookings << Place::Booking.new(
+ id: -1,
+ booking_type: BOOKING_TYPE,
+ booking_start: res_start,
+ booking_end: res_end,
+ user_id: reservation.assigned_to.as(String),
+ user_email: reservation.assigned_to.as(String),
+ user_name: reservation.assigned_name.as(String),
+ zones: [level_zone, building_zone],
+ booked_by_name: reservation.assigned_name.as(String),
+ booked_by_email: reservation.assigned_to.as(String),
+ asset_id: reservation.id,
+ checked_in: true,
+ )
+ end
+ end
+
+ new_bookings = Hash(String, Array(Booking)).new do |hash, key|
+ hash[key] = [] of Booking
+ end
+
+ bookings.each do |booking|
+ next if booking.rejected
+ new_bookings[booking.user_email] << booking
+ @known_users[booking.user_id] = {booking.user_email, booking.user_name}
+ end
+
+ @bookings = new_bookings
+ end
+end
diff --git a/drivers/place/parking/locations_spec.cr b/drivers/place/parking/locations_spec.cr
new file mode 100644
index 00000000000..deddad83165
--- /dev/null
+++ b/drivers/place/parking/locations_spec.cr
@@ -0,0 +1,161 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Parking::Locations" do
+ system({
+ StaffAPI: {StaffAPIMock},
+ AreaManagement: {AreaManagementMock},
+ })
+
+ exec(:parking_spaces).get.should eq({
+ "zone-EYEnrhbaQz" => [
+ {
+ "id" => "park-001",
+ "name" => "Bay 001",
+ "map_id" => "park-001",
+ },
+ {
+ "id" => "parking-zone-FlWVOXv9yY.472179",
+ "name" => "Bay 005 Test",
+ "map_id" => "park-005",
+ "assigned_to" => "AdeleV@0cbfs.onmicrosoft.com",
+ "assigned_name" => "Adele Vance",
+ },
+ ],
+ })
+end
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ def query_bookings(type : String, zones : Array(String))
+ logger.debug { "Querying desk bookings!" }
+
+ now = Time.local
+ start = now.at_beginning_of_day.to_unix
+ ending = now.at_end_of_day.to_unix
+ [
+ {
+ id: 1,
+ booking_type: type,
+ booking_start: start,
+ booking_end: ending,
+ asset_id: "desk-123",
+ user_id: "user-1234",
+ user_email: "user1234@org.com",
+ user_name: "Bob Jane",
+ zones: zones + ["zone-building"],
+ checked_in: true,
+ rejected: false,
+ booked_by_name: "Bob Jane",
+ booked_by_email: "user1234@org.com",
+ },
+ {
+ id: 2,
+ booking_type: type,
+ booking_start: start,
+ booking_end: ending,
+ asset_id: "desk-456",
+ user_id: "user-456",
+ user_email: "zdoo@org.com",
+ user_name: "Zee Doo",
+ zones: zones + ["zone-building"],
+ checked_in: false,
+ rejected: false,
+ booked_by_name: "Zee Doo",
+ booked_by_email: "zdoo@org.com",
+ },
+ ]
+ end
+
+ def metadata_children(id : String, key : String? = nil)
+ logger.info { "requesting zone #{id} and key #{key}" }
+
+ [
+ {
+ "zone": {
+ "created_at": 1668744303,
+ "updated_at": 1668744303,
+ "id": "zone-FlWVOXv9yY",
+ "name": "PlaceOS Dev Sydney Catering Enabled",
+ "display_name": "Catering ",
+ "location": "",
+ "description": "",
+ "code": "",
+ "type": "",
+ "count": 0,
+ "capacity": 0,
+ "map_id": "",
+ "tags": [] of String,
+ "triggers": [] of String,
+ "parent_id": "zone-DnTcV5ZeEq",
+ },
+ "metadata": {} of String => String,
+ },
+ {
+ "zone": {
+ "created_at": 1691972553,
+ "updated_at": 1701398359,
+ "id": "zone-EYEnrhbaQz",
+ "name": "LEVEL Parking",
+ "display_name": "Parking",
+ "location": "",
+ "description": "",
+ "code": "",
+ "type": "",
+ "count": 0,
+ "capacity": 0,
+ "map_id": "https://s3-ap-southeast-2.amazonaws.com/os.place.tech/placeos-dev.aca.im/169197263162476823.svg",
+ "tags": [
+ "level",
+ "parking",
+ ],
+ "triggers": [] of String,
+ "parent_id": "zone-DnTcV5ZeEq",
+ },
+ "metadata": {
+ "parking-spaces": {
+ "name": "parking-spaces",
+ "description": "List of available parking spaces",
+ "details": [
+ {
+ "id": "park-001",
+ "name": "Bay 001",
+ "notes": "notes new",
+ "map_id": "park-001",
+ "assigned_to": nil,
+ "map_rotation": 0,
+ "assigned_name": nil,
+ "assigned_user": nil,
+ },
+ {
+ "id": "parking-zone-FlWVOXv9yY.472179",
+ "name": "Bay 005 Test",
+ "notes": "",
+ "map_id": "park-005",
+ "assigned_to": "AdeleV@0cbfs.onmicrosoft.com",
+ "map_rotation": 0,
+ "assigned_name": "Adele Vance",
+ },
+ ],
+ "parent_id": "zone-FlWVOXv9yY",
+ "editors": [] of String,
+ "modified_by_id": "user-DGLTbVU8eqiSRn",
+ },
+ },
+ },
+ ]
+ end
+end
+
+# :nodoc:
+class AreaManagementMock < DriverSpecs::MockDriver
+ def update_available(zones : Array(String))
+ logger.info { "requested update to #{zones}" }
+ nil
+ end
+
+ def level_buildings
+ {
+ "zone-EYEnrhbaQz": "zone-DnTcV5ZeEq",
+ }
+ end
+end
diff --git a/drivers/place/password_generator_helper.cr b/drivers/place/password_generator_helper.cr
new file mode 100644
index 00000000000..91ac343af92
--- /dev/null
+++ b/drivers/place/password_generator_helper.cr
@@ -0,0 +1,58 @@
+# Password defaults
+DEFAULT_PASSWORD_LENGTH = 6
+DEFAULT_PASSWORD_EXCLUDE = "0Oo1Il`'\\/"
+DEFAULT_PASSWORD_MINIMUM_LOWERCASE = 1
+DEFAULT_PASSWORD_MINIMUM_UPPERCASE = 0
+DEFAULT_PASSWORD_MINIMUM_NUMBERS = 1
+DEFAULT_PASSWORD_MINIMUM_SYMBOLS = 0
+
+PASSWORD_LOWERCASE_CHARACTERS = ('a'..'z').to_a
+PASSWORD_UPPERCASE_CHARACTERS = ('A'..'Z').to_a
+PASSWORD_NUMBER_CHARACTERS = ('0'..'9').to_a
+PASSWORD_SYMBOL_CHARACTERS = ['!', '@', '#', '$', '%', '^', '&', '*', '(', ')', '_', '+', '-', '=', '{', '}', '[', ']', '|', '\\', ':', ';', '"', '\'', '<', '>', ',', '.', '?', '/', '`', '~']
+
+def generate_password(
+ length : Int32? = DEFAULT_PASSWORD_LENGTH,
+ exclude : String? = DEFAULT_PASSWORD_EXCLUDE,
+ minimum_lowercase : Int32? = DEFAULT_PASSWORD_MINIMUM_LOWERCASE,
+ minimum_uppercase : Int32? = DEFAULT_PASSWORD_MINIMUM_UPPERCASE,
+ minimum_numbers : Int32? = DEFAULT_PASSWORD_MINIMUM_NUMBERS,
+ minimum_symbols : Int32? = DEFAULT_PASSWORD_MINIMUM_SYMBOLS
+) : String
+ length ||= DEFAULT_PASSWORD_LENGTH
+ exclude ||= DEFAULT_PASSWORD_EXCLUDE
+ minimum_lowercase ||= DEFAULT_PASSWORD_MINIMUM_LOWERCASE
+ minimum_uppercase ||= DEFAULT_PASSWORD_MINIMUM_UPPERCASE
+ minimum_numbers ||= DEFAULT_PASSWORD_MINIMUM_NUMBERS
+ minimum_symbols ||= DEFAULT_PASSWORD_MINIMUM_SYMBOLS
+
+ # Make sure the lenght is at least the minimums
+ minimums = minimum_lowercase + minimum_uppercase + minimum_numbers + minimum_symbols
+ length = minimums if length < minimums
+
+ characters = [] of Char
+ characters = PASSWORD_LOWERCASE_CHARACTERS if minimum_lowercase > 0
+ characters += PASSWORD_UPPERCASE_CHARACTERS if minimum_uppercase > 0
+ characters += PASSWORD_NUMBER_CHARACTERS if minimum_numbers > 0
+ characters += PASSWORD_SYMBOL_CHARACTERS if minimum_symbols > 0
+ characters = characters - exclude.chars
+
+ # make sure we have some characters to work with
+ if characters.empty?
+ characters = (PASSWORD_LOWERCASE_CHARACTERS + PASSWORD_NUMBER_CHARACTERS) - DEFAULT_PASSWORD_EXCLUDE.chars
+ end
+
+ password = [] of Char
+
+ # Add the minimums
+ minimum_lowercase.times { password << (PASSWORD_LOWERCASE_CHARACTERS - exclude.chars).sample(random: Random::Secure) }
+ minimum_uppercase.times { password << (PASSWORD_UPPERCASE_CHARACTERS - exclude.chars).sample(random: Random::Secure) }
+ minimum_numbers.times { password << (PASSWORD_NUMBER_CHARACTERS - exclude.chars).sample(random: Random::Secure) }
+ minimum_symbols.times { password << (PASSWORD_SYMBOL_CHARACTERS - exclude.chars).sample(random: Random::Secure) }
+
+ # Add the rest
+ (length - minimums).times { password << characters.sample(random: Random::Secure) }
+
+ # Shuffle the password
+ password.shuffle(random: Random::Secure).join
+end
diff --git a/drivers/place/pinger.cr b/drivers/place/pinger.cr
new file mode 100644
index 00000000000..f210ae7041d
--- /dev/null
+++ b/drivers/place/pinger.cr
@@ -0,0 +1,38 @@
+require "placeos-driver"
+require "pinger"
+
+class Place::Pinger < PlaceOS::Driver
+ descriptive_name "Device Pinger"
+ generic_name :Ping
+
+ # Discard port
+ udp_port 9
+ description %(periodically pings a device)
+
+ default_settings({
+ ping_every: 60,
+ })
+
+ def on_update
+ # Use quite a large random value to spread load
+ period = setting?(Int32, :ping_every) || 60
+ period = period * 1000 + rand(1000)
+
+ schedule.clear
+ schedule.every(period.milliseconds) { ping }
+ end
+
+ def ping
+ hostname = config.ip.not_nil!
+ pinger = ::Pinger.new(hostname, count: 3)
+ pinger.ping
+
+ pingable = pinger.pingable
+ if !pingable
+ self[:last_error] = pinger.exception || pinger.warning || "unknown error"
+ end
+
+ set_connected_state pingable
+ self[:pingable] = pingable
+ end
+end
diff --git a/drivers/place/pinger_spec.cr b/drivers/place/pinger_spec.cr
new file mode 100644
index 00000000000..b76080508fb
--- /dev/null
+++ b/drivers/place/pinger_spec.cr
@@ -0,0 +1,6 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::Pinger" do
+ exec(:ping).get.should eq(true)
+ status[:pingable].should eq(true)
+end
diff --git a/drivers/place/rbp_remote_logger.cr b/drivers/place/rbp_remote_logger.cr
new file mode 100644
index 00000000000..05905001380
--- /dev/null
+++ b/drivers/place/rbp_remote_logger.cr
@@ -0,0 +1,61 @@
+require "placeos-driver"
+require "json"
+
+class Place::RbpRemoteLogger < PlaceOS::Driver
+ descriptive_name "Log Receiver for Room Booking Panel app"
+ generic_name :Logger
+ description %(Recieve logs streamed from Room Booking Panel app)
+
+ default_settings({
+ enabled: false,
+ max_log_entries: 1000,
+ debug: false,
+ })
+
+ @enabled : Bool = false
+ @max_log_entries : Int32 = 1000
+ @debug : Bool = false
+ @entries : Hash(String, Array(JSON::Any)) = {} of String => Array(JSON::Any)
+
+ def on_update
+ @logging_enabled = setting?(Bool, "enabled") || true
+ @max_log_entries = setting?(Int32, "max_log_entries") || 1000
+ @debug = setting?(Bool, "debug") || false
+
+ self[:enabled] = @logging_enabled
+ end
+
+ def post_event(payload : JSON::Any | String)
+ logger.debug { "Received: #{payload}" } if @debug
+
+ payload = payload.to_json if payload.is_a?(JSON::Any)
+ payload = payload.to_s if payload.is_a?(String)
+
+ entry = Entry.from_json(payload)
+
+ @entries[entry.device_id] ||= [] of JSON::Any
+
+ @entries[entry.device_id] =
+ @entries
+ .[entry.device_id]
+ .unshift(JSON.parse(payload))
+ .truncate(0, @max_log_entries)
+
+ self[:entries] = @entries
+
+ entry
+ end
+
+ class Entry
+ include JSON::Serializable
+
+ property id : String
+ property device_id : String
+ property type : String # Enum 'network' | 'console' | 'dom'
+ property subtype : String
+ property timestamp : Int64
+ property raw : JSON::Any
+ property data : JSON::Any
+ property metadata : JSON::Any
+ end
+end
diff --git a/drivers/place/rbp_remote_logger_spec.cr b/drivers/place/rbp_remote_logger_spec.cr
new file mode 100644
index 00000000000..239d67df95a
--- /dev/null
+++ b/drivers/place/rbp_remote_logger_spec.cr
@@ -0,0 +1,23 @@
+require "placeos-driver/spec"
+require "uuid"
+
+DriverSpecs.mock_driver "Place::RbpRemoteLogger" do
+ subpayload = {"id" => "1"}
+
+ payload = {
+ "id" => "1",
+ "type" => "3",
+ "subtype" => "4",
+ "timestamp" => 5,
+ "raw" => subpayload,
+ "data" => subpayload,
+ "metadata" => subpayload,
+ }
+
+ 5.times do
+ payload.merge!({"device_id" => UUID.random.to_s})
+ entry = exec(:post_event, payload.to_json).get.not_nil!
+ end
+
+ status.[:entries].as_h.keys.size.should eq 5
+end
diff --git a/drivers/place/room_at_capacity_mailer.cr b/drivers/place/room_at_capacity_mailer.cr
new file mode 100644
index 00000000000..3f321161775
--- /dev/null
+++ b/drivers/place/room_at_capacity_mailer.cr
@@ -0,0 +1,148 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+
+class Place::RoomAtCapacityMailer < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+
+ descriptive_name "PlaceOS Room at capacity mailer"
+ generic_name :RoomAtCapacityMailer
+ description %(notifies when a room is at capacity)
+
+ default_settings({
+ notify_email: ["concierge@place.com"],
+ email_template: "room_at_capacity",
+ debounce_time_minutes: 60, # the time to wait before sending another email
+ check_every_minutes: 5, # the frequency to check rooms
+ over_capactity_detected_count: 2, # the number of times over capacity before sending an email
+ })
+
+ accessor staff_api : StaffAPI_1
+ accessor locations : LocationServices_1
+
+ def mailer
+ system.implementing(Interface::Mailer)[0]
+ end
+
+ getter building_id : String do
+ locations.building_id.get.as_s
+ end
+
+ # Grabs the list of systems in the building
+ getter systems : Hash(String, Array(String)) do
+ staff_api.systems_in_building(building_id).get.as_h.transform_values(&.as_a.map(&.as_s))
+ end
+
+ def on_load
+ on_update
+ end
+
+ @notify_email : Array(String) = [] of String
+ @email_template : String = "room_at_capacity"
+ @debounce_time_minutes : Int32 = 60
+ @over_capactity_detected_count : Int32 = 2
+
+ @last_email_sent : Hash(String, Time) = {} of String => Time
+ @over_capacity : Hash(String, Int32) = Hash(String, Int32).new { |hash, sys_id| hash[sys_id] = 0 }
+
+ def on_update
+ @building_id = nil
+ @systems = nil
+
+ @notify_email = setting?(Array(String), :notify_email) || [] of String
+ @email_template = setting?(String, :email_template) || "room_at_capacity"
+ @debounce_time_minutes = setting?(Int32, :debounce_time_minutes) || 60
+ @over_capactity_detected_count = setting?(Int32, :over_capactity_detected_count) || 2
+
+ period = setting?(Int32, :check_every_minutes) || 5
+ schedule.clear
+ schedule.every(period.minutes) { check_capacity }
+ end
+
+ def check_capacity
+ systems.each do |level_id, system_ids|
+ system_ids.each do |system_id|
+ sys = system(system_id)
+ next unless sys.exists?("Bookings", 1)
+ next unless sys.capacity > 0
+
+ if people_count = sys.get("Bookings", 1).status?(Float64, "people_count")
+ logger.debug { "people count for #{system_id}: #{people_count}" }
+
+ if people_count >= sys.capacity
+ @over_capacity[system_id] += 1
+ else
+ @over_capacity[system_id] = 0
+ end
+
+ if (over = @over_capacity[system_id]?) && over == @over_capactity_detected_count
+ send_email(
+ sys.capacity,
+ people_count,
+ system_id,
+ sys.name,
+ sys.display_name,
+ sys.description,
+ sys.email,
+ )
+ end
+ end
+ end
+ end
+ end
+
+ @[Security(Level::Support)]
+ def send_email(
+ capacity : Int32,
+ people_count : Float64,
+ system_id : String,
+ name : String? = nil,
+ display_name : String? = nil,
+ description : String? = nil,
+ system_email : String? = nil,
+ )
+ if (last = @last_email_sent[system_id]?) && Time.utc - last < @debounce_time_minutes.minutes
+ logger.debug { "skipping email for #{system_id} due to debounce timer" }
+ return
+ end
+
+ args = {
+ system_id: system_id,
+ name: name,
+ display_name: display_name,
+ description: description,
+ system_email: system_email,
+ capacity: capacity,
+ people_count: people_count,
+ }
+
+ begin
+ mailer.send_template(
+ to: @notify_email,
+ template: {"room_at_capacity", @email_template},
+ args: args)
+ @last_email_sent[system_id] = Time.utc
+ rescue error
+ logger.warn(exception: error) { "failed to send at capacity email for zone #{system_id}" }
+ end
+ end
+
+ def template_fields : Array(TemplateFields)
+ [
+ TemplateFields.new(
+ trigger: {"room_at_capacity", @email_template},
+ name: "Room at capacity",
+ description: "Notification when a room is at capacity",
+ fields: [
+ {name: "system_id", description: "Identifier of the room/system"},
+ {name: "name", description: "Room name"},
+ {name: "display_name", description: "Room display name"},
+ {name: "description", description: "Room description"},
+ {name: "system_email", description: "System/room email address"},
+ {name: "capacity", description: "Capacity of the room"},
+ {name: "people_count", description: "Number of people in the room"},
+ ]
+ ),
+ ]
+ end
+end
diff --git a/drivers/place/room_booking_approval.cr b/drivers/place/room_booking_approval.cr
new file mode 100644
index 00000000000..d7c7c8d610b
--- /dev/null
+++ b/drivers/place/room_booking_approval.cr
@@ -0,0 +1,72 @@
+require "placeos-driver"
+require "place_calendar"
+
+class Place::RoomBookingApproval < PlaceOS::Driver
+ descriptive_name "PlaceOS Room Booking Approval"
+ generic_name :RoomBookingApproval
+ description %(Room Booking approval for tentative events)
+
+ default_settings({} of String => String)
+
+ accessor calendar : Calendar_1
+
+ getter building_id : String { get_building_id.not_nil! }
+ getter systems : Hash(String, Array(String)) { get_systems_list.not_nil! }
+
+ def on_update
+ @building_id = nil
+ @systems = nil
+
+ schedule.clear
+ # used to detect changes in building configuration
+ schedule.every(1.hour) { @systems = get_systems_list.not_nil! }
+
+ # The search
+ schedule.every(5.minutes) { find_bookings_for_approval }
+ end
+
+ # Finds the building ID for the current location services object
+ def get_building_id
+ zone_ids = system["StaffAPI"].zones(tags: "building").get.as_a.map(&.[]("id").as_s)
+ (zone_ids & system.zones).first
+ rescue error
+ logger.warn(exception: error) { "unable to determine building zone id" }
+ nil
+ end
+
+ # Grabs the list of systems in the building
+ def get_systems_list
+ system["StaffAPI"].systems_in_building(building_id).get.as_h.transform_values(&.as_a.map(&.as_s))
+ rescue error
+ logger.warn(exception: error) { "unable to obtain list of systems in the building" }
+ nil
+ end
+
+ def find_bookings_for_approval : Hash(String, Array(PlaceCalendar::Event))
+ results = {} of String => Array(PlaceCalendar::Event)
+
+ systems.each do |level_id, system_ids|
+ system_ids.each do |system_id|
+ sys = system(system_id)
+ if sys.exists?("Bookings", 1)
+ if bookings = sys.get("Bookings", 1).status?(Array(PlaceCalendar::Event), "bookings")
+ bookings.select! { |event| event.status == "tentative" }
+ results[system_id] = bookings unless bookings.empty?
+ end
+ end
+ end
+ end
+
+ self[:approval_required] = results
+ end
+
+ @[Security(Level::Support)]
+ def accept_event(calendar_id : String, event_id : String, user_id : String? = nil, notify : Bool = false, comment : String? = nil)
+ calendar.accept_event(calendar_id: calendar_id, event_id: event_id, user_id: user_id, notify: notify, comment: comment)
+ end
+
+ @[Security(Level::Support)]
+ def decline_event(calendar_id : String, event_id : String, user_id : String? = nil, notify : Bool = false, comment : String? = nil)
+ calendar.decline_event(calendar_id: calendar_id, event_id: event_id, user_id: user_id, notify: notify, comment: comment)
+ end
+end
diff --git a/drivers/place/room_booking_approval_spec.cr b/drivers/place/room_booking_approval_spec.cr
new file mode 100644
index 00000000000..f87901b0d22
--- /dev/null
+++ b/drivers/place/room_booking_approval_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::RoomBookingApprovalAltnerative" do
+end
diff --git a/drivers/place/router.cr b/drivers/place/router.cr
new file mode 100644
index 00000000000..82a9765bbbe
--- /dev/null
+++ b/drivers/place/router.cr
@@ -0,0 +1,46 @@
+require "placeos-driver"
+
+# this driver only exists to test router functionality
+# please use the meet driver
+
+# :nodoc:
+class Place::RouterTest < PlaceOS::Driver
+ generic_name :Switcher
+ descriptive_name "Signal router"
+ description <<-DESC
+ A virtual matrix switcher for arbitrary signal networks.
+
+ Following configuration, this driver can be used to perform simple input → \
+ output routing, regardless of intermediate hardware. Drivers it interacts \
+ with _must_ implement the `Switchable`, `InputSelection` or `Muteable` \
+ interfaces.
+
+ Configuration is specified as a map of devices and their attached inputs. \
+ This must exist under a top-level `connections` key.
+
+ Inputs can be either named:
+
+ Display_1:
+ hdmi: VidConf_1
+
+ Or, index based:
+
+ Switcher_1:
+ - Camera_1
+ - Camera_2
+
+ If an input is not a device with an associated module, prefix with an \
+ asterisk (`*`) to create a named alias.
+
+ Display_1:
+ hdmi: *Laptop
+
+ DESC
+end
+
+require "./router/core"
+
+# :nodoc:
+class Place::RouterTest < PlaceOS::Driver
+ include Router::Core
+end
diff --git a/drivers/place/router/core.cr b/drivers/place/router/core.cr
new file mode 100644
index 00000000000..56d00cbb0e5
--- /dev/null
+++ b/drivers/place/router/core.cr
@@ -0,0 +1,275 @@
+require "placeos-driver"
+require "levenshtein"
+require "promise"
+
+require "./settings"
+require "./signal_graph"
+
+# Core routing methods and functionality. This exists as module to enable
+# inclusion in other drivers, such as room logic, that provide auxillary
+# functionality to signal distribution.
+module Place::Router::Core
+ alias NodeRef = SignalGraph::Node::Ref
+
+ # Wrapper for providng simple interaction with a signal node and it's
+ # associated driver.
+ struct SignalNode
+ @label : SignalGraph::Node::Label
+ @proxy : Future::Compute(PlaceOS::Driver::Proxy::Driver)
+
+ def initialize(@label, @proxy)
+ end
+
+ forward_missing_to @label
+
+ def proxy
+ @proxy.get
+ end
+
+ def to_s(io)
+ io << ref
+ end
+
+ def watch(&handler : self ->)
+ @label.watch { handler.call self }
+ end
+ end
+
+ private getter! siggraph : SignalGraph
+
+ private getter! resolver : Hash(String, NodeRef)
+
+ getter current_routes : Hash(String, String?) = {} of String => String?
+
+ def on_update
+ load_siggraph
+ end
+
+ protected def load_siggraph
+ logger.debug { "loading signal graph from settings" }
+ connections = setting(Settings::Connections::Map, :connections)
+ load_siggraph connections
+ end
+
+ protected def load_siggraph(connections : Settings::Connections::Map)
+ nodes, links, aliases = Settings::Connections.parse connections, system.id
+ @siggraph = SignalGraph.build nodes, links
+ @resolver = init_resolver aliases
+ on_siggraph_load
+ end
+
+ protected def init_resolver(seed)
+ resolver = Hash(String, NodeRef).new(initial_capacity: seed.size) do |cache, key|
+ if ref = NodeRef.resolve? key, system.id
+ cache[key] = ref
+ else
+ alt = Levenshtein.find key, cache.keys, 3
+ msg = String.build do |err|
+ err << %(unknown signal node "#{key}")
+ err << %( - did you mean "#{alt}"?) if alt
+ end
+ raise KeyError.new msg
+ end
+ end
+ resolver.merge! seed
+ resolver
+ end
+
+ # Reads settings with node metadata into the graph.
+ protected def load_io(key : Symbol) : Enumerable(SignalGraph::Node::Label)?
+ logger.debug { "loading #{key}" }
+ if io = setting?(Settings::IOMeta, key)
+ io.map do |(key, meta)|
+ ref = resolver[key]
+ node = siggraph[ref]
+ node.meta = meta
+ node
+ end
+ else
+ logger.debug { "no #{key} configured" }
+ nil
+ end
+ end
+
+ protected def on_siggraph_load
+ aliases = resolver.invert
+ to_name = ->(ref : NodeRef) { aliases[ref]? || ref.local(system.id) }
+
+ inputs = load_io(:inputs) || siggraph.inputs.to_a
+ outputs = load_io(:outputs) || siggraph.outputs.to_a
+
+ # Persist previous state across module restarts or settings load
+ persist = ->(key : String, node : SignalGraph::Node::Label) do
+ self[key]?.try(&.as_h?).try &.each do |attr, value|
+ case attr
+ when "ref"
+ # Ignore
+ when "source"
+ node.source = signal_node(value.as_s).ref
+ when "locked"
+ node.locked = value.as_bool
+ else
+ node[attr] = value
+ end
+ rescue e
+ logger.info(exception: e) { "when loading previous #{key}/#{attr}" }
+ end
+ end
+
+ # Expose a list of input keys, along with an `input/` with a hash of
+ # metadata and state info for each.
+ self[:inputs] = inputs.map do |node|
+ key = to_name.call node.ref
+ persist.call "input/#{key}", node
+ node["name"] ||= key
+ node.watch { self["input/#{key}"] = node }
+ key
+ end
+
+ # As above, but for the outputs.
+ self[:outputs] = outputs.map do |node|
+ key = to_name.call node.ref
+
+ persist.call "output/#{key}", node
+ source_ref = node.source
+ current_routes[key] = source_ref ? to_name.call(source_ref.as(NodeRef)) : nil
+ node["name"] ||= key
+
+ # Discover inputs available to each output
+ reachable = siggraph.inputs(node.ref).select &.in?(inputs)
+ node["inputs"] = reachable.map(&.ref).map(&to_name).to_a
+
+ node.watch do
+ source_ref = node.source
+ current_routes[key] = source_ref ? to_name.call(source_ref.as(NodeRef)) : nil
+ self["output/#{key}"] = node
+ end
+ key
+ end
+
+ inodes, onodes = {inputs, outputs}.map &.each.map { |n| signal_node n.ref }
+ on_siggraph_loaded inodes, onodes
+ end
+
+ # Optional callback for overriding by driver extending this.
+ protected def on_siggraph_loaded(input, outputs)
+ end
+
+ protected def signal_node(key : String)
+ ref = resolver[key]
+ signal_node ref
+ end
+
+ protected def signal_node(ref : NodeRef)
+ node = siggraph[ref]
+
+ proxy = lazy do
+ case ref
+ when SignalGraph::Device, SignalGraph::Input, SignalGraph::Output
+ proxy_for ref.mod
+ else
+ raise "no device associated with #{ref}"
+ end
+ end
+
+ SignalNode.new node, proxy
+ end
+
+ protected def proxy_for(mod : SignalGraph::Mod)
+ (mod.sys == system.id ? system : system mod.sys).get mod.name, mod.idx
+ end
+
+ # Routes signal from *input* to *output*.
+ #
+ # Performs all intermediate device interaction based on current system
+ # config.
+ def route_signal(input : String, output : String, max_dist : Int32? = nil, simulate : Bool = false, follow_additional_routes : Bool = true)
+ logger.debug { "requesting route from #{input} to #{output}" }
+
+ src, dst = resolver.values_at input, output
+ dst_node = siggraph[dst]
+ src_node = siggraph[src]
+
+ path = siggraph.route(src, dst, max_dist) || raise "no route found"
+
+ execs = path.compact_map do |(node, edge, next_node)|
+ logger.debug { "#{node} → #{next_node}" }
+
+ raise "#{next_node} is locked, aborting" if next_node.locked
+
+ case edge
+ in SignalGraph::Edge::Static
+ nil
+ in SignalGraph::Edge::Active
+ Promise.defer(timeout: 1.second) do
+ next_node.source = siggraph[src].source
+
+ # OPTIMIZE: split this to perform an inital pass to build a hash
+ # from Driver::Proxy => [Edge::Active] then form the minimal set of
+ # execs that satisfies these.
+ if !simulate
+ mod = proxy_for edge.mod
+ case func = edge.func
+ in SignalGraph::Edge::Func::Mute
+ # check if we want to mute a video or audio layer
+ dst_layer = dst_node.ref.layer.downcase
+ case dst_layer
+ when "audio", "video"
+ mod.mute func.state, func.index, dst_layer
+ else
+ mod.mute func.state, func.index
+ end
+ in SignalGraph::Edge::Func::Select
+ mod.switch_to func.input
+
+ # ensure the device is unmuted
+ mod.mute(false, layer: :video) if mod.implements?(::PlaceOS::Driver::Interface::Muteable)
+ in SignalGraph::Edge::Func::Switch
+ mod.switch({func.input => [func.output]}, func.layer)
+ end
+ end
+ nil
+ end
+ end
+ end
+
+ # are there any additional switching actions to perform (combined outputs)
+ if follow_additional_routes
+ routes = {} of String => Tuple(String, String, Int32?, Bool, Bool)
+
+ if following_outputs = dst_node["followers"]?.try(&.as_a)
+ logger.debug { "routing #{following_outputs.size} additional followers" }
+ following_outputs.each { |output_follow| routes[output_follow.as_s] = {input, output_follow.as_s, max_dist, simulate, false} }
+ end
+
+ ignore_source_routes = dst_node["ignore_source_routes"]?.try(&.as_bool) || false
+
+ # perform_routes: {output: input}
+ if !ignore_source_routes && (additional_routes = src_node["perform_routes"]?.try(&.as_h))
+ logger.debug { "perfoming #{additional_routes.size} additional routes" }
+ additional_routes.each { |ad_output, ad_input| routes[ad_output] = {ad_input.as_s, ad_output, max_dist, simulate, false} }
+ end
+
+ spawn {
+ routes.each_value do |route|
+ begin
+ route_signal(*route)
+ rescue error
+ logger.warn(exception: error) { "issue routing: #{route[0]}=>#{route[1]}" }
+ end
+ end
+ }
+ end
+
+ logger.debug { "awaiting responses" }
+ execs.each do |promise|
+ begin
+ promise.get
+ rescue error
+ logger.warn(exception: error) { "processing route" }
+ end
+ end
+
+ :ok
+ end
+end
diff --git a/drivers/place/router/digraph.cr b/drivers/place/router/digraph.cr
new file mode 100644
index 00000000000..455475684f9
--- /dev/null
+++ b/drivers/place/router/digraph.cr
@@ -0,0 +1,224 @@
+# Labelled digraph. Holds node labels of type *N* and edge labels of type *E*.
+#
+# Nodes are stored on UInt64 ID's. This provides an interface that should feel
+# similar to `Indexable` for interacting with nodes labels. Similarly edges can
+# be placed and retrieved by using a dual index of {predescessor, successor}.
+#
+# OPTIMIZE: replace with a sparse matrix and graphBLAS operations.
+class Place::Router::Digraph(N, E)
+ class Error < Exception; end
+
+ record Node(N, E),
+ attr : N,
+ succ : Hash(UInt64, E)
+
+ @nodes : Hash(UInt64, Node(N, E))
+
+ delegate clear, to: @nodes
+
+ def initialize(initial_capacity = nil)
+ @nodes = Hash(UInt64, Node(N, E)).new initial_capacity: initial_capacity
+ end
+
+ private def node(id)
+ node(id) { raise Error.new "Node #{id} does not exist" }
+ end
+
+ private def node(id, &)
+ id = id.to_u64
+ @nodes.fetch(id) { yield id }
+ end
+
+ private def check_node_exists(id)
+ check_node_exists(id) { raise Error.new "Node #{id} does not exist" }
+ end
+
+ private def check_node_exists(id, &)
+ id = id.to_u64
+ @nodes.has_key?(id) ? id : yield id
+ end
+
+ # Retrieves the label attached to node *id*.
+ def [](id)
+ node(id).attr
+ end
+
+ # Retrieves the label attached to node *id*. Yields if it does not exist.
+ def fetch(id, &) : N
+ node = node(id) { return yield id }
+ node.attr
+ end
+
+ # Insert a new node.
+ def []=(id, attr)
+ insert(id, attr) { raise Error.new "Node #{attr.inspect} (#{id}) already exists" }
+ end
+
+ # Inserts a node. Yields if it already exists.
+ def insert(id, attr : N, &)
+ id = id.to_u64
+ if @nodes.has_key? id
+ yield id
+ else
+ @nodes[id] = Node(N, E).new attr, {} of UInt64 => E
+ end
+ end
+
+ # Retrieves the label attached to the edge that joins *pred_id* and *succ_id*.
+ def [](pred_id, succ_id)
+ fetch(pred_id, succ_id) do
+ raise Error.new "Edge #{pred_id} -> #{succ_id} does not exist"
+ end
+ end
+
+ # :ditto:
+ def fetch(pred_id, succ_id, &) : E
+ succ_id = check_node_exists succ_id
+ node(pred_id).succ.fetch(succ_id) { yield pred_id, succ_id }
+ end
+
+ # Inserts an edge.
+ def []=(pred_id, succ_id, attr)
+ insert(pred_id, succ_id, attr) do
+ raise Error.new "Edge #{pred_id} -> #{succ_id} already exists"
+ end
+ end
+
+ # :ditto:
+ def insert(pred_id, succ_id, attr : E, &)
+ succ_id = check_node_exists succ_id
+ pred = node pred_id
+ if pred.succ.has_key? succ_id
+ yield pred_id, succ_id
+ else
+ pred.succ[succ_id] = attr
+ end
+ end
+
+ # Perform a breadth first search across the graph, starting at *from*.
+ #
+ # Each node id is yielded as it's traversed. The search will terminate when
+ # this block returns true. If `nil` is returned the node is skipped, but the
+ # traversal continues.
+ #
+ # Results are provided as a Hash that includes all reached nodes as the keys,
+ # and their predecessor as the associated value.
+ def breadth_first_search(from, & : UInt64 -> Bool?)
+ paths = Hash(UInt64, UInt64).new
+ queue = Deque(UInt64).new 1, from
+
+ while pred_id = queue.shift?
+ node(pred_id).succ.each_key do |succ_id|
+ # Already visited
+ next if paths.has_key? succ_id
+
+ done = yield succ_id
+
+ next if done.nil?
+
+ paths[succ_id] = pred_id
+
+ return paths if done
+
+ queue << succ_id
+ end
+ end
+ end
+
+ # Returns a list of node IDs that form the shortest path between the passed
+ # nodes or `nil` if no path exists.
+ def path(from, to, invert = false) : Enumerable(UInt64)?
+ from = check_node_exists from
+ to = check_node_exists to
+
+ paths = breadth_first_search from, &.== to
+ return if paths.nil?
+
+ # Unwind the path captured in the hash.
+ nodes = [to]
+ until nodes.last == from
+ nodes << paths[nodes.last]
+ end
+
+ invert ? nodes : nodes.reverse!
+ end
+
+ # Provides all nodes present within the graph.
+ #
+ # NOTE: ordering of nodes is _not_ defined.
+ def nodes : Enumerable(UInt64)
+ @nodes.each_key
+ end
+
+ # Checks if a node has incoming edges only.
+ def sink?(id) : Bool
+ outdegree(id).zero? && !indegree(id).zero?
+ end
+
+ # Provides all nodes with incoming edges only.
+ def sinks : Enumerable(UInt64)
+ nodes.select { |id| sink? id }
+ end
+
+ # Checks if a node has outgoing edges only.
+ def source?(id) : Bool
+ !outdegree(id).zero? && indegree(id).zero?
+ end
+
+ # Provides all nodes with outgoing edges only.
+ #
+ # OPTIMIZE: this is _very_ slow [O(V * E)], but works for testing purposes.
+ # Switching the sparse matrix should assist so not worth optimising for this
+ # setup.
+ def sources : Enumerable(UInt64)
+ nodes.select { |id| source? id }
+ end
+
+ # The outgoing edges from *id*.
+ def outdegree(id)
+ node(id).succ.size
+ end
+
+ # The number of incomming edges to *id*.
+ def indegree(id)
+ id = check_node_exists id
+ @nodes.reduce(0) do |count, (_, node)|
+ count += 1 if node.succ.has_key? id
+ count
+ end
+ end
+
+ # Provides all nodes reachable from *id*.
+ def subtree(id) : Enumerable(UInt64)
+ id = check_node_exists id
+ SubtreeIterator.new self, id
+ end
+
+ private class SubtreeIterator
+ include Iterator(UInt64)
+
+ @ch = Channel(UInt64).new
+
+ def initialize(g, id)
+ spawn do
+ g.breadth_first_search id do |node|
+ begin
+ @ch.send node
+ false
+ rescue Channel::ClosedError
+ true
+ end
+ end
+ @ch.close unless @ch.closed?
+ end
+ end
+
+ def finalize
+ @ch.close unless @ch.closed?
+ end
+
+ def next
+ @ch.receive? || stop
+ end
+ end
+end
diff --git a/drivers/place/router/digraph_spec.cr b/drivers/place/router/digraph_spec.cr
new file mode 100644
index 00000000000..11f64f9a7aa
--- /dev/null
+++ b/drivers/place/router/digraph_spec.cr
@@ -0,0 +1,147 @@
+require "spec"
+require "./digraph"
+
+alias Digraph = Place::Router::Digraph
+
+describe Digraph do
+ describe "node insertion / retrieval" do
+ it "inserts a node with the specified ID" do
+ g = Digraph(String, String).new
+ g[42] = "foo"
+ g[42].should eq("foo")
+ end
+
+ it "raises when inserting on ID conflict" do
+ g = Digraph(String, String).new
+ expect_raises(Digraph::Error) do
+ g[42] = "foo"
+ g[42] = "bar"
+ end
+ end
+
+ it "raises when retrieving if node does not exist" do
+ g = Digraph(String, String).new
+ expect_raises(Digraph::Error) do
+ g[123]
+ end
+ end
+ end
+
+ describe "edge insertion / retrieval" do
+ it "inserts between the specified IDs" do
+ g = Digraph(String, String).new
+ g[0] = "foo"
+ g[1] = "bar"
+ g[0, 1] = "foobar"
+ g[0, 1].should eq("foobar")
+ end
+
+ it "raises if setting an edge that already exists" do
+ g = Digraph(String, String).new
+ expect_raises(Digraph::Error) do
+ g.insert(0, "foo") { }
+ g.insert(1, "bar") { }
+ g[0, 1] = "foobar"
+ g[0, 1] = "foobar"
+ end
+ end
+
+ it "raises when reading an edge that does not exist" do
+ g = Digraph(String, String).new
+ expect_raises(Digraph::Error) do
+ g[1, 0]
+ end
+ end
+ end
+
+ describe "#path" do
+ it "works on a trival graph" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[2] = "c"
+ g[0, 1] = "ab"
+ g[1, 2] = "bc"
+ g.path(0, 2).should eq([0, 1, 2])
+ g.path(2, 0).should be_nil
+ end
+
+ it "finds the shortest path" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[2] = "c"
+ g[0, 1] = "ab"
+ g[1, 2] = "bc"
+
+ g[3] = "x"
+ g[4] = "y"
+ g[5] = "z"
+ g[0, 3] = "ax"
+ g[3, 4] = "xy"
+ g[4, 5] = "yz"
+ g[5, 2] = "zc"
+
+ g.path(0, 2).should eq([0, 1, 2])
+ end
+ end
+
+ describe "#nodes" do
+ it "provides all nodes" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[2] = "c"
+ (g.nodes.to_a - [0, 1, 2]).should be_empty
+ end
+ end
+
+ describe "#outdegree" do
+ it "counts outgoing edges" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[0, 1] = "ab"
+ g.outdegree(0).should eq(1)
+ g.outdegree(1).should eq(0)
+ end
+ end
+
+ describe "#indegree" do
+ it "counts incoming edges" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[0, 1] = "ab"
+ g.indegree(0).should eq(0)
+ g.indegree(1).should eq(1)
+ end
+ end
+
+ describe "#subtree" do
+ g = Digraph(String, String).new
+ g[0] = "a"
+ g[1] = "b"
+ g[2] = "c"
+ g[0, 1] = "ab"
+ g[1, 2] = "bc"
+ g[3] = "x"
+
+ it "returns all reachable nodes" do
+ reachable = g.subtree(0).to_a
+ expected = [1, 2]
+ (expected - reachable).should be_empty
+ end
+
+ it "does not return disconnected nodes" do
+ reachable = g.subtree(0)
+ reachable.should_not contain(3_u64)
+ end
+
+ it "traverses lazilly" do
+ reachable = g.subtree 0
+ g[2, 3] = "cx"
+ reachable.should contain(3_u64)
+ end
+ end
+end
diff --git a/drivers/place/router/settings.cr b/drivers/place/router/settings.cr
new file mode 100644
index 00000000000..c7f1bfe3150
--- /dev/null
+++ b/drivers/place/router/settings.cr
@@ -0,0 +1,176 @@
+require "json"
+require "./signal_graph"
+
+module Place::Router::Core::Settings
+ # Types for representing the settings format for defining connections.
+ module Connections
+ module Deserializable
+ macro extended
+ def self.new(pull : JSON::PullParser)
+ parse?(pull.read_string) || pull.raise("Invalid #{self} (#{pull.string_value.inspect})")
+ end
+ end
+
+ abstract def parse?(raw : String)
+
+ def from_json_object_key?(key : String)
+ parse? key
+ end
+
+ def get_parts(module_id : String) : {String, Int32?}
+ mod_name, match, index = module_id.rpartition('_')
+ if match.empty?
+ {module_id, 1}
+ else
+ # we want the `.to_i` to be able to fail, this indicates it's probably a DeviceOutput
+ {mod_name, index.to_i?}
+ end
+ end
+ end
+
+ # Module name of a device within the local system e.g. `"Switcher_1"`.
+ record Device, mod : String, idx : Int32 do
+ extend Deserializable
+
+ def self.parse?(raw : String)
+ return if name = raw.lchop?('*')
+ mod, idx = get_parts(raw)
+ new mod, idx if idx
+ end
+ end
+
+ # Reference to a specific output on a device that has multiple outputs.
+ # This is a concatenation of the `Device` reference a `.` and the output.
+ # For example, output 3 of Switcher_1 is `"Switcher_1.3"`.
+ record DeviceOutput, mod : String, idx : Int32, output : String | Int32, layer : String? do
+ extend Deserializable
+
+ def self.parse?(raw : String)
+ return if name = raw.lchop?('*')
+ mod_name, match, outp = raw.rpartition(/_\d+\./)
+ if !match.empty?
+ mod, idx = mod_name, match[1..-2].to_i
+ outp_idx, match, layer = outp.rpartition('!')
+ if match.empty?
+ output = outp.to_i? || outp
+ new mod, idx, output, nil
+ else
+ output = outp_idx.to_i? || outp_idx
+ new mod, idx, output, layer
+ end
+ end
+ end
+ end
+
+ # Alias used to refer to a signal node that does not have an accompanying
+ # module. This can be useful for declaring the concept of a device that is
+ # attached to an input (e.g. `"*Laptop"`). All alias' must be prefixed with
+ # an asterisk ('*') within connections settings.
+ record Alias, name : String do
+ extend Deserializable
+
+ def self.parse?(raw : String)
+ if name = raw.lchop?('*')
+ new name
+ end
+ end
+ end
+
+ # The device a signal is originating from.
+ alias Source = Device | DeviceOutput | Alias
+
+ # The device that recieves the signal.
+ alias Sink = Device | Alias
+
+ # Identifier for the input on Sink.
+ alias Input = String
+
+ # Structure for a full connection map.
+ #
+ # ```json
+ # {
+ # "Display_1": {
+ # "hdmi": "Switcher_1.1"
+ # },
+ # "Switcher_1": ["*Foo", "*Bar"],
+ # "*FloorBox": "Switcher_1.2"
+ # }
+ # ```
+ alias Map = Hash(Sink, Hash(Input, Source) | Array(Source) | DeviceOutput)
+
+ # Parses a `Map` containing the system conectivity into a set of nodes and
+ # links that can be used for assembling the `SignalGraph`.
+ def self.parse(map : Map, sys : String)
+ nodes = [] of SignalGraph::Node::Ref
+ links = [] of {SignalGraph::Node::Ref, SignalGraph::Node::Ref}
+ aliases = {} of String => SignalGraph::Node::Ref
+
+ make_alias = ->(name : String, node : SignalGraph::Node::Ref) do
+ if prev = aliases[name]?
+ raise %(invalid configuration: "#{name}" refers to both #{prev} and #{node})
+ end
+ aliases[name] = node
+ end
+
+ map.each do |sink, inputs|
+ if sink.is_a? Alias
+ source = inputs
+ unless source.is_a? DeviceOutput
+ raise %(invalid configuration: "#{sink}" must link to a DeviceOutput)
+ end
+ onode = SignalGraph::Output.new sys, source.mod, source.idx, source.output, source.layer
+ nodes << onode
+ make_alias.call sink.name, onode
+ else
+ # Direct link only supported by output aliases.
+ if inputs.is_a? DeviceOutput
+ raise %(invalid configuration: "#{sink}" must specify inputs as either a hash or array)
+ end
+
+ nodes << SignalGraph::Device.new sys, sink.mod, sink.idx
+
+ # Iterate source arrays as 1-based input id's
+ inputs = inputs.each.with_index(1).map &.reverse if inputs.is_a? Array
+
+ inputs.each do |input, input_source|
+ inode = SignalGraph::Input.new sys, sink.mod, sink.idx, input
+ nodes << inode
+
+ if input_source.is_a? Alias
+ make_alias.call input_source.name, inode
+ next
+ end
+
+ onode = case input_source
+ in Device
+ SignalGraph::Device.new sys, input_source.mod, input_source.idx
+ in DeviceOutput
+ SignalGraph::Output.new sys, input_source.mod, input_source.idx, input_source.output, input_source.layer
+ end
+ nodes << onode
+
+ links << {onode, inode}
+ end
+ end
+ end
+
+ {nodes, links, aliases}
+ end
+ end
+
+ # Input/outputs and their associated metadata. Attributes specified here are
+ # progated to the assocated input status keys. This allows information such as
+ # name, type etc to be exposed to UI's.
+ alias IOMeta = Hash(String, Hash(String, JSON::Any))
+end
+
+# FIXME: submit as PR to crystal standard lib to support this neatly
+struct Union
+ def self.from_json_object_key?(key : String)
+ {% for t in T %}
+ instance = {{t}}.from_json_object_key? key
+ return instance unless instance.nil?
+ {% end %}
+ raise JSON::ParseException.new("Couldn't parse #{self} from #{key}", __LINE__, 0)
+ end
+end
diff --git a/drivers/place/router/settings_spec.cr b/drivers/place/router/settings_spec.cr
new file mode 100644
index 00000000000..78a8c65ddae
--- /dev/null
+++ b/drivers/place/router/settings_spec.cr
@@ -0,0 +1,77 @@
+require "spec"
+require "./settings"
+
+alias Settings = Place::Router::Core::Settings
+alias SignalGraph = Place::Router::SignalGraph
+
+class PlaceOS::Driver::Proxy::System
+ def self.module_id?(sys, name, idx) : String?
+ mock_id = {sys, name, idx}.hash
+ "mod-#{mock_id}"
+ end
+end
+
+describe Settings::Connections do
+ connections = <<-JSON
+ {
+ "Display_1": {
+ "hdmi": "Switcher_1.1"
+ },
+ "Switcher_1": ["*Foo", "*Bar"],
+ "*FloorBox": "Switcher_1.2"
+ }
+ JSON
+
+ describe "Map" do
+ it "deserializes from JSON" do
+ Settings::Connections::Map.from_json connections
+ end
+ end
+
+ describe ".parse" do
+ it "extracts nodes, links, aliases" do
+ map = Settings::Connections::Map.from_json connections
+ nodes, links, aliases = Settings::Connections.parse map, sys: "abc123"
+ nodes.size.should eq(7)
+ links.should contain({
+ SignalGraph::Output.new("abc123", "Switcher", 1, 1, "all"),
+ SignalGraph::Input.new("abc123", "Display", 1, "hdmi"),
+ })
+ aliases.keys.should contain "Foo"
+ aliases.keys.should contain "FloorBox"
+ end
+
+ it "extracts nodes, links, aliases and layers" do
+ connections2 = <<-JSON
+ {
+ "Display_1": {
+ "hdmi": "15.07_Switcher_1.1!video"
+ },
+ "Switcher_1": ["*Foo", "*Bar"],
+ "*FloorBox": "Switcher_1.2"
+ }
+ JSON
+
+ map = Settings::Connections::Map.from_json connections2
+ nodes, links, aliases = Settings::Connections.parse map, sys: "abc123"
+ nodes.size.should eq(7)
+ links.should contain({
+ SignalGraph::Output.new("abc123", "15.07_Switcher", 1, 1, "video"),
+ SignalGraph::Input.new("abc123", "Display", 1, "hdmi"),
+ })
+ aliases.keys.should contain "Foo"
+ aliases.keys.should contain "FloorBox"
+ end
+
+ it "detects alias conflicts" do
+ map = Settings::Connections::Map.from_json <<-JSON
+ {
+ "Switcher_1": ["*Foo", "*Foo"]
+ }
+ JSON
+ expect_raises(Exception) do
+ Settings::Connections.parse map, sys: "abc123"
+ end
+ end
+ end
+end
diff --git a/drivers/place/router/signal_graph.cr b/drivers/place/router/signal_graph.cr
new file mode 100644
index 00000000000..9751b32e67f
--- /dev/null
+++ b/drivers/place/router/signal_graph.cr
@@ -0,0 +1,185 @@
+require "set"
+require "./digraph"
+require "./signal_graph/*"
+
+# Structures and types for mapping between sys,mod,idx,io referencing and the
+# underlying graph structure.
+#
+# The SignalGraph class _does not_ perform any direct interaction with devices,
+# but does provide the ability to discover routes and available connectivity
+# when may then be acted on.
+class Place::Router::SignalGraph
+ alias Input = Node::DeviceInput
+
+ alias Output = Node::DeviceOutput
+
+ alias Device = Node::Device
+
+ Mute = Node::Mute.instance
+
+ private getter g : Digraph(Node::Label, Edge::Label)
+
+ private def initialize(initial_capacity = nil)
+ @g = Digraph(Node::Label, Edge::Label).new initial_capacity
+ end
+
+ # Inserts *node*.
+ protected def insert(node : Node::Ref)
+ g[node.id] = Node::Label.new node
+ end
+
+ # :ditto:
+ protected def insert(node : Node::Mute)
+ mute = Node::Label.new node
+ mute.source = Mute
+ mute.locked = true
+ g[node.id] = mute
+ end
+
+ # Defines a physical connection between two devices.
+ #
+ # *output* and *input* must both already exist within the underlying graph as
+ # signal nodes.
+ protected def connect(output : Node::Ref, input : Node::Ref)
+ g[input.id, output.id] = Edge::Static.instance
+ end
+
+ # Given a *mod* and sets of known *inputs* and *outputs* in use on it, wire up
+ # any active edges between these based on the interfaces available.
+ protected def link(mod : Mod, inputs : Enumerable(Input), outputs : Enumerable(Output))
+ if mod.switchable? && !outputs.empty?
+ inputs.each do |input|
+ outputs.each do |output|
+ func = Edge::Func::Switch.new input.input, output.output, output.layer
+ g[output.id, input.id] = Edge::Active.new mod, func
+ end
+ end
+ elsif mod.selectable?
+ inputs.each do |input|
+ output = Node::Device.new mod
+ func = Edge::Func::Select.new input.input
+ g[output.id, input.id] = Edge::Active.new mod, func
+ end
+ end
+
+ if mod.muteable?
+ if outputs.empty?
+ output = Node::Device.new mod
+ func = Edge::Func::Mute.new true
+ g[output.id, Mute.id] = Edge::Active.new mod, func
+ else
+ # ameba:disable Lint/ShadowingOuterLocalVar
+ outputs.each do |output|
+ func = Edge::Func::Mute.new true, output.output
+ g[output.id, Mute.id] = Edge::Active.new mod, func
+ end
+ end
+ end
+ end
+
+ # Construct a graph from a pre-parsed configuration.
+ #
+ # *nodes* must contain the set of all signal nodes that form the device inputs
+ # and outputs across the system. This includes those at the "edge" of the
+ # signal network (e.g. a input to a switcher) as well as inputs in use on
+ # intermediate devices (e.g. a input on a display, which in turn is attached to
+ # the switcher above).
+ #
+ # *links* declares the interconnections between devices.
+ #
+ # Modules associated with any of these nodes are then introspected for
+ # switching, input selection and mute control based on the interfaces they
+ # expose.
+ def self.build(nodes : Enumerable(Node::Ref), links : Enumerable({Node::Ref, Node::Ref}))
+ mod_io = Hash(Mod, {Set(Input), Set(Output)}).new do |h, k|
+ h[k] = {Set(Input).new, Set(Output).new}
+ end
+
+ siggraph = new initial_capacity: nodes.size
+
+ siggraph.insert Mute
+
+ # Create verticies for each signal node
+ nodes.each do |node|
+ siggraph.insert node
+
+ # Track device IO in use for building active edges
+ case node
+ when Input
+ inputs, _ = mod_io[node.mod]
+ inputs << node
+ when Output
+ _, outputs = mod_io[node.mod]
+ outputs << node
+ end
+ end
+
+ # Insert the static edges.
+ links.each { |source, dest| siggraph.connect source, dest }
+
+ # Wire up the active edges.
+ mod_io.each { |mod, (inputs, outputs)| siggraph.link mod, inputs, outputs }
+
+ # Set a loopback source on all inputs.
+ siggraph.inputs.each { |node| node.source = node.ref }
+
+ siggraph
+ end
+
+ # Retrieves the labelled state for *node*.
+ def [](node : Node::Ref)
+ g[node.id]
+ end
+
+ # Retrieves the labelled state for the signal node at *node_id*.
+ def [](node_id)
+ g[node_id]
+ end
+
+ # Find the signal path that connects *source* to *dest*, or `nil` if this is
+ # not possible.
+ #
+ # Provides an `Iterator` that provides labels across each node, the edge, and
+ # subsequent node.
+ def route(source : Node::Ref, destination : Node::Ref, max_dist = nil)
+ path = g.path destination.id, source.id, invert: true
+
+ return nil unless path
+
+ return nil if max_dist && path.size > max_dist
+
+ path.each_cons(2, true).map do |(succ, pred)|
+ {
+ g[succ], # source
+ g[pred, succ], # edge
+ g[pred], # next node
+ }
+ end
+ end
+
+ # Checks if *node* is a system input.
+ def input?(node : Node::Ref) : Bool
+ g.sink? node.id
+ end
+
+ # Provide the signal nodes that form system inputs.
+ def inputs
+ # Graph connectivity is inverse to signal direction, hence sinks here.
+ g.sinks.compact_map { |id| g[id] unless id == Mute.id }
+ end
+
+ # Provide all signal nodes that can be routed to *destination*.
+ def inputs(destination : Node::Ref)
+ g.subtree(destination.id).map { |id| g[id] }
+ end
+
+ # Checks if *node* is a system output.
+ def output?(node : Node::Ref) : Bool
+ g.source? node.id
+ end
+
+ # Provide the signal nodes that form system outputs.
+ def outputs
+ g.sources.compact_map { |id| g[id] unless id == Mute.id }
+ end
+end
diff --git a/drivers/place/router/signal_graph/edge.cr b/drivers/place/router/signal_graph/edge.cr
new file mode 100644
index 00000000000..cceb5e67a30
--- /dev/null
+++ b/drivers/place/router/signal_graph/edge.cr
@@ -0,0 +1,39 @@
+require "./mod"
+
+class Place::Router::SignalGraph
+ module Edge
+ alias Label = Static | Active
+
+ class Static
+ class_getter instance : self { new }
+
+ protected def initialize; end
+ end
+
+ record Active, mod : Mod, func : Func::Type
+
+ module Func
+ record Mute,
+ state : Bool,
+ index : Int32 | String = 0
+
+ record Select,
+ input : Int32 | String
+
+ record Switch,
+ input : Int32 | String,
+ output : Int32 | String,
+ layer : String
+
+ # NOTE: currently not supported. Requires interaction via
+ # Proxy::RemoteDriver to support dynamic method execution.
+ # record Custom,
+ # func : String,
+ # args : Hash(String, JSON::Any::Type)
+
+ macro finished
+ alias Type = {{ @type.constants.join(" | ").id }}
+ end
+ end
+ end
+end
diff --git a/drivers/place/router/signal_graph/mod.cr b/drivers/place/router/signal_graph/mod.cr
new file mode 100644
index 00000000000..488f5434359
--- /dev/null
+++ b/drivers/place/router/signal_graph/mod.cr
@@ -0,0 +1,60 @@
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/switchable"
+
+class Place::Router::SignalGraph
+ # Reference to a PlaceOS module that provides IO nodes within the graph.
+ class Mod
+ getter sys : String
+ getter name : String
+ getter idx : Int32
+
+ getter id : String
+
+ def initialize(@sys, @name, @idx)
+ id = PlaceOS::Driver::Proxy::System.module_id? sys, name, idx
+ @id = id || raise %("#{name}/#{idx}" does not exist in #{sys})
+ end
+
+ def metadata
+ if meta = PlaceOS::Driver::Proxy::System.driver_metadata?(id)
+ meta
+ else
+ # TODO:: warn about offline device
+ PlaceOS::Driver::DriverModel::Metadata.new(interface: {} of String => Hash(String, JSON::Any))
+ end
+ rescue error
+ raise RuntimeError.new("failed to obtain metadata for #{id}", cause: error)
+ end
+
+ # FIXME: drop if / after renaming InputSelection -> Selectable
+ def selectable?
+ interface = {{PlaceOS::Driver::Interface::InputSelection.name(generic_args: false).stringify}}
+ interface.in? metadata.implements
+ end
+
+ macro finished
+ {% for interface in PlaceOS::Driver::Interface.constants %}
+ {% type = PlaceOS::Driver::Interface.constant(interface) %}
+ def {{interface.underscore}}?
+ {{type.name(generic_args: false).stringify}}.in? metadata.implements
+ end
+ {% end %}
+ end
+
+ def_equals_and_hash @id
+
+ def to_s(io)
+ io << sys << '/' << name << '_' << idx
+ end
+
+ def self.parse?(ref)
+ if m = ref.match /^(.+)\/(.+)\_(\d+)$/
+ sys = m[1]
+ mod = m[2]
+ idx = m[3].to_i
+ new sys, mod, idx
+ end
+ end
+ end
+end
diff --git a/drivers/place/router/signal_graph/node.cr b/drivers/place/router/signal_graph/node.cr
new file mode 100644
index 00000000000..a8da7feab5a
--- /dev/null
+++ b/drivers/place/router/signal_graph/node.cr
@@ -0,0 +1,260 @@
+require "json"
+require "./mod"
+require "./watchable"
+
+class Place::Router::SignalGraph
+ module Node
+ # Metadata tracked against each signal node.
+ class Label
+ include JSON::Serializable
+ include Watchable
+
+ def initialize(@ref)
+ end
+
+ def to_s(io)
+ io << ref
+ end
+
+ # The `Node::Ref` used when creating this node.
+ getter ref : Ref
+
+ # `Ref` of the upstream signal source currently feeding this node.
+ property source : Ref? = nil
+
+ # Locked state. When `true` changes to signal routes that transit this
+ # are blocked.
+ property locked : Bool = false
+
+ # Additional metadata passed in from settings or dynamically applied.
+ # Information here is propogated to exposed state keys. May be used for
+ # any information needed by a user interface or external system.
+ @[JSON::Field(ignore: true)]
+ property meta : Hash(String, JSON::Any) { Hash(String, JSON::Any).new }
+
+ delegate :[], :[]?, to: meta
+
+ # Sets a metadata property of `self`.
+ def []=(key, value : JSON::Any)
+ meta[key] = value
+ self.notify
+ value
+ end
+
+ def []=(key, value)
+ self[key] = JSON::Any.new value
+ end
+
+ def []=(key, value : Int)
+ self[key] = JSON::Any.new value.to_i64
+ end
+
+ def []=(key, value : Float)
+ self[key] = JSON::Any.new value.to_f64
+ end
+
+ def []=(key, value : Array)
+ self[key] = JSON::Any.new value.map { |x| JSON::Any.new x }
+ end
+
+ def []=(key, value : Hash)
+ self[key] = JSON::Any.new value.transform_values { |x| JSON::Any.new x }
+ end
+
+ protected def on_to_json(json)
+ @meta.try &.each do |key, value|
+ json.field(key) { value.to_json(json) }
+ end
+ end
+ end
+
+ # Base structure for referring to a node within the graph.
+ abstract struct Ref
+ # Resolves a string-based node *key* to a fully-qualified reference.
+ #
+ # If a system component is not present within *key*, this is resolved
+ # within the context of *sys*. For example:
+ #
+ # Ref.resolve("Display_1:hdmi", "sys-abc123")
+ # # => DeviceInput(sys: "sys-abc123", mod: {"Display", 1}, input: "hdmi")
+ #
+ def self.resolve?(key : String, sys = nil)
+ ref = key.includes?('/') ? key : "#{sys}/#{key}"
+ {% begin %}
+ {% for type in @type.subclasses %}
+ {{type}}.parse?(ref) || \
+ {% end %}
+ nil
+ {% end %}
+ end
+
+ # Node identifier for usage as the graph ID.
+ def id
+ self.class.hash ^ self.hash
+ end
+
+ abstract def mod
+
+ DEFAULT_LAYER = "all"
+
+ def layer
+ DEFAULT_LAYER
+ end
+
+ def ==(other : Ref)
+ id == other.id
+ end
+
+ def local(sys : String)
+ to_s.lchop "#{sys}/"
+ end
+
+ def to_json(json)
+ json.string to_s
+ end
+
+ private module ClassMethods(T)
+ # Parses a string-based *ref* to {{@type}}.
+ abstract def parse?(ref : String) : T?
+ end
+
+ macro inherited
+ extend ClassMethods(self)
+ end
+ end
+
+ # Reference to the default / central node for a device.
+ #
+ # These take the cannonical string form of:
+ #
+ # sys-abc123/Display_1
+ # │ │ │
+ # │ │ └module index
+ # │ └module name
+ # └system
+ #
+ struct Device < Ref
+ getter mod : Mod
+
+ def initialize(sys, name, idx)
+ @mod = Mod.new sys, name, idx
+ end
+
+ def initialize(@mod)
+ end
+
+ def to_s(io)
+ io << mod
+ end
+
+ def self.parse?(ref) : self?
+ if mod = Mod.parse? ref
+ new mod
+ end
+ end
+ end
+
+ # Reference to a signal output from a device.
+ #
+ # These take the cannonical string form of:
+ #
+ # sys-abc123/Switcher_1.1!video
+ # │ │ │ │ │_layer
+ # │ │ │ └output
+ # │ │ └module index
+ # │ └module namme
+ # └system
+ #
+ struct DeviceOutput < Ref
+ getter mod : Mod
+ getter output : Int32 | String
+ getter layer : String
+
+ def initialize(sys, name, idx, @output, layer)
+ @mod = Mod.new sys, name, idx
+ @layer = layer.try(&.downcase) || DEFAULT_LAYER
+ end
+
+ def initialize(@mod, @output)
+ @layer = DEFAULT_LAYER
+ end
+
+ def to_s(io)
+ io << mod << '.' << output
+ io << '!' << @layer unless @layer == DEFAULT_LAYER
+ end
+
+ def self.parse?(ref) : self?
+ # as match == "_123."
+ mod_name, match, outp = ref.rpartition(/_\d+\./)
+ mod_name = "#{mod_name}_#{match[1..-2]}" if !match.empty?
+
+ if mod = Mod.parse? mod_name
+ output = outp.to_i? || outp
+ new mod, output
+ end
+ end
+ end
+
+ # Reference to a signal input to a device.
+ #
+ # These take the cannonical string form of:
+ #
+ # sys-abc123/Display_1:hdmi
+ # │ │ │ │
+ # │ │ │ └input
+ # │ │ └module index
+ # │ └module namme
+ # └system
+ #
+ struct DeviceInput < Ref
+ getter mod : Mod
+ getter input : Int32 | String
+
+ def initialize(sys, name, idx, @input)
+ @mod = Mod.new sys, name, idx
+ end
+
+ def initialize(@mod, @input)
+ end
+
+ def to_s(io)
+ io << mod << ':' << input
+ end
+
+ def self.parse?(ref) : self?
+ m, _, i = ref.rpartition ':'
+ if mod = Mod.parse? m
+ input = i.to_i? || i
+ new mod, input
+ end
+ end
+ end
+
+ # Virtual node representing (any) mute source.
+ #
+ # This may be refernced simply as `MUTE`.
+ struct Mute < Ref
+ class_getter instance : self { new }
+
+ protected def initialize
+ end
+
+ def id
+ 0_u64
+ end
+
+ def mod
+ end
+
+ def self.parse?(ref) : self?
+ # See Ref#resolve? on line 82 of this file for what is passed here
+ instance if ref.upcase.ends_with?("MUTE")
+ end
+
+ def to_s(io)
+ io << "MUTE"
+ end
+ end
+ end
+end
diff --git a/drivers/place/router/signal_graph/watchable.cr b/drivers/place/router/signal_graph/watchable.cr
new file mode 100644
index 00000000000..d862b5c05d7
--- /dev/null
+++ b/drivers/place/router/signal_graph/watchable.cr
@@ -0,0 +1,29 @@
+class Place::Router::SignalGraph
+ module Watchable
+ # Subscribe to updates.
+ def watch(initial = true, &handler : self ->) : Nil
+ subscribers << handler
+ handler.call(self) if initial
+ end
+
+ # Notify subscribers with current state.
+ def notify : Nil
+ @subscribers.try &.each &.call(self)
+ end
+
+ macro included
+ @[JSON::Field(ignore: true)]
+ private getter subscribers : Array(self ->) { Array(self ->).new }
+
+ {% verbatim do %}
+ macro finished
+ {% for method in @type.methods.select &.name.ends_with? '=' %}
+ def {{method.name}}({{method.args.splat}})
+ previous_def.tap { notify }
+ end
+ {% end %}
+ end
+ {% end %}
+ end
+ end
+end
diff --git a/drivers/place/router/signal_graph_spec.cr b/drivers/place/router/signal_graph_spec.cr
new file mode 100644
index 00000000000..33d73a0e4dd
--- /dev/null
+++ b/drivers/place/router/signal_graph_spec.cr
@@ -0,0 +1,251 @@
+abstract class PlaceOS::Driver; end
+
+require "spec"
+require "placeos-driver/driver_model"
+require "./signal_graph"
+
+alias SigGraph = Place::Router::SignalGraph
+
+abstract class PlaceOS::Driver
+ module Interface
+ module Switchable; end
+
+ module Selectable; end
+
+ module Muteable; end
+
+ # TODO: expand interfaces in `placeos-driver` to cover this
+ module InputMuteable; end
+ end
+
+ class Proxy::System
+ def self.module_id?(sys, name, idx) : String?
+ mock_id = {sys, name, idx}.hash
+ "mod-#{mock_id}"
+ end
+
+ def self.driver_metadata?(id) : DriverModel::Metadata?
+ m = DriverModel::Metadata.new
+ m.implements << {{Interface::Switchable.name(generic_args: false).stringify}}
+ m.implements << {{Interface::Selectable.name(generic_args: false).stringify}}
+ m.implements << {{Interface::Muteable.name(generic_args: false).stringify}}
+ m
+ end
+ end
+end
+
+# Settings:
+#
+# connections = {
+# Display_1: {
+# hdmi: "15.02_Switcher_1.1"
+# },
+# 15.02_Switcher_1: ["*foo", "*bar"],
+# Display_2: {
+# hdmi: "*baz"
+# }
+# }
+#
+# inputs = {
+# foo: "laptop",
+# bar: "pc"
+# }
+
+# Set of inputs in use
+# NOTE: alias are only used in the local system, no impact here
+nodes = [
+ SigGraph::Input.new("sys-123", "Display", 1, "hdmi"),
+ SigGraph::Input.new("sys-123", "Display", 2, "hdmi"),
+ SigGraph::Input.new("sys-123", "15.02_Switcher", 1, 1),
+ SigGraph::Input.new("sys-123", "15.02_Switcher", 1, 2),
+ SigGraph::Output.new("sys-123", "15.02_Switcher", 1, 1, "all"),
+ SigGraph::Device.new("sys-123", "Display", 1),
+ SigGraph::Device.new("sys-123", "Display", 2),
+ SigGraph::Device.new("sys-123", "15.02_Switcher", 1),
+]
+
+connections = [
+ {SigGraph::Output.new("sys-123", "15.02_Switcher", 1, 1, "all"), SigGraph::Input.new("sys-123", "Display", 1, "hdmi")},
+]
+
+inputs = {
+ foo: SigGraph::Input.new("sys-123", "15.02_Switcher", 1, 1),
+ bar: SigGraph::Input.new("sys-123", "15.02_Switcher", 1, 2),
+ baz: SigGraph::Input.new("sys-123", "Display", 2, "hdmi"),
+}
+
+outputs = {
+ display: SigGraph::Device.new("sys-123", "Display", 1),
+ display2: SigGraph::Device.new("sys-123", "Display", 2),
+}
+
+describe SigGraph do
+ describe ".build" do
+ it "builds from config" do
+ SigGraph.build nodes, connections
+ end
+ end
+
+ describe "#[]" do
+ n = SigGraph::Device.new("sys-123", "Display", 1)
+ g = SigGraph.build [n], [] of {SigGraph::Node::Ref, SigGraph::Node::Ref}
+
+ it "provides node details from a Ref" do
+ g[n].should be_a(SigGraph::Node::Label)
+ end
+
+ it "provides nodes details from an ID" do
+ g[n.id].should be_a(SigGraph::Node::Label)
+ end
+
+ it "provides the same label for both accessors" do
+ g[n].should eq(g[n.id])
+ end
+ end
+
+ describe "#route" do
+ g = SigGraph.build nodes, connections
+
+ it "returns nil if no path exists" do
+ path = g.route inputs[:foo], outputs[:display2]
+ path.should be_nil
+ end
+
+ it "provides the path connects a signal source to a destination" do
+ source = inputs[:foo]
+ dest = outputs[:display]
+
+ path = g.route source, dest
+ path = path.not_nil!
+
+ path.each_with_index do |(node, edge, next_node), step|
+ case step
+ when 0
+ node.should eq g[source]
+ edge = edge.as SigGraph::Edge::Active
+ edge.mod.name.should eq "15.02_Switcher"
+ edge.func.should eq SigGraph::Edge::Func::Switch.new 1, 1, "all"
+ when 1
+ edge.should be_a SigGraph::Edge::Static
+ next_node.should eq g[SigGraph::Input.new("sys-123", "Display", 1, "hdmi")]
+ when 2
+ edge = edge.as SigGraph::Edge::Active
+ edge.mod.name.should eq "Display"
+ edge.mod.idx.should eq 1
+ edge.func.should eq SigGraph::Edge::Func::Select.new "hdmi"
+ when 4
+ fail "path iterator did not terminate"
+ end
+ end
+ end
+
+ it "provides mute activation on an output device" do
+ source = SigGraph::Mute
+ dest = outputs[:display]
+
+ path = g.route source, dest
+ path = path.not_nil!
+
+ node, edge, next_node = path.first
+ node.should eq g[source]
+ edge = edge.as SigGraph::Edge::Active
+ edge.mod.name.should eq "Display"
+ edge.func.should eq SigGraph::Edge::Func::Mute.new true
+ next_node.should eq g[dest]
+ end
+
+ it "provide mute activate on an intermediate switcher" do
+ source = SigGraph::Mute
+ dest = SigGraph::Output.new("sys-123", "15.02_Switcher", 1, 1, "all")
+
+ path = g.route source, dest
+ path = path.not_nil!
+
+ node, edge, next_node = path.first
+ node.should eq g[source]
+ edge = edge.as SigGraph::Edge::Active
+ edge.mod.name.should eq "15.02_Switcher"
+ edge.func.should eq SigGraph::Edge::Func::Mute.new true, 1
+ next_node.should eq g[dest]
+ end
+ end
+
+ describe "#input?" do
+ g = SigGraph.build nodes, connections
+
+ it "returns true if the node is an input" do
+ g.input?(inputs.values.sample).should be_true
+ end
+
+ it "returns false otherwise" do
+ g.input?(outputs.values.sample).should be_false
+ end
+ end
+
+ describe "#inputs" do
+ it "provides a list of input nodes within the graph" do
+ g = SigGraph.build nodes, connections
+ expected = inputs.values
+ discovered = g.inputs.map(&.ref).to_a
+ expected.each { |input| discovered.should contain input }
+ end
+ end
+
+ describe "#inputs(destination)" do
+ it "provides a list of inputs nodes accessible to an output" do
+ g = SigGraph.build nodes, connections
+ reachable = g.inputs(outputs[:display]).map(&.ref).to_a
+ expected = {inputs[:foo], inputs[:bar]}
+ expected.each { |input| reachable.should contain input }
+ end
+ end
+
+ describe "#output?" do
+ g = SigGraph.build nodes, connections
+
+ it "returns true if the node is an output" do
+ g.output?(outputs.values.sample).should be_true
+ end
+
+ it "returns false otherwise" do
+ g.output?(inputs.values.sample).should be_false
+ end
+ end
+
+ describe "#outputs" do
+ it "list the output nodes present in the graph" do
+ g = SigGraph.build nodes, connections
+ expected = outputs.values
+ discovered = g.outputs.map(&.ref).to_a
+ expected.each { |output| discovered.should contain output }
+ end
+ end
+
+ pending "#to_json" do
+ end
+ pending ".from_json" do
+ end
+
+ pending "#merge" do
+ end
+
+ describe SigGraph::Node::Label do
+ it "supports change notification" do
+ n = SigGraph::Device.new("sys-123", "Display", 1)
+ g = SigGraph.build [n], [] of {SigGraph::Node::Ref, SigGraph::Node::Ref}
+
+ x = 0
+
+ g[n].watch(initial: false) { x += 1 }
+
+ x.should eq 0
+ g[n].notify
+ x.should eq 1
+
+ g[n].locked.should be_false
+ g[n].locked = true
+ x.should eq 2
+ g[n].locked.should be_true
+ end
+ end
+end
diff --git a/drivers/place/router_spec.cr b/drivers/place/router_spec.cr
new file mode 100644
index 00000000000..08a49570987
--- /dev/null
+++ b/drivers/place/router_spec.cr
@@ -0,0 +1,102 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/switchable"
+
+# :nodoc:
+class RouterDisplay < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Powerable
+ include PlaceOS::Driver::Interface::Muteable
+
+ enum Inputs
+ HDMI
+ HDMI2
+ end
+
+ include PlaceOS::Driver::Interface::InputSelection(Inputs)
+
+ # implement the abstract methods required by the interfaces
+ def power(state : Bool)
+ self[:power] = state
+ end
+
+ def switch_to(input : Inputs)
+ mute(false)
+ self[:input] = input
+ end
+
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ self[:mute] = state
+ end
+end
+
+# :nodoc:
+class RouterSwitcher < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Switchable(Int32, Int32)
+
+ def switch_to(input : Int32)
+ self[:input] = input
+ end
+
+ def switch(map : Hash(Input, Array(Output)), layer : SwitchLayer? = nil)
+ self["last_switched_layer"] = layer.to_s.downcase
+ map.each do |(input, outputs)|
+ outputs.each do |output|
+ self["output#{output}"] = input
+ end
+ end
+ end
+end
+
+DriverSpecs.mock_driver "Place::RouterTest" do
+ system({
+ Display: {RouterDisplay},
+ Switcher: {RouterSwitcher},
+ })
+
+ settings({
+ connections: {
+ Display_1: {
+ hdmi: "Switcher_1.1!video",
+ },
+ Switcher_1: ["*Foo", "*Bar"],
+ "*FloorBox": "Switcher_1.2",
+ },
+ })
+
+ # Give the settings time to load
+ sleep 2
+
+ status["inputs"].as_a.should contain("Foo")
+ status["inputs"].as_a.should contain("Bar")
+ status["outputs"].as_a.should contain("Display_1")
+ status["outputs"].as_a.should contain("FloorBox")
+ status["output/Display_1"]["inputs"].should eq(["Foo", "Bar"])
+
+ exec(:route_signal, "Foo", "Display_1").get
+ status["output/Display_1"]["source"].should eq(status["input/Foo"]["ref"])
+ system(:Switcher_1)["last_switched_layer"].should eq("video")
+
+ expect_raises(
+ PlaceOS::Driver::RemoteException,
+ %(unknown signal node "Baz" - did you mean "Bar"?)
+ ) do
+ exec(:route_signal, "Foo", "Baz").get
+ end
+
+ # Ensure previous status persists settings reloads for continuing nodes
+ settings({
+ connections: {
+ Display_1: {
+ hdmi: "Switcher_1.1",
+ },
+ Switcher_1: ["*Foo", "*Bar"],
+ },
+ })
+ sleep 2
+ status["output/Display_1"]["source"].should eq(status["input/Foo"]["ref"])
+end
diff --git a/drivers/place/smtp.cr b/drivers/place/smtp.cr
new file mode 100644
index 00000000000..6375355f4d4
--- /dev/null
+++ b/drivers/place/smtp.cr
@@ -0,0 +1,161 @@
+require "qr-code"
+require "qr-code/export/png"
+require "base64"
+require "email"
+require "uri"
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+
+class Place::Smtp < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::Mailer
+
+ descriptive_name "SMTP Mailer"
+ generic_name :Mailer
+ uri_base "https://smtp.host.com"
+ description %(sends emails via SMTP)
+
+ default_settings({
+ sender: "support@place.tech",
+ # host: "smtp.host",
+ # port: 587,
+ tls_mode: EMail::Client::TLSMode::STARTTLS.to_s,
+ ssl_verify_ignore: false,
+ username: "", # Username/Password for SMTP servers with basic authorization
+ password: "",
+
+ email_templates: {visitor: {checkin: {
+ subject: "%{name} has arrived",
+ text: "for your meeting at %{time}",
+ }}},
+ })
+
+ private def smtp_client : EMail::Client
+ @smtp_client ||= new_smtp_client
+ end
+
+ @smtp_client : EMail::Client?
+ @sender : String = "support@place.tech"
+ @username : String = ""
+ @password : String = ""
+ @host : String = "smtp.host"
+ @port : Int32 = 587
+ @tls_mode : EMail::Client::TLSMode = EMail::Client::TLSMode::STARTTLS
+ @send_lock : Mutex = Mutex.new
+ @ssl_verify_ignore : Bool = false
+
+ def on_update
+ defaults = URI.parse(config.uri.not_nil!)
+ tls_mode = if scheme = defaults.scheme
+ scheme.ends_with?('s') ? EMail::Client::TLSMode::SMTPS : EMail::Client::TLSMode::STARTTLS
+ else
+ EMail::Client::TLSMode::STARTTLS
+ end
+ port = defaults.port || 587
+ host = defaults.host || "smtp.host"
+
+ @username = setting?(String, :username) || ""
+ @password = setting?(String, :password) || ""
+ @sender = setting?(String, :sender) || "support@place.tech"
+ @host = setting?(String, :host) || host
+ @port = setting?(Int32, :port) || port
+ @tls_mode = setting?(EMail::Client::TLSMode, :tls_mode) || tls_mode
+ @ssl_verify_ignore = setting?(Bool, :ssl_verify_ignore) || false
+
+ @smtp_client = new_smtp_client
+
+ @templates = setting?(Templates, :email_templates) || Templates.new
+ end
+
+ # Create and configure an SMTP client
+ private def new_smtp_client
+ email_config = EMail::Client::Config.new(@host, @port)
+ email_config.log = logger
+ email_config.client_name = "PlaceOS"
+
+ unless @username.empty? || @password.empty?
+ email_config.use_auth(@username, @password)
+ end
+
+ email_config.use_tls(@tls_mode)
+ email_config.tls_context.verify_mode = OpenSSL::SSL::VerifyMode::None if @ssl_verify_ignore
+
+ EMail::Client.new(email_config)
+ end
+
+ def generate_svg_qrcode(text : String) : String
+ QRCode.new(text).as_svg
+ end
+
+ def generate_png_qrcode(text : String, size : Int32 = 128) : String
+ Base64.strict_encode QRCode.new(text).as_png(size: size)
+ end
+
+ def send_mail(
+ to : String | Array(String),
+ subject : String,
+ message_plaintext : String? = nil,
+ message_html : String? = nil,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ ) : Bool
+ to = {to} unless to.is_a?(Array)
+
+ from = {from} unless from.nil? || from.is_a?(Array)
+ cc = {cc} unless cc.nil? || cc.is_a?(Array)
+ bcc = {bcc} unless bcc.nil? || bcc.is_a?(Array)
+ reply_to = {reply_to} unless reply_to.nil? || reply_to.is_a?(Array)
+
+ message = EMail::Message.new
+
+ message.subject(subject)
+
+ message.sender(@sender)
+
+ if from.nil? || from.empty?
+ message.from(@sender)
+ else
+ from.each { |_from| message.from(_from) }
+ end
+
+ to.each { |_to| message.to(_to) }
+ bcc.each { |_bcc| message.bcc(_bcc) }
+ cc.each { |_cc| message.cc(_cc) }
+
+ if reply_to
+ reply_to.each { |_reply| message.reply_to(_reply) }
+ end
+
+ message.message(message_plaintext.as(String)) unless message_plaintext.presence.nil?
+ message.message_html(message_html.as(String)) unless message_html.presence.nil?
+
+ # Traverse all attachments
+ {resource_attachments, attachments}.map(&.each).each.flatten.each do |attachment|
+ # Base64 decode to memory, then attach to email
+ attachment_io = IO::Memory.new
+ Base64.decode(attachment[:content], attachment_io)
+ attachment_io.rewind
+
+ case attachment
+ in Attachment
+ message.attach(io: attachment_io, file_name: attachment[:file_name])
+ in ResourceAttachment
+ message.message_resource(io: attachment_io, file_name: attachment[:file_name], cid: attachment[:content_id])
+ end
+ end
+
+ sent = false
+
+ # Ensure only a single send at a time
+ @send_lock.synchronize do
+ smtp_client.start do
+ sent = send(message)
+ end
+ end
+
+ sent
+ end
+end
diff --git a/drivers/place/smtp_spec.cr b/drivers/place/smtp_spec.cr
new file mode 100644
index 00000000000..989f6ad5218
--- /dev/null
+++ b/drivers/place/smtp_spec.cr
@@ -0,0 +1,41 @@
+require "placeos-driver/spec"
+require "email"
+
+# for local testing use: http://nilhcem.com/FakeSMTP/download.html
+
+DriverSpecs.mock_driver "Place::Smtp" do
+ settings({
+ sender: "support@place.tech",
+ host: ENV["PLACE_SMTP_HOST"]? || "localhost",
+ port: ENV["PLACE_SMTP_PORT"]?.try(&.to_i) || 25,
+ username: ENV["PLACE_SMTP_USER"]? || "", # Username/Password for SMTP servers with basic authorization
+ password: ENV["PLACE_SMTP_PASS"]? || "",
+ tls_mode: ENV["PLACE_SMTP_MODE"]? || "none",
+
+ email_templates: {visitor: {checkin: {
+ subject: "%{name} has arrived",
+ text: "for your meeting at %{time}",
+ }}},
+ })
+
+ response = exec(
+ :send_mail,
+ subject: "Test Email",
+ to: ENV["PLACE_TEST_EMAIL"]? || "support@place.tech",
+ message_plaintext: "Hello!",
+ ).get
+
+ response.should be_true
+
+ response = exec(
+ :send_template,
+ to: "steve@place.tech",
+ template: {"visitor", "checkin"},
+ args: {
+ name: "Bob",
+ time: "1:30pm",
+ }
+ ).get
+
+ response.should be_true
+end
diff --git a/drivers/place/spec_helper.cr b/drivers/place/spec_helper.cr
new file mode 100644
index 00000000000..ac332cfa843
--- /dev/null
+++ b/drivers/place/spec_helper.cr
@@ -0,0 +1,8 @@
+require "placeos-driver"
+
+class Place::SpecHelper < PlaceOS::Driver
+ # This method will be exposed on the module
+ def implemented_in_driver
+ "woot!"
+ end
+end
diff --git a/drivers/place/staff_api.cr b/drivers/place/staff_api.cr
new file mode 100644
index 00000000000..6b3cdd43317
--- /dev/null
+++ b/drivers/place/staff_api.cr
@@ -0,0 +1,1051 @@
+require "json-schema"
+require "placeos-driver"
+require "oauth2"
+require "placeos"
+require "link-header"
+require "simple_retry"
+require "place_calendar"
+require "./booking_model"
+
+# This comment is to force a recompile of the driver with updated models
+
+class Place::StaffAPI < PlaceOS::Driver
+ descriptive_name "PlaceOS Staff API"
+ generic_name :StaffAPI
+ description %(helpers for requesting data held in the staff API.)
+
+ # The PlaceOS API
+ uri_base "https://staff"
+
+ default_settings({
+ # PlaceOS X-API-key, for simpler authentication
+ api_key: "",
+ disable_event_notify: false,
+ query_limit: 100,
+ period_end_default_in_min: 60,
+ })
+
+ @place_domain : URI = URI.parse("https://staff")
+ @host_header : String = ""
+ @api_key : String = ""
+
+ @authority_id : String = ""
+ @event_monitoring : PlaceOS::Driver::Subscriptions::ChannelSubscription? = nil
+ @notify_count : UInt64 = 0_u64
+ @notify_fails : UInt64 = 0_u64
+
+ @query_limit : Int32 = 100
+ @period_end_default_in_min : Int32? = nil
+
+ def on_update
+ # x-api-key is the preferred method for API access
+ @api_key = setting(String, :api_key) || ""
+ @access_expires = 30.years.from_now if @api_key.presence
+
+ @place_domain = URI.parse(config.uri.not_nil!)
+ @host_header = setting?(String, :host_header) || @place_domain.host.not_nil!
+
+ @placeos_client = nil
+ @query_limit = setting?(Int32, :query_limit) || 100
+ @period_end_default_in_min = setting?(Int32, :period_end_default_in_min)
+
+ # skip if not going to work
+ return unless @api_key.presence
+ return if setting?(Bool, :disable_event_notify)
+ schedule.clear
+ schedule.every(1.hour + rand(300).seconds) { lookup_authority_id }
+ schedule.in(1.second) { lookup_authority_id }
+ end
+
+ def lookup_authority_id(retry : Int32 = 0)
+ response = get("/auth/authority")
+ raise "unexpected response for /auth/authority: #{response.status_code}\n#{response.body}" unless response.success?
+
+ old_id = @authority_id
+ @authority_id = NamedTuple(id: String).from_json(response.body)[:id]
+ monitor_event_changes unless old_id == @authority_id
+ @authority_id
+ rescue error
+ logger.warn(exception: error) { "failed to lookup authority id" }
+ sleep rand(3).seconds
+ retry += 1
+ return if retry == 10
+ spawn { lookup_authority_id(retry) }
+ end
+
+ protected def monitor_event_changes
+ if monitor = @event_monitoring
+ subscriptions.unsubscribe(monitor)
+ @event_monitoring = nil
+ end
+
+ @event_monitoring = monitor("#{@authority_id}/bookings/event") { |_subscription, payload| push_event_occured(payload) }
+ end
+
+ struct PushEvent
+ include JSON::Serializable
+
+ getter event_id : String
+ getter change : String
+ getter system_id : String
+ getter event : JSON::Any?
+ end
+
+ protected def push_event_occured(payload)
+ @notify_count += 1
+ logger.debug { "new push event: #{payload}" }
+
+ event = PushEvent.from_json payload
+
+ response = post("/api/staff/v1/events/notify/#{event.change}/#{event.system_id}/#{event.event_id}",
+ body: event.event.to_json,
+ headers: authentication(HTTP::Headers{
+ "Content-Type" => "application/json",
+ })
+ )
+ if !response.success?
+ @notify_fails += 1
+ raise "unexpected response processing push event: #{response.status_code}\n#{payload}"
+ end
+ end
+
+ def push_event_status
+ {
+ authority_id: @authority_id,
+ monitoring: !!@event_monitoring,
+ events: @notify_count,
+ failures: @notify_fails,
+ }
+ end
+
+ def auth_authority
+ response = get("/auth/authority")
+ raise "unexpected response for /auth/authority: #{response.status_code}\n#{response.body}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ def domain : String
+ @place_domain.host.as(String)
+ end
+
+ def get_system(id : String, complete : Bool = false)
+ response = get("/api/engine/v2/systems/#{id}?complete=#{complete}", headers: authentication)
+ raise "unexpected response for system id #{id}: #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing system #{id}:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ def systems(
+ q : String? = nil,
+ zone_id : String? = nil,
+ capacity : Int32? = nil,
+ bookable : Bool? = nil,
+ features : String? = nil,
+ limit : Int32 = 1000,
+ offset : Int32 = 0,
+ )
+ placeos_client.systems.search(
+ q: q,
+ limit: limit,
+ offset: offset,
+ zone_id: zone_id,
+ capacity: capacity,
+ bookable: bookable,
+ features: features
+ )
+ end
+
+ record Setting, keys : Array(String), settings_string : String? do
+ include JSON::Serializable
+ end
+
+ @[Security(Level::Support)]
+ def system_settings(id : String, key : String)
+ response = get("/api/engine/v2/systems/#{id}/settings", headers: authentication)
+ raise "settings request failed for #{id}: #{response.status_code}" unless response.success?
+ setting = Array(Setting).from_json(response.body).select { |sub_setting|
+ sub_setting.settings_string && sub_setting.keys.includes?(key)
+ }.last?
+ return nil unless setting
+ YAML.parse(setting.settings_string.as(String))[key]
+ end
+
+ def systems_in_building(zone_id : String, ids_only : Bool = true)
+ levels = zones(parent: zone_id, tags: ["level"])
+ if ids_only
+ hash = {} of String => Array(String)
+ levels.each { |level| hash[level.id] = systems(zone_id: level.id).map(&.id) }
+ else
+ hash = {} of String => Array(::PlaceOS::Client::API::Models::System)
+ levels.each { |level| hash[level.id] = systems(zone_id: level.id) }
+ end
+ hash
+ end
+
+ # Staff details returns the information from AD
+ def staff_details(email : String)
+ response = get("/api/staff/v1/people/#{email}", headers: authentication)
+ raise "unexpected response for staff #{email}: #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing staff #{email}:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # ===================================
+ # Modules
+ # ===================================
+
+ @[Security(Level::Administrator)]
+ def start_or_stop_module(module_id : String, start : Bool)
+ response = post("/api/engine/v2/modules/#{module_id}/#{start ? "start" : "stop"}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # ===================================
+ # User details
+ # ===================================
+ def user(id : String)
+ placeos_client.users.fetch(id)
+ end
+
+ @[Security(Level::Support)]
+ def create_user(body_json : String)
+ response = post("/api/engine/v2/users", body: body_json, headers: authentication(HTTP::Headers{
+ "Content-Type" => "application/json",
+ }))
+ raise "failed to create user: #{response.status_code}" unless response.success?
+ PlaceOS::Client::API::Models::User.from_json response.body
+ end
+
+ @[Security(Level::Support)]
+ def update_user(id : String, body_json : String) : Nil
+ response = patch("/api/engine/v2/users/#{id}", body: body_json, headers: authentication(HTTP::Headers{
+ "Content-Type" => "application/json",
+ }))
+
+ raise "failed to update user #{id}: #{response.status_code}" unless response.success?
+ end
+
+ @[Security(Level::Support)]
+ def delete_user(id : String, force_removal : Bool = false) : Nil
+ response = delete("/api/engine/v2/users/#{id}?force_removal=#{force_removal}", headers: authentication)
+ raise "failed to delete user #{id}: #{response.status_code}" unless response.success?
+ end
+
+ @[Security(Level::Support)]
+ def revive_user(id : String) : Nil
+ response = post("/api/engine/v2/users/#{id}/revive", headers: authentication)
+ raise "failed to revive user #{id}: #{response.status_code}" unless response.success?
+ end
+
+ @[Security(Level::Support)]
+ def resource_token
+ response = post("/api/engine/v2/users/resource_token", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # NOTE:: this function requires "users" scope to be specified explicity for access
+ @[Security(Level::Administrator)]
+ def user_resource_token
+ response = post("/api/engine/v2/users/#{invoked_by_user_id}/resource_token", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ @[Security(Level::Support)]
+ def query_users(
+ q : String? = nil,
+ limit : Int32 = 20,
+ offset : Int32 = 0,
+ authority_id : String? = nil,
+ include_deleted : Bool = false,
+ )
+ placeos_client.users.search(q: q, limit: limit, offset: offset, authority_id: authority_id, include_deleted: include_deleted)
+ end
+
+ # ===================================
+ # WebRTC Helper functions
+ # ===================================
+
+ @[Security(Level::Support)]
+ def transfer_user(user_id : String, session_id : String, payload : JSON::Any)
+ status = 200
+ payload_str = payload.to_json
+ SimpleRetry.try_to(
+ max_attempts: 5,
+ base_interval: 1.second,
+ max_interval: 10.seconds,
+ ) do
+ response = post("/api/engine/v2/webrtc/transfer/#{user_id}/#{session_id}", headers: authentication, body: payload_str)
+ # 200 == success
+ # 428 == client is not connected to received the message, should be retried
+ status = response.status_code
+ raise "client not yet connected" unless response.success?
+ end
+ status
+ end
+
+ @[Security(Level::Support)]
+ def kick_user(user_id : String, session_id : String, reason : String)
+ response = post("/api/engine/v2/webrtc/kick/#{user_id}/#{session_id}", headers: authentication, body: {
+ reason: reason,
+ }.to_json)
+ response.status_code
+ end
+
+ def chat_members(session_id : String) : Array(String)
+ SimpleRetry.try_to(
+ max_attempts: 3,
+ base_interval: 1.second,
+ max_interval: 5.seconds,
+ ) do
+ response = get("/api/engine/v2/webrtc/members/#{session_id}", headers: authentication)
+ raise "webrtc service possibly unavailable" unless response.success?
+ Array(String).from_json(response.not_nil!.body)
+ end
+ end
+
+ # ===================================
+ # Uploads
+ # ===================================
+
+ def uploads(search : String? = nil, tags : Array(String) = [] of String, limit : Int32? = nil, offset : Int32? = nil)
+ tags_param = tags.join(",")
+
+ params = URI::Params.build do |form|
+ form.add("file_search", search.to_s) if search.presence
+ form.add("tags", tags_param) if tags_param.presence
+ form.add("limit", limit.to_s) if limit
+ form.add("offset", offset.to_s) if offset
+ end
+
+ response = get("/api/engine/v2/uploads?#{params}", headers: authentication)
+ raise "uploads request failed #{response.status_code}\n#{response.body}" unless response.success?
+
+ JSON.parse(response.body)
+ end
+
+ enum UploadPermissions
+ None
+ Admin
+ Support
+ end
+
+ # returns details for a signed URL that can be used to upload the file
+ # obviously this doesn't actually upload the file directly
+ def upload(
+ file_name : String,
+ file_size : Int64,
+ file_md5 : String,
+ file_mime : String? = nil,
+ file_path : String? = nil,
+ permissions : UploadPermissions = UploadPermissions::None,
+ public : Bool = false, # public internet accessible
+ tags : Array(String) = [] of String,
+ cache_etag : String? = nil,
+ cache_modified : Time? = nil,
+ )
+ response = post("/api/engine/v2/uploads", headers: authentication, body: {
+ file_name: file_name,
+ file_size: file_size,
+ file_id: file_md5,
+ file_mime: file_mime,
+ file_path: file_path,
+ permissions: permissions,
+ public: public,
+ tags: tags,
+ cache_etag: cache_etag,
+ cache_modified: cache_modified,
+ }.to_json)
+ raise "upload request failed #{response.status_code}\n#{response.body}" unless response.success?
+
+ # Looks like: {type: "chunked_upload" | "direct_upload", upload_id: "upload-1234", residence: "S3" | "AzureStorage",
+ # signature: {verb: "PUT", url: "https://signed.url/file", headers: {"Content-Type": "image/jpeg"}}}
+ JSON.parse(response.body)
+ end
+
+ # returns a temporary URL where you can download the upload contents
+ def upload_content_url(upload_id : String) : String
+ response = get("/api/engine/v2/uploads/#{upload_id}/url", headers: authentication)
+ raise "uploads request failed #{response.status_code}\n#{response.body}" unless response.status.see_other?
+ response.headers["Location"]
+ end
+
+ def upload_remove(upload_id : String) : Bool
+ response = delete("/api/engine/v2/uploads/#{upload_id}", headers: authentication)
+ raise "upload removal failed #{response.status_code}\n#{response.body}" unless response.success?
+ true
+ end
+
+ # ===================================
+ # Guest details
+ # ===================================
+ @[Security(Level::Support)]
+ def guest_details(guest_id : String)
+ response = get("/api/staff/v1/guests/#{guest_id}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ @[Security(Level::Support)]
+ def update_guest(id : String, body_json : String) : Nil
+ response = patch("/api/staff/v1/guests/#{id}", body: body_json, headers: authentication(HTTP::Headers{
+ "Content-Type" => "application/json",
+ }))
+
+ raise "failed to update guest #{id}: #{response.status_code}" unless response.success?
+ end
+
+ @[Security(Level::Support)]
+ def query_guests(period_start : Int64, period_end : Int64, zones : Array(String))
+ params = URI::Params.build do |form|
+ form.add "period_start", period_start.to_s
+ form.add "period_end", period_end.to_s
+ form.add "zone_ids", zones.join(",")
+ end
+
+ response = get("/api/staff/v1/guests?#{params}", headers: authentication)
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # ===================================
+ # CALENDAR EVENT ACTIONS (via staff api)
+ # ===================================
+ @[Security(Level::Support)]
+ def query_events(
+ period_start : Int64,
+ period_end : Int64,
+ zones : Array(String)? = nil,
+ systems : Array(String)? = nil,
+ capacity : Int32? = nil,
+ features : String? = nil,
+ bookable : Bool? = nil,
+ include_cancelled : Bool? = nil,
+ )
+ params = URI::Params.build do |form|
+ form.add "period_start", period_start.to_s
+ form.add "period_end", period_end.to_s
+ form.add "zone_ids", zones.join(",") if zones && !zones.empty?
+ form.add "system_ids", systems.join(",") if systems && !systems.empty?
+ form.add "capacity", capacity.to_s if capacity
+ form.add "features", features if features
+ form.add "bookable", bookable.to_s if !bookable.nil?
+ form.add "include_cancelled", include_cancelled.to_s if !include_cancelled.nil?
+ end
+
+ response = get("/api/staff/v1/events?#{params}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # gets an event from either the `system_id` or `calendar` if only one is provided
+ # if both are provided, it gets the event from `calendar` and the metadata from `system_id`
+ # NOTE:: the use of `calendar` will typically not work from a driver unless the X-API-Key
+ # has read access to it. From a driver perspective you should probably use a
+ # dedicated Calendar driver with application access and the query_metadata function
+ # below if metadata is required: `query_metadata(system_id: "sys", event_ref: ["id", "uuid"])`
+ def get_event(event_id : String, system_id : String? = nil, calendar : String? = nil)
+ raise ArgumentError.new("requires system_id or calendar param") unless calendar.presence || system_id.presence
+ params = URI::Params.build do |form|
+ form.add "calendar", calendar.to_s if calendar.presence
+ form.add "system_id", system_id.to_s if system_id.presence
+ end
+
+ response = get("/api/staff/v1/events/#{event_id}?#{params}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # NOTE:: https://docs.google.com/document/d/1OaZljpjLVueFitmFWx8xy8BT8rA2lITyPsIvSYyNNW8/edit#
+ # The service account making this request needs delegated access and hence you can only edit
+ # events associated with a resource calendar
+ def update_event(system_id : String, event : PlaceCalendar::Event)
+ response = patch("/api/staff/v1/events/#{event.id}?system_id=#{system_id}", headers: authentication, body: event.to_json)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ PlaceCalendar::Event.from_json(response.body)
+ end
+
+ def create_event(event : PlaceCalendar::Event)
+ response = post("/api/staff/v1/events", headers: authentication, body: event.to_json)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ PlaceCalendar::Event.from_json(response.body)
+ end
+
+ def delete_event(system_id : String, event_id : String)
+ response = delete("/api/staff/v1/events/#{event_id}?system_id=#{system_id}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success? || response.status_code == 404
+ true
+ end
+
+ def patch_event_metadata(system_id : String, event_id : String, metadata : JSON::Any, ical_uid : String? = nil, setup_time : Int64? = nil, breakdown_time : Int64? = nil, setup_event_id : String? = nil, breakdown_event_id : String? = nil)
+ params = URI::Params.build do |form|
+ form.add "ical_uid", ical_uid.to_s if ical_uid.presence
+ form.add "setup_time", setup_time.to_s if setup_time
+ form.add "breakdown_time", breakdown_time.to_s if breakdown_time
+ form.add "setup_event_id", setup_event_id.to_s if setup_event_id
+ form.add "breakdown_event_id", breakdown_event_id.to_s if breakdown_event_id
+ end
+ response = patch("/api/staff/v1/events/#{event_id}/metadata/#{system_id}?#{params}", headers: authentication, body: metadata.to_json)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ JSON::Any.from_json(response.body)
+ end
+
+ def replace_event_metadata(system_id : String, event_id : String, metadata : JSON::Any, ical_uid : String? = nil, setup_time : Int64? = nil, breakdown_time : Int64? = nil, setup_event_id : String? = nil, breakdown_event_id : String? = nil)
+ params = URI::Params.build do |form|
+ form.add "ical_uid", ical_uid.to_s if ical_uid.presence
+ form.add "setup_time", setup_time.to_s if setup_time
+ form.add "breakdown_time", breakdown_time.to_s if breakdown_time
+ form.add "setup_event_id", setup_event_id.to_s if setup_event_id
+ form.add "breakdown_event_id", breakdown_event_id.to_s if breakdown_event_id
+ end
+ response = put("/api/staff/v1/events/#{event_id}/metadata/#{system_id}?#{params}", headers: authentication, body: metadata.to_json)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ JSON::Any.from_json(response.body)
+ end
+
+ # Search for metadata that exists on events to obtain the event information.
+ # For response details see `EventMetadata__Assigner` in the OpenAPI docs
+ # https://editor.swagger.io/?url=https://raw.githubusercontent.com/PlaceOS/staff-api/master/OPENAPI_DOC.yml
+ def query_metadata(
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ field_name : String? = nil,
+ value : String? = nil,
+ system_id : String? = nil,
+ event_ref : Array(String)? = nil,
+ )
+ params = URI::Params.build do |form|
+ form.add "period_start", period_start.to_s if period_start
+ form.add "period_end", period_end.to_s if period_end
+ form.add "field_name", field_name if field_name.presence
+ form.add "value", value if value.presence
+ form.add "event_ref", event_ref.join(",") if event_ref && !event_ref.empty?
+ end
+
+ response = get("/api/staff/v1/events/extension_metadata/#{system_id}?#{params}", headers: authentication)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ begin
+ JSON.parse(response.body)
+ rescue error
+ logger.debug { "issue parsing:\n#{response.body.inspect}" }
+ raise error
+ end
+ end
+
+ # ===================================
+ # ZONE METADATA
+ # ===================================
+ def metadata(id : String, key : String? = nil)
+ placeos_client.metadata.fetch(id, key)
+ end
+
+ def metadata_children(id : String, key : String? = nil)
+ placeos_client.metadata.children(id, key)
+ end
+
+ @[Security(Level::Support)]
+ def write_metadata(id : String, key : String, payload : JSON::Any, description : String = "")
+ placeos_client.metadata.update(id, key, payload, description)
+ end
+
+ @[Security(Level::Support)]
+ def merge_metadata(id : String, key : String, payload : JSON::Any, description : String = "")
+ placeos_client.metadata.merge(id, key, payload, description)
+ end
+
+ # ===================================
+ # ZONE INFORMATION
+ # ===================================
+ def zone(zone_id : String)
+ placeos_client.zones.fetch zone_id
+ end
+
+ def zones(q : String? = nil,
+ limit : Int32 = 1000,
+ offset : Int32 = 0,
+ parent : String? = nil,
+ tags : Array(String) | String? = nil)
+ placeos_client.zones.search(
+ q: q,
+ limit: limit,
+ offset: offset,
+ parent_id: parent,
+ tags: tags
+ )
+ end
+
+ # ===================================
+ # BOOKINGS ACTIONS
+ # ===================================
+ @[Security(Level::Support)]
+ def create_booking(
+ booking_type : String,
+ asset_id : String,
+ user_id : String,
+ user_email : String,
+ user_name : String,
+ zones : Array(String),
+ booking_start : Int64? = nil,
+ booking_end : Int64? = nil,
+ checked_in : Bool = false,
+ approved : Bool? = nil,
+ title : String? = nil,
+ description : String? = nil,
+ time_zone : String? = nil,
+ extension_data : JSON::Any? = nil,
+ utm_source : String? = nil,
+ limit_override : Int64? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ attendees : Array(PlaceCalendar::Event::Attendee)? = nil,
+ process_state : String? = nil,
+ recurrence_type : String? = nil,
+ recurrence_days : Int32? = nil,
+ recurrence_nth_of_month : Int32? = nil,
+ recurrence_interval : Int32? = nil,
+ recurrence_end : Int64? = nil,
+ asset_ids : Array(String)? = nil,
+ asset_name : String? = nil,
+ )
+ now = time_zone ? Time.local(Time::Location.load(time_zone)) : Time.local
+ booking_start ||= now.at_beginning_of_day.to_unix
+ booking_end ||= now.at_end_of_day.to_unix
+
+ checked_in_at = now.to_unix if checked_in
+
+ logger.debug { "creating a #{booking_type} booking, starting #{booking_start}, asset #{asset_id}" }
+
+ params = URI::Params.build do |form|
+ form.add "utm_source", utm_source.to_s unless utm_source.nil?
+ form.add "limit_override", limit_override.to_s unless limit_override.nil?
+ form.add "event_id", event_id.to_s unless event_id.nil?
+ form.add "ical_uid", ical_uid.to_s unless ical_uid.nil?
+ end
+
+ response = post("/api/staff/v1/bookings?#{params}", headers: authentication, body: {
+ "booking_start" => booking_start,
+ "booking_end" => booking_end,
+ "booking_type" => booking_type,
+ "asset_id" => asset_id,
+ "asset_ids" => asset_ids,
+ "asset_name" => asset_name,
+ "user_id" => user_id,
+ "user_email" => user_email,
+ "user_name" => user_name,
+ "zones" => zones,
+ "checked_in" => checked_in,
+ "checked_in_at" => checked_in_at,
+ "approved" => approved,
+ "title" => title,
+ "description" => description,
+ "timezone" => time_zone,
+ "extension_data" => extension_data || JSON.parse("{}"),
+ "attendees" => attendees,
+ "process_state" => process_state,
+ "recurrence_type" => recurrence_type,
+ "recurrence_days" => recurrence_days,
+ "recurrence_nth_of_month" => recurrence_nth_of_month,
+ "recurrence_interval" => recurrence_interval,
+ "recurrence_end" => recurrence_end,
+ }.compact.to_json)
+ raise "issue creating #{booking_type} booking, starting #{booking_start}, asset #{asset_id}: #{response.status_code}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ @[Security(Level::Support)]
+ def update_booking(
+ booking_id : String | Int64,
+ booking_start : Int64? = nil,
+ booking_end : Int64? = nil,
+ asset_id : String? = nil,
+ title : String? = nil,
+ description : String? = nil,
+ timezone : String? = nil,
+ extension_data : JSON::Any? = nil,
+ approved : Bool? = nil,
+ checked_in : Bool? = nil,
+ limit_override : Int64? = nil,
+ instance : Int64? = nil,
+ recurrence_end : Int64? = nil,
+ )
+ logger.debug { "updating booking #{booking_id}" }
+
+ case checked_in
+ in true
+ checked_in_at = Time.utc.to_unix
+ in false
+ checked_out_at = Time.utc.to_unix
+ in nil
+ end
+
+ params = URI::Params.build do |form|
+ form.add "limit_override", limit_override.to_s unless limit_override.nil?
+ end
+
+ response = patch("/api/staff/v1/bookings/#{booking_id}?#{params}", headers: authentication, body: {
+ "booking_start" => booking_start,
+ "booking_end" => booking_end,
+ "checked_in" => checked_in,
+ "checked_in_at" => checked_in_at,
+ "checked_out_at" => checked_out_at,
+ "asset_id" => asset_id,
+ "title" => title,
+ "description" => description,
+ "timezone" => timezone,
+ "extension_data" => extension_data,
+ "instance" => instance,
+ "recurrence_end" => recurrence_end,
+ }.compact.to_json)
+ raise "issue updating booking #{booking_id}: #{response.status_code}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ @[Security(Level::Support)]
+ def reject(booking_id : String | Int64, utm_source : String? = nil, instance : Int64? = nil)
+ logger.debug { "rejecting booking #{booking_id}" }
+
+ params = URI::Params.build do |form|
+ form.add "instance", instance.to_s unless instance.nil?
+ form.add "utm_source", utm_source.to_s unless utm_source.nil?
+ end
+
+ response = post("/api/staff/v1/bookings/#{booking_id}/reject?#{params}", headers: authentication)
+ raise "issue rejecting booking #{booking_id}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ @[Security(Level::Support)]
+ def approve(booking_id : String | Int64, instance : Int64? = nil)
+ logger.debug { "approving booking #{booking_id}" }
+ inst = "/instance/#{instance}" if instance
+ response = post("/api/staff/v1/bookings/#{booking_id}/approve#{inst}", headers: authentication)
+ raise "issue approving booking #{booking_id}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ @[Security(Level::Support)]
+ def booking_state(booking_id : String | Int64, state : String, instance : Int64? = nil)
+ logger.debug { "updating booking #{booking_id}.#{instance} state to: #{state}" }
+ inst = "&instance=#{instance}" if instance
+ response = post("/api/staff/v1/bookings/#{booking_id}/update_state?state=#{state}#{inst}", headers: authentication)
+ raise "issue updating booking state #{booking_id}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ @[Security(Level::Support)]
+ def booking_check_in(booking_id : String | Int64, state : Bool = true, utm_source : String? = nil, instance : Int64? = nil)
+ logger.debug { "checking in booking #{booking_id}.#{instance} to: #{state}" }
+
+ params = URI::Params.build do |form|
+ form.add "instance", instance.to_s unless instance.nil?
+ form.add "utm_source", utm_source.to_s unless utm_source.nil?
+ form.add "state", state.to_s
+ end
+ response = post("/api/staff/v1/bookings/#{booking_id}/check_in?#{params}", headers: authentication)
+ raise "issue checking in booking #{booking_id}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ @[Security(Level::Support)]
+ def booking_delete(booking_id : String | Int64, utm_source : String? = nil, instance : Int64? = nil)
+ logger.debug { "deleting booking #{booking_id}" }
+ params = URI::Params.build do |form|
+ form.add "instance", instance.to_s unless instance.nil?
+ form.add "utm_source", utm_source.to_s unless utm_source.nil?
+ end
+ response = delete("/api/staff/v1/bookings/#{booking_id}?#{params}", headers: authentication)
+ raise "issue updating booking state #{booking_id}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ @[Security(Level::Support)]
+ def booking_extension_data(booking_id : String | Int64, extension_data : Hash(String, JSON::Any), instance : Int64? = nil, signal_changes : Bool = false)
+ logger.debug { "updating booking ext data #{booking_id}.#{instance} with: #{extension_data}" }
+
+ params = URI::Params.build do |form|
+ form.add "signal_changes", signal_changes.to_s
+ end
+
+ response = patch("/api/staff/v1/bookings/#{booking_id}/ext_data/#{instance}?#{params}", headers: authentication, body: extension_data.to_json)
+ raise "issue updating booking #{booking_id}.#{instance}: #{response.status_code}\n#{response.body}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ # ===================================
+ # BOOKINGS QUERY
+ # ===================================
+ def query_bookings(
+ type : String? = nil,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ rejected : Bool? = nil,
+ checked_in : Bool? = nil,
+ include_checked_out : Bool? = nil,
+ extension_data : JSON::Any? = nil,
+ deleted : Bool? = nil,
+ asset_id : String? = nil,
+ limit : Int32? = nil,
+ )
+ default_end = @period_end_default_in_min || 30
+
+ # Assumes occuring now
+ period_start ||= Time.utc.to_unix
+ period_end ||= default_end.minutes.from_now.to_unix
+ limit ||= @query_limit
+
+ params = URI::Params.build do |form|
+ form.add "period_start", period_start.to_s if period_start
+ form.add "period_end", period_end.to_s if period_end
+ form.add "type", type.to_s if type.presence
+
+ form.add "zones", zones.join(",") unless zones.empty?
+ form.add "user", user.to_s if user.presence
+ form.add "email", email.to_s if email.presence
+ form.add "state", state.to_s if state.presence
+ form.add "created_before", created_before.to_s if created_before
+ form.add "created_after", created_after.to_s if created_after
+ form.add "approved", approved.to_s unless approved.nil?
+ form.add "rejected", rejected.to_s unless rejected.nil?
+ form.add "checked_in", checked_in.to_s unless checked_in.nil?
+ form.add "deleted", deleted.to_s unless deleted.nil?
+ form.add "event_id", event_id.to_s if event_id.presence
+ form.add "ical_uid", ical_uid.to_s if ical_uid.presence
+ form.add "include_checked_out", include_checked_out.to_s unless include_checked_out.nil?
+
+ form.add "asset_id", asset_id.to_s unless asset_id.nil?
+ form.add "limit", limit.to_s
+
+ if extension_data
+ value = extension_data.as_h.map { |k, v| "#{k}:#{v}" }.join(",")
+ form.add "extension_data", "{#{value}}"
+ end
+ end
+
+ logger.debug { "requesting staff/v1/bookings: #{params}" }
+
+ # Get the existing bookings from the API to check if there is space
+ bookings = [] of JSON::Any
+ next_request = "/api/staff/v1/bookings?#{params}"
+
+ loop do
+ response = get(next_request, headers: authentication)
+ raise "issue loading list of bookings (zones #{zones}): #{response.status_code}" unless response.success?
+ links = LinkHeader.new(response)
+
+ # Just parse it here instead of using the Bookings object
+ # it will be parsed into an object on the far end
+ new_bookings = JSON.parse(response.body).as_a
+ bookings.concat new_bookings
+
+ last_req = next_request
+ next_request = links["next"]?
+ break if next_request.nil? || new_bookings.empty? || last_req == next_request
+ end
+
+ logger.debug { "bookings count: #{bookings.size}" }
+
+ bookings
+ end
+
+ def get_booking(booking_id : String | Int64, instance : Int64? = nil)
+ logger.debug { "getting booking #{booking_id}" }
+ params = "?instance=#{instance}" if instance
+ response = get("/api/staff/v1/bookings/#{booking_id}#{params}", headers: authentication)
+ raise "issue getting booking #{booking_id}: #{response.status_code}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ # lists asset IDs based on the parameters provided
+ #
+ # booking_type is required unless event_id or ical_uid is present
+ def booked(
+ type : String? = nil,
+ period_start : Int64? = nil,
+ period_end : Int64? = nil,
+ zones : Array(String) = [] of String,
+ user : String? = nil,
+ email : String? = nil,
+ state : String? = nil,
+ event_id : String? = nil,
+ ical_uid : String? = nil,
+ created_before : Int64? = nil,
+ created_after : Int64? = nil,
+ approved : Bool? = nil,
+ checked_in : Bool? = nil,
+ include_checked_out : Bool? = nil,
+ include_booked_by : Bool? = nil,
+ department : String? = nil,
+ limit : Int32? = nil,
+ offset : Int32? = nil,
+ permission : String? = nil,
+ extension_data : JSON::Any? = nil,
+ )
+ params = URI::Params.build do |form|
+ form.add "period_start", period_start.to_s if period_start
+ form.add "period_end", period_end.to_s if period_end
+ form.add "type", type.to_s if type.presence
+
+ form.add "zones", zones.join(",") unless zones.empty?
+ form.add "user", user.to_s if user.presence
+ form.add "email", email.to_s if email.presence
+ form.add "state", state.to_s if state.presence
+ form.add "created_before", created_before.to_s if created_before
+ form.add "created_after", created_after.to_s if created_after
+ form.add "approved", approved.to_s unless approved.nil?
+ form.add "checked_in", checked_in.to_s unless checked_in.nil?
+ form.add "event_id", event_id.to_s if event_id.presence
+ form.add "ical_uid", ical_uid.to_s if ical_uid.presence
+ form.add "include_checked_out", include_checked_out.to_s unless include_checked_out.nil?
+ form.add "include_booked_by", include_booked_by.to_s unless include_booked_by.nil?
+ form.add "department", department.to_s if department.presence
+ form.add "limit", limit.to_s if limit
+ form.add "offset", offset.to_s if offset
+ form.add "permission", permission.to_s if permission.presence
+
+ if extension_data
+ value = extension_data.as_h.map { |k, v| "#{k}:#{v}" }.join(",")
+ form.add "extension_data", "{#{value}}"
+ end
+ end
+
+ logger.debug { "requesting staff/v1/bookings/booked: #{params}" }
+ response = get("/api/staff/v1/bookings/booked?#{params}", headers: authentication)
+ raise "issue getting booked assets: #{response.status_code}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ # ===================================
+ # Driver debugging
+ # ===================================
+
+ def driver_introspection
+ {
+ protocol: PlaceOS::Driver::Stats.protocol_tracking,
+ memory: PlaceOS::Driver::Stats.memory_usage,
+ queue: @__queue__.@queue.size,
+ }
+ end
+
+ # ===================================
+ # SURVEYS
+ # ===================================
+
+ def get_survey_invites(survey_id : Int64? = nil, sent : Bool? = nil)
+ logger.debug { "getting survey_invites (survey #{survey_id}, sent #{sent})" }
+ params = URI::Params.new
+ params["survey_id"] = survey_id.to_s if survey_id
+ params["sent"] = sent.to_s unless sent.nil?
+ response = get("/api/staff/v1/surveys/invitations", params, headers: authentication)
+ raise "issue getting survey invitations (survey #{survey_id}, sent #{sent}): #{response.status_code}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ @[Security(Level::Support)]
+ def update_survey_invite(
+ token : String,
+ email : String? = nil,
+ sent : Bool? = nil,
+ )
+ logger.debug { "updating survey invite #{token}" }
+ response = patch("/api/staff/v1/surveys/invitations/#{token}", headers: authentication, body: {
+ "email" => email,
+ "sent" => sent,
+ }.compact.to_json)
+ raise "issue updating survey invite #{token}: #{response.status_code}" unless response.success?
+ true
+ end
+
+ # ===================================
+
+ @[Security(Level::Support)]
+ def signal(channel : String, payload : JSON::Any? = nil)
+ placeos_client.root.signal(channel, payload)
+ end
+
+ # For accessing PlaceOS APIs
+ protected getter placeos_client : PlaceOS::Client do
+ insecure = setting?(Bool, :https_insecure) || setting?(String, :https_verify) == "none"
+ PlaceOS::Client.new(
+ @place_domain,
+ host_header: @host_header,
+ x_api_key: @api_key,
+ insecure: insecure
+ )
+ end
+
+ # ===================================
+ # PLACEOS AUTHENTICATION:
+ # ===================================
+ protected def authentication(headers : HTTP::Headers = HTTP::Headers.new) : HTTP::Headers
+ headers["Accept"] = "application/json"
+ headers["X-API-Key"] = @api_key.presence || "spec-test"
+ headers
+ end
+end
diff --git a/drivers/place/staff_api_spec.cr b/drivers/place/staff_api_spec.cr
new file mode 100644
index 00000000000..76ede5046fc
--- /dev/null
+++ b/drivers/place/staff_api_spec.cr
@@ -0,0 +1,92 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::StaffAPI" do
+ resp = exec(:query_bookings, "desk")
+
+ expect_http_request do |request, response|
+ headers = request.headers
+ if headers["X-API-Key"]? == "spec-test"
+ response.status_code = 200
+ response << %([{
+ "id": 1234,
+ "user_id": "user-12345",
+ "user_email": "steve@place.tech",
+ "user_name": "Steve T",
+ "asset_id": "desk-2-12",
+ "zones": ["zone-build1", "zone-level2"],
+ "booking_type": "Steve T",
+ "booking_start": 123456,
+ "booking_end": 12345678,
+ "timezone": "Australia/Sydney",
+ "checked_in": true,
+ "rejected": false,
+ "approved": false
+ }])
+ else
+ response.status_code = 401
+ end
+ end
+
+ resp.get.should eq(JSON.parse(%([{
+ "id": 1234,
+ "user_id": "user-12345",
+ "user_email": "steve@place.tech",
+ "user_name": "Steve T",
+ "asset_id": "desk-2-12",
+ "zones": ["zone-build1", "zone-level2"],
+ "booking_type": "Steve T",
+ "booking_start": 123456,
+ "booking_end": 12345678,
+ "timezone": "Australia/Sydney",
+ "checked_in": true,
+ "rejected": false,
+ "approved": false
+ }])))
+
+ sleep 1
+ invites_resp = exec(:get_survey_invites, sent: false)
+
+ expect_http_request do |request, response|
+ headers = request.headers
+ if headers["X-API-Key"]? == "spec-test"
+ response.status_code = 200
+
+ params = request.query_params
+ survey_id = params["survey_id"]? || 1234
+ sent = params["sent"]?
+
+ sent_invite = {
+ id: 123,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user@spec.test",
+ sent: true,
+ }
+ unsent_invite = {
+ id: 123,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user@spec.test",
+ sent: false,
+ }
+
+ if sent == "true"
+ response << [sent_invite].to_json
+ elsif sent == "false"
+ response << [unsent_invite].to_json
+ else
+ response << [sent_invite, unsent_invite].to_json
+ end
+ else
+ response.status_code = 401
+ end
+ end
+
+ invites_resp.get.should eq(JSON.parse(%([{
+ "id": 123,
+ "survey_id": 1234,
+ "token": "QWERTY",
+ "email": "user@spec.test",
+ "sent": false
+ }])))
+end
diff --git a/drivers/place/survey_mailer.cr b/drivers/place/survey_mailer.cr
new file mode 100644
index 00000000000..4f65d195b91
--- /dev/null
+++ b/drivers/place/survey_mailer.cr
@@ -0,0 +1,98 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+
+class Place::SurveyMailer < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+
+ descriptive_name "PlaceOS Survey Mailer"
+ generic_name :SurveyMailer
+ description %(emails survey invites)
+
+ default_settings({
+ timezone: "GMT",
+ send_invites: "*/3 * * * *",
+ email_template: "survey",
+ })
+
+ accessor staff_api : StaffAPI_1
+
+ def mailer
+ system.implementing(Interface::Mailer)[0]
+ end
+
+ @time_zone : Time::Location = Time::Location.load("GMT")
+
+ @visitor_emails_sent : UInt64 = 0_u64
+ @visitor_email_errors : UInt64 = 0_u64
+
+ @email_template : String = "survey"
+ @send_invites : String? = nil
+
+ def on_update
+ @send_invites = setting?(String, :send_invites).presence
+ @email_template = setting?(String, :email_template) || "survey"
+
+ time_zone = setting?(String, :timezone).presence || "GMT"
+ @time_zone = Time::Location.load(time_zone)
+
+ schedule.clear
+ if invites = @send_invites
+ schedule.cron(invites, @time_zone) { send_survey_emails }
+ end
+ end
+
+ def template_fields : Array(TemplateFields)
+ [
+ TemplateFields.new(
+ trigger: {@email_template, "invite"},
+ name: "Survey invite",
+ description: "Email invitation sent to participants to complete a survey",
+ fields: [
+ {name: "email", description: "Email address of the survey recipient"},
+ {name: "token", description: "Unique authentication token for accessing the survey"},
+ {name: "survey_id", description: "Unique identifier of the survey to be completed"},
+ ]
+ ),
+ ]
+ end
+
+ @[Security(Level::Support)]
+ def send_survey_emails
+ invites = Array(SurveyInvite).from_json staff_api.get_survey_invites(sent: false).get.to_json
+ sent_invites : Hash(String, Array(Int64)) = {} of String => Array(Int64)
+
+ invites.each do |invite|
+ next if invite.sent
+ begin
+ if !(sent_surveys = sent_invites[invite.email]?) || !sent_surveys.includes?(invite.survey_id)
+ sent_invites[invite.email] ||= [] of Int64
+ sent_invites[invite.email] << invite.survey_id
+
+ mailer.send_template(
+ to: invite.email,
+ template: {@email_template, "invite"},
+ args: {
+ email: invite.email,
+ token: invite.token,
+ survey_id: invite.survey_id,
+ })
+ end
+
+ staff_api.update_survey_invite(invite.token, sent: true)
+ rescue error
+ logger.warn(exception: error) { "failed to send survey email to #{invite.email}" }
+ end
+ end
+ end
+
+ struct SurveyInvite
+ include JSON::Serializable
+
+ property id : Int64
+ property survey_id : Int64
+ property token : String
+ property email : String
+ property sent : Bool?
+ end
+end
diff --git a/drivers/place/survey_mailer_spec.cr b/drivers/place/survey_mailer_spec.cr
new file mode 100644
index 00000000000..aca455dde19
--- /dev/null
+++ b/drivers/place/survey_mailer_spec.cr
@@ -0,0 +1,99 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/mailer"
+
+class StaffAPI < DriverSpecs::MockDriver
+ def get_survey_invites(survey_id : Int64? = nil, sent : Bool? = nil)
+ survey_id ||= 1
+
+ invites = [
+ {
+ id: 1,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user1@spec.test",
+ sent: false,
+ },
+ {
+ id: 2,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user1@spec.test",
+ sent: false,
+ },
+ {
+ id: 3,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user2@spec.test",
+ sent: false,
+ },
+ {
+ id: 4,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user3@spec.test",
+ sent: nil,
+ },
+ {
+ id: 5,
+ survey_id: survey_id,
+ token: "QWERTY",
+ email: "user4@spec.test",
+ sent: true,
+ },
+ ]
+
+ JSON.parse(invites.to_json)
+ end
+
+ def update_survey_invite(token : String, email : String? = nil, sent : Bool? = nil)
+ true
+ end
+end
+
+class Mailer < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Mailer
+
+ def on_load
+ self[:sent] = 0
+ end
+
+ def send_template(
+ to : String | Array(String),
+ template : Tuple(String, String),
+ args : TemplateItems,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ )
+ self[:sent] = self[:sent].as_i + 1
+ end
+
+ def send_mail(
+ to : String | Array(String),
+ subject : String,
+ message_plaintext : String? = nil,
+ message_html : String? = nil,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ ) : Bool
+ true
+ end
+end
+
+DriverSpecs.mock_driver "Place::StaffAPI" do
+ system({
+ StaffAPI: {StaffAPI},
+ Mailer: {Mailer},
+ })
+
+ _resp = exec(:send_survey_emails).get
+ system(:Mailer_1)[:sent].should eq 3
+end
diff --git a/drivers/place/template_mailer.cr b/drivers/place/template_mailer.cr
new file mode 100644
index 00000000000..abb827cd83c
--- /dev/null
+++ b/drivers/place/template_mailer.cr
@@ -0,0 +1,298 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+
+# This driver uses metadata templates to send emails via the SMTP mailer.
+# It should be configured as Mailer_1 with the next mailer in the chain as Mailer_2.
+#
+# It also updates metadata in the staff API with available fields for use in email templates.
+class Place::TemplateMailer < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::Mailer
+
+ alias TemplateFields = PlaceOS::Driver::Interface::MailerTemplates::TemplateFields
+
+ descriptive_name "Template Mailer"
+ generic_name :Mailer
+ description %(uses metadata templates to send emails via the SMTP mailer)
+
+ default_settings({
+ cache_timeout: 300, # timeout for the template cache
+ keep_if_not_seen: 6, # keep fields for x updates if not seen, -1 to keep forever, 0 to never keep
+ timezone: "Australia/Sydney",
+ update_schedule: "*/20 * * * *", # cron schedule for updating template fields
+ })
+
+ accessor staff_api : StaffAPI_1
+
+ getter org_zone_ids : Array(String) { get_zone_ids?("org").not_nil! }
+ getter region_zone_ids : Array(String) { get_zone_ids?("region").not_nil! }
+ getter building_zone_ids : Array(String) { get_zone_ids?("building").not_nil! }
+ getter level_zone_ids : Array(String) { get_zone_ids?("level").not_nil! }
+
+ getter org_zone_id : String { get_local_zone_id(org_zone_ids).not_nil! }
+ getter building_zone_id : String { get_local_zone_id(building_zone_ids).not_nil! }
+
+ def mailer
+ system.implementing(Interface::Mailer)[1]
+ end
+
+ SEPERATOR = "."
+
+ @template_cache : TemplateCache = TemplateCache.new
+ @cache_timeout : Int64 = 300
+
+ # keep fields for x updates if not seen
+ # -1 to keep forever
+ # 0 to never keep
+ # 1 to keep for 1 update
+ @keep_if_not_seen : Int64 = 6
+ @not_seen_times : Hash(String, Int64) = Hash(String, Int64).new
+
+ @timezone : Time::Location = Time::Location.load("Australia/Sydney")
+ @update_schedule : String? = nil
+
+ def on_update
+ @org_zone_ids = nil
+ @region_zone_ids = nil
+ @building_zone_ids = nil
+ @level_zone_ids = nil
+
+ @org_zone_id = nil
+ @building_zone_id = nil
+
+ @cache_timeout = setting?(Int64, :cache_timeout) || 300_i64
+ @keep_if_not_seen = setting?(Int64, :keep_if_not_seen) || 6_i64
+
+ timezone = setting?(String, :timezone).presence || "Australia/Sydney"
+ @timezone = Time::Location.load(timezone)
+ @update_schedule = setting?(String, :update_schedule).presence
+
+ schedule.clear
+
+ if update_schedule = @update_schedule
+ schedule.cron(update_schedule, @timezone) do
+ update_template_fields(org_zone_id)
+ end
+ end
+
+ update_template_fields(org_zone_id)
+ end
+
+ def get_zone_ids?(tag : String) : Array(String)?
+ staff_api.zones(tags: tag).get.as_a.map(&.[]("id").as_s)
+ rescue error
+ logger.warn(exception: error) { "unable to determine #{tag} zone ids" }
+ nil
+ end
+
+ def get_local_zone_id(zone_ids : Array(String)) : String?
+ (zone_ids & system.zones).first
+ rescue error
+ logger.warn(exception: error) { "unable to determine local zone id" }
+ nil
+ end
+
+ def get_template_fields?(zone_id : String) : Hash(String, MetadataTemplateFields)?
+ metadata = Metadata.from_json staff_api.metadata(zone_id, "email_template_fields").get["email_template_fields"].to_json
+ Hash(String, MetadataTemplateFields).from_json metadata.details.to_json
+ rescue error
+ logger.warn(exception: error) { "unable to get email template fields from zone #{zone_id} metadata" }
+ nil
+ end
+
+ def sticky_template_fields(zone_id : String) : Hash(String, MetadataTemplateFields)
+ # keep nothing
+ return Hash(String, MetadataTemplateFields).new if @keep_if_not_seen == 0
+
+ current_fields = get_template_fields?(zone_id) || Hash(String, MetadataTemplateFields).new
+ return current_fields if current_fields.empty?
+
+ # keep forever
+ return current_fields if @keep_if_not_seen == -1
+
+ sticky_fields = Hash(String, MetadataTemplateFields).new
+
+ current_fields.keys.each do |key|
+ @not_seen_times[key] = @not_seen_times[key]? ? @not_seen_times[key] + 1 : 1_i64
+
+ if @not_seen_times[key] <= @keep_if_not_seen
+ sticky_fields[key] = current_fields[key]
+ end
+ end
+
+ sticky_fields
+ end
+
+ def update_template_fields(zone_id : String)
+ template_fields : Hash(String, MetadataTemplateFields) = sticky_template_fields(zone_id)
+
+ system.implementing(Interface::MailerTemplates).each do |driver|
+ # next if the driver is turned off, or anything else goes wrong
+ begin
+ driver_template_fields = Array(TemplateFields).from_json driver.template_fields.get.to_json
+ rescue error
+ logger.warn(exception: error) { "unable to get template fields from module #{driver.module_id}" }
+ next
+ end
+
+ driver_template_fields = Array(TemplateFields).from_json driver.template_fields.get.to_json
+ driver_template_fields.each do |field_list|
+ template_fields["#{field_list[:trigger].join(SEPERATOR)}"] = MetadataTemplateFields.new(
+ module_name: driver.module_name,
+ name: field_list[:name],
+ description: field_list[:description],
+ fields: field_list[:fields],
+ )
+ end
+ end
+
+ template_fields.keys.each do |key|
+ @not_seen_times[key] = 0_i64
+ end
+
+ self[:template_fields] = template_fields
+
+ unless template_fields.empty?
+ staff_api.write_metadata(id: zone_id, key: "email_template_fields", payload: template_fields, description: "Available fields for use in email templates").get
+ end
+ end
+
+ # fetch templates from cache or metadata
+ def fetch_templates(zone_id : String?) : Array(Template)
+ return [] of Template unless zone_id
+
+ if (cache = @template_cache[zone_id]?) && cache[0] > Time.utc.to_unix
+ cache[1]
+ else
+ templates = get_templates?(zone_id) || [] of Template
+ @template_cache[zone_id] = {Time.utc.to_unix + @cache_timeout, templates}
+ templates
+ end
+ end
+
+ def template_cache
+ @template_cache
+ end
+
+ def clear_template_cache(zone_id : String? = nil)
+ if zone_id && !zone_id.blank?
+ @template_cache.delete(zone_id)
+ else
+ @template_cache = TemplateCache.new
+ end
+ end
+
+ # get templates from metadata
+ def get_templates?(zone_id : String) : Array(Template)?
+ metadata = Metadata.from_json staff_api.metadata(zone_id, "email_templates").get["email_templates"].to_json
+ metadata.details.as_a.map { |template| Template.from_json template.to_json }
+ rescue
+ logger.debug { "unable to get email templates from zone #{zone_id} metadata" }
+ nil
+ end
+
+ def find_template?(template : String, zone_ids : Array(String)) : Template?
+ org_id = (zone_ids & org_zone_ids)[0]?
+ region_id = (zone_ids & region_zone_ids)[0]?
+ building_id = (zone_ids & building_zone_ids)[0]?
+ level_id = (zone_ids & level_zone_ids)[0]?
+
+ # find the requested template
+ # order of precedence: level, building, region, org
+ fetch_templates(level_id).find { |t| t["trigger"] == template } ||
+ fetch_templates(building_id).find { |t| t["trigger"] == template } ||
+ fetch_templates(region_id).find { |t| t["trigger"] == template } ||
+ fetch_templates(org_id).find { |t| t["trigger"] == template } ||
+ nil
+ end
+
+ def generate_svg_qrcode(text : String) : String
+ mailer.generate_svg_qrcode(text).get.as_s
+ end
+
+ def generate_png_qrcode(text : String, size : Int32 = 128) : String
+ mailer.generate_png_qrcode(text, size).get.as_s
+ end
+
+ def send_mail(
+ to : String | Array(String),
+ subject : String,
+ message_plaintext : String? = nil,
+ message_html : String? = nil,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ )
+ mailer.send_mail(to, subject, message_plaintext, message_html, resource_attachments, attachments, cc, bcc, from, reply_to)
+ end
+
+ def send_template(
+ to : String | Array(String),
+ template : Tuple(String, String),
+ args : TemplateItems,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ )
+ zone_ids = if (zones = args["zone_ids"]?) && zones.is_a?(Array(String))
+ zones
+ else
+ [org_zone_id, building_zone_id]
+ end
+
+ metadata_template = find_template?(template.join(SEPERATOR), zone_ids)
+
+ if metadata_template
+ subject = build_template(metadata_template["subject"].to_s, args)
+ text = build_template(metadata_template["text"]?.try &.to_s, args) || ""
+ html = build_template(metadata_template["html"]?.try &.to_s, args) || ""
+ from = metadata_template["from"].to_s if (from_template = metadata_template["from"]?) && from_template.to_s.presence
+ reply_to = metadata_template["reply_to"].to_s if (reply_to_template = metadata_template["reply_to"]?) && reply_to_template.to_s.presence
+
+ mailer.send_mail(to, subject, text, html, resource_attachments, attachments, cc, bcc, from, reply_to)
+ else
+ logger.info { "unable to find template #{template.join(SEPERATOR)} from zones #{zone_ids} metadata, forwarding to Mailer_2" }
+ mailer.send_template(to, template, args, resource_attachments, attachments, cc, bcc, from, reply_to)
+ end
+ end
+
+ alias Template = Hash(String, String | Int64)
+
+ # zone_id, timeout, templates
+ alias TemplateCache = Hash(String, Tuple(Int64, Array(Template)))
+
+ struct Metadata
+ include JSON::Serializable
+
+ property name : String
+ property description : String = ""
+ property details : JSON::Any
+ property parent_id : String
+ property schema_id : String? = nil
+ property editors : Set(String) = Set(String).new
+ property modified_by_id : String? = nil
+ end
+
+ struct MetadataTemplateFields
+ include JSON::Serializable
+
+ property module_name : String = ""
+ property name : String = ""
+ property description : String? = nil
+ property fields : Array(NamedTuple(name: String, description: String)) = [] of NamedTuple(name: String, description: String)
+
+ def initialize(
+ @module_name : String,
+ @name : String,
+ @description : String? = nil,
+ @fields : Array(NamedTuple(name: String, description: String)) = [] of NamedTuple(name: String, description: String)
+ )
+ end
+ end
+end
diff --git a/drivers/place/template_mailer_spec.cr b/drivers/place/template_mailer_spec.cr
new file mode 100644
index 00000000000..b1bd6e50c64
--- /dev/null
+++ b/drivers/place/template_mailer_spec.cr
@@ -0,0 +1,157 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+
+class StaffAPI < DriverSpecs::MockDriver
+ ZONES = [
+ {
+ created_at: 1660537814,
+ updated_at: 1681800971,
+ id: "zone-org-1234",
+ name: "Test Org Zone",
+ display_name: "Test Org Zone",
+ location: "",
+ description: "",
+ code: "",
+ type: "",
+ count: 0,
+ capacity: 0,
+ map_id: "",
+ tags: [
+ "org",
+ ],
+ triggers: [] of String,
+ parent_id: "zone-0000",
+ timezone: "Australia/Sydney",
+ },
+ {
+ created_at: 1660537814,
+ updated_at: 1681800971,
+ id: "zone-bld-1234",
+ name: "Test Building Zone",
+ display_name: "Test Building Zone",
+ location: "",
+ description: "",
+ code: "",
+ type: "",
+ count: 0,
+ capacity: 0,
+ map_id: "",
+ tags: [
+ "building",
+ ],
+ triggers: [] of String,
+ parent_id: "zone-0000",
+ timezone: "Australia/Sydney",
+ },
+ ]
+
+ # METADATA_TEMPLATES = {
+ # email_templates = {
+ # name: "email_templates",
+ # description: "Email Templates for Zone",
+ # details: [
+ # {
+ # id: "template-1",
+ # from: "support@example.com",
+ # html: "This is a test template
",
+ # text: "This is a test template",
+ # subject: "Test 1",
+ # trigger: "visitor_invited.visitor",
+ # zone_id: "zone-1234",
+ # category: "internal",
+ # reply_to: "noreply@example.com",
+ # created_at: 1725519680,
+ # updated_at: 1725519680,
+ # },
+ # {
+ # id: "template-2",
+ # from: "support@example.com",
+ # html: "This is a test template
",
+ # text: "This is a test template",
+ # subject: "Test 2",
+ # trigger: "visitor_invited.event",
+ # zone_id: "zone-1234",
+ # category: "internal",
+ # reply_to: "noreply@example.com",
+ # created_at: 1727745875,
+ # updated_at: 1727745875,
+ # },
+ # ],
+ # parent_id: "zone-1234",
+ # editors: [] of String,
+ # modified_by_id: "user-1234",
+ # },
+ # }
+
+ def zones(q : String? = nil,
+ limit : Int32 = 1000,
+ offset : Int32 = 0,
+ parent : String? = nil,
+ tags : Array(String) | String? = nil)
+ zones = ZONES
+ zones = zones.select { |zone| zone["tags"].includes?(tags) } if tags.is_a?(String)
+ JSON.parse(zones.to_json)
+ end
+
+ # def metadata(id : String, key : String? = nil)
+ # case key
+ # when "email_templates"
+ # JSON.parse(METADATA_TEMPLATES.to_json)
+ # when "email_template_fields"
+ # nil
+ # else
+ # nil
+ # end
+ # end
+end
+
+class Mailer < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::Mailer
+
+ def on_load
+ self[:sent] = 0
+ end
+
+ def send_template(
+ to : String | Array(String),
+ template : Tuple(String, String),
+ args : TemplateItems,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ )
+ self[:sent] = self[:sent].as_i + 1
+ true
+ end
+
+ def send_mail(
+ to : String | Array(String),
+ subject : String,
+ message_plaintext : String? = nil,
+ message_html : String? = nil,
+ resource_attachments : Array(ResourceAttachment) = [] of ResourceAttachment,
+ attachments : Array(Attachment) = [] of Attachment,
+ cc : String | Array(String) = [] of String,
+ bcc : String | Array(String) = [] of String,
+ from : String | Array(String) | Nil = nil,
+ reply_to : String | Array(String) | Nil = nil
+ ) : Bool
+ self[:sent] = self[:sent].as_i + 1
+ true
+ end
+end
+
+DriverSpecs.mock_driver "Place::TemplateMailer" do
+ # system({
+ # StaffAPI: {StaffAPI},
+ # Mailer_1: {Mailer},
+ # Mailer_2: {Mailer},
+ # })
+
+ # Missing hash key: "mod-Mailer/2" (KeyError)
+ # system(:Mailer_2)[:sent].should eq 0
+end
diff --git a/drivers/place/user_group_mappings.cr b/drivers/place/user_group_mappings.cr
new file mode 100644
index 00000000000..979ad7fa0b8
--- /dev/null
+++ b/drivers/place/user_group_mappings.cr
@@ -0,0 +1,185 @@
+require "placeos-driver"
+
+class Place::UserGroupMappings < PlaceOS::Driver
+ descriptive_name "User Group Mappings"
+ generic_name :UserGroupMappings
+ description "monitors user logins and maps relevent groups to the local user profile"
+
+ accessor staff_api : StaffAPI_1
+ accessor calendar_api : Calendar_1
+
+ # NOTE:: user_sys_admin, user_support sets the users persmissions flags
+ default_settings({
+ # ID => place_name
+ group_mappings: {
+ "group_id" => {
+ place_id: "manager",
+ description: "managers of the level2 building",
+ },
+ "group2_id" => {
+ place_id: "boss",
+ description: "people that can access everything",
+ },
+ "ad_group3_id" => {
+ place_id: "user_sys_admin",
+ description: "this is a special group that sets place users as sys_admins",
+ },
+ },
+
+ # Group name prefix => group mappings
+ group_prefix: {
+ "group_name_prefix_" => {
+ strip_prefix: false,
+ place_id: "optional-place-id",
+ },
+ },
+
+ # authority id
+ authority_id: "authority-12345",
+ })
+
+ class UserLogin
+ include JSON::Serializable
+
+ property user_id : String
+ property provider : String
+ end
+
+ def on_load
+ monitor("auth/login") { |_subscription, payload| new_user_login(payload) }
+ on_update
+ end
+
+ alias Mapping = NamedTuple(place_id: String)
+ alias Prefix = NamedTuple(strip_prefix: Bool?, place_id: String?)
+
+ @authority_id : Array(String) = [] of String
+ @group_mappings : Hash(String, Mapping) = {} of String => Mapping
+ @group_prefixes : Hash(String, Prefix) = {} of String => Prefix
+ @users_checked : UInt64 = 0_u64
+ @error_count : UInt64 = 0_u64
+
+ def on_update
+ @group_mappings = setting?(Hash(String, Mapping), :group_mappings) || {} of String => Mapping
+ @group_prefixes = setting?(Hash(String, Prefix), :group_prefix) || {} of String => Prefix
+ @group_prefixes = @group_prefixes.transform_keys(&.downcase)
+
+ authority_id = setting?(String | Array(String), :authority_id) || "authority-12345"
+ case authority_id
+ in String
+ @authority_id = [authority_id]
+ in Array(String)
+ @authority_id = authority_id
+ end
+ end
+
+ protected def new_user_login(user_json)
+ user_details = UserLogin.from_json user_json
+ check_user(user_details.user_id)
+
+ @users_checked += 1
+ self[:users_checked] = @users_checked
+ rescue error
+ logger.error { error.inspect_with_backtrace }
+ self[:last_error] = {
+ error: error.message,
+ time: Time.local.to_s,
+ user: user_json,
+ }
+ @error_count += 1
+ self[:error_count] = @error_count
+ end
+
+ @[Security(Level::Support)]
+ def check_user(id : String) : Nil
+ logger.debug { "checking groups of: #{id}" }
+
+ # Loading the existing user info in PlaceOS (we need the users id)
+ user_json = staff_api.user(id).get
+ auth_id = user_json["authority_id"].as_s
+ return unless auth_id.in?(@authority_id)
+ sync_user(user_json)
+ end
+
+ protected def sync_user(user_json)
+ # Loading the existing user info in PlaceOS (we need the users id)
+ user = NamedTuple(id: String, email: String, login_name: String?).from_json user_json.to_json
+ email = user[:login_name].presence || user[:email]
+ logger.debug { "found placeos user info: #{user[:email]}, id #{user[:email]}" }
+
+ # Request user details from GraphAPI or Google
+ users_groups = calendar_api.get_groups(email).get
+ logger.debug { "found user groups: #{users_groups.to_pretty_json}" }
+ users_groups = users_groups.as_a
+
+ users_group_ids = users_groups.map { |group| group["id"].as_s }
+ users_group_names = users_groups.map { |group| group["name"].as_s.downcase }
+
+ # Build the list of placeos groups based on the mappings and update the user model
+ groups = [] of String
+ @group_mappings.each { |group_id, place_group| groups << place_group[:place_id] if users_group_ids.includes? group_id }
+ @group_prefixes.each do |group_prefix, place_group|
+ users_group_names.each do |name|
+ if name.starts_with?(group_prefix)
+ if place_name = place_group[:place_id]
+ groups << place_name
+ elsif place_group[:strip_prefix]
+ groups << name.split(group_prefix, 2)[-1]
+ else
+ groups << name
+ end
+ end
+ end
+ end
+ staff_api.update_user(user[:id], {groups: groups}.to_json).get
+
+ logger.debug { "checked #{users_groups.size}, found #{groups.size} matching: #{groups}" }
+ end
+
+ @syncing : Bool = false
+
+ @[PlaceOS::Driver::Security(Level::Support)]
+ def sync_all_users
+ @authority_id.each do |auth_id|
+ sync_users(auth_id)
+ end
+ end
+
+ protected def sync_users(authority_id)
+ return "currently syncing" if @syncing
+ @syncing = true
+
+ limit = 100
+ offset = 0
+
+ issues_with = [] of String
+
+ loop do
+ users = staff_api.query_users(
+ limit: limit,
+ offset: offset,
+ authority_id: authority_id
+ ).get.as_a
+
+ logger.debug { "syncing users #{offset}->#{offset + limit}..." }
+
+ # process 20 users a second
+ users.each do |user|
+ begin
+ sync_user(user)
+ sleep 50.milliseconds
+ rescue error
+ issues_with << user["email"].as_s
+ end
+ end
+
+ break if users.size < limit
+ offset += limit
+ end
+
+ logger.debug { "sync complete! issues with #{issues_with.size}:\n#{issues_with}" }
+ issues_with
+ ensure
+ @syncing = false
+ end
+end
diff --git a/drivers/place/user_group_mappings_spec.cr b/drivers/place/user_group_mappings_spec.cr
new file mode 100644
index 00000000000..92f3c11f53c
--- /dev/null
+++ b/drivers/place/user_group_mappings_spec.cr
@@ -0,0 +1,47 @@
+require "placeos-driver/spec"
+
+# :nodoc:
+class StaffAPIMock < DriverSpecs::MockDriver
+ def user(id : String)
+ {id: "user-1234", email: "steve@placeos.tech", authority_id: "authority-12345"}
+ end
+
+ def update_user(id : String, body_json : String) : Nil
+ self[id] = body_json
+ end
+end
+
+# :nodoc:
+class CalendarMock < DriverSpecs::MockDriver
+ def get_groups(user_id : String)
+ [
+ {
+ id: "5f4694-96f3-4209-a432-b04ac06ca7",
+ name: "Azure-Global-Microsoft Intune Users-Licensed",
+ description: "Azure-Global-Microsoft Intune Users-Licensed",
+ },
+ {
+ id: "bb8836-5942-402d-8d67-55b1a642",
+ name: "All Users",
+ description: "Auto generated group, do not change",
+ },
+ ]
+ end
+end
+
+DriverSpecs.mock_driver "Place::LogicExample" do
+ system({
+ StaffAPI: {StaffAPIMock},
+ Calendar: {CalendarMock},
+ })
+
+ settings({
+ group_mappings: {
+ "5f4694-96f3-4209-a432-b04ac06ca7" => {"place_id" => "intune"},
+ "admins" => {"place_id" => "im an admin"},
+ },
+ })
+
+ exec(:check_user, "user-1234").get
+ system(:StaffAPI_1)["user-1234"].should eq({"groups" => ["intune"]}.to_json)
+end
diff --git a/drivers/place/visitor_mailer.cr b/drivers/place/visitor_mailer.cr
new file mode 100644
index 00000000000..88b216a2aa4
--- /dev/null
+++ b/drivers/place/visitor_mailer.cr
@@ -0,0 +1,654 @@
+require "placeos-driver"
+require "placeos-driver/interface/mailer"
+require "placeos-driver/interface/mailer_templates"
+require "placeos-models/placeos-models/base/jwt"
+
+require "./password_generator_helper"
+require "./visitor_models"
+
+require "uuid"
+require "oauth2"
+require "jwt"
+
+class Place::VisitorMailer < PlaceOS::Driver
+ include PlaceOS::Driver::Interface::MailerTemplates
+
+ descriptive_name "PlaceOS Visitor Mailer"
+ generic_name :VisitorMailer
+ description %(emails visitors when they are invited and notifies hosts when they check in)
+
+ default_settings({
+ timezone: "GMT",
+ date_time_format: "%c",
+ time_format: "%l:%M%p",
+ date_format: "%A, %-d %B",
+ booking_space_name: "Client Floor",
+ determine_host_name_using: "calendar-driver",
+
+ send_reminders: "0 7 * * *",
+ reminder_template: "visitor",
+ event_template: "event",
+ booking_template: "booking",
+ notify_checkin_template: "notify_checkin",
+ notify_induction_accepted_template: "induction_accepted",
+ notify_induction_declined_template: "induction_declined",
+ group_event_template: "group_event",
+ disable_qr_code: false,
+ send_network_credentials: false,
+ network_password_length: DEFAULT_PASSWORD_LENGTH,
+ network_password_exclude: DEFAULT_PASSWORD_EXCLUDE,
+ network_password_minimum_lowercase: DEFAULT_PASSWORD_MINIMUM_LOWERCASE,
+ network_password_minimum_uppercase: DEFAULT_PASSWORD_MINIMUM_UPPERCASE,
+ network_password_minimum_numbers: DEFAULT_PASSWORD_MINIMUM_NUMBERS,
+ network_password_minimum_symbols: DEFAULT_PASSWORD_MINIMUM_SYMBOLS,
+ network_group_ids: [] of String,
+ debug: false,
+ host_domain_filter: [] of String,
+
+ disable_event_visitors: true,
+ invite_zone_tag: "building",
+ is_campus: false,
+
+ domain_uri: "https://example.com/",
+ jwt_private_key: PlaceOS::Model::JWTBase.private_key,
+ })
+
+ accessor staff_api : StaffAPI_1
+ accessor calendar : Calendar_1
+ accessor network_provider : NetworkAccess_1 # Written for Cisco ISE Driver, but ideally compatible with others
+
+ def mailer
+ system.implementing(Interface::Mailer)[0]
+ end
+
+ def on_load
+ # Guest has been marked as attending a meeting in person
+ monitor("staff/guest/attending") { |_subscription, payload| guest_event(payload.gsub(/[^[:print:]]/, "")) }
+
+ # Guest has arrived in the lobby
+ monitor("staff/guest/checkin") { |_subscription, payload| guest_event(payload.gsub(/[^[:print:]]/, "")) }
+
+ # Booking induction status has been updated
+ monitor("staff/guest/induction_accepted") { |_subscription, payload| guest_event(payload.gsub(/[^[:print:]]/, "")) }
+ monitor("staff/guest/induction_declined") { |_subscription, payload| guest_event(payload.gsub(/[^[:print:]]/, "")) }
+
+ on_update
+ end
+
+ @time_zone : Time::Location = Time::Location.load("GMT")
+
+ @debug : Bool = false
+ @is_parent_zone : Bool = false
+ @users_checked_in : UInt64 = 0_u64
+ @users_accepted_induction : UInt64 = 0_u64
+ @users_declined_induction : UInt64 = 0_u64
+ @error_count : UInt64 = 0_u64
+
+ @visitor_emails_sent : UInt64 = 0_u64
+ @visitor_email_errors : UInt64 = 0_u64
+ @disable_qr_code : Bool = false
+ @host_domain_filter : Array(String) = [] of String
+
+ # See: https://crystal-lang.org/api/0.35.1/Time/Format.html
+ @date_time_format : String = "%c"
+ @time_format : String = "%l:%M%p"
+ @date_format : String = "%A, %-d %B"
+
+ getter building_zone : ZoneDetails do
+ find_building(control_system_zone_list)
+ end
+
+ getter parent_zone_ids : Array(String) = [] of String
+ @booking_space_name : String = "Client Floor"
+ @invite_zone_tag : String = "building"
+
+ @reminder_template : String = "visitor"
+ @send_reminders : String? = nil
+ @event_template : String = "event"
+ @booking_template : String = "booking"
+ @notify_checkin_template : String = "notify_checkin"
+ @notify_induction_accepted_template : String = "induction_accepted"
+ @notify_induction_declined_template : String = "induction_declined"
+ @group_event_template : String = "group_event"
+ @determine_host_name_using : String = "calendar-driver"
+ @send_network_credentials = false
+ @network_password_length : Int32 = DEFAULT_PASSWORD_LENGTH
+ @network_password_exclude : String = DEFAULT_PASSWORD_EXCLUDE
+ @network_password_minimum_lowercase : Int32 = DEFAULT_PASSWORD_MINIMUM_LOWERCASE
+ @network_password_minimum_uppercase : Int32 = DEFAULT_PASSWORD_MINIMUM_UPPERCASE
+ @network_password_minimum_numbers : Int32 = DEFAULT_PASSWORD_MINIMUM_NUMBERS
+ @network_password_minimum_symbols : Int32 = DEFAULT_PASSWORD_MINIMUM_SYMBOLS
+ @network_group_ids = [] of String
+ @disable_event_visitors : Bool = true
+
+ @uri : URI = URI.new
+ @jwt_private_key : String = PlaceOS::Model::JWTBase.private_key
+
+ def on_update
+ @debug = setting?(Bool, :debug) || true
+ @date_time_format = setting?(String, :date_time_format) || "%c"
+ @time_format = setting?(String, :time_format) || "%l:%M%p"
+ @date_format = setting?(String, :date_format) || "%A, %-d %B"
+ @send_reminders = setting?(String, :send_reminders).presence
+ @reminder_template = setting?(String, :reminder_template) || "visitor"
+ @event_template = setting?(String, :event_template) || "event"
+ @booking_template = setting?(String, :booking_template) || "booking"
+ @notify_checkin_template = setting?(String, :notify_checkin_template) || "notify_checkin"
+ @notify_induction_accepted_template = setting?(String, :induction_accepted) || "induction_accepted"
+ @notify_induction_declined_template = setting?(String, :induction_declined) || "induction_declined"
+ @group_event_template = setting?(String, :group_event_template) || "group_event"
+ @disable_qr_code = setting?(Bool, :disable_qr_code) || false
+ @determine_host_name_using = setting?(String, :determine_host_name_using) || "calendar-driver"
+ @send_network_credentials = setting?(Bool, :send_network_credentials) || false
+ @network_password_length = setting?(Int32, :password_length) || DEFAULT_PASSWORD_LENGTH
+ @network_password_exclude = setting?(String, :password_exclude) || DEFAULT_PASSWORD_EXCLUDE
+ @network_password_minimum_lowercase = setting?(Int32, :password_minimum_lowercase) || DEFAULT_PASSWORD_MINIMUM_LOWERCASE
+ @network_password_minimum_uppercase = setting?(Int32, :password_minimum_uppercase) || DEFAULT_PASSWORD_MINIMUM_UPPERCASE
+ @network_password_minimum_numbers = setting?(Int32, :password_minimum_numbers) || DEFAULT_PASSWORD_MINIMUM_NUMBERS
+ @network_password_minimum_symbols = setting?(Int32, :password_minimum_symbols) || DEFAULT_PASSWORD_MINIMUM_SYMBOLS
+ @network_group_ids = setting?(Array(String), :network_group_ids) || [] of String
+ @host_domain_filter = setting?(Array(String), :host_domain_filter) || [] of String
+ @disable_event_visitors = setting?(Bool, :disable_event_visitors) || false
+ @invite_zone_tag = setting?(String, :invite_zone_tag) || "building"
+ @is_parent_zone = setting?(Bool, :is_campus) || false
+
+ time_zone = setting?(String, :timezone).presence || "GMT"
+ @time_zone = Time::Location.load(time_zone)
+
+ @booking_space_name = setting?(String, :booking_space_name).presence || "Client Floor"
+
+
+ @uri = URI.parse(setting?(String, :domain_uri) || "")
+ @jwt_private_key = setting?(String, :jwt_private_key) || PlaceOS::Model::JWTBase.private_key
+
+ zones = config.control_system.not_nil!.zones
+ schedule.clear
+ if reminders = @send_reminders
+ schedule.cron(reminders, @time_zone) { send_reminder_emails }
+ end
+ spawn { ensure_building_zone(zones) }
+ end
+
+ def control_system_zone_list
+ config.control_system.not_nil!.zones
+ end
+
+ protected def ensure_building_zone(zones) : Nil
+ find_building(zones)
+ rescue error
+ logger.warn(exception: error) { "error looking up building zone" }
+ schedule.in(5.seconds) { ensure_building_zone(zones) }
+ end
+
+ protected def find_building(zones : Array(String)) : ZoneDetails
+ zones.each do |zone_id|
+ zone = ZoneDetails.from_json staff_api.zone(zone_id).get.to_json
+ if zone.tags.includes?(@invite_zone_tag)
+ @building_zone = zone
+ if @is_parent_zone && (child_zones = Array(ZoneDetails).from_json(staff_api.zones(parent: zone_id).get.to_json))
+ @parent_zone_ids = child_zones.map(&.id)
+ else
+ @parent_zone_ids = [] of String
+ end
+ break
+ end
+ end
+ raise "no building zone found in System" unless @building_zone
+ @building_zone.as(ZoneDetails)
+ end
+
+ protected def guest_event(payload)
+ logger.debug { "received guest event payload: #{payload}" }
+ guest_details = GuestNotification.from_json payload
+
+ # ensure the event is for this building
+ if zones = guest_details.zones
+ check = [building_zone.id] + @parent_zone_ids
+
+ if (check & zones).empty?
+ logger.debug { "ignoring event as does not match any zones: #{check}" }
+ return
+ end
+ end
+
+ # don't email staff members
+ if !@host_domain_filter.empty? && guest_details.attendee_email.split('@', 2)[1].downcase.in?(@host_domain_filter)
+ logger.debug { "ignoring event matches host domain filter" }
+ return
+ end
+
+ case guest_details
+ in GuestCheckin
+ send_checkedin_email(
+ @notify_checkin_template,
+ guest_details.attendee_email,
+ guest_details.attendee_name,
+ guest_details.host,
+ guest_details.event_title || guest_details.event_summary,
+ guest_details.event_starting
+ )
+ self[:users_checked_in] = @users_checked_in += 1
+ return
+ in BookingInduction
+ if guest_details.induction.accepted?
+ send_induction_email(
+ @notify_induction_accepted_template,
+ guest_details.attendee_email,
+ guest_details.attendee_name,
+ guest_details.host,
+ guest_details.event_title || guest_details.event_summary,
+ guest_details.event_starting,
+ guest_details.induction
+ )
+ self[:users_accepted_induction] = @users_accepted_induction += 1
+ elsif guest_details.induction.declined?
+ send_induction_email(
+ @notify_induction_declined_template,
+ guest_details.attendee_email,
+ guest_details.attendee_name,
+ guest_details.host,
+ guest_details.event_title || guest_details.event_summary,
+ guest_details.event_starting,
+ guest_details.induction
+ )
+ self[:users_declined_induction] = @users_declined_induction += 1
+ end
+
+ return
+ in EventGuest
+ return if @disable_event_visitors
+
+ room = get_room_details(guest_details.system_id)
+ area_name = room.display_name.presence || room.name
+ template = @event_template
+ in BookingGuest
+ area_name = @booking_space_name
+ template = @booking_template
+ booking_type = staff_api.get_booking(guest_details.booking_id).get["booking_type"].as_s
+ template = @group_event_template if booking_type == "group-event"
+ in GuestNotification
+ # should never get here
+ return
+ end
+
+ send_visitor_qr_email(
+ template,
+ guest_details.attendee_email,
+ guest_details.attendee_name,
+ guest_details.host,
+ guest_details.event_title || guest_details.event_summary,
+ guest_details.event_starting,
+ guest_details.resource_id,
+ guest_details.event_id,
+ area_name,
+ system_id: guest_details.responds_to?(:system_id) ? guest_details.system_id : nil,
+ )
+ rescue error
+ logger.error { error.inspect_with_backtrace }
+ self[:error_count] = @error_count += 1
+ self[:last_error] = {
+ error: error.message,
+ time: Time.local.to_s,
+ user: payload,
+ }
+ end
+
+ @[Security(Level::Support)]
+ def send_checkedin_email(
+ template : String,
+ visitor_email : String,
+ visitor_name : String?,
+ host_email : String?,
+ event_title : String?,
+ event_start : Int64
+ )
+ local_start_time = Time.unix(event_start).in(@time_zone)
+
+ mailer.send_template(
+ host_email,
+ {"visitor_invited", template}, # Template selection: "visitor_invited" "notify_checkin"
+ {
+ visitor_email: visitor_email,
+ visitor_name: visitor_name,
+ host_name: get_host_name(host_email),
+ host_email: host_email,
+ building_name: building_zone.display_name.presence || building_zone.name,
+ event_title: event_title,
+ event_start: local_start_time.to_s(@time_format),
+ event_date: local_start_time.to_s(@date_format),
+ event_time: local_start_time.to_s(@time_format),
+ }
+ )
+ end
+
+ @[Security(Level::Support)]
+ def send_induction_email(
+ template : String,
+ visitor_email : String,
+ visitor_name : String?,
+ host_email : String?,
+ event_title : String?,
+ event_start : Int64,
+ induction_status : Induction
+ )
+ local_start_time = Time.unix(event_start).in(@time_zone)
+
+ mailer.send_template(
+ host_email,
+ {"visitor_invited", template}, # Template selection: "visitor_invited" "induction_accepted"
+ {
+ visitor_email: visitor_email,
+ visitor_name: visitor_name,
+ host_name: get_host_name(host_email),
+ host_email: host_email,
+ building_name: building_zone.display_name.presence || building_zone.name,
+ event_title: event_title,
+ event_start: local_start_time.to_s(@time_format),
+ event_date: local_start_time.to_s(@date_format),
+ event_time: local_start_time.to_s(@time_format),
+ induction_status: induction_status.to_s,
+ }
+ )
+ end
+
+ def template_fields : Array(TemplateFields)
+ time_now = Time.utc.in(@time_zone)
+ common_fields = [
+ {name: "visitor_email", description: "Email address of the visiting guest"},
+ {name: "visitor_name", description: "Full name of the visiting guest"},
+ {name: "host_name", description: "Name of the person hosting the visitor"},
+ {name: "host_email", description: "Email address of the host"},
+ {name: "building_name", description: "Name of the building where the visit occurs"},
+ {name: "event_title", description: "Title or purpose of the visit"},
+ {name: "event_start", description: "Start time (e.g., #{time_now.to_s(@time_format)})"},
+ {name: "event_date", description: "Date of the visit (e.g., #{time_now.to_s(@date_format)})"},
+ {name: "event_time", description: "Time of the visit (or 'all day' for 24-hour events)"},
+ ]
+
+ invitation_fields = common_fields + [
+ {name: "room_name", description: "Name of the room or area being visited"},
+ {name: "network_username", description: "Network access username (if network credentials enabled)"},
+ {name: "network_password", description: "Generated network access password (if network credentials enabled)"},
+ ]
+
+ induction_fields = common_fields + [
+ {name: "induction_status", description: "Status of the induction (e.g., accepted or declined)"},
+ ]
+
+ jwt_fields = [
+ {name: "guest_jwt", description: "JWT token for the guest"},
+ {name: "kiosk_url", description: "URL for the visitor kiosk"},
+ ]
+
+ [
+ TemplateFields.new(
+ trigger: {"visitor_invited", @reminder_template},
+ name: "Visitor invited",
+ description: "Reminder email for upcoming visitor appointments",
+ fields: invitation_fields
+ ),
+ TemplateFields.new(
+ trigger: {"visitor_invited", @event_template},
+ name: "Visitor invited to event",
+ description: "Initial invitation for a visitor attending a calendar event",
+ fields: invitation_fields + jwt_fields
+ ),
+ TemplateFields.new(
+ trigger: {"visitor_invited", @booking_template},
+ name: "Visitor invited to booking",
+ description: "Initial invitation for a visitor with a space booking",
+ fields: invitation_fields + jwt_fields
+ ),
+ TemplateFields.new(
+ trigger: {"visitor_invited", @group_event_template},
+ name: "Visitor invited to group event booking",
+ description: "Initial invitation for a visitor attending a group event",
+ fields: invitation_fields
+ ),
+ TemplateFields.new(
+ trigger: {"visitor_invited", @notify_checkin_template},
+ name: "Visitor check in notification",
+ description: "Notification to host when their visitor checks in",
+ fields: common_fields
+ ),
+ TemplateFields.new(
+ trigger: {"visitor_invited", @notify_induction_accepted_template},
+ name: "Visitor induction accepted notification",
+ description: "Notification to host when their visitor accepts the induction",
+ fields: induction_fields
+ ),
+ TemplateFields.new(
+ trigger: {"visitor_invited", @notify_induction_declined_template},
+ name: "Visitor induction declined notification",
+ description: "Notification to host when their visitor declines the induction",
+ fields: induction_fields
+ ),
+ ]
+ end
+
+ @[Security(Level::Support)]
+ def send_visitor_qr_email(
+ template : String,
+ visitor_email : String,
+ visitor_name : String?,
+ host_email : String?,
+ event_title : String?,
+ event_start : Int64,
+
+ resource_id : String,
+ event_id : String,
+ area_name : String,
+
+ event_end : Int64? = nil,
+ system_id : String? = nil,
+ )
+ local_start_time = Time.unix(event_start).in(@time_zone)
+
+ attach = if @disable_qr_code
+ [] of NamedTuple(file_name: String, content: String, content_id: String)
+ else
+ qr_png = mailer.generate_png_qrcode(text: "VISIT:#{visitor_email},#{resource_id},#{event_id},#{host_email}", size: 256).get.as_s
+ [
+ {
+ file_name: "qr.png",
+ content: qr_png,
+ content_id: visitor_email,
+ },
+ ]
+ end
+
+ network_username = network_password = ""
+ network_username, network_password = update_network_user_password(
+ visitor_email,
+ generate_password(
+ length: @network_password_length,
+ exclude: @network_password_exclude,
+ minimum_lowercase: @network_password_minimum_lowercase,
+ minimum_uppercase: @network_password_minimum_uppercase,
+ minimum_numbers: @network_password_minimum_numbers,
+ minimum_symbols: @network_password_minimum_symbols
+ ),
+ @network_group_ids
+ ) if @send_network_credentials
+
+ event_time = if (end_timestamp = event_end) && (Time.unix(end_timestamp) - Time.unix(event_start)) == 24.hours
+ "all day"
+ else
+ local_start_time.to_s(@time_format)
+ end
+
+ guest_jwt = generate_guest_jwt(visitor_name || visitor_email, visitor_email, visitor_email, event_id, system_id || resource_id)
+ kiosk_url = "/visitor-kiosk/#/checkin/preferences?email=#{visitor_email}&jwt=#{guest_jwt}&event_id=#{event_id}"
+
+ mailer.send_template(
+ visitor_email,
+ {"visitor_invited", template}, # Template selection: "visitor_invited" action, "visitor" email
+ {
+ visitor_email: visitor_email,
+ visitor_name: visitor_name,
+ host_name: get_host_name(host_email),
+ host_email: host_email,
+ room_name: area_name,
+ building_name: building_zone.display_name.presence || building_zone.name,
+ event_title: event_title,
+ event_start: local_start_time.to_s(@time_format),
+ event_date: local_start_time.to_s(@date_format),
+ event_time: event_time,
+ network_username: network_username,
+ network_password: network_password,
+ guest_jwt: guest_jwt,
+ kiosk_url: kiosk_url,
+ },
+ attach
+ )
+ end
+
+ @[Security(Level::Support)]
+ def send_reminder_emails
+ now = 1.hour.ago.to_unix
+ later = 12.hours.from_now.to_unix
+
+ guests = staff_api.query_guests(
+ period_start: now,
+ period_end: later,
+ zones: {building_zone.id}
+ ).get.as_a
+
+ guests.uniq! { |g| g["email"].as_s.downcase }
+ guests.each do |guest|
+ begin
+ if event = guest["event"]?
+ send_visitor_qr_email(
+ @reminder_template,
+ guest["email"].as_s,
+ guest["name"].as_s?,
+ event["host"].as_s,
+ event["title"].as_s,
+ event["event_start"].as_i64,
+ event.dig("system", "id").as_s,
+ event["id"].as_s,
+ (event.dig?("system", "display_name") || event.dig("system", "name")).as_s,
+ event_end: event["event_end"].as_i64
+ )
+ elsif booking = guest["booking"]?
+ send_visitor_qr_email(
+ @reminder_template,
+ guest["email"].as_s,
+ guest["name"].as_s?,
+ booking["user_email"].as_s,
+ booking["title"].as_s?,
+ booking["booking_start"].as_i64,
+ booking["asset_id"].as_s,
+ booking["id"].as_i64.to_s,
+ @booking_space_name,
+ event_end: booking["booking_end"].as_i64
+ )
+ end
+ rescue error
+ logger.warn(exception: error) { "failed to send reminder email to #{guest["email"]}" }
+ end
+ end
+ end
+
+ # ===================================
+ # Guest JWT Generation:
+ # ===================================
+
+ @[Security(Level::Administrator)]
+ def generate_guest_jwt(name : String, email : String, guest_id : String, event_id : String, system_id : String)
+ now = Time.local(@time_zone)
+ tonight = now.at_end_of_day
+ tomorrow_night = tonight + 24.hours
+
+ payload = {
+ iss: "POS",
+ iat: now.to_unix,
+ exp: tomorrow_night.to_unix,
+ jti: UUID.random.to_s,
+ aud: @uri.try &.host,
+ scope: ["guest"],
+ sub: guest_id,
+ u: {
+ n: name,
+ e: email,
+ p: 0,
+ r: [event_id, system_id],
+ },
+ }
+
+ JWT.encode(payload, @jwt_private_key, JWT::Algorithm::RS256)
+ end
+
+ # ===================================
+ # PlaceOS API requests
+ # ===================================
+
+ class ZoneDetails
+ include JSON::Serializable
+
+ property id : String
+ property name : String
+ property display_name : String?
+ property location : String?
+ property tags : Array(String)
+ property parent_id : String?
+ end
+
+ class SystemDetails
+ include JSON::Serializable
+
+ property id : String
+ property name : String
+ property display_name : String?
+ property map_id : String?
+ end
+
+ protected def get_room_details(system_id : String, retries = 0)
+ SystemDetails.from_json staff_api.get_system(system_id).get.to_json
+ rescue error
+ raise "issue loading system details #{system_id}" if retries > 3
+ sleep 1.second
+ get_room_details(system_id, retries + 1)
+ end
+
+ protected def get_host_name(host_email)
+ @determine_host_name_using == "staff-api-driver" ? get_host_name_from_staff_api_driver(host_email) : get_host_name_from_calendar_driver(host_email)
+ end
+
+ protected def get_host_name_from_calendar_driver(host_email)
+ calendar.get_user(host_email).get["name"]
+ rescue error
+ logger.error { "issue loading host details #{host_email}" }
+ return "your host"
+ end
+
+ protected def get_host_name_from_staff_api_driver(host_email, retries = 0)
+ staff_api.staff_details(host_email).get["name"].as_s.split('(')[0]
+ rescue error
+ if retries > 3
+ logger.error { "issue loading host details #{host_email}" }
+ return "your host"
+ end
+ sleep 1.second
+ get_host_name_from_staff_api_driver(host_email, retries + 1)
+ end
+
+ # For Cisco ISE network credentials
+
+ def update_network_user_password(user_email : String, password : String, network_group_ids : Array(String) = [] of String)
+ # Check if they already exist
+ response = network_provider.update_internal_user_password_by_name(user_email, password).get
+ logger.debug { "Response from Network Identity provider for lookup of #{user_email} was:\n#{response}" } if @debug
+ rescue # todo: catch the specific error where the user already exists, instead of any error. Catch other errors in seperate rescue
+ # Create them if they don't already exist
+ create_network_user(user_email, password, network_group_ids)
+ else
+ {user_email, password}
+ end
+
+ def create_network_user(user_email : String, password : String, group_ids : Array(String) = [] of String)
+ response = network_provider.create_internal_user(email: user_email, name: user_email, password: password, identity_groups: group_ids).get
+ logger.debug { "Response from Network Identity provider for creating user #{user_email} was:\n #{response}\n\nDetails:\n#{response.inspect}" } if @debug
+ {response["name"], password}
+ end
+end
diff --git a/drivers/place/visitor_mailer_spec.cr b/drivers/place/visitor_mailer_spec.cr
new file mode 100644
index 00000000000..1dbd48e16f4
--- /dev/null
+++ b/drivers/place/visitor_mailer_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Place::VisitorMailer" do
+end
diff --git a/drivers/place/visitor_models.cr b/drivers/place/visitor_models.cr
new file mode 100644
index 00000000000..1bcd5341e9c
--- /dev/null
+++ b/drivers/place/visitor_models.cr
@@ -0,0 +1,83 @@
+require "json"
+
+module Place
+ enum Induction
+ TENTATIVE
+ ACCEPTED
+ DECLINED
+ end
+
+ abstract class GuestNotification
+ include JSON::Serializable
+
+ use_json_discriminator "action", {
+ "booking_created" => BookingGuest,
+ "booking_updated" => BookingGuest,
+ "meeting_created" => EventGuest,
+ "meeting_update" => EventGuest,
+ "checkin" => GuestCheckin,
+ "induction_accepted" => BookingInduction,
+ "induction_declined" => BookingInduction,
+ }
+
+ property action : String
+
+ property checkin : Bool?
+ property event_title : String?
+ property event_summary : String
+ property event_starting : Int64
+ property attendee_name : String?
+ property attendee_email : String
+ property host : String
+
+ # This is optional for backwards compatibility
+ property zones : Array(String)?
+
+ property ext_data : Hash(String, JSON::Any)?
+ end
+
+ class EventGuest < GuestNotification
+ include JSON::Serializable
+
+ property system_id : String
+ property event_id : String
+ property resource : String
+
+ def resource_id
+ system_id
+ end
+ end
+
+ class BookingGuest < GuestNotification
+ include JSON::Serializable
+
+ property booking_id : Int64
+ property resource_id : String
+
+ def event_id
+ booking_id.to_s
+ end
+ end
+
+ class GuestCheckin < GuestNotification
+ include JSON::Serializable
+
+ property system_id : String = ""
+ property event_id : String = ""
+ property resource : String = ""
+ property resource_id : String = ""
+ end
+
+ class BookingInduction < GuestNotification
+ include JSON::Serializable
+
+ property induction : Induction = Induction::TENTATIVE
+ property booking_id : Int64
+ property resource_id : String
+ property resource_ids : Array(String)
+
+ def event_id
+ booking_id.to_s
+ end
+ end
+end
diff --git a/drivers/planar/clarity_matrix.cr b/drivers/planar/clarity_matrix.cr
new file mode 100644
index 00000000000..bd8e7039d2e
--- /dev/null
+++ b/drivers/planar/clarity_matrix.cr
@@ -0,0 +1,94 @@
+require "placeos-driver"
+require "placeos-driver/interface/powerable"
+
+# Documentation: https://aca.im/driver_docs/Planar/020-1028-00%20RS232%20for%20Matrix.pdf
+# also https://aca.im/driver_docs/Planar/020-0567-05_WallNet_guide.pdf
+
+class Planar::ClarityMatrix < PlaceOS::Driver
+ include Interface::Powerable
+
+ # Discovery Information
+ descriptive_name "Planar Clarity Matrix Video Wall"
+ generic_name :VideoWall
+
+ # Global Cache Port
+ tcp_port 4999
+
+ def on_load
+ # Communication settings
+ queue.wait = false
+ transport.tokenizer = Tokenizer.new("\r")
+ end
+
+ def connected
+ do_poll
+ schedule.every(60.seconds) { do_poll }
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ @power : Bool = false
+
+ def power(state : Bool)
+ power?.get
+ if state && @power == false
+ send("op ** display.power = on \r", name: "power", delay: 3.seconds)
+ result = power?
+ schedule.in(20.seconds) { recall(0) }
+ result
+ elsif !state && @power == true
+ send("op ** display.power = off \r", name: "power", delay: 3.seconds)
+ power?
+ end
+ end
+
+ def power?
+ send("op A1 display.power ? \r", wait: true, priority: 0)
+ end
+
+ def recall(preset : UInt32, **options)
+ send("op ** slot.recall (#{preset}) \r", **options, name: "recall")
+ end
+
+ def input_status?(**options)
+ send("op A1 slot.current ? \r", wait: true)
+ end
+
+ def do_poll
+ power?
+ input_status?(priority: 0) if @power
+ end
+
+ def build_date?
+ send("ST A1 BUILD.DATE ? \r", wait: true)
+ end
+
+ def received(data, task)
+ data = String.new(data)
+ logger.debug { "sent: #{data}" }
+
+ data = data.split('.') # OPA1DISPLAY.POWER=ON || OPA1SLOT.CURRENT=0
+ component = data[0] # OPA1DISPLAY || OPA1SLOT
+ data = data[1].split('=')
+
+ status = data[0].downcase.strip # POWER || CURRENT
+ value = data[1].strip # ON || 0
+
+ case status
+ when "power"
+ self[:power] = @power = value == "ON"
+ task.try &.success(@power)
+ when "current"
+ input = value.to_i
+ self[:input] = input
+ task.try &.success(input)
+ when "date"
+ # remove the inverted commas
+ task.try &.success(value[1..-2])
+ else
+ task.try &.success
+ end
+ end
+end
diff --git a/drivers/planar/clarity_matrix_spec.cr b/drivers/planar/clarity_matrix_spec.cr
new file mode 100644
index 00000000000..8703a16b324
--- /dev/null
+++ b/drivers/planar/clarity_matrix_spec.cr
@@ -0,0 +1,21 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Planar::ClarityMatrix" do
+ # On connect it queries the state of the device
+ should_send("op A1 display.power ? \r")
+ responds("OPA1DISPLAY.POWER=OFF\r")
+
+ resp = exec(:build_date?)
+ should_send("ST A1 BUILD.DATE ? \r")
+ responds(%(ST A1 BUILD.DATE= "JUN 15 2009 08:48:24"\r))
+ resp.get.should eq "JUN 15 2009 08:48:24"
+
+ resp = exec(:power, true)
+ should_send("op A1 display.power ? \r")
+ responds("OPA1DISPLAY.POWER=OFF\r")
+ should_send("op ** display.power = on \r")
+ sleep 3
+ should_send("op A1 display.power ? \r")
+ responds("OPA1DISPLAY.POWER=ON\r")
+ resp.get.should eq true
+end
diff --git a/drivers/point_grab/cogni_point.cr b/drivers/point_grab/cogni_point.cr
new file mode 100644
index 00000000000..742dea01415
--- /dev/null
+++ b/drivers/point_grab/cogni_point.cr
@@ -0,0 +1,380 @@
+require "uri"
+require "uuid"
+require "placeos-driver"
+
+# Documentation: https://aca.im/driver_docs/PointGrab/CogniPointAPI2-1.pdf
+
+class PointGrab::CogniPoint < PlaceOS::Driver
+ # Discovery Information
+ generic_name :CogniPoint
+ descriptive_name "PointGrab CogniPoint REST API"
+
+ default_settings({
+ user_id: "10000000",
+ app_key: "c5a6adc6-UUID-46e8-b72d-91395bce9565",
+ })
+
+ @user_id : String = ""
+ @app_key : String = ""
+ @auth_token : String = ""
+ @auth_expiry : Time = 1.minute.ago
+
+ def on_update
+ @user_id = setting(String, :user_id)
+ @app_key = setting(String, :app_key)
+ end
+
+ class TokenResponse
+ include JSON::Serializable
+
+ property token : String
+ property expires_in : Int32
+ end
+
+ def expire_token!
+ @auth_expiry = 1.minute.ago
+ end
+
+ def token_expired?
+ @auth_expiry < Time.utc
+ end
+
+ def get_token
+ return @auth_token unless token_expired?
+
+ response = post("/be/cp/oauth2/token", body: "grant_type=client_credentials", headers: {
+ "Content-Type" => "application/x-www-form-urlencoded",
+ "Accept" => "application/json",
+ "Authorization" => "Basic #{Base64.strict_encode("#{@user_id}:#{@app_key}")}",
+ })
+
+ body = response.body
+ logger.debug { "received login response: #{body}" }
+
+ if response.success?
+ resp = TokenResponse.from_json(body.not_nil!)
+ token = resp.token
+ @auth_expiry = Time.utc + (resp.expires_in - 5).seconds
+ @auth_token = "Bearer #{resp.token}"
+ else
+ logger.error { "authentication failed with HTTP #{response.status_code}" }
+ raise "failed to obtain access token"
+ end
+ end
+
+ macro get_request(path, result_type)
+ begin
+ %token = get_token
+ %response = get({{path}}, headers: {
+ "Accept" => "application/json",
+ "Authorization" => %token
+ })
+
+ if %response.success?
+ {{result_type}}.from_json(%response.body.not_nil!)
+ else
+ expire_token! if %response.status_code == 401
+ raise "unexpected response #{%response.status_code}\n#{%response.body}"
+ end
+ end
+ end
+
+ class Customer
+ include JSON::Serializable
+
+ property id : String
+ property name : String
+ end
+
+ def customers
+ customers = get_request("/be/cp/v2/customers", NamedTuple(endCustomers: Array(Customer)))
+ customers[:endCustomers]
+ end
+
+ class GeoPosition
+ include JSON::Serializable
+
+ property latitude : Float64
+ property longitude : Float64
+ end
+
+ class MetricPositions
+ include JSON::Serializable
+
+ @[JSON::Field(key: "posX")]
+ property pos_x : Float64
+
+ @[JSON::Field(key: "posY")]
+ property pos_y : Float64
+ end
+
+ class Site
+ include JSON::Serializable
+
+ property id : String
+ property name : String
+
+ class Location
+ include JSON::Serializable
+
+ @[JSON::Field(key: "houseNo")]
+ property house_number : String
+ property street : String
+ property city : String
+ property county : String
+ property state : String
+ property country : String
+ property zip : String
+
+ @[JSON::Field(key: "geoPosition")]
+ property geo_position : GeoPosition
+ end
+
+ @[JSON::Field(key: "customerId")]
+ property customer_id : String
+ property location : Location
+ end
+
+ def sites
+ sites = get_request("/be/cp/v2/sites", NamedTuple(sites: Array(Site)))
+ sites[:sites]
+ end
+
+ def site(site_id : String)
+ get_request("/be/cp/v2/sites/#{site_id}", Site)
+ end
+
+ class Building
+ include JSON::Serializable
+
+ property id : String
+ property name : String
+
+ @[JSON::Field(key: "siteId")]
+ property site_id : String
+
+ property location : Site::Location
+ end
+
+ def buildings(site_id : String)
+ buildings = get_request("/be/cp/v2/sites/#{site_id}/buildings", NamedTuple(buildings: Array(Building)))
+ buildings[:buildings]
+ end
+
+ def building(site_id : String, building_id : String)
+ get_request("/be/cp/v2/sites/#{site_id}/buildings/#{building_id}", Building)
+ end
+
+ class Floor
+ include JSON::Serializable
+
+ property id : String
+ property name : String
+
+ @[JSON::Field(key: "floorNumber")]
+ property floor_number : String
+
+ @[JSON::Field(key: "floorPlanURL")]
+ property floor_plan_url : String
+
+ @[JSON::Field(key: "widthDistance")]
+ property width_distance : Float64
+
+ @[JSON::Field(key: "lengthDistance")]
+ property length_distance : Float64
+
+ # NOTE:: unknown format for referencePoints => Array(?)
+ end
+
+ def floors(site_id : String, building_id : String)
+ floors = get_request("/be/cp/v2/sites/#{site_id}/buildings/#{building_id}/floors", NamedTuple(floors: Array(Building)))
+ floors[:floors]
+ end
+
+ def floor(site_id : String, building_id : String, floor_id : String)
+ get_request("/be/cp/v2/sites/#{site_id}/buildings/#{building_id}/floors/#{floor_id}", Floor)
+ end
+
+ class Area
+ include JSON::Serializable
+
+ property id : String
+ property name : String
+ property length : Float64
+ property width : Float64
+
+ @[JSON::Field(key: "centerX")]
+ property center_x : Float64
+
+ @[JSON::Field(key: "centerY")]
+ property center_y : Float64
+
+ property rotation : Int32
+ property frequency : Int32
+
+ @[JSON::Field(key: "deviceIDs")]
+ property device_ids : Array(String)
+
+ class Application
+ include JSON::Serializable
+
+ @[JSON::Field(key: "areaType")]
+ property area_type : String
+
+ @[JSON::Field(key: "applicationType")]
+ property application_type : String
+ end
+
+ property applications : Array(Application)
+
+ # Area Polygon positions in meters
+ @[JSON::Field(key: "metricPositions")]
+ property metric_positions : Array(MetricPositions)
+
+ # Area Polygon Coordinates positions
+ @[JSON::Field(key: "geoPositions")]
+ property geo_positions : Array(GeoPosition)?
+ end
+
+ class FloorAreas
+ include JSON::Serializable
+
+ @[JSON::Field(key: "floorId")]
+ property floor_id : String
+ property areas : Array(Area)
+ end
+
+ def building_areas(site_id : String, building_id : String)
+ floors = get_request("/be/cp/v2/sites/#{site_id}/buildings/#{building_id}/areas", NamedTuple(
+ floorsAreas: FloorAreas))
+ floors[:floorsAreas]
+ end
+
+ def areas(site_id : String, building_id : String, floor_id : String)
+ areas = get_request("/be/cp/v2/sites/#{site_id}/buildings/#{building_id}/floors/#{floor_id}/areas", NamedTuple(
+ areas: Array(Area)))
+ areas[:areas]
+ end
+
+ def area(site_id : String, building_id : String, floor_id : String, area_id : String)
+ get_request("/be/cp/v2/sites/#{site_id}/buildings/#{building_id}/floors/#{floor_id}/areas/#{area_id}", Area)
+ end
+
+ class Handler
+ include JSON::Serializable
+
+ property id : String
+ property token : String
+
+ @[JSON::Field(key: "thirdPartyAppID")]
+ property app_id : UInt32
+
+ @[JSON::Field(key: "endPoint")]
+ property end_point : String
+ end
+
+ def handlers
+ handlers = get_request("/be/cp/v2/resources/handlers", NamedTuple(
+ handlers: Array(Handler)))
+ handlers[:handlers]
+ end
+
+ class Subscription
+ include JSON::Serializable
+
+ property id : String
+ property token : String
+ property started : Bool
+ property endpoint : String
+ property uri : String
+
+ @[JSON::Field(key: "notificationType")]
+ property notification_type : String
+
+ @[JSON::Field(key: "subscriptionType")]
+ property subscription_type : String
+ end
+
+ enum NotificationType
+ Counting
+ Traffic
+ end
+
+ def subscribe(handler_uri : String, auth_token : String = UUID.random.to_s, events : NotificationType = NotificationType::Counting)
+ # Ensure the handler is a valid URI
+ URI.parse handler_uri
+
+ token = get_token
+ response = post(
+ "/be/cp/v2/telemetry/subscriptions",
+ body: {
+ subscriptionType: "PUSH",
+ notificationType: events.to_s.upcase,
+ endpoint: handler_uri,
+ token: auth_token,
+ }.to_json,
+ headers: {
+ "Content-Type" => "application/json",
+ "Accept" => "application/json",
+ "Authorization" => token,
+ }
+ )
+
+ body = response.body
+ logger.debug { "received login response: #{body}" }
+
+ if response.success?
+ Subscription.from_json(body.not_nil!)
+ else
+ logger.error { "authentication failed with HTTP #{response.status_code}" }
+ raise "failed to obtain access token"
+ end
+ end
+
+ def subscriptions
+ get_request("/be/cp/v2/telemetry/subscriptions", Array(Subscription))
+ end
+
+ def delete_subscription(id : String)
+ token = get_token
+ delete("/be/cp/v2/telemetry/subscriptions/#{id}",
+ headers: {
+ "Accept" => "application/json",
+ "Authorization" => token,
+ }
+ ).success?
+ end
+
+ def update_subscription(id : String, started : Bool = true)
+ token = get_token
+ patch(
+ "/be/cp/v2/telemetry/subscriptions/#{id}",
+ body: {started: started}.to_json,
+ headers: {
+ "Content-Type" => "application/json",
+ "Accept" => "application/json",
+ "Authorization" => token,
+ }
+ ).success?
+ end
+
+ # TODO:: this data is posted to the subscription endpoint
+ # we need to implement webhooks for this to work properly
+ class CountUpdate
+ include JSON::Serializable
+
+ @[JSON::Field(key: "areaId")]
+ property area_id : String
+ property devices : Array(String)
+
+ @[JSON::Field(key: "type")]
+ property event_type : String
+ property timestamp : UInt64
+ property count : Int32
+ end
+
+ def update_count(count_json : String)
+ count = CountUpdate.from_json(count_json)
+ self["area_#{count.area_id}"] = count.count
+ end
+end
diff --git a/drivers/point_grab/cogni_point_spec.cr b/drivers/point_grab/cogni_point_spec.cr
new file mode 100644
index 00000000000..adb4ed1c2fe
--- /dev/null
+++ b/drivers/point_grab/cogni_point_spec.cr
@@ -0,0 +1,33 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "PointGrab::CogniPoint" do
+ # Send the request
+ retval = exec(:get_token)
+ token = "eyJhbGciOiJIUzI1NiIsInR5cCI6IkpXVCJ9.eyJzY29wZSI6WyJSRUFEIiwiV1JJVEUiXSwiZXhwIjoxNTc0MjMzNjEyLCJhdXRob3JpdGllcyI6WyJST0xFX1RSVVNURURfQ0xJRU5UIl0sImp0aSI6IjM1ZjkxYjlkLTVmZmMtNDJkYy05YWZkLTJiZTE0YjI1MmE1NCIsImNsaWVudF9pZCI6IjEwMDAwMjEzIn0.Wzrsaey5z3ShAFYKOaWmgfoRZNsk-PclSK9IRtYf4b8"
+
+ # We should request a new token from Floorsense
+ expect_http_request do |request, response|
+ if io = request.body
+ data = io.gets_to_end
+
+ # The request is param encoded
+ if data == "grant_type=client_credentials" && request.headers["Authorization"] == "Basic #{Base64.strict_encode("10000000:c5a6adc6-UUID-46e8-b72d-91395bce9565")}"
+ response.status_code = 200
+ response.output.puts %({
+ "token": "#{token}",
+ "access_token": "#{token}",
+ "token_type": "bearer",
+ "expires_in": 3599
+ })
+ else
+ response.status_code = 401
+ response.output.puts ""
+ end
+ else
+ raise "expected request to include token type"
+ end
+ end
+
+ # What the function should return (for use in making further requests)
+ retval.get.should eq("Bearer #{token}")
+end
diff --git a/drivers/qbic/touch_panel.cr b/drivers/qbic/touch_panel.cr
new file mode 100644
index 00000000000..e8425db9445
--- /dev/null
+++ b/drivers/qbic/touch_panel.cr
@@ -0,0 +1,268 @@
+require "placeos-driver"
+require "uri"
+
+# docs: https://drive.google.com/file/d/1ytAML83qloy9o0WN6C1GWjJ1P-Hcq-WY/view
+
+class Qbic::TouchPanel < PlaceOS::Driver
+ descriptive_name "Qbic Touch Panel"
+ generic_name :Panel
+
+ default_settings({
+ password: "12345678",
+ })
+
+ uri_base "https://192.168.12.0"
+
+ USERNAME = "admin"
+ @password : String = ""
+ @auth_token : String = ""
+ @refresh_token : String? = nil
+ @expired : Bool = true
+
+ def on_update
+ @password = URI.encode_www_form setting(String, :password)
+
+ transport.before_request do |request|
+ request.headers["Content-Type"] = "application/json"
+ request.headers["Authorization"] = @auth_token unless token_expired?
+ end
+
+ schedule.clear
+ schedule.every(1.minute) do
+ logger.debug { "polling to check connectivity" }
+ resp = get("/v1/public/info/")
+ if resp.success?
+ logger.debug { resp.body }
+ get_all_leds
+ end
+ end
+ end
+
+ class FailureResponse
+ include JSON::Serializable
+
+ property detail : String
+ end
+
+ class AuthResponse
+ include JSON::Serializable
+
+ # Returned on success
+ property access_token : String
+ property refresh_token : String
+ property token_type : String
+ end
+
+ def token_expired?
+ @expired
+ end
+
+ def get_token
+ return @auth_token unless token_expired?
+
+ # attempt to use refresh token if one is available
+ if refresh_token = @refresh_token
+ response = post("/v1/oauth2/token",
+ body: {
+ grant_type: "refresh_token",
+ refresh_token: refresh_token,
+ }.to_json
+ )
+
+ if response.success?
+ resp = AuthResponse.from_json(response.body.not_nil!)
+ @expired = false
+ @auth_token = "#{resp.token_type} #{resp.access_token}"
+ @refresh_token = resp.refresh_token
+ return @auth_token
+ else
+ logger.debug { "refresh token request failed" }
+ end
+ end
+
+ # Fall back to using the username and password
+ response = post("/v1/oauth2/token",
+ body: {
+ grant_type: "password",
+ username: USERNAME,
+ password: @password,
+ }.to_json
+ )
+
+ data = response.body.not_nil!
+
+ if response.success?
+ resp = AuthResponse.from_json(data)
+ @expired = false
+ @refresh_token = resp.refresh_token
+ @auth_token = "#{resp.token_type} #{resp.access_token}"
+ else
+ resp = FailureResponse.from_json(data)
+ raise "failed to obtain access token: #{resp.detail} (#{response.status})"
+ end
+ end
+
+ @[Security(Level::Administrator)]
+ def update_password(new_password : String)
+ raise "password must be between 4 and 16 characters" unless new_password.size >= 4 && new_password.size <= 16
+ query("POST", "/v1/user/password") do
+ define_setting(:password, new_password)
+ end
+ end
+
+ @[Security(Level::Administrator)]
+ def wifi_scan
+ query("GET", "/v1/wifi/scan_results") { |data| JSON.parse(data.not_nil!) }
+ end
+
+ enum AdvertiseMode
+ LowLatency
+ Balanced
+ LowPower
+ end
+
+ @[Security(Level::Administrator)]
+ def set_ibeacon(
+ enabled : Bool,
+ major : UInt16? = nil,
+ minor : UInt16? = nil,
+ uuid : String? = nil,
+ advertise_mode : AdvertiseMode? = nil,
+ power : Int8? = nil
+ )
+ query("POST", "/v1/net/beacon/ibeacon", {
+ enabled: enabled ? "enabled" : "disabled",
+ major: major,
+ minor: minor,
+ uuid: uuid,
+ advertise_mode: advertise_mode.to_s.underscore,
+ power: power,
+ }.to_json) { true }
+ end
+
+ def get_ibeacon
+ query("GET", "/v1/net/beacon/ibeacon") { |data| JSON.parse(data.not_nil!) }
+ end
+
+ # https://github.com/google/eddystone/tree/master/eddystone-uid
+ @[Security(Level::Administrator)]
+ def set_eddystone_uid(
+ enabled : Bool,
+ namespace : String? = nil,
+ instance : String? = nil,
+ advertise_mode : AdvertiseMode? = nil,
+ power : Int8? = nil
+ )
+ query("POST", "/v1/net/beacon/eddystone_uid", {
+ enabled: enabled ? "enabled" : "disabled",
+ namespace: namespace,
+ instance: instance,
+ advertise_mode: advertise_mode.to_s.underscore,
+ power: power,
+ }.to_json) { true }
+ end
+
+ def get_eddystone_uid
+ query("GET", "/v1/net/beacon/eddystone_uid") { |data| JSON.parse(data.not_nil!) }
+ end
+
+ @[Security(Level::Administrator)]
+ def set_eddystone_url(
+ enabled : Bool,
+ url : String? = nil,
+ advertise_mode : AdvertiseMode? = nil,
+ power : Int8? = nil
+ )
+ query("POST", "/v1/net/beacon/eddystone_url", {
+ enabled: enabled ? "enabled" : "disabled",
+ url: url,
+ advertise_mode: advertise_mode.to_s.underscore,
+ power: power,
+ }.to_json) { true }
+ end
+
+ def get_eddystone_url
+ query("GET", "/v1/net/beacon/eddystone_url") { |data| JSON.parse(data.not_nil!) }
+ end
+
+ def device_info
+ query("GET", "/v1/info/") { |data| JSON.parse(data.not_nil!) }
+ end
+
+ def settings
+ query("GET", "/v1/settings") { |data| JSON.parse(data.not_nil!) }
+ end
+
+ @[Security(Level::Administrator)]
+ def set_setting(key : String, value : String | JSON::Any)
+ query("POST", "/v1/settings/#{key}", {
+ value: value,
+ }.to_json) { true }
+ end
+
+ @[Security(Level::Support)]
+ def set_url(value : String)
+ set_setting "content_url", value
+ end
+
+ def leds
+ query("GET", "/v1/led") { |data| self[:leds] = NamedTuple(results: Array(String)).from_json(data.not_nil!)[:results] }
+ end
+
+ def get_led_state(name : String)
+ query("GET", "/v1/led/#{name}") { |data| self[name] = JSON.parse(data.not_nil!) }
+ end
+
+ def get_all_leds
+ query("GET", "/v1/led") do |data|
+ leds = NamedTuple(results: Array(String)).from_json(data.not_nil!)[:results]
+ self[:light_names] = leds
+ leds.each { |name| get_led_state(name) }
+ true
+ end
+ end
+
+ @[Security(Level::Support)]
+ def set_led_state(name : String, red : UInt8, green : UInt8, blue : UInt8)
+ value = {
+ red: red,
+ green: green,
+ blue: blue,
+ }
+ query("POST", "/v1/led/#{name}", value.to_json) { self[name] = value }
+ end
+
+ def set_all_leds(red : UInt8, green : UInt8, blue : UInt8)
+ query("GET", "/v1/led") do |data|
+ leds = NamedTuple(results: Array(String)).from_json(data.not_nil!)[:results]
+ leds.each { |name| set_led_state(name, red, green, blue) }
+ true
+ end
+ end
+
+ private def query(
+ method, path, body : ::HTTP::Client::BodyType = nil,
+ params : Hash(String, String?) | URI::Params = URI::Params.new,
+ headers : Hash(String, String) | HTTP::Headers = HTTP::Headers.new,
+ **opts, &block : String -> _
+ )
+ queue(**opts) do |task|
+ response = http(method, path, body, params, headers)
+
+ if response.status.unauthorized?
+ @expired = true
+ get_token
+ task.retry
+ elsif response.success?
+ task.success block.call(response.body)
+ else
+ begin
+ resp = FailureResponse.from_json(response.body.not_nil!)
+ task.abort "#{resp.detail} - #{response.status} (#{response.status_code})"
+ rescue
+ task.abort "unexpected response #{response.status} (#{response.status_code})\n#{response.body}"
+ end
+ end
+ end
+ end
+end
diff --git a/drivers/qbic/touch_panel_spec.cr b/drivers/qbic/touch_panel_spec.cr
new file mode 100644
index 00000000000..1bcba72473d
--- /dev/null
+++ b/drivers/qbic/touch_panel_spec.cr
@@ -0,0 +1,44 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Qbic::TouchPanel" do
+ # Send the request
+ retval = exec(:get_token)
+
+ # We should request a new token from Floorsense
+ expect_http_request do |request, response|
+ if io = request.body
+ data = io.gets_to_end
+ request = JSON.parse(data)
+
+ if request["grant_type"] == "password" && request["username"] == "admin" && request["password"] == "12345678"
+ response.status_code = 200
+ response.output.puts %({"access_token":"t6pm11le6m6pvae18ar9jqdap4","refresh_token":"gq5c6p1lps3m24nf1th0cmda32","token_type":"Bearer"})
+ else
+ response.status_code = 400
+ response.output.puts %({"detail":"Invalid_client, make sure username and password is correct."})
+ end
+ else
+ raise "expected request to include username and password"
+ end
+ end
+
+ # What the function should return (for use in making further requests)
+ retval.get.should eq("Bearer t6pm11le6m6pvae18ar9jqdap4")
+
+ # Get the list of LEDs on the device
+ retval = exec(:leds)
+
+ expect_http_request do |request, response|
+ if request.headers["Authorization"]? == "Bearer t6pm11le6m6pvae18ar9jqdap4"
+ response.status_code = 200
+ response.output.puts %({"results":["side_led", "front_led"]})
+ else
+ response.status_code = 401
+ response.output.puts %({"detail":"Invalid Authorization"})
+ end
+ end
+
+ retval.get.should eq ["side_led", "front_led"]
+
+ status[:leds].should eq ["side_led", "front_led"]
+end
diff --git a/drivers/qsc/q_sys_control.cr b/drivers/qsc/q_sys_control.cr
new file mode 100644
index 00000000000..eb10d434b1c
--- /dev/null
+++ b/drivers/qsc/q_sys_control.cr
@@ -0,0 +1,409 @@
+require "placeos-driver"
+
+# Documentation https://q-syshelp.qsc.com/Content/External_Control_APIs/ECP/ECP_Commands.htm
+
+class Qsc::QSysControl < PlaceOS::Driver
+ # Discovery Information
+ tcp_port 1702
+ descriptive_name "QSC Audio DSP External Control"
+ generic_name :Mixer
+
+ default_settings({
+ _change_groups: {
+ "room123_phone" => {
+ id: 1,
+ controls: ["VoIPCallStatusProgress", "VoIPCallStatusRinging", "VoIPCallStatusOffHook"],
+ },
+ },
+ })
+
+ alias Group = NamedTuple(id: Int32, controls: Set(String))
+ alias Ids = String | Array(String)
+ alias Val = Int32 | Float64
+
+ @username : String? = nil
+ @password : String? = nil
+
+ @connected : Bool = false
+ @change_group_id : Int32 = 30
+ @em_id : String? = nil
+ @emergency_subscribe : PlaceOS::Driver::Subscriptions::Subscription? = nil
+ getter history : Hash(String, Symbol) = {} of String => Symbol
+
+ @static_change_groups = {} of String => Group
+ @dynamic_change_groups = {} of String => Group
+
+ def on_load
+ transport.tokenizer = Tokenizer.new("\r\n")
+ queue.retries = 1
+ on_update
+ end
+
+ def on_update
+ @username = setting?(String, :username)
+ @password = setting?(String, :password)
+
+ @static_change_groups = setting?(Hash(String, Group), :change_groups) || {} of String => Group
+
+ if @connected
+ login if @username
+ recreate_change_groups
+ end
+ end
+
+ def connected
+ @connected = true
+ login if @username
+ recreate_change_groups
+ schedule.every(40.seconds) do
+ logger.debug { "Maintaining Connection" }
+ about
+ end
+ end
+
+ def disconnected
+ @connected = false
+ schedule.clear
+ end
+
+ protected def recreate_change_groups
+ return unless @connected
+ change_groups = @static_change_groups.merge @dynamic_change_groups
+ change_groups.each do |name, group|
+ logger.debug { "configuring change group #{name}" }
+ group_id = group[:id]
+ controls = group[:controls]
+
+ # Re-create change groups and poll every 2 seconds
+ do_send("cgc #{group_id}\n") # , wait: false)
+ do_send("cgsna #{group_id} 2000\n") # , wait: false)
+ controls.each do |id|
+ do_send("cga #{group_id} #{id}\n") # , wait: false)
+ end
+ end
+
+ em_id = setting?(String, :emergency)
+
+ # Emergency ID changed
+ if (e = @emergency_subscribe) && @em_id != em_id
+ subscriptions.unsubscribe(e)
+ end
+
+ # Emergency ID exists
+ if em_id
+ group = create_change_group(:emergency)
+ group_id = group[:id]
+ controls = group[:controls]
+
+ # Add id to change group as required
+ unless controls.includes?(em_id)
+ # subscribe to changes
+ @em_id = em_id
+ @emergency_subscribe = subscribe(em_id) do |_, value|
+ self[:emergency] = value
+ end
+
+ update_change_group(:emergency, group_id, Set.new([em_id]))
+ do_send("cga #{group_id} #{em_id}\n") # , wait: false)
+ end
+ end
+ end
+
+ def get_status(control_id : String, **options)
+ fader_type = options[:fader_type]?
+ @history[control_id] = fader_type if fader_type
+ do_send("cg #{control_id}\n", **options)
+ end
+
+ def set_position(control_id : String, position : Int32, ramp_time : Val? = nil)
+ if ramp_time
+ do_send("cspr \"#{control_id}\" #{position} #{ramp_time}\n") # , wait: false)
+ schedule.in(ramp_time.seconds + 200.milliseconds) { get_status(control_id) }
+ else
+ do_send("csp \"#{control_id}\" #{position}\n")
+ end
+ end
+
+ def set_value(control_id : String, value : Val, ramp_time : Val? = nil, **options)
+ fader_type = options[:fader_type]?
+ @history[control_id] = fader_type if fader_type
+ if ramp_time
+ do_send("csvr \"#{control_id}\" #{value} #{ramp_time}\n", **options) # , wait: false)
+ schedule.in(ramp_time.seconds + 200.milliseconds) { get_status(control_id) }
+ else
+ do_send("csv \"#{control_id}\" #{value}\n", **options)
+ end
+ end
+
+ def about
+ do_send("sg\n", name: :status, priority: 0)
+ end
+
+ def login(username : String? = nil, password : String? = nil)
+ username ||= @username
+ password ||= @password
+ do_send("login #{username} #{password}\n", name: :login, priority: 99)
+ end
+
+ # Used to set a dial number/string
+ def set_string(control_ids : Ids, text : String)
+ ensure_array(control_ids).each do |id|
+ do_send("css \"#{id}\" \"#{text}\"\n").get
+ self[id] = text
+ end
+ end
+
+ # Used to trigger dialing etc
+ def trigger(control_id : String)
+ logger.debug { "Sending trigger to Qsys: ct #{control_id}" }
+ do_send("ct \"#{control_id}\"\n") # , wait: false)
+ end
+
+ # Compatibility Methods
+ def fader(fader_ids : Ids, level : Val)
+ level = level.to_f.clamp(0.0, 100.0)
+ percentage = level / 100.0
+ range = -100..20
+
+ # adjust into range
+ level_actual = percentage * (range.size - 1).to_f
+ level_actual = (level_actual + range.begin.to_f).round(1)
+
+ ensure_array(fader_ids).each do |f_id|
+ if @history[f_id]? == :percentage_fader
+ set_value(f_id, level, name: "fader#{f_id}")
+ else
+ set_value(f_id, level_actual, name: "fader#{f_id}", fader_type: :fader)
+ end
+ end
+ end
+
+ def faders(fader_ids : Ids, level : Val)
+ fader(fader_ids, level)
+ end
+
+ def mute(mute_ids : Ids, state : Bool = true)
+ level = state ? 1 : 0
+ ensure_array(mute_ids).each { |m_id| set_value(m_id, level, fader_type: :mute) }
+ end
+
+ def mutes(mute_ids : Ids, state : Bool)
+ mute(mute_ids, state)
+ end
+
+ def unmute(mute_ids : Ids)
+ mute(mute_ids, false)
+ end
+
+ def mute_toggle(mute_id : Ids)
+ mute(mute_id, !self["fader#{mute_id}_mute"]?.try(&.as_bool))
+ end
+
+ def snapshot(name : String, index : Int32, ramp_time : Val = 1.5)
+ do_send("ssl \"#{name}\" #{index} #{ramp_time}\n") # , wait: false)
+ end
+
+ def save_snapshot(name : String, index : Int32)
+ do_send("sss \"#{name}\" #{index}\n") # , wait: false)
+ end
+
+ # For inter-module compatibility
+ def query_fader(fader_ids : Ids)
+ fad = ensure_array(fader_ids)[0]
+ get_status(fad, fader_type: (@history[fad]? || :fader))
+ end
+
+ def query_faders(fader_ids : Ids)
+ ensure_array(fader_ids).each { |f_id| get_status(f_id, fader_type: (@history[f_id]? || :fader)) }
+ end
+
+ def query_mute(fader_ids : Ids)
+ fad = ensure_array(fader_ids)[0]
+ get_status(fad, fader_type: :mute)
+ end
+
+ def query_mutes(fader_ids : Ids)
+ ensure_array(fader_ids).each { |fad| get_status(fad, fader_type: :mute) }
+ end
+
+ def phone_number(number : String, control_id : String)
+ set_string(control_id, number)
+ end
+
+ def phone_dial(control_id : String)
+ trigger(control_id)
+ schedule.in(200.milliseconds) { poll_change_group(:phone) }
+ end
+
+ def phone_hangup(control_id : String)
+ phone_dial(control_id)
+ end
+
+ private def create_change_group(name) : Group
+ name = name.to_s
+
+ if group = @dynamic_change_groups[name]?
+ return group
+ end
+
+ # Provide a unique group id
+ next_id = @change_group_id
+ @change_group_id += 1
+
+ @dynamic_change_groups[name] = {
+ id: next_id,
+ controls: Set(String).new,
+ }
+
+ # create change group and poll every 2 seconds
+ do_send("cgc #{next_id}\n") # , wait: false)
+ do_send("cgsna #{next_id} 2000\n") # , wait: false)
+ @dynamic_change_groups[name]
+ end
+
+ private def update_change_group(name, id, controls) : Group
+ @dynamic_change_groups[name.to_s] = {
+ id: id,
+ controls: controls,
+ }
+ end
+
+ private def poll_change_group(name)
+ if group = @dynamic_change_groups[name]
+ do_send("cgpna #{group[:id]}\n") # , wait: false)
+ end
+ end
+
+ def received(data, task)
+ data = String.new(data)
+ puts "GOT: #{data}"
+ return task.try(&.success) if data == "none\r\n"
+ logger.debug { "QSys sent: #{data}" }
+ resp = shellsplit(data)
+
+ case resp[0]
+ when "cv"
+ control_id = resp[1]
+ string_rep = resp[2]
+ value = resp[-2]
+ position = resp[-1].to_f
+
+ self["pos_#{control_id}"] = position
+ @history[control_id] = :percentage_fader if string_rep.ends_with?('%')
+
+ if type = @history[control_id]?
+ case type
+ when :fader
+ range = -100..20
+ vol_percent = ((value.to_f - range.begin.to_f) / (range.size - 1).to_f) * 100.0
+ self["fader#{control_id}"] = vol_percent.round(2)
+ when :percentage_fader
+ self["fader#{control_id}"] = value.to_f
+ when :mute
+ self["fader#{control_id}_mute"] = value.to_i == 1
+ end
+ else
+ value = resp[2]
+ if value == "false" || value == "true"
+ self[control_id] = value == "true"
+ else
+ self[control_id] = value.gsub('_', ' ')
+ end
+ logger.debug { "Received response from unknown ID type: #{control_id} == #{value}" }
+ end
+ when "cvv" # Control status, Array of control status
+ control_id = resp[1]
+ count = resp[2].to_i
+
+ if type = @history[control_id]?
+ # Skip strings and extract the values
+ next_count = count + 3
+ count = resp[next_count].to_i
+ 1.upto(count) do |index|
+ value = resp[next_count + index]
+
+ case type
+ when :fader
+ range = -100..20
+ vol_percent = ((value.to_f - range.begin.to_f) / (range.size - 1).to_f) * 100.0
+ self["fader#{control_id}"] = vol_percent.round(2)
+ when :mute
+ self["fader#{control_id}_mute"] = value == 1
+ end
+ end
+ else
+ # Don't skip strings here
+ next_count = 2
+ 1.upto(count) do |index|
+ value = resp[next_count + index]
+
+ if value == "false" || value == "true"
+ self[control_id] = value == "true"
+ else
+ self[control_id] = value.gsub('_', ' ')
+ end
+ end
+ logger.debug { "Received response from unknown ID type: #{control_id}" }
+
+ # Jump to the position values
+ next_count = count + 3
+ count = resp[next_count].to_i
+ end
+
+ # Grab the positions
+ next_count = next_count + count + 1
+ count = resp[next_count].to_i
+ 1.upto(count) do |index|
+ value = resp[next_count + index]
+ self["pos_#{control_id}"] = value
+ end
+ when "sr" # About response
+ self[:design_name] = resp[1]
+ self[:is_primary] = resp[3] == "1"
+ self[:is_active] = resp[4] == "1"
+ when "core_not_active", "bad_change_group_handle", "bad_command", "bad_id", "control_read_only", "too_many_change_groups"
+ return task.try(&.abort("Error response received: #{data}"))
+ when "login_required"
+ login if @username
+ return task.try(&.abort("Login is required!"))
+ when "login_success"
+ logger.debug { "Login success!" }
+ when "login_failed"
+ return task.try(&.abort("Invalid login details provided"))
+ when "rc"
+ logger.warn { "System is notifying us of a disconnect!" }
+ when "cmvv"
+ logger.debug { "received cmvv response" }
+ else
+ logger.warn { "Unknown response received #{data}" }
+ end
+
+ task.try(&.success)
+ end
+
+ private def do_send(req, fader_type : Symbol? = nil, **options)
+ logger.debug { "sending #{req}" }
+ send(req, **options)
+ end
+
+ private def ensure_array(object)
+ object.is_a?(Array) ? object : [object]
+ end
+
+ # Quick dirty port of https://github.com/ruby/ruby/blob/master/lib/shellwords.rb
+ private def shellsplit(line : String) : Array(String)
+ words = [] of String
+ field = ""
+ pattern = /\G\s*(?>([^\s\\\'\"]+)|'([^\']*)'|"((?:[^\"\\]|\\.)*)"|(\\.?)|(\S))(\s|\z)?/m
+ line.scan(pattern) do |match|
+ _, word, sq, dq, esc, garbage, sep = match.to_a
+ raise ArgumentError.new("Unmatched quote: #{line.inspect}") if garbage
+ field += (word || sq || dq.try(&.gsub(/\\([$`"\\\n])/, "\\1")) || esc.not_nil!.gsub(/\\(.)/, "\\1"))
+ if sep
+ words << field
+ field = ""
+ end
+ end
+ words
+ end
+end
diff --git a/drivers/qsc/q_sys_control_spec.cr b/drivers/qsc/q_sys_control_spec.cr
new file mode 100644
index 00000000000..326f5d9b1f7
--- /dev/null
+++ b/drivers/qsc/q_sys_control_spec.cr
@@ -0,0 +1,79 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Qsc::QSysControl" do
+ sleep 1
+
+ settings({
+ username: "user",
+ password: "pass",
+ emergency: "6",
+ })
+
+ should_send("login user pass\n")
+ responds("login_success\r\n")
+ should_send("cgc 30\n")
+ responds("none\r\n")
+ should_send("cgsna 30 2000\n")
+ responds("none\r\n")
+ should_send("cga 30 6\n")
+ responds("none\r\n")
+
+ exec(:about)
+ should_send("sg\n")
+ responds("sr \"MyDesign\" \"NIEC2bxnVZ6a\" 1 1\r\n")
+ status[:design_name].should eq("MyDesign")
+ status[:is_primary].should eq(true)
+ status[:is_active].should eq(true)
+
+ exec(:mute, ["1", "2", "3"], true)
+ should_send("csv \"1\" 1\n")
+ responds("cv \"1\" \"control string\" 1 8\r\n")
+ status[:pos_1].should eq(8)
+ status[:fader1_mute].should eq(true)
+ should_send("csv \"2\" 1\n")
+ responds("cv \"2\" \"control string\" 1 5\r\n")
+ status[:pos_2].should eq(5)
+ status[:fader2_mute].should eq(true)
+ should_send("csv \"3\" 1\n")
+ responds("cv \"3\" \"control string\" 1 4\r\n")
+ status[:pos_3].should eq(4)
+ status[:fader3_mute].should eq(true)
+
+ exec(:faders, ["1", "2", "3"], 90)
+ should_send("csv \"1\" 8.0\n")
+ responds("cv \"1\" \"control string\" 9 6\r\n")
+ status[:pos_1].should eq(6)
+ status[:fader1].should eq(90.83)
+ status[:fader1_mute].should eq(true)
+ should_send("csv \"2\" 8.0\n")
+ responds("cv \"2\" \"control string\" 8 7\r\n")
+ status[:pos_2].should eq(7)
+ status[:fader2].should eq(90)
+ should_send("csv \"3\" 8.0\n")
+ responds("cv \"3\" \"control string\" 8 8\r\n")
+ status[:pos_3].should eq(8)
+ status[:fader3].should eq(90)
+
+ exec(:fader, "HH2:Level", 90)
+ should_send(%(csv "HH2:Level" 8.0\n))
+ responds %(cv "HH2:Level" "-53.2dB" -53.2 8.0\r\n)
+ status["faderHH2:Level"].should eq(39.0)
+
+ exec(:phone_number, "0123456789", "1")
+ should_send("css \"1\" \"0123456789\"\n")
+ responds("cv \"1\" \"0123456789\" 9 8\r\n")
+ status[:"1"].should eq("0123456789")
+
+ # Test percentage faders
+ exec(:query_fader, ["3"])
+ should_send %(cg 3\n)
+ responds %(cv 3 "0%" 0 0\r\n)
+ status[:pos_3].should eq(0.0)
+ status[:fader3].should eq(0.0)
+
+ exec(:query_fader, ["2"])
+ should_send %(cg 2\n)
+ responds %(cv 2 "20%" 20 20\r\n)
+ status[:pos_2].should eq(20.0)
+ status[:fader2].should eq(20.0)
+end
diff --git a/drivers/qsc/q_sys_remote.cr b/drivers/qsc/q_sys_remote.cr
new file mode 100644
index 00000000000..b5706faa822
--- /dev/null
+++ b/drivers/qsc/q_sys_remote.cr
@@ -0,0 +1,433 @@
+require "json"
+require "placeos-driver"
+
+# Documentation: https://aca.im/driver_docs/QSC/QRCDocumentation.pdf
+# https://q-syshelp.qsc.com/Content/External_Control_APIs/QRC/QRC_Commands.htm
+
+class Qsc::QSysRemote < PlaceOS::Driver
+ tcp_port 1710
+ descriptive_name "QSC Audio DSP"
+ generic_name :Mixer
+
+ @id : Int32 = 0
+ @db_based_faders : Bool? = nil
+ @username : String? = nil
+ @password : String? = nil
+
+ Delimiter = "\0"
+ JsonRpcVer = "2.0"
+ Errors = {
+ -32700 => "Parse error. Invalid JSON was received by the server.",
+ -32600 => "Invalid request. The JSON sent is not a valid Request object.",
+ -32601 => "Method not found.",
+ -32602 => "Invalid params.",
+ -32603 => "Server error.",
+ 2 => "Invalid Page Request ID",
+ 3 => "Bad Page Request - could not create the requested Page Request",
+ 4 => "Missing file",
+ 5 => "Change Groups exhausted",
+ 6 => "Unknown change croup",
+ 7 => "Unknown component name",
+ 8 => "Unknown control",
+ 9 => "Illegal mixer channel index",
+ 10 => "Logon required",
+ }
+ DB_RANGE = -100..20
+
+ alias Num = Int32 | Float64
+ alias ValTup = NamedTuple(Name: String, Value: Num)
+ alias PosTup = NamedTuple(Name: String, Position: Num)
+ alias Values = ValTup | PosTup | Array(ValTup) | Array(PosTup)
+ alias Ids = String | Array(String)
+
+ def on_load
+ transport.tokenizer = Tokenizer.new(Delimiter)
+ on_update
+ end
+
+ def on_update
+ @db_based_faders = setting?(Bool, :db_based_faders)
+ @username = setting?(String, :username)
+ @password = setting?(String, :password)
+ logon if @username && @password
+ end
+
+ def connected
+ schedule.every(20.seconds) do
+ logger.debug { "Maintaining Connection" }
+ no_op
+ end
+ @id = 0
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ # This command does nothing but is useful for making sure the socket is left open
+ def no_op
+ do_send(cmd: :NoOp, priority: 0, wait: false)
+ end
+
+ def get_status
+ do_send(next_id, cmd: :StatusGet, params: 0, priority: 0)
+ end
+
+ def logon
+ do_send(
+ cmd: :Logon,
+ params: {
+ :User => @username,
+ :Password => @password,
+ },
+ priority: 99
+ )
+ end
+
+ def control_set(name : String, value : Num | Bool, ramp : Num? = nil, **options)
+ if ramp
+ params = {
+ :Name => name,
+ :Value => value,
+ :Ramp => ramp,
+ }
+ else
+ params = {
+ :Name => name,
+ :Value => value,
+ }
+ end
+
+ do_send(next_id, "Control.Set", params, **options)
+ end
+
+ def control_get(names : Array(String), **options)
+ do_send(next_id, "Control.Get", names, **options)
+ end
+
+ def component_get(c_name : String, controls : Array(String), **options)
+ do_send(next_id, "Component.Get", {
+ :Name => c_name,
+ :Controls => controls.map { |ctrl| {:Name => ctrl} },
+ }, **options)
+ end
+
+ def component_set(c_name : String, values : Values, **options)
+ values = ensure_array(values)
+
+ do_send(next_id, "Component.Set", {
+ :Name => c_name,
+ :Controls => values,
+ }, **options)
+ end
+
+ def component_trigger(component : String, trigger : String, **options)
+ do_send(next_id, "Component.Trigger", {
+ :Name => component,
+ :Controls => [{:Name => trigger}],
+ }, **options)
+ end
+
+ def get_components(**options)
+ do_send(next_id, "Component.GetComponents", **options)
+ end
+
+ def change_group_add_controls(group_id : String, controls : Array(String), **options)
+ do_send(next_id, "ChangeGroup.AddControl", {
+ :Id => group_id,
+ :Controls => controls,
+ }, **options)
+ end
+
+ def change_group_remove_controls(group_id : String, controls : Array(String), **options)
+ do_send(next_id, "ChangeGroup.Remove", {
+ :Id => group_id,
+ :Controls => controls,
+ }, **options)
+ end
+
+ def change_group_add_component(group_id : String, component_name : String, controls : Array(String), **options)
+ do_send(next_id, "ChangeGroup.AddComponentControl", {
+ :Id => group_id,
+ :Component => {
+ :Name => component_name,
+ :Controls => controls.map { |ctrl| {:Name => ctrl} },
+ },
+ }, **options)
+ end
+
+ # Returns values for all the controls
+ def poll_change_group(group_id : String, **options)
+ do_send(next_id, "ChangeGroup.Poll", {:Id => group_id}, **options)
+ end
+
+ # Removes the change group
+ def destroy_change_group(group_id : String, **options)
+ do_send(next_id, "ChangeGroup.Destroy", {:Id => group_id}, **options)
+ end
+
+ # Removes all controls from change group
+ def clear_change_group(group_id : String, **options)
+ do_send(next_id, "ChangeGroup.Clear", {:Id => group_id}, **options)
+ end
+
+ # Where every is the number of seconds between polls
+ def auto_poll_change_group(group_id : String, every : Num, **options)
+ do_send(next_id, "ChangeGroup.AutoPoll", {
+ :Id => group_id,
+ :Rate => every,
+ }, **options) # , wait: false)
+ end
+
+ # Example usage:
+ # mixer 'Parade', {1 => [2,3,4], 3 => 6}, true
+ def mixer(name : String, inouts : Hash(Int32, Int32 | Array(Int32)), mute : Bool = false, **options)
+ inouts.each do |input, outputs|
+ outputs = ensure_array(outputs)
+
+ do_send(next_id, "Mixer.SetCrossPointMute", {
+ :Name => name,
+ :Inputs => input.to_s,
+ :Outputs => outputs.join(' '),
+ :Value => mute,
+ }, **options)
+ end
+ end
+
+ Faders = {
+ matrix_in: {
+ type: :"Mixer.SetInputGain",
+ pri: :Inputs,
+ },
+ matrix_out: {
+ type: :"Mixer.SetOutputGain",
+ pri: :Outputs,
+ },
+ matrix_crosspoint: {
+ type: :"Mixer.SetCrossPointGain",
+ pri: :Inputs,
+ sec: :Outputs,
+ },
+ }
+
+ def matrix_fader(name : String, level : Num, index : Array(Int32), type : String = "matrix_out", **options)
+ info = Faders[type]
+
+ level = level.to_f.clamp(0.0, 100.0)
+ percentage = level / 100.0
+
+ # adjust into range
+ level_actual = percentage * (DB_RANGE.size - 1).to_f
+ level_actual = (level_actual + DB_RANGE.begin.to_f).round(1)
+
+ if sec = info[:sec]?
+ params = {
+ :Name => name,
+ info[:pri] => index[0],
+ sec => index[1],
+ :Value => level_actual,
+ }
+ else
+ params = {
+ :Name => name,
+ info[:pri] => index,
+ :Value => level_actual,
+ }
+ end
+
+ do_send(next_id, info[:type], params, **options)
+ end
+
+ Mutes = {
+ matrix_in: {
+ type: :"Mixer.SetInputMute",
+ pri: :Inputs,
+ },
+ matrix_out: {
+ type: :"Mixer.SetOutputMute",
+ pri: :Outputs,
+ },
+ }
+
+ def matrix_mute(name : String, value : Num, index : Array(Int32), type : String = "matrix_out", **options)
+ info = Mutes[type]
+
+ do_send(next_id, info[:type], {
+ :Name => name,
+ info[:pri] => index,
+ :Value => value,
+ }, **options)
+ end
+
+ # value can either be a number to set actual numeric values like decibels
+ # or Bool to deal with mute state
+ def fader(fader_ids : Ids, value : Num | Bool, component : String? = nil, type : String = "fader", use_value : Bool = false, **options)
+ faders = ensure_array(fader_ids)
+ if component && (val = value.as?(Num))
+ val = val.to_f.clamp(0.0, 100.0)
+
+ if @db_based_faders || use_value
+ percentage = val / 100.0
+
+ # adjust into range
+ level_actual = percentage * (DB_RANGE.size - 1).to_f
+ level_actual = (level_actual + DB_RANGE.begin.to_f).round(1)
+
+ fads = faders.map { |fad| {Name: fad, Value: level_actual} }
+ else
+ # I think this means 0-100%
+ fads = faders.map { |fad| {Name: fad, Position: val} }
+ end
+ component_set(component, fads, name: "level_#{faders[0]}").get
+ component_get(component, faders)
+ else
+ reqs = faders.map { |fad| control_set(fad, value) }
+ reqs.last.get
+ control_get(faders)
+ end
+ end
+
+ def faders(ids : Ids, value : Num | Bool, component : String? = nil, type : String = "fader", **options)
+ fader(ids, value, component, type, **options)
+ end
+
+ def mute(fader_id : Ids, state : Bool = true, component : String? = nil, type : String = "fader", **options)
+ fader(fader_id, state, component, type, state, **options)
+ end
+
+ def mutes(ids : Ids, state : Bool = true, component : String? = nil, type : String = "fader", **options)
+ mute(ids, state, component, type, **options)
+ end
+
+ def unmute(fader_id : Ids, component : String? = nil, type : String = "fader", **options)
+ mute(fader_id, false, component, type, **options)
+ end
+
+ def query_fader(fader_id : Ids, component : String? = nil, type : String = "fader")
+ faders = ensure_array(fader_id)
+ component ? component_get(component, faders) : control_get(faders)
+ end
+
+ def query_faders(ids : Ids, component : String? = nil, type : String = "fader", **options)
+ query_fader(ids, component, type, **options)
+ end
+
+ def query_mute(fader_id : Ids, component : String? = nil, type : String = "fader")
+ query_fader(fader_id, component, type)
+ end
+
+ def query_mutes(ids : Ids, component : String? = nil, type : String = "fader", **options)
+ query_fader(ids, component, type, **options)
+ end
+
+ def received(data, task)
+ data = String.new(data[0..-2])
+ response = JSON.parse(data)
+
+ logger.debug { "QSys sent:" }
+ logger.debug { response }
+
+ if err = response["error"]?
+ code = err["code"]
+ logger.warn { "Error code #{code} - #{Errors[code]}" }
+
+ if code == 10
+ if @username && @password
+ logon.get
+ return task.try(&.retry("Logged on and retrying command"))
+ else
+ return task.try(&.abort("Login required but no username and/or password in settings"))
+ end
+ end
+
+ return task.try(&.abort(err["message"]))
+ end
+
+ return task.try(&.success("Unknown response")) unless result = response["result"]?
+
+ case result
+ when .as_h?
+ if result["Controls"]? # Probably Component.Get
+ process(result["Controls"].as_a, result["Name"]?)
+ elsif result["Platform"]? # StatusGet
+ result.as_h.each { |k, v| self[k.underscore] = v }
+ end
+ when .as_a? # Control.Get
+ process(result.as_a)
+ end
+
+ task.try(&.success)
+ end
+
+ BoolVals = {"true", "false", "muted", "unmuted"}
+ BoolTrue = {"true", "muted"}
+
+ private def process(values : Array, name : JSON::Any? = nil)
+ component = name.try(&.as_s?) ? "_#{name}" : ""
+ values.each do |value|
+ name = value["Name"]
+
+ next unless val = value["Value"]?
+
+ pos = value["Position"]?
+ str = value["String"]?.try(&.as_s)
+
+ if BoolVals.includes?(str)
+ self["fader#{name}#{component}_mute"] = str.in?(BoolTrue)
+ else
+ # Seems like string values can be independent of the other values
+ # This should mostly work to detect a string value
+ if val == 0 && pos == 0 && str && str[0] != '0'
+ self["#{name}#{component}"] = str
+ next
+ end
+
+ if pos && (pos = pos.as_f?)
+ self["fader#{name}#{component}_pos"] = pos
+ self["fader#{name}#{component}"] = pos * 100.0
+ end
+
+ if val.as_s?
+ self["#{name}#{component}"] = val
+ elsif val = (val.as_i? || val.as_f?)
+ self["fader#{name}#{component}_val"] = val
+ end
+ end
+ end
+ end
+
+ def next_id
+ @id += 1
+ @id
+ end
+
+ private def do_send(id : Int32? = nil, cmd = nil, params = {} of String => String, **options)
+ if id
+ req = {
+ jsonrpc: JsonRpcVer,
+ id: id,
+ method: cmd,
+ params: params,
+ }
+ else
+ req = {
+ jsonrpc: JsonRpcVer,
+ method: cmd,
+ params: params,
+ }
+ end
+
+ logger.debug { "sending: #{req}" }
+
+ cmd = req.to_json + Delimiter
+
+ logger.debug { "sending json" }
+ logger.debug { cmd.inspect }
+
+ send(cmd, **options)
+ end
+
+ private def ensure_array(object)
+ object.is_a?(Array) ? object : [object]
+ end
+end
diff --git a/drivers/qsc/q_sys_remote_spec.cr b/drivers/qsc/q_sys_remote_spec.cr
new file mode 100644
index 00000000000..fb98549c46c
--- /dev/null
+++ b/drivers/qsc/q_sys_remote_spec.cr
@@ -0,0 +1,151 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Qsc::QSysRemote" do
+ settings({
+ username: "user",
+ password: "pass",
+ })
+
+ # logon
+ should_send({
+ jsonrpc: "2.0",
+ method: "Logon",
+ params: {
+ "User" => "user",
+ "Password" => "pass",
+ },
+ }.to_json + "\0")
+ responds({"TODO" => "response not defined in docs"}.to_json + "\0")
+
+ exec(:no_op)
+ should_send({
+ jsonrpc: "2.0",
+ method: "NoOp",
+ params: {} of String => String,
+ }.to_json + "\0")
+ responds({"TODO" => "response not defined in docs"}.to_json + "\0")
+
+ exec(:get_status)
+ should_send({
+ jsonrpc: "2.0",
+ id: 1,
+ method: "StatusGet",
+ params: 0,
+ }.to_json + "\0")
+ responds({
+ "jsonrpc" => "2.0",
+ "id" => 1,
+ "result" => {
+ "Platform" => "Core 500i",
+ "State" => "Active",
+ "DesignName" => "SAF‐MainPA",
+ "DesignCode" => "qALFilm6IcAz",
+ "IsRedundant" => false,
+ "IsEmulator" => true,
+ "Status" => {
+ "Code" => 0,
+ "String" => "OK",
+ },
+ },
+ }.to_json + "\0")
+ status[:platform].should eq("Core 500i")
+ status[:state].should eq("Active")
+ status[:design_name].should eq("SAF‐MainPA")
+ status[:design_code].should eq("qALFilm6IcAz")
+ status[:is_redundant].should eq(false)
+ status[:is_emulator].should eq(true)
+ status[:status].should eq({
+ "Code" => 0,
+ "String" => "OK",
+ })
+
+ exec(:control_set, "MainGain", 8)
+ should_send({
+ "jsonrpc" => "2.0",
+ "id" => 2,
+ "method" => "Control.Set",
+ "params" => {
+ "Name" => "MainGain",
+ "Value" => 8,
+ },
+ }.to_json + "\0")
+ responds({
+ "jsonrpc" => "2.0",
+ "id" => 1234,
+ "result" => [
+ {
+ "Name" => "MainGain",
+ "Value" => 8,
+ },
+ ],
+ }.to_json + "\0")
+ status[:faderMainGain_val].should eq(8)
+
+ exec(:component_get, "My APM", ["ent.xfade.gain", "ent.xfade.gain2"])
+ should_send({
+ "jsonrpc" => "2.0",
+ "id" => 3,
+ "method" => "Component.Get",
+ "params" => {
+ "Name" => "My APM",
+ "Controls" => [
+ {"Name" => "ent.xfade.gain"},
+ {"Name" => "ent.xfade.gain2"},
+ ],
+ },
+ }.to_json + "\0")
+ responds({
+ "jsonrpc" => "2.0",
+ "result" => {
+ "Name" => "My APM",
+ "Controls" => [
+ {
+ "Name" => "ent.xfade.gain",
+ "Value" => -100.0,
+ "String" => "‐100.0dB",
+ "Position" => 0,
+ },
+ {
+ "Name" => "ent.xfade.gain2",
+ "Value" => 8.0,
+ "String" => "8.0dB",
+ "Position" => 0.9,
+ },
+ ],
+ },
+ }.to_json + "\0")
+ status["faderent.xfade.gain_My APM_pos"].should eq(0)
+ status["faderent.xfade.gain_My APM"].should eq(0)
+ status["faderent.xfade.gain2_My APM_pos"].should eq(0.9)
+ status["faderent.xfade.gain2_My APM"].should eq(90.0)
+
+ exec(:change_group_add_controls, "my change group", ["some control", "another control"])
+ should_send({
+ "jsonrpc" => "2.0",
+ "id" => 4,
+ "method" => "ChangeGroup.AddControl",
+ "params" => {
+ "Id" => "my change group",
+ "Controls" => ["some control", "another control"],
+ },
+ }.to_json + "\0")
+ responds({
+ "jsonrpc" => "2.0",
+ "id" => 4,
+ "result" => {
+ "Id" => "my change group",
+ "Changes" => [
+ {
+ "Name" => "some control",
+ "Value" => -12,
+ "String" => "‐12dB",
+ },
+ {
+ "Name" => "another control",
+ "Value" => -6,
+ "String" => "‐6dB",
+ },
+ ],
+ },
+ }.to_json + "\0")
+end
diff --git a/drivers/rhb_access/axiom_room_logic.cr b/drivers/rhb_access/axiom_room_logic.cr
new file mode 100644
index 00000000000..7070ccf7aad
--- /dev/null
+++ b/drivers/rhb_access/axiom_room_logic.cr
@@ -0,0 +1,55 @@
+require "placeos-driver"
+
+class RHBAccess::AxiomRoomLogic < PlaceOS::Driver
+ descriptive_name "Room Access Logic for Axiom rooms"
+ generic_name :RoomAccess
+ description "Abstracts room access for Axiom"
+
+ default_settings({
+ axiom_door_ids: [] of String,
+ axiom_status_poll_cron: "*/5 * * * *",
+ })
+
+ accessor axiom : AxiomXa
+
+ @door_ids = [] of String
+ @cron_string : String = "*/5 * * * *"
+
+ def on_update
+ @door_ids = setting(Array(String), :axiom_door_ids)
+ @cron_string = setting(String, :axiom_status_poll_cron)
+ schedule.clear
+ schedule.cron(@cron_string) { status? }
+ end
+
+ def lock
+ @door_ids.map { |d| axiom.lock(d).get }
+ rescue
+ logger.error { "AxiomXa: ERROR while LOCKING #{@door_ids}" }
+ else
+ self["locked_by_placeos_at"] = Time.local
+ status?
+ end
+
+ def unlock
+ @door_ids.map { |d| axiom.unlock(d).get }
+ rescue
+ logger.error { "AxiomXa: ERROR while UNLOCKING #{@door_ids}" }
+ else
+ self["unlocked_by_placeos_at"] = Time.local
+ status?
+ end
+
+ def status?
+ result = @door_ids.map { |id| {id, axiom.status?(id).get} }
+ rescue
+ logger.error { "AxiomXa: ERROR requesting STATUS of #{@door_ids}" }
+ else
+ doors_locked = 0
+ result.each do |id, status|
+ self[id] = status["Status"]
+ doors_locked += 1 if status["Status"].to_s.starts_with? "Locked"
+ end
+ self["doors_locked"] = doors_locked
+ end
+end
diff --git a/drivers/rhb_access/axiomxa.cr b/drivers/rhb_access/axiomxa.cr
new file mode 100644
index 00000000000..5b3eb05a5c9
--- /dev/null
+++ b/drivers/rhb_access/axiomxa.cr
@@ -0,0 +1,37 @@
+require "placeos-driver"
+require "axio"
+
+class RHBAccess::Axiomxa < PlaceOS::Driver
+ descriptive_name "RHB Access AxiomXA"
+ generic_name :AxiomXa
+ uri_base "http://127.0.0.1:60001"
+
+ alias Client = Axio::Client
+
+ default_settings({
+ username: "ABCDEFGHIJKLMNOPQRSTUVWXYZ",
+ password: "ABCDEF123456",
+ })
+
+ protected getter! client : Client
+
+ def on_update
+ host_name = config.uri.not_nil!.to_s
+ @client = Client.new(base_url: host_name.to_s, username: setting(String, :username), password: setting(String, :password))
+ end
+
+ def lock(id : String, permanent : Bool = false)
+ @client.try(&.access_points.lock(id: id, permanent: permanent.to_s))
+ self["access_point_#{id}"] = {"Status" => "locked", "permanent" => permanent.to_s}
+ end
+
+ def unlock(id : String, permanent : Bool = false)
+ @client.try(&.access_points.unlock(id: id, permanent: permanent.to_s))
+ self["access_point_#{id}"] = {"Status" => "unlocked", "permanent" => permanent.to_s}
+ end
+
+ def status?(id : String)
+ response = @client.try(&.access_points.status(id: id))
+ self["access_point_#{id}_status"] = JSON.parse(response.not_nil!.body)
+ end
+end
diff --git a/drivers/rhombus/integration_details.md b/drivers/rhombus/integration_details.md
new file mode 100644
index 00000000000..b51dd0ac517
--- /dev/null
+++ b/drivers/rhombus/integration_details.md
@@ -0,0 +1,102 @@
+# Webhook interaction details
+
+PlaceOS implements the following webhook methods for Rhombus initiated interactions.
+
+A webhook will be create in backoffice on PlaceOS that is unique for each client that will look something like this: https://instance.placeos.com/api/engine/v2/webhook/trig-DHgkU1~p/notify?secret=kfwu5WYc3a1suZ&exec=true&mod=RhombusSecurity&method=request
+
+or
+
+https://instance.placeos.com/api/engine/v2/webhook/trig-DHgkU1~p/notify/{secret}/{mod}/{index}/{request}
+
+## Creating the Webhook
+
+1. Add a new webhook
+ * enable webhook
+ * add supported methods: GET, POST, PUT, PATCH, DELETE
+2. Add the trigger to the system
+ * edit it to enable execute
+3. Copy the webhook link and add `exec=true&mod=RhombusSecurity&method=request` to the end of the URL
+
+## Supported methods
+
+These indicate the desired action to be performed, where `Place Webhook` is the unique webhook generated for the client and defined in Rhombus
+
+### POST Place Webhook
+
+Creates a new Rhombus subscription when POSTED with the following body:
+
+```yaml
+{
+ "webhook": "https://webhooks.rhombussystems.com/external/placeOsWebhook/AAAAAAAAAAAAAA",
+ # Random data if signed requests are desirable (optional)
+ "secret": "123456"
+}
+```
+
+responds 201 on success
+
+### DELETE Place Webhook
+
+Removes a Rhombus subscription when DELETED with the following body:
+
+```yaml
+{
+ "webhook": "https://webhooks.rhombussystems.com/external/placeOsWebhook/AAAAAAAAAAAAAA"
+}
+```
+
+expects the webhook URL to match an existing subscription
+responds 202 on success
+
+### GET Place Webhook
+
+Responds 200 and returns the list of doors in the security system:
+
+```yaml
+[
+ {
+ "door_id": "1234-2342",
+ "description": "Lobby Entrance"
+ },
+ {
+ "door_id": "5678-9012"
+ }
+]
+```
+
+### PUT Place Webhook
+
+Attempts to unlock a door when PUT with the following body:
+
+```yaml
+{
+ "door_id": "5678-9012"
+}
+```
+
+responds:
+
+* 200 for success
+* 403 when failed to unlock for any reason
+* 501 if the security system doesn't support remote door unlock
+
+## PlaceOS -> Rhombus
+
+When a door event is detected, the following is sent to each of the Rombus subscriptions
+
+### POST webhooks.rhombussystems
+
+with body
+
+```yaml
+{
+ "door_id": "123456",
+ "timestamp": "2022-04-03T23:59:25Z",
+ # signature set if a secret was provided with the initail subscription
+ "signature": "HMAC hex digest sha256 signature of timestamp",
+ "action": "granted", # or `"denied"` `"tamper"` `"request_to_exit"`
+ "card_id": "123456", # optional
+ "user_name": "Steve Place", # optional
+ "user_email": "steve@place.org", # optional
+}
+```
diff --git a/drivers/rhombus/security_interop.cr b/drivers/rhombus/security_interop.cr
new file mode 100644
index 00000000000..2bab9e3942d
--- /dev/null
+++ b/drivers/rhombus/security_interop.cr
@@ -0,0 +1,98 @@
+require "http"
+require "placeos-driver"
+require "./security_interop_models"
+
+class Rhombus::SecurityInterop < PlaceOS::Driver
+ descriptive_name "Rhombus Security Interop"
+ generic_name :RhombusSecurity
+ description %(provides an interface for rhombus and local security platforms.)
+
+ default_settings({
+ debug_webhook: false,
+ organization_id: "event",
+ })
+
+ @debug_webhook : Bool = false
+ @subscriptions : Array(Subscription) = [] of Subscription
+ @event_count : UInt64 = 0_u64
+
+ def on_update
+ subscriptions.clear
+ org_id = setting?(String, :organization_id) || "event"
+ monitor("security/#{org_id}/door") { |_subscription, payload| door_event(payload) }
+ @subscriptions = setting?(Array(Subscription), :subscriptions) || [] of Subscription
+ @debug_webhook = setting?(Bool, :debug_webhook) || false
+ end
+
+ protected def security
+ system.implementing(Interface::DoorSecurity)
+ end
+
+ def request(method : String, headers : Hash(String, Array(String)), body : String)
+ logger.debug { "webhook received: #{method},\nheaders #{headers},\nbody size #{body.size}" }
+ logger.debug { body } if @debug_webhook
+
+ case method.downcase
+ when "post"
+ # new subscription
+ @subscriptions << Subscription.from_json(body)
+ define_setting(:subscriptions, @subscriptions)
+ {HTTP::Status::CREATED.to_i, {} of String => String, ""}
+ when "delete"
+ # delete subscription
+ sub_webhook = Subscription.from_json(body).webhook
+ @subscriptions.reject! { |sub| sub.webhook == sub_webhook }
+ define_setting(:subscriptions, @subscriptions)
+ {HTTP::Status::ACCEPTED.to_i, {} of String => String, ""}
+ when "get"
+ # return the list of doors
+ all_doors = [] of JSON::Any
+ security.door_list.get.each do |doors|
+ all_doors.concat doors.as_a
+ end
+ {HTTP::Status::OK.to_i, {"Content-Type" => "application/json"}, {
+ doors: all_doors,
+ }.to_json}
+ when "put"
+ # unlock a door
+ door = Interface::DoorSecurity::Door.from_json(body).door_id
+ case security.unlock(door).get.first.as_bool?
+ in true
+ {HTTP::Status::OK.to_i, {} of String => String, ""}
+ in false
+ {HTTP::Status::FORBIDDEN.to_i, {} of String => String, ""}
+ in nil
+ {HTTP::Status::NOT_IMPLEMENTED.to_i, {} of String => String, ""}
+ end
+ else
+ {HTTP::Status::BAD_REQUEST.to_i, {"Content-Type" => "application/json"}, {error: "unexpected HTTP request method: #{method}"}.to_json}
+ end
+ rescue error
+ logger.warn(exception: error) { "processing webhook request" }
+ {HTTP::Status::INTERNAL_SERVER_ERROR.to_i, {"Content-Type" => "application/json"}, error.message.to_s}
+ end
+
+ @[Security(Level::Administrator)]
+ def door_event(json : String)
+ logger.debug { "new door event detected: #{json}" }
+ webhook = Webhook.new Interface::DoorSecurity::DoorEvent.from_json(json)
+ @event_count += 1_u64
+
+ @subscriptions.each do |sub|
+ begin
+ logger.debug { "notifying webhook of new door event: #{sub.webhook}" }
+ webhook.sign(sub.secret)
+ response = HTTP::Client.post(
+ sub.webhook,
+ HTTP::Headers{"Content-Type" => "application/json"},
+ webhook.to_json
+ )
+ logger.warn { "request #{sub.webhook} failed with status: #{response.status_code}\n#{response.body}" } unless response.success?
+ rescue error
+ logger.error(exception: error) { "failed to notify subscription: #{sub.webhook}" }
+ end
+ end
+
+ self[:event_count] = @event_count
+ end
+end
diff --git a/drivers/rhombus/security_interop_models.cr b/drivers/rhombus/security_interop_models.cr
new file mode 100644
index 00000000000..18d31bb1363
--- /dev/null
+++ b/drivers/rhombus/security_interop_models.cr
@@ -0,0 +1,46 @@
+require "json"
+require "openssl/hmac"
+require "placeos-driver/interface/door_security"
+
+module Rhombus
+ class Subscription
+ include JSON::Serializable
+
+ getter webhook : String
+ getter secret : String?
+
+ def initialize(@webhook, @secret = nil)
+ end
+ end
+
+ class Webhook
+ include JSON::Serializable
+
+ getter door_id : String
+ getter timestamp : Time
+ getter signature : String? = nil
+ getter action : PlaceOS::Driver::Interface::DoorSecurity::Action
+ getter card_id : String?
+ getter user_name : String?
+ getter user_email : String?
+
+ def initialize(event : PlaceOS::Driver::Interface::DoorSecurity::DoorEvent)
+ @action = event.action
+ @door_id = event.door_id
+ @timestamp = Time.unix event.timestamp
+
+ @card_id = event.card_id
+ @user_name = event.user_name
+ @user_email = event.user_email
+ end
+
+ def sign(secret : String?)
+ if key = secret.presence
+ @signature = OpenSSL::HMAC.hexdigest(:sha256, key, timestamp.to_rfc3339)
+ else
+ @signature = nil
+ end
+ self
+ end
+ end
+end
diff --git a/drivers/rhombus/security_interop_spec.cr b/drivers/rhombus/security_interop_spec.cr
new file mode 100644
index 00000000000..b237a8f1d9c
--- /dev/null
+++ b/drivers/rhombus/security_interop_spec.cr
@@ -0,0 +1,68 @@
+require "placeos-driver/spec"
+require "placeos-driver/interface/door_security"
+
+DriverSpecs.mock_driver "Rhombus::SecurityInterop" do
+ system({
+ SecuritySystem: {DoorSecurityMock},
+ })
+
+ settings({
+ debug_webhook: true,
+ subscriptions: [{
+ # spec ports
+ webhook: URI.new("http", "127.0.0.1", __get_ports__[1]).to_s,
+ }],
+ })
+
+ # test notifying of a door event
+ timestamp = Time.utc
+ exec(:door_event, {
+ module_id: "testing",
+ security_system: "testing",
+ door_id: "the-door",
+ timestamp: timestamp.to_unix,
+ action: "RequestToExit",
+ }.to_json)
+
+ webhook = nil
+ expect_http_request do |request, response|
+ webhook = request.body.not_nil!.gets_to_end
+ response.status_code = 200
+ end
+
+ raise "no webhook payload" unless webhook
+
+ JSON.parse(webhook.not_nil!).should eq({
+ "door_id" => "the-door",
+ "timestamp" => timestamp.to_rfc3339,
+ "action" => "request_to_exit",
+ })
+
+ # test listing of doors
+ resp = exec(:request, "GET", {} of String => Array(String), "").get.not_nil!
+ JSON.parse(resp[2].as_s).should eq({
+ "doors" => [{
+ "door_id" => "testing",
+ }],
+ })
+
+ # test unlocking a door
+ resp = exec(:request, "PUT", {} of String => Array(String), %({"door_id": "some-door"})).get.not_nil!
+ resp[0].should eq(200)
+
+ system(:SecuritySystem_1)[:last_unlocked].should eq "some-door"
+end
+
+# :nodoc:
+class DoorSecurityMock < DriverSpecs::MockDriver
+ include PlaceOS::Driver::Interface::DoorSecurity
+
+ def door_list : Array(Door)
+ [Door.new("testing")]
+ end
+
+ def unlock(door_id : String) : Bool?
+ self[:last_unlocked] = door_id
+ true
+ end
+end
diff --git a/drivers/rhombus/security_mock.cr b/drivers/rhombus/security_mock.cr
new file mode 100644
index 00000000000..633d8b20bab
--- /dev/null
+++ b/drivers/rhombus/security_mock.cr
@@ -0,0 +1,85 @@
+require "json"
+require "faker"
+require "placeos-driver"
+require "placeos-driver/interface/door_security"
+
+class Rhombus::SecurityMock < PlaceOS::Driver
+ descriptive_name "Rhombus Mock Security System"
+ generic_name :SecurityMock
+ description %(a mock security system for interface testing)
+
+ include PlaceOS::Driver::Interface::DoorSecurity
+
+ default_settings({
+ door_list_size: 30,
+ swipe_event_every: 30,
+ })
+
+ record CardUser, card_id : String, user_name : String, user_email : String do
+ include JSON::Serializable
+ end
+
+ getter door_list : Array(Door) = [] of Door
+ getter card_holders : Array(CardUser) = [] of CardUser
+
+ def on_update
+ # ensure door names and IDs don't change between reloads
+ door_list_size = setting?(Int32, :door_list_size) || 30
+ Faker.seed door_list_size
+ door_id = 1000
+
+ doors = Array(Door).new(door_list_size)
+ door_list_size.times do
+ doors << Door.new(
+ door_id.to_s,
+ Faker::Commerce.department
+ )
+ door_id += 1
+ end
+ @door_list = doors
+
+ # generate some card holders
+ @card_holders = (0..10).map do
+ CardUser.new(
+ Faker::Business.credit_card_number,
+ Faker::Name.name,
+ Faker::Internet.safe_email
+ )
+ end
+
+ # Trigger regular swipe events
+ swipe_event_period = setting?(Int32, :swipe_event_every) || 30
+ schedule.clear
+ schedule.every(swipe_event_period.seconds) do
+ door = doors.sample
+ action = Action::Granted
+
+ case rand(6)
+ when 0, 1, 2
+ user = card_holders.sample
+ when 3
+ action = Action::Denied
+ user = card_holders.sample
+ when 4
+ action = Action::Tamper
+ when 5
+ action = Action::RequestToExit
+ end
+
+ publish("security/event/door", DoorEvent.new(
+ module_id: module_id,
+ security_system: "mock",
+ door_id: door.door_id,
+ action: action,
+ card_id: user.try &.card_id,
+ user_name: user.try &.user_name,
+ user_email: user.try &.user_email
+ ).to_json)
+ end
+ end
+
+ def unlock(door_id : String) : Bool?
+ self[:last_unlocked] = door_id
+ true
+ end
+end
diff --git a/drivers/samsung/displays/mdc_protocol.cr b/drivers/samsung/displays/mdc_protocol.cr
new file mode 100644
index 00000000000..43d22d9505b
--- /dev/null
+++ b/drivers/samsung/displays/mdc_protocol.cr
@@ -0,0 +1,365 @@
+require "placeos-driver"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/switchable"
+
+class Samsung::Displays::MDCProtocol < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Muteable
+
+ INDICATOR = 0xAA_u8
+
+ enum Input
+ Vga = 0x14 # pc in manual
+ Dvi = 0x18
+ DviVideo = 0x1F
+ Hdmi = 0x21
+ HdmiPc = 0x22
+ Hdmi2 = 0x23
+ Hdmi2Pc = 0x24
+ Hdmi3 = 0x31
+ Hdmi3Pc = 0x32
+ Hdmi4 = 0x33
+ Hdmi4Pc = 0x34
+ DisplayPort = 0x25
+ Dtv = 0x40
+ Media = 0x60
+ Widi = 0x61
+ MagicInfo = 0x20
+ Whiteboard = 0x64
+ end
+
+ include Interface::InputSelection(Input)
+
+ # Discovery Information
+ tcp_port 1515
+ descriptive_name "Samsung MD, DM & QM Series LCD"
+ generic_name :Display
+
+ # Markdown description
+ description <<-DESC
+ For DM displays configure the following 1:
+
+ 1. Network Standby = ON
+ 2. Set Auto Standby = OFF
+ 3. Set Eco Solution, Auto Off = OFF
+
+ Hard Power off displays each night and hard power ON in the morning.
+ DESC
+
+ default_settings({
+ display_id: 0,
+ rs232_control: false,
+ })
+
+ @id : UInt8 = 0
+ @rs232 : Bool = false
+ @blank : Input?
+ @previous_volume : Int32 = 50
+ @input_target : Input? = nil
+ @power_target : Bool? = nil
+
+ def on_load
+ transport.tokenizer = Tokenizer.new do |io|
+ bytes = io.peek
+ logger.debug { "Received: #{bytes.hexstring}" }
+
+ # Ensure message indicator is well-formed
+ if bytes.first == INDICATOR
+ # [header, command, id, data.size, [data], checksum]
+ # return 0 if the message is incomplete
+ bytes.size < 4 ? 0 : bytes[3].to_i + 5
+ else
+ logger.debug { "Ignoring unexpected message" }
+ io.clear
+ 0
+ end
+ end
+
+ on_update
+ end
+
+ def on_update
+ @id = setting(UInt8, :display_id)
+ @rs232 = setting(Bool, :rs232_control)
+ @blank = setting?(String, :blanking_input).try &->Input.parse(String)
+ end
+
+ def connected
+ do_device_config unless self[:hard_off]?.try &.as_bool
+
+ schedule.every(30.seconds, true) do
+ do_poll
+ end
+ end
+
+ def disconnected
+ self[:power] = false unless @rs232
+ schedule.clear
+ end
+
+ # As true power off disconnects the server we only want to power off the panel
+ def power(state : Bool)
+ @power_target = state
+
+ if state
+ # Power on
+ do_send(Command::HardOff, 1)
+ do_send(Command::PanelMute, 0)
+ else
+ # Blank the screen before turning off panel if required
+ # required by some video walls where screens are chained
+ if (blanking_input = @blank) && self[:power]?
+ switch_to(blanking_input)
+ end
+ do_send(Command::PanelMute, 1)
+ end
+ end
+
+ def hard_off
+ do_send(Command::PanelMute, 0) if self[:power]?.try &.as_bool
+ do_send(Command::HardOff, 0)
+ end
+
+ def power?(**options) : Bool
+ do_send(Command::PanelMute, Bytes.empty, **options).get
+ !!self[:power]?.try(&.as_bool)
+ end
+
+ # Mutes both audio/video
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ mute_video(state) if layer.video? || layer.audio_video?
+ mute_audio(state) if layer.audio? || layer.audio_video?
+ end
+
+ # Adds video mute state compatible with projectors
+ def mute_video(state : Bool = true)
+ state = state ? 1 : 0
+ do_send(Command::PanelMute, state)
+ end
+
+ # Emulate audio mute
+ def mute_audio(state : Bool = true)
+ # Do nothing if already in desired state
+ return if self[:audio_mute]?.try(&.as_bool) == state
+ self[:audio_mute] = state
+ if state
+ @previous_volume = self[:volume]?.try(&.as_i) || 0
+ volume(0)
+ else
+ volume(@previous_volume)
+ end
+ end
+
+ # check software version
+ def software_version
+ do_send(Command::SoftwareVersion)
+ end
+
+ def serial_number
+ do_send(Command::SerialNumber)
+ end
+
+ def switch_to(input : Input, **options)
+ @input_target = input
+ do_send(Command::Input, input.value, **options)
+ end
+
+ enum SpeakerMode
+ Internal = 0
+ External = 1
+ end
+
+ def speaker_select(mode : SpeakerMode, **options)
+ do_send(Command::Speaker, mode.value, **options)
+ end
+
+ def do_poll
+ do_send(Command::Status, Bytes.empty, priority: 0)
+ power? unless self[:hard_off]?.try &.as_bool
+ end
+
+ alias Num = Int32 | Float64
+
+ DEVICE_SETTINGS = {
+ network_standby: Bool,
+ auto_off_timer: Bool,
+ auto_power: Bool,
+ volume: Num,
+ contrast: Num,
+ brightness: Num,
+ sharpness: Num,
+ colour: Num,
+ tint: Num,
+ red_gain: Num,
+ green_gain: Num,
+ blue_gain: Num,
+ }
+ {% for name, kind in DEVICE_SETTINGS %}
+ @[Security(Level::Administrator)]
+ def {{name.id}}(value : {{kind}}, **options)
+ {% if kind.resolve == Bool %}
+ state = value ? 1 : 0
+ data = {{name.id.stringify}} == "auto_off_timer" ? Bytes[0x81, state] : state
+ {% else %}
+ data = value.to_f.clamp(0.0, 100.0).round_away.to_i
+ {% end %}
+ do_send(Command.parse({{name.id.stringify}}), data, **options)
+ end
+ {% end %}
+
+ def do_device_config
+ {% for name, kind in DEVICE_SETTINGS %}
+ %value = setting?({{kind}}, {{name.id.stringify}})
+ {{name.id}}(%value) if %value
+ {% end %}
+ end
+
+ def volume_up
+ current_volume = status?(Float64, :volume) || 50.0
+ volume(current_volume + 5.0)
+ end
+
+ def volume_down
+ current_volume = status?(Float64, :volume) || 50.0
+ volume(current_volume - 5.0)
+ end
+
+ enum ResponseStatus
+ Ack = 0x41 # A
+ Nak = 0x4e # N
+ end
+
+ def received(data, task)
+ hex = data.hexstring
+ logger.debug { "Samsung sent: #{hex}" }
+
+ # Verify the checksum of the response
+ if data[-1] != (checksum = data[1..-2].sum(0) & 0xFF)
+ logger.error { "Invalid response, checksum should be: #{checksum.to_s(16)}" }
+ return task.try &.retry
+ end
+
+ status = ResponseStatus.from_value(data[4])
+ command = Command.from_value(data[5])
+ values = data[6..-2]
+ value = values.first
+
+ case status
+ when .ack?
+ case command
+ when .status?
+ self[:hard_off] = hard_off = values[0] == 0
+ self[:power] = false if hard_off
+ self[:volume] = values[1]
+ self[:audio_mute] = values[2] == 1
+ self[:input] = Input.from_value(values[3])
+ check_power_state
+ when .panel_mute?
+ self[:power] = value == 0
+ check_power_state
+ when .volume?
+ self[:volume] = value
+ self[:audio_mute] = false if value > 0
+ when .brightness?
+ self[:brightness] = value
+ when .input?
+ current_input = Input.from_value(value)
+ self[:input] = current_input
+ # The input feedback behaviour seems to go a little odd when
+ # screen split is active. Ignore any input forcing when on.
+ unless self[:screen_split]?.try &.as_bool
+ if current_input == @input_target
+ @input_target = nil
+ elsif input_target = @input_target
+ switch_to(input_target)
+ end
+ end
+ when .speaker?
+ self[:speaker] = SpeakerMode.from_value(value)
+ when .hard_off?
+ unless self[:hard_off]?.try &.as_bool
+ self[:hard_off] = hard_off = value == 0
+ self[:power] = false if hard_off
+ end
+ when .screen_split?
+ self[:screen_split] = value >= 0
+ when .software_version?
+ self[:software_version] = values.join
+ when .serial_number?
+ self[:serial_number] = values.join
+ else
+ logger.debug { "Samsung responded with ACK: #{value}" }
+ end
+
+ task.try &.success
+ when .nak?
+ task.try &.abort("Samsung responded with NAK: #{hex}")
+ else
+ task.try &.retry
+ end
+ end
+
+ private def check_power_state
+ if self[:power]? == @power_target
+ @power_target = nil
+ elsif power_target = @power_target
+ power(power_target)
+ end
+ end
+
+ enum Command : UInt8
+ Status = 0x00
+ HardOff = 0x11 # Completely powers off
+ PanelMute = 0xF9 # Screen blanking / visual mute
+ Volume = 0x12
+ Contrast = 0x24
+ Brightness = 0x25
+ Sharpness = 0x26
+ Colour = 0x27
+ Tint = 0x28
+ RedGain = 0x29
+ GreenGain = 0x2A
+ BlueGain = 0x2B
+ Input = 0x14
+ Mode = 0x18
+ Size = 0x19
+ Pip = 0x3C # picture in picture
+ AutoAdjust = 0x3D
+ WallMode = 0x5C # Video wall mode
+ Safety = 0x5D
+ WallOn = 0x84 # Video wall enabled
+ WallUser = 0x89 # Video wall user control
+ Speaker = 0x68
+ NetworkStandby = 0xB5 # Keep NIC active in standby, enable power on (without WOL)
+ AutoOffTimer = 0xE6 # Eco options (auto power off)
+ AutoPower = 0x33 # Device auto power control (presumably signal based?)
+ ScreenSplit = 0xB2 # Tri / quad split (larger panels only)
+ SoftwareVersion = 0x0E
+ SerialNumber = 0x0B
+ Time = 0xA7
+ Timer = 0xA4
+
+ def build(id : UInt8, data : Bytes) : Bytes
+ Bytes.new(data.size + 5).tap do |bytes|
+ bytes[0] = INDICATOR # Header
+ bytes[1] = self.value # Command
+ bytes[2] = id # Display ID
+ bytes[3] = data.size.to_u8 # Data size
+ data.each_with_index(4) { |b, i| bytes[i] = b } # Data
+ bytes[-1] = (bytes[1..-2].sum(0) & 0xFF).to_u8 # Checksum
+ end
+ end
+ end
+
+ private def do_send(command : Command, data : Int | Bytes = Bytes.empty, **options)
+ data = Bytes[data] if data.is_a?(Int)
+ bytes = command.build(@id, data)
+ logger.debug { "Sending to Samsung: #{bytes.hexstring}" }
+ send(bytes, **options)
+ end
+end
diff --git a/drivers/samsung/displays/mdc_protocol_spec.cr b/drivers/samsung/displays/mdc_protocol_spec.cr
new file mode 100644
index 00000000000..8f1e8761e94
--- /dev/null
+++ b/drivers/samsung/displays/mdc_protocol_spec.cr
@@ -0,0 +1,67 @@
+require "placeos-driver/spec"
+
+# [header, command, id, data.size, [data], checksum]
+
+DriverSpecs.mock_driver "Samsung::Displays::MDCProtocol" do
+ id = "\x00"
+
+ # connected -> do_poll
+ # power? will take priority over status as status has priority = 0
+ # power? -> panel_mute
+ should_send("\xAA\xF9#{id}\x00\xF9")
+ responds("\xAA\xFF#{id}\x03A\xF9\x00\x3C")
+ status[:power].should eq(true)
+ # status
+ should_send("\xAA\x00#{id}\x00\x00")
+ responds("\xAA\xFF#{id}\x09A\x00\x01\x06\x00\x14\x00\x00\x00\x64")
+ status[:hard_off].should eq(false)
+ status[:power].should eq(true)
+ status[:volume].should eq(6)
+ status[:audio_mute].should eq(false)
+ status[:input].should eq("Vga")
+
+ exec(:volume, 24)
+ should_send("\xAA\x12#{id}\x01\x18\x2B")
+ responds("\xAA\xFF#{id}\x03A\x12\x18\x6D")
+ status[:volume].should eq(24)
+ status[:audio_mute].should eq(false)
+
+ exec(:volume, 6)
+ should_send("\xAA\x12#{id}\x01\x06\x19")
+ responds("\xAA\xFF#{id}\x03A\x12\x06\x5B")
+ status[:volume].should eq(6)
+ status[:audio_mute].should eq(false)
+
+ exec(:mute)
+ # Video mute
+ should_send("\xAA\xF9#{id}\x01\x01\xFB")
+ responds("\xAA\xFF#{id}\x03A\xF9\x01\x3D")
+ status[:power].should eq(false)
+ # Audio mute
+ should_send("\xAA\x12#{id}\x01\x00\x13")
+ responds("\xAA\xFF\x00\x03A\x12\x00\x55")
+ status[:audio_mute].should eq(true)
+ status[:volume].should eq(0)
+
+ exec(:unmute)
+ # Video unmute
+ should_send("\xAA\xF9#{id}\x01\x00\xFA")
+ responds("\xAA\xFF#{id}\x03A\xF9\x00\x3C")
+ status[:power].should eq(true)
+ # Audio unmute
+ should_send("\xAA\x12#{id}\x01\x06\x19")
+ responds("\xAA\xFF#{id}\x03A\x12\x06\x5B")
+ status[:audio_mute].should eq(false)
+ status[:volume].should eq(6)
+
+ exec(:switch_to, "hdmi")
+ should_send("\xAA\x14#{id}\x01\x21\x36")
+ responds("\xAA\xFF#{id}\x03A\x14\x21\x78")
+ status[:input].should eq("Hdmi")
+
+ # power(false) == video_mute(true)
+ exec(:power, false)
+ should_send("\xAA\xF9#{id}\x01\x01\xFB")
+ responds("\xAA\xFF#{id}\x03A\xF9\x01\x3D")
+ status[:power].should eq(false)
+end
diff --git a/drivers/samsung/displays/reduced_mdc_protocol.cr b/drivers/samsung/displays/reduced_mdc_protocol.cr
new file mode 100644
index 00000000000..45a65dbeb16
--- /dev/null
+++ b/drivers/samsung/displays/reduced_mdc_protocol.cr
@@ -0,0 +1,290 @@
+require "placeos-driver"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/switchable"
+
+class Samsung::Displays::ReducedMDCProtocol < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Muteable
+
+ INDICATOR = 0xAA_u8
+
+ enum Input
+ Vga = 0x14 # pc in manual
+ Dvi = 0x18
+ DviVideo = 0x1F
+ Hdmi = 0x21
+ HdmiPc = 0x22
+ Hdmi2 = 0x23
+ Hdmi2Pc = 0x24
+ Hdmi3 = 0x31
+ Hdmi3Pc = 0x32
+ Hdmi4 = 0x33
+ Hdmi4Pc = 0x34
+ DisplayPort = 0x25
+ Dtv = 0x40
+ Media = 0x60
+ Widi = 0x61
+ MagicInfo = 0x20
+ Whiteboard = 0x64
+ end
+
+ include Interface::InputSelection(Input)
+
+ # Discovery Information
+ tcp_port 1515
+ descriptive_name "Samsung Simplified Control Set"
+ generic_name :Display
+
+ # Markdown description
+ description <<-DESC
+ For DM displays configure the following 1:
+
+ 1. Network Standby = ON
+ 2. Set Auto Standby = OFF
+ 3. Set Eco Solution, Auto Off = OFF
+
+ Hard Power off displays each night and hard power ON in the morning.
+ DESC
+
+ default_settings({
+ display_id: 0,
+ rs232_control: false,
+ })
+
+ @id : UInt8 = 0
+ @rs232 : Bool = false
+ @blank : Input?
+ @previous_volume : Int32 = 50
+ @input_target : Input? = nil
+ @whiteboard_clear_input : Input? = nil
+ @power_target : Bool? = nil
+
+ def on_load
+ transport.tokenizer = Tokenizer.new do |io|
+ bytes = io.peek
+ logger.debug { "Received: #{bytes.hexstring}" }
+
+ # Ensure message indicator is well-formed
+ if bytes.first == INDICATOR
+ # [header, command, id, data.size, [data], checksum]
+ # return 0 if the message is incomplete
+ bytes.size < 4 ? 0 : bytes[3].to_i + 5
+ else
+ logger.debug { "Ignoring unexpected message" }
+ io.clear
+ 0
+ end
+ end
+
+ on_update
+ end
+
+ def on_update
+ @id = setting(UInt8, :display_id)
+ @rs232 = setting(Bool, :rs232_control)
+ if clear_input = setting?(String, :whiteboard_clear_input)
+ @whiteboard_clear_input = Input.parse(clear_input)
+ else
+ @whiteboard_clear_input = nil
+ end
+ end
+
+ def connected
+ schedule.every(30.seconds, true) do
+ do_poll
+ end
+ end
+
+ def disconnected
+ self[:power] = false unless @rs232
+ schedule.clear
+ end
+
+ # As true power off disconnects the server we only want to power off the panel
+ def power(state : Bool)
+ @power_target = state
+ do_send(Command::HardOff, state ? 1 : 0)
+ end
+
+ def hard_off
+ do_send(Command::HardOff, 0)
+ end
+
+ def power?(**options) : Bool
+ do_send(Command::HardOff, Bytes.empty, **options).get
+ !!self[:power]?.try(&.as_bool)
+ end
+
+ # Mutes both audio/video
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ mute_audio(state) if layer.audio? || layer.audio_video?
+ end
+
+ # Emulate audio mute
+ def mute_audio(state : Bool = true)
+ # Do nothing if already in desired state
+ return if self[:audio_mute]?.try(&.as_bool) == state
+ self[:audio_mute] = state
+ if state
+ @previous_volume = self[:volume]?.try(&.as_i) || 0
+ volume(0)
+ else
+ volume(@previous_volume)
+ end
+ end
+
+ def switch_to(input : Input, **options)
+ @input_target = input
+ do_send(Command::Input, input.value, **options)
+ end
+
+ # if the user has been using the display as a whiteboard
+ # then the display needs to switch input
+ def clear_whiteboard
+ target_input = @input_target
+ clear_input = @whiteboard_clear_input
+ if target_input && clear_input
+ switch_to(clear_input).get
+ switch_to target_input
+ end
+ end
+
+ def do_poll
+ if power?
+ # not even the input query is supported
+ # do_send(Command::Input, Bytes.empty, priority: 0)
+ do_send(Command::Volume, Bytes.empty, priority: 0)
+ end
+ end
+
+ def do_device_config
+ value = setting?(Int32 | Float64, :volume)
+ volume(value) if value
+ end
+
+ def volume(value : Int32 | Float64, **options)
+ data = value.to_f.clamp(0.0, 100.0).round_away.to_i
+ do_send(Command::Volume, data, **options)
+ end
+
+ def volume_up
+ current_volume = status?(Float64, :volume) || 50.0
+ volume(current_volume + 5.0)
+ end
+
+ def volume_down
+ current_volume = status?(Float64, :volume) || 50.0
+ volume(current_volume - 5.0)
+ end
+
+ enum ResponseStatus
+ Ack = 0x41 # A
+ Nak = 0x4e # N
+ end
+
+ def received(data, task)
+ hex = data.hexstring
+ logger.debug { "Samsung sent: #{hex}" }
+
+ # Verify the checksum of the response
+ if data[-1] != (checksum = data[1..-2].sum(0) & 0xFF)
+ logger.error { "Invalid response, checksum should be: #{checksum.to_s(16)}" }
+ return task.try &.retry
+ end
+
+ status = ResponseStatus.from_value(data[4])
+ command = Command.from_value(data[5])
+ values = data[6..-2]
+ value = values.first
+
+ case status
+ when .ack?
+ case command
+ when .volume?
+ self[:volume] = value
+ self[:audio_mute] = false if value > 0
+ when .input?
+ current_input = Input.from_value(value)
+ self[:input] = current_input
+ when .hard_off?
+ self[:power] = value != 0
+ check_power_state
+ else
+ logger.debug { "Samsung responded with ACK: #{value}" }
+ end
+
+ task.try &.success
+ when .nak?
+ task.try &.abort("Samsung responded with NAK: #{hex}")
+ else
+ task.try &.retry
+ end
+ end
+
+ private def check_power_state
+ power_target = @power_target
+ return if power_target.nil?
+
+ if self[:power]? == power_target
+ @power_target = nil
+ else
+ power(power_target)
+ end
+ end
+
+ enum Command : UInt8
+ Status = 0x00
+ HardOff = 0x11 # Completely powers off
+ PanelMute = 0xF9 # Screen blanking / visual mute
+ Volume = 0x12
+ Contrast = 0x24
+ Brightness = 0x25
+ Sharpness = 0x26
+ Colour = 0x27
+ Tint = 0x28
+ RedGain = 0x29
+ GreenGain = 0x2A
+ BlueGain = 0x2B
+ Input = 0x14
+ Mode = 0x18
+ Size = 0x19
+ Pip = 0x3C # picture in picture
+ AutoAdjust = 0x3D
+ WallMode = 0x5C # Video wall mode
+ Safety = 0x5D
+ WallOn = 0x84 # Video wall enabled
+ WallUser = 0x89 # Video wall user control
+ Speaker = 0x68
+ NetworkStandby = 0xB5 # Keep NIC active in standby, enable power on (without WOL)
+ AutoOffTimer = 0xE6 # Eco options (auto power off)
+ AutoPower = 0x33 # Device auto power control (presumably signal based?)
+ ScreenSplit = 0xB2 # Tri / quad split (larger panels only)
+ SoftwareVersion = 0x0E
+ SerialNumber = 0x0B
+ Time = 0xA7
+ Timer = 0xA4
+
+ def build(id : UInt8, data : Bytes) : Bytes
+ Bytes.new(data.size + 5).tap do |bytes|
+ bytes[0] = INDICATOR # Header
+ bytes[1] = self.value # Command
+ bytes[2] = id # Display ID
+ bytes[3] = data.size.to_u8 # Data size
+ data.each_with_index(4) { |b, i| bytes[i] = b } # Data
+ bytes[-1] = (bytes[1..-2].sum(0) & 0xFF).to_u8 # Checksum
+ end
+ end
+ end
+
+ private def do_send(command : Command, data : Int | Bytes = Bytes.empty, **options)
+ data = Bytes[data] if data.is_a?(Int)
+ bytes = command.build(@id, data)
+ logger.debug { "Sending to Samsung: #{bytes.hexstring}" }
+ send(bytes, **options)
+ end
+end
diff --git a/drivers/samsung/displays/reduced_mdc_protocol_spec.cr b/drivers/samsung/displays/reduced_mdc_protocol_spec.cr
new file mode 100644
index 00000000000..98c94158ad7
--- /dev/null
+++ b/drivers/samsung/displays/reduced_mdc_protocol_spec.cr
@@ -0,0 +1,50 @@
+require "placeos-driver/spec"
+
+# [header, command, id, data.size, [data], checksum]
+
+DriverSpecs.mock_driver "Samsung::Displays::ReducedMDCProtocol" do
+ id = "\x00"
+
+ # connected -> do_poll
+ # power? will take priority over status as status has priority = 0
+ # power? -> panel_mute
+ should_send("\xAA\x11#{id}\x00\x11")
+ responds("\xAA\xFF#{id}\x03A\x11\x00\x54")
+ status[:power].should eq(false)
+
+ exec(:power, true)
+ should_send("\xAA\x11#{id}\x01\x01\x13")
+ responds("\xAA\xFF#{id}\x03A\x11\x01\x55")
+ status[:power].should eq(true)
+
+ exec(:volume, 24)
+ should_send("\xAA\x12#{id}\x01\x18\x2B")
+ responds("\xAA\xFF#{id}\x03A\x12\x18\x6D")
+ status[:volume].should eq(24)
+ status[:audio_mute].should eq(false)
+
+ exec(:volume, 6)
+ should_send("\xAA\x12#{id}\x01\x06\x19")
+ responds("\xAA\xFF#{id}\x03A\x12\x06\x5B")
+ status[:volume].should eq(6)
+ status[:audio_mute].should eq(false)
+
+ exec(:mute)
+ # Audio mute
+ should_send("\xAA\x12#{id}\x01\x00\x13")
+ responds("\xAA\xFF\x00\x03A\x12\x00\x55")
+ status[:audio_mute].should eq(true)
+ status[:volume].should eq(0)
+
+ exec(:unmute)
+ # Audio unmute
+ should_send("\xAA\x12#{id}\x01\x06\x19")
+ responds("\xAA\xFF#{id}\x03A\x12\x06\x5B")
+ status[:audio_mute].should eq(false)
+ status[:volume].should eq(6)
+
+ exec(:switch_to, "hdmi")
+ should_send("\xAA\x14#{id}\x01\x21\x36")
+ responds("\xAA\xFF#{id}\x03A\x14\x21\x78")
+ status[:input].should eq("Hdmi")
+end
diff --git a/drivers/screen_technics/connect.cr b/drivers/screen_technics/connect.cr
new file mode 100644
index 00000000000..c0eabcf27ce
--- /dev/null
+++ b/drivers/screen_technics/connect.cr
@@ -0,0 +1,181 @@
+require "placeos-driver"
+require "placeos-driver/interface/moveable"
+require "placeos-driver/interface/stoppable"
+
+# Documentation: https://aca.im/driver_docs/Screen%20Technics/Screen%20Technics%20IP%20Connect%20module.pdf
+# Default user: Admin
+# Default pass: Connect
+
+class ScreenTechnics::Connect < PlaceOS::Driver
+ include Interface::Moveable
+ include Interface::Stoppable
+
+ # Discovery Information
+ descriptive_name "Screen Technics Projector Screen Control"
+ generic_name :Screen
+ tcp_port 3001
+
+ COMMANDS = {
+ up: 30,
+ down: 33,
+ status: 1, # this differs from the doc, but appears to work
+ stop: 36,
+ }
+
+ CMD_LOOKUP = {
+ 30 => :up,
+ 33 => :down,
+ 1 => :status,
+ 36 => :stop,
+ }
+
+ def on_load
+ # Communication settings
+ queue.delay = 500.milliseconds
+ transport.tokenizer = Tokenizer.new("\r\n")
+
+ on_update
+ end
+
+ def on_update
+ @count = setting?(Int32, :screen_count) || 1
+ end
+
+ def connected
+ schedule.every(15.seconds, immediate: true) {
+ (0...@count).each { |index| query_state(index) }
+ }
+ end
+
+ def disconnected
+ queue.clear
+ schedule.clear
+ end
+
+ def move(position : MoveablePosition, index : Int32 | String = 0)
+ index = index.to_i
+
+ case position
+ when MoveablePosition::Up
+ up(index)
+ when MoveablePosition::Down
+ down(index)
+ else
+ raise "invalid position requested"
+ end
+ end
+
+ def down(index : Int32 = 0)
+ return if down?(index)
+ stop(index)
+ do_send :down, index, name: "direction#{index}"
+ query_state(index)
+ end
+
+ def down?(index : Int32 = 0)
+ {"moving_bottom", "at_bottom"}.includes?(self["screen#{index}"]?)
+ end
+
+ def up(index : Int32 = 0)
+ return if up?(index)
+ stop(index)
+ do_send :up, index, name: "direction#{index}"
+ query_state(index)
+ end
+
+ def up?(index : Int32 = 0)
+ {"moving_top", "at_top"}.includes?(self["screen#{index}"]?)
+ end
+
+ def stop(index : Int32 | String = 0, emergency : Bool = false)
+ index = index.to_i
+
+ do_send(
+ :stop, index,
+ name: "stop#{index}",
+ clear_queue: emergency,
+ priority: emergency ? (queue.priority + 50) : queue.priority
+ )
+ end
+
+ def query_state(index : Int32 = 0)
+ do_send :status, index, 0x20
+ end
+
+ STATUS = {
+ 0 => :moving_top,
+ 1 => :moving_bottom,
+ 2 => :moving_preset_1,
+ 3 => :moving_preset_2,
+ 4 => :moving_top, # preset top
+ 5 => :moving_bottom, # preset bottom
+ 6 => :at_top,
+ 7 => :at_bottom,
+ 8 => :at_preset_1,
+ 9 => :at_preset_2,
+ 10 => :stopped,
+ 11 => :error,
+ # 12 => undefined
+ 13 => :error_timeout,
+ 14 => :error_current,
+ 15 => :error_rattle,
+ 16 => :at_bottom, # preset bottom
+ }
+
+ def received(data, task)
+ data = String.new(data)
+ logger.debug { "Screen sent #{data}" }
+
+ # Builds an array of numbers from the returned string
+ parts = data.split(/,/).map &.strip.to_i
+ cmd = CMD_LOOKUP[parts[0] - 100]?
+
+ if cmd
+ index = parts[2] - 17
+
+ case cmd
+ when :up
+ logger.debug { "Screen#{index} moving up" }
+ self["position#{index}"] = MoveablePosition::Up
+ self["moving#{index}"] = true
+ when :down
+ logger.debug { "Screen#{index} moving down" }
+ self["position#{index}"] = MoveablePosition::Down
+ self["moving#{index}"] = true
+ when :stop
+ logger.debug { "Screen#{index} stopped" }
+ self["moving#{index}"] = false
+ screen = "screen#{index}"
+ self[screen] = :stopped unless {"at_top", "at_bottom"}.includes?(self[screen]?)
+ when :status
+ self["screen#{index}"] = status = STATUS[parts[-1]]
+
+ case status
+ when :moving_top, :at_top
+ self["position#{index}"] = MoveablePosition::Up
+ self["moving#{index}"] = status == :moving_top
+ when :moving_bottom, :at_bottom
+ self["position#{index}"] = MoveablePosition::Down
+ self["moving#{index}"] = status == :moving_bottom
+ when :stopped
+ self["moving#{index}"] = false
+ when :error, :error_timeout, :error_current, :error_rattle
+ self["moving#{index}"] = false
+ end
+ end
+
+ task.try &.success
+ else
+ error = "Unknown command #{parts[0]}"
+ logger.debug { error }
+ task.try &.abort(error)
+ end
+ end
+
+ protected def do_send(cmd, index = 0, *args, **options)
+ address = index + 17
+ parts = {COMMANDS[cmd], address} + args
+ request = "#{parts.join(", ")}\r\n"
+ send request, **options
+ end
+end
diff --git a/drivers/screen_technics/connect_spec.cr b/drivers/screen_technics/connect_spec.cr
new file mode 100644
index 00000000000..d57166adab6
--- /dev/null
+++ b/drivers/screen_technics/connect_spec.cr
@@ -0,0 +1,68 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "ScreenTechnics::Connect" do
+ # On connect it queries the state of all screens
+ should_send("1, 17, 32\r\n")
+ responds("101, 1, 17, 1\r\n")
+
+ status[:position0].should eq("Down")
+ status[:moving0].should be_true
+ status[:screen0].should eq("moving_bottom")
+
+ # Screen Technics requires a large delay between requests
+ # The timeout is because this execute won't occur until after a delay
+ exec(:query_state, index: 1) do |ret_val|
+ should_send("1, 18, 32\r\n", timeout: 1.second)
+ responds("101, 1, 18, 6\r\n")
+
+ # Wait for the execute return value
+ ret_val.get
+
+ status[:position1].should eq("Up")
+ status[:moving1].should eq(false)
+ status[:screen1].should eq("at_top")
+ end
+
+ # ===================
+ # Test emergency stop
+ # ===================
+ exec(:move, "Down", 2) do |ret_val|
+ # A call to down involves a
+ # * stop command
+ # * down command
+ # * status request
+ sleep 1.second
+ should_send("36, 19\r\n", timeout: 1.second)
+ responds("136, 1, 19\r\n")
+
+ # --> Wait for the down command
+ should_send("33, 19\r\n", timeout: 1.second)
+
+ # Execute the emergency stop and request another down request
+ exec(:stop, index: 2, emergency: true) do |response|
+ exec(:move, "Down", 2)
+ sleep 500.milliseconds
+
+ # --> respond to the down command
+ responds("133, 1, 19, 1\r\n")
+
+ # Should receive emergency stop command
+ should_send("36, 19\r\n", timeout: 1.second)
+ responds("136, 1, 19\r\n")
+ status[:moving2].should eq(false)
+ response.get
+ end
+
+ # Original down command should have failed
+ expect_raises(PlaceOS::Driver::RemoteException, "queue cleared (Abort)") do
+ ret_val.get
+ end
+
+ puts "(timeout below expected)"
+
+ # Ensure second down command is not sent
+ expect_raises(Channel::ClosedError) do
+ should_send("33, 17\r\n", timeout: 1.second)
+ end
+ end
+end
diff --git a/drivers/secure_os/ws_api.cr b/drivers/secure_os/ws_api.cr
new file mode 100644
index 00000000000..68e29475da0
--- /dev/null
+++ b/drivers/secure_os/ws_api.cr
@@ -0,0 +1,190 @@
+require "placeos-driver"
+require "./ws_api_models"
+
+# docs: https://drive.google.com/file/d/1moo9NnFWukSf6fegxaZnSP5ShqSr_A03/view?usp=sharing
+
+class SecureOS::WsApi < PlaceOS::Driver
+ generic_name :SecureOS
+ descriptive_name "SecureOS WebSocket API"
+
+ uri_base "ws://secureos.server:8888/"
+ default_settings({
+ shared_host: true,
+ rest_api_host: "http://172.16.1.120:8888",
+ basic_auth: {
+ username: "srvc_acct",
+ password: "password!",
+ },
+ camera_types: [] of String,
+ camera_states: [StateType::Attached, StateType::Armed, StateType::Alarmed],
+ camera_events: [] of String,
+ })
+
+ @rest_api_host : String = ""
+ @camera_list : Array(Camera) = [] of Camera
+ @camera_types : Array(String) = [] of String
+ @camera_states : Array(StateType) = [] of StateType
+ @camera_events : Array(String) = [] of String
+ @watchlist_list : Array(Watchlist) = [] of Watchlist
+
+ getter! basic_auth : NamedTuple(username: String, password: String)
+
+ def on_update
+ @rest_api_host = setting String, :rest_api_host
+ @basic_auth = setting NamedTuple(username: String, password: String), :basic_auth
+ @camera_types = setting Array(String), :camera_types
+ @camera_states = setting Array(StateType), :camera_states
+ @camera_events = setting Array(String), :camera_events
+ end
+
+ def connected
+ response = http_client.get "#{@rest_api_host}/api/v1/ws_auth"
+ if response.success?
+ auth = AuthResponse.from_json response.body
+ send({type: :auth, token: auth.data.token}.to_json, wait: false)
+ else
+ raise "Authentication failed"
+ end
+
+ schedule.every(30.seconds) { send({type: :get_server_time}.to_json, name: :server_time) }
+ schedule.every(5.minutes, immediate: true) do
+ camera_list
+ subscribe_all
+ watchlist_list
+ end
+ rescue error
+ logger.warn(exception: error) { "Authentication failed" }
+ disconnect
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ protected def http_client
+ host = setting?(Bool, :shared_host) ? config.uri.not_nil! : @rest_api_host
+ client = HTTP::Client.new URI.parse(host)
+ client.basic_auth **basic_auth
+ client
+ end
+
+ private def subscribe_all
+ states = @camera_states.empty? ? nil : @camera_states
+ events = @camera_events.empty? ? nil : @camera_events
+ rules = [] of SubscribeRule
+
+ @camera_list.each do |camera|
+ next unless @camera_types.empty? || @camera_types.includes? camera.type
+
+ rules << SubscribeRule.new(
+ type: camera.type,
+ id: camera.id,
+ action: :STATE_CHANGED,
+ states: states,
+ )
+ rules << SubscribeRule.new(
+ type: camera.type,
+ id: camera.id,
+ action: :EVENT,
+ events: events,
+ )
+ end
+
+ return if rules.empty?
+
+ send({
+ type: :subscribe,
+ # id: 1234, # optional id used in error responses
+ data: {
+ add_rules: rules,
+ },
+ }.to_json, wait: false)
+ end
+
+ private def camera_list
+ response = http_client.get "#{@rest_api_host}/api/v1/cameras"
+ if response
+ json_response = CameraResponse.from_json response.body
+ self["camera_list"] = @camera_list = json_response.data
+ else
+ logger.warn { "Failed to get camera list" }
+ end
+ rescue error
+ logger.warn(exception: error) { "Failed to get camera list" }
+ end
+
+ def watchlist_add_lp(watchlist : String, license_plate : String, comment : String = "")
+ if wl = @watchlist_list.find { |l| l.name == watchlist }
+ response = http_client.post(
+ "#{@rest_api_host}/api/v1/watchlists/#{wl.id}/set",
+ headers: HTTP::Headers{"Content-Type" => "application/json"},
+ body: {
+ number: license_plate,
+ comment: comment,
+ }.to_json
+ )
+ unless response
+ logger.warn { "Failed to add license plate to watchlist" }
+ end
+ else
+ logger.warn { "Failed to find a watchlist named: #{watchlist}" }
+ end
+ rescue error
+ logger.warn(exception: error) { "Failed to add license plate to watchlist" }
+ end
+
+ def watchlist_remove_lp(watchlist : String, license_plate : String)
+ if wl = @watchlist_list.find { |l| l.name == watchlist }
+ response = http_client.post(
+ "#{@rest_api_host}/api/v1/watchlists/#{wl.id}/delete",
+ headers: HTTP::Headers{"Content-Type" => "application/json"},
+ body: {number: license_plate}.to_json
+ )
+ unless response
+ logger.warn { "Failed to remove license plate from watchlist" }
+ end
+ else
+ logger.warn { "Failed to find a watchlist named: #{watchlist}" }
+ end
+ rescue error
+ logger.warn(exception: error) { "Failed to remove license plate from watchlist" }
+ end
+
+ private def watchlist_list
+ response = http_client.get "#{@rest_api_host}/api/v1/watchlists"
+ if response
+ json_response = WatchlistResponse.from_json response.body
+ self["watchlist_list"] = @watchlist_list = json_response.data
+ else
+ logger.warn { "Failed to get watchlist list" }
+ end
+ rescue error
+ logger.warn(exception: error) { "Failed to get watchlist list" }
+ end
+
+ def received(data, task)
+ raw_json = String.new data
+ logger.debug { "SecureOS sent: #{raw_json}" }
+
+ type_check = JSON.parse(raw_json)["type"]?
+ if type_check
+ response = Response.from_json raw_json
+ case response
+ in StateWrapper
+ self["camera_#{response.data.id}_states"] = response.data
+ in EventWrapper
+ self["camera_#{response.data.id}"] = response.data
+ in ErrorWrapper
+ logger.warn { "SecureOS error: #{response.data}" }
+ if response.data.error.in?({"INVALID_AUTH_TOKEN", "UNAUTHORIZED"})
+ disconnect
+ else
+ self["last_error"] = response.data
+ end
+ in Response
+ end
+ end
+
+ task.try &.success
+ end
+end
diff --git a/drivers/secure_os/ws_api_models.cr b/drivers/secure_os/ws_api_models.cr
new file mode 100644
index 00000000000..457da680f23
--- /dev/null
+++ b/drivers/secure_os/ws_api_models.cr
@@ -0,0 +1,133 @@
+require "json"
+
+module SecureOS
+ enum StateType
+ Attached
+ Armed
+ Alarmed
+ end
+
+ struct SubscribeRule
+ include JSON::Serializable
+
+ getter type : String
+ getter id : String
+ getter states : Array(StateType)? = nil
+ getter events : Array(String)? = nil
+ getter action : Symbol
+
+ def initialize(
+ @type : String,
+ @id : String,
+ @action : Symbol,
+ @states : Array(StateType)? = nil,
+ @events : Array(String)? = nil
+ )
+ end
+ end
+
+ abstract class Response
+ include JSON::Serializable
+ include JSON::Serializable::Unmapped
+
+ use_json_discriminator "type", {
+ "state" => StateWrapper,
+ "event" => EventWrapper,
+ "error" => ErrorWrapper,
+ }
+ end
+
+ class StateWrapper < Response
+ getter type : String = "state"
+ getter data : State
+ end
+
+ class EventWrapper < Response
+ getter type : String = "event"
+ getter data : Event
+ end
+
+ class ErrorWrapper < Response
+ getter type : String = "error"
+ getter data : Error
+ end
+
+ struct State
+ include JSON::Serializable
+
+ getter type : String
+ getter id : String | Int64?
+ getter ticks : Int64
+
+ @[JSON::Field(converter: Time::Format.new("%FT%T.%L", Time::Location::UTC))]
+ getter time : Time # "2017-02-02T16:10:07.241"
+
+ getter states : Hash(String, Bool)
+ end
+
+ struct Event
+ include JSON::Serializable
+
+ getter type : String
+ getter id : String | Int64?
+ getter action : String
+ getter ticks : Int64?
+
+ @[JSON::Field(converter: Time::Format.new("%FT%T.%L", Time::Location::UTC))]
+ getter time : Time # "2017-02-02T16:10:07.241"
+
+ getter parameters : JSON::Any?
+ end
+
+ struct Error
+ include JSON::Serializable
+
+ getter request_id : String | Int64?
+ getter message : String
+ getter error : String
+ end
+
+ struct AuthResponse
+ include JSON::Serializable
+
+ getter data : AuthToken
+ getter status : String
+ end
+
+ struct AuthToken
+ include JSON::Serializable
+
+ getter token : String
+ end
+
+ struct CameraResponse
+ include JSON::Serializable
+
+ getter data : Array(Camera)
+ getter status : String
+ end
+
+ struct Camera
+ include JSON::Serializable
+
+ getter id : String
+ getter name : String
+ getter settings : JSON::Any
+ getter status : JSON::Any
+ getter type : String
+ end
+
+ struct WatchlistResponse
+ include JSON::Serializable
+
+ getter data : Array(Watchlist)
+ getter status : String
+ end
+
+ struct Watchlist
+ include JSON::Serializable
+
+ getter id : String
+ getter name : String
+ end
+end
diff --git a/drivers/secure_os/ws_api_spec.cr b/drivers/secure_os/ws_api_spec.cr
new file mode 100644
index 00000000000..81631701320
--- /dev/null
+++ b/drivers/secure_os/ws_api_spec.cr
@@ -0,0 +1,150 @@
+require "placeos-driver/spec"
+require "./ws_api_models"
+
+private macro respond_with(code, body)
+ res.headers["Content-Type"] = "application/json"
+ res.status_code = {{code}}
+ res.output << {{body}}
+end
+
+DriverSpecs.mock_driver "SecureOS::WsApi" do
+ # Getting WebSocket auth token
+ expect_http_request do |req, res|
+ req.method.should eq("GET")
+ req.path.should eq("/api/v1/ws_auth")
+ req.headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("srvc_acct:password!")}")
+ respond_with 200, {data: {token: "qwertyuio"}, status: :success}.to_json
+ end
+ should_send({type: :auth, token: "qwertyuio"}.to_json)
+
+ # Getting a list of cameras
+ camera = {
+ "id" => "1",
+ "name" => "Camera 1",
+ "settings" => {"telemetry_id" => "native"},
+ "status" => {
+ "enabled" => true,
+ "state" => "DISARMED",
+ },
+ "type" => "CAM",
+ }
+ expect_http_request do |req, res|
+ req.method.should eq("GET")
+ req.path.should eq("/api/v1/cameras")
+ req.headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("srvc_acct:password!")}")
+ respond_with 200, {
+ data: [camera],
+ status: "success",
+ }.to_json
+ end
+ status[:camera_list].should eq([camera])
+
+ # Subscribing to states/events
+ should_send({
+ type: :subscribe,
+ data: {
+ add_rules: [
+ {
+ type: "CAM",
+ id: "1",
+ states: [
+ SecureOS::StateType::Attached,
+ SecureOS::StateType::Armed,
+ SecureOS::StateType::Alarmed,
+ ],
+ action: :STATE_CHANGED,
+ },
+ {
+ type: "CAM",
+ id: "1",
+ action: :EVENT,
+ },
+ ],
+ },
+ }.to_json)
+
+ # Getting a list of watchlists
+ expect_http_request do |req, res|
+ req.method.should eq("GET")
+ req.path.should eq("/api/v1/watchlists")
+ req.headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("srvc_acct:password!")}")
+ respond_with 200, {
+ data: [
+ {id: "1", name: "some list"},
+ ],
+ status: "success",
+ }.to_json
+ end
+ status[:camera_list].should eq([camera])
+
+ # Adding a license plate to a watchlist
+ exec(:watchlist_add_lp, watchlist: "some list", license_plate: "ABC", comment: "Test plate")
+ expect_http_request do |req, res|
+ req.method.should eq("POST")
+ req.path.should eq("/api/v1/watchlists/1/set")
+ req.headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("srvc_acct:password!")}")
+ req.headers["Content-Type"]?.should eq("application/json")
+ respond_with 200, "Comment for number ABC has been set."
+ end
+
+ # Removing a license plate from a watchlist
+ exec(:watchlist_remove_lp, watchlist: "some list", license_plate: "ABC")
+ expect_http_request do |req, res|
+ req.method.should eq("POST")
+ req.path.should eq("/api/v1/watchlists/1/delete")
+ req.headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("srvc_acct:password!")}")
+ req.headers["Content-Type"]?.should eq("application/json")
+ respond_with 200, "Number ABC has been deleted from the watchlist."
+ end
+
+ # Recieving states
+ states = {
+ "type" => "CAM",
+ "id" => "1",
+ "ticks" => 501234,
+ "time" => "2017-02-02T16:10:07.241",
+ "states" => {
+ "attached" => true,
+ "armed" => true,
+ "alarmed" => false,
+ },
+ }
+ transmit({
+ type: :state,
+ data: states,
+ }.to_json)
+ status[:camera_1_states].should eq(states)
+
+ # Recieving events
+ event = {
+ "type" => "CAM",
+ "id" => "1",
+ "action" => "CAR_LP_RECOGNIZED",
+ "ticks" => 501234,
+ "time" => "2017-02-02T16:10:07.241",
+ "parameters" => {
+ "camera_id" => "6",
+ "direction_name" => "approaching",
+ "number" => "T345 LYW",
+ "recognizer_id" => "1",
+ "recognizer_type" => "LPR_CAM",
+ },
+ }
+ transmit({
+ type: :event,
+ data: event,
+ }.to_json)
+ status[:camera_1].should eq(event)
+
+ # A delete event is sent if a subscribed camera is removed
+ transmit({
+ type: :event,
+ data: {
+ type: :CAM,
+ id: "1",
+ action: :DELETED,
+ time: "2017-02-02T16:10:07.241",
+ },
+ }.to_json)
+ status[:camera_1]["parameters"]?.should be_nil
+end
diff --git a/drivers/sennheiser/models.cr b/drivers/sennheiser/models.cr
new file mode 100644
index 00000000000..8628679a61c
--- /dev/null
+++ b/drivers/sennheiser/models.cr
@@ -0,0 +1,79 @@
+module Sennheiser::Models
+ macro def_get(name, resource)
+ def {{name.id}}
+ api_get({{resource}})
+ end
+ end
+
+ macro def_put(name, resource, **params)
+ def {{name.id}}(
+ {% for param, klass in params %}
+ {% optional = false %}
+ {% if param.stringify.ends_with?("_") %}
+ {% optional = true %}
+ {% param = param.stringify[0..-2] %}
+ {% end %}
+
+ {% if klass.is_a?(RangeLiteral) %}
+ {{param.id}} : Int32{% if optional %}? = nil{% end %},
+ {% else %}
+ {{param.id}} : {{klass}}{% if optional %}? = nil{% end %},
+ {% end %}
+ {% end %}
+ )
+ {% for param, klass in params %}
+ {% if klass.is_a?(RangeLiteral) %}
+ {% optional = false %}
+ {% if param.stringify.ends_with?("_") %}
+ {% optional = true %}
+ {% param = param.stringify[0..-2] %}
+ {% end %}
+ {% if optional %} if {{param.id}}{% end %}
+ raise ArgumentError.new("#{ {{param.stringify}} } must be within #{ {{klass}} }, was #{ {{param.id}} }") unless ({{klass}}).includes?({{param.id}})
+ {% if optional %}end{% end %}
+ {% end %}
+ {% end %}
+
+ api_put({{resource}},{
+ {% for param, klass in params %}
+ {% if param.stringify.ends_with?("_") %}
+ {% param = param.stringify[0..-2] %}
+ {% end %}
+ "{{param.id.camelcase(lower: true)}}" => JSON.parse({{param.id}}.to_json),
+ {% end %}
+ }.to_json
+ )
+ end
+ end
+
+ enum Color
+ LightGreen
+ Green
+ Blue
+ Red
+ Yellow
+ Orange
+ Cyan
+ Pink
+ end
+
+ enum InstallationType
+ FlushMounted
+ SurfaceMounted
+ Suspended
+ end
+
+ enum DetectionThreshold
+ QuietRoom
+ NormalRomm
+ LoudRoom
+ end
+
+ enum SwitchOutput
+ FarendOutput
+ LocalOutput
+ end
+
+ alias MicTuple = NamedTuple(color: Color)
+ alias MicCustomTuple = NamedTuple(enabled: Bool, color: Color)
+end
diff --git a/drivers/sennheiser/sscv2.cr b/drivers/sennheiser/sscv2.cr
new file mode 100644
index 00000000000..46db2e352a4
--- /dev/null
+++ b/drivers/sennheiser/sscv2.cr
@@ -0,0 +1,578 @@
+require "placeos-driver"
+require "placeos-driver/interface/muteable"
+require "./sscv2_models"
+
+# https://docs.cloud.sennheiser.com/en-us/api-docs/api-docs/open-api-tc-ceiling-medium.html#/FastResource/get_api_audio_roomInUse_activityLevel
+
+class Sennheiser::SSCv2Driver < PlaceOS::Driver
+ include Interface::AudioMuteable
+
+ descriptive_name "Sennheiser Sound Control Protocol v2"
+ generic_name :AudioDevice
+ description "Driver for Sennheiser TeamConnect Ceiling Microphone (TCCM) using SSCv2 protocol. Requires third-party access to be enabled in Sennheiser Control Cockpit with configured password. Automatically subscribes to real-time device state, beam direction, audio levels, and room occupancy when running_specs is false or nil."
+
+ uri_base "https://device_ip"
+
+ default_settings({
+ basic_auth: {
+ username: "api",
+ password: "configured_password",
+ },
+ running_specs: true,
+ subscription_resources: [
+ "/api/device/site",
+ ] of String,
+ # Note: /api/device/status and /api/device/info are automatically
+ # subscribed when running_specs is false or nil
+ })
+
+ @username : String = "api"
+ @password : String = ""
+ @subscription_resources : Array(String) = [] of String
+ @running_specs : Bool = true
+ @subscription_processor : Sennheiser::SSCv2::SubscriptionProcessor?
+
+ def on_load
+ on_update
+ end
+
+ def on_update
+ # Extract basic auth credentials
+ if basic_auth = setting?(Hash(String, String), :basic_auth)
+ @username = basic_auth["username"]? || "api"
+ @password = basic_auth["password"]? || ""
+ else
+ @username = "api"
+ @password = ""
+ end
+
+ @subscription_resources = setting?(Array(String), :subscription_resources) || [] of String
+ running_specs_setting = setting?(Bool, :running_specs)
+ @running_specs = running_specs_setting.nil? ? false : running_specs_setting
+
+ # Stop existing subscription processor
+ @subscription_processor.try(&.stop)
+ @subscription_processor = nil
+
+ # Don't start SSE subscriptions during specs
+ return if @running_specs
+
+ # Add default subscriptions
+ default_resources = [
+ "/api/device/state",
+ "/api/device/identity",
+ "/api/audio/inputs/microphone/beam/direction",
+ "/api/audio/inputs/microphone/level",
+ "/api/audio/roomInUse",
+ "/api/audio/roomInUse/activityLevel",
+ ]
+ default_resources.each do |resource|
+ @subscription_resources << resource unless @subscription_resources.includes?(resource)
+ end
+
+ # Initialize subscription processor
+ base_url = config.uri.not_nil!.to_s.rchop("/")
+ processor = Sennheiser::SSCv2::SubscriptionProcessor.new(base_url, @username, @password)
+
+ # Set up callbacks
+ processor.on_data do |resource_path, data|
+ handle_subscription_data(resource_path, data)
+ end
+
+ processor.on_error do |error|
+ logger.warn { "SSE subscription error: #{error}" }
+ end
+
+ @subscription_processor = processor
+ end
+
+ def connected
+ return if @running_specs
+
+ # Start SSE subscription
+ spawn { start_subscription }
+ end
+
+ def disconnected
+ @subscription_processor.try(&.stop)
+ end
+
+ # === API Methods ===
+
+ # SSC and Device Info
+ def ssc_version
+ get("/api/ssc/version")
+ end
+
+ def ssc_schema
+ get("/api/ssc/schema")
+ end
+
+ def device_identity
+ get("/api/device/identity")
+ end
+
+ def device_identification
+ get("/api/device/identification")
+ end
+
+ def set_device_identification(visual : Bool)
+ put("/api/device/identification", body: {visual: visual}.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ def device_site
+ get("/api/device/site")
+ end
+
+ def device_state
+ get("/api/device/state")
+ end
+
+ def firmware_update_state
+ get("/api/firmware/update/state")
+ end
+
+ def set_device_name(deviceName : String)
+ put("/api/device/site", body: {deviceName: deviceName}.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ def set_device_location(location : String)
+ put("/api/device/site", body: {location: location}.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ def set_device_position(position : String)
+ put("/api/device/site", body: {position: position}.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ # Audio Control
+ def audio_global_mute
+ get("/api/audio/outputs/global/mute")
+ end
+
+ def set_audio_global_mute(enabled : Bool)
+ put("/api/audio/outputs/global/mute", body: {enabled: enabled}.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ def microphone_beam
+ get("/api/audio/inputs/microphone/beam")
+ end
+
+ def set_microphone_beam(installationType : String? = nil, sourceDetectionThreshold : String? = nil, offset : Int32? = nil)
+ body = {} of String => JSON::Any::Type
+ body["installationType"] = installationType if installationType
+ body["sourceDetectionThreshold"] = sourceDetectionThreshold if sourceDetectionThreshold
+ body["offset"] = offset.to_i64 if offset
+ put("/api/audio/inputs/microphone/beam", body: body.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ def beam_direction
+ get("/api/audio/inputs/microphone/beam/direction")
+ end
+
+ def microphone_level
+ get("/api/audio/inputs/microphone/level")
+ end
+
+ def reference_level
+ get("/api/audio/inputs/reference/level")
+ end
+
+ def room_in_use
+ get("/api/audio/roomInUse")
+ end
+
+ def room_in_use_activity_level
+ get("/api/audio/roomInUse/activityLevel")
+ end
+
+ def room_in_use_config
+ get("/api/audio/roomInUse/config")
+ end
+
+ # Audio Outputs
+ def analog_output
+ get("/api/audio/outputs/analog")
+ end
+
+ def set_analog_output(gain : Int32? = nil, switch : String? = nil)
+ body = {} of String => JSON::Any::Type
+ body["gain"] = gain.to_i64 if gain
+ body["switch"] = switch if switch
+ put("/api/audio/outputs/analog", body: body.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ def dante_farend_output
+ get("/api/audio/outputs/dante/farEnd")
+ end
+
+ def set_dante_farend_output(gain : Int32? = nil, noiseGateEnabled : Bool? = nil, equalizerEnabled : Bool? = nil, delay : Int32? = nil)
+ body = {} of String => JSON::Any::Type
+ body["gain"] = gain.to_i64 if gain
+ body["noiseGateEnabled"] = noiseGateEnabled unless noiseGateEnabled.nil?
+ body["equalizerEnabled"] = equalizerEnabled unless equalizerEnabled.nil?
+ body["delay"] = delay.to_i64 if delay
+ put("/api/audio/outputs/dante/farEnd", body: body.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ def dante_local_output
+ get("/api/audio/outputs/dante/local")
+ end
+
+ def set_dante_local_output(gain : Int32? = nil, noiseGateEnabled : Bool? = nil, equalizerEnabled : Bool? = nil, voiceLiftEnabled : Bool? = nil, delay : Int32? = nil)
+ body = {} of String => JSON::Any::Type
+ body["gain"] = gain.to_i64 if gain
+ body["noiseGateEnabled"] = noiseGateEnabled unless noiseGateEnabled.nil?
+ body["equalizerEnabled"] = equalizerEnabled unless equalizerEnabled.nil?
+ body["voiceLiftEnabled"] = voiceLiftEnabled unless voiceLiftEnabled.nil?
+ body["delay"] = delay.to_i64 if delay
+ put("/api/audio/outputs/dante/local", body: body.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ # Audio Inputs
+ def reference_input
+ get("/api/audio/inputs/dante/reference")
+ end
+
+ def set_reference_input(gain : Int32? = nil, farEndAutoAdjustEnabled : Bool? = nil)
+ body = {} of String => JSON::Any::Type
+ body["gain"] = gain.to_i64 if gain
+ body["farEndAutoAdjustEnabled"] = farEndAutoAdjustEnabled unless farEndAutoAdjustEnabled.nil?
+ put("/api/audio/inputs/dante/reference", body: body.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ # Audio Processing
+ def voice_lift
+ get("/api/audio/voiceLift")
+ end
+
+ def set_voice_lift(emergencyMuteThreshold : Int32? = nil, emergencyMuteTime : Int32? = nil)
+ body = {} of String => JSON::Any::Type
+ body["emergencyMuteThreshold"] = emergencyMuteThreshold.to_i64 if emergencyMuteThreshold
+ body["emergencyMuteTime"] = emergencyMuteTime.to_i64 if emergencyMuteTime
+ put("/api/audio/voiceLift", body: body.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ def equalizer
+ get("/api/audio/equalizer")
+ end
+
+ def set_equalizer(gains : Array(Int32))
+ put("/api/audio/equalizer", body: {gains: gains}.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ def noise_gate
+ get("/api/audio/noiseGate")
+ end
+
+ def set_noise_gate(threshold : Int32? = nil, holdTime : Int32? = nil)
+ body = {} of String => JSON::Any::Type
+ body["threshold"] = threshold.to_i64 if threshold
+ body["holdTime"] = holdTime.to_i64 if holdTime
+ put("/api/audio/noiseGate", body: body.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ def denoiser
+ get("/api/audio/inputs/microphone/denoiser")
+ end
+
+ def set_denoiser(setting : String)
+ put("/api/audio/inputs/microphone/denoiser", body: {setting: setting}.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ # Zones
+ def exclusion_zones
+ get("/api/audio/inputs/microphone/exclusionZones")
+ end
+
+ def exclusion_zone(id : Int32)
+ get("/api/audio/inputs/microphone/exclusionZones/#{id}")
+ end
+
+ def set_exclusion_zone(id : Int32, enabled : Bool? = nil, elevation_min : Int32? = nil, elevation_max : Int32? = nil, azimuth_min : Int32? = nil, azimuth_max : Int32? = nil)
+ body = {} of String => (String | Int64 | Bool | Hash(String, Int64))
+ body["enabled"] = enabled unless enabled.nil?
+
+ if elevation_min || elevation_max
+ elevation = {} of String => Int64
+ elevation["min"] = elevation_min.to_i64 if elevation_min
+ elevation["max"] = elevation_max.to_i64 if elevation_max
+ body["elevation"] = elevation
+ end
+
+ if azimuth_min || azimuth_max
+ azimuth = {} of String => Int64
+ azimuth["min"] = azimuth_min.to_i64 if azimuth_min
+ azimuth["max"] = azimuth_max.to_i64 if azimuth_max
+ body["azimuth"] = azimuth
+ end
+
+ put("/api/audio/inputs/microphone/exclusionZones/#{id}", body: body.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ def priority_zones
+ get("/api/audio/inputs/microphone/priorityZones")
+ end
+
+ def priority_zone(id : Int32)
+ get("/api/audio/inputs/microphone/priorityZones/#{id}")
+ end
+
+ def set_priority_zone(id : Int32, enabled : Bool? = nil, weight : Float32? = nil, elevation_min : Int32? = nil, elevation_max : Int32? = nil, azimuth_min : Int32? = nil, azimuth_max : Int32? = nil)
+ body = {} of String => (String | Int64 | Bool | Float64 | Hash(String, Int64))
+ body["enabled"] = enabled unless enabled.nil?
+ body["weight"] = weight.to_f64 if weight
+
+ if elevation_min || elevation_max
+ elevation = {} of String => Int64
+ elevation["min"] = elevation_min.to_i64 if elevation_min
+ elevation["max"] = elevation_max.to_i64 if elevation_max
+ body["elevation"] = elevation
+ end
+
+ if azimuth_min || azimuth_max
+ azimuth = {} of String => Int64
+ azimuth["min"] = azimuth_min.to_i64 if azimuth_min
+ azimuth["max"] = azimuth_max.to_i64 if azimuth_max
+ body["azimuth"] = azimuth
+ end
+
+ put("/api/audio/inputs/microphone/priorityZones/#{id}", body: body.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ # Device LEDs
+ def led_ring
+ get("/api/device/leds/ring")
+ end
+
+ def set_led_ring(brightness : Int32? = nil, showFarendActivity : Bool? = nil, micOn_color : String? = nil, micMute_color : String? = nil, micCustom_enabled : Bool? = nil, micCustom_color : String? = nil)
+ body = {} of String => (String | Int64 | Bool | Hash(String, String) | Hash(String, String | Bool))
+ body["brightness"] = brightness.to_i64 if brightness
+ body["showFarendActivity"] = showFarendActivity unless showFarendActivity.nil?
+
+ if micOn_color
+ body["micOn"] = {"color" => micOn_color}
+ end
+
+ if micMute_color
+ body["micMute"] = {"color" => micMute_color}
+ end
+
+ if micCustom_enabled || micCustom_color
+ micCustom = {} of String => (String | Bool)
+ micCustom["enabled"] = micCustom_enabled unless micCustom_enabled.nil?
+ micCustom["color"] = micCustom_color if micCustom_color
+ body["micCustom"] = micCustom
+ end
+
+ put("/api/device/leds/ring", body: body.to_json, headers: {"Content-Type" => "application/json"})
+ end
+
+ # Device Power
+ def poe_daisychain
+ get("/api/device/power/poe/daisychain")
+ end
+
+ # License Agreements
+ def license_agreements_hash
+ get("/api/device/licenseAgreements/hash")
+ end
+
+ def license_agreements_licenses
+ get("/api/device/licenseAgreements/licenses")
+ end
+
+ # === Interface::AudioMuteable Implementation ===
+
+ def mute_audio(state : Bool = true, index : Int32 | String = 0)
+ set_audio_global_mute(state)
+ end
+
+ # === Convenience Methods ===
+
+ # Mute/unmute microphone
+ def mute(state : Bool = true)
+ set_audio_global_mute(state)
+ end
+
+ def unmute
+ mute(false)
+ end
+
+ # Device identification (visual LED flash)
+ def identify(enable : Bool = true)
+ set_device_identification(enable)
+ end
+
+ # Quick beam configuration
+ def configure_beam(installation_type : String, detection_threshold : String = "NormalRoom", offset : Int32 = 0)
+ set_microphone_beam(installation_type, detection_threshold, offset)
+ end
+
+ # LED ring brightness control
+ def set_brightness(level : Int32)
+ set_led_ring(brightness: level)
+ end
+
+ # Set LED colors for different states
+ def set_led_colors(mic_on : String? = nil, mic_mute : String? = nil)
+ set_led_ring(micOn_color: mic_on, micMute_color: mic_mute)
+ end
+
+ # Quick equalizer presets
+ def equalizer_flat
+ set_equalizer([0, 0, 0, 0, 0, 0, 0])
+ end
+
+ def equalizer_voice_boost
+ # Boost 1-4kHz range for voice clarity
+ set_equalizer([0, 0, 2, 3, 3, 1, 0])
+ end
+
+ # Room sensing configuration
+ def configure_room_sensing(trigger_time : Int32 = 15, release_time : Int32 = 300, threshold : Int32 = 10)
+ # Note: This would require a PUT endpoint for room config which isn't in the current API
+ # For now, users would need to use the web interface to configure this
+ logger.info { "Room sensing config - use web interface: trigger=#{trigger_time}s, release=#{release_time}s, threshold=#{threshold}dB" }
+ end
+
+ # Get current audio status summary
+ def audio_status
+ {
+ "muted" => self[:global_mute]?.try(&.as_h).try(&.["enabled"]?),
+ "beam_direction" => self[:beam_direction]?,
+ "microphone_level" => self[:microphone_level]?,
+ "room_in_use" => self[:room_in_use]?.try(&.as_h).try(&.["active"]?),
+ "room_activity" => self[:room_activity_level]?.try(&.as_h).try(&.["peak"]?),
+ }
+ end
+
+ # Get device information summary
+ def device_info
+ {
+ "identity" => self[:device_identity]?,
+ "site" => {
+ "name" => self[:device_name]?,
+ "location" => self[:device_location]?,
+ "position" => self[:device_position]?,
+ },
+ "state" => self[:device_state]?,
+ }
+ end
+
+ # === Subscription Management ===
+
+ def subscribe_to_resources(resources : Array(String))
+ return if @running_specs
+ @subscription_processor.try(&.subscribe_to_resources(resources))
+ end
+
+ def add_subscription_resources(resources : Array(String))
+ return if @running_specs
+ @subscription_processor.try(&.add_resources(resources))
+ end
+
+ def remove_subscription_resources(resources : Array(String))
+ return if @running_specs
+ @subscription_processor.try(&.remove_resources(resources))
+ end
+
+ def get_subscription_status
+ processor = @subscription_processor
+
+ if processor
+ {
+ "session_uuid" => processor.session_uuid || "",
+ "subscribed_resources" => processor.subscribed_resources,
+ "running" => processor.running,
+ }
+ else
+ {
+ "session_uuid" => "",
+ "subscribed_resources" => [] of String,
+ "running" => false,
+ }
+ end
+ end
+
+ # === Private Methods ===
+
+ private def start_subscription
+ processor = @subscription_processor
+ return unless processor
+
+ processor.start
+
+ # Wait a moment for connection to establish, then subscribe to default resources
+ sleep 2.seconds
+ if !@subscription_resources.empty?
+ processor.subscribe_to_resources(@subscription_resources)
+ end
+ end
+
+ private def handle_subscription_data(resource_path : String, data : JSON::Any)
+ logger.debug { "Received SSE data for #{resource_path}: #{data}" }
+
+ # Update driver state based on resource path
+ case resource_path
+ when "/api/device/site"
+ begin
+ site_data = Sennheiser::SSCv2::DeviceSite.from_json(data.to_json)
+ self[:device_name] = site_data.deviceName
+ self[:device_location] = site_data.location
+ self[:device_position] = site_data.position
+ rescue JSON::ParseException
+ logger.warn { "Failed to parse device site data: #{data}" }
+ end
+ when "/api/device/identity"
+ self[:device_identity] = data.as_h
+ when "/api/device/identification"
+ self[:device_identification] = data.as_h
+ when "/api/device/state"
+ self[:device_state] = data.as_h
+ when "/api/audio/outputs/global/mute"
+ self[:global_mute] = data.as_h
+ when "/api/audio/inputs/microphone/beam"
+ self[:microphone_beam] = data.as_h
+ when "/api/audio/inputs/microphone/beam/direction"
+ self[:beam_direction] = data.as_h
+ when "/api/audio/inputs/microphone/level"
+ self[:microphone_level] = data.as_h
+ when "/api/audio/inputs/reference/level"
+ self[:reference_level] = data.as_h
+ when "/api/audio/roomInUse"
+ self[:room_in_use] = data.as_h
+ when "/api/audio/roomInUse/activityLevel"
+ self[:room_activity_level] = data.as_h
+ when "/api/audio/outputs/analog"
+ self[:analog_output] = data.as_h
+ when "/api/audio/outputs/dante/farEnd"
+ self[:dante_farend_output] = data.as_h
+ when "/api/audio/outputs/dante/local"
+ self[:dante_local_output] = data.as_h
+ when "/api/audio/inputs/dante/reference"
+ self[:reference_input] = data.as_h
+ when "/api/audio/voiceLift"
+ self[:voice_lift] = data.as_h
+ when "/api/audio/equalizer"
+ self[:equalizer] = data.as_h
+ when "/api/audio/noiseGate"
+ self[:noise_gate] = data.as_h
+ when "/api/device/leds/ring"
+ self[:led_ring] = data.as_h
+ when "/api/device/power/poe/daisychain"
+ self[:poe_daisychain] = data.as_h
+ when "/api/audio/inputs/microphone/denoiser"
+ self[:denoiser] = data.as_h
+ when .starts_with?("/api/audio/inputs/microphone/exclusionZones/")
+ zone_id = resource_path.split("/").last
+ self["exclusion_zone_#{zone_id}"] = data.as_h
+ when .starts_with?("/api/audio/inputs/microphone/priorityZones/")
+ zone_id = resource_path.split("/").last
+ self["priority_zone_#{zone_id}"] = data.as_h
+ else
+ # Store generic resource data
+ resource_key = resource_path.gsub("/", "_").gsub(/^_/, "")
+ self[resource_key] = data.as_h
+ end
+ end
+end
diff --git a/drivers/sennheiser/sscv2_models.cr b/drivers/sennheiser/sscv2_models.cr
new file mode 100644
index 00000000000..9093bcedeee
--- /dev/null
+++ b/drivers/sennheiser/sscv2_models.cr
@@ -0,0 +1,611 @@
+require "json"
+require "http/client"
+require "uri"
+
+module Sennheiser::SSCv2
+ # SSE Event types
+ enum EventType
+ Open
+ Message
+ Close
+
+ def self.from_string(value : String)
+ case value.downcase
+ when "open"
+ Open
+ when "message", ""
+ Message
+ when "close"
+ Close
+ else
+ Message
+ end
+ end
+ end
+
+ # SSE Event structure
+ struct SSEEvent
+ include JSON::Serializable
+
+ getter event_type : EventType
+ getter data : JSON::Any
+
+ def initialize(@event_type : EventType, @data : JSON::Any)
+ end
+
+ def self.parse_line(line : String) : SSEEvent?
+ return nil if line.blank?
+
+ if line.starts_with?("event:")
+ event_type = EventType.from_string(line[6..].strip)
+ return SSEEvent.new(event_type, JSON::Any.new({} of String => JSON::Any))
+ elsif line.starts_with?("data:")
+ data_str = line[5..].strip
+ begin
+ data = JSON.parse(data_str)
+ return SSEEvent.new(EventType::Message, data)
+ rescue JSON::ParseException
+ return nil
+ end
+ end
+
+ nil
+ end
+ end
+
+ # Subscription status response
+ struct SubscriptionStatus
+ include JSON::Serializable
+
+ getter path : String
+ getter sessionUUID : String
+
+ def initialize(@path : String, @sessionUUID : String)
+ end
+ end
+
+ # Error response structure
+ struct ErrorResponse
+ include JSON::Serializable
+
+ getter path : String
+ getter error : Int32
+
+ def initialize(@path : String, @error : Int32)
+ end
+ end
+
+ # Device site information
+ struct DeviceSite
+ include JSON::Serializable
+
+ getter deviceName : String
+ getter location : String
+ getter position : String
+
+ def initialize(@deviceName : String, @location : String, @position : String)
+ end
+ end
+
+ # Device identity
+ struct DeviceIdentity
+ include JSON::Serializable
+
+ getter product : String
+ getter hardwareRevision : String
+ getter serial : String
+ getter vendor : String
+
+ def initialize(@product : String, @hardwareRevision : String, @serial : String, @vendor : String)
+ end
+ end
+
+ # Device identification (visual indicator)
+ struct DeviceIdentification
+ include JSON::Serializable
+
+ getter visual : Bool
+
+ def initialize(@visual : Bool)
+ end
+ end
+
+ # Device state
+ struct DeviceState
+ include JSON::Serializable
+
+ getter state : String
+ getter warnings : Array(String)
+
+ def initialize(@state : String, @warnings : Array(String))
+ end
+ end
+
+ # Audio global mute
+ struct AudioGlobalMute
+ include JSON::Serializable
+
+ getter enabled : Bool
+
+ def initialize(@enabled : Bool)
+ end
+ end
+
+ # Microphone beam settings
+ struct MicrophoneBeam
+ include JSON::Serializable
+
+ getter installationType : String
+ getter sourceDetectionThreshold : String
+ getter offset : Int32
+
+ def initialize(@installationType : String, @sourceDetectionThreshold : String, @offset : Int32)
+ end
+ end
+
+ # Beam direction
+ struct BeamDirection
+ include JSON::Serializable
+
+ getter azimuth : Int32
+ getter elevation : Int32
+ getter beamFreezeActive : Bool
+
+ def initialize(@azimuth : Int32, @elevation : Int32, @beamFreezeActive : Bool)
+ end
+ end
+
+ # Audio level
+ struct AudioLevel
+ include JSON::Serializable
+
+ getter peak : Int32?
+ getter rms : Int32?
+
+ def initialize(@peak : Int32? = nil, @rms : Int32? = nil)
+ end
+ end
+
+ # Room in use
+ struct RoomInUse
+ include JSON::Serializable
+
+ getter active : Bool
+
+ def initialize(@active : Bool)
+ end
+ end
+
+ # Room in use activity level
+ struct RoomInUseActivityLevel
+ include JSON::Serializable
+
+ getter peak : Int32
+
+ def initialize(@peak : Int32)
+ end
+ end
+
+ # Room in use config
+ struct RoomInUseConfig
+ include JSON::Serializable
+
+ getter triggerTime : Int32
+ getter releaseTime : Int32
+ getter threshold : Int32
+
+ def initialize(@triggerTime : Int32, @releaseTime : Int32, @threshold : Int32)
+ end
+ end
+
+ # Analog output settings
+ struct AnalogOutput
+ include JSON::Serializable
+
+ getter gain : Int32
+ getter switch : String
+
+ def initialize(@gain : Int32, @switch : String)
+ end
+ end
+
+ # Dante output settings
+ struct DanteOutput
+ include JSON::Serializable
+
+ getter gain : Int32
+ getter noiseGateEnabled : Bool
+ getter equalizerEnabled : Bool
+ getter delay : Int32
+ getter voiceLiftEnabled : Bool?
+
+ def initialize(@gain : Int32, @noiseGateEnabled : Bool, @equalizerEnabled : Bool, @delay : Int32, @voiceLiftEnabled : Bool? = nil)
+ end
+ end
+
+ # Reference input settings
+ struct ReferenceInput
+ include JSON::Serializable
+
+ getter gain : Int32
+ getter farEndAutoAdjustEnabled : Bool
+
+ def initialize(@gain : Int32, @farEndAutoAdjustEnabled : Bool)
+ end
+ end
+
+ # Voice lift settings
+ struct VoiceLift
+ include JSON::Serializable
+
+ getter emergencyMuteThreshold : Int32
+ getter emergencyMuteTime : Int32
+
+ def initialize(@emergencyMuteThreshold : Int32, @emergencyMuteTime : Int32)
+ end
+ end
+
+ # Equalizer settings
+ struct Equalizer
+ include JSON::Serializable
+
+ getter gains : Array(Int32)
+
+ def initialize(@gains : Array(Int32))
+ end
+ end
+
+ # Noise gate settings
+ struct NoiseGate
+ include JSON::Serializable
+
+ getter threshold : Int32
+ getter holdTime : Int32
+
+ def initialize(@threshold : Int32, @holdTime : Int32)
+ end
+ end
+
+ # LED ring color
+ struct LedColor
+ include JSON::Serializable
+
+ getter color : String
+
+ def initialize(@color : String)
+ end
+ end
+
+ # LED ring custom
+ struct LedCustom
+ include JSON::Serializable
+
+ getter enabled : Bool
+ getter color : String
+
+ def initialize(@enabled : Bool, @color : String)
+ end
+ end
+
+ # LED ring settings
+ struct LedRing
+ include JSON::Serializable
+
+ getter brightness : Int32
+ getter showFarendActivity : Bool
+ getter micOn : LedColor
+ getter micMute : LedColor
+ getter micCustom : LedCustom
+
+ def initialize(@brightness : Int32, @showFarendActivity : Bool, @micOn : LedColor, @micMute : LedColor, @micCustom : LedCustom)
+ end
+ end
+
+ # PoE daisy chain info
+ struct PoeDaisyChain
+ include JSON::Serializable
+
+ getter sufficientPower : Bool
+ getter inUse : Bool
+
+ def initialize(@sufficientPower : Bool, @inUse : Bool)
+ end
+ end
+
+ # Zone angle range
+ struct AngleRange
+ include JSON::Serializable
+
+ getter min : Int32
+ getter max : Int32
+
+ def initialize(@min : Int32, @max : Int32)
+ end
+ end
+
+ # Exclusion zone
+ struct ExclusionZone
+ include JSON::Serializable
+
+ getter id : Int32
+ getter enabled : Bool
+ getter elevation : AngleRange
+ getter azimuth : AngleRange
+
+ def initialize(@id : Int32, @enabled : Bool, @elevation : AngleRange, @azimuth : AngleRange)
+ end
+ end
+
+ # Priority zone
+ struct PriorityZone
+ include JSON::Serializable
+
+ getter id : Int32
+ getter enabled : Bool
+ getter weight : Float32
+ getter elevation : AngleRange
+ getter azimuth : AngleRange
+
+ def initialize(@id : Int32, @enabled : Bool, @weight : Float32, @elevation : AngleRange, @azimuth : AngleRange)
+ end
+ end
+
+ # Denoiser setting
+ struct Denoiser
+ include JSON::Serializable
+
+ getter setting : String
+
+ def initialize(@setting : String)
+ end
+ end
+
+ # Firmware update state
+ struct FirmwareUpdateState
+ include JSON::Serializable
+
+ getter deviceVersion : String
+ getter danteVersion : String
+ getter state : String
+ getter progress : Int32
+ getter lastStatus : String
+
+ def initialize(@deviceVersion : String, @danteVersion : String, @state : String, @progress : Int32, @lastStatus : String)
+ end
+ end
+
+ # SSE Subscription processor
+ class SubscriptionProcessor
+ getter session_uuid : String?
+ getter base_url : String
+ getter username : String
+ getter password : String
+ getter subscribed_resources : Array(String)
+ getter running : Bool = false
+
+ private getter client : HTTP::Client?
+ private getter callback : Proc(String, JSON::Any, Nil)?
+ private getter error_callback : Proc(String, Nil)?
+ private getter reconnect_attempts : Int32 = 0
+ private getter max_reconnect_attempts : Int32 = 10
+ private getter base_reconnect_delay : Time::Span = 1.second
+ private getter max_reconnect_delay : Time::Span = 5.seconds
+
+ def initialize(@base_url : String, @username : String, @password : String)
+ @subscribed_resources = Array(String).new
+ @running = false
+ end
+
+ def on_data(&block : String, JSON::Any -> Nil)
+ @callback = block
+ end
+
+ def on_error(&block : String -> Nil)
+ @error_callback = block
+ end
+
+ def start
+ return if @running
+ @running = true
+ @reconnect_attempts = 0
+ connect
+ end
+
+ def stop
+ @running = false
+ @client.try(&.close)
+ @client = nil
+ @session_uuid = nil
+ end
+
+ def subscribe_to_resources(resources : Array(String))
+ return unless session_uuid = @session_uuid
+ return if resources.empty?
+
+ uri = URI.parse(@base_url)
+ client = HTTP::Client.new(uri.host.not_nil!, uri.port)
+ client.basic_auth(@username, @password)
+
+ begin
+ response = client.put("/api/ssc/state/subscriptions/#{session_uuid}",
+ headers: HTTP::Headers{"Content-Type" => "application/json"},
+ body: resources.to_json)
+
+ if response.success?
+ @subscribed_resources.clear
+ @subscribed_resources.concat(resources)
+ else
+ @error_callback.try(&.call("Failed to subscribe to resources: #{response.status_code}"))
+ end
+ rescue ex
+ @error_callback.try(&.call("Error subscribing to resources: #{ex.message}"))
+ ensure
+ client.close
+ end
+ end
+
+ def add_resources(resources : Array(String))
+ return unless session_uuid = @session_uuid
+ return if resources.empty?
+
+ uri = URI.parse(@base_url)
+ client = HTTP::Client.new(uri.host.not_nil!, uri.port)
+ client.basic_auth(@username, @password)
+
+ begin
+ response = client.put("/api/ssc/state/subscriptions/#{session_uuid}/add",
+ headers: HTTP::Headers{"Content-Type" => "application/json"},
+ body: resources.to_json)
+
+ if response.success?
+ @subscribed_resources.concat(resources)
+ else
+ @error_callback.try(&.call("Failed to add resources: #{response.status_code}"))
+ end
+ rescue ex
+ @error_callback.try(&.call("Error adding resources: #{ex.message}"))
+ ensure
+ client.close
+ end
+ end
+
+ def remove_resources(resources : Array(String))
+ return unless session_uuid = @session_uuid
+ return if resources.empty?
+
+ uri = URI.parse(@base_url)
+ client = HTTP::Client.new(uri.host.not_nil!, uri.port)
+ client.basic_auth(@username, @password)
+
+ begin
+ response = client.put("/api/ssc/state/subscriptions/#{session_uuid}/remove",
+ headers: HTTP::Headers{"Content-Type" => "application/json"},
+ body: resources.to_json)
+
+ if response.success?
+ resources.each { |resource| @subscribed_resources.delete(resource) }
+ else
+ @error_callback.try(&.call("Failed to remove resources: #{response.status_code}"))
+ end
+ rescue ex
+ @error_callback.try(&.call("Error removing resources: #{ex.message}"))
+ ensure
+ client.close
+ end
+ end
+
+ private def connect
+ return unless @running
+
+ uri = URI.parse(@base_url)
+ client = HTTP::Client.new(uri.host.not_nil!, uri.port)
+ client.basic_auth(@username, @password)
+ @client = client
+
+ begin
+ client.exec("GET", "/api/ssc/state/subscriptions") do |response|
+ if response.success?
+ @reconnect_attempts = 0
+
+ # Extract session UUID from Content-Location header
+ if location = response.headers["Content-Location"]?
+ @session_uuid = location.split("/").last
+ end
+
+ # Process the SSE stream
+ process_sse_stream(response.body_io)
+ else
+ handle_connection_error("HTTP error: #{response.status_code}")
+ end
+ end
+ rescue ex
+ handle_connection_error("Connection error: #{ex.message}")
+ end
+ end
+
+ private def process_sse_stream(io : IO)
+ buffer = ""
+ current_event_type = EventType::Message
+
+ while @running
+ begin
+ line = io.gets
+ break if line.nil?
+
+ line = line.strip
+
+ if line.empty?
+ # End of event, process if we have data
+ if !buffer.empty?
+ process_event(current_event_type, buffer)
+ buffer = ""
+ current_event_type = EventType::Message
+ end
+ elsif line.starts_with?("event:")
+ current_event_type = EventType.from_string(line[6..].strip)
+ elsif line.starts_with?("data:")
+ data_line = line[5..].strip
+ buffer += data_line
+ end
+ rescue ex
+ @error_callback.try(&.call("Error reading SSE stream: #{ex.message}"))
+ break
+ end
+ end
+
+ # Connection ended, schedule reconnect if still running
+ if @running
+ handle_connection_error("SSE stream ended")
+ end
+ end
+
+ private def process_event(event_type : EventType, data : String)
+ case event_type
+ when .open?
+ begin
+ parsed_data = JSON.parse(data)
+ if session_uuid = parsed_data["sessionUUID"]?.try(&.as_s)
+ @session_uuid = session_uuid
+ end
+ rescue JSON::ParseException
+ @error_callback.try(&.call("Failed to parse open event data"))
+ end
+ when .message?
+ begin
+ parsed_data = JSON.parse(data)
+ # Process each resource update in the data
+ parsed_data.as_h.each do |resource_path, resource_data|
+ @callback.try(&.call(resource_path, resource_data))
+ end
+ rescue JSON::ParseException
+ @error_callback.try(&.call("Failed to parse message event data"))
+ end
+ when .close?
+ @running = false
+ @session_uuid = nil
+ end
+ end
+
+ private def handle_connection_error(error : String)
+ @error_callback.try(&.call(error))
+
+ return unless @running
+ return if @reconnect_attempts >= @max_reconnect_attempts
+
+ @reconnect_attempts += 1
+ delay = calculate_reconnect_delay
+
+ spawn do
+ sleep delay
+ connect if @running
+ end
+ end
+
+ private def calculate_reconnect_delay : Time::Span
+ # Exponential backoff with jitter
+ delay_seconds = [@base_reconnect_delay.seconds * (2 ** (@reconnect_attempts - 1)), @max_reconnect_delay.seconds].min
+ jitter = Random.rand(0.1..0.3) * delay_seconds
+ (delay_seconds + jitter).seconds
+ end
+ end
+end
diff --git a/drivers/sennheiser/sscv2_spec.cr b/drivers/sennheiser/sscv2_spec.cr
new file mode 100644
index 00000000000..29fe8b03e06
--- /dev/null
+++ b/drivers/sennheiser/sscv2_spec.cr
@@ -0,0 +1,314 @@
+require "placeos-driver/spec"
+require "./sscv2"
+
+DriverSpecs.mock_driver "Sennheiser::SSCv2Driver" do
+ settings({
+ basic_auth: {
+ username: "api",
+ password: "test_password",
+ },
+ running_specs: true,
+ subscription_resources: ["/api/device/site"] of String,
+ })
+
+ # Test device identity API
+ exec(:device_identity)
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ request.method.should eq("GET")
+ request.path.should eq("/api/device/identity")
+
+ response.status_code = 200
+ response << {
+ "product": "TeamConnect Ceiling Medium",
+ "hardwareRevision": "1.0",
+ "serial": "TCC001234",
+ "vendor": "Sennheiser",
+ }.to_json
+ end
+
+ # Test device site API
+ exec(:device_site)
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ request.method.should eq("GET")
+ request.path.should eq("/api/device/site")
+
+ response.status_code = 200
+ response << {
+ "deviceName": "Conference Room A",
+ "location": "Building 1, Floor 2",
+ "position": "Main Campus",
+ }.to_json
+ end
+
+ # Test device state API
+ exec(:device_state)
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ request.method.should eq("GET")
+ request.path.should eq("/api/device/state")
+
+ response.status_code = 200
+ response << {
+ "state": "Ok",
+ "warnings": [] of String,
+ }.to_json
+ end
+
+ # Test SSC version API
+ exec(:ssc_version)
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ request.method.should eq("GET")
+ request.path.should eq("/api/ssc/version")
+
+ response.status_code = 200
+ response << {
+ "version": "2.0",
+ "api_version": "v2",
+ }.to_json
+ end
+
+ # Test setting device name
+ exec(:set_device_name, "New Room Name")
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ headers["Content-Type"]?.should eq("application/json")
+ request.method.should eq("PUT")
+ request.path.should eq("/api/device/site")
+
+ body = JSON.parse(request.body.not_nil!)
+ body["deviceName"]?.should eq("New Room Name")
+
+ response.status_code = 200
+ response << {
+ "deviceName": "New Room Name",
+ "location": "Building 1, Floor 2",
+ "position": "Main Campus",
+ }.to_json
+ end
+
+ # Test setting device location
+ exec(:set_device_location, "Building 2, Floor 3")
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ headers["Content-Type"]?.should eq("application/json")
+ request.method.should eq("PUT")
+ request.path.should eq("/api/device/site")
+
+ body = JSON.parse(request.body.not_nil!)
+ body["location"]?.should eq("Building 2, Floor 3")
+
+ response.status_code = 200
+ response << {
+ "deviceName": "Conference Room A",
+ "location": "Building 2, Floor 3",
+ "position": "Main Campus",
+ }.to_json
+ end
+
+ # Test setting device position
+ exec(:set_device_position, "Secondary Campus")
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ headers["Content-Type"]?.should eq("application/json")
+ request.method.should eq("PUT")
+ request.path.should eq("/api/device/site")
+
+ body = JSON.parse(request.body.not_nil!)
+ body["position"]?.should eq("Secondary Campus")
+
+ response.status_code = 200
+ response << {
+ "deviceName": "Conference Room A",
+ "location": "Building 1, Floor 2",
+ "position": "Secondary Campus",
+ }.to_json
+ end
+
+ # Test subscription status (should return empty when running specs)
+ result = exec(:get_subscription_status)
+ status = result.get
+ status.should_not be_nil
+ if status_hash = status.try(&.as_h)
+ status_hash["session_uuid"]?.should eq("")
+ status_hash["running"]?.should eq(false)
+ end
+
+ # Test that subscription methods don't crash when running specs
+ exec(:subscribe_to_resources, ["/api/device/info"])
+ exec(:add_subscription_resources, ["/api/device/status"])
+ exec(:remove_subscription_resources, ["/api/device/info"])
+
+ # Note: In production (running_specs = false/nil), the driver automatically
+ # subscribes to /api/device/status and /api/device/info in addition to
+ # any manually configured subscription_resources
+
+ # Test SSE event parsing in models
+ event = Sennheiser::SSCv2::SSEEvent.parse_line("event: open")
+ event.should_not be_nil
+ event.not_nil!.event_type.should eq(Sennheiser::SSCv2::EventType::Open)
+
+ data_line = "data: {\"name\": \"Test Device\"}"
+ event = Sennheiser::SSCv2::SSEEvent.parse_line(data_line)
+ event.should_not be_nil
+ event.not_nil!.event_type.should eq(Sennheiser::SSCv2::EventType::Message)
+ event.not_nil!.data["name"]?.should eq("Test Device")
+
+ event = Sennheiser::SSCv2::SSEEvent.parse_line("")
+ event.should be_nil
+
+ event = Sennheiser::SSCv2::SSEEvent.parse_line("data: invalid json")
+ event.should be_nil
+
+ # Test event type parsing
+ Sennheiser::SSCv2::EventType.from_string("open").should eq(Sennheiser::SSCv2::EventType::Open)
+ Sennheiser::SSCv2::EventType.from_string("OPEN").should eq(Sennheiser::SSCv2::EventType::Open)
+ Sennheiser::SSCv2::EventType.from_string("message").should eq(Sennheiser::SSCv2::EventType::Message)
+ Sennheiser::SSCv2::EventType.from_string("").should eq(Sennheiser::SSCv2::EventType::Message)
+ Sennheiser::SSCv2::EventType.from_string("close").should eq(Sennheiser::SSCv2::EventType::Close)
+ Sennheiser::SSCv2::EventType.from_string("unknown").should eq(Sennheiser::SSCv2::EventType::Message)
+
+ # Test subscription processor initialization
+ processor = Sennheiser::SSCv2::SubscriptionProcessor.new("https://device.local", "api", "password")
+ processor.base_url.should eq("https://device.local")
+ processor.username.should eq("api")
+ processor.password.should eq("password")
+ processor.running.should eq(false)
+ processor.subscribed_resources.should be_empty
+ processor.session_uuid.should be_nil
+
+ # Test JSON serialization models
+ site = Sennheiser::SSCv2::DeviceSite.new("Test Room", "Building 1", "Campus A")
+ json = site.to_json
+ parsed = Sennheiser::SSCv2::DeviceSite.from_json(json)
+ parsed.deviceName.should eq("Test Room")
+ parsed.location.should eq("Building 1")
+ parsed.position.should eq("Campus A")
+
+ status_obj = Sennheiser::SSCv2::SubscriptionStatus.new("/api/ssc/state/subscriptions/123", "123")
+ json = status_obj.to_json
+ parsed_status = Sennheiser::SSCv2::SubscriptionStatus.from_json(json)
+ parsed_status.path.should eq("/api/ssc/state/subscriptions/123")
+ parsed_status.sessionUUID.should eq("123")
+
+ error = Sennheiser::SSCv2::ErrorResponse.new("/api/device/invalid", 404)
+ json = error.to_json
+ parsed_error = Sennheiser::SSCv2::ErrorResponse.from_json(json)
+ parsed_error.path.should eq("/api/device/invalid")
+ parsed_error.error.should eq(404)
+
+ # === Test AudioMuteable Interface ===
+
+ # Test mute_audio method (Interface::AudioMuteable)
+ exec(:mute_audio, true)
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ headers["Content-Type"]?.should eq("application/json")
+ request.method.should eq("PUT")
+ request.path.should eq("/api/audio/outputs/global/mute")
+
+ body = JSON.parse(request.body.not_nil!)
+ body["enabled"]?.should eq(true)
+
+ response.status_code = 200
+ response << {
+ "enabled" => true,
+ }.to_json
+ end
+
+ # Test mute_audio unmute (Interface::AudioMuteable)
+ exec(:mute_audio, false)
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ headers["Content-Type"]?.should eq("application/json")
+ request.method.should eq("PUT")
+ request.path.should eq("/api/audio/outputs/global/mute")
+
+ body = JSON.parse(request.body.not_nil!)
+ body["enabled"]?.should eq(false)
+
+ response.status_code = 200
+ response << {
+ "enabled" => false,
+ }.to_json
+ end
+
+ # Test mute_audio with index parameter (should still work, index ignored for global mute)
+ exec(:mute_audio, true, 1)
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ headers["Content-Type"]?.should eq("application/json")
+ request.method.should eq("PUT")
+ request.path.should eq("/api/audio/outputs/global/mute")
+
+ body = JSON.parse(request.body.not_nil!)
+ body["enabled"]?.should eq(true)
+
+ response.status_code = 200
+ response << {
+ "enabled" => true,
+ }.to_json
+ end
+
+ # Test convenience mute method
+ exec(:mute, true)
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ headers["Content-Type"]?.should eq("application/json")
+ request.method.should eq("PUT")
+ request.path.should eq("/api/audio/outputs/global/mute")
+
+ body = JSON.parse(request.body.not_nil!)
+ body["enabled"]?.should eq(true)
+
+ response.status_code = 200
+ response << {
+ "enabled" => true,
+ }.to_json
+ end
+
+ # Test convenience unmute method
+ exec(:unmute)
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ headers["Content-Type"]?.should eq("application/json")
+ request.method.should eq("PUT")
+ request.path.should eq("/api/audio/outputs/global/mute")
+
+ body = JSON.parse(request.body.not_nil!)
+ body["enabled"]?.should eq(false)
+
+ response.status_code = 200
+ response << {
+ "enabled" => false,
+ }.to_json
+ end
+
+ # Test audio global mute get status
+ exec(:audio_global_mute)
+ expect_http_request do |request, response|
+ headers = request.headers
+ headers["Authorization"]?.should eq("Basic #{Base64.strict_encode("api:test_password")}")
+ request.method.should eq("GET")
+ request.path.should eq("/api/audio/outputs/global/mute")
+
+ response.status_code = 200
+ response << {
+ "enabled" => false,
+ }.to_json
+ end
+end
diff --git a/drivers/sennheiser/tcc2_sscv1.cr b/drivers/sennheiser/tcc2_sscv1.cr
new file mode 100644
index 00000000000..244a5132253
--- /dev/null
+++ b/drivers/sennheiser/tcc2_sscv1.cr
@@ -0,0 +1,610 @@
+require "placeos-driver"
+require "placeos-driver/interface/muteable"
+
+class Sennheiser::TCC2SSCv1 < PlaceOS::Driver
+ include Interface::AudioMuteable
+
+ descriptive_name "Sennheiser TCC2 Microphone (SSCv1)"
+ generic_name :TCC2
+ description "Driver for Sennheiser TCC2 TeamConnect Ceiling Microphone using Sound Control Protocol v1 (SSCV1). Uses UDP port 45 with JSON messages following exact protocol specification."
+
+ udp_port 45
+
+ default_settings({
+ poll_interval: 30, # seconds
+ })
+
+ @poll_interval : Int32 = 30
+
+ def on_load
+ on_update
+ end
+
+ def on_update
+ @poll_interval = setting?(Int32, :poll_interval) || 30
+ end
+
+ def connected
+ # Get protocol version first
+ get_osc_version
+ # Get initial device state
+ get_device_identity
+ get_audio_mute_status
+
+ # Schedule periodic status polling
+ schedule.every(@poll_interval.seconds, immediate: true) do
+ query_device_status
+ end
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ def received(data, task)
+ data = String.new(data)
+ logger.debug { "Received: #{data}" }
+
+ begin
+ # Parse JSON response
+ message = JSON.parse(data)
+
+ if task
+ # Handle response to a specific request
+ handle_response(message, task)
+ else
+ # Handle unsolicited messages (status updates, notifications)
+ handle_notification(message)
+ end
+ rescue e : JSON::ParseException
+ logger.warn { "Failed to parse JSON: #{e.message}" }
+ task.try(&.abort("Invalid JSON response"))
+ end
+ end
+
+ # === Interface::AudioMuteable Implementation ===
+
+ def mute_audio(state : Bool = true, index : Int32 | String = 0)
+ set_mute(state)
+ end
+
+ # === OSC Protocol Methods ===
+
+ def get_osc_version
+ message = {"osc" => {"version" => nil}}
+ send_command(message)
+ end
+
+ def get_osc_ping
+ message = {"osc" => {"ping" => nil}}
+ send_command(message)
+ end
+
+ # === Audio Control Methods (following exact SSCV1 protocol) ===
+
+ def set_mute(muted : Bool)
+ message = {"audio" => {"mute" => muted}}
+ send_command(message, name: "mute")
+ end
+
+ def get_audio_mute_status
+ message = {"audio" => {"mute" => nil}}
+ send_command(message)
+ end
+
+ def get_audio_room_in_use
+ message = {"audio" => {"room_in_use" => nil}}
+ send_command(message)
+ end
+
+ def set_audio_installation_type(type : String)
+ # Valid options: "flush_mount", "suspended"
+ unless ["flush_mount", "suspended"].includes?(type)
+ raise ArgumentError.new("Invalid installation type: #{type}")
+ end
+ message = {"audio" => {"installation_type" => type}}
+ send_command(message, name: "installation_type")
+ end
+
+ def get_audio_installation_type
+ message = {"audio" => {"installation_type" => nil}}
+ send_command(message)
+ end
+
+ # === Audio Output Controls ===
+
+ def set_audio_out1_attenuation(level : Int32)
+ # Range: -18 to 0 dB
+ clamped_level = level.clamp(-18, 0)
+ message = {"audio" => {"out1" => {"attenuation" => clamped_level}}}
+ send_command(message, name: "out1_attenuation")
+ end
+
+ def get_audio_out1_attenuation
+ message = {"audio" => {"out1" => {"attenuation" => nil}}}
+ send_command(message)
+ end
+
+ def set_audio_out2_gain(level : Int32)
+ # Range: 0 to 24 dB (Dante output)
+ clamped_level = level.clamp(0, 24)
+ message = {"audio" => {"out2" => {"gain" => clamped_level}}}
+ send_command(message, name: "out2_gain")
+ end
+
+ def get_audio_out2_gain
+ message = {"audio" => {"out2" => {"gain" => nil}}}
+ send_command(message)
+ end
+
+ # === Audio Reference Controls ===
+
+ def set_audio_ref1_gain(level : Int32)
+ # Range: -60 to 10 dB (AEC Reference gain)
+ clamped_level = level.clamp(-60, 10)
+ message = {"audio" => {"ref1" => {"gain" => clamped_level}}}
+ send_command(message, name: "ref1_gain")
+ end
+
+ def get_audio_ref1_gain
+ message = {"audio" => {"ref1" => {"gain" => nil}}}
+ send_command(message)
+ end
+
+ def set_audio_ref1_farend_auto_adjust(enable : Bool)
+ message = {"audio" => {"ref1" => {"farend_auto_adjust_enable" => enable}}}
+ send_command(message, name: "farend_auto_adjust")
+ end
+
+ def get_audio_ref1_farend_auto_adjust
+ message = {"audio" => {"ref1" => {"farend_auto_adjust_enable" => nil}}}
+ send_command(message)
+ end
+
+ # === Metering Methods ===
+
+ def get_meter_beam_elevation
+ message = {"m" => {"beam" => {"elevation" => nil}}}
+ send_command(message)
+ end
+
+ def get_meter_beam_azimuth
+ message = {"m" => {"beam" => {"azimuth" => nil}}}
+ send_command(message)
+ end
+
+ def get_meter_input_peak
+ message = {"m" => {"in1" => {"peak" => nil}}}
+ send_command(message)
+ end
+
+ def get_meter_ref1_rms
+ message = {"m" => {"ref1" => {"rms" => nil}}}
+ send_command(message)
+ end
+
+ # === Device Control Methods ===
+
+ def set_device_identification_visual(enable : Bool)
+ message = {"device" => {"identification" => {"visual" => enable}}}
+ send_command(message, name: "identification")
+ end
+
+ def get_device_identification_visual
+ message = {"device" => {"identification" => {"visual" => nil}}}
+ send_command(message)
+ end
+
+ def get_device_identity
+ # Get all device identity information
+ get_device_identity_version
+ get_device_identity_vendor
+ get_device_identity_product
+ get_device_identity_serial
+ get_device_identity_hw_revision
+ end
+
+ def get_device_identity_version
+ message = {"device" => {"identity" => {"version" => nil}}}
+ send_command(message)
+ end
+
+ def get_device_identity_vendor
+ message = {"device" => {"identity" => {"vendor" => nil}}}
+ send_command(message)
+ end
+
+ def get_device_identity_product
+ message = {"device" => {"identity" => {"product" => nil}}}
+ send_command(message)
+ end
+
+ def get_device_identity_serial
+ message = {"device" => {"identity" => {"serial" => nil}}}
+ send_command(message)
+ end
+
+ def get_device_identity_hw_revision
+ message = {"device" => {"identity" => {"hw_revision" => nil}}}
+ send_command(message)
+ end
+
+ def set_device_name(name : String)
+ # Name must be 8 chars max, start with letter, end with letter/digit
+ if name.size > 8
+ raise ArgumentError.new("Device name must be 8 characters or less")
+ end
+ message = {"device" => {"name" => name}}
+ send_command(message, name: "device_name")
+ end
+
+ def get_device_name
+ message = {"device" => {"name" => nil}}
+ send_command(message)
+ end
+
+ def set_device_location(location : String)
+ # Max 100 characters
+ if location.size > 100
+ raise ArgumentError.new("Device location must be 100 characters or less")
+ end
+ message = {"device" => {"location" => location}}
+ send_command(message, name: "device_location")
+ end
+
+ def get_device_location
+ message = {"device" => {"location" => nil}}
+ send_command(message)
+ end
+
+ def set_device_position(position : String)
+ # Max 30 characters
+ if position.size > 30
+ raise ArgumentError.new("Device position must be 30 characters or less")
+ end
+ message = {"device" => {"position" => position}}
+ send_command(message, name: "device_position")
+ end
+
+ def get_device_position
+ message = {"device" => {"position" => nil}}
+ send_command(message)
+ end
+
+ def device_restart
+ message = {"device" => {"restart" => true}}
+ send_command(message, name: "restart")
+ end
+
+ def device_restore(type : String)
+ # Valid options: "FACTORY_DEFAULTS", "AUDIO_DEFAULTS", "DANTE_FACTORY_DEFAULTS"
+ valid_types = ["FACTORY_DEFAULTS", "AUDIO_DEFAULTS", "DANTE_FACTORY_DEFAULTS"]
+ unless valid_types.includes?(type)
+ raise ArgumentError.new("Invalid restore type: #{type}")
+ end
+ message = {"device" => {"restore" => type}}
+ send_command(message, name: "restore")
+ end
+
+ # === LED Control Methods ===
+
+ def set_device_led_brightness(level : Int32)
+ # Range: 0 to 5 (6 steps, 0 = off)
+ clamped_level = level.clamp(0, 5)
+ message = {"device" => {"led" => {"brightness" => clamped_level}}}
+ send_command(message, name: "led_brightness")
+ end
+
+ def get_device_led_brightness
+ message = {"device" => {"led" => {"brightness" => nil}}}
+ send_command(message)
+ end
+
+ def set_device_led_custom_color(color : String)
+ # Valid colors: LIGHT_GREEN, GREEN, BLUE, RED, YELLOW, ORANGE, CYAN, PINK
+ valid_colors = ["LIGHT_GREEN", "GREEN", "BLUE", "RED", "YELLOW", "ORANGE", "CYAN", "PINK"]
+ unless valid_colors.includes?(color)
+ raise ArgumentError.new("Invalid LED color: #{color}")
+ end
+ message = {"device" => {"led" => {"custom" => {"color" => color}}}}
+ send_command(message, name: "led_custom_color")
+ end
+
+ def get_device_led_custom_color
+ message = {"device" => {"led" => {"custom" => {"color" => nil}}}}
+ send_command(message)
+ end
+
+ def set_device_led_custom_active(enable : Bool)
+ message = {"device" => {"led" => {"custom" => {"active" => enable}}}}
+ send_command(message, name: "led_custom_active")
+ end
+
+ def get_device_led_custom_active
+ message = {"device" => {"led" => {"custom" => {"active" => nil}}}}
+ send_command(message)
+ end
+
+ def set_device_led_mic_mute_color(color : String)
+ valid_colors = ["LIGHT_GREEN", "GREEN", "BLUE", "RED", "YELLOW", "ORANGE", "CYAN", "PINK"]
+ unless valid_colors.includes?(color)
+ raise ArgumentError.new("Invalid LED color: #{color}")
+ end
+ message = {"device" => {"led" => {"mic_mute" => {"color" => color}}}}
+ send_command(message, name: "led_mic_mute_color")
+ end
+
+ def get_device_led_mic_mute_color
+ message = {"device" => {"led" => {"mic_mute" => {"color" => nil}}}}
+ send_command(message)
+ end
+
+ def set_device_led_mic_on_color(color : String)
+ valid_colors = ["LIGHT_GREEN", "GREEN", "BLUE", "RED", "YELLOW", "ORANGE", "CYAN", "PINK"]
+ unless valid_colors.includes?(color)
+ raise ArgumentError.new("Invalid LED color: #{color}")
+ end
+ message = {"device" => {"led" => {"mic_on" => {"color" => color}}}}
+ send_command(message, name: "led_mic_on_color")
+ end
+
+ def get_device_led_mic_on_color
+ message = {"device" => {"led" => {"mic_on" => {"color" => nil}}}}
+ send_command(message)
+ end
+
+ def set_device_led_show_farend_activity(enable : Bool)
+ message = {"device" => {"led" => {"show_farend_activity" => enable}}}
+ send_command(message, name: "led_farend_activity")
+ end
+
+ def get_device_led_show_farend_activity
+ message = {"device" => {"led" => {"show_farend_activity" => nil}}}
+ send_command(message)
+ end
+
+ # === Beam Orientation Methods ===
+
+ def set_beam_orientation_offset(offset : Int32)
+ # Valid options: 0, 90, 180, 270
+ valid_offsets = [0, 90, 180, 270]
+ unless valid_offsets.includes?(offset)
+ raise ArgumentError.new("Invalid beam orientation offset: #{offset}")
+ end
+ message = {"beam" => {"orientation" => {"offset" => offset}}}
+ send_command(message, name: "beam_orientation")
+ end
+
+ def get_beam_orientation_offset
+ message = {"beam" => {"orientation" => {"offset" => nil}}}
+ send_command(message)
+ end
+
+ def set_beam_orientation_visual(enable : Bool)
+ message = {"beam" => {"orientation" => {"visual" => enable}}}
+ send_command(message, name: "beam_visual_orientation")
+ end
+
+ def get_beam_orientation_visual
+ message = {"beam" => {"orientation" => {"visual" => nil}}}
+ send_command(message)
+ end
+
+ # === Convenience Methods ===
+
+ def mute
+ set_mute(true)
+ end
+
+ def unmute
+ set_mute(false)
+ end
+
+ def identify
+ set_device_identification_visual(true)
+ end
+
+ def stop_identify
+ set_device_identification_visual(false)
+ end
+
+ # === Status Query Methods ===
+
+ def query_device_status
+ get_audio_mute_status
+ get_audio_room_in_use
+ get_meter_beam_azimuth
+ get_meter_beam_elevation
+ get_meter_input_peak
+ end
+
+ def status
+ {
+ "protocol_version" => self[:protocol_version]?,
+ "muted" => self[:muted]?,
+ "room_in_use" => self[:room_in_use]?,
+ "beam_azimuth" => self[:beam_azimuth]?,
+ "beam_elevation" => self[:beam_elevation]?,
+ "input_peak_level" => self[:input_peak_level]?,
+ "ref1_rms_level" => self[:ref1_rms_level]?,
+ "device_name" => self[:device_name]?,
+ "device_location" => self[:device_location]?,
+ "device_position" => self[:device_position]?,
+ "firmware_version" => self[:firmware_version]?,
+ "serial_number" => self[:serial_number]?,
+ "led_brightness" => self[:led_brightness]?,
+ "installation_type" => self[:installation_type]?,
+ "out1_attenuation" => self[:out1_attenuation]?,
+ "out2_gain" => self[:out2_gain]?,
+ "ref1_gain" => self[:ref1_gain]?,
+ }
+ end
+
+ # === Private Methods ===
+
+ private def send_command(message : Hash, **options)
+ json_data = message.to_json
+ logger.debug { "Sending: #{json_data}" }
+ send(json_data.to_slice, **options)
+ end
+
+ private def handle_response(message : JSON::Any, task : PlaceOS::Driver::Task)
+ # Check for OSC error format
+ if error_data = message["osc"]?.try(&.["error"]?)
+ error_msg = error_data.to_s
+ logger.warn { "Command failed: #{error_msg}" }
+ task.abort(error_msg)
+ return
+ end
+
+ # Process successful response - update state and notify task
+ update_state_from_message(message)
+ task.success(message)
+ end
+
+ private def handle_notification(message : JSON::Any)
+ logger.debug { "Notification: #{message}" }
+ update_state_from_message(message)
+ end
+
+ private def update_state_from_message(message : JSON::Any)
+ # Handle OSC responses
+ if osc = message["osc"]?
+ if version = osc["version"]?
+ self[:protocol_version] = version.as_s
+ end
+ end
+
+ # Handle metering responses (m namespace)
+ if m = message["m"]?
+ if beam = m["beam"]?
+ if azimuth = beam["azimuth"]?
+ self[:beam_azimuth] = azimuth.as_i unless azimuth.raw.nil?
+ end
+ if elevation = beam["elevation"]?
+ self[:beam_elevation] = elevation.as_i unless elevation.raw.nil?
+ end
+ end
+ if in1 = m["in1"]?
+ if peak = in1["peak"]?
+ self[:input_peak_level] = peak.as_i unless peak.raw.nil?
+ end
+ end
+ if ref1 = m["ref1"]?
+ if rms = ref1["rms"]?
+ self[:ref1_rms_level] = rms.as_i unless rms.raw.nil?
+ end
+ end
+ end
+
+ # Handle audio responses
+ if audio = message["audio"]?
+ if mute = audio["mute"]?
+ self[:muted] = mute.as_bool unless mute.raw.nil?
+ end
+ if room_in_use = audio["room_in_use"]?
+ self[:room_in_use] = room_in_use.as_bool unless room_in_use.raw.nil?
+ end
+ if installation_type = audio["installation_type"]?
+ self[:installation_type] = installation_type.as_s unless installation_type.raw.nil?
+ end
+
+ # Audio output controls
+ if out1 = audio["out1"]?
+ if attenuation = out1["attenuation"]?
+ self[:out1_attenuation] = attenuation.as_i unless attenuation.raw.nil?
+ end
+ end
+ if out2 = audio["out2"]?
+ if gain = out2["gain"]?
+ self[:out2_gain] = gain.as_i unless gain.raw.nil?
+ end
+ end
+ if ref1 = audio["ref1"]?
+ if gain = ref1["gain"]?
+ self[:ref1_gain] = gain.as_i unless gain.raw.nil?
+ end
+ if farend_auto = ref1["farend_auto_adjust_enable"]?
+ self[:ref1_farend_auto_adjust] = farend_auto.as_bool unless farend_auto.raw.nil?
+ end
+ end
+ end
+
+ # Handle device responses
+ if device = message["device"]?
+ if identity = device["identity"]?
+ if version = identity["version"]?
+ self[:firmware_version] = version.as_s
+ end
+ if vendor = identity["vendor"]?
+ self[:vendor] = vendor.as_s
+ end
+ if product = identity["product"]?
+ self[:product] = product.as_s
+ end
+ if serial = identity["serial"]?
+ self[:serial_number] = serial.as_s
+ end
+ if hw_revision = identity["hw_revision"]?
+ self[:hw_revision] = hw_revision.as_s
+ end
+ end
+
+ if identification = device["identification"]?
+ if visual = identification["visual"]?
+ self[:identification_visual] = visual.as_bool unless visual.raw.nil?
+ end
+ end
+
+ if name = device["name"]?
+ self[:device_name] = name.as_s unless name.raw.nil?
+ end
+ if location = device["location"]?
+ self[:device_location] = location.as_s unless location.raw.nil?
+ end
+ if position = device["position"]?
+ self[:device_position] = position.as_s unless position.raw.nil?
+ end
+
+ # LED responses
+ if led = device["led"]?
+ if brightness = led["brightness"]?
+ self[:led_brightness] = brightness.as_i unless brightness.raw.nil?
+ end
+ if custom = led["custom"]?
+ if color = custom["color"]?
+ self[:led_custom_color] = color.as_s unless color.raw.nil?
+ end
+ if active = custom["active"]?
+ self[:led_custom_active] = active.as_bool unless active.raw.nil?
+ end
+ end
+ if mic_mute = led["mic_mute"]?
+ if color = mic_mute["color"]?
+ self[:led_mic_mute_color] = color.as_s unless color.raw.nil?
+ end
+ end
+ if mic_on = led["mic_on"]?
+ if color = mic_on["color"]?
+ self[:led_mic_on_color] = color.as_s unless color.raw.nil?
+ end
+ end
+ if farend_activity = led["show_farend_activity"]?
+ self[:led_farend_activity] = farend_activity.as_bool unless farend_activity.raw.nil?
+ end
+ end
+ end
+
+ # Handle beam orientation responses
+ if beam = message["beam"]?
+ if orientation = beam["orientation"]?
+ if offset = orientation["offset"]?
+ self[:beam_orientation_offset] = offset.as_i unless offset.raw.nil?
+ end
+ if visual = orientation["visual"]?
+ self[:beam_orientation_visual] = visual.as_bool unless visual.raw.nil?
+ end
+ end
+ end
+ end
+end
diff --git a/drivers/sennheiser/tcc2_sscv1_spec.cr b/drivers/sennheiser/tcc2_sscv1_spec.cr
new file mode 100644
index 00000000000..dd3bf7c3db8
--- /dev/null
+++ b/drivers/sennheiser/tcc2_sscv1_spec.cr
@@ -0,0 +1,193 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Sennheiser::TCC2SSCv1" do
+ settings({
+ poll_interval: 30,
+ })
+
+ # Expect initial messages from connected method (updated to match new SSCV1 protocol)
+ # get_osc_version
+ should_send(%({"osc":{"version":null}}))
+ responds(%({"osc":{"version":"1.2"}}))
+
+ # get_device_identity (multiple calls)
+ should_send(%({"device":{"identity":{"version":null}}}))
+ responds(%({"device":{"identity":{"version":"1.0.0"}}}))
+ should_send(%({"device":{"identity":{"vendor":null}}}))
+ responds(%({"device":{"identity":{"vendor":"Sennheiser"}}}))
+ should_send(%({"device":{"identity":{"product":null}}}))
+ responds(%({"device":{"identity":{"product":"TCC2"}}}))
+ should_send(%({"device":{"identity":{"serial":null}}}))
+ responds(%({"device":{"identity":{"serial":"ABC123456"}}}))
+ should_send(%({"device":{"identity":{"hw_revision":null}}}))
+ responds(%({"device":{"identity":{"hw_revision":"1.0"}}}))
+
+ # get_audio_mute_status
+ should_send(%({"audio":{"mute":null}}))
+ responds(%({"audio":{"mute":false}}))
+
+ # query_device_status calls
+ should_send(%({"audio":{"mute":null}}))
+ responds(%({"audio":{"mute":false}}))
+ should_send(%({"audio":{"room_in_use":null}}))
+ responds(%({"audio":{"room_in_use":false}}))
+ should_send(%({"m":{"beam":{"azimuth":null}}}))
+ responds(%({"m":{"beam":{"azimuth":180}}}))
+ should_send(%({"m":{"beam":{"elevation":null}}}))
+ responds(%({"m":{"beam":{"elevation":45}}}))
+ should_send(%({"m":{"in1":{"peak":null}}}))
+ responds(%({"m":{"in1":{"peak":-25}}}))
+
+ # Test OSC version
+ exec(:get_osc_version)
+ should_send(%({"osc":{"version":null}}))
+ responds(%({"osc":{"version":"1.0"}}))
+ status["protocol_version"]?.should eq("1.0")
+
+ # Test OSC ping
+ exec(:get_osc_ping)
+ should_send(%({"osc":{"ping":null}}))
+ responds(%({"osc":{"ping":"pong"}}))
+
+ # Test mute functionality
+ exec(:set_mute, true)
+ should_send(%({"audio":{"mute":true}}))
+ responds(%({"audio":{"mute":true}}))
+ status["muted"]?.should eq(true)
+
+ # Test unmute functionality
+ exec(:set_mute, false)
+ should_send(%({"audio":{"mute":false}}))
+ responds(%({"audio":{"mute":false}}))
+ status["muted"]?.should eq(false)
+
+ # Test AudioMuteable interface
+ exec(:mute_audio, true, 0)
+ should_send(%({"audio":{"mute":true}}))
+ responds(%({"audio":{"mute":true}}))
+ status["muted"]?.should eq(true)
+
+ # Test convenience mute method
+ exec(:mute)
+ should_send(%({"audio":{"mute":true}}))
+ responds(%({"audio":{"mute":true}}))
+ status["muted"]?.should eq(true)
+
+ # Test convenience unmute method
+ exec(:unmute)
+ should_send(%({"audio":{"mute":false}}))
+ responds(%({"audio":{"mute":false}}))
+ status["muted"]?.should eq(false)
+
+ # Test room in use detection
+ exec(:get_audio_room_in_use)
+ should_send(%({"audio":{"room_in_use":null}}))
+ responds(%({"audio":{"room_in_use":true}}))
+ status["room_in_use"]?.should eq(true)
+
+ # Test installation type setting
+ exec(:set_audio_installation_type, "suspended")
+ should_send(%({"audio":{"installation_type":"suspended"}}))
+ responds(%({"audio":{"installation_type":"suspended"}}))
+ status["installation_type"]?.should eq("suspended")
+
+ # Test out1 attenuation control
+ exec(:set_audio_out1_attenuation, -10)
+ should_send(%({"audio":{"out1":{"attenuation":-10}}}))
+ responds(%({"audio":{"out1":{"attenuation":-10}}}))
+ status["out1_attenuation"]?.should eq(-10)
+
+ # Test out2 gain control
+ exec(:set_audio_out2_gain, 12)
+ should_send(%({"audio":{"out2":{"gain":12}}}))
+ responds(%({"audio":{"out2":{"gain":12}}}))
+ status["out2_gain"]?.should eq(12)
+
+ # Test ref1 gain control
+ exec(:set_audio_ref1_gain, -20)
+ should_send(%({"audio":{"ref1":{"gain":-20}}}))
+ responds(%({"audio":{"ref1":{"gain":-20}}}))
+ status["ref1_gain"]?.should eq(-20)
+
+ # Test metering - beam elevation
+ exec(:get_meter_beam_elevation)
+ should_send(%({"m":{"beam":{"elevation":null}}}))
+ responds(%({"m":{"beam":{"elevation":45}}}))
+ status["beam_elevation"]?.should eq(45)
+
+ # Test metering - beam azimuth
+ exec(:get_meter_beam_azimuth)
+ should_send(%({"m":{"beam":{"azimuth":null}}}))
+ responds(%({"m":{"beam":{"azimuth":180}}}))
+ status["beam_azimuth"]?.should eq(180)
+
+ # Test metering - input peak
+ exec(:get_meter_input_peak)
+ should_send(%({"m":{"in1":{"peak":null}}}))
+ responds(%({"m":{"in1":{"peak":-25}}}))
+ status["input_peak_level"]?.should eq(-25)
+
+ # Test device identification
+ exec(:set_device_identification_visual, true)
+ should_send(%({"device":{"identification":{"visual":true}}}))
+ responds(%({"device":{"identification":{"visual":true}}}))
+ status["identification_visual"]?.should eq(true)
+
+ # Test convenience identify method
+ exec(:identify)
+ should_send(%({"device":{"identification":{"visual":true}}}))
+ responds(%({"device":{"identification":{"visual":true}}}))
+ status["identification_visual"]?.should eq(true)
+
+ # Test device name setting
+ exec(:set_device_name, "MIC_A01")
+ should_send(%({"device":{"name":"MIC_A01"}}))
+ responds(%({"device":{"name":"MIC_A01"}}))
+ status["device_name"]?.should eq("MIC_A01")
+
+ # Test LED brightness control
+ exec(:set_device_led_brightness, 3)
+ should_send(%({"device":{"led":{"brightness":3}}}))
+ responds(%({"device":{"led":{"brightness":3}}}))
+ status["led_brightness"]?.should eq(3)
+
+ # Test LED custom color setting
+ exec(:set_device_led_custom_color, "CYAN")
+ should_send(%({"device":{"led":{"custom":{"color":"CYAN"}}}}))
+ responds(%({"device":{"led":{"custom":{"color":"CYAN"}}}}))
+ status["led_custom_color"]?.should eq("CYAN")
+
+ # Test beam orientation offset
+ exec(:set_beam_orientation_offset, 90)
+ should_send(%({"beam":{"orientation":{"offset":90}}}))
+ responds(%({"beam":{"orientation":{"offset":90}}}))
+ status["beam_orientation_offset"]?.should eq(90)
+
+ # Test device restart
+ exec(:device_restart)
+ should_send(%({"device":{"restart":true}}))
+ responds(%({"device":{"restart":true}}))
+
+ # Test device restore
+ exec(:device_restore, "FACTORY_DEFAULTS")
+ should_send(%({"device":{"restore":"FACTORY_DEFAULTS"}}))
+ responds(%({"device":{"restore":"FACTORY_DEFAULTS"}}))
+
+ # Test clamping - attenuation to valid range
+ exec(:set_audio_out1_attenuation, -25)
+ should_send(%({"audio":{"out1":{"attenuation":-18}}}))
+ responds(%({"audio":{"out1":{"attenuation":-18}}}))
+ status["out1_attenuation"]?.should eq(-18)
+
+ # Test clamping - gain to valid range
+ exec(:set_audio_out2_gain, 30)
+ should_send(%({"audio":{"out2":{"gain":24}}}))
+ responds(%({"audio":{"out2":{"gain":24}}}))
+ status["out2_gain"]?.should eq(24)
+
+ # Test clamping - LED brightness to valid range
+ exec(:set_device_led_brightness, 10)
+ should_send(%({"device":{"led":{"brightness":5}}}))
+ responds(%({"device":{"led":{"brightness":5}}}))
+ status["led_brightness"]?.should eq(5)
+end
diff --git a/drivers/sennheiser/team_connect_ceiling_medium.cr b/drivers/sennheiser/team_connect_ceiling_medium.cr
new file mode 100644
index 00000000000..0ef2cdaab2d
--- /dev/null
+++ b/drivers/sennheiser/team_connect_ceiling_medium.cr
@@ -0,0 +1,93 @@
+require "placeos-driver"
+require "placeos-driver/interface/muteable"
+require "./models"
+
+class Sennheiser::TeamConnectCM < PlaceOS::Driver
+ include Interface::AudioMuteable
+ include Sennheiser::Models
+ descriptive_name "TeamConnect Ceiling Medium"
+ generic_name :TCCM
+
+ uri_base "https://device_ip"
+
+ default_settings({
+ basic_auth: {
+ username: "api",
+ password: "",
+ },
+ device_ip: "192.168.0.1",
+ debug_payload: false,
+ })
+
+ @debug_payload : Bool = false
+
+ def on_load
+ transport.before_request do |request|
+ logger.debug { "performing request: #{request.method} #{request.path}\nheaders: #{request.headers}" }
+ end
+
+ on_update
+ end
+
+ def on_update
+ device_ip = setting(String, :device_ip)
+ @debug_payload = setting?(Bool, :debug_payload) || false
+ end
+
+ # ====================
+ # Audio Mute Interface
+ # ====================
+
+ def mute_audio(state : Bool = true, index : Int32 | String = 0)
+ set_mute_status(state)
+ end
+
+ # SSC API (Sennheiser Sound Control API)
+ def_get :ssc_version, "/api/ssc/version"
+ def_get :ssc_schema, "/api/ssc/schema"
+ def_get :ssc_subscriptions, "/api/ssc/state/subscriptions"
+
+ # Device
+ def_get :device_identity, "/api/device/identity"
+
+ def_get :device_identification, "/api/device/identification"
+ def_put :set_device_dentification, "/api/device/identification", visual: Bool
+
+ def_get :device_site, "/api/device/site"
+ def_get :device_state, "/api/device/state"
+
+ def_get :device_led_ring, "/api/device/leds/ring"
+ def_put :set_device_led_ring, "/api/device/leds/ring", brightness: 0..5, show_farend_activity: Bool, mic_on: MicTuple, mic_mute: MicTuple, mic_custom: MicCustomTuple
+
+ # Audio
+ def_get :mute_status, "/api/audio/outputs/global/mute"
+ def_put :set_mute_status, "/api/audio/outputs/global/mute", enabled: Bool
+
+ def_get :beam_settings, "/api/audio/inputs/microphone/beam"
+ def_put :set_beam_settings, "/api/audio/inputs/microphone/beam", installation_type: InstallationType, source_detection_threshold: DetectionThreshold, offset: 0..330
+
+ def_get :beam_direction, "/api/audio/inputs/microphone/beam/direction"
+ def_get :microphone_input_level, "/api/audio/inputs/microphone/level"
+ def_get :digital_reference_input_level, "/api/audio/inputs/reference/level"
+ def_get :room_in_use, "/api/audio/roomInUse"
+ def_get :room_in_use_activity_level, "/api/audio/roomInUse/activityLevel"
+ def_get :room_in_use_config, "/api/audio/roomInUse/config"
+
+ def_get :analog_output_settings, "/api/audio/outputs/analog"
+ def_put :set_analog_output_settings, "/api/audio/outputs/analog", gain: -18..0, switch: SwitchOutput
+
+ def api_get(resource : String, query : String? = nil)
+ logger.debug { {msg: "GET #{resource}:", query: query.to_s} } if @debug_payload
+ uri = query.presence ? resource + "?#{query}" : resource
+ response = get(uri)
+ raise "failed to get #{resource}, code #{response.status_code}, body: #{response.body}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ def api_put(uri : String, payload : String)
+ logger.debug { {msg: "PUT HTTP Data:", payload: payload} } if @debug_payload
+ response = put(uri, body: payload)
+ raise "failed to invoke put command, code #{response.status_code}, body: #{response.body}" unless response.success?
+ JSON.parse(response.body)
+ end
+end
diff --git a/drivers/sennheiser/team_connect_ceiling_medium_spec.cr b/drivers/sennheiser/team_connect_ceiling_medium_spec.cr
new file mode 100644
index 00000000000..a8ccaf84dec
--- /dev/null
+++ b/drivers/sennheiser/team_connect_ceiling_medium_spec.cr
@@ -0,0 +1,89 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Sennheiser::TeamConnectCM" do
+ settings({
+ basic_auth: {
+ username: "api",
+ password: "password",
+ },
+ device_ip: "192.168.1.0",
+ debug_payload: true,
+ })
+
+ ret_val = exec(:device_identity)
+
+ expect_http_request(2.seconds) do |request, response|
+ auth = Base64.strict_encode("api:password")
+ if request.headers["Authorization"]? == "Basic #{auth}"
+ response.status_code = 200
+ response << device_identity_resp.to_json
+ else
+ response.status_code = 401
+ end
+ end
+
+ ret_val.get.should eq(device_identity_resp)
+
+ ret_val = exec(:set_device_dentification, true)
+
+ expect_http_request(2.seconds) do |request, response|
+ auth = Base64.strict_encode("api:password")
+ io = request.body
+ if io
+ data = io.gets_to_end
+ body = JSON.parse(data)
+ if request.headers["Authorization"]? == "Basic #{auth}"
+ response.status_code = 200
+ response << body.to_json
+ else
+ response.status_code = 401
+ end
+ end
+ end
+
+ ret_val.get.should eq({"visual" => true})
+
+ ret_val = exec(:set_device_led_ring, brightness: 5, show_farend_activity: true, mic_on: {color: "Green"}, mic_mute: {color: "Blue"}, mic_custom: {enabled: true, color: "Green"})
+
+ expect_http_request(2.seconds) do |request, response|
+ auth = Base64.strict_encode("api:password")
+ io = request.body
+ if io
+ data = io.gets_to_end
+ body = JSON.parse(data)
+ if request.headers["Authorization"]? == "Basic #{auth}"
+ response.status_code = 200
+ response << body.to_json
+ else
+ response.status_code = 401
+ end
+ end
+ end
+
+ ret_val.get.try &.as_h["brightness"].should eq(5)
+
+ ret_val = exec(:mute_audio)
+
+ expect_http_request(2.seconds) do |request, response|
+ auth = Base64.strict_encode("api:password")
+ if request.headers["Authorization"]? == "Basic #{auth}"
+ response.status_code = 200
+ response << {enabled: true}.to_json
+ else
+ response.status_code = 401
+ end
+ end
+
+ ret_val.get.should eq({"enabled" => true})
+end
+
+def device_identity_resp
+ %(
+{
+ "product": "TCCM",
+ "hardwareRevision": "1",
+ "serial": "1023456789",
+ "vendor": "Sennheiser electronic GmbH & Co. KG"
+}
+)
+end
diff --git a/drivers/sharp/pn_series.cr b/drivers/sharp/pn_series.cr
new file mode 100644
index 00000000000..b8cb3b30f2c
--- /dev/null
+++ b/drivers/sharp/pn_series.cr
@@ -0,0 +1,292 @@
+require "placeos-driver"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/switchable"
+
+# Documentation: https://aca.im/driver_docs/Sharp/pnl601b.pdf
+# also https://aca.im/driver_docs/Sharp/PN_L802B_operation_guide.pdf
+
+class Sharp::PnSeries < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Muteable
+
+ enum Input
+ DVI = 1
+ HDMI = 10
+ HDMI2 = 13
+ HDMI3 = 18
+ DisplayPort = 14
+ VGA = 2
+ VGA2 = 16
+ Component = 3
+
+ def data
+ "INPS" + self.value.to_s.rjust(4, '0')
+ end
+ end
+
+ include Interface::InputSelection(Input)
+
+ tcp_port 10008
+ descriptive_name "Sharp Monitor"
+ generic_name :Display
+
+ @volume_min : Int32 = 0
+ @volume_max : Int32 = 31
+ @brightness_min : Int32 = 0
+ @brightness_max : Int32 = 31
+ @contrast_min : Int32 = 0
+ @contrast_max : Int32 = 60 # multiply by two when VGA selected
+ @dbl_contrast : Bool = true
+ @model_number : Bool = false
+
+ @vol_status : PlaceOS::Driver::Proxy::Scheduler::TaskWrapper? = nil
+
+ DELIMITER = "\x0D\x0A"
+
+ def on_load
+ transport.tokenizer = Tokenizer.new(DELIMITER)
+ end
+
+ def connected
+ # Will be sent after login is requested (config - wait ready)
+ send_credentials
+
+ schedule.every(60.seconds) do
+ logger.debug { "-- Polling Display" }
+ do_poll
+ end
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ def power(state : Bool)
+ delay = self[:power_on_delay]?.try(&.as_i) || 5
+
+ # If the requested state is different from the current state
+ if state != !!self[:power]?.try(&.as_bool)
+ if state
+ logger.debug { "-- Sharp LCD, requested to power on" }
+ do_send("POWR 1", name: :POWR, timeout: delay.seconds + 15.seconds)
+ self[:warming] = true
+ self[:power] = true
+ do_send("POWR????", name: :POWR, timeout: 10.seconds) # clears warming
+ else
+ logger.debug { "-- Sharp LCD, requested to power off" }
+ do_send("POWR 0", name: :POWR, timeout: 15.seconds)
+ self[:power] = false
+ end
+ end
+
+ power?
+ mute_status(0)
+ volume_status(0)
+ end
+
+ def power?(**options)
+ do_send("POWR????", **options, name: :POWR, timeout: 10.seconds).get
+ self[:power].as_bool
+ end
+
+ # Resets the brightness and contrast settings
+ def reset
+ do_send("ARST 2")
+ end
+
+ def switch_to(input : Input)
+ logger.debug { "-- Sharp LCD, requested to switch to: #{input}" }
+ do_send(input.data, name: :input, delay: 2.seconds, timeout: 20.seconds).get # does an auto adjust on switch to vga
+ video_input(40)
+ brightness_status(40) # higher status than polling commands - lower than input switching (vid then audio is common)
+ contrast_status(40)
+ end
+
+ AUDIO = {
+ audio1: "ASDP 2",
+ audio2: "ASDP 3",
+ dvi: "ASDP 1",
+ dvi_alt: "ASDA 1",
+ hdmi: "ASHP 0",
+ hdmi_3mm: "ASHP 1",
+ hdmi_rca: "ASHP 2",
+ vga: "ASAP 1",
+ component: "ASCA 1",
+ }
+ AUDIO_RESPONSE = AUDIO.to_h.invert
+
+ def switch_audio(input : String)
+ logger.debug { "-- Sharp LCD, requested to switch audio to: #{input}" }
+
+ do_send(AUDIO[input], name: "audio")
+ mute_status(40) # higher status than polling commands - lower than input switching
+ volume_status(40) # Mute response requests volume
+ end
+
+ def auto_adjust
+ do_send("AGIN 1", timeout: 20.seconds)
+ end
+
+ def brightness(val : Int32 | Float64)
+ val = val.to_f.clamp(0.0, 100.0)
+ percentage = val / 100.0
+ brightness = (percentage * @brightness_max.to_f).round_away.to_i
+
+ do_send("VLMP#{brightness.to_s.rjust(4, ' ')}")
+ end
+
+ def contrast(val : Int32 | Float64)
+ val = val.to_f.clamp(0.0, 100.0)
+ percentage = val / 100.0
+ contrast = (percentage * @contrast_max.to_f).round_away.to_i
+
+ # See Sharp manual
+ multiplier = self[:input]? == "VGA" && @dbl_contrast ? 2 : 1
+ contrast = contrast * multiplier
+ do_send("CONT#{contrast.to_s.rjust(4, ' ')}")
+ end
+
+ def volume(val : Int32 | Float64)
+ @vol_status.try(&.cancel)
+ @vol_status = schedule.in(2.seconds) do
+ @vol_status = nil
+ volume_status
+ end
+
+ val = val.to_f.clamp(0.0, 100.0)
+ percentage = val / 100.0
+ vol_actual = (percentage * @volume_max.to_f).round_away.to_i
+
+ do_send("VOLM#{vol_actual.to_s.rjust(4, ' ')}")
+ end
+
+ def volume_up
+ current_volume = status?(Float64, :volume) || 50.0
+ volume(current_volume + 5.0)
+ end
+
+ def volume_down
+ current_volume = status?(Float64, :volume) || 50.0
+ volume(current_volume - 5.0)
+ end
+
+ # There seems to only be audio mute available
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ if layer == MuteLayer::Video
+ logger.warn { "Sharp LCD requested to mute video which is unsupported" }
+ else
+ logger.debug { "Sharp LCD, requested to mute #{state}" }
+ do_send("MUTE #{state ? '1' : '0'}")
+ mute_status(50) # High priority mute status
+ end
+ end
+
+ OPERATION_CODE = {
+ video_input: "INPS",
+ volume_status: "VOLM",
+ mute_status: "MUTE",
+ power_on_delay: "PWOD",
+ contrast_status: "CONT",
+ brightness_status: "VLMP",
+ model_number: "INF1",
+ }
+ {% for name, cmd in OPERATION_CODE %}
+ @[Security(Level::Administrator)]
+ def {{name.id}}(priority : Int32 = 0, **options)
+ data = {{cmd.id.stringify}} + "????"
+ logger.debug { "Sharp sending: #{data}" }
+ do_send(data, **options, priority: priority) # Status polling is a low priority
+ end
+ {% end %}
+
+ def do_poll
+ if power?
+ model_number unless self[:model_number]? # only query the model number if we don't already have it
+ power_on_delay
+ mute_status
+ end
+ end
+
+ private def determine_contrast_mode
+ # As of 09/2015 only the PN-L802B does not have double contrast on RGB input.
+ # All prior models do double the contrast and don't have an L so let's assume it's the L in the model number that determines this for now
+ # (we can confirm the logic as more models are released)
+ @dbl_contrast = false if self[:model_number].as_s.includes?('L')
+ logger.debug { "dbl_contrast is #{@dbl_contrast}" }
+ end
+
+ private def send_credentials
+ do_send(setting?(String?, :username) || "", priority: 100, delay: 500.milliseconds) # , wait: false)
+ # TODO: figure out equivalent in crystal for delay_on_receive
+ do_send(setting?(String?, :password) || "", priority: 100) # , delay_on_receive: 1000)
+ end
+
+ def received(data, task)
+ data = String.new(data[0..-3])
+ logger.debug { "-- Sharp LCD, received: #{data}" }
+
+ if data == "Password:OK"
+ return task.try(&.success("Login successful"))
+ elsif data == "Password:Login incorrect"
+ schedule.in(5.seconds) { send_credentials }
+ return task.try(&.success("Sharp LCD, bad login or logged off. Attempting login.."))
+ elsif data == "OK"
+ return task.try(&.success)
+ elsif data == "WAIT"
+ logger.debug { "-- Sharp LCD, wait" }
+ return
+ elsif data == "ERR"
+ return task.try(&.abort("-- Sharp LCD, error"))
+ elsif data.size < 8 # Out of order send?
+ return task.try(&.abort("Sharp sent out of order response: #{data}"))
+ end
+
+ command, value = data.split
+
+ case command
+ when "POWR" # Power status
+ self[:warming] = false
+ self[:power] = value.to_i > 0
+ when "INPS" # Input status
+ input = Input.from_value?(value.to_i)
+ self[:input] = input || "unknown"
+ logger.debug { "-- Sharp LCD, input #{self[:input]} == #{value}" }
+ when "VOLM" # Volume status
+ vol_percent = (value.to_i.to_f / @volume_max.to_f) * 100.0
+ self[:volume] = vol_percent.round(2) unless self[:audio_mute]?.try(&.as_bool)
+ when "MUTE" # Mute status
+ self[:audio_mute] = (mute = value.to_i == 1)
+ if mute
+ self[:volume] = 0
+ else
+ volume_status(90) # high priority
+ end
+ when "CONT" # Contrast status
+ val = value.to_i / (self[:input]? == "VGA" && @dbl_contrast ? 2 : 1)
+ contrast = (val.to_f / @contrast_max.to_f) * 100.0
+ self[:contrast] = contrast.round(2)
+ when "VLMP" # brightness status
+ brightness = (value.to_i.to_f / @brightness_max.to_f) * 100.0
+ self[:brightness] = brightness.round(2)
+ when "PWOD"
+ self[:power_on_delay] = value.to_i
+ when "INF1"
+ self[:model_number] = value
+ logger.debug { "-- Sharp LCD, model number #{self[:model_number]}" }
+ determine_contrast_mode
+ when "ASDP", "ASDA", "ASHP", "ASAP", "ASCA" # audio switching commands
+ self[:audio_input] = AUDIO_RESPONSE[data] || "unknown"
+ end
+
+ task.try(&.success)
+ end
+
+ private def do_send(data, delay = 100.milliseconds, **options)
+ send("#{data}#{DELIMITER}", **options, delay: delay)
+ end
+end
diff --git a/drivers/sharp/pn_series_spec.cr b/drivers/sharp/pn_series_spec.cr
new file mode 100644
index 00000000000..052afd71955
--- /dev/null
+++ b/drivers/sharp/pn_series_spec.cr
@@ -0,0 +1,76 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Sharp::PnSeries" do
+ # connected
+ # send_credentials
+ should_send("\x0D\x0A")
+ responds("OK\x0D\x0A")
+ should_send("\x0D\x0A")
+ responds("Password:Login incorrect\x0D\x0A")
+
+ # Settings can only be accessed after on_load and connected
+ settings({
+ username: "user",
+ password: "pass",
+ })
+
+ # Retrying send_credentials
+ sleep 5
+ should_send("user\x0D\x0A")
+ responds("OK\x0D\x0A")
+ should_send("pass\x0D\x0A")
+ responds("Password:OK\x0D\x0A")
+
+ exec(:do_poll)
+ should_send("POWR????\x0D\x0A")
+ responds("POWR 001\x0D\x0A")
+ status[:warming].should eq(false)
+ status[:power].should eq(true)
+ should_send("INF1????\x0D\x0A")
+ responds("INF1 P802B\x0D\x0A")
+ status[:model_number].should eq("P802B")
+ should_send("PWOD????\x0D\x0A")
+ responds("PWOD 002\x0D\x0A")
+ status[:power_on_delay].should eq(2)
+ should_send("MUTE????\x0D\x0A")
+ responds("MUTE 000\x0D\x0A")
+ status[:audio_mute].should eq(false)
+ should_send("VOLM????\x0D\x0A")
+ responds("VOLM 010\x0D\x0A")
+ status[:volume].should eq(32.26)
+
+ exec(:switch_to, "hdmi")
+ should_send("INPS0010\x0D\x0A")
+ responds("WAIT\x0D\x0A")
+ responds("OK\x0D\x0A")
+ sleep 2
+ should_send("INPS????\x0D\x0A")
+ responds("INPS 10\x0D\x0A")
+ status[:input].should eq("HDMI")
+ should_send("VLMP????\x0D\x0A")
+ responds("VLMP 15\x0D\x0A")
+ status[:brightness].should eq(48.39)
+ should_send("CONT????\x0D\x0A")
+ responds("CONT 15\x0D\x0A")
+ status[:contrast].should eq(25.0)
+
+ exec(:switch_audio, "component")
+ should_send("ASCA 1\x0D\x0A")
+ responds("ASCA 1\x0D\x0A")
+ status[:audio_input].should eq("component")
+
+ should_send("MUTE????\x0D\x0A")
+ responds("MUTE 000\x0D\x0A")
+
+ should_send("VOLM????\x0D\x0A")
+ responds("VOLM 015\x0D\x0A")
+ status[:volume].should eq(48.39)
+
+ exec(:volume, 100)
+ should_send("VOLM????\x0D\x0A")
+ responds("VOLM 015\x0D\x0A")
+ status[:volume].should eq(48.39)
+
+ should_send("VOLM 31\x0D\x0A")
+ responds("ASCA 1\x0D\x0A")
+end
diff --git a/drivers/shure/intellimix_room.cr b/drivers/shure/intellimix_room.cr
new file mode 100644
index 00000000000..948ce1e2fca
--- /dev/null
+++ b/drivers/shure/intellimix_room.cr
@@ -0,0 +1,228 @@
+require "placeos-driver"
+require "placeos-driver/interface/muteable"
+
+# Documentation: https://www.shure.com/en-US/docs/commandstrings/IntelliMixRoom
+# TCP Port: 2202
+
+class Shure::IntellimixRoom < PlaceOS::Driver
+ include Interface::AudioMuteable
+
+ tcp_port 2202
+ descriptive_name "Shure IntelliMix Room Audio Processor"
+ generic_name :Mixer
+ description "Software-based digital signal processing for Shure networked microphones"
+
+ default_settings({
+ poll_channels: true,
+ channel_count: 8,
+ })
+
+ def connected
+ # Shure uses space + > as the response terminator
+ transport.tokenizer = Tokenizer.new(" >")
+ logger.debug { "-- Polling device status" }
+ get_device_info
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ # Device Information
+ def get_device_info
+ do_send "GET MODEL", name: :get_device_model
+ do_send "GET FW_VER", name: :get_firmware_version
+ do_send "GET DEVICE_ID", name: :get_device_info
+ do_send "GET ALL", name: :get_all
+ end
+
+ def get_all
+ do_send "GET ALL", name: :get_all
+ end
+
+ def get_na_device_name
+ do_send "GET NA_DEVICE_NAME", name: :get_na_device_name
+ end
+
+ def get_onhook_enable
+ do_send "GET ONHOOK_ENABLE", name: :get_onhook_enable
+ end
+
+ def set_onhook_enable(enable : Bool)
+ do_send "SET ONHOOK_ENABLE #{enable ? "ON" : "OFF"}", name: :set_onhook_enable
+ end
+
+ # Presets
+ def get_preset
+ do_send "GET PRESET", name: :get_preset
+ end
+
+ def set_preset(number : Int32)
+ do_send "SET PRESET #{number.to_s(precision: 2)}", name: :set_preset
+ end
+
+ # Channel Commands
+ def get_audio_gain_hi_res(index : Int32)
+ do_send "GET #{index.to_s(precision: 2)} AUDIO_GAIN_HI_RES", name: :get_audio_gain_hi_res
+ end
+
+ def set_audio_gain_hi_res(index : Int32, value : Int32)
+ do_send "SET #{index.to_s(precision: 2)} AUDIO_GAIN_HI_RES #{value.to_s(precision: 4)}", name: :set_audio_gain_hi_res
+ end
+
+ def get_device_audio_mute
+ do_send "GET DEVICE_AUDIO_MUTE", name: :get_device_audio_mute
+ end
+
+ def set_device_audio_mute(mute : Bool)
+ do_send "SET DEVICE_AUDIO_MUTE #{mute ? "ON" : "OFF"}", name: :set_device_audio_mute
+ end
+
+ def get_audio_mute(index : Int32)
+ do_send "GET #{index.to_s(precision: 2)} AUDIO_MUTE", name: :get_audio_mute
+ end
+
+ def set_audio_mute(index : Int32, mute : Bool)
+ do_send "SET #{index.to_s(precision: 2)} AUDIO_MUTE #{mute ? "ON" : "OFF"}", name: :set_audio_mute
+ end
+
+ def get_matrix_mxr_route(input : Int32, output : Int32)
+ do_send "GET #{input.to_s(precision: 2)} MATRIX_MXR_ROUTE #{output.to_s(precision: 2)}", name: :get_matrix_mxr_route
+ end
+
+ def set_matrix_mxr_route(input : Int32, output : Int32, enabled : Bool)
+ do_send "SET #{input.to_s(precision: 2)} MATRIX_MXR_ROUTE #{output.to_s(precision: 2)} #{enabled ? "ON" : "OFF"}", name: :set_matrix_mxr_route
+ end
+
+ def get_matrix_mxr_gain(input : Int32, output : Int32)
+ do_send "GET #{input.to_s(precision: 2)} MATRIX_MXR_GAIN #{output.to_s(precision: 2)}", name: :get_matrix_mxr_gain
+ end
+
+ def set_matrix_mxr_gain(input : Int32, output : Int32, gain : Int32)
+ do_send "SET #{input.to_s(precision: 2)} MATRIX_MXR_GAIN #{output.to_s(precision: 2)} #{gain.to_s(precision: 4)}", name: :set_matrix_mxr_gain
+ end
+
+ def get_automxr_mute(index : Int32)
+ do_send "GET #{index.to_s(precision: 2)} AUTOMXR_MUTE", name: :get_automxr_mute
+ end
+
+ def set_automxr_mute(index : Int32, mute : Bool)
+ do_send "SET #{index.to_s(precision: 2)} AUTOMXR_MUTE #{mute ? "ON" : "OFF"}", name: :set_automxr_mute
+ end
+
+ def get_audio_gain_postgate(index : Int32)
+ do_send "GET #{index.to_s(precision: 2)} AUDIO_GAIN_POSTGATE", name: :get_audio_gain_postgate
+ end
+
+ def set_audio_gain_postgate(index : Int32, gain : Int32)
+ do_send "SET #{index.to_s(precision: 2)} AUDIO_GAIN_POSTGATE #{gain.to_s(precision: 4)}", name: :set_audio_gain_postgate
+ end
+
+ def get_automxr_gate(index : Int32)
+ do_send "GET #{index.to_s(precision: 2)} AUTOMXR_GATE", name: :get_automxr_gate
+ end
+
+ def get_chan_config
+ do_send "GET CHAN_CONFIG", name: :get_chan_config
+ end
+
+ def get_chan_count
+ do_send "GET CHAN_COUNT", name: :get_chan_count
+ end
+
+ def get_lic_exp_date
+ do_send "GET LIC_EXP_DATE", name: :get_lic_exp_date
+ end
+
+ def get_lic_type
+ do_send "GET LIC_TYPE", name: :get_lic_type
+ end
+
+ def get_lic_valid
+ do_send "GET LIC_VALID", name: :get_lic_valid
+ end
+
+ def get_denoiser_enable(index : Int32)
+ do_send "GET #{index.to_s(precision: 2)} DENOISER_ENABLE", name: :get_denoiser_enable
+ end
+
+ def set_denoiser_enable(index : Int32, enable : Bool)
+ do_send "SET #{index.to_s(precision: 2)} DENOISER_ENABLE #{enable ? "ON" : "OFF"}", name: :set_denoiser_enable
+ end
+
+ def get_denoiser_level(index : Int32)
+ do_send "GET #{index.to_s(precision: 2)} DENOISER_LEVEL", name: :get_denoiser_level
+ end
+
+ def set_denoiser_level(index : Int32, level : String)
+ raise "ArgumentError: level must be LOW, MEDIUM or HIGH" unless level.in?(["LOW", "MEDIUM", "HIGH"])
+ do_send "SET #{index.to_s(precision: 2)} DENOISER_LEVEL #{level}", name: :set_denoiser_level
+ end
+
+ # === Interface::AudioMuteable Implementation ===
+
+ def mute_audio(state : Bool = true, index : Int32 | String = 0)
+ set_audio_mute(index.to_i, state)
+ end
+
+ def mute(state : Bool = true)
+ set_device_audio_mute(state)
+ end
+
+ def unmute
+ set_device_audio_mute(false)
+ end
+
+ def received(bytes, task)
+ data = String.new(bytes).strip
+ logger.debug { "-- received: #{data}" }
+
+ response = data.lstrip("< REP ").rstrip(" >")
+ parts = response.split
+ return task.try(&.abort("Empty response")) if parts.empty?
+
+ # Handle error responses
+ if parts.first == "ERR"
+ logger.error { "Device error: #{response}" }
+ return task.try(&.abort(response))
+ end
+
+ # Parse response based on parameter structure
+ case parts.size
+ when 1
+ # Must be ERR, which is handled above
+ when 2
+ # Parameter with 1 value
+ self[parts[0].downcase] = parts[1]
+ when 3
+ # Channel-specific parameter like "nn AUDIO_MUTE sts"
+ channel = parts[0]
+ param = parts[1].downcase
+ value = parts[2]
+ self["#{param}_#{channel}"] = value
+ when 4
+ # Matrix-specific parameter like "1 input MATRIX_MXR_ROUTE output sts"
+ input = parts[0]
+ param = parts[1].downcase
+ output = parts[2]
+ value = parts[3]
+ self["#{param}_#{input}_#{output}"] = value
+ else
+ # Handle multi-part responses or unknown formats
+ logger.warn { "Unknown response format: #{response}" }
+ end
+ task.try(&.success)
+ end
+
+ protected def do_send(*command, **options)
+ cmd = "< #{command.join(" ")} >"
+ logger.debug { "-- sending: #{cmd}" }
+ send(cmd, **options)
+ end
+
+ # def send_command(command : String)
+ # cmd = "<"
+ # logger.debug { "-- sending: #{command}" }
+ # transport.send(command)
+ # end
+end
diff --git a/drivers/shure/intellimix_room_spec.cr b/drivers/shure/intellimix_room_spec.cr
new file mode 100644
index 00000000000..676b9ae66f5
--- /dev/null
+++ b/drivers/shure/intellimix_room_spec.cr
@@ -0,0 +1,32 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Shure::IntellimixRoom" do
+ # Test initial connection and device info queries
+ should_send("< GET MODEL >").responds "< REP MODEL INTELLIMIX_ROOM >"
+ status[:model].should eq("INTELLIMIX_ROOM")
+
+ should_send("< GET FW_VER >").responds "< REP FW_VER 4.7.4 >"
+ status[:fw_ver].should eq("4.7.4")
+
+ should_send("< GET DEVICE_ID >").responds "< REP DEVICE_ID IntelliMix_Room_001 >"
+ status[:device_id].should eq("IntelliMix_Room_001")
+
+ should_send("< GET ALL >")
+
+ # Test presets
+ exec(:get_preset)
+ should_send("< GET PRESET >").responds "< REP PRESET 3 >"
+ status[:preset].should eq(3)
+
+ exec(:set_preset, 5)
+ should_send("< SET PRESET 5 >").responds "< REP PRESET 5 >"
+ status[:preset].should eq(5)
+
+ exec(:set_preset, 10)
+ should_send("< SET PRESET 10 >").responds "< REP PRESET 10 >"
+ status[:preset].should eq(10)
+
+ exec(:get_audio_gain_hi_res, 1)
+ should_send("< GET 01 AUDIO_GAIN_HI_RES >").responds "< REP 01 AUDIO_GAIN_HI_RES 1234 >"
+ status[:audio_gain_hi_res_01].should eq(1234)
+end
diff --git a/drivers/shure/microphone/mxa.cr b/drivers/shure/microphone/mxa.cr
new file mode 100644
index 00000000000..b2066089c5e
--- /dev/null
+++ b/drivers/shure/microphone/mxa.cr
@@ -0,0 +1,218 @@
+require "placeos-driver"
+require "placeos-driver/interface/muteable"
+
+# Documentation: https://aca.im/driver_docs/Shure/MXA910%20command%20strings.pdf
+
+class Shure::Microphone::MXA < PlaceOS::Driver
+ include Interface::AudioMuteable
+
+ tcp_port 2202
+ descriptive_name "Shure Ceiling Array Microphone"
+ generic_name :CeilingMic
+
+ default_settings({
+ send_meter_levels: false,
+ })
+
+ def connected
+ transport.tokenizer = Tokenizer.new(" >")
+
+ schedule.every(60.seconds) do
+ logger.debug { "-- Polling Mics" }
+ do_poll
+ end
+
+ query_all
+ set_meter_rate(0) if setting?(Bool, :send_meter_levels) != true
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ def query_all
+ do_send "GET 0 ALL"
+ end
+
+ def query_device_id
+ do_send "GET DEVICE_ID", name: :device_id
+ end
+
+ def query_firmware
+ do_send "GET FW_VER", name: :firmware
+ end
+
+ # rate in milliseconds
+ def set_meter_rate(rate : Int32)
+ raise "rate must be a number greater than 100, was #{rate}" unless rate == 0 || rate >= 100
+ do_send "SET METER_RATE", rate.to_s, name: :meter_rate
+ end
+
+ # Mute commands
+ def query_mute
+ do_send "GET DEVICE_AUDIO_MUTE"
+ end
+
+ def mute(state : Bool = true)
+ val = state ? "ON" : "OFF"
+ do_send "SET DEVICE_AUDIO_MUTE", val, name: :mute
+ end
+
+ def unmute
+ mute false
+ end
+
+ # part of the mutable interface
+ def mute_audio(state : Bool = true, index : Int32 | String = 0)
+ mute(state)
+ end
+
+ # Preset commands
+ def query_preset
+ do_send "GET PRESET"
+ end
+
+ def preset(number : Int32)
+ raise "must be a number between 1-10, was #{number}" unless number.in?(1..10)
+ do_send "SET PRESET", number.to_s, name: :preset
+ end
+
+ # flash the LED for 30 seconds
+ def flash
+ do_send "SET FLASH ON"
+ end
+
+ enum Colour
+ RED
+ GREEN
+ BLUE
+ PINK
+ PURPLE
+ YELLOW
+ ORANGE
+ WHITE
+ end
+
+ # LED Setup
+ def query_led_state
+ do_send "GET DEV_LED_IN_STATE"
+ end
+
+ def led(on : Bool = true)
+ led_state_muted on
+ led_state_unmuted on
+ end
+
+ def query_led_colour_muted
+ do_send "GET LED_COLOR_MUTED"
+ end
+
+ # Supported colours: :RED, :GREEN, :BLUE, :PINK, :PURPLE, :YELLOW, :ORANGE, :WHITE
+ def led_colour_muted(colour : Colour)
+ do_send "SET LED_COLOR_MUTED", colour.to_s.upcase, name: :muted_color
+ end
+
+ def query_led_colour_unmuted
+ do_send "GET LED_COLOR_UNMUTED"
+ end
+
+ def led_colour_unmuted(colour : Colour)
+ do_send "SET LED_COLOR_UNMUTED", colour.to_s.upcase, name: :unmuted_color
+ end
+
+ def query_led_state_unmuted
+ do_send "GET LED_STATE_UNMUTED"
+ end
+
+ def led_state_unmuted(on : Bool = true)
+ state = on ? "ON" : "OFF"
+ do_send "SET LED_STATE_UNMUTED", state
+ end
+
+ def query_led_state_muted
+ do_send "GET LED_STATE_MUTED"
+ end
+
+ def led_state_muted(on : Bool = true)
+ state = on ? "ON" : "OFF"
+ do_send "SET LED_STATE_MUTED", state
+ end
+
+ def received(bytes, task)
+ data = String.new(bytes)
+ logger.debug { "-- received: #{data}" }
+
+ # Convert { some data here } to " some data here " and remove control chars
+ data = data.split("< ", 2)[1].gsub(/[\{\}]/, '"').rchop(" >")
+
+ # Then use shellsplit to capture the parts and remove whitespace
+ resp = shellsplit(data).map(&.strip)
+
+ # We want to ignore sample responses
+ if resp[0] == "SAMPLE"
+ resp[1..-1].each_with_index do |level, index|
+ self["output#{index + 1}"] = level.to_i
+ end
+ return
+ end
+
+ return task.try &.abort if resp[1] == "ERR"
+
+ # Check if the first value is a number - channel level details
+ if resp[1] =~ /^[0-9]+$/
+ chann = resp[1]
+ param = resp[2].try &.downcase
+ value = resp[3].try &.downcase
+
+ self["#{param}_#{chann}"] = value
+ return task.try &.success
+ end
+
+ # Global value details
+ param = resp[1].downcase
+ value = resp[2]
+
+ case param
+ when "device_audio_mute" then self[:muted] = value == "ON"
+ when "dev_led_state_muted" then self[:led_muted] = value == "ON"
+ when "dev_led_state_unmuted" then self[:led_unmuted] = value == "ON"
+ else
+ self[param] = case value
+ when "ON" then true
+ when "OFF" then false
+ when .to_i? then value.to_i
+ else
+ value
+ end
+ end
+
+ task.try &.success
+ end
+
+ def do_poll
+ query_device_id
+ end
+
+ protected def do_send(*command, **options)
+ cmd = "< #{command.join(' ')} >"
+ logger.debug { "-- sending: #{cmd}" }
+ send(cmd, **options)
+ end
+
+ # Quick dirty port of https://github.com/ruby/ruby/blob/master/lib/shellwords.rb
+ protected def shellsplit(line : String) : Array(String)
+ words = [] of String
+ field = ""
+ pattern = /\G\s*(?>([^\s\\\'\"]+)|'([^\']*)'|"((?:[^\"\\]|\\.)*)"|(\\.?)|(\S))(\s|\z)?/m
+ line.scan(pattern) do |match|
+ _, word, sq, dq, esc, garbage, sep = match.to_a
+ raise ArgumentError.new("Unmatched quote: #{line.inspect}") if garbage
+ field += (word || sq || dq.try(&.gsub(/\\([$`"\\\n])/, "\\1")) || esc.not_nil!.gsub(/\\(.)/, "\\1"))
+ if sep
+ words << field
+ field = ""
+ end
+ end
+ words
+ end
+end
diff --git a/drivers/shure/microphone/mxa_spec.cr b/drivers/shure/microphone/mxa_spec.cr
new file mode 100644
index 00000000000..5c1e2866df9
--- /dev/null
+++ b/drivers/shure/microphone/mxa_spec.cr
@@ -0,0 +1,18 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Shure::Microphone::MXA" do
+ should_send("< GET 0 ALL >").responds "< REP PRESET 10 >"
+ status[:preset].should eq(10)
+
+ should_send("< SET METER_RATE 0 >").responds "< REP METER_RATE 0 >"
+ status[:meter_rate].should eq(0)
+
+ exec(:query_device_id)
+ should_send("< GET DEVICE_ID >").responds "< REP DEVICE_ID { steves dev } >"
+ status[:device_id].should eq("steves dev")
+
+ responds "< SAMPLE 002 003 002 000 000 001 002 003 000 >"
+ sleep 1
+ status[:output1].should eq 2
+ status[:output2].should eq 3
+end
diff --git a/drivers/siemens/desigo.cr b/drivers/siemens/desigo.cr
new file mode 100644
index 00000000000..f317657fe8c
--- /dev/null
+++ b/drivers/siemens/desigo.cr
@@ -0,0 +1,55 @@
+require "placeos-driver"
+require "desigo"
+
+class Siemens::Desigo < PlaceOS::Driver
+ descriptive_name "Siemens Desigo Gateway"
+ generic_name :Desigo
+ uri_base "https://127.0.0.1:8080/WebService/api/"
+
+ alias Client = ::Desigo::Client
+
+ default_settings({
+ username: "admin",
+ password: "admin",
+ })
+
+ protected getter! client : Client
+
+ def on_update
+ base_url = config.uri.not_nil!.to_s
+ username = setting(String, :username)
+ password = setting(String, :password)
+
+ @client = Client.new(base_url: base_url, username: username, password: password)
+
+ spawn do
+ loop do
+ @client.try(&.heartbeat.signal)
+ sleep 60
+ end
+ end
+ end
+
+ def property_values(id : String)
+ property_values = @client.try(&.property_values.get(id: id))
+ self["property_values#{id}"] = property_values
+ end
+
+ def values(id : String)
+ values = @client.try(&.values.get(id: id))
+ self["values#{id}"] = values
+ end
+
+ def commands(id : String)
+ commands = @client.try(&.commands.get(id: id))
+ self["commands#{id}"] = commands
+ end
+
+ # Because of the introspect failing on generics,
+ # we can pass in the `command_inputs_for_execution` as a JSON string
+ # "[{\"Name\": \"Value\", \"DataType\": \"ExtendedEnum\", \"Value\": \"1\"}]"
+ def execute(id : String, property_name : String, command_id : String, command_inputs_for_execution : String)
+ return_value = @client.try(&.commands.execute(id: id, property_name: property_name, command_id: command_id, command_inputs_for_execution: JSON.parse(command_inputs_for_execution)))
+ self["execute#{id}_property#{property_name}_command#{command_id}"] = return_value
+ end
+end
diff --git a/drivers/siemens/desigo/room_logic.cr b/drivers/siemens/desigo/room_logic.cr
new file mode 100644
index 00000000000..0c331fd7965
--- /dev/null
+++ b/drivers/siemens/desigo/room_logic.cr
@@ -0,0 +1,36 @@
+require "placeos-driver"
+
+class Siemens::Desigo::RoomLogic < PlaceOS::Driver
+ descriptive_name "Siemens Desigo single room status abstraction"
+ generic_name :RoomBMS
+ description "Exposes Desigo values for a single room"
+
+ default_settings({
+ desigo_queries: [] of Query,
+ desigo_status_poll_cron: "*/5 * * * *",
+ })
+
+ accessor desigo : Desigo
+
+ @queries = [] of Query
+ @cron_string : String = "*/5 * * * *"
+
+ def on_update
+ @queries = setting(Array(Query), :desigo_queries)
+ @cron_string = setting(String, :desigo_status_poll_cron)
+ schedule.clear
+ schedule.cron(@cron_string) { do_queries }
+ end
+
+ def do_queries
+ responses = @queries.map { |q| {q.name, desigo.values(q.param).get} }
+ responses.each { |name, value| self[name] = value.as_a.first.as_h["Value"]["Value"] }
+ end
+
+ struct Query
+ include JSON::Serializable
+ getter name : String
+ property command : String # todo: support different commands
+ property param : String # todo: support multiple params
+ end
+end
diff --git a/drivers/solutions2/pms.cr b/drivers/solutions2/pms.cr
new file mode 100644
index 00000000000..6f110d7cd83
--- /dev/null
+++ b/drivers/solutions2/pms.cr
@@ -0,0 +1,230 @@
+require "placeos-driver"
+
+class PMS < PlaceOS::Driver
+ # Discovery Information
+ descriptive_name "Parking Management System"
+ generic_name :PMS
+
+ uri_base "https://api.pmssandbox.expocitydubai.com/"
+
+ default_settings({
+ base_url: "",
+ username: "",
+ password: "",
+ debug_payload: false,
+ })
+
+ @username : String = ""
+ @password : String = ""
+ @debug_payload : Bool = false
+ getter! pms_token : AccessToken
+
+ def on_update
+ @username = setting(String, :username)
+ @password = setting(String, :password)
+ @debug_payload = setting?(Bool, :debug_payload) || false
+
+ if uri_override = setting?(String, :base_url)
+ transport.http_uri_override = URI.parse uri_override
+ else
+ transport.http_uri_override = nil
+ end
+
+ transport.before_request do |request|
+ logger.debug { "requesting: #{request.method} #{request.path}?#{request.query}\n#{request.body}" }
+ end
+ end
+
+ def list_departments
+ request("GET", "/api/departments")
+ end
+
+ def list_vehicles
+ request("GET", "/api/vehicles")
+ end
+
+ def register_vehicle(plate_number : String, plate_source : String, plate_category : String, plate_code : String, license_expiry_date : String)
+ body = URI::Params.build do |form|
+ form.add("PlateNumber", plate_number)
+ form.add("Platesource", plate_source)
+ form.add("PlateCategory", plate_category)
+ form.add("PlateCode", plate_code)
+ form.add("LicenseExpiryDate", license_expiry_date)
+ end
+ request("POST", "/api/vehicles/register", body)
+ end
+
+ def update_vehicle(vehicle_id : String, plate_number : String, plate_source : String, plate_category : String, plate_code : String, license_expiry_date : String, vehicle_status : String)
+ body = URI::Params.build do |form|
+ form.add("PlateNumber", plate_number)
+ form.add("Platesource", plate_source)
+ form.add("PlateCategory", plate_category)
+ form.add("PlateCode", plate_code)
+ form.add("LicenseExpiryDate", license_expiry_date)
+ form.add("VehicleStatus", vehicle_status)
+ end
+ request("PATCH", "/api/vehicles/update/#{vehicle_id}", body)
+ end
+
+ def list_employees
+ request("GET", "/api/employees")
+ end
+
+ def assign_department(employee_id : String, department_id : String)
+ body = URI::Params.build do |form|
+ form.add("DepartmentId", department_id)
+ end
+
+ request("PUT", "/api/employees/assign-department/#{employee_id}", body)
+ end
+
+ def assign_vehicle(employee_id : String, vehicle_id : String)
+ body = URI::Params.build do |form|
+ form.add("VehicleId", vehicle_id)
+ end
+
+ request("PUT", "/api/employees/assign-vehicle/#{employee_id}", body)
+ end
+
+ def unassign_vehicle(employee_id : String, vehicle_id : String)
+ body = URI::Params.build do |form|
+ form.add("VehicleId", vehicle_id)
+ end
+
+ request("PUT", "/api/employees/unassign-vehicle/#{employee_id}", body)
+ end
+
+ def owner_type(employee_id : String, owner_type : String)
+ body = URI::Params.build do |form|
+ form.add("OwnerType", owner_type)
+ end
+
+ request("PUT", "/api/employees/ownertype/#{employee_id}", body)
+ end
+
+ def visitor_parking_requests(from_date : String, to_date : String)
+ body = URI::Params.build do |form|
+ form.add("visitordatefrom", from_date)
+ form.add("visitordateto", to_date)
+ end
+
+ request("GET", "/api/visitors/visitorparking", body)
+ end
+
+ def visitor_registration(first_name : String, last_name : String, email : String, contact_num : String, nationality : String, visit_purpose : String, visit_purpose_comment : String,
+ visit_date_from : String, visit_date_to : String, visit_time : Time, plate_number : String, plate_source : String, plate_category : String, plate_code : String, internal_department : String,
+ owner_type : String, uploaded_file_content : String, uploaded_file_name : String)
+ body = URI::Params.build do |form|
+ form.add("FirstName", first_name)
+ form.add("LastName", last_name)
+ form.add("Email", email)
+ form.add("ContactNumber", contact_num)
+ form.add("Nationality", nationality)
+ form.add("VisitPurpose", visit_purpose)
+ form.add("CommentVisitPurpose", visit_purpose_comment)
+ form.add("VisitDateFrom", visit_date_from)
+ form.add("VisitDateTo", visit_date_to)
+ form.add("VisitTime", visit_time.to_s)
+ form.add("PlateNumber", plate_number)
+ form.add("Platesource", plate_source)
+ form.add("PlateCategory", plate_category)
+ form.add("PlateCode", plate_code)
+ form.add("InternalDepartment", internal_department)
+ form.add("BasementParking", "TRUE")
+ form.add("OwnerType", owner_type)
+ form.add("UploadedFileContent", uploaded_file_content)
+ form.add("UploadedFileName", uploaded_file_name)
+ end
+
+ request("POST", "/api/visitors/registration", body)
+ end
+
+ def visitor_parking_cancel(id : String)
+ request("PUT", "/api/visitors/visitorparkingcancel/#{id}")
+ end
+
+ def available_slots
+ request("GET", "/api/parking/available-slots")
+ end
+
+ def occupied_slots
+ request("GET", "/api/parking/occupied-slots")
+ end
+
+ def full_notifications
+ request("GET", "/api/parking/full-notifications")
+ end
+
+ private def request(method : String, resource : String, payload : String? = nil, params : Hash(String, String?) | URI::Params = URI::Params.new)
+ headers = get_headers("application/x-www-form-urlencoded")
+ logger.debug { {msg: "#{method} #{resource}:", headers: headers.to_json, payload: payload} } if @debug_payload
+ response = http(method: method, path: resource, headers: headers, body: payload, params: params)
+ raise "failed to #{method} #{resource}, code #{response.status_code}, body: #{response.body}" unless response.success?
+
+ JSON.parse(response.body)
+ end
+
+ private def get_headers(content_type : String = "application/json")
+ HTTP::Headers{
+ "Authorization" => access_token,
+ "Content-Type" => content_type,
+ "Accept" => "application/json",
+ }
+ end
+
+ private def access_token
+ return pms_token.auth_token if pms_token? && !pms_token.expired?
+ generate_token
+ end
+
+ private def generate_token
+ body = URI::Params.build do |form|
+ form.add("Username", @username)
+ form.add("Password", @password)
+ end
+
+ headers = HTTP::Headers{
+ "Content-Type" => "application/x-www-form-urlencoded",
+ "Accept" => "application/json",
+ }
+ response = post("/api/Token", headers: headers, body: body)
+ raise "failed to get access token: response code #{response.status_code}, body #{response.body}" unless response.success?
+ @pms_token = AccessToken.from_json(response.body, root: "Data")
+ pms_token.auth_token
+ end
+
+ record AccessToken, token : String, userid : String, expiry : Int64 do
+ include JSON::Serializable
+
+ @[JSON::Field(ignore: true)]
+ getter! token_expiry : Time
+
+ def after_initialize
+ @token_expiry = Time.utc + expiry.seconds
+ end
+
+ def expired?
+ Time.utc >= token_expiry
+ end
+
+ def auth_token
+ "Bearer #{token}"
+ end
+ end
+
+ struct Department
+ include JSON::Serializable
+
+ @[JSON::Field(key: "Name")]
+ getter name : String
+
+ @[JSON::Field(key: "ParkingSlots")]
+ getter parking_slots : Int32
+
+ @[JSON::Field(key: "Status")]
+ getter status : String
+
+ @[JSON::Field(key: "Id")]
+ getter id : String
+ end
+end
diff --git a/drivers/solutions2/pms_logic.cr b/drivers/solutions2/pms_logic.cr
new file mode 100644
index 00000000000..35b02c52e6d
--- /dev/null
+++ b/drivers/solutions2/pms_logic.cr
@@ -0,0 +1,64 @@
+require "placeos-driver"
+
+class PMSLogic < PlaceOS::Driver
+ descriptive_name "Parking Management System Logic"
+ generic_name :PMSLogic
+ description "Abstracts Parking slots access for PMS"
+
+ default_settings({
+ poll_parking_cron: "*/5 * * * *",
+ })
+
+ accessor pms : PMS_1
+
+ @cron_string : String = "*/5 * * * *"
+
+ def on_update
+ @cron_string = setting(String, :poll_parking_cron)
+ schedule.clear
+ schedule.cron(@cron_string) { get_parking_status }
+ end
+
+ def get_parking_status
+ parking_slots = Array(ParkingStatus).from_json(pms.available_slots.get.to_json)
+ self[:parking_slots_status] = parking_slots
+ parking_slots
+ end
+
+ struct ParkingStatus
+ include JSON::Serializable
+
+ @[JSON::Field(key: "DeptId", ignore_serialize: true)]
+ getter dept_id : String
+
+ getter(department_id : String) { dept_id }
+
+ @[JSON::Field(key: "DepartmentName", ignore_serialize: true)]
+ getter dept_name : String
+
+ getter(department_name : String) { dept_name }
+
+ @[JSON::Field(key: "NoofParkingSlots", ignore_serialize: true)]
+ getter no_of_slots : String
+
+ getter(total_parking_slots : Int32) { no_of_slots.to_i }
+
+ @[JSON::Field(key: "OccupiedParkingSlots", ignore_serialize: true)]
+ getter occupied_slots : String
+
+ getter(occupied_parking_slots : Int32) { occupied_slots.to_i }
+
+ @[JSON::Field(key: "AvailableParkingSlots", ignore_serialize: true)]
+ getter available_slots : String
+
+ getter(available_parking_slots : Int32) { available_slots.to_i }
+
+ def after_initialize
+ department_id
+ department_name
+ total_parking_slots
+ occupied_parking_slots
+ available_parking_slots
+ end
+ end
+end
diff --git a/drivers/solutions2/pms_logic_spec.cr b/drivers/solutions2/pms_logic_spec.cr
new file mode 100644
index 00000000000..3c41ea5a0bf
--- /dev/null
+++ b/drivers/solutions2/pms_logic_spec.cr
@@ -0,0 +1,47 @@
+require "placeos-driver/spec"
+
+class PMS < DriverSpecs::MockDriver
+ def available_slots
+ data = <<-JSON
+[
+ {
+ "DepartmentName": "CMO",
+ "DeptId": "af22ac15-b85c-f011-bec2-6045bd69cb6a",
+ "NoofParkingSlots": "10",
+ "OccupiedParkingSlots": "1",
+ "AvailableParkingSlots": "9"
+ },
+ {
+ "DepartmentName": "PMO1111111",
+ "DeptId": "e989057d-9460-f011-bec2-6045bd1585f5",
+ "NoofParkingSlots": "4",
+ "OccupiedParkingSlots": "4",
+ "AvailableParkingSlots": "0"
+ },
+ {
+ "DepartmentName": "Solutions21",
+ "DeptId": "87336d6a-2d5e-f011-bec1-0022480ce5ed",
+ "NoofParkingSlots": "10",
+ "OccupiedParkingSlots": "10",
+ "AvailableParkingSlots": "0"
+ },
+ {
+ "DepartmentName": "TECHNOLOGY",
+ "DeptId": "4a813c24-7a67-f011-bec3-6045bd69cb6a",
+ "NoofParkingSlots": "4",
+ "OccupiedParkingSlots": "0",
+ "AvailableParkingSlots": "4"
+ }
+]
+JSON
+ JSON.parse(data)
+ end
+end
+
+DriverSpecs.mock_driver "PMSLogic" do
+ system({
+ PMS: {PMS},
+ })
+
+ val = exec(:get_parking_status).get.as_a.size.should eq(4)
+end
diff --git a/drivers/solutions2/pms_spec.cr b/drivers/solutions2/pms_spec.cr
new file mode 100644
index 00000000000..7479573fb43
--- /dev/null
+++ b/drivers/solutions2/pms_spec.cr
@@ -0,0 +1,98 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "PMS" do
+ settings({
+ username: "placeos_demo",
+ password: "test-pwd",
+ debug_payload: true,
+ })
+
+ ret_val = exec(:list_departments)
+
+ expect_http_request(2.seconds) do |request, response|
+ if request.path == "/api/Token"
+ response.status_code = 200
+ response << generate_token.to_json
+ else
+ response.status_code = 401
+ end
+ end
+
+ expect_http_request(2.seconds) do |request, response|
+ if request.path == "/api/departments"
+ response.status_code = 200
+ response << departments_data.to_json
+ else
+ response.status_code = 404
+ end
+ end
+
+ ret_val.get.try &.as_a.size.should eq 3
+
+ ret_val = exec(:list_vehicles)
+ expect_http_request(2.seconds) do |request, response|
+ if request.method == "GET" && request.path == "/api/vehicles"
+ response.status_code = 200
+ response << vehicles_data.to_json
+ else
+ response.status_code = 404
+ end
+ end
+
+ ret_val.get.try &.as_a.size.should eq 2
+end
+
+def generate_token
+ {
+ "Data": {
+ "token": "iYambvQ7MSBqZ7_u63VjzqXlG6sq-_xQIUxYcQ9vmjXFaTuTxqrs23SjC7803VRF69iThuXH9rTnOGPawMJhBXf4YIU7pslcp85zZJvJbinM3t-7zsSjNFIBh80B8iBLinhCah8hzd2gCs8Cvd32Lb-fV2L4Rr9Lo_XQQQiS7bx-ebcJL70-sXJrCLZtMUoZ-wFM-XftIpbcIN2M0t8u7tKzywhFDtADY1ILpqcqs7O7XhoHBQXJ560-BoZc-rQajBrWb1TqbUGVNYlF-qs3yI7skkYem8TVATrnH4xt9neo92v4KV7IwlPJ_2pN4R1leSW5RE-oSeURliULdOpD2YsQTNMrm0_Vm6jGvZHGRfirnrfLKVe9aFnXYGCgP8MHw7cFIcVGIaOh7DqOZpmPuZH4A5exJs3hgLIqwA6cIBTyk2dYPUMG9daLfdljAMJy3UzuE3hKjKIjIl7Ze_rQAGJneuKFe7trF0TqCfBOFw51RGMw1JIf7OnHK5nvA4OQmrQgQD_SbjCYRFvs6bbJG0QI_P4c03lHTgFu5L2FgN4_jB7hj1fR7kAFAAe-gY_5",
+ "userid": "placeos_demo",
+ "expiry": 86399,
+ },
+ "JsonRequestBehavior": 0,
+ }
+end
+
+def departments_data
+ [
+ {
+ "Name": "CMO",
+ "ParkingSlots": "10",
+ "Status": "🟢 Enabled",
+ "Id": "af22ac15-b85c-f011-bec2-6045bd69cb6a",
+ },
+ {
+ "Name": "CMO",
+ "ParkingSlots": "12",
+ "Status": "🟢 Enabled",
+ "Id": "af5d4b39-b85c-f011-bec2-6045bd69d9b0",
+ },
+ {
+ "Name": "PMO1111111",
+ "ParkingSlots": "4",
+ "Status": "🟢 Enabled",
+ "Id": "6d407fbb-b75c-f011-bec2-6045bd1585f5",
+ },
+ ]
+end
+
+def vehicles_data
+ [
+ {
+ "PlateNumber": "0000212",
+ "Platesource": "Dubai",
+ "PlateCategory": "Private",
+ "PlateCode": "K",
+ "VehicleStatus": "For Approval",
+ "Id": "4fd82430-ea6d-f011-b4cc-6045bd69cb6a",
+ },
+ {
+ "PlateNumber": "0022545",
+ "Platesource": "Dubai",
+ "PlateCategory": "Private",
+ "PlateCode": "K",
+ "VehicleStatus": "For Approval",
+ "Id": "8b4afab2-ea6d-f011-b4cc-0022480dcd74",
+ },
+ ]
+end
diff --git a/drivers/sony/camera/cgi_protocol.cr b/drivers/sony/camera/cgi_protocol.cr
new file mode 100644
index 00000000000..89e914e6ef4
--- /dev/null
+++ b/drivers/sony/camera/cgi_protocol.cr
@@ -0,0 +1,431 @@
+require "placeos-driver"
+require "placeos-driver/interface/camera"
+require "placeos-driver/interface/powerable"
+require "http-client-digest_auth"
+
+# Documentation https://aca.im/driver_docs/Sony/sony-camera-CGI-Commands-1.pdf
+
+class Sony::Camera::CGI < PlaceOS::Driver
+ # include Interface::Powerable
+ include Interface::Camera
+
+ # Discovery Information
+ generic_name :Camera
+ descriptive_name "Sony Camera HTTP CGI Protocol"
+
+ default_settings({
+ digest_auth: {
+ username: "admin",
+ password: "Admin_1234",
+ },
+ invert_controls: false,
+ presets: {
+ name: {pan: 1, tilt: 1, zoom: 1},
+ },
+ enable_debug_logging: false,
+ poll_interval_in_minutes: 5
+ })
+
+ enum Movement
+ Idle
+ Moving
+ Unknown
+ end
+
+ def on_load
+ # Configure the constants
+ @pantilt_speed = -100..100
+ self[:pan_speed] = self[:tilt_speed] = {min: -100, max: 100, stop: 0}
+ self[:has_discrete_zoom] = true
+
+ # Initialize digest auth
+ @digest_auth = HTTP::Client::DigestAuth.new
+ @auth_challenge = ""
+ @auth_uri = URI.parse(config.uri.not_nil!)
+
+ schedule.every(60.seconds) { query_status }
+ schedule.in(5.seconds) do
+ query_status
+ info?
+ end
+ on_update
+ end
+
+ @invert_controls = false
+ @presets = {} of String => NamedTuple(pan: Int32, tilt: Int32, zoom: Int32, focus: Int32)
+ @digest_auth : HTTP::Client::DigestAuth = HTTP::Client::DigestAuth.new
+ @auth_challenge = ""
+ @auth_uri : URI = URI.parse("http://localhost")
+
+ def on_update
+ self[:invert_controls] = @invert_controls = setting?(Bool, :invert_controls) || false
+ @presets = setting?(Hash(String, NamedTuple(pan: Int32, tilt: Int32, zoom: Int32, focus: Int32)), :presets) || {} of String => NamedTuple(pan: Int32, tilt: Int32, zoom: Int32, focus: Int32)
+ self[:presets] = @presets.keys
+ @debug_enabled = setting?(Bool, :enable_debug_logging) || false
+ @poll_interval = setting?(Int32, :poll_interval_in_minutes) || 5
+
+ schedule.every(@poll_interval.not_nil!.minutes) { query_status }
+
+ # Update digest auth credentials
+ if auth_info = setting?(Hash(String, String), :digest_auth)
+ @auth_uri.user = auth_info["username"]?
+ @auth_uri.password = auth_info["password"]?
+ end
+ logger.debug { "Digest auth credentials set to #{@auth_uri.user}:#{@auth_uri.password}" } if @debug_enabled
+ end
+
+ # 24bit twos complement
+ private def twos_complement(value)
+ if value > 0
+ value > 0x80000 ? -(((~(value & 0xFFFFF)) + 1) & 0xFFFFF) : value
+ else
+ ((~(-value & 0xFFFFF)) + 1) & 0xFFFFF
+ end
+ end
+
+ private def authenticate_if_needed(path : String)
+ return unless @auth_challenge.empty?
+
+ # Make initial GET request to get challenge
+ response = http("GET", path)
+ if response.status_code == 401 && (challenge = response.headers["WWW-Authenticate"]?)
+ @auth_challenge = challenge
+ else
+ raise "Failed to get digest auth challenge: #{response.status_code}"
+ end
+ end
+
+ private def get_with_digest_auth(path : String, headers : HTTP::Headers? = nil)
+ authenticate_if_needed(path)
+
+ uri = URI.parse(config.uri.not_nil! + path)
+ @auth_uri.path = uri.path
+ @auth_uri.query = uri.query
+ logger.debug { "Fetching digest auth header with #{@auth_uri.inspect}, #{@auth_challenge.inspect}" } if @debug_enabled
+ auth_header = @digest_auth.auth_header(@auth_uri, @auth_challenge, "GET")
+ logger.debug { "Digest auth header: #{auth_header.inspect}" } if @debug_enabled
+ request_headers = headers || HTTP::Headers.new
+ request_headers["Authorization"] = auth_header
+
+ response = get(path, headers: request_headers)
+ if response.status_code == 401
+ # Auth failed, clear challenge to re-authenticate next time
+ @auth_challenge = ""
+ get_with_digest_auth(path)
+ else
+ response
+ end
+ end
+
+ private def query(path, **opts, &block : Hash(String, String) -> _)
+ queue(**opts) do |task|
+ response = get_with_digest_auth(path)
+ data = response.body.not_nil!
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+
+ # convert data into more consumable state
+ state = {} of String => String
+ data.split("&").each do |key_value|
+ parts = key_value.strip.split("=")
+ state[parts[0]] = parts[1]
+ end
+
+ result = block.call(state)
+ task.success result
+ end
+ end
+
+ # Temporary values until the camera is queried
+ @moving = false
+ @zooming = false
+ @max_speed = 1
+ @zoom_raw = 0
+ @focus_raw = 0
+ @pan = 0
+ @tilt = 0
+ @pan_range = 0..1
+ @tilt_range = 0..1
+ @zoom_range = 0..1
+ @focus_range = 0..61440
+
+ def query_status(priority : Int32 = 0)
+ # Response looks like:
+ # AbsolutePTZF=15400,fd578,0000,cbde&PanMovementRange=eac00,15400
+ query("/command/inquiry.cgi?inq=ptzf", priority: priority) do |response|
+ # load the current state
+ response.each do |key, value|
+ case key
+ when "AbsolutePTZF"
+ # Pan, Tilt, Zoom,Focus
+ # AbsolutePTZF=15400,fd578,0000,ca52
+ parts = value.split(",")
+ self[:pan] = @pan = twos_complement parts[0].to_i(16)
+ self[:tilt] = @tilt = twos_complement parts[1].to_i(16)
+ @zoom_raw = parts[2].to_i(16)
+ @focus_raw = parts[3].to_i(16)
+ when "PanMovementRange"
+ # PanMovementRange=eac00,15400
+ parts = value.split(",")
+ pan_min = twos_complement parts[0].to_i(16)
+ pan_max = twos_complement parts[1].to_i(16)
+ @pan_range = pan_min..pan_max
+ self[:pan_range] = {min: pan_min, max: pan_max}
+ when "TiltMovementRange"
+ # TiltMovementRange=fc400,b400
+ parts = value.split(",")
+ tilt_min = twos_complement parts[0].to_i(16)
+ tilt_max = twos_complement parts[1].to_i(16)
+ @tilt_range = tilt_min..tilt_max
+ self[:tilt_range] = {min: tilt_min, max: tilt_max}
+ when "ZoomMovementRange"
+ # min, max, digital
+ # ZoomMovementRange=0000,4000,7ac0
+ parts = value.split(",")
+ zoom_min = parts[0].to_i(16)
+ zoom_max = parts[1].to_i(16)
+ @zoom_range = zoom_min..zoom_max
+ self[:zoom_range] = {min: zoom_min, max: zoom_max}
+ when "PtzfStatus"
+ # PtzfStatus=idle,idle,idle,idle
+ parts = value.split(",").map { |state| Movement.parse(state) }[0..2]
+ self[:moving] = @moving = parts.includes?(Movement::Moving)
+
+ # when "AbsoluteZoom"
+ # # AbsoluteZoom=609
+ # self[:zoom] = @zoom_raw = value.to_i(16)
+
+ # NOTE:: These are not required as speeds are scaled
+ #
+ # when "ZoomMaxVelocity"
+ # # ZoomMaxVelocity=8
+ # @zoom_speed = 1..value.to_i(16)
+
+ when "PanTiltMaxVelocity"
+ # PanTiltMaxVelocity=24
+ @max_speed = value.to_i(16)
+ end
+ end
+
+ self[:zoom] = @zoom_raw.not_nil!.to_f * (100.0 / @zoom_range.end.to_f)
+ self[:focus] = @focus_raw
+
+ response
+ end
+ end
+
+ def info?
+ query("/command/inquiry.cgi?inq=system", priority: 0) do |response|
+ response.each do |key, value|
+ if {"ModelName", "Serial", "SoftVersion", "ModelForm", "CGIVersion"}.includes?(key)
+ self[key.underscore] = value
+ end
+ end
+ response
+ end
+ end
+
+ private def action(path, **opts, &block : HTTP::Client::Response -> _)
+ queue(**opts) do |task|
+ response = get_with_digest_auth(path)
+ raise "request error #{response.status_code}\n#{response.body}" unless response.success?
+
+ result = block.call(response)
+ task.success result
+ end
+ end
+
+ # Implement Stoppable interface
+ def stop(index : Int32 | String = 0, emergency : Bool = false)
+ # indexes start at 1 on sony cameras
+ index = index.to_i + 1
+
+ action("/command/ptzf.cgi?Move=stop,motor,image#{index}",
+ priority: 999,
+ name: "moving",
+ clear_queue: emergency
+ ) do
+ zoom ZoomDirection::Stop if @zooming
+ self[:moving] = @moving = false
+ query_status
+ end
+ end
+
+ # Implement Moveable interface
+ def move(position : MoveablePosition, index : Int32 | String = 0)
+ # indexes start at 1 on sony cameras
+ index = index.to_i + 1
+
+ case position
+ when MoveablePosition::Up, MoveablePosition::Down,
+ MoveablePosition::Left, MoveablePosition::Right
+ # Tilt, Pan
+ if @invert_controls && (position.up? || position.down?)
+ position = position.up? ? MoveablePosition::Down : MoveablePosition::Up
+ end
+
+ action("/command/ptzf.cgi?Move=#{position.to_s.downcase},0,image#{index}",
+ name: "moving",
+ priority: queue.priority + 50,
+ ) { self[:moving] = @moving = true }
+ when MoveablePosition::In
+ zoom ZoomDirection::In
+ when MoveablePosition::Out
+ zoom ZoomDirection::Out
+ else
+ raise "unsupported direction: #{position}"
+ end
+ end
+
+ macro in_range(range, value)
+ {{value}} = if {{range}}.includes? {{value}}
+ {{value}}
+ else
+ {{value}} < {{range}}.begin ? {{range}}.begin : {{range}}.end
+ end
+ {{value}} = twos_complement({{value}})
+ end
+
+ def pantilt(pan : Int32, tilt : Int32, zoom : Int32? = nil, focus : Int32? = nil) : Nil
+ in_range @pan_range, pan
+ in_range @tilt_range, tilt
+
+ if zoom
+ in_range @zoom_range, zoom
+ param = "#{pan.to_s(16)},#{tilt.to_s(16)},#{zoom.to_s(16)}"
+ if focus
+ in_range @focus_range, focus
+ param += ",#{focus.to_s(16)}"
+ end
+ action("/command/ptzf.cgi?AbsolutePTZF=#{param}",
+ name: "position"
+ ) do
+ self[:pan] = @pan = pan
+ self[:tilt] = @tilt = tilt
+ self[:zoom] = @zoom_raw = zoom.not_nil!
+ end
+ else
+ action("/command/ptzf.cgi?AbsolutePanTilt=#{pan.to_s(16)},#{tilt.to_s(16)},#{@max_speed.to_s(16)}",
+ name: "position"
+ ) do
+ self[:pan] = @pan = pan
+ self[:tilt] = @tilt = tilt
+ end
+ end
+ end
+
+ # Implement Camera interface
+ def joystick(pan_speed : Float64, tilt_speed : Float64, index : Int32 | String = 0)
+ index = index.to_i + 1
+ pan_speed = pan_speed.to_i
+ tilt_speed = tilt_speed.to_i
+
+ range = -100..100
+ in_range range, pan_speed
+ in_range range, tilt_speed
+
+ tilt_speed = -tilt_speed if @invert_controls && tilt_speed != 0
+
+ action("/command/ptzf.cgi?ContinuousPanTiltZoom=#{pan_speed.to_s(16)},#{tilt_speed.to_s(16)},0,image#{index}",
+ name: "moving",
+ priority: queue.priority + 50,
+ ) do
+ self[:moving] = @moving = (pan_speed != 0 || tilt_speed != 0)
+ query_status if !@moving
+ @moving
+ end
+ end
+
+ def zoom_to(position : Float64, auto_focus : Bool = true, index : Int32 | String = 0)
+ index = index.to_i + 1
+
+ position = position.clamp(0.0, 100.0)
+ percentage = position / 100.0
+ zoom_value = (percentage * @zoom_range.end.to_f).to_i
+
+ action("/command/ptzf.cgi?AbsoluteZoom=#{zoom_value.to_s(16)}",
+ name: "zooming"
+ ) do
+ @zoom_raw = zoom_value
+ self[:zoom] = @zoom = position
+ end
+ end
+
+ def zoom(direction : ZoomDirection, index : Int32 | String = 0)
+ index = index.to_i + 1
+
+ if direction.stop?
+ action("/command/ptzf.cgi?Move=stop,zoom,image#{index}",
+ priority: 999,
+ name: "zooming"
+ ) { self[:zooming] = @zooming = false }
+ else
+ action("/command/ptzf.cgi?Move=#{direction.out? ? "wide" : "near"},0,image#{index}",
+ name: "zooming",
+ priority: queue.priority + 40,
+ ) { self[:zooming] = @zooming = true }
+ end
+ end
+
+ def home
+ action("/command/presetposition.cgi?HomePos=recall",
+ name: "position"
+ ) { query_status }
+ end
+
+ def recall(position : String, index : Int32 | String = 0)
+ preset = @presets[position]?
+ if preset
+ pantilt **preset
+ else
+ raise "unknown preset #{position}"
+ end
+ end
+
+ def save_position(name : String, index : Int32 | String = 0)
+ @presets[name] = {
+ pan: @pan, tilt: @tilt, zoom: @zoom_raw, focus: @focus_raw
+ }
+ define_setting(:presets, @presets)
+ self[:presets] = @presets.keys
+ end
+
+ def remove_position(name : String, index : Int32 | String = 0)
+ @presets.delete name
+ define_setting(:presets, @presets)
+ self[:presets] = @presets.keys
+ end
+
+ #autoframing toggle and status query
+ def autoframe(state : Bool)
+ action("/analytics/ptzautoframing.cgi?PtzAutoFraming=#{state ? "on" : "off"}",
+ name: "auto-framing"
+ ) { autoframing? }
+ end
+
+ def autoframing?
+ autoframe_status: String? = nil
+ query("/command/inquiry.cgi?inq=ptzautoframing", priority: 0) do |response|
+ autoframe_status = response["PtzAutoFraming"]?
+ end
+ return nil unless autoframe_status
+ self[:autoframe] = autoframe_status == "on" # device returns "on" or "off"
+ end
+
+ # ====== Powerable Interface ======
+
+ def power(state : Bool)
+ action("/command/main.cgi?System=#{state ? "on" : "standby"}",
+ name: "power"
+ ) { power? }
+ end
+
+ def power?
+ power_status : String? = nil
+ query("/command/inquiry.cgi?inq=sysinfo", priority: 0) do |response|
+ power_status = response["Power"]?
+ end
+ return nil unless power_status
+ self[:power] = power_status == "on" # device returns "on" or "standby"
+ end
+end
diff --git a/drivers/sony/camera/cgi_protocol_spec.cr b/drivers/sony/camera/cgi_protocol_spec.cr
new file mode 100644
index 00000000000..10e41531ff7
--- /dev/null
+++ b/drivers/sony/camera/cgi_protocol_spec.cr
@@ -0,0 +1,34 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Sony::Camera::CGI" do
+ # Test digest auth flow - first GET request for auth challenge
+ retval = exec(:query_status)
+
+ # First request should be GET to get auth challenge
+ expect_http_request do |request, response|
+ request.method.should eq("GET")
+ request.resource.should eq("/command/inquiry.cgi?inq=ptzf")
+
+ response.status_code = 401
+ response.headers["WWW-Authenticate"] = %(Digest realm="Sony Camera", nonce="abc123", qop="auth", algorithm=MD5)
+ end
+
+ # Second request should be GET with digest auth header
+ expect_http_request do |request, response|
+ request.method.should eq("GET")
+ request.resource.should eq("/command/inquiry.cgi?inq=ptzf")
+ request.headers["Authorization"]?.should_not be_nil
+ request.headers["Authorization"].should contain("Digest")
+
+ response.status_code = 200
+ response.output.puts %(AbsolutePTZF=15400,fd578,0000,cb5a&PanMovementRange=eac00,15400&PanPanoramaRange=de00,2200&PanTiltMaxVelocity=24&PtzInstance=1&TiltMovementRange=fc400,b400&TiltPanoramaRange=fc00,1200&ZoomMaxVelocity=8&ZoomMovementRange=0000,4000,7ac0&PtzfStatus=idle,idle,idle,idle&AbsoluteZoom=609)
+ end
+
+ # What the function should return (for use in making further requests)
+ retval.get.not_nil!["AbsoluteZoom"].should eq("609")
+ status[:pan].should eq(87040)
+ status[:pan_range].should eq({"min" => -87040, "max" => 87040})
+
+ status[:tilt].should eq(-10888)
+ status[:tilt_range].should eq({"min" => -15360, "max" => 46080})
+end
diff --git a/drivers/sony/camera/visca.cr b/drivers/sony/camera/visca.cr
new file mode 100644
index 00000000000..5e24380a0db
--- /dev/null
+++ b/drivers/sony/camera/visca.cr
@@ -0,0 +1,434 @@
+require "placeos-driver"
+require "placeos-driver/interface/camera"
+require "placeos-driver/interface/powerable"
+require "bindata"
+
+# Documentation: https://aca.im/driver_docs/Sony/sony_visca_over_ip.pdf
+# https://aca.im/driver_docs/Aver/tr530-320-control-codes.pdf
+
+class Sony::Camera::VISCA < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Camera
+
+ # Discovery Information.
+ generic_name :Camera
+ descriptive_name "VISCA PTZ Camera"
+ udp_port 52381
+
+ default_settings({
+ max_pan_tilt_speed: 0x0F,
+ zoom_speed: 0x07,
+ zoom_max: 0x4000,
+ camera_no: 0x01,
+ invert_controls: false,
+ })
+
+ @sequence : UInt32 = 0
+
+ @max_pan_tilt_speed : UInt8 = 0x0F_u8
+ @zoom_speed : UInt8 = 0x03_u8
+ @zoom_max : UInt16 = 0x4000_u16
+ @camera_address : UInt8 = 0x81_u8
+ @invert : Bool = false
+
+ alias Presets = Hash(String, Tuple(UInt16, UInt16, Float64))
+ @presets : Presets = {} of String => Tuple(UInt16, UInt16, Float64)
+ getter zoom_raw : UInt16 = 0_u16
+ @zoom_pos : Float64 = 0.0
+ getter tilt_pos : UInt16 = 0_u16
+ getter pan_pos : UInt16 = 0_u16
+
+ # we want to tokenize the stream, ensure we only process a single packet at a time
+ # and that we have the complete message
+ def on_load
+ transport.tokenizer = Tokenizer.new do |io|
+ bytes = io.peek
+ # return 0 if the message is incomplete
+ next 0 if bytes.size < 4
+ # return the length of the message
+ IO::Memory.new(bytes[2..3]).read_bytes(UInt16, IO::ByteFormat::BigEndian).to_i + 8
+ end
+
+ on_update
+ end
+
+ def on_update
+ @presets = setting?(Presets, :camera_presets) || @presets
+
+ @max_pan_tilt_speed = setting?(UInt8, :max_pan_tilt_speed) || 0x0F_u8
+ @zoom_speed = setting?(UInt8, :zoom_speed) || 0x03_u8
+ @zoom_max = setting?(UInt16, :zoom_max) || 0x4000_u16
+ @camera_address = 0x80_u8 | (setting?(UInt8, :camera_no) || 1_u8)
+ self[:presets] = @presets.keys
+ self[:inverted] = @invert = setting?(Bool, :invert_controls) || false
+ end
+
+ # clear the interface
+ def connected
+ reset_sequence_number
+ send_cmd(Bytes[0x00, 0x01], name: :if_clear, priority: 98)
+ end
+
+ # ====== Powerable Interface ======
+
+ def power(state : Bool)
+ payload = state ? Bytes[0x04, 0x00, 0x02] : Bytes[0x04, 0x00, 0x03]
+ send_cmd(payload, name: :power)
+ end
+
+ def power?
+ send_inq(Bytes[0x04, 0x00], name: :power_query)
+ end
+
+ # ====== Camera Interface ======
+
+ def home
+ send_cmd(Bytes[0x06, 0x04], name: :pantilt)
+ end
+
+ def joystick(pan_speed : Float64, tilt_speed : Float64, index : Int32 | String = 0)
+ tilt_speed = -tilt_speed if @invert
+
+ pan_neg, pan_value, pan_zero = joyspeed(pan_speed, @max_pan_tilt_speed)
+ tilt_neg, tilt_value, tilt_zero = joyspeed(tilt_speed, @max_pan_tilt_speed)
+
+ pan_direction = pan_zero ? "03" : (pan_neg ? "01" : "02")
+ tilt_direction = tilt_zero ? "03" : (tilt_neg ? "02" : "01")
+ stopping = pan_zero && tilt_zero
+ priority = queue.priority + (stopping ? 100 : 50)
+
+ bytes = "0601#{pan_value}#{tilt_value}#{pan_direction}#{tilt_direction}"
+ resp = send_cmd(bytes.hexbytes, name: :joystick, priority: priority)
+
+ # query the current position after we've stopped moving
+ if pan_zero && tilt_zero
+ spawn do
+ resp.get
+ schedule.in(1.seconds) { pantilt? }
+ end
+ end
+
+ resp
+ end
+
+ protected def joyspeed(speed : Float64, max)
+ speed = speed.clamp(-100.0, 100.0)
+ negative = speed < 0.0
+ speed = speed.abs if negative
+
+ percentage = speed / 100.0
+ value = (percentage * max.to_f).round.to_u8
+
+ bytes = Bytes[value].hexstring.rjust(2, '0')
+ {negative, bytes, value.zero?}
+ end
+
+ def encode_position(value : UInt16) : String
+ io = IO::Memory.new
+ io.write_bytes(value, IO::ByteFormat::BigEndian)
+ bytes = io.to_slice.hexstring.rjust(4, '0')
+ "0#{bytes[0]}0#{bytes[1]}0#{bytes[2]}0#{bytes[3]}"
+ end
+
+ protected def decode_position(bytes : Bytes) : UInt16
+ pos_data = bytes.hexstring.rjust(8, '0')
+ hexstring = "#{pos_data[1]}#{pos_data[3]}#{pos_data[5]}#{pos_data[7]}"
+ IO::Memory.new(hexstring.hexbytes).read_bytes(UInt16, IO::ByteFormat::BigEndian)
+ end
+
+ # moves to an absolute position
+ def pantilt(pan : UInt16, tilt : UInt16, speed : UInt8)
+ speed = speed.clamp(0_u8, @max_pan_tilt_speed)
+ bytes = "0602#{Bytes[speed].hexstring.rjust(2, '0')}00#{encode_position(pan)}#{encode_position(tilt)}"
+ send_cmd(bytes.hexbytes, name: :pantilt)
+ end
+
+ def recall(position : String, index : Int32 | String = 0)
+ if pos = @presets[position]?
+ pan_pos, tilt_pos, zoom_pos = pos
+ pantilt(pan_pos, tilt_pos, @max_pan_tilt_speed)
+ zoom_to(zoom_pos)
+ else
+ raise "unknown preset #{position}"
+ end
+ end
+
+ def save_position(name : String, index : Int32 | String = 0)
+ @presets[name] = {@pan_pos, @tilt_pos, @zoom_pos}
+ save_presets
+ end
+
+ def remove_position(name : String, index : Int32 | String = 0)
+ @presets.delete(name)
+ save_presets
+ end
+
+ protected def save_presets
+ define_setting(:camera_presets, @presets)
+ self[:presets] = @presets.keys
+ end
+
+ # ====== Moveable Interface ======
+
+ # moves at 50% of max speed
+ def move(position : MoveablePosition, index : Int32 | String = 0)
+ case position
+ in .up?
+ joystick(pan_speed: 0.0, tilt_speed: 50.0)
+ in .down?
+ joystick(pan_speed: 0.0, tilt_speed: -50.0)
+ in .left?
+ joystick(pan_speed: -50.0, tilt_speed: 0.0)
+ in .right?
+ joystick(pan_speed: 50.0, tilt_speed: 0.0)
+ in .in?
+ zoom(:in)
+ in .out?
+ zoom(:out)
+ in .open?, .close?
+ # not supported
+ end
+ end
+
+ # ====== Zoomable Interface ======
+
+ # Zooms to an absolute position
+ def zoom_to(position : Float64, auto_focus : Bool = true, index : Int32 | String = 0)
+ position = position.clamp(0.0, 100.0)
+ percentage = position / 100.0
+ zoom_value = (percentage * @zoom_max.to_f).to_u16
+
+ bytes = "0447#{encode_position(zoom_value)}"
+ send_cmd(bytes.hexbytes, name: :zoom_to)
+ end
+
+ def zoom(direction : ZoomDirection, index : Int32 | String = 0)
+ priority = queue.priority + 40
+ speed_byte = case direction
+ in .stop?
+ priority = priority + 40
+ schedule.in(500.milliseconds) { zoom? }
+ 0x00_u8
+ in .out?
+ 0x20_u8 | @zoom_speed
+ in .in?
+ 0x30_u8 | @zoom_speed
+ end
+
+ send_cmd(Bytes[0x04, 0x07, speed_byte], name: :zoom, priority: priority)
+ end
+
+ def zoom?
+ send_inq Bytes[0x04, 0x47], name: :zoom_query, priority: 0
+ end
+
+ def pantilt?
+ send_inq Bytes[0x06, 0x12], name: :pantilt_query, priority: 0
+ end
+
+ # ====== Stoppable Interface ======
+
+ def stop(index : Int32 | String = 0, emergency : Bool = false)
+ zoom(:stop)
+ end
+
+ # =================================
+
+ # VISCA over IP packet layout
+ class Packet < BinData
+ endian big
+
+ enum Type : UInt16
+ Command = 0x0100
+ Inquiry = 0x0110
+ Reply = 0x0111
+ # VISCA device setting
+ DeviceSetting = 0x0120
+
+ # reset: 0x01
+ # error: 0x0Fyy (yy = 01 : sequence number error, 02 : message error)
+ DeviceControl = 0x0200
+
+ # Acknowledge for reset
+ DeviceReply = 0x0201
+ end
+
+ enum_field UInt16, type : Type = Type::Command
+ uint16 :size, value: -> { payload.size.to_u16 }
+ uint32 :sequence
+ bytes :payload, length: -> { size }
+ end
+
+ @[Security(Level::Administrator)]
+ def send_cmd(bytes : String)
+ send_cmd(bytes.hexbytes)
+ end
+
+ protected def send_cmd(bytes : Bytes, **options)
+ # VISCA message
+ payload = IO::Memory.new
+ payload.write Bytes[@camera_address, 0x01]
+ payload.write bytes
+ payload.write_byte 0xFF_u8
+
+ # OverIP wrapper
+ packet = Packet.new
+ packet.type = :command
+ packet.payload = payload.to_slice
+
+ queue(**options) do |task|
+ sequence = next_sequence
+ packet.sequence = sequence
+
+ transport.send(packet, task) do |data, the_task|
+ # curry in the sequence we are expecting
+ received(data, the_task, sequence)
+ end
+ end
+ end
+
+ @[Security(Level::Administrator)]
+ def send_inq(bytes : String)
+ send_inq(bytes.hexbytes)
+ end
+
+ protected def send_inq(bytes : Bytes, **options)
+ # VISCA message
+ payload = IO::Memory.new
+ payload.write Bytes[@camera_address, 0x09]
+ payload.write bytes
+ payload.write_byte 0xFF_u8
+
+ # OverIP wrapper
+ packet = Packet.new
+ packet.type = :inquiry
+ packet.payload = payload.to_slice
+
+ queue(**options) do |task|
+ sequence = next_sequence
+ packet.sequence = sequence
+
+ transport.send(packet, task) do |data, the_task|
+ # curry in the sequence we are expecting
+ received(data, the_task, sequence)
+ end
+ end
+ end
+
+ protected def next_sequence : UInt32
+ # we want to ignore overflows
+ @sequence = @sequence &+ 1_u32
+ end
+
+ @[Security(Level::Administrator)]
+ def reset_sequence_number(directly : Bool = false)
+ packet = Packet.new
+ packet.type = :device_control
+ packet.sequence = @sequence = 1_u32
+ packet.payload = Bytes[0x01_u8]
+
+ return transport.send(packet) if directly
+ queue(name: :reset_sequence_number, priority: 99) do |task|
+ transport.send(packet, task) do |data|
+ # curry in the sequence we are expecting
+ received(data, task, @sequence)
+ end
+ end
+ end
+
+ # process incoming data, tokenised so we know each data packet is exactly one message
+ def received(data, task, sequence : UInt32? = nil) : Nil
+ logger.debug { "Camera sent: 0x#{data.hexstring}" }
+
+ # Was this expected data? Should have a sequence curried in
+ if sequence.nil?
+ logger.info { "unexpected packet received, ignoring as no sequence pending" }
+ return
+ end
+
+ io = IO::Memory.new(data)
+ packet = io.read_bytes(Packet)
+ payload = packet.payload
+
+ # process any errors
+ case packet.type
+ when .device_control?
+ case payload[-1]
+ when 1_u8
+ # Abnormality in the sequence number, let's reset it
+ # then we can retry the task in the ack
+ reset_sequence_number(directly: true)
+ logger.info { "sequence number error, resetting sequence" }
+ when 2_u8
+ # Abnormality in the message
+ task.try(&.abort("bad request"))
+ end
+ return
+ when .device_reply?
+ if task && task.name == "reset_sequence_number"
+ task.success
+ else
+ task.try(&.retry("sequence number reset, retrying task"))
+ end
+ return
+ when .reply?
+ # ensure it's for the current request
+ if sequence != packet.sequence
+ logger.info { "unexpected sequence number, ignoring" }
+ return
+ end
+ else
+ logger.info { "unexpected packet type #{packet.type}, ignoring" }
+ return
+ end
+
+ # Check response
+ check_command = payload[1] & 0xF0_u8
+ case check_command
+ when 0x40_u8
+ # ignore accepted message, we are interested in the completion message
+ logger.debug { "ignoring command accepted message" }
+ return
+ when 0x50_u8
+ logger.debug { "command complete message" }
+ # command execution completed successfully
+ # fall through to processing
+ when 0x60_u8
+ # an error occured!
+ case payload[2]
+ when 0x02_u8
+ task.try(&.abort("syntax error in request"))
+ when 0x03_u8
+ # command buffer is full, lets retry the request
+ schedule.in(50.milliseconds) { task.try &.retry("camera busy") }
+ when 0x04_u8
+ task.try(&.abort("request was cancelled by the user"))
+ when 0x05_u8
+ # attempt to cancel a command that might have already executed
+ task.try(&.success)
+ when 0x41_u8
+ # command can't be executed with the current camera state
+ task.try(&.abort("request could not be performed"))
+ end
+ return
+ end
+
+ # process the packet!
+ case task.try &.name
+ when "zoom_query"
+ @zoom_raw = zoom_value = decode_position(payload[2..5])
+ self[:zoom] = @zoom_pos = zoom_value.to_f * (100.0 / @zoom_max.to_f)
+ when "pantilt_query"
+ @pan_pos = decode_position(payload[2..5])
+ @tilt_pos = decode_position(payload[6..9])
+ when "zoom_to"
+ zoom?
+ when "pantilt"
+ pantilt?
+ when "power_query"
+ self[:power] = payload[-2] == 0x02_u8
+ end
+
+ task.try &.success
+ end
+end
diff --git a/drivers/sony/camera/visca_spec.cr b/drivers/sony/camera/visca_spec.cr
new file mode 100644
index 00000000000..565ad41bba8
--- /dev/null
+++ b/drivers/sony/camera/visca_spec.cr
@@ -0,0 +1,84 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Sony::Camera::VISCA" do
+ # reset the sequence number
+ puts "Testing sequence reset"
+ should_send Bytes[0x02, 0x00, 0x00, 0x01, 0x00, 0x00, 0x00, 0x01, 0x01]
+ responds Bytes[0x02, 0x01, 0x00, 0x01, 0x00, 0x00, 0x00, 0x01, 0x01]
+
+ # clear the interface socket
+ puts "Testing interface clear"
+ should_send Bytes[0x01, 0x00, 0x00, 0x05, 0x00, 0x00, 0x00, 0x02, 0x81, 0x01, 0x00, 0x01, 0xFF]
+ responds Bytes[0x01, 0x11, 0x00, 0x03, 0x00, 0x00, 0x00, 0x02, 0x90, 0x50, 0xFF]
+
+ puts "Testing camera go-home"
+ exec :home
+ should_send Bytes[0x01, 0x00, 0x00, 0x05, 0x00, 0x00, 0x00, 0x03, 0x81, 0x01, 0x06, 0x04, 0xFF]
+ responds Bytes[0x01, 0x11, 0x00, 0x03, 0x00, 0x00, 0x00, 0x03, 0x90, 0x40, 0xFF]
+ responds Bytes[0x01, 0x11, 0x00, 0x03, 0x00, 0x00, 0x00, 0x03, 0x90, 0x50, 0xFF]
+
+ # Should then query the current camera position
+ puts "Testing camera pan tilt position query"
+ should_send Bytes[0x01, 0x10, 0x00, 0x05, 0x00, 0x00, 0x00, 0x04, 0x81, 0x09, 0x06, 0x12, 0xFF]
+ responds Bytes[0x01, 0x11, 0x00, 0x03, 0x00, 0x00, 0x00, 0x04, 0x90, 0x40, 0xFF]
+ responds Bytes[0x01, 0x11, 0x00, 0x0B, 0x00, 0x00, 0x00, 0x04, 0x90, 0x50,
+ 0x0B, 0x0E, 0x0E, 0x0F, # pan pos
+ 0x01, 0x02, 0x03, 0x04, # tilt pos
+ 0xFF,
+ ]
+
+ # Check the positions are parsed correctly
+ puts "Confirming pan tilt position parsing"
+ exec(:pan_pos).get.should eq 0xBEEF
+ exec(:tilt_pos).get.should eq 0x1234
+
+ # should be able to set the camera position
+ puts "Check pan tilt request"
+ exec(:pantilt, 0x3456, 0x7890, 0xFF)
+ should_send Bytes[0x01, 0x00, 0x00, 0x0F, 0x00, 0x00, 0x00, 0x05, 0x81, 0x01,
+ 0x06, 0x02,
+ 0x0F, 0x00, # speed
+ 0x03, 0x04, 0x05, 0x06, # pan pos
+ 0x07, 0x08, 0x09, 0x00, # tilt pos
+ 0xFF,
+ ]
+ responds Bytes[0x01, 0x11, 0x00, 0x03, 0x00, 0x00, 0x00, 0x05, 0x90, 0x40, 0xFF]
+ responds Bytes[0x01, 0x11, 0x00, 0x03, 0x00, 0x00, 0x00, 0x05, 0x90, 0x50, 0xFF]
+
+ # Should then query the current camera position
+ puts "Should query pan tilt position"
+ should_send Bytes[0x01, 0x10, 0x00, 0x05, 0x00, 0x00, 0x00, 0x06, 0x81, 0x09, 0x06, 0x12, 0xFF]
+ responds Bytes[0x01, 0x11, 0x00, 0x03, 0x00, 0x00, 0x00, 0x06, 0x90, 0x40, 0xFF]
+ responds Bytes[0x01, 0x11, 0x00, 0x0B, 0x00, 0x00, 0x00, 0x06, 0x90, 0x50,
+ 0x03, 0x04, 0x05, 0x06, # pan pos
+ 0x07, 0x08, 0x09, 0x00, # tilt pos
+ 0xFF,
+ ]
+
+ # Check the positions are parsed correctly
+ puts "Confirming pan tilt position were updated"
+ exec(:pan_pos).get.should eq 0x3456
+ exec(:tilt_pos).get.should eq 0x7890
+
+ puts "Zoom to an absolute position"
+ exec(:zoom_to, 25.0)
+ should_send Bytes[0x01, 0x00, 0x00, 0x09, 0x00, 0x00, 0x00, 0x07, 0x81, 0x01,
+ 0x04, 0x47,
+ 0x01, 0x00, 0x00, 0x00, # zoom value
+ 0xFF,
+ ]
+ responds Bytes[0x01, 0x11, 0x00, 0x03, 0x00, 0x00, 0x00, 0x07, 0x90, 0x40, 0xFF]
+ responds Bytes[0x01, 0x11, 0x00, 0x03, 0x00, 0x00, 0x00, 0x07, 0x90, 0x50, 0xFF]
+
+ # Should then query the current camera zoom level
+ puts "Should query zoom level"
+ should_send Bytes[0x01, 0x10, 0x00, 0x05, 0x00, 0x00, 0x00, 0x08, 0x81, 0x09, 0x04, 0x47, 0xFF]
+ responds Bytes[0x01, 0x11, 0x00, 0x03, 0x00, 0x00, 0x00, 0x08, 0x90, 0x40, 0xFF]
+ responds Bytes[0x01, 0x11, 0x00, 0x07, 0x00, 0x00, 0x00, 0x08, 0x90, 0x50,
+ 0x01, 0x00, 0x00, 0x00, # pan pos
+ 0xFF,
+ ]
+
+ exec(:zoom_raw).get.should eq 0x1000
+ status[:zoom].should eq 25
+end
diff --git a/drivers/sony/displays/bravia.cr b/drivers/sony/displays/bravia.cr
new file mode 100644
index 00000000000..badf93e6714
--- /dev/null
+++ b/drivers/sony/displays/bravia.cr
@@ -0,0 +1,257 @@
+require "placeos-driver"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/switchable"
+
+# Documentation: https://aca.im/driver_docs/Sony/sony%20bravia%20simple%20ip%20control.pdf
+
+class Sony::Displays::Bravia < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Muteable
+
+ private INDICATOR = "\x2A\x53" # *S
+ private HASH = "################"
+
+ # Discovery Information
+ tcp_port 20060
+ descriptive_name "Sony Bravia LCD Display"
+ generic_name :Display
+
+ enum Input : UInt32
+ {% for idx in 0..3 %}
+ Tv{{idx}} = {{ idx }}
+ Hdmi{{idx}} = {{10000_0000 + idx}}
+ Mirror{{idx}} = {{50000_0000 + idx}}
+ Vga{{idx}} = {{60000_0000 + idx}}
+ {% end %}
+
+ def self.from_param(value : String) : self
+ from_value UInt32.new(value)
+ rescue
+ raise "Unknown enum #{self} value: #{value}"
+ end
+
+ def to_param : String
+ value.to_s.rjust(5, '0')
+ end
+ end
+
+ include Interface::InputSelection(Input)
+
+ def switch_to(input : Input)
+ logger.debug { "switching input to #{input}" }
+ request(Command::Input, input.to_param)
+ self[:input] = input.to_s
+ input?
+ end
+
+ def input?
+ query(Command::Input, priority: 0)
+ end
+
+ def on_load
+ self[:volume_min] = 0
+ self[:volume_max] = 100
+ end
+
+ def connected
+ schedule.every(30.seconds, true) do
+ do_poll
+ end
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ def power(state : Bool)
+ request(Command::Power, state)
+ power?
+ end
+
+ def power?
+ query(Command::Power)
+ end
+
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ request(Command::Mute, state)
+ mute?
+ end
+
+ def unmute
+ mute false
+ end
+
+ def mute?
+ query(Command::Mute, priority: 0)
+ end
+
+ def mute_audio(state : Bool = true)
+ request(Command::AudioMute, state)
+ audio_mute?
+ end
+
+ def unmute_audio
+ mute_audio false
+ end
+
+ def audio_mute?
+ query(Command::AudioMute, priority: 0)
+ end
+
+ def volume(level : Int32 | Float64)
+ level = level.to_f.clamp(0.0, 100.0).round_away.to_i
+ request(Command::Volume, level)
+ volume?
+ end
+
+ def volume?
+ query(Command::Volume, priority: 0)
+ end
+
+ def volume_up
+ current_volume = status?(Float64, :volume) || 50.0
+ volume(current_volume + 5.0)
+ end
+
+ def volume_down
+ current_volume = status?(Float64, :volume) || 50.0
+ volume(current_volume - 5.0)
+ end
+
+ def do_poll
+ if self[:power]?
+ input?
+ mute?
+ audio_mute?
+ volume?
+ end
+ end
+
+ enum MessageType : UInt8
+ Answer = 0x41
+ Control = 0x43
+ Enquiry = 0x45
+ Notify = 0x4e
+ Error = 0x46
+
+ def control_character
+ value.chr
+ end
+ end
+
+ def received(data, task)
+ parsed_data = convert_binary(data[3..6])
+ cmd = Command.from_response?(parsed_data)
+
+ logger.debug { "Sony sent: #{cmd}" }
+
+ return task.try(&.abort("unrecognised command: #{parsed_data}")) if cmd.nil?
+ param = data[7..-1]
+ return task.try(&.abort("error")) if param.first? == MessageType::Error.value
+ case MessageType.from_value?(data[2])
+ when MessageType::Answer
+ update_status cmd, param
+ task.try &.success
+ when MessageType::Notify
+ update_status cmd, param
+ else
+ logger.debug { "Unhandled device response: #{data[2].chr rescue data[2]}" }
+ task.try &.abort("Unhandled device response")
+ end
+ end
+
+ COMMANDS = {
+ ir_code: "IRCC",
+ power: "POWR",
+ volume: "VOLU",
+ audio_mute: "AMUT",
+ mute: "PMUT",
+ channel: "CHNN",
+ tv_input: "ISRC",
+ input: "INPT",
+ toggle_mute: "TPMU",
+ pip: "PIPI",
+ toggle_pip: "TPIP",
+ position_pip: "TPPP",
+ broadcast_address: "BADR",
+ mac_address: "MADR",
+ }
+
+ {% begin %}
+ enum Command
+ {% begin %}
+ {% for command in COMMANDS.keys %}
+ {{ command.camelcase.id }}
+ {% end %}
+ {% end %}
+
+ def function
+ {% begin %}
+ case self
+ {% for kv in COMMANDS.to_a %}
+ {% command, value = kv[0], kv[1] %}
+ in {{ command.camelcase }} then {{ value }}
+ {% end %}
+ end
+ {% end %}
+ end
+
+ def self.from_response?(message)
+ {% begin %}
+ case message
+ {% for kv in COMMANDS.to_a %}
+ {% command, value = kv[0], kv[1] %}
+ when {{ value }} then {{ command.camelcase.id }}
+ {% end %}
+ end
+ {% end %}
+ end
+ end
+ {% end %}
+
+ protected def convert_binary(data)
+ String.new(slice: data)
+ end
+
+ protected def request(command, parameter, **options)
+ cmd = command.function
+ parameter = parameter ? 1 : 0 if parameter.is_a?(Bool)
+ param = parameter.to_s.rjust(16, '0')
+ do_send(MessageType::Control, cmd, param, **options)
+ end
+
+ protected def query(state, **options)
+ cmd = state.function
+ do_send(MessageType::Enquiry, cmd, HASH, **options)
+ end
+
+ protected def do_send(type, command, parameter, **options)
+ cmd = "#{INDICATOR}#{type.control_character}#{command}#{parameter}\n"
+ send(cmd, **options)
+ end
+
+ protected def update_status(cmd : Command, param)
+ parsed_data = convert_binary(param)
+ case cmd
+ when .power?
+ self[:power] = parsed_data.to_i == 1
+ when .mute?
+ self[:mute] = parsed_data.to_i == 1
+ when .audio_mute?
+ self[:audio_mute] = parsed_data.to_i == 1
+ when .pip?
+ self[:pip] = parsed_data.to_i == 1
+ when .volume?
+ self[:volume] = parsed_data.to_i
+ when .mac_address?
+ self[:mac_address] = parsed_data.split('#')[0]
+ when .input?
+ self[:input] = Input.from_param(parsed_data[7..15])
+ end
+ end
+end
diff --git a/drivers/sony/displays/bravia_pro.cr b/drivers/sony/displays/bravia_pro.cr
new file mode 100644
index 00000000000..b02277fe0f0
--- /dev/null
+++ b/drivers/sony/displays/bravia_pro.cr
@@ -0,0 +1,374 @@
+require "placeos-driver"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/switchable"
+
+# Documentation: https://pro-bravia.sony.net/develop/integrate/rest-api/spec/
+
+class Sony::Displays::BraviaPro < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Muteable
+
+ # Discovery Information
+ uri_base "http://"
+ descriptive_name "Sony Bravia Pro Display (REST API)"
+ generic_name :Display
+
+ default_settings({
+ psk: "1234", # Pre-Shared Key for authentication
+ })
+
+ enum Input
+ Hdmi1
+ Hdmi2
+ Hdmi3
+ Hdmi4
+ Tv
+ ComponentVideo
+ CompositeVideo
+ Scart
+ Pc
+ AnalogRgb
+ DviD
+
+ def to_api_uri : String
+ case self
+ when .hdmi1?
+ "extInput:hdmi?port=1"
+ when .hdmi2?
+ "extInput:hdmi?port=2"
+ when .hdmi3?
+ "extInput:hdmi?port=3"
+ when .hdmi4?
+ "extInput:hdmi?port=4"
+ when .tv?
+ "tv:dvbt"
+ when .component_video?
+ "extInput:component?port=1"
+ when .composite_video?
+ "extInput:composite?port=1"
+ when .scart?
+ "extInput:scart?port=1"
+ when .pc?
+ "extInput:vga?port=1"
+ when .analog_rgb?
+ "extInput:vga?port=1"
+ when .dvi_d?
+ "extInput:dvi?port=1"
+ else
+ "extInput:hdmi?port=1"
+ end
+ end
+
+ def self.from_api_uri(uri : String) : Input?
+ case uri
+ when /hdmi.*port=1/
+ Hdmi1
+ when /hdmi.*port=2/
+ Hdmi2
+ when /hdmi.*port=3/
+ Hdmi3
+ when /hdmi.*port=4/
+ Hdmi4
+ when /tv:dvbt/
+ Tv
+ when /component/
+ ComponentVideo
+ when /composite/
+ CompositeVideo
+ when /scart/
+ Scart
+ when /vga/
+ AnalogRgb
+ when /dvi/
+ DviD
+ else
+ nil
+ end
+ end
+ end
+
+ include Interface::InputSelection(Input)
+
+ @psk : String = "1234"
+
+ def on_load
+ @psk = setting(String, :psk) || "1234"
+
+ self[:volume_min] = 0
+ self[:volume_max] = 100
+ end
+
+ def on_update
+ @psk = setting(String, :psk) || "1234"
+ end
+
+ def connected
+ schedule.every(30.seconds, true) do
+ do_poll
+ end
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ # Power Control
+ def power(state : Bool)
+ method = state ? "setPowerStatus" : "setPowerStatus"
+ status = state ? "active" : "standby"
+
+ response = post("/sony/system",
+ headers: auth_headers,
+ body: {
+ method: method,
+ id: 1,
+ params: [{status: status}],
+ version: "1.0",
+ }.to_json
+ )
+
+ if response.success?
+ self[:power] = state
+ power?
+ else
+ logger.warn { "Power command failed: #{response.body}" }
+ end
+
+ state
+ end
+
+ def power?
+ response = post("/sony/system",
+ headers: auth_headers,
+ body: {
+ method: "getPowerStatus",
+ id: 2,
+ params: [] of String,
+ version: "1.0",
+ }.to_json
+ )
+
+ if response.success?
+ data = JSON.parse(response.body)
+ if result = data["result"]?.try(&.as_a?.try(&.first?))
+ status = result["status"]?.try(&.as_s)
+ power_state = status == "active"
+ self[:power] = power_state
+ power_state
+ else
+ logger.warn { "Failed to parse power status response: #{response.body}" }
+ nil
+ end
+ else
+ logger.warn { "Power status query failed: #{response.body}" }
+ nil
+ end
+ end
+
+ # Volume Control
+ def volume(level : Int32 | Float64)
+ level = level.to_f.clamp(0.0, 100.0).round_away.to_i
+
+ response = post("/sony/audio",
+ headers: auth_headers,
+ body: {
+ method: "setAudioVolume",
+ id: 3,
+ params: [{
+ target: "speaker",
+ volume: level.to_s,
+ }],
+ version: "1.0",
+ }.to_json
+ )
+
+ if response.success?
+ self[:volume] = level
+ volume?
+ else
+ logger.warn { "Volume command failed: #{response.body}" }
+ end
+
+ level
+ end
+
+ def volume?
+ response = post("/sony/audio",
+ headers: auth_headers,
+ body: {
+ method: "getVolumeInformation",
+ id: 4,
+ params: [] of String,
+ version: "1.0",
+ }.to_json
+ )
+
+ if response.success?
+ data = JSON.parse(response.body)
+ if result = data["result"]?.try(&.as_a?.try(&.first?))
+ if targets = result.as_a?
+ speaker_info = targets.find { |t| t["target"]? == "speaker" }
+ if speaker_info
+ volume_level = speaker_info["volume"]?.try(&.as_s.to_i?)
+ if volume_level
+ self[:volume] = volume_level
+ return volume_level
+ end
+ end
+ end
+ end
+ logger.warn { "Failed to parse volume response: #{response.body}" }
+ nil
+ else
+ logger.warn { "Volume query failed: #{response.body}" }
+ nil
+ end
+ end
+
+ def volume_up
+ current_volume = status?(Int32, :volume) || 50
+ volume(current_volume + 5)
+ end
+
+ def volume_down
+ current_volume = status?(Int32, :volume) || 50
+ volume(current_volume - 5)
+ end
+
+ # Mute Control
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo,
+ )
+ response = post("/sony/audio",
+ headers: auth_headers,
+ body: {
+ method: "setAudioMute",
+ id: 5,
+ params: [{
+ status: state,
+ }],
+ version: "1.0",
+ }.to_json
+ )
+
+ if response.success?
+ self[:mute] = state
+ mute?
+ else
+ logger.warn { "Mute command failed: #{response.body}" }
+ end
+
+ state
+ end
+
+ def unmute
+ mute(false)
+ end
+
+ def mute?
+ response = post("/sony/audio",
+ headers: auth_headers,
+ body: {
+ method: "getVolumeInformation",
+ id: 6,
+ params: [] of String,
+ version: "1.0",
+ }.to_json
+ )
+
+ if response.success?
+ data = JSON.parse(response.body)
+ if result = data["result"]?.try(&.as_a?.try(&.first?))
+ if targets = result.as_a?
+ speaker_info = targets.find { |t| t["target"]? == "speaker" }
+ if speaker_info
+ mute_state = speaker_info["mute"]?.try(&.as_bool)
+ if !mute_state.nil?
+ self[:mute] = mute_state
+ return mute_state
+ end
+ end
+ end
+ end
+ logger.warn { "Failed to parse mute response: #{response.body}" }
+ nil
+ else
+ logger.warn { "Mute query failed: #{response.body}" }
+ nil
+ end
+ end
+
+ # Input Selection
+ def switch_to(input : Input)
+ logger.debug { "switching input to #{input}" }
+
+ response = post("/sony/avContent",
+ headers: auth_headers,
+ body: {
+ method: "setPlayContent",
+ id: 7,
+ params: [{
+ uri: input.to_api_uri,
+ }],
+ version: "1.0",
+ }.to_json
+ )
+
+ if response.success?
+ self[:input] = input.to_s
+ input?
+ else
+ logger.warn { "Input switch failed: #{response.body}" }
+ end
+
+ input
+ end
+
+ def input?
+ response = post("/sony/avContent",
+ headers: auth_headers,
+ body: {
+ method: "getPlayingContentInfo",
+ id: 8,
+ params: [] of String,
+ version: "1.0",
+ }.to_json
+ )
+
+ if response.success?
+ data = JSON.parse(response.body)
+ if result = data["result"]?.try(&.as_a?.try(&.first?))
+ if uri = result["uri"]?.try(&.as_s)
+ if input = Input.from_api_uri(uri)
+ self[:input] = input.to_s
+ input
+ else
+ logger.warn { "Unknown input URI: #{uri}" }
+ nil
+ end
+ end
+ end
+ else
+ logger.warn { "Input query failed: #{response.body}" }
+ nil
+ end
+ end
+
+ private def do_poll
+ if self[:power]?
+ input?
+ mute?
+ volume?
+ end
+ end
+
+ private def auth_headers
+ HTTP::Headers{
+ "X-Auth-PSK" => @psk,
+ "Content-Type" => "application/json",
+ }
+ end
+end
diff --git a/drivers/sony/displays/bravia_pro_spec.cr b/drivers/sony/displays/bravia_pro_spec.cr
new file mode 100644
index 00000000000..11698c22711
--- /dev/null
+++ b/drivers/sony/displays/bravia_pro_spec.cr
@@ -0,0 +1,153 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Sony::Displays::BraviaPro" do
+ settings({
+ psk: "test1234",
+ })
+
+ # Test power on
+ exec(:power, true)
+ expect_http_request do |request, response|
+ request.method.should eq("POST")
+ request.path.should eq("/sony/system")
+ request.headers["X-Auth-PSK"]?.should eq("test1234")
+ request.headers["Content-Type"]?.should eq("application/json")
+
+ if io = request.body
+ data = JSON.parse(io.gets_to_end)
+ data["method"].should eq("setPowerStatus")
+ data["params"][0]["status"].should eq("active")
+ end
+
+ response.status_code = 200
+ response.headers["Content-Type"] = "application/json"
+ response.output << {"result": [] of String, "id": 1}.to_json
+ end
+
+ expect_http_request do |request, response|
+ request.method.should eq("POST")
+ request.path.should eq("/sony/system")
+
+ if io = request.body
+ data = JSON.parse(io.gets_to_end)
+ data["method"].should eq("getPowerStatus")
+ end
+
+ response.status_code = 200
+ response.headers["Content-Type"] = "application/json"
+ response.output << {"result": [{"status": "active"}], "id": 2}.to_json
+ end
+
+ status[:power].should eq(true)
+
+ # Test power off
+ exec(:power, false)
+ expect_http_request do |request, response|
+ if io = request.body
+ data = JSON.parse(io.gets_to_end)
+ data["params"][0]["status"].should eq("standby")
+ end
+
+ response.status_code = 200
+ response.headers["Content-Type"] = "application/json"
+ response.output << {"result": [] of String, "id": 1}.to_json
+ end
+
+ expect_http_request do |request, response|
+ response.status_code = 200
+ response.headers["Content-Type"] = "application/json"
+ response.output << {"result": [{"status": "standby"}], "id": 2}.to_json
+ end
+
+ status[:power].should eq(false)
+
+ # Test volume setting
+ exec(:volume, 75)
+ expect_http_request do |request, response|
+ request.path.should eq("/sony/audio")
+
+ if io = request.body
+ data = JSON.parse(io.gets_to_end)
+ data["method"].should eq("setAudioVolume")
+ data["params"][0]["volume"].should eq("75")
+ end
+
+ response.status_code = 200
+ response.headers["Content-Type"] = "application/json"
+ response.output << {"result": [] of String, "id": 3}.to_json
+ end
+
+ expect_http_request do |request, response|
+ if io = request.body
+ data = JSON.parse(io.gets_to_end)
+ data["method"].should eq("getVolumeInformation")
+ end
+
+ response.status_code = 200
+ response.headers["Content-Type"] = "application/json"
+ response.output << {"result": [[{"target": "speaker", "volume": "75", "mute": false}]], "id": 4}.to_json
+ end
+
+ status[:volume].should eq(75)
+
+ # Test mute
+ exec(:mute, true)
+ expect_http_request do |request, response|
+ if io = request.body
+ data = JSON.parse(io.gets_to_end)
+ data["method"].should eq("setAudioMute")
+ data["params"][0]["status"].should eq(true)
+ end
+
+ response.status_code = 200
+ response.headers["Content-Type"] = "application/json"
+ response.output << {"result": [] of String, "id": 5}.to_json
+ end
+
+ expect_http_request do |request, response|
+ response.status_code = 200
+ response.headers["Content-Type"] = "application/json"
+ response.output << {"result": [[{"target": "speaker", "volume": "75", "mute": true}]], "id": 6}.to_json
+ end
+
+ status[:mute].should eq(true)
+
+ # Test input switching
+ exec(:switch_to, "hdmi1")
+ expect_http_request do |request, response|
+ request.path.should eq("/sony/avContent")
+
+ if io = request.body
+ data = JSON.parse(io.gets_to_end)
+ data["method"].should eq("setPlayContent")
+ data["params"][0]["uri"].should eq("extInput:hdmi?port=1")
+ end
+
+ response.status_code = 200
+ response.headers["Content-Type"] = "application/json"
+ response.output << {"result": [] of String, "id": 7}.to_json
+ end
+
+ expect_http_request do |request, response|
+ if io = request.body
+ data = JSON.parse(io.gets_to_end)
+ data["method"].should eq("getPlayingContentInfo")
+ end
+
+ response.status_code = 200
+ response.headers["Content-Type"] = "application/json"
+ response.output << {"result": [{"uri": "extInput:hdmi?port=1", "title": "HDMI 1"}], "id": 8}.to_json
+ end
+
+ status[:input].should eq("Hdmi1")
+
+ # Test volume query
+ exec(:volume?)
+ expect_http_request do |request, response|
+ response.status_code = 200
+ response.headers["Content-Type"] = "application/json"
+ response.output << {"result": [[{"target": "speaker", "volume": "65", "mute": false}]], "id": 4}.to_json
+ end
+
+ status[:volume].should eq(65)
+end
diff --git a/drivers/sony/displays/bravia_spec.cr b/drivers/sony/displays/bravia_spec.cr
new file mode 100644
index 00000000000..275d3457b14
--- /dev/null
+++ b/drivers/sony/displays/bravia_spec.cr
@@ -0,0 +1,55 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Sony::Displays::Bravia" do
+ exec(:power, true)
+ should_send("\x2A\x53\x43POWR0000000000000001\n")
+ responds("\x2A\x53\x41POWR0000000000000000\n")
+ should_send("\x2A\x53\x45POWR################\n")
+ responds("\x2A\x53\x41POWR0000000000000001\n")
+ status[:power].should eq(true)
+
+ exec(:switch_to, "hdmi1")
+ should_send("\x2A\x53\x43INPT0000000100000001\n")
+ responds("\x2A\x53\x41INPT0000000000000000\n")
+ should_send("\x2A\x53\x45INPT################\n")
+ responds("\x2A\x53\x41INPT0000000100000001\n")
+ status[:input].should eq("Hdmi1")
+
+ exec(:switch_to, "vga3")
+ should_send("\x2A\x53\x43INPT0000000600000003\n")
+ responds("\x2A\x53\x41INPT0000000000000000\n")
+ should_send("\x2A\x53\x45INPT################\n")
+ responds("\x2A\x53\x41INPT0000000600000003\n")
+ status[:input].should eq("Vga3")
+
+ exec(:volume, 99)
+ should_send("\x2A\x53\x43VOLU0000000000000099\n")
+ responds("\x2A\x53\x41VOLU0000000000000000\n")
+ should_send("\x2A\x53\x45VOLU################\n")
+ responds("\x2A\x53\x41VOLU0000000000000099\n")
+ status[:volume].should eq(99)
+
+ # Test failure
+ exec(:mute)
+ should_send("\x2A\x53\x43PMUT0000000000000001\n")
+ responds("\x2A\x53\x41PMUT0000000000000000\n")
+ should_send("\x2A\x53\x45PMUT################\n")
+ responds("\x2A\x53\x41PMUT0000000000000001\n")
+ status[:mute].should eq(true)
+
+ exec(:unmute)
+ should_send("\x2A\x53\x43PMUT0000000000000000\n")
+ responds("\x2A\x53\x41PMUTFFFFFFFFFFFFFFFF\n")
+ should_send("\x2A\x53\x45PMUT################\n")
+ responds("\x2A\x53\x41PMUT0000000000000001\n")
+ status[:mute].should eq(true)
+
+ exec(:volume, 50)
+ should_send("\x2A\x53\x43VOLU0000000000000050\n")
+ responds("\x2A\x53\x4EPMUT0000000000000000\n") # mix in a notify
+ responds("\x2A\x53\x41VOLU0000000000000000\n")
+ should_send("\x2A\x53\x45VOLU################\n")
+ responds("\x2A\x53\x41VOLU0000000000000050\n")
+ status[:volume].should eq(50)
+ status[:mute].should eq(false)
+end
diff --git a/drivers/sony/projector/fh.cr b/drivers/sony/projector/fh.cr
new file mode 100644
index 00000000000..bfbc9871e85
--- /dev/null
+++ b/drivers/sony/projector/fh.cr
@@ -0,0 +1,171 @@
+require "placeos-driver"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/switchable"
+
+# Documentation: https://drive.google.com/a/room.tools/file/d/1C0gAWNOtkbrHFyky_9LfLCkPoMcYU9lO/view?usp=sharing
+
+class Sony::Projector::Fh < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Muteable
+
+ enum Inputs
+ HDMI
+ DVI
+ Video
+ SVideo
+ RGB
+ HDBaseT
+ InputA
+ InputB
+ InputC
+ InputD
+ InputE
+
+ def to_message : String
+ case self
+ in HDMI, DVI, Video, SVideo, RGB, HDBaseT
+ to_s.downcase + "1"
+ in InputA, InputB, InputC, InputD, InputE
+ to_s.underscore
+ end
+ end
+
+ def readable : String
+ to_s.downcase
+ end
+ end
+
+ include PlaceOS::Driver::Interface::InputSelection(Inputs)
+
+ descriptive_name "Sony Projector FH Series"
+ generic_name :Display
+
+ def on_load
+ transport.tokenizer = Tokenizer.new("\r\n")
+ end
+
+ def connected
+ schedule.every(60.seconds) { do_poll }
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ def power(state : Bool)
+ set("power", state ? "on" : "off").get
+ self[:power] = state
+ end
+
+ def power?
+ get("power_status")
+ !!self[:power]?.try(&.as_bool)
+ end
+
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ set("blank", state ? "on" : "off").get
+ self[:mute] = state
+ end
+
+ def mute?
+ get("blank").get
+ self[:mute].as_bool
+ end
+
+ INPUTS_LOOKUP = {
+ "hdmi1" => Inputs::HDMI,
+ "dvi1" => Inputs::DVI,
+ "video1" => Inputs::Video,
+ "svideo1" => Inputs::SVideo,
+ "rgb1" => Inputs::RGB,
+ "hdbaset1" => Inputs::HDBaseT,
+ "input_a" => Inputs::InputA,
+ "input_b" => Inputs::InputB,
+ "input_c" => Inputs::InputC,
+ "input_d" => Inputs::InputD,
+ "input_e" => Inputs::InputE,
+ }
+
+ def switch_to(input : Inputs)
+ set("input", input.to_message).get
+ self[:input] = input.readable
+ end
+
+ def input?
+ get("input").get
+ self[:input].as_s
+ end
+
+ {% for name in ["contrast", "brightness", "color", "hue", "sharpness"] %}
+ def {{name.id}}?
+ get({{name.id.stringify}})
+ end
+
+ def {{name.id}}(val : Int32)
+ set({{name.id.stringify}}, val.clamp(0, 100))
+ end
+ {% end %}
+
+ private def do_poll
+ return unless power?
+ input?
+ mute?
+ end
+
+ def received(response, task)
+ process_response(response, task)
+ end
+
+ private def process_response(response, task, path = nil)
+ response = String.new(response)
+ logger.debug { "Sony proj sent: #{response}" }
+ data = shellsplit(response.strip.downcase)
+
+ return task.try &.success if data[0] == "ok"
+ return task.try &.abort if data[0] == "err_cmd"
+
+ case path
+ when "power_status"
+ self[:power] = data[0] == "on"
+ when "blank"
+ self[:mute] = data[0] == "on"
+ when "input"
+ self[:input] = INPUTS_LOOKUP[data[0]].readable
+ end
+ task.try &.success
+ end
+
+ private def get(path, **options)
+ cmd = "#{path} ?\r\n"
+ logger.debug { "Sony projector FH requesting: #{cmd}" }
+ send(cmd, **options) { |data, task| process_response(data, task, path) }
+ end
+
+ private def set(path, arg, **options)
+ cmd = "#{path} \"#{arg}\"\r\n"
+ logger.debug { "Sony projector FH sending: #{cmd}" }
+ send(cmd, **options) { |data, task| process_response(data, task, path) }
+ end
+
+ # Quick dirty port of https://github.com/ruby/ruby/blob/master/lib/shellwords.rb
+ private def shellsplit(line : String) : Array(String)
+ words = [] of String
+ field = ""
+ pattern = /\G\s*(?>([^\s\\\'\"]+)|'([^\']*)'|"((?:[^\"\\]|\\.)*)"|(\\.?)|(\S))(\s|\z)?/m
+ line.scan(pattern) do |match|
+ _, word, sq, dq, esc, garbage, sep = match.to_a
+ raise ArgumentError.new("Unmatched quote: #{line.inspect}") if garbage
+ field += (word || sq || dq.try(&.gsub(/\\([$`"\\\n])/, "\\1")) || esc.not_nil!.gsub(/\\(.)/, "\\1"))
+ if sep
+ words << field
+ field = ""
+ end
+ end
+ words
+ end
+end
diff --git a/drivers/sony/projector/fh_spec.cr b/drivers/sony/projector/fh_spec.cr
new file mode 100644
index 00000000000..908f8fab38e
--- /dev/null
+++ b/drivers/sony/projector/fh_spec.cr
@@ -0,0 +1,33 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Sony::Projector::Fh" do
+ exec(:power?)
+ should_send("power_status ?\r\n")
+ responds("\"standby\"\r\n")
+ status[:power].should eq(false)
+
+ exec(:power, true)
+ should_send("power \"on\"\r\n")
+ responds("ok\r\n")
+ status[:power].should eq(true)
+
+ exec(:mute?)
+ should_send("blank ?\r\n")
+ responds("\"on\"\r\n")
+ status[:mute].should eq(true)
+
+ exec(:mute, false)
+ should_send("blank \"off\"\r\n")
+ responds("ok\r\n")
+ status[:mute].should eq(false)
+
+ exec(:input?)
+ should_send("input ?\r\n")
+ responds("\"hdmi1\"\r\n")
+ status[:input].should eq("hdmi")
+
+ exec(:switch_to, "rgb")
+ should_send("input \"rgb1\"\r\n")
+ responds("ok\r\n")
+ status[:input].should eq("rgb")
+end
diff --git a/drivers/sony/projector/pj_talk.cr b/drivers/sony/projector/pj_talk.cr
new file mode 100644
index 00000000000..a0c287bb336
--- /dev/null
+++ b/drivers/sony/projector/pj_talk.cr
@@ -0,0 +1,292 @@
+require "placeos-driver"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/switchable"
+
+# Documentation: https://aca.im/driver_docs/Sony/Sony_Q004_R1_protocol.pdf
+# also https://aca.im/driver_docs/Sony/TCP_CMDs.pdf
+
+class Sony::Projector::PjTalk < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Muteable
+
+ descriptive_name "Sony Projector PjTalk"
+ generic_name :Display
+ tcp_port 53484
+
+ default_settings({
+ community: "SONY",
+ })
+
+ @community : String = ""
+
+ def on_load
+ # abstract tokenizer, expects us to return the message length
+ transport.tokenizer = Tokenizer.new do |io|
+ bytes = io.to_slice
+
+ # Min message length is 10 bytes, with the 10th byte being the payload size
+ bytes.size < 10 ? -1 : 10 + bytes[9]
+ end
+
+ on_update
+ end
+
+ def on_update
+ @community = setting?(String, :community) || "SONY"
+ end
+
+ def connected
+ schedule.every(60.seconds) { do_poll }
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ def power(state : Bool)
+ if state
+ # Need to send twice in case of deep sleep
+ logger.debug { "requested to power on" }
+ do_send(:set, :power_on, name: :power)
+ else
+ logger.debug { "requested to power off" }
+ do_send(:set, :power_off, name: :power, delay: 3.seconds)
+ end
+
+ # Request status update
+ power?(priority: 50)
+ end
+
+ def power?(priority : Int32 = 0, **options)
+ do_send(:get, :power_status, **options, priority: priority).get
+ !!self[:power].try(&.as_bool)
+ end
+
+ enum Input
+ HDMI = 0x0003 # same as InputB
+ InputA = 0x0002
+ InputB = 0x0003
+ InputC = 0x0004
+ InputD = 0x0005
+ USB = 0x0006 # USB type B
+ Network = 0x0007 # network
+
+ def to_bytes : Bytes
+ Bytes[self.value >> 8, self.value & 0xFF]
+ end
+
+ def self.from_bytes(b : Bytes)
+ Input.from_value((b[0].to_u16 << 8) + b[1])
+ end
+ end
+
+ include PlaceOS::Driver::Interface::InputSelection(Input)
+
+ def switch_to(input : Input)
+ do_send(:set, :input, input.to_bytes) # , delay_on_receive: 500.milliseconds)
+ logger.debug { "requested to switch to: #{input}" }
+
+ input?
+ end
+
+ def input?
+ do_send(:get, :input, priority: 0)
+ end
+
+ def lamp_time?
+ do_send(:get, :lamp_timer, priority: 0)
+ end
+
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ do_send(:set, :mute, Bytes[0, state ? 1 : 0]) # , delay_on_receive: 500)
+ mute?
+ end
+
+ def mute?
+ do_send(:get, :mute, priority: 0)
+ end
+
+ METHODS = [:contrast, :brightness, :color, :hue, :sharpness]
+
+ {% for name in METHODS %}
+ @[Security(Level::Administrator)]
+ def {{name.id}}?
+ do_send(:get, {{name}}, priority: 0)
+ end
+ {% end %}
+
+ {% for name in METHODS %}
+ @[Security(Level::Administrator)]
+ def {{name.id}}(value : UInt8)
+ do_send(:set, {{name}}, Bytes[0, value.clamp(0, 100)], priority: 0)
+ end
+ {% end %}
+
+ enum Command
+ PowerOn = 0x172E
+ PowerOff = 0x172F
+ Input = 0x0001
+ Mute = 0x0030
+ ErrorStatus = 0x0101
+ PowerStatus = 0x0102
+ Contrast = 0x0010
+ Brightness = 0x0011
+ Color = 0x0012
+ Hue = 0x0013
+ Sharpness = 0x0014
+ LampTimer = 0x0113
+
+ def to_bytes : Bytes
+ Bytes[self.value >> 8, self.value & 0xFF]
+ end
+
+ def self.from_bytes(b : Bytes)
+ Command.from_value((b[0].to_u16 << 8) + b[1])
+ end
+ end
+
+ enum CommandType : UInt8
+ Set = 0
+ Get
+ end
+
+ PJTALK_HEADER = Bytes[0x02, 0x0a]
+
+ protected def do_send(cmd_type : CommandType, command : Command, param : Bytes? = nil, name : String | Symbol? = nil, **options)
+ io = IO::Memory.new(14)
+ io.write PJTALK_HEADER
+ io << @community
+ io.write_byte(cmd_type.value)
+ io.write(command.to_bytes)
+
+ if param
+ io.write_byte param.size.to_u8
+ io.write param
+ else
+ io.write_byte 0_u8
+ end
+
+ send(io.to_slice, **options, name: name || (param ? "#{command}_req" : command))
+ end
+
+ def do_poll
+ if power?
+ input?
+ mute?
+ do_send(:get, :error_status, priority: 0)
+ lamp_time?
+ end
+ end
+
+ enum ResponseStatus : UInt8
+ NoGood = 0
+ Okay
+ end
+
+ def received(data, task)
+ logger.debug { "sony proj sent: 0x#{data.hexstring}" }
+
+ response_status = ResponseStatus.from_value data[6]
+ pjt_command = Command.from_bytes data[7..8]
+ pjt_length = data[9]
+ pjt_data = pjt_length > 0 ? data[10..-1] : Bytes.new(0)
+
+ # check for error response
+ if response_status.no_good?
+ category = ERROR_CATEGORY[pjt_data[0]]? || :unknown
+ message = ERRORS[category][pjt_data[1]]? || "unknown: category #{pjt_data[1].to_s(16)}, reason #{pjt_data[1].to_s(16)}"
+
+ self[:last_error] = "#{category}: #{message}"
+ logger.debug { "Command #{pjt_command} failed with #{category}: #{message}" }
+ return task.try &.abort
+ end
+
+ # process a successful response
+ case pjt_command
+ when .power_on?
+ self[:power] = true
+ when .power_off?
+ self[:power] = false
+ when .lamp_timer?
+ # Two bytes converted to a 16bit integer
+ # we use negative indexes as can be a 32bit response (only 16bits needed)
+ self[:lamp_usage] = (pjt_data[-2].to_u16 << 8) + pjt_data[-1]
+ when .power_status?
+ case pjt_data[-1]
+ when 0, 8
+ self[:warming] = self[:cooling] = self[:power] = false
+ when 1, 2
+ self[:cooling] = false
+ self[:warming] = self[:power] = true
+ when 3
+ self[:power] = true
+ self[:warming] = self[:cooling] = false
+ when 4, 5, 6, 7
+ self[:cooling] = true
+ self[:warming] = self[:power] = false
+ end
+ schedule.in(5.seconds) { power? } if self[:warming] || self[:cooling]
+ when .mute?
+ self[:mute] = pjt_data[-1] == 1
+ when .input?
+ self[:input] = Input.from_bytes(pjt_data)
+ when .contrast?, .brightness?, color?, .hue?, .sharpness?
+ self[pjt_command.to_s.downcase] = pjt_data[-1]
+ end
+
+ task.try &.success
+ end
+
+ ERROR_CATEGORY = {
+ 0x01_u8 => :item_error,
+ 0x02_u8 => :community_error,
+ 0x10_u8 => :request_error,
+ 0x20_u8 => :network_error,
+ 0xF0_u8 => :comms_error,
+ 0xF1_u8 => :ram_error,
+ }
+
+ ERRORS = {
+ item_error: {
+ 0x01_u8 => "Invalid Item",
+ 0x02_u8 => "Invalid Item Request",
+ 0x03_u8 => "Invalid Length",
+ 0x04_u8 => "Invalid Data",
+ 0x11_u8 => "Short Data",
+ 0x80_u8 => "Not Applicable Item",
+ },
+ community_error: {
+ 0x01_u8 => "Different Community",
+ },
+ request_error: {
+ 0x01_u8 => "Invalid Version",
+ 0x02_u8 => "Invalid Category",
+ 0x03_u8 => "Invalid Request",
+ 0x11_u8 => "Short Header",
+ 0x12_u8 => "Short Community",
+ 0x13_u8 => "Short Command",
+ },
+ network_error: {
+ 0x01_u8 => "Timeout",
+ },
+ comms_error: {
+ 0x01_u8 => "Timeout",
+ 0x10_u8 => "Check Sum Error",
+ 0x20_u8 => "Framing Error",
+ 0x30_u8 => "Parity Error",
+ 0x40_u8 => "Over Run Error",
+ 0x50_u8 => "Other Comm Error",
+ 0xF0_u8 => "Unknown Response",
+ },
+ ram_error: {
+ 0x10_u8 => "Read Error",
+ 0x20_u8 => "Write Error",
+ },
+ unknown: {} of UInt8 => String,
+ }
+end
diff --git a/drivers/sony/projector/pj_talk_spec.cr b/drivers/sony/projector/pj_talk_spec.cr
new file mode 100644
index 00000000000..9afd43d1431
--- /dev/null
+++ b/drivers/sony/projector/pj_talk_spec.cr
@@ -0,0 +1,17 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Sony::Projector::PjTalk" do
+ resp = exec(:power?)
+ should_send("020a534f4e5901010200".hexbytes)
+ responds("020a534f4e590101020100".hexbytes)
+ resp.get.should eq false
+ status[:power].should eq(false)
+
+ exec(:power, true)
+ should_send("020a534f4e5900172E00".hexbytes)
+ responds("020a534f4e5901172E00".hexbytes)
+
+ should_send("020a534f4e5901010200".hexbytes)
+ responds("020a534f4e590101020103".hexbytes)
+ status[:power].should eq(true)
+end
diff --git a/drivers/sony/projector/serial_control.cr b/drivers/sony/projector/serial_control.cr
new file mode 100644
index 00000000000..07375056974
--- /dev/null
+++ b/drivers/sony/projector/serial_control.cr
@@ -0,0 +1,229 @@
+require "placeos-driver"
+require "placeos-driver/interface/powerable"
+require "placeos-driver/interface/muteable"
+require "placeos-driver/interface/switchable"
+
+# Documentation: https://aca.im/driver_docs/Sony/Sony_Q004_R1_protocol.pdf
+
+class Sony::Projector::SerialControl < PlaceOS::Driver
+ include Interface::Powerable
+ include Interface::Muteable
+
+ descriptive_name "Sony Projector (RS232 Control)"
+ generic_name :Display
+
+ INDICATOR = 0xA9_u8
+ DELIMITER = 0x9A_u8
+
+ def on_load
+ transport.tokenizer = Tokenizer.new(Bytes[DELIMITER])
+ end
+
+ def connected
+ schedule.every(60.seconds) { do_poll }
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ def power(state : Bool)
+ if state
+ # Need to send twice in case of deep sleep
+ logger.debug { "requested to power on" }
+ do_send(Type::Set, Command::PowerOn, name: :power)
+ do_send(Type::Set, Command::PowerOn, name: :power, delay: 3.seconds)
+ else
+ logger.debug { "requested to power off" }
+ do_send(Type::Set, Command::PowerOff, name: :power, delay: 3.seconds)
+ end
+
+ # Request status update
+ power?(priority: 50)
+ end
+
+ def power?(priority : Int32 = 0, **options)
+ do_send(Type::Get, Command::PowerStatus, **options, priority: priority).get
+ !!self[:power].try(&.as_bool)
+ end
+
+ enum Input
+ HDMI = 0x0003 # same as InputB
+ InputA = 0x0002
+ InputB = 0x0003
+ InputC = 0x0004
+ InputD = 0x0005
+ USB = 0x0006 # USB type B
+ Network = 0x0007 # network
+
+ def to_bytes : Bytes
+ Bytes[self.value >> 8, self.value & 0xFF]
+ end
+
+ def self.from_bytes(b : Bytes)
+ Input.from_value((b[0].to_u16 << 8) + b[1])
+ end
+ end
+
+ include PlaceOS::Driver::Interface::InputSelection(Input)
+
+ def switch_to(input : Input)
+ do_send(Type::Set, Command::Input, input.to_bytes) # , delay_on_receive: 500.milliseconds)
+ logger.debug { "requested to switch to: #{input}" }
+
+ input?
+ end
+
+ def input?
+ do_send(Type::Get, Command::Input, priority: 0)
+ end
+
+ def lamp_time?
+ do_send(Type::Get, Command::LampTimer, priority: 0)
+ end
+
+ def mute(
+ state : Bool = true,
+ index : Int32 | String = 0,
+ layer : MuteLayer = MuteLayer::AudioVideo
+ )
+ do_send(Type::Set, Command::Mute, Bytes[0, state ? 1 : 0]) # , delay_on_receive: 500)
+ mute?
+ end
+
+ def mute?
+ do_send(Type::Get, Command::Mute, priority: 0)
+ end
+
+ METHODS = ["Contrast", "Brightness", "Color", "Hue", "Sharpness"]
+
+ {% for name in METHODS %}
+ @[Security(Level::Administrator)]
+ def {{name.id.downcase}}?
+ do_send(Type::Get, Command::{{name.id}}, priority: 0)
+ end
+ {% end %}
+
+ {% for name in METHODS %}
+ @[Security(Level::Administrator)]
+ def {{name.id.downcase}}(value : UInt8)
+ do_send(Type::Set, Command::{{name.id}}, Bytes[0, value.clamp(0, 100)], priority: 0)
+ end
+ {% end %}
+
+ ERRORS = {
+ 0x00 => "No Error",
+ 0x01 => "Lamp Error",
+ 0x02 => "Fan Error",
+ 0x04 => "Cover Error",
+ 0x08 => "Temperature Error",
+ 0x10 => "D5V Error",
+ 0x20 => "Power Error",
+ 0x40 => "Warning Error",
+ 0x80 => "NVM Data ERROR",
+ }
+
+ private def do_poll
+ if power?(priority: 0)
+ input?
+ mute?
+ do_send(Type::Get, Command::ErrorStatus, priority: 0)
+ lamp_time?
+ end
+ end
+
+ enum Command
+ PowerOn = 0x172E
+ PowerOff = 0x172F
+ Input = 0x0001
+ Mute = 0x0030
+ ErrorStatus = 0x0101
+ PowerStatus = 0x0102
+ Contrast = 0x0010
+ Brightness = 0x0011
+ Color = 0x0012
+ Hue = 0x0013
+ Sharpness = 0x0014
+ LampTimer = 0x0113
+
+ def to_bytes : Bytes
+ Bytes[self.value >> 8, self.value & 0xFF]
+ end
+
+ def self.from_bytes(b : Bytes)
+ Command.from_value((b[0].to_u16 << 8) + b[1])
+ end
+ end
+
+ enum Type : UInt8
+ Set
+ Get
+ end
+
+ private def do_send(type : Type, command : Command, param : Bytes = Bytes.new(2), **options)
+ # indicator: 1, command: 2, type: 1, param: 2, checksum: 1, delimiter: 1
+ data = Bytes.new(8).tap do |bytes|
+ bytes[0] = INDICATOR
+ command.to_bytes.each_with_index(1) { |b, i| bytes[i] = b } # bytes[1..2]
+ bytes[3] = type.value
+ param.each_with_index(4) { |b, i| bytes[i] = b } # bytes[4..5]
+ bytes[7] = DELIMITER
+ end
+ data[6] = data[1..5].reduce { |a, b| a |= b } # checksum
+
+ send(data, **options)
+ end
+
+ def received(data, task)
+ logger.debug { "sony proj sent: 0x#{data.hexstring}" }
+
+ cmd = data[1..2]
+ type = data[3]
+ resp = data[4..5]
+
+ checksum = data[1..5].reduce { |a, b| a |= b }
+ return task.try &.abort("Checksum should be 0x#{checksum.to_s(base: 16, upcase: true)}") unless data[6] == checksum
+
+ # Check if an ACK/NAK
+ if type == 0x03
+ if cmd == Bytes[0, 0]
+ return task.try &.success
+ else # Command failed
+ return task.try &.abort("Command failed with 0x#{cmd.join(&.to_s(base: 16, upcase: true))}")
+ end
+ else
+ case command = Command.from_bytes(cmd)
+ when .power_on?
+ self[:power] = true
+ when .power_off?
+ self[:power] = false
+ when .lamp_timer?
+ # Two bytes converted to a 16bit integer
+ self[:lamp_usage] = (resp[-2].to_u16 << 8) + resp[-1]
+ when .power_status?
+ case resp[-1]
+ when 0, 8
+ self[:warming] = self[:cooling] = self[:power] = false
+ when 1, 2
+ self[:cooling] = false
+ self[:warming] = self[:power] = true
+ when 3
+ self[:power] = true
+ self[:warming] = self[:cooling] = false
+ when 4, 5, 6, 7
+ self[:cooling] = true
+ self[:warming] = self[:power] = false
+ end
+ schedule.in(5.seconds) { power? } if self[:warming] || self[:cooling]
+ when .mute?
+ self[:mute] = resp[-1] == 1
+ when .input?
+ self[:input] = Input.from_bytes(resp)
+ when .contrast?, .brightness?, color?, .hue?, .sharpness?
+ self[command.to_s.downcase] = resp[-1]
+ end
+ end
+
+ task.try &.success
+ end
+end
diff --git a/drivers/sony/projector/serial_control_spec.cr b/drivers/sony/projector/serial_control_spec.cr
new file mode 100644
index 00000000000..20ba8289b32
--- /dev/null
+++ b/drivers/sony/projector/serial_control_spec.cr
@@ -0,0 +1,48 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Sony::Projector::SerialControl" do
+ exec(:power, true)
+ should_send("\xA9\x17\x2E\x00\x00\x00\x3F\x9A")
+ responds("\xA9\x00\x00\x03\x00\x00\x03\x9A")
+ should_send("\xA9\x17\x2E\x00\x00\x00\x3F\x9A")
+ responds("\xA9\x00\x00\x03\x00\x00\x03\x9A")
+ sleep 3
+ # power?
+ should_send("\xA9\x01\x02\x01\x00\x00\x03\x9A")
+ responds("\xA9\x01\x02\x02\x00\x03\x03\x9A")
+ status[:cooling].should eq(false)
+ status[:warming].should eq(false)
+ status[:power].should eq(true)
+
+ exec(:switch_to, "hdmi")
+ should_send("\xA9\x00\x01\x00\x00\x03\x03\x9A")
+ responds("\xA9\x00\x00\x03\x00\x00\x03\x9A")
+ # input?
+ should_send("\xA9\x00\x01\x01\x00\x00\x01\x9A")
+ responds("\xA9\x00\x01\x02\x00\x03\x03\x9A")
+ status[:input].should eq("HDMI")
+
+ exec(:mute)
+ should_send("\xA9\x00\x30\x00\x00\x01\x31\x9A")
+ responds("\xA9\x00\x00\x03\x00\x00\x03\x9A")
+ # mute?
+ should_send("\xA9\x00\x30\x01\x00\x00\x31\x9A")
+ responds("\xA9\x00\x30\x02\x00\x01\x33\x9A")
+ status[:mute].should eq(true)
+
+ exec(:lamp_time?)
+ should_send("\xA9\x01\x13\x01\x00\x00\x13\x9A")
+ responds("\xA9\x01\x13\x02\x03\xE8\xFB\x9A")
+ status[:lamp_usage].should eq(1000)
+
+ exec(:power, false)
+ should_send("\xA9\x17\x2F\x00\x00\x00\x3F\x9A")
+ responds("\xA9\x00\x00\x03\x00\x00\x03\x9A")
+ sleep 3
+ # power?
+ should_send("\xA9\x01\x02\x01\x00\x00\x03\x9A")
+ responds("\xA9\x01\x02\x02\x00\x04\x07\x9A")
+ status[:cooling].should eq(true)
+ status[:warming].should eq(false)
+ status[:power].should eq(false)
+end
diff --git a/drivers/steinel/hpd2.cr b/drivers/steinel/hpd2.cr
new file mode 100644
index 00000000000..e3ccc46b0f7
--- /dev/null
+++ b/drivers/steinel/hpd2.cr
@@ -0,0 +1,239 @@
+require "placeos-driver"
+require "placeos-driver/interface/sensor"
+
+class Steinel::HPD2 < PlaceOS::Driver
+ include Interface::Sensor
+
+ # Discovery Information
+ generic_name :PeopleCounter
+ descriptive_name "Steinel HPD-2"
+
+ # Local network
+ uri_base "https://192.168.0.20"
+
+ default_settings({
+ basic_auth: {
+ username: "admin",
+ password: "steinel",
+ },
+ })
+
+ @mac : String = ""
+ getter! state : NamedTuple(
+ illuminance: Interface::Sensor::Detail,
+ temperature: Interface::Sensor::Detail,
+ humidity: Interface::Sensor::Detail,
+ presence: Interface::Sensor::Detail,
+ people: Interface::Sensor::Detail,
+ illuminance_zones: Array(Interface::Sensor::Detail),
+ presence_zones: Array(Interface::Sensor::Detail),
+ people_zones: Array(Interface::Sensor::Detail),
+ )
+
+ def on_update
+ @mac = URI.parse(config.uri.not_nil!).hostname.not_nil!
+ schedule.every(5.seconds) { get_status }
+ end
+
+ {% begin %}
+ def sensor(mac : String, id : String? = nil) : Interface::Sensor::Detail?
+ logger.debug { "sensor mac: #{mac}, id: #{id} requested" }
+ return nil unless @mac == mac
+ return nil unless id
+
+ # https://crystal-lang.org/api/1.1.0/String.html#rpartition(search:Char%7CString):Tuple(String,String,String)-instance-method
+ sensor, _, index_str = id.rpartition('-')
+ if sensor.empty?
+ case id
+ {% for sensor in %w(humidity temperature presence people illuminance) %}
+ when {{sensor}}
+ state[{{sensor.id.symbolize}}]
+ {% end %}
+ end
+ elsif index = index_str.to_i?
+ case id
+ {% for sensor in %w(presence people illuminance) %}
+ when {{sensor}}
+ state[{{sensor.id.symbolize}}_zones][index]?
+ {% end %}
+ end
+ end
+ rescue error
+ logger.warn(exception: error) { "checking for sensor" }
+ nil
+ end
+ {% end %}
+
+ alias SensorType = Interface::Sensor::SensorType
+
+ TYPES = {
+ illuminance: SensorType::Illuminance,
+ temperature: SensorType::Temperature,
+ humidity: SensorType::Humidity,
+ presence: SensorType::Presence,
+ people: SensorType::PeopleCount,
+
+ illuminance_zones: SensorType::Illuminance,
+ presence_zones: SensorType::Presence,
+ people_zones: SensorType::PeopleCount,
+ }
+
+ NO_MATCH = [] of Interface::Sensor::Detail
+
+ def sensors(type : String? = nil, mac : String? = nil, zone_id : String? = nil) : Array(Interface::Sensor::Detail)
+ logger.debug { "sensors of type: #{type}, mac: #{mac}, zone_id: #{zone_id} requested" }
+ return NO_MATCH if mac && mac != @mac
+ return state.values.to_a.flatten unless type
+
+ sensor_type = SensorType.parse(type)
+ matches = [] of Interface::Sensor::Detail | Array(Interface::Sensor::Detail)
+ TYPES.each { |key, key_type| matches << state[key] if key_type == sensor_type }
+
+ matches.flatten
+ rescue error
+ logger.warn(exception: error) { "searching for sensors" }
+ NO_MATCH
+ end
+
+ def get_status
+ response = get("/api/sensorstatus.php")
+
+ logger.debug { "received #{response.body}" }
+
+ if response.success?
+ status = SensorStatus.from_json(response.body.not_nil!)
+
+ time = Time.utc.to_unix
+ mod_id = module_id
+ humidity = Interface::Sensor::Detail.new(SensorType::Humidity, status.humidity.to_f, time, @mac, "humidity", "Humidity", module_id: mod_id, binding: "humidity")
+ self[:humidity] = status.humidity.to_f
+ temperature = Interface::Sensor::Detail.new(SensorType::Temperature, status.temperature.to_f, time, @mac, "temperature", "Temperature", module_id: mod_id, binding: "temperature", unit: "Cel")
+ self[:temperature] = status.temperature.to_f
+ pres = status.person_presence.zero? ? 0.0 : 1.0
+ presence = Interface::Sensor::Detail.new(SensorType::Presence, pres, time, @mac, "presence", "Person Presence", module_id: mod_id, binding: "presence")
+ self[:presence] = pres
+ people = Interface::Sensor::Detail.new(SensorType::PeopleCount, status.detected_persons.to_f, time, @mac, "people", "Detected Persons", module_id: mod_id, binding: "people")
+ self[:people] = status.detected_persons
+ illuminance = Interface::Sensor::Detail.new(SensorType::Illuminance, status.global_illuminance_lux, time, @mac, "illuminance", "Illuminance", module_id: mod_id, binding: "illuminance", unit: "lx")
+ self[:illuminance] = status.global_illuminance_lux
+
+ self[:presence_zones] = status.person_presence_zone.map { |value| value.zero? ? 0.0 : 1.0 }
+ presence_zones = status.person_presence_zone.map_with_index do |value, index|
+ Interface::Sensor::Detail.new(SensorType::Presence, value.zero? ? 0.0 : 1.0, time, @mac, "presence-#{index}", "Person Presence in Zone#{index}")
+ end
+ self[:people_zones] = status.detected_persons_zone
+ people_zones = status.detected_persons_zone.map_with_index do |value, index|
+ Interface::Sensor::Detail.new(SensorType::PeopleCount, value.to_f, time, @mac, "people-#{index}", "Detected People in Zone#{index}")
+ end
+ self[:illuminance_zones] = status.lux_zone
+ illuminance_zones = status.lux_zone.map_with_index do |value, index|
+ Interface::Sensor::Detail.new(SensorType::Illuminance, value, time, @mac, "illuminance-#{index}", "Illuminance in Zone#{index}", unit: "lx")
+ end
+
+ @state = {
+ humidity: humidity,
+ temperature: temperature,
+ presence: presence,
+ people: people,
+ illuminance: illuminance,
+
+ presence_zones: presence_zones,
+ people_zones: people_zones,
+ illuminance_zones: illuminance_zones,
+ }
+
+ status
+ else
+ raise "unexpected response #{response.status_code}\n#{response.body}"
+ end
+ end
+
+ class SensorStatus
+ include JSON::Serializable
+
+ @[JSON::Field(key: "AppVersion")]
+ property app_version : String
+
+ @[JSON::Field(key: "FpgaVersion")]
+ property fpga_version : String
+
+ @[JSON::Field(key: "KnxSapNumber")]
+ property knx_sap_number : String
+
+ @[JSON::Field(key: "KnxVersion")]
+ property knx_version : String
+
+ @[JSON::Field(key: "KnxAddr")]
+ property knx_address : String
+
+ @[JSON::Field(key: "GitRevision")]
+ property git_revision : String
+
+ @[JSON::Field(key: "ModelName")]
+ property model_name : String
+
+ @[JSON::Field(key: "FrameProcessingTimeMs")]
+ property frame_processing_time_ms : Int32
+
+ @[JSON::Field(key: "AverageFps5")]
+ property average_fps5 : Float64
+
+ @[JSON::Field(key: "AverageFps50")]
+ property average_fps50 : Float64
+
+ @[JSON::Field(key: "RunningTimeHHMMSS")]
+ property running_time : String
+
+ @[JSON::Field(key: "UptimeHHMMSS")]
+ property uptime : String
+
+ @[JSON::Field(key: "IrLedOn")]
+ property ir_led_on : Int32
+
+ @[JSON::Field(key: "DetectedPersons")]
+ property detected_persons : Int32
+
+ @[JSON::Field(key: "PersonPresence")]
+ property person_presence : Int32
+
+ @[JSON::Field(key: "DetectedPersonsZone")]
+ property detected_persons_zone : Array(Int32)
+
+ @[JSON::Field(key: "PersonPresenceZone")]
+ property person_presence_zone : Array(Int32)
+
+ @[JSON::Field(key: "DetectionZonesPresent")]
+ property detection_zones_present : Int32
+
+ @[JSON::Field(key: "GlobalIlluminanceLux")]
+ property global_illuminance_lux : Float64
+
+ @[JSON::Field(key: "LuxZone")]
+ property lux_zone : Array(Float64)
+
+ @[JSON::Field(key: "GlobalLightValue")]
+ property global_light_value : Int32
+
+ @[JSON::Field(key: "ArmsensorCpuUsage")]
+ property arm_sensor_cpu_usage : String
+
+ @[JSON::Field(key: "WebServerCpuUsage")]
+ property web_server_cpu_usage : String
+
+ @[JSON::Field(key: "Temperature")]
+ property temperature : String
+
+ @[JSON::Field(key: "Humidity")]
+ property humidity : String
+
+ @[JSON::Field(key: "KnxDetected")]
+ property knx_detected : String
+
+ @[JSON::Field(key: "KnxProgramMode")]
+ property knx_program_mode : String
+
+ @[JSON::Field(key: "KnxLedState")]
+ property knx_led_state : String
+ property final : String
+ end
+end
diff --git a/drivers/steinel/hpd2_spec.cr b/drivers/steinel/hpd2_spec.cr
new file mode 100644
index 00000000000..b4975736552
--- /dev/null
+++ b/drivers/steinel/hpd2_spec.cr
@@ -0,0 +1,29 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Xovis::SensorAPI" do
+ # Send the request
+ retval = exec(:get_status)
+ data = %({"AppVersion": "3.2.3", "FpgaVersion": "v300", "KnxSapNumber": "0", "KnxVersion": "0", "KnxAddr":
+ "", "GitRevision": "d45734c2", "ModelName": "15_2xroute_fix26", "FrameProcessingTimeMs": 1179,
+ "AverageFps5": 0.850314, "AverageFps50": 0.855873, "RunningTimeHHMMSS": "672:55:58",
+ "UptimeHHMMSS": "672:56:35", "IrLedOn": 0, "DetectedPersons": 0, "PersonPresence": 0,
+ "DetectedPersonsZone": [0, 0, 0, 0, 0], "PersonPresenceZone": [0, 0, 0, 0, 0],
+ "DetectionZonesPresent": 0, "GlobalIlluminanceLux": 39.0, "LuxZone": [0.0, 0.0, 0.0, 0.0, 0.0],
+ "GlobalLightValue": 72, "ArmsensorCpuUsage": "20", "WebServerCpuUsage": "2", "Temperature":
+ "27.745661", "Humidity": "25.286158", "KnxDetected": "0", "KnxProgramMode": "0", "KnxLedState":
+ "0", "final": "OK" })
+
+ # We should request a new token from Floorsense
+ expect_http_request do |request, response|
+ if request.headers["Authorization"]? == "Basic YWRtaW46c3RlaW5lbA=="
+ response.status_code = 200
+ response.output.puts data
+ else
+ puts request.headers.inspect
+ response.status_code = 401
+ end
+ end
+
+ # What the function should return (for use in making further requests)
+ retval.get.should eq(JSON.parse(data))
+end
diff --git a/drivers/stripe/api.cr b/drivers/stripe/api.cr
new file mode 100644
index 00000000000..f67c62a45e6
--- /dev/null
+++ b/drivers/stripe/api.cr
@@ -0,0 +1,105 @@
+require "placeos-driver"
+require "stripetease"
+
+class Stripe::API < PlaceOS::Driver
+ descriptive_name "Stripe API Gateway"
+ generic_name :Payment
+ uri_base "https://api.stripe.com"
+
+ alias Client = Stripetease::Client
+
+ default_settings({api_key: "ABCDEFGHIJKLMNOPQRSTUVWXYZ"})
+
+ protected getter! client : Client
+
+ def on_update
+ host_name = config.uri.not_nil!.to_s
+ api_key = setting(String, :api_key)
+
+ @client = Stripetease::Client.new(base_url: host_name, api_key: api_key)
+ end
+
+ def add_payment_method(
+ type : String,
+ billing_details : Hash(String, String)? = nil,
+ metadata : Hash(String, String)? = nil,
+ acss_debit : Hash(String, String)? = nil,
+ affirm : Hash(String, String)? = nil,
+ afterpay_clearpay : Hash(String, String)? = nil,
+ alipay : Hash(String, String)? = nil,
+ au_becs_debit : Hash(String, String)? = nil,
+ bacs_debit : Hash(String, String)? = nil,
+ bancontact : Hash(String, String)? = nil,
+ blik : Hash(String, String)? = nil,
+ boleto : Hash(String, String)? = nil,
+ card : Hash(String, String)? = nil,
+ customer_balance : Hash(String, String)? = nil,
+ eps : Hash(String, String)? = nil,
+ fpx : Hash(String, String)? = nil,
+ giropay : Hash(String, String)? = nil,
+ ideal : Hash(String, String)? = nil,
+ interac_present : Hash(String, String)? = nil,
+ klarna : Hash(String, String)? = nil,
+ konbini : Hash(String, String)? = nil,
+ link : Hash(String, String)? = nil,
+ oxxo : Hash(String, String)? = nil,
+ p24 : Hash(String, String)? = nil,
+ paynow : Hash(String, String)? = nil,
+ promptpay : Hash(String, String)? = nil,
+ radar_options : Hash(String, String)? = nil,
+ sepa_debit : Hash(String, String)? = nil,
+ sofort : Hash(String, String)? = nil,
+ us_bank_account : Hash(String, String)? = nil,
+ wechat_pay : Hash(String, String)? = nil
+ )
+ payment_method = @client.not_nil!.payment_methods.create(type, billing_details, metadata, acss_debit, affirm, afterpay_clearpay, alipay, au_becs_debit, bacs_debit, bancontact, blik, boleto, card, customer_balance, eps, fpx, giropay, ideal, interac_present, klarna, konbini, link, oxxo, p24, paynow, promptpay, radar_options, sepa_debit, sofort, us_bank_account, wechat_pay)
+ self["payment_method"] = payment_method
+ end
+
+ def list_payment_methods(type : String, customer : String? = nil, ending_before : String? = nil, limit : Int32? = nil, starting_after : String? = nil)
+ payment_methods = @client.not_nil!.payment_methods.list(type: type, customer: customer, ending_before: ending_before, limit: limit, starting_after: starting_after)
+ self["payment_methods"] = payment_methods
+ end
+
+ def get_product_prices(active : Bool? = nil, currency : String? = nil, product : String? = nil, type : String? = nil, created : Hash(String, String)? = nil, ending_before : String? = nil, limit : Int32? = nil, lookup_keys : Array(String)? = nil, recurring : Hash(String, String)? = nil, starting_after : String? = nil)
+ product_prices = @client.not_nil!.prices.list(active: active, currency: currency, product: product, type: type, created: created, ending_before: ending_before, limit: limit, lookup_keys: lookup_keys, recurring: recurring, starting_after: starting_after)
+ self["product_prices"] = product_prices
+ end
+
+ def create_payment_intent(amount : Int32, currency : String, automatic_payment_methods : Hash(String, String)? = nil, confirm : Bool? = nil, customer : String? = nil, description : String? = nil, metadata : Hash(String, String)? = nil, off_session : Bool? = nil, payment_method : String? = nil, receipt_email : String? = nil, setup_future_usage : String? = nil, shipping : Hash(String, String)? = nil, statement_descriptor : String? = nil, statement_descriptor_suffix : String? = nil, application_fee_amount : Int32? = nil, capture_method : String? = nil, confrimation_method : String? = nil, error_on_requires_action : Bool? = nil, mandate : String? = nil, mandate_data : Hash(String, String)? = nil, on_behalf_of : String? = nil, payment_method_data : Hash(String, String)? = nil, payment_method_types : Array(String)? = nil, payment_method_options : Hash(String, String)? = nil, radar_options : Hash(String, String)? = nil, return_url : String? = nil, transfer_data : Hash(String, String)? = nil, transfer_group : String? = nil, use_stripe_sdk : Bool? = nil)
+ payment_intent = @client.not_nil!.payment_intents.create(amount: amount, currency: currency, automatic_payment_methods: automatic_payment_methods, confirm: confirm, customer: customer, description: description, metadata: metadata, off_session: off_session, payment_method: payment_method, receipt_email: receipt_email, setup_future_usage: setup_future_usage, shipping: shipping, statement_descriptor: statement_descriptor, statement_descriptor_suffix: statement_descriptor_suffix, application_fee_amount: application_fee_amount, capture_method: capture_method, confrimation_method: confrimation_method, error_on_requires_action: error_on_requires_action, mandate_data: mandate_data, on_behalf_of: on_behalf_of, payment_method_data: payment_method_data, payment_method_types: payment_method_types, payment_method_options: payment_method_options, radar_options: radar_options, return_url: return_url, transfer_data: transfer_data, transfer_group: transfer_group, use_stripe_sdk: use_stripe_sdk)
+ self["payment_intent"] = payment_intent
+ end
+
+ def confirm_payment_intent(id : String, payment_method : String? = nil, receipt_email : String? = nil, setup_future_usage : String? = nil, shipping : Hash(String, String)? = nil, capture_method : String? = nil, error_on_requires_action : Bool? = nil, mandate : String? = nil, mandate_data : Hash(String, String)? = nil, off_session : Bool? = nil, payment_method_data : Hash(String, String)? = nil, payment_method_options : Hash(String, String)? = nil, payment_method_types : Array(String)? = nil, radar_options : Hash(String, String)? = nil, return_url : String? = nil, use_stripe_sdk : Bool? = nil)
+ payment_intent = @client.not_nil!.payment_intents.confirm(id: id, payment_method: payment_method, receipt_email: receipt_email, setup_future_usage: setup_future_usage, shipping: shipping, capture_method: capture_method, error_on_requires_action: error_on_requires_action, mandate: mandate, mandate_data: mandate_data, off_session: off_session, payment_method_data: payment_method_data, payment_method_options: payment_method_options, payment_method_types: payment_method_types, radar_options: radar_options, use_stripe_sdk: use_stripe_sdk)
+ self["payment_intent"] = payment_intent
+ end
+
+ def cancel_payment_intent(id : String, cancellation_reason : String? = nil)
+ @client.not_nil!.payment_intents.cancel(id: id, cancellation_reason: cancellation_reason)
+ self["payment_intent"] = nil
+ end
+
+ def get_customer(id : String)
+ self["customer"] = @client.not_nil!.customers.get(id)
+ end
+
+ def list_customers(email : String? = nil, created : Hash(String, String)? = nil, ending_before : String? = nil, limit : Int32? = nil, starting_after : String? = nil)
+ self["customers"] = @client.not_nil!.customers.list(email: email, created: created, ending_before: ending_before, limit: limit, starting_after: starting_after)
+ end
+
+ def search_customers(query : String, limit : Int32? = nil, page : Int32? = nil)
+ self["customers"] = @client.not_nil!.customers.search(query: query, limit: limit, page: page)
+ end
+
+ def create_customer(account_balance : Int32? = nil, coupon : String? = nil, default_source : String? = nil, description : String? = nil, email : String? = nil, invoice_prefix : String? = nil, metadata : Hash(String, String)? = nil, shipping : Hash(String, String)? = nil, source : String? = nil, tax_info : Hash(String, String)? = nil)
+ customer = @client.not_nil!.customers.create(account_balance: account_balance, coupon: coupon, default_source: default_source, description: description, email: email, invoice_prefix: invoice_prefix, metadata: metadata, shipping: shipping, source: source, tax_info: tax_info)
+ self["customer"] = customer
+ end
+
+ def update_customer(id : String, customer : String? = nil, account_balance : Int32? = nil, coupon : String? = nil, default_source : String? = nil, description : String? = nil, email : String? = nil, invoice_prefix : String? = nil, metadata : Hash(String, String)? = nil, shipping : Hash(String, String)? = nil, source : String? = nil, tax_info : Hash(String, String)? = nil)
+ customer = @client.not_nil!.customers.update(id: id, customer: customer, account_balance: account_balance, coupon: coupon, default_source: default_source, description: description, email: email, invoice_prefix: invoice_prefix, metadata: metadata, shipping: shipping, source: source, tax_info: tax_info)
+ self["customer"] = customer
+ end
+end
diff --git a/drivers/tv_one/corio_master.cr b/drivers/tv_one/corio_master.cr
new file mode 100644
index 00000000000..fee922aed88
--- /dev/null
+++ b/drivers/tv_one/corio_master.cr
@@ -0,0 +1,298 @@
+require "placeos-driver"
+
+# Documentation: https://aca.im/driver_docs/TV%20One/CORIOmaster-Commands-v1.7.0.pdf
+
+class PlaceOS::Driver::Task
+ # allows us to access request data in the response
+
+ property request_payload : String? = nil
+end
+
+class TvOne::CorioMaster < PlaceOS::Driver
+ # Discovery Information
+ descriptive_name "tvOne CORIOmaster image processor"
+ generic_name :VideoWall
+ tcp_port 10001
+
+ default_settings({
+ username: "admin",
+ password: "adminpw",
+ })
+
+ @username : String = "admin"
+ @password : String = "adminpw"
+ @ready : Bool = false
+ @window_cache : Hash(UInt32, JSON::Any) = {} of UInt32 => JSON::Any
+
+ def on_update
+ @username = setting(String, :username)
+ @password = setting(String, :password)
+ end
+
+ def disconnected
+ schedule.clear
+ self[:ready] = @ready = false
+ end
+
+ def connected
+ # fallback if we don't get the ready signal
+ schedule.in(30.seconds) { disconnect unless @ready }
+
+ # maintain the connection
+ schedule.every(1.minute) { do_poll }
+
+ spawn { init_connection }
+ end
+
+ protected def init_connection
+ task = exec("login", @username, @password, priority: 99, name: "login").get
+ sync_state
+ end
+
+ def sync_state
+ query("Preset.Take", expose_as: :preset)
+ query_preset_list(expose_as: :presets)
+ deep_query("Windows", expose_as: :windows)
+ deep_query("Canvases", expose_as: :canvases)
+ deep_query("Layouts", expose_as: :layouts)
+ query "CORIOmax.Serial_Number", expose_as: :serial_number
+ query "CORIOmax.Software_Version", expose_as: :firmware
+ end
+
+ def do_poll
+ logger.debug { "polling device" }
+ query "Preset.Take", expose_as: :preset
+ end
+
+ def preset(id : UInt32)
+ set("Preset.Take", id).get
+ self[:preset] = id
+ if wins = @window_cache[id]?
+ logger.debug { "loading cached window state" }
+ self[:windows] = wins
+ end
+
+ # The full query of window params can take up to ~15 seconds. To
+ # speed things up a little for other modules that depend on this
+ # state, cache window info against preset ID's. These are then used
+ # to provide instant status updates.
+ #
+ # As the device only supports a single connection the only time the
+ # cache will contain stale data is following editing of presets, in
+ # which case window state will update silently in the background.
+ spawn do
+ windows = query_windows
+ logger.debug { "window cache for preset #{id} updated" }
+ self[:windows] = @window_cache[id] = windows
+ end
+ id
+ end
+
+ def switch(map : Hash(String, Array(UInt32)))
+ results = map.flat_map do |slot, windows|
+ windows.map { |id| window(id, "Input", slot) }
+ end
+
+ spawn do
+ # wait for operations to complete
+ results.each(&.get)
+
+ # patch state
+ if state = status?(Hash(String, Hash(String, JSON::Any)), :windows)
+ map.each do |slot, windows|
+ value = JSON::Any.new(slot)
+ windows.each do |id|
+ if win = state["window#{id}"]?
+ win["input"] = value
+ end
+ end
+ end
+
+ self["windows"] = state
+ end
+ end
+ nil
+ end
+
+ def window(id : UInt32, property : String, value : Int64 | Bool | Nil | String)
+ set("Window#{id}.#{property}", value)
+ end
+
+ def query_windows
+ deep_query("Windows")
+ end
+
+ def preset_list
+ query_preset_list
+ end
+
+ alias PresetList = Hash(Int32, NamedTuple(name: String, canvas: String, time: Int64))
+
+ # Get the presets available for recall - for some inexplicible reason this
+ # has a wildly different API to the rest of the system
+ protected def query_preset_list(expose_as = nil)
+ task = exec("Routing.Preset.PresetList").get(response_required: true)
+ raise "exec failed" unless task.state.success?
+
+ if preset_list = JSON.parse(task.payload).as_h?
+ presets = preset_list.each_with_object(PresetList.new) do |(key, val), h|
+ id = key[/\d+/].to_i
+ name, canvas, time = val.as_s.split ","
+ h[id] = {
+ name: name,
+ canvas: canvas,
+ time: time.to_i64,
+ }
+ end
+
+ self[expose_as] = presets unless expose_as.nil?
+ presets
+ end
+ end
+
+ protected def query(path, expose_as = nil, **opts)
+ logger.debug { "querying: #{path}" }
+
+ task = send("#{path}\r\n", **opts).get(response_required: true)
+ raise "query failed" unless task.state.success?
+
+ logger.debug { "query response: #{task.payload}" }
+
+ result = JSON.parse(task.payload)
+ self[expose_as] = result if expose_as
+ result
+ end
+
+ protected def deep_query(path, expose_as = nil, **opts)
+ logger.debug { "deep querying: #{path}" }
+
+ result = query(path, **opts)
+ logger.debug { "deep response: #{result.inspect}" }
+
+ if val = result.as_h?
+ val.each do |k, v|
+ val[k] = deep_query(k) if v == "<...>"
+ end
+ val
+
+ self[expose_as] = val if expose_as
+ JSON::Any.new(val)
+ else
+ self[expose_as] = result if expose_as
+ result
+ end
+ end
+
+ protected def set(path, val, **opts)
+ logger.debug { "setting #{path} to #{val}" }
+ send("#{path} = #{val}\r\n", **opts, name: path)
+ end
+
+ protected def exec(command, *params, **opts)
+ param_string = params.join ','
+ logger.debug { "executing: #{command}(#{param_string})" }
+ send "#{command}(#{param_string})\r\n", **opts
+ end
+
+ def received(data, task)
+ data = String.new(data)
+ logger.debug { "Received => #{data}" }
+
+ # wait for an indicator string that hints at the start of the protocol
+ if !@ready
+ if data =~ /Interface Ready/i
+ configure_tokenizer
+ self[:ready] = @ready = true
+ end
+ return
+ end
+
+ # split the result into lines
+ body = data.lines
+ captures = /!(\w+)\W*(.*)$/.match(body.pop).try &.captures
+ return task.try(&.abort("")) unless captures
+
+ type = captures[0].as(String)
+ message = captures[1].as(String).downcase
+
+ # extract the path in the original request
+ # can be "the.path" or "the.path = val" formats
+ request = task.try &.request_payload.try(&.strip.downcase.split(" ")[0])
+
+ # process the result
+ case type
+ when "Done"
+ if request && request == message
+ response = parse_response(body, request)
+ task.try &.success(response)
+ end
+ when "Info"
+ logger.info { "#{request} => #{message}" }
+ task.try &.success
+ when "Error"
+ logger.error { message }
+ task.try &.abort
+ when "Event"
+ logger.info { "unhandled event: #{message}" }
+ else
+ logger.error { "unhandled response: #{data}" }
+ task.try &.abort
+ end
+ end
+
+ protected def configure_tokenizer
+ transport.tokenizer = Tokenizer.new do |io|
+ buffer = String.new(io.peek)
+
+ # start of final line of the payload
+ final_start = buffer.index('!')
+ next 0 unless final_start
+
+ # end of the final line
+ final_line_end = buffer.index("\r\n", final_start)
+
+ if final_line_end
+ final_line_end + 2
+ else
+ 0
+ end
+ end
+ end
+
+ protected def parse_response(lines, command)
+ kv_pairs = lines.map do |line|
+ k, v = line.split("=")
+ {k.strip.downcase, v.strip}
+ end
+
+ updates = kv_pairs.to_h.transform_values do |val|
+ if resp = val.to_i64?
+ resp
+ else
+ case val
+ when "NULL" then nil
+ when /(Off)|(No)/ then false
+ when /(On)|(Yes)/ then true
+ else
+ val
+ end
+ end
+ end
+
+ updates.reject! { |k, _| k.ends_with? "()" }
+
+ return nil if updates.empty?
+
+ if updates.size == 1 && (single_value = updates[command]?)
+ # Single property query
+ single_value
+ elsif updates.values.all?(&.nil?)
+ # Property list
+ updates.keys
+ else
+ # Property set
+ remove = "#{command}."
+ updates.transform_keys { |x| x.sub(remove, "") }
+ end
+ end
+end
diff --git a/drivers/tv_one/corio_master_spec.cr b/drivers/tv_one/corio_master_spec.cr
new file mode 100644
index 00000000000..8d83848a060
--- /dev/null
+++ b/drivers/tv_one/corio_master_spec.cr
@@ -0,0 +1,181 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "TvOne::CorioMaster" do
+ transmit <<-INIT
+ // ===================\r
+ // CORIOmaster - CORIOmax\r
+ // ===================\r
+ // Command Interface Ready\r
+ Please login. Use 'login(username,password)'\r
+ INIT
+
+ should_send "login(admin,adminpw)\r\n"
+ responds "!Info : User admin Logged In\r\n"
+ status[:connected].should be_true
+ status[:ready].should be_true
+
+ should_send "Preset.Take\r\n"
+ responds <<-RX
+ Preset.Take = 1\r
+ !Done Preset.Take\r\n
+ RX
+
+ status[:preset]?.should eq 1
+
+ should_send "Routing.Preset.PresetList()\r\n"
+ responds <<-RX
+ !Done Routing.Preset.PresetList()\r\n
+ RX
+ status[:presets]?.should be_nil
+
+ should_send "Windows\r\n"
+ responds <<-RX
+ !Done Windows\r\n
+ RX
+ should_send "Canvases\r\n"
+ responds <<-RX
+ !Done Canvases\r\n
+ RX
+ should_send "Layouts\r\n"
+ responds <<-RX
+ !Done Layouts\r\n
+ RX
+ should_send "CORIOmax.Serial_Number\r\n"
+ responds <<-RX
+ CORIOmax.Serial_Number = 2218031005149\r
+ !Done CORIOmax.Serial_Number\r\n
+ RX
+ status[:serial_number].should eq 2218031005149_i64
+
+ should_send "CORIOmax.Software_Version\r\n"
+ responds <<-RX
+ CORIOmax.Software_Version = V1.30701.P4 Master\r
+ !Done CORIOmax.Software_Version\r\n
+ RX
+ status[:firmware].should eq "V1.30701.P4 Master"
+
+ result = exec(:query_windows)
+ should_send("Windows\r\n")
+ responds(
+ <<-RX
+ Windows.Window1 = <...>\r
+ Windows.Window2 = <...>\r
+ !Done Windows\r\n
+ RX
+ )
+ should_send("window1\r\n")
+ responds(
+ <<-RX
+ Window1.FullName = Window1\r
+ Window1.Alias = NULL\r
+ Window1.Input = Slot3.In1\r
+ Window1.Canvas = Canvas1\r
+ Window1.CanWidth = 1280\r
+ Window1.CanHeight = 720\r
+ !Done Window1\r\n
+ RX
+ )
+ should_send("window2\r\n")
+ responds(
+ <<-RX
+ Window2.FullName = Window2\r
+ Window2.Alias = NULL\r
+ Window2.Input = Slot3.In2\r
+ Window2.Canvas = Canvas1\r
+ Window2.CanWidth = 1280\r
+ Window2.CanHeight = 720\r
+ !Done Window2\r\n
+ RX
+ )
+
+ result.get.should eq({
+ "window1" => {
+ "fullname" => "Window1",
+ "alias" => nil,
+ "input" => "Slot3.In1",
+ "canvas" => "Canvas1",
+ "canwidth" => 1280,
+ "canheight" => 720,
+ },
+ "window2" => {
+ "fullname" => "Window2",
+ "alias" => nil,
+ "input" => "Slot3.In2",
+ "canvas" => "Canvas1",
+ "canwidth" => 1280,
+ "canheight" => 720,
+ },
+ })
+
+ result = exec(:preset_list)
+ should_send("Routing.Preset.PresetList()\r\n")
+ responds(
+ <<-RX
+ Routing.Preset.PresetList[1]=Sharing-Standard,Canvas1,0\r
+ Routing.Preset.PresetList[2]=Standard-4-Screen,Canvas1,0\r
+ Routing.Preset.PresetList[3]=Standard-10-Screen,Canvas1,0\r
+ Routing.Preset.PresetList[11]=Clear,Canvas1,0\r
+ !Done Routing.Preset.PresetList()\r\n
+ RX
+ )
+ result.get.should eq({
+ "1" => {"name" => "Sharing-Standard", "canvas" => "Canvas1", "time" => 0},
+ "2" => {"name" => "Standard-4-Screen", "canvas" => "Canvas1", "time" => 0},
+ "3" => {"name" => "Standard-10-Screen", "canvas" => "Canvas1", "time" => 0},
+ "11" => {"name" => "Clear", "canvas" => "Canvas1", "time" => 0},
+ })
+
+ result = exec(:preset, 1)
+ should_send("Preset.Take = 1\r\n")
+ responds(
+ <<-RX
+ Preset.Take = 1\r
+ !Done Preset.Take\r\n
+ RX
+ )
+
+ result.get.should eq 1
+ status[:preset]?.should eq 1
+
+ should_send("Windows\r\n")
+ responds(
+ <<-RX
+ Windows.Window1 = <...>\r
+ !Done Windows\r\n
+ RX
+ )
+ should_send("window1\r\n")
+ responds(
+ <<-RX
+ Window1.FullName = Window1\r
+ Window1.Alias = NULL\r
+ Window1.Input = Slot3.In1\r
+ Window1.Canvas = Canvas1\r
+ Window1.CanWidth = 1280\r
+ Window1.CanHeight = 720\r
+ !Done Window1\r\n
+ RX
+ )
+
+ status[:windows]?.should eq({
+ "window1" => {
+ "fullname" => "Window1",
+ "alias" => nil,
+ "input" => "Slot3.In1",
+ "canvas" => "Canvas1",
+ "canwidth" => 1280,
+ "canheight" => 720,
+ },
+ })
+
+ exec(:switch, {"Slot1.In1" => [1]})
+ should_send("Window1.Input = Slot1.In1\r\n")
+ responds(
+ <<-RX
+ Window1.Input = Slot1.In1\r
+ !Done Window1.Input\r\n
+ RX
+ )
+
+ status[:windows]["window1"]["input"].should eq("Slot1.In1")
+end
diff --git a/drivers/tv_one/window_stacker.cr b/drivers/tv_one/window_stacker.cr
new file mode 100644
index 00000000000..41243003395
--- /dev/null
+++ b/drivers/tv_one/window_stacker.cr
@@ -0,0 +1,88 @@
+require "placeos-driver"
+
+class TvOne::WindowStacker < PlaceOS::Driver
+ descriptive_name "Videowall Window Stacker Logic"
+ generic_name :WindowStacker
+
+ description <<-DESC
+ The CORIOmaster videowall processors does not provide the ability to hide
+ windows on signal loss. This logic module may be used to bind windows used
+ in a layout to displays defined within a system. When a display has no source
+ routed it's Z-index will be dropped to 0, revealing background content.
+
+ Use settings to define mapping between system outputs and window ID's:
+ ```
+ {
+ "windows": {
+ "Display_1": [1, 2, 3],
+ "Display_2": 7,
+ "Display_3": [9, 4]
+ }
+ }
+ ```
+ DESC
+
+ default_settings({
+ show_z_index: 15,
+ hide_z_index: 0,
+ videowall: "VideoWall_1",
+ windows: {
+ "Display_1" => [1, 2, 3],
+ "Display_2" => 7,
+ "Display_3" => [9, 4],
+ },
+ })
+
+ @subscriptions : Array(::PlaceOS::Driver::Subscriptions::IndirectSubscription) = [] of PlaceOS::Driver::Subscriptions::IndirectSubscription
+ @videowall : String = "VideoWall_1"
+ @show : Int32 = 15
+ @hide : Int32 = 0
+
+ def on_update
+ clear_subscriptions
+
+ bindings = setting?(Hash(String, Int32 | Array(Int32)), :windows) || {} of String => Int32 | Array(Int32)
+ @videowall = setting?(String, :videowall) || "VideoWall_1"
+ @show = setting?(Int32, :show_z_index) || 15 # visible z layer
+ @hide = setting?(Int32, :hide_z_index) || 0 # hidden z layer
+
+ # Subscribe to source updates and relayer on change
+ sys = system[:System_1]
+ @subscriptions = bindings.map do |display, window|
+ sys.subscribe("output/#{display}") do |_sub, value|
+ logger.debug { "Restacking #{display} linked windows due to source change" }
+ source = JSON.parse(value)["source"]?.try(&.as_s?)
+ restack window, source
+ end
+ end
+
+ # Also restack after a videowall preset recall
+ @subscriptions << system[@videowall].subscribe("preset") do |_sub, notice|
+ logger.debug { "Restacking all videowall windows due to preset change" }
+ bindings.each do |display, window|
+ begin
+ source = system[:System]["output/#{display}"]["source"]?.try(&.as_s?)
+ restack window, source
+ rescue
+ logger.warn { "could not find active source for #{display}" }
+ end
+ end
+ end
+ end
+
+ protected def clear_subscriptions
+ logger.debug { "clearing subscriptions!" }
+ @subscriptions.each { |sub| subscriptions.unsubscribe(sub) }
+ @subscriptions.clear
+ end
+
+ protected def restack(window : Int32 | Array(Int32), source : String?)
+ window = window.is_a?(Array) ? window : [window]
+ wall_controller = system[@videowall]
+
+ z_index = {nil, "MUTE"}.includes?(source) ? @hide : @show
+ window.each do |id|
+ wall_controller.window id, "Zorder", z_index
+ end
+ end
+end
diff --git a/drivers/tv_one/window_stacker_spec.cr b/drivers/tv_one/window_stacker_spec.cr
new file mode 100644
index 00000000000..d5c594ef58b
--- /dev/null
+++ b/drivers/tv_one/window_stacker_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "TvOne::WindowStacker" do
+end
diff --git a/drivers/twenty_five_live_pro/api.cr b/drivers/twenty_five_live_pro/api.cr
new file mode 100644
index 00000000000..806b2cf22da
--- /dev/null
+++ b/drivers/twenty_five_live_pro/api.cr
@@ -0,0 +1,323 @@
+require "placeos-driver"
+require "./models/*"
+
+module TwentyFiveLivePro
+ class API < PlaceOS::Driver
+ descriptive_name "25 Live Pro API Gateway"
+ generic_name :Bookings
+ uri_base "https://example.com/r25ws/wrd/partners/run"
+
+ default_settings({
+ username: "admin",
+ password: "admin",
+ user_agent: "PlaceOS",
+ })
+
+ def on_load
+ on_update
+ end
+
+ @username : String = "admin"
+ @password : String = "admin"
+
+ @user_agent : String = "PlaceOS"
+
+ def on_update
+ @username = setting(String, :username)
+ @password = setting(String, :password)
+
+ @user_agent = setting?(String, :user_agent) || "PlaceOS"
+ end
+
+ def get_space_details(id : Int32, included_elements : Array(String) = [] of String, expanded_elements : Array(String) = [] of String)
+ params = URI::Params.build do |form|
+ form.add "include", included_elements.join(",")
+ form.add "expand", expanded_elements.join(",")
+ end
+
+ response = get("/external/space/#{id}/detail.json?#{params}", headers: HTTP::Headers{"Authorization" => get_basic_authorization, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+
+ Models::SpaceDetail.from_json(response.body)
+ end
+
+ def list_spaces(page : Int32 = 1, items_per_page : Int32 = 100, paginate : String? = nil)
+ spaces = [] of Models::Space
+
+ loop do
+ params = URI::Params.build do |form|
+ form.add "page", page.to_s
+ form.add "itemsPerPage", items_per_page.to_s
+ form.add "paginate", paginate if paginate
+ end
+
+ response = get("/external/space/list.json?#{params}", headers: HTTP::Headers{"Authorization" => get_basic_authorization, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+
+ paginated_response = Models::PaginatedResponse.from_json(response.body)
+
+ if page < paginated_response.content.data.total_pages
+ begin
+ Array(Models::Space).from_json(paginated_response.content.data.json_unmapped.["items"].to_json).each do |space|
+ spaces.push(space)
+ end
+
+ page += 1
+ rescue exception
+ logger.warn { "failed to parse body:\n#{response.body}" }
+ raise exception
+ end
+ elsif page == paginated_response.content.data.total_pages
+ begin
+ Array(Models::Space).from_json(paginated_response.content.data.json_unmapped.["items"].to_json).each do |space|
+ spaces.push(space)
+ end
+
+ break
+ rescue exception
+ logger.warn { "failed to parse body:\n#{response.body}" }
+ raise exception
+ end
+ else
+ break
+ end
+ end
+
+ spaces
+ end
+
+ def availability(id : Int32, start_date : String, end_date : String, included_elements : Array(String) = [] of String, expanded_elements : Array(String) = [] of String)
+ params = URI::Params.build do |form|
+ form.add "include", included_elements.join(",")
+ form.add "expand", expanded_elements.join(",")
+ end
+
+ body = {
+ "spaces" => [
+ {
+ "spaceId" => id,
+ "dates" => {
+ "startDt" => start_date,
+ "endDt" => end_date,
+ },
+ },
+ ],
+ }
+
+ response = post("/external/spaceAvailability.json?#{params}", headers: HTTP::Headers{"Authorization" => get_basic_authorization, "User-Agent" => @user_agent, "Content-Type" => "application/json"}, body: body.to_json)
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+
+ Models::Availability.from_json(response.body)
+ end
+
+ def get_resource_details(id : Int32, included_elements : Array(String) = [] of String, expanded_elements : Array(String) = [] of String)
+ params = URI::Params.build do |form|
+ form.add "include", included_elements.join(",")
+ form.add "expand", expanded_elements.join(",")
+ end
+
+ response = get("/external/resource/#{id}/detail.json?#{params}", headers: HTTP::Headers{"Authorization" => get_basic_authorization, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+
+ Models::ResourceDetail.from_json(response.body)
+ end
+
+ def list_resources(page : Int32 = 1, items_per_page : Int32 = 100, paginate : String? = nil)
+ resources = [] of Models::Resource
+
+ loop do
+ params = URI::Params.build do |form|
+ form.add "page", page.to_s
+ form.add "itemsPerPage", items_per_page.to_s
+ form.add "paginate", paginate if paginate
+ end
+
+ response = get("/external/resource/list.json?#{params}", headers: HTTP::Headers{"Authorization" => get_basic_authorization, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+
+ paginated_response = Models::PaginatedResponse.from_json(response.body)
+
+ if page < paginated_response.content.data.total_pages
+ begin
+ Array(Models::Resource).from_json(paginated_response.content.data.json_unmapped.["items"].to_json).each do |resource|
+ resources.push(resource)
+ end
+
+ page += 1
+ rescue exception
+ logger.warn { "failed to parse body:\n#{response.body}" }
+ raise exception
+ end
+ elsif page == paginated_response.content.data.total_pages
+ begin
+ Array(Models::Resource).from_json(paginated_response.content.data.json_unmapped.["items"].to_json).each do |resource|
+ resources.push(resource)
+ end
+
+ break
+ rescue exception
+ logger.warn { "failed to parse body:\n#{response.body}" }
+ raise exception
+ end
+ else
+ break
+ end
+ end
+
+ resources
+ end
+
+ def get_organization_details(id : Int32, included_elements : Array(String) = [] of String, expanded_elements : Array(String) = [] of String)
+ params = URI::Params.build do |form|
+ form.add "include", included_elements.join(",")
+ form.add "expand", expanded_elements.join(",")
+ end
+
+ response = get("/external/organization/#{id}/detail.json?#{params}", headers: HTTP::Headers{"Authorization" => get_basic_authorization, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+
+ Models::OrganizationDetail.from_json(response.body)
+ end
+
+ def list_organizations(page : Int32 = 1, items_per_page : Int32 = 100, paginate : String? = nil)
+ organizations = [] of Models::Organization
+
+ loop do
+ params = URI::Params.build do |form|
+ form.add "page", page.to_s
+ form.add "itemsPerPage", items_per_page.to_s
+ form.add "paginate", paginate if paginate
+ end
+
+ response = get("/external/organization/list.json?#{params}", headers: HTTP::Headers{"Authorization" => get_basic_authorization, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+
+ paginated_response = Models::PaginatedResponse.from_json(response.body)
+
+ if page < paginated_response.content.data.total_pages
+ begin
+ Array(Models::Organization).from_json(paginated_response.content.data.json_unmapped.["items"].to_json).each do |organization|
+ organizations.push(organization)
+ end
+
+ page += 1
+ rescue exception
+ logger.warn { "failed to parse body:\n#{response.body}" }
+ raise exception
+ end
+ elsif page == paginated_response.content.data.total_pages
+ begin
+ Array(Models::Organization).from_json(paginated_response.content.data.json_unmapped.["items"].to_json).each do |organization|
+ organizations.push(organization)
+ end
+
+ break
+ rescue exception
+ logger.warn { "failed to parse body:\n#{response.body}" }
+ raise exception
+ end
+ else
+ break
+ end
+ end
+
+ organizations
+ end
+
+ def list_reservations(space_id : Int32, start_date : String, end_date : String)
+ params = URI::Params.build do |form|
+ form.add "space_id", space_id.to_s
+ form.add "start_dt", start_date
+ form.add "end_dt", end_date
+ end
+
+ response = get("/reservations.json?#{params}", headers: HTTP::Headers{"Authorization" => get_basic_authorization, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+
+ Models::Reservations.from_json(response.body)
+ end
+
+ def get_event_details(id : Int32, included_elements : Array(String) = [] of String, expanded_elements : Array(String) = [] of String)
+ params = URI::Params.build do |form|
+ form.add "include", included_elements.join(",")
+ form.add "expand", expanded_elements.join(",")
+ end
+
+ response = get("/external/event/#{id}/detail.json?#{params}", headers: HTTP::Headers{"Authorization" => get_basic_authorization, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+
+ Models::EventDetail.from_json(response.body)
+ end
+
+ def list_events(space_id : Int32 = 1, page : Int32 = 1, items_per_page : Int32 = 100, since : String? = nil, paginate : String? = nil)
+ events = [] of Models::Event
+
+ loop do
+ params = URI::Params.build do |form|
+ form.add "space_id", space_id.to_s
+ form.add "page", page.to_s
+ form.add "itemsPerPage", items_per_page.to_s
+ form.add "created_since", since if since
+ form.add "paginate", paginate if paginate
+ end
+
+ response = get("/external/event/list.json?#{params}", headers: HTTP::Headers{"Authorization" => get_basic_authorization, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+
+ paginated_response = Models::PaginatedResponse.from_json(response.body)
+
+ if page < paginated_response.content.data.total_pages
+ begin
+ Array(Models::Event).from_json(paginated_response.content.data.json_unmapped.["items"].to_json).each do |event|
+ events.push(event)
+ end
+
+ page += 1
+ rescue exception
+ logger.warn { "failed to parse body:\n#{response.body}" }
+ raise exception
+ end
+ elsif page == paginated_response.content.data.total_pages
+ begin
+ Array(Models::Event).from_json(paginated_response.content.data.json_unmapped.["items"].to_json).each do |event|
+ events.push(event)
+ end
+
+ break
+ rescue exception
+ logger.warn { "failed to parse body:\n#{response.body}" }
+ raise exception
+ end
+ else
+ break
+ end
+ end
+
+ events
+ end
+
+ protected def get_basic_authorization
+ "Basic #{Base64.strict_encode("#{@username}:#{@password}")}"
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/api_spec.cr b/drivers/twenty_five_live_pro/api_spec.cr
new file mode 100644
index 00000000000..4778fa334be
--- /dev/null
+++ b/drivers/twenty_five_live_pro/api_spec.cr
@@ -0,0 +1,886 @@
+require "./models/**"
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "TwentyFiveLivePro::API" do
+ # Spaces
+
+ get_space_details = exec(:get_space_details, 1, ["all"], ["all"])
+
+ expect_http_request do |request, response|
+ case "#{request.path}?#{request.query}"
+ when "/space/1/detail.json?include=all&expand=all"
+ response.status_code = 200
+ response << %({
+ "content": {
+ "requestId": 365785,
+ "updated": "2023-04-05T00:37:53-07:00",
+ "data": {
+ "items": [
+ {
+ "kind": "space",
+ "id": 1,
+ "etag": "00000029",
+ "spaceName": "0104-232",
+ "spaceFormalName": "Cox Science Center, 232",
+ "maxCapacity": 24,
+ "updated": "2013-08-01T08:17:01-07:00",
+ "layouts": [],
+ "features": [],
+ "categories": [],
+ "attributes": [
+ {
+ "attributeId": -38,
+ "value": "Wet Lab - Research"
+ },
+ {
+ "attributeId": -37,
+ "value": "OPEN"
+ },
+ {
+ "attributeId": -36,
+ "value": "G"
+ },
+ {
+ "attributeId": -33,
+ "value": "Second Floor"
+ },
+ {
+ "attributeId": -32
+ },
+ {
+ "attributeId": -31,
+ "value": "2008-05-30"
+ },
+ {
+ "attributeId": -30,
+ "value": "T"
+ },
+ {
+ "attributeId": -12,
+ "value": "1350"
+ },
+ {
+ "attributeId": -10,
+ "value": "2"
+ },
+ {
+ "attributeId": -9,
+ "value": "250-04"
+ },
+ {
+ "attributeId": -7
+ },
+ {
+ "attributeId": -6,
+ "value": "Cox Science Center"
+ }
+ ],
+ "roles": []
+ }
+ ]
+ },
+ "expandedInfo": {
+ "attributes": [
+ {
+ "attributeId": -30,
+ "attributeName": "1",
+ "dataType": "B"
+ },
+ {
+ "attributeId": -31,
+ "attributeName": "1",
+ "dataType": "D"
+ },
+ {
+ "attributeId": -32,
+ "attributeName": "1",
+ "dataType": "D"
+ },
+ {
+ "attributeId": -33,
+ "attributeName": "1",
+ "dataType": "S"
+ },
+ {
+ "attributeId": -38,
+ "attributeName": "1",
+ "dataType": "S"
+ },
+ {
+ "attributeId": -36,
+ "attributeName": "1",
+ "dataType": "S"
+ },
+ {
+ "attributeId": -37,
+ "attributeName": "1",
+ "dataType": "S"
+ },
+ {
+ "attributeId": -12,
+ "attributeName": "1",
+ "dataType": "N"
+ },
+ {
+ "attributeId": -6,
+ "attributeName": "1",
+ "dataType": "S"
+ },
+ {
+ "attributeId": -10,
+ "attributeName": "1",
+ "dataType": "S"
+ },
+ {
+ "attributeId": -7,
+ "attributeName": "1",
+ "dataType": "2"
+ },
+ {
+ "attributeId": -9,
+ "attributeName": "1",
+ "dataType": "S"
+ }
+ ],
+ "roles": [],
+ "contacts": []
+ }
+ }
+ })
+ else
+ response.status_code = 500
+ response << "expected get space details request"
+ end
+ end
+
+ space_detail = TwentyFiveLivePro::Models::SpaceDetail.from_json(get_space_details.get.not_nil!.to_json)
+ space_detail.content.data.items.first.id.should eq 1
+
+ list_spaces = exec(:list_spaces, 1, 10, nil)
+
+ expect_http_request do |request, response|
+ case "#{request.path}?#{request.query}"
+ when "/space/list.json?page=1&itemsPerPage=10"
+ response.status_code = 200
+ response << %({
+ "content": {
+ "requestId": 365784,
+ "updated": "2023-04-04T22:19:51-07:00",
+ "data": {
+ "paginateKey": 16414,
+ "pageIndex": 1,
+ "totalPages": 1,
+ "totalItems": 10,
+ "currentItemCount": 10,
+ "itemsPerPage": 10,
+ "pagingLinkTemplate": "https://webservices.collegenet.com/r25ws/wrd/partners/run/external/space/list.json?current_cont_id=754&paginate=16414&page={index}&order=asc",
+ "items": [
+ {
+ "kind": "space",
+ "id": 37932,
+ "etag": "00000029",
+ "spaceName": "0104-232",
+ "spaceFormalName": "Cox Science Center, 232",
+ "maxCapacity": 24,
+ "canRequest": true
+ },
+ {
+ "kind": "space",
+ "id": 37929,
+ "etag": "00000027",
+ "spaceName": "0509-111",
+ "spaceFormalName": "Handleman Building, 111",
+ "maxCapacity": 10,
+ "canRequest": true
+ },
+ {
+ "kind": "space",
+ "id": 37671,
+ "etag": "00000021",
+ "spaceName": "1_R1",
+ "spaceFormalName": "First Floor Conference Room",
+ "maxCapacity": 12,
+ "canRequest": true
+ },
+ {
+ "kind": "space",
+ "id": 13296,
+ "etag": "00000024",
+ "spaceName": "100*133",
+ "spaceFormalName": "Classroom - M",
+ "maxCapacity": 42,
+ "canRequest": true
+ },
+ {
+ "kind": "space",
+ "id": 13301,
+ "etag": "00000024",
+ "spaceName": "100*142",
+ "spaceFormalName": "Classroom - M",
+ "maxCapacity": 49,
+ "canRequest": true
+ },
+ {
+ "kind": "space",
+ "id": 40771,
+ "etag": "00000021",
+ "spaceName": "1028 DANA",
+ "maxCapacity": 30,
+ "canRequest": true
+ },
+ {
+ "kind": "space",
+ "id": 40759,
+ "etag": "00000021",
+ "spaceName": "1040 DANA",
+ "maxCapacity": 30,
+ "canRequest": true
+ },
+ {
+ "kind": "space",
+ "id": 40779,
+ "etag": "00000021",
+ "spaceName": "1045 GGBL",
+ "maxCapacity": 30,
+ "canRequest": true
+ },
+ {
+ "kind": "space",
+ "id": 40793,
+ "etag": "00000021",
+ "spaceName": "1121 LBME",
+ "maxCapacity": 30,
+ "canRequest": true
+ },
+ {
+ "kind": "space",
+ "id": 40747,
+ "etag": "00000021",
+ "spaceName": "130 TAP",
+ "maxCapacity": 30,
+ "canRequest": true
+ }
+ ]
+ }
+ }
+ })
+ else
+ response.status_code = 500
+ response << "expected list spaces request"
+ end
+ end
+
+ spaces = Array(TwentyFiveLivePro::Models::Space).from_json(list_spaces.get.not_nil!.to_json)
+ spaces.size.should eq 10
+
+ get_availability = exec(:availability, 1, "2023-06-04T14:30:00-07:00", "2023-06-04T15:30:00-07:00", ["all"], ["all"])
+
+ expect_http_request do |request, response|
+ case "#{request.path}?#{request.query}"
+ when "/spaceAvailability.json?include=all&expand=all"
+ response.status_code = 200
+ response << %({
+ "content": {
+ "requestId": "365796",
+ "updated": "2023-04-05T01:32:44-07:00",
+ "data": {
+ "spaces": [
+ {
+ "spaceId": 1,
+ "dates": [
+ {
+ "startDt": "2023-06-04T14:30:00-07:00",
+ "endDt": "2023-06-04T15:30:00-07:00"
+ }
+ ],
+ "available": false,
+ "conflictType": 3
+ }
+ ]
+ },
+ "expandedInfo": {
+ "conflictTypes": [
+ {
+ "conflictTypeId": 1,
+ "conflictTypeName": "pendRes",
+ "conflictTypeDescription": "Conflicts with a pending space reservation for this space."
+ },
+ {
+ "conflictTypeId": 2,
+ "conflictTypeName": "res",
+ "conflictTypeDescription": "Conflicts with a space reservation for this space."
+ },
+ {
+ "conflictTypeId": 3,
+ "conflictTypeName": "hour",
+ "conflictTypeDescription": "Conflicts with the Open/Close hour setting for this space."
+ },
+ {
+ "conflictTypeId": 4,
+ "conflictTypeName": "blackout",
+ "conflictTypeDescription": "Conflicts with a blackout for this space."
+ }
+ ]
+ }
+ }
+ })
+ else
+ response.status_code = 500
+ response << "expected list spaces request"
+ end
+ end
+
+ availability = TwentyFiveLivePro::Models::Availability.from_json(get_availability.get.not_nil!.to_json)
+ availability.content.data.spaces.first.space_id.should eq 1
+
+ # Resources
+
+ get_resource_details = exec(:get_resource_details, 1, ["all"], ["all"])
+
+ expect_http_request do |request, response|
+ case "#{request.path}?#{request.query}"
+ when "/resource/1/detail.json?include=all&expand=all"
+ response.status_code = 200
+ response << %({
+ "content": {
+ "requestId": 365793,
+ "updated": "2023-04-05T01:03:14-07:00",
+ "data": {
+ "items": [
+ {
+ "kind": "resource",
+ "id": 1,
+ "etag": "00000021",
+ "resourceName": "1",
+ "updated": "2001-11-19T11:41:39-08:00",
+ "categories": [
+ {
+ "categoryId": 935
+ }
+ ],
+ "attributes": [],
+ "stock": [
+ {
+ "versionNumber": 2,
+ "startDate": "2001-11-19T00:00:00",
+ "endDate": "2100-12-31T00:00:00",
+ "stockLevel": 2
+ }
+ ]
+ }
+ ]
+ },
+ "expandedInfo": [
+ {
+ "categories": [
+ {
+ "categoryId": 935,
+ "categoryName": "1"
+ }
+ ]
+ }
+ ]
+ }
+ })
+ else
+ response.status_code = 500
+ response << "expected get resource details request"
+ end
+ end
+
+ resource_detail = TwentyFiveLivePro::Models::ResourceDetail.from_json(get_resource_details.get.not_nil!.to_json)
+ resource_detail.content.data.items.first.id.should eq 1
+
+ list_resources = exec(:list_resources, 1, 10, nil)
+
+ expect_http_request do |request, response|
+ case "#{request.path}?#{request.query}"
+ when "/resource/list.json?page=1&itemsPerPage=10"
+ response.status_code = 200
+ response << %({
+ "content": {
+ "requestId": 365792,
+ "updated": "2023-04-05T01:01:36-07:00",
+ "data": {
+ "paginateKey": 16419,
+ "pageIndex": 1,
+ "totalPages": 1,
+ "totalItems": 67,
+ "currentItemCount": 10,
+ "itemsPerPage": 10,
+ "pagingLinkTemplate": "https://webservices.collegenet.com/r25ws/wrd/partners/run/external/resource/list.json?current_cont_id=754&paginate=16419&page={index}&order=asc",
+ "items": [
+ {
+ "kind": "resource",
+ "id": 29,
+ "etag": "00000021",
+ "resourceName": "1",
+ "canRequest": true
+ },
+ {
+ "kind": "resource",
+ "id": 87,
+ "etag": "00000021",
+ "resourceName": "1",
+ "canRequest": true
+ },
+ {
+ "kind": "resource",
+ "id": 12,
+ "etag": "00000021",
+ "resourceName": "1",
+ "canRequest": true
+ },
+ {
+ "kind": "resource",
+ "id": 62,
+ "etag": "00000021",
+ "resourceName": "1",
+ "canRequest": true
+ },
+ {
+ "kind": "resource",
+ "id": 69,
+ "etag": "00000021",
+ "resourceName": "1",
+ "canRequest": true
+ },
+ {
+ "kind": "resource",
+ "id": 10,
+ "etag": "00000021",
+ "resourceName": "1",
+ "canRequest": true
+ },
+ {
+ "kind": "resource",
+ "id": 57,
+ "etag": "00000021",
+ "resourceName": "1",
+ "canRequest": true
+ },
+ {
+ "kind": "resource",
+ "id": 54,
+ "etag": "00000021",
+ "resourceName": "1",
+ "canRequest": true
+ },
+ {
+ "kind": "resource",
+ "id": 4,
+ "etag": "00000021",
+ "resourceName": "1",
+ "canRequest": true
+ },
+ {
+ "kind": "resource",
+ "id": 75,
+ "etag": "00000021",
+ "resourceName": "1",
+ "canRequest": true
+ }
+ ]
+ }
+ }
+ })
+ else
+ response.status_code = 500
+ response << "expected list resources request"
+ end
+ end
+
+ resources = Array(TwentyFiveLivePro::Models::Resource).from_json(list_resources.get.not_nil!.to_json)
+ resources.size.should eq 10
+
+ # Organizations
+
+ get_organization_details = exec(:get_organization_details, 1, ["all"], ["all"])
+
+ expect_http_request do |request, response|
+ case "#{request.path}?#{request.query}"
+ when "/organization/1/detail.json?include=all&expand=all"
+ response.status_code = 200
+ response << %({
+ "content": {
+ "requestId": 1,
+ "updated": "2023-04-05T01:00:08-07:00",
+ "data": {
+ "items": [
+ {
+ "kind": "organization",
+ "id": 1,
+ "etag": "0000003A",
+ "organizationName": "1",
+ "organizationTitle": "1",
+ "updated": "2013-08-01T08:16:20.230-07:00",
+ "organizationTypeId": 16,
+ "categories": [
+ {
+ "categoryId": 945
+ }
+ ],
+ "attributes": [
+ {
+ "attributeId": -42,
+ "value": "F"
+ },
+ {
+ "attributeId": -41,
+ "value": "22505-00"
+ }
+ ]
+ }
+ ]
+ },
+ "expandedInfo": [
+ {
+ "categories": [
+ {
+ "categoryId": 945,
+ "categoryName": "1"
+ }
+ ],
+ "attributes": [
+ {
+ "attributeId": -41,
+ "attributeName": "1",
+ "dataType": "S"
+ },
+ {
+ "attributeId": -42,
+ "attributeName": "1",
+ "dataType": "B"
+ }
+ ],
+ "organization_types": [
+ {
+ "organizationTypeId": 16,
+ "orgTypeName": "1",
+ "rateGroupId": 11
+ }
+ ]
+ }
+ ]
+ }
+ })
+ else
+ response.status_code = 500
+ response << "expected get organization details request"
+ end
+ end
+
+ organization_detail = TwentyFiveLivePro::Models::OrganizationDetail.from_json(get_organization_details.get.not_nil!.to_json)
+ organization_detail.content.data.items.first.id.should eq 1
+
+ list_organizations = exec(:list_organizations, 1, 10, nil)
+
+ expect_http_request do |request, response|
+ case "#{request.path}?#{request.query}"
+ when "/organization/list.json?page=1&itemsPerPage=10"
+ response.status_code = 200
+ response << %({
+ "content": {
+ "requestId": 365790,
+ "updated": "2023-04-05T00:57:56-07:00",
+ "data": {
+ "paginateKey": 16418,
+ "pageIndex": 1,
+ "totalPages": 1,
+ "totalItems": 291,
+ "currentItemCount": 10,
+ "itemsPerPage": 10,
+ "pagingLinkTemplate": "https://webservices.collegenet.com/r25ws/wrd/partners/run/external/organization/list.json?current_cont_id=754&paginate=16418&page={index}&order=asc",
+ "items": [
+ {
+ "kind": "organization",
+ "id": 31888,
+ "etag": "0000003A",
+ "organizationName": "1",
+ "organizationTitle": "1",
+ "organizationTypeId": 16
+ },
+ {
+ "kind": "organization",
+ "id": 32247,
+ "etag": "00000021",
+ "organizationName": "1",
+ "organizationTypeId": 27
+ },
+ {
+ "kind": "organization",
+ "id": 269,
+ "etag": "0000002C",
+ "organizationName": "1",
+ "organizationTitle": "1",
+ "organizationTypeId": 23
+ },
+ {
+ "kind": "organization",
+ "id": 211,
+ "etag": "00000026",
+ "organizationName": "1",
+ "organizationTitle": "1",
+ "organizationTypeId": 23
+ },
+ {
+ "kind": "organization",
+ "id": 32103,
+ "etag": "00000033",
+ "organizationName": "1"
+ },
+ {
+ "kind": "organization",
+ "id": 32096,
+ "etag": "00000033",
+ "organizationName": "1"
+ },
+ {
+ "kind": "organization",
+ "id": 31383,
+ "etag": "00000021",
+ "organizationName": "1",
+ "organizationTypeId": 27
+ },
+ {
+ "kind": "organization",
+ "id": 31951,
+ "etag": "00000039",
+ "organizationName": "1",
+ "organizationTitle": "1",
+ "organizationTypeId": 16
+ },
+ {
+ "kind": "organization",
+ "id": 15988,
+ "etag": "00000024",
+ "organizationName": "1",
+ "organizationTitle": "1",
+ "organizationTypeId": 27
+ },
+ {
+ "kind": "organization",
+ "id": 247,
+ "etag": "00000025",
+ "organizationName": "1",
+ "organizationTitle": "1",
+ "organizationTypeId": 16
+ }
+ ]
+ }
+ }
+ })
+ else
+ response.status_code = 500
+ response << "expected list organizations request"
+ end
+ end
+
+ organizations = Array(TwentyFiveLivePro::Models::Organization).from_json(list_organizations.get.not_nil!.to_json)
+ organizations.size.should eq 10
+
+ # Events
+
+ get_event_details = exec(:get_event_details, 1, ["all"], ["all"])
+
+ expect_http_request do |request, response|
+ case "#{request.path}?#{request.query}"
+ when "/event/1/detail.json?include=all&expand=all"
+ response.status_code = 200
+ response << %({
+ "content": {
+ "id": 365795,
+ "updated": "2023-04-05T01:08:28-07:00",
+ "data": {
+ "items": [
+ {
+ "kind": "event",
+ "id": 1,
+ "etag": "00000021",
+ "name": "cccccccc",
+ "title": "RoomView Created Event",
+ "eventLocator": "2023-AASXCJ",
+ "priority": 0,
+ "updated": "2023-04-04T17:17:52-07:00",
+ "dates": {
+ "startDate": "2023-04-04T14:30:00-07:00",
+ "endDate": "2023-04-04T15:00:00-07:00"
+ },
+ "organizations": {},
+ "context": {
+ "state": 1,
+ "typeId": 231,
+ "parentId": 63070
+ },
+ "categories": [],
+ "attributes": [],
+ "requirements": [],
+ "roles": [
+ {
+ "roleId": -2,
+ "contactId": 718
+ }
+ ],
+ "text": [
+ {}
+ ],
+ "profiles": [
+ {
+ "profileId": 169006,
+ "name": "Rsrv_169006",
+ "expectedCount": null,
+ "registeredCount": null,
+ "occurrenceDefn": {
+ "recTypeId": 0,
+ "initStartDt": "2023-04-04T14:30:00-07:00",
+ "initEndDt": "2023-04-04T15:00:00-07:00"
+ },
+ "comments": "~tromeo@crestron.com~admin",
+ "reservations": [
+ {
+ "rsrvId": 1031353,
+ "state": 1,
+ "rsrvStartDt": "2023-04-04T14:30:00-07:00",
+ "evStartDt": "2023-04-04T14:30:00-07:00",
+ "evEndDt": "2023-04-04T15:00:00-07:00",
+ "rsrvEndDt": "2023-04-04T15:00:00-07:00",
+ "spaces": [
+ {
+ "reserved": [
+ {
+ "spaceId": 40722,
+ "share": false,
+ "instructions": "[rv]",
+ "rating": 0
+ }
+ ]
+ }
+ ]
+ }
+ ]
+ }
+ ]
+ }
+ ]
+ },
+ "expandedInfo": {
+ "organizations": [],
+ "roles": [
+ {
+ "roleId": -2,
+ "etag": "00000021",
+ "roleName": "Scheduler"
+ }
+ ],
+ "spaces": [
+ {
+ "spaceId": 40722,
+ "etag": "00000021",
+ "spaceName": "MSIMS_003",
+ "spaceFormalName": "Michael Sims Test Room 003",
+ "maxCapacity": 60
+ }
+ ],
+ "resources": [],
+ "states": [
+ {
+ "state": 1,
+ "stateName": "Tentative"
+ }
+ ],
+ "eventTypes": [
+ {
+ "typeId": 231,
+ "typeName": "Meeting"
+ }
+ ],
+ "parentNodes": [
+ {
+ "id": 63070,
+ "locator": "2019-AAHVAJ",
+ "name": "Standard Events",
+ "title": "New Folder 63070",
+ "nodeType": "folder",
+ "typeName": "Event Folder",
+ "startDt": "2019-01-01T00:00:00-08:00",
+ "endDt": "2050-12-31T23:59:00-08:00"
+ }
+ ],
+ "contacts": [
+ {
+ "contactId": 718,
+ "etag": "00000021",
+ "firstName": null,
+ "familyName": "Crestron",
+ "email": "rpollard@crestron.com",
+ "isFavorite": false
+ }
+ ]
+ }
+ }
+ })
+ else
+ response.status_code = 500
+ response << "expected get event details request"
+ end
+ end
+
+ event_detail = TwentyFiveLivePro::Models::EventDetail.from_json(get_event_details.get.not_nil!.to_json)
+ event_detail.content.data.items.first.id.should eq 1
+
+ list_events = exec(:list_events, 1, 10, nil)
+
+ expect_http_request do |request, response|
+ case "#{request.path}?#{request.query}"
+ when "/event/list.json?page=1&itemsPerPage=10"
+ response.status_code = 200
+ response << %({
+ "content": {
+ "requestId": 365786,
+ "updated": "2023-04-05T00:51:51-07:00",
+ "data": {
+ "paginateKey": 16415,
+ "pageIndex": 1,
+ "totalPages": 1,
+ "totalItems": 2,
+ "currentItemCount": 2,
+ "itemsPerPage": 10,
+ "pagingLinkTemplate": "https://webservices.collegenet.com/r25ws/wrd/partners/run/external/event/list.json?current_cont_id=754&paginate=16415&page={index}&sort=event_name&order=asc",
+ "items": [
+ {
+ "kind": "event",
+ "id": 63065,
+ "etag": "00000022",
+ "eventName": "Academic Cabinet",
+ "eventLocator": "2019-AAHVAC",
+ "updated": "2019-06-13T10:05:20-07:00",
+ "dates": {
+ "startDate": "2019-01-01T00:00:00-08:00",
+ "endDate": "2050-12-31T23:59:00-08:00"
+ }
+ },
+ {
+ "kind": "event",
+ "id": 63066,
+ "etag": "00000023",
+ "eventName": "Event Cabinet",
+ "eventLocator": "2019-AAHVAD",
+ "updated": "2019-06-13T10:21:03-07:00",
+ "dates": {
+ "startDate": "2019-01-01T00:00:00-08:00",
+ "endDate": "2050-12-31T23:59:00-08:00"
+ }
+ }
+ ]
+ }
+ }
+ })
+ else
+ response.status_code = 500
+ response << "expected list events request"
+ end
+ end
+
+ events = Array(TwentyFiveLivePro::Models::Event).from_json(list_events.get.not_nil!.to_json)
+ events.size.should eq 2
+end
diff --git a/drivers/twenty_five_live_pro/models/attribute.cr b/drivers/twenty_five_live_pro/models/attribute.cr
new file mode 100644
index 00000000000..889d054c871
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/attribute.cr
@@ -0,0 +1,12 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ struct Attribute
+ include JSON::Serializable
+
+ @[JSON::Field(key: "attributeId")]
+ property attribute_id : Int64
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/availability.cr b/drivers/twenty_five_live_pro/models/availability.cr
new file mode 100644
index 00000000000..21ffca88c11
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/availability.cr
@@ -0,0 +1,59 @@
+require "json"
+require "./expanded/conflict"
+
+module TwentyFiveLivePro
+ module Models
+ struct Availability
+ include JSON::Serializable
+
+ struct Content
+ include JSON::Serializable
+
+ @[JSON::Field(key: "requestId")]
+ property request_id : String
+
+ @[JSON::Field(key: "updated")]
+ property updated : String
+
+ struct Data
+ include JSON::Serializable
+
+ struct Space
+ include JSON::Serializable
+
+ @[JSON::Field(key: "spaceId")]
+ property space_id : Int64
+
+ @[JSON::Field(key: "dates")]
+ property dates : Array(Hash(String, JSON::Any))
+
+ @[JSON::Field(key: "available")]
+ property available : Bool
+
+ @[JSON::Field(key: "conflictType")]
+ property conflict_type : Int64?
+ end
+
+ @[JSON::Field(key: "spaces")]
+ property spaces : Array(Space)
+ end
+
+ @[JSON::Field(key: "data")]
+ property data : Data
+
+ struct ExpandedInfo
+ include JSON::Serializable
+
+ @[JSON::Field(key: "conflictTypes")]
+ property conflict_types : Array(Expanded::Conflict)?
+ end
+
+ @[JSON::Field(key: "expandedInfo")]
+ property expanded_info : ExpandedInfo?
+ end
+
+ @[JSON::Field(key: "content")]
+ property content : Content
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/category.cr b/drivers/twenty_five_live_pro/models/category.cr
new file mode 100644
index 00000000000..07d2673ba88
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/category.cr
@@ -0,0 +1,14 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ struct Category
+ include JSON::Serializable
+
+ @[JSON::Field(key: "categoryId")]
+ property category_id : Int64
+ @[JSON::Field(key: "inheritCode")]
+ property inherit_code : Int64?
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/date.cr b/drivers/twenty_five_live_pro/models/date.cr
new file mode 100644
index 00000000000..636f1f4a7de
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/date.cr
@@ -0,0 +1,29 @@
+require "json"
+
+module TwentyFiveLivePro
+ struct Date
+ include JSON::Serializable
+
+ @[JSON::Field(key: "startDate", converter: TwentyFiveLivePro::Date::Converter)]
+ property start_date : Time
+
+ @[JSON::Field(key: "endDate", converter: TwentyFiveLivePro::Date::Converter)]
+ property end_date : Time
+
+ def duration
+ end_date - start_date
+ end
+
+ module Converter
+ extend self
+
+ def to_json(value, json : JSON::Builder)
+ json.string(value.to_rfc3339)
+ end
+
+ def from_json(value : JSON::PullParser)
+ Time.parse_rfc3339(value.read_string)
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/event.cr b/drivers/twenty_five_live_pro/models/event.cr
new file mode 100644
index 00000000000..7b96e249c0e
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/event.cr
@@ -0,0 +1,35 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ struct Event
+ include JSON::Serializable
+
+ @[JSON::Field(key: "kind")]
+ property kind : String
+
+ @[JSON::Field(key: "id")]
+ property id : Int64
+
+ @[JSON::Field(key: "etag")]
+ property etag : String
+
+ @[JSON::Field(key: "eventName")]
+ property name : String
+
+ @[JSON::Field(key: "eventTitle")]
+ property title : String?
+
+ @[JSON::Field(key: "eventLocator")]
+ property event_locator : String
+
+ @[JSON::Field(key: "updated")]
+ property updated : String
+
+ @[JSON::Field(key: "dates")]
+ property date : Date
+
+ property container : Bool?
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/event_detail.cr b/drivers/twenty_five_live_pro/models/event_detail.cr
new file mode 100644
index 00000000000..565f9e72ba7
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/event_detail.cr
@@ -0,0 +1,95 @@
+require "json"
+require "./expanded/**"
+
+module TwentyFiveLivePro
+ module Models
+ struct EventDetail
+ include JSON::Serializable
+
+ struct Content
+ include JSON::Serializable
+
+ @[JSON::Field(key: "id")]
+ property id : Int64?
+
+ @[JSON::Field(key: "updated")]
+ property updated : String?
+
+ struct Data
+ include JSON::Serializable
+
+ struct Event
+ include JSON::Serializable
+
+ @[JSON::Field(key: "kind")]
+ property kind : String
+
+ @[JSON::Field(key: "id")]
+ property id : Int64
+
+ @[JSON::Field(key: "etag")]
+ property etag : String
+
+ @[JSON::Field(key: "name")]
+ property name : String
+
+ @[JSON::Field(key: "eventLocator")]
+ property event_locator : String
+
+ @[JSON::Field(key: "priority")]
+ property priority : Int64
+
+ @[JSON::Field(key: "updated")]
+ property updated : String
+
+ @[JSON::Field(key: "dates")]
+ property date : Date
+ end
+
+ @[JSON::Field(key: "items")]
+ property items : Array(Event)
+ end
+
+ @[JSON::Field(key: "data")]
+ property data : Data
+
+ struct ExpandedInfo
+ include JSON::Serializable
+
+ @[JSON::Field(key: "organizations")]
+ property organizations : Array(Expanded::Organization)?
+
+ @[JSON::Field(key: "attributes")]
+ property attributes : Array(Expanded::Attribute)?
+
+ @[JSON::Field(key: "roles")]
+ property roles : Array(Expanded::Role)?
+
+ @[JSON::Field(key: "spaces")]
+ property spaces : Array(Expanded::Space)?
+
+ @[JSON::Field(key: "resources")]
+ property resources : Array(Expanded::Resource)?
+
+ @[JSON::Field(key: "states")]
+ property states : Array(Expanded::State)?
+
+ @[JSON::Field(key: "eventTypes")]
+ property event_types : Array(Expanded::EventType)?
+
+ @[JSON::Field(key: "parentNodes")]
+ property parent_nodes : Array(Expanded::ParentNode)?
+
+ @[JSON::Field(key: "contacts")]
+ property contacts : Array(Expanded::Contact)?
+ end
+
+ @[JSON::Field(key: "expandedInfo")]
+ property expanded_info : ExpandedInfo?
+ end
+
+ @[JSON::Field(key: "content")]
+ property content : Content
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/attribute.cr b/drivers/twenty_five_live_pro/models/expanded/attribute.cr
new file mode 100644
index 00000000000..5587aed9f9f
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/attribute.cr
@@ -0,0 +1,18 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct Attribute
+ include JSON::Serializable
+
+ @[JSON::Field(key: "attributeId")]
+ property attribute_id : Int64
+ @[JSON::Field(key: "attributeName")]
+ property attribute_name : String
+ @[JSON::Field(key: "attributeType")]
+ property attribute_type : String?
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/category.cr b/drivers/twenty_five_live_pro/models/expanded/category.cr
new file mode 100644
index 00000000000..8e151c04513
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/category.cr
@@ -0,0 +1,16 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct Category
+ include JSON::Serializable
+
+ @[JSON::Field(key: "categoryId")]
+ property category_id : Int64
+ @[JSON::Field(key: "categoryName")]
+ property category_name : String
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/conflict.cr b/drivers/twenty_five_live_pro/models/expanded/conflict.cr
new file mode 100644
index 00000000000..141fbcb73e9
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/conflict.cr
@@ -0,0 +1,18 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct Conflict
+ include JSON::Serializable
+
+ @[JSON::Field(key: "conflictTypeId")]
+ property conflict_type_id : Int64
+ @[JSON::Field(key: "conflictTypeName")]
+ property conflict_type_name : String
+ @[JSON::Field(key: "conflictTypeDescription")]
+ property conflict_type_description : String
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/contact.cr b/drivers/twenty_five_live_pro/models/expanded/contact.cr
new file mode 100644
index 00000000000..23b70c4ace2
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/contact.cr
@@ -0,0 +1,22 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct Contact
+ include JSON::Serializable
+
+ @[JSON::Field(key: "contactId")]
+ property contact_id : Int64?
+ @[JSON::Field(key: "etag")]
+ property etag : String?
+ @[JSON::Field(key: "firstName")]
+ property first_name : String?
+ @[JSON::Field(key: "familyName")]
+ property family_name : String?
+ @[JSON::Field(key: "email")]
+ property email : String?
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/event_type.cr b/drivers/twenty_five_live_pro/models/expanded/event_type.cr
new file mode 100644
index 00000000000..c08d281df65
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/event_type.cr
@@ -0,0 +1,16 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct EventType
+ include JSON::Serializable
+
+ @[JSON::Field(key: "typeId")]
+ property type_id : Int64
+ @[JSON::Field(key: "typeName")]
+ property type_name : String
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/feature.cr b/drivers/twenty_five_live_pro/models/expanded/feature.cr
new file mode 100644
index 00000000000..a7c57fcfc16
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/feature.cr
@@ -0,0 +1,16 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct Feature
+ include JSON::Serializable
+
+ @[JSON::Field(key: "featureId")]
+ property feature_id : Int64
+ @[JSON::Field(key: "featureName")]
+ property feature_name : String
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/layout.cr b/drivers/twenty_five_live_pro/models/expanded/layout.cr
new file mode 100644
index 00000000000..c6259a4780a
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/layout.cr
@@ -0,0 +1,16 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct Layout
+ include JSON::Serializable
+
+ @[JSON::Field(key: "layoutId")]
+ property layout_id : Int64
+ @[JSON::Field(key: "layoutName")]
+ property layout_name : String
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/organization.cr b/drivers/twenty_five_live_pro/models/expanded/organization.cr
new file mode 100644
index 00000000000..79c6cdb5a84
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/organization.cr
@@ -0,0 +1,18 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct Organization
+ include JSON::Serializable
+
+ @[JSON::Field(key: "organizationId")]
+ property organization_id : Int64
+ @[JSON::Field(key: "etag")]
+ property etag : String
+ @[JSON::Field(key: "organizationName")]
+ property organization_name : String
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/organization_type.cr b/drivers/twenty_five_live_pro/models/expanded/organization_type.cr
new file mode 100644
index 00000000000..3a0fd2d9053
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/organization_type.cr
@@ -0,0 +1,16 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct OrganizationType
+ include JSON::Serializable
+
+ @[JSON::Field(key: "organizationTypeId")]
+ property organization_type_id : Int64
+ @[JSON::Field(key: "organizationTypeName")]
+ property organization_type_name : String
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/parent_node.cr b/drivers/twenty_five_live_pro/models/expanded/parent_node.cr
new file mode 100644
index 00000000000..1ecb726c9f0
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/parent_node.cr
@@ -0,0 +1,28 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct ParentNode
+ include JSON::Serializable
+
+ @[JSON::Field(key: "id")]
+ property id : Int64
+ @[JSON::Field(key: "locator")]
+ property locator : String
+ @[JSON::Field(key: "name")]
+ property name : String
+ @[JSON::Field(key: "title")]
+ property title : String
+ @[JSON::Field(key: "nodeType")]
+ property node_type : String
+ @[JSON::Field(key: "typeName")]
+ property type_name : String
+ @[JSON::Field(key: "startDt")]
+ property start_dt : String
+ @[JSON::Field(key: "endDt")]
+ property end_dt : String
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/resource.cr b/drivers/twenty_five_live_pro/models/expanded/resource.cr
new file mode 100644
index 00000000000..3b8b937d5f5
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/resource.cr
@@ -0,0 +1,18 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct Resource
+ include JSON::Serializable
+
+ @[JSON::Field(key: "resourceId")]
+ property resource_id : Int64
+ @[JSON::Field(key: "etag")]
+ property etag : String
+ @[JSON::Field(key: "resourceName")]
+ property resource_name : String
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/role.cr b/drivers/twenty_five_live_pro/models/expanded/role.cr
new file mode 100644
index 00000000000..bfcb073655b
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/role.cr
@@ -0,0 +1,18 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct Role
+ include JSON::Serializable
+
+ @[JSON::Field(key: "roleId")]
+ property role_id : Int64
+ @[JSON::Field(key: "etag")]
+ property etag : String
+ @[JSON::Field(key: "roleName")]
+ property role_name : String
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/space.cr b/drivers/twenty_five_live_pro/models/expanded/space.cr
new file mode 100644
index 00000000000..3cc0a24a7d2
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/space.cr
@@ -0,0 +1,22 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct Space
+ include JSON::Serializable
+
+ @[JSON::Field(key: "spaceId")]
+ property space_id : Int64
+ @[JSON::Field(key: "etag")]
+ property etag : String
+ @[JSON::Field(key: "spaceName")]
+ property space_name : String
+ @[JSON::Field(key: "spaceFormalName")]
+ property space_formal_name : String
+ @[JSON::Field(key: "maxCapacity")]
+ property max_capacity : Int64
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/expanded/state.cr b/drivers/twenty_five_live_pro/models/expanded/state.cr
new file mode 100644
index 00000000000..a578604085c
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/expanded/state.cr
@@ -0,0 +1,16 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ module Expanded
+ struct State
+ include JSON::Serializable
+
+ @[JSON::Field(key: "state")]
+ property state : Int64
+ @[JSON::Field(key: "stateName")]
+ property state_name : String
+ end
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/feature.cr b/drivers/twenty_five_live_pro/models/feature.cr
new file mode 100644
index 00000000000..42f30dd6c55
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/feature.cr
@@ -0,0 +1,14 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ struct Feature
+ include JSON::Serializable
+
+ @[JSON::Field(key: "featureId")]
+ property feature_id : Int64
+ @[JSON::Field(key: "quantity")]
+ property quantity : Int64
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/layout.cr b/drivers/twenty_five_live_pro/models/layout.cr
new file mode 100644
index 00000000000..8831af0f9ff
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/layout.cr
@@ -0,0 +1,20 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ struct Layout
+ include JSON::Serializable
+
+ @[JSON::Field(key: "layoutId")]
+ property layout_id : Int64
+ @[JSON::Field(key: "defaultLayout")]
+ property default_layout : Bool
+ @[JSON::Field(key: "layoutPhotoId")]
+ property layout_photo_id : Int64?
+ @[JSON::Field(key: "layoutDiagramId")]
+ property layout_diagram_id : Int64?
+ @[JSON::Field(key: "layoutCapacity")]
+ property layout_capacity : Int64
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/organization.cr b/drivers/twenty_five_live_pro/models/organization.cr
new file mode 100644
index 00000000000..87986f208a9
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/organization.cr
@@ -0,0 +1,27 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ struct Organization
+ include JSON::Serializable
+
+ @[JSON::Field(key: "kind")]
+ property kind : String
+
+ @[JSON::Field(key: "id")]
+ property id : Int64
+
+ @[JSON::Field(key: "etag")]
+ property etag : String
+
+ @[JSON::Field(key: "organizationName")]
+ property organization_name : String
+
+ @[JSON::Field(key: "organizationTitle")]
+ property organization_title : String?
+
+ @[JSON::Field(key: "organizationTypeId")]
+ property organization_type_id : Int64?
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/organization_detail.cr b/drivers/twenty_five_live_pro/models/organization_detail.cr
new file mode 100644
index 00000000000..fbbbd34d122
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/organization_detail.cr
@@ -0,0 +1,73 @@
+require "json"
+
+require "./expanded/organization_type"
+require "./expanded/category"
+
+module TwentyFiveLivePro
+ module Models
+ struct OrganizationDetail
+ include JSON::Serializable
+
+ struct Content
+ include JSON::Serializable
+
+ @[JSON::Field(key: "requestId")]
+ property request_id : Int64
+
+ @[JSON::Field(key: "updated")]
+ property updated : String
+
+ struct Data
+ include JSON::Serializable
+
+ struct Organization
+ include JSON::Serializable
+
+ @[JSON::Field(key: "kind")]
+ property kind : String
+
+ @[JSON::Field(key: "id")]
+ property id : Int64
+
+ @[JSON::Field(key: "etag")]
+ property etag : String
+
+ @[JSON::Field(key: "organizationName")]
+ property organization_name : String
+
+ @[JSON::Field(key: "organizationTitle")]
+ property organization_title : String
+
+ @[JSON::Field(key: "updated")]
+ property updated : String
+
+ @[JSON::Field(key: "organizationTypeId")]
+ property organization_type_id : Int64
+ end
+
+ @[JSON::Field(key: "items")]
+ property items : Array(Organization)
+ end
+
+ @[JSON::Field(key: "data")]
+ property data : Data
+
+ struct ExpandedInfo
+ include JSON::Serializable
+
+ @[JSON::Field(key: "organizationTypes")]
+ property organization_types : Array(Expanded::OrganizationType)?
+
+ @[JSON::Field(key: "organizationCategories")]
+ property organization_categories : Array(Expanded::Category)?
+ end
+
+ @[JSON::Field(key: "expandedInfo")]
+ property expanded_info : Array(ExpandedInfo)?
+ end
+
+ @[JSON::Field(key: "content")]
+ property content : Content
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/paginated_response.cr b/drivers/twenty_five_live_pro/models/paginated_response.cr
new file mode 100644
index 00000000000..bda9ef696c5
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/paginated_response.cr
@@ -0,0 +1,45 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ struct PaginatedResponse
+ include JSON::Serializable
+
+ struct Content
+ include JSON::Serializable
+
+ struct Data
+ include JSON::Serializable
+ include JSON::Serializable::Unmapped
+
+ @[JSON::Field(key: "paginateKey")]
+ property paginate_key : Int64
+
+ @[JSON::Field(key: "pageIndex")]
+ property page_index : Int64
+
+ @[JSON::Field(key: "totalPages")]
+ property total_pages : Int64
+
+ @[JSON::Field(key: "totalItems")]
+ property total_items : Int64
+
+ @[JSON::Field(key: "currentItemCount")]
+ property current_item_count : Int64
+
+ @[JSON::Field(key: "itemsPerPage")]
+ property items_per_page : Int64
+
+ @[JSON::Field(key: "pagingLinkTemplate")]
+ property paging_link_template : String
+ end
+
+ @[JSON::Field(field: "data")]
+ property data : Data
+ end
+
+ @[JSON::Field(field: "content")]
+ property content : Content
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/reservations.cr b/drivers/twenty_five_live_pro/models/reservations.cr
new file mode 100644
index 00000000000..985e5c02acb
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/reservations.cr
@@ -0,0 +1,146 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ struct Reservations
+ include JSON::Serializable
+
+ @[JSON::Field(key: "engine")]
+ property engine : String?
+
+ struct Data
+ include JSON::Serializable
+
+ @[JSON::Field(key: "post_event_dt")]
+ property post_event_dt : Date
+
+ @[JSON::Field(key: "registration_url")]
+ property registration_url : String
+
+ @[JSON::Field(key: "event_end_dt")]
+ property event_end_dt : Date
+
+ @[JSON::Field(key: "profile_description")]
+ property profile_description : String
+
+ @[JSON::Field(key: "profile_name")]
+ property profile_name : String?
+
+ @[JSON::Field(key: "reservation_comment_id")]
+ property reservation_comment_id : String?
+
+ @[JSON::Field(key: "expected_count")]
+ property expected_count : Int64
+
+ @[JSON::Field(key: "reservation_state_name")]
+ property reservation_state_name : String?
+
+ @[JSON::Field(key: "last_mod_dt")]
+ property last_mod_dt : Date
+
+ struct Space
+ include JSON::Serializable
+
+ @[JSON::Field(key: "default_layout_capacity")]
+ property default_layout_capacity : String?
+
+ @[JSON::Field(key: "shared")]
+ property shared : String?
+
+ @[JSON::Field(key: "layout_id")]
+ property layout_id : Int64
+
+ @[JSON::Field(key: "layout_name")]
+ property layout_name : String?
+
+ @[JSON::Field(key: "space_instructions")]
+ property space_instructions : String?
+
+ @[JSON::Field(key: "space_name")]
+ property space_name : String?
+
+ @[JSON::Field(key: "space_instruction_id")]
+ property space_instruction_id : String?
+
+ @[JSON::Field(key: "selected_layout_capacity")]
+ property selected_layout_capacity : Int64
+
+ @[JSON::Field(key: "actual_count")]
+ property actual_count : String?
+
+ @[JSON::Field(key: "space_id")]
+ property space_id : Int64
+
+ @[JSON::Field(key: "formal_name")]
+ property formal_name : String?
+ end
+
+ @[JSON::Field(key: "space_reservation")]
+ property space_reservation : Space
+
+ @[JSON::Field(key: "event_title")]
+ property event_title : String?
+
+ @[JSON::Field(key: "reservation_state")]
+ property reservation_state : Int64
+
+ @[JSON::Field(key: "event_locator")]
+ property event_locator : String?
+
+ @[JSON::Field(key: "organization_name")]
+ property organization_name : String?
+
+ @[JSON::Field(key: "event_type_class")]
+ property event_type_class : String?
+
+ @[JSON::Field(key: "event_type_name")]
+ property event_type_name : String?
+
+ @[JSON::Field(key: "reservation_start_dt")]
+ property reservation_start_dt : Date
+
+ @[JSON::Field(key: "reservation_comments")]
+ property reservation_comments : String?
+
+ @[JSON::Field(key: "reservation_id")]
+ property reservation_id : Int64
+
+ @[JSON::Field(key: "pre_event_dt")]
+ property pre_event_dt : Date
+
+ @[JSON::Field(key: "event_id")]
+ property event_id : Int64
+
+ @[JSON::Field(key: "profile_id")]
+ property profile_id : Int64
+
+ @[JSON::Field(key: "organization_id")]
+ property organization_id : Int64
+
+ @[JSON::Field(key: "reservation_end_dt")]
+ property reservation_end_dt : Date
+
+ @[JSON::Field(key: "registered_count")]
+ property registered_count : Int64
+
+ @[JSON::Field(key: "last_mod_user")]
+ property last_mod_user : String?
+
+ @[JSON::Field(key: "event_name")]
+ property event_name : String?
+
+ @[JSON::Field(key: "event_start_dt")]
+ property event_start_dt : Date
+
+ @[JSON::Field(key: "registration_label")]
+ property registration_label : String?
+ end
+
+ @[JSON::Field(key: "reservation")]
+ property reservation : Array(Data)
+ end
+
+ @[JSON::Field(key: "Reservations")]
+ property reservations : Reservations
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/resource.cr b/drivers/twenty_five_live_pro/models/resource.cr
new file mode 100644
index 00000000000..f82ba29050c
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/resource.cr
@@ -0,0 +1,24 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ struct Resource
+ include JSON::Serializable
+
+ @[JSON::Field(key: "kind")]
+ property kind : String
+
+ @[JSON::Field(key: "id")]
+ property id : Int64
+
+ @[JSON::Field(key: "etag")]
+ property etag : String
+
+ @[JSON::Field(key: "resourceName")]
+ property resource_name : String
+
+ @[JSON::Field(key: "canRequest")]
+ property can_request : Bool
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/resource_detail.cr b/drivers/twenty_five_live_pro/models/resource_detail.cr
new file mode 100644
index 00000000000..c6e0b53b46b
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/resource_detail.cr
@@ -0,0 +1,67 @@
+require "json"
+
+require "./expanded/category.cr"
+require "./expanded/attribute.cr"
+
+module TwentyFiveLivePro
+ module Models
+ struct ResourceDetail
+ include JSON::Serializable
+
+ struct Content
+ include JSON::Serializable
+
+ @[JSON::Field(key: "requestId")]
+ property request_id : Int64
+
+ @[JSON::Field(key: "updated")]
+ property updated : String
+
+ struct Data
+ include JSON::Serializable
+
+ struct Resource
+ include JSON::Serializable
+
+ @[JSON::Field(key: "kind")]
+ property kind : String
+
+ @[JSON::Field(key: "id")]
+ property id : Int64
+
+ @[JSON::Field(key: "etag")]
+ property etag : String
+
+ @[JSON::Field(key: "resourceName")]
+ property resource_name : String
+
+ @[JSON::Field(key: "updated")]
+ property updated : String
+ end
+
+ @[JSON::Field(key: "items")]
+ property items : Array(Resource)
+ end
+
+ @[JSON::Field(key: "data")]
+ property data : Data
+
+ struct ExpandedInfo
+ include JSON::Serializable
+
+ @[JSON::Field(key: "categories")]
+ property categories : Array(Expanded::Category)?
+
+ @[JSON::Field(key: "attributes")]
+ property attributes : Array(Expanded::Attribute)?
+ end
+
+ @[JSON::Field(key: "expandedInfo")]
+ property expanded_info : Array(ExpandedInfo)?
+ end
+
+ @[JSON::Field(key: "content")]
+ property content : Content
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/role.cr b/drivers/twenty_five_live_pro/models/role.cr
new file mode 100644
index 00000000000..990612cfa30
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/role.cr
@@ -0,0 +1,15 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ struct Role
+ include JSON::Serializable
+
+ @[JSON::Field(key: "roleId")]
+ property role_id : Int64
+
+ @[JSON::Field(key: "contactId")]
+ property contact_id : Int64
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/space.cr b/drivers/twenty_five_live_pro/models/space.cr
new file mode 100644
index 00000000000..82bde03fa7a
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/space.cr
@@ -0,0 +1,30 @@
+require "json"
+
+module TwentyFiveLivePro
+ module Models
+ struct Space
+ include JSON::Serializable
+
+ @[JSON::Field(key: "kind")]
+ property kind : String
+
+ @[JSON::Field(key: "id")]
+ property id : Int64
+
+ @[JSON::Field(key: "etag")]
+ property etag : String
+
+ @[JSON::Field(key: "spaceName")]
+ property space_name : String
+
+ @[JSON::Field(key: "spaceFormalName")]
+ property space_formal_name : String?
+
+ @[JSON::Field(key: "maxCapacity")]
+ property max_capacity : Int64
+
+ @[JSON::Field(key: "canRequest")]
+ property can_request : Bool
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/models/space_detail.cr b/drivers/twenty_five_live_pro/models/space_detail.cr
new file mode 100644
index 00000000000..113d0ec5dc6
--- /dev/null
+++ b/drivers/twenty_five_live_pro/models/space_detail.cr
@@ -0,0 +1,99 @@
+require "json"
+
+require "./expanded/**"
+
+module TwentyFiveLivePro
+ module Models
+ struct SpaceDetail
+ include JSON::Serializable
+
+ struct Content
+ include JSON::Serializable
+
+ @[JSON::Field(key: "requestId")]
+ property request_id : Int64
+
+ @[JSON::Field(key: "updated")]
+ property updated : String
+
+ struct Data
+ include JSON::Serializable
+
+ struct Space
+ include JSON::Serializable
+
+ @[JSON::Field(key: "kind")]
+ property kind : String
+
+ @[JSON::Field(key: "id")]
+ property id : Int64
+
+ @[JSON::Field(key: "etag")]
+ property etag : String
+
+ @[JSON::Field(key: "spaceName")]
+ property space_name : String
+
+ @[JSON::Field(key: "spaceFormalName")]
+ property space_formal_name : String?
+
+ @[JSON::Field(key: "maxCapacity")]
+ property max_capacity : Int64
+
+ @[JSON::Field(key: "updated")]
+ property updated : String
+
+ @[JSON::Field(key: "layouts")]
+ property layouts : Array(Layout)?
+
+ @[JSON::Field(key: "features")]
+ property features : Array(Feature)?
+
+ @[JSON::Field(key: "categories")]
+ property categories : Array(Category)?
+
+ @[JSON::Field(key: "attributes")]
+ property attributes : Array(Attribute)?
+
+ @[JSON::Field(key: "roles")]
+ property roles : Array(Role)?
+ end
+
+ @[JSON::Field(key: "items")]
+ property items : Array(Space)
+ end
+
+ @[JSON::Field(key: "data")]
+ property data : Data
+
+ struct ExpandedInfo
+ include JSON::Serializable
+
+ @[JSON::Field(key: "layouts")]
+ property layouts : Array(Expanded::Layout)?
+
+ @[JSON::Field(key: "features")]
+ property features : Array(Expanded::Feature)?
+
+ @[JSON::Field(key: "categories")]
+ property categories : Array(Expanded::Category)?
+
+ @[JSON::Field(key: "attributes")]
+ property attributes : Array(Expanded::Attribute)?
+
+ @[JSON::Field(key: "roles")]
+ property roles : Array(Expanded::Role)?
+
+ @[JSON::Field(key: "contacts")]
+ property contacts : Array(Expanded::Contact)?
+ end
+
+ @[JSON::Field(key: "expandedInfo")]
+ property expanded_info : ExpandedInfo?
+ end
+
+ @[JSON::Field(key: "content")]
+ property content : Content
+ end
+ end
+end
diff --git a/drivers/twenty_five_live_pro/room_schedule.cr b/drivers/twenty_five_live_pro/room_schedule.cr
new file mode 100644
index 00000000000..f01798f8a8b
--- /dev/null
+++ b/drivers/twenty_five_live_pro/room_schedule.cr
@@ -0,0 +1,181 @@
+require "placeos-driver"
+require "./models/**"
+
+class TwentyFiveLivePro::RoomSchedule < PlaceOS::Driver
+ descriptive_name "25Live Pro Room Schedule Logic"
+ generic_name :RoomSchedule
+ description %(Polls 25Live Pro API Module to expose bookings relevant for the selected System)
+
+ default_settings({
+ twenty_five_live_pro_space_id: "set 25Live Pro Space ID here",
+ polling_cron: "*/15 * * * *",
+ debug: false,
+ })
+
+ accessor twenty_five_live_pro : API_1
+
+ @space_id : String = "set 25Live Pro Space ID here"
+ @cron_string : String = "*/15 * * * *"
+ @debug : Bool = false
+ @next_countdown : PlaceOS::Driver::Proxy::Scheduler::TaskWrapper? = nil
+ @request_lock : Mutex = Mutex.new
+ @request_running : Bool = false
+
+ def on_update
+ @debug = setting(Bool, :debug) || false
+ @space_id = setting(String, :twenty_five_live_pro_space_id)
+ @cron_string = setting(String, :polling_cron)
+ schedule.clear
+ schedule.cron(@cron_string, immediate: true) { fetch_and_expose_todays_events }
+ end
+
+ def fetch_and_expose_todays_events
+ return if @request_running
+
+ @request_lock.synchronize do
+ begin
+ @request_running = true
+ @next_countdown.try &.cancel
+ @next_countdown = nil
+ today = Time.local
+ todays_events = fetch_events(today.to_s("%Y-%m-%d"), today.to_s("%Y-%m-%d"), today.to_s("%Y%m%d"))
+
+ # Determine which events contain other events
+ todays_events.sort_by(&.date.duration).reverse!
+
+ todays_events.each_with_index do |e, i|
+ if todays_events.skip(i + 1).find { |f| contains?(e, f) }
+ e.container = true
+ else
+ e.container = false
+ end
+ end
+
+ current_and_past_events, future_events = todays_events.partition { |e| Time.local > e.date.start_date }
+ current_events, past_events = current_and_past_events.partition { |e| in_progress?(e) }
+
+ if @debug
+ self[:todays_upcoming_events] = future_events
+ self[:todays_past_events] = past_events
+ end
+
+ next_event = future_events.min_by? &.date.start_date
+ previous_event = past_events.max_by? &.date.end_date
+ current_event = current_events.find { |e| !e.container }
+ current_container_event = current_events.find(&.container)
+
+ update_event_details(previous_event, current_event, next_event)
+ advance_countdowns(previous_event, current_event, next_event, current_container_event)
+ todays_events
+ ensure
+ @request_running = false
+ end
+ end
+ end
+
+ def fetch_events(start_date : String, end_date : String, since : String)
+ relevant_events = [] of Models::Event
+ events = Array(Models::Event).from_json(twenty_five_live_pro.list_events(1, 100, since, nil).get.not_nil!.to_json)
+
+ events.each do |event|
+ details = Models::EventDetail.from_json(twenty_five_live_pro.get_event_details(event.id, ["all"], ["all"]).get.not_nil!.to_json)
+
+ if expanded_info = details.content.expanded_info
+ if spaces = expanded_info.spaces
+ next if spaces.empty?
+
+ if @space_id == spaces.first.space_id
+ if event_data = details.content.data
+ if event_items = event_data.items
+ next if event_items.empty?
+
+ event_items.each do |event_item|
+ if date = event_item.date
+ if date.start_date.to_rfc3339.includes?(start_date) && date.end_date.to_rfc3339.includes?(start_date)
+ relevant_events.push(Models::Event.from_json(event_item.to_json))
+ end
+ end
+ end
+ end
+ end
+ end
+ end
+ end
+ end
+
+ relevant_events
+ end
+
+ private def update_event_details(previous_event : Models::Event | Nil = nil, current_event : Models::Event | Nil = nil, next_event : Models::Event | Nil = nil)
+ if previous_event
+ self[:previous_event_ends_at] = previous_event.date.end_date
+ self[:previous_event_was_container] = previous_event.container
+ self[:previous_event_id] = previous_event.id if @debug
+ end
+
+ if current_event
+ self[:current_event_starts_at] = current_event.date.start_date
+ self[:current_event_ends_at] = current_event.date.end_date
+ self[:current_event_id] = current_event.id if @debug
+ self[:current_event_description] = current_event.name if @debug
+ end
+
+ if next_event
+ self[:next_event_starts_at] = next_event.date.start_date
+ self[:next_event_is_container] = next_event.container
+ self[:next_event_id] = next_event.id if @debug
+ end
+ end
+
+ private def advance_countdowns(previous : Models::Event | Nil, current : Models::Event | Nil, next_event : Models::Event | Nil, container : Models::Event | Nil)
+ previous ? countup_previous_event(previous) : (self[:minutes_since_previous_event] = nil)
+ next_event_started = next_event ? countdown_next_event(next_event) : (self[:minutes_til_next_event] = nil)
+ current_event_ended = current ? countdown_current_event(current) : (self[:minutes_since_current_event_started] = self[:minutes_til_current_event_ends] = nil)
+
+ logger.debug { "Next event started? #{next_event_started}\nCurrent event ended? #{current_event_ended}" } if @debug
+ @next_countdown = if next_event_started || current_event_ended
+ schedule.in(1.minutes) { fetch_and_expose_todays_events.as(Array(Models::Event)) }
+ else
+ schedule.in(1.minutes) { advance_countdowns(previous, current, next_event, container).as(Bool) }
+ end
+
+ self[:event_in_progress] = current ? in_progress?(current) : false
+ self[:container_event_in_progess] = container ? in_progress?(container) : false
+ self[:no_upcoming_events] = next_event.nil?
+ end
+
+ private def countup_previous_event(previous : Models::Event)
+ time_since_previous = Time.local - previous.date.end_date
+ self[:minutes_since_previous_event] = time_since_previous.total_minutes.to_i
+ end
+
+ private def countdown_next_event(next_event : Models::Event)
+ time_til_next = next_event.date.start_date - Time.local
+ self[:minutes_til_next_event] = time_til_next.total_minutes.to_i
+ # return whether the next event has started
+ Time.local >= next_event.date.start_date
+ end
+
+ private def countdown_current_event(current : Models::Event)
+ time_since_start = Time.local - current.date.start_date
+ time_til_end = current.date.end_date - Time.local
+ self[:minutes_since_current_event_started] = time_since_start.total_minutes.to_i
+ self[:minutes_til_current_event_ends] = time_til_end.total_minutes.to_i
+ # return whether the current event has ended
+ Time.local > current.date.end_date
+ end
+
+ private def in_progress?(event : Models::Event)
+ now = Time.local
+ now >= event.date.start_date && now <= event.date.end_date
+ end
+
+ # Does a contain b?
+ private def contains?(a : Models::Event, b : Models::Event)
+ b.date.start_date >= a.date.start_date && b.date.end_date <= a.date.end_date
+ end
+
+ private def overlaps?(a : Models::Event, b : Models::Event)
+ b.date.start_date < a.date.end_date || b.date.end_date > a.date.start_date
+ end
+end
diff --git a/drivers/ubipark/api.cr b/drivers/ubipark/api.cr
new file mode 100644
index 00000000000..2a32bacbee3
--- /dev/null
+++ b/drivers/ubipark/api.cr
@@ -0,0 +1,152 @@
+require "placeos-driver"
+require "json"
+
+module UbiPark
+ class API < PlaceOS::Driver
+ descriptive_name "UbiPark API Gateway"
+ generic_name :Bookings
+ uri_base "https://api-data.ubipark.com/"
+
+ default_settings({
+ api_key: "WWvT7qvWd2ZcQmo67CutkyAvbGumG4b7",
+ tenant_id: 0,
+ api_version: "v1.0",
+ user_agent: "PlaceOS",
+ })
+
+ def on_load
+ on_update
+ end
+
+ @api_key : String = "WWvT7qvWd2ZcQmo67CutkyAvbGumG4b7"
+ @tenant_id : Int32 = 0
+
+ @api_version : String = "v1.0"
+
+ @user_agent : String = "PlaceOS"
+
+ def on_update
+ @api_key = setting(String, :api_key)
+ @tenant_id = setting(Int32, :tenant_id)
+
+ @api_version = setting(String, :api_version)
+
+ @user_agent = setting?(String, :user_agent) || "PlaceOS"
+ end
+
+ def list_users(max_records : Int32, offset : Int32, from_last_modified_time : String)
+ body = {
+ "maxRecords" => max_records,
+ "offset" => offset,
+ "fromLastModifiedTime" => from_last_modified_time,
+ }.to_json
+
+ response = http("GET", "/data/export/#{@api_version}/user/list", body: body, headers: HTTP::Headers{"X-ApiKey" => @api_key, "X-ApiTenantID" => @tenant_id.to_s, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ logger.debug { "response status code: #{response.status_code}" }
+ logger.debug { "response body:\n#{response.body}" }
+
+ unless response.success?
+ self[:error] = "The response returned by the server had a status code of #{response.status_code}, see the logs for the response body"
+ raise "unexpected response #{response.status_code}\n#{response.body}"
+ end
+
+ JSON.parse(response.body)
+ end
+
+ def list_userpermits(max_records : Int32, offset : Int32, from_last_modified_time : String, car_park_id : Int32, user_id : Int32)
+ body = {
+ "maxRecords" => max_records,
+ "offset" => offset,
+ "fromLastModifiedTime" => from_last_modified_time,
+ "carParkId" => car_park_id,
+ "userId" => user_id,
+ }.to_json
+
+ response = http("GET", "/data/export/#{@api_version}/userpermit/list", body: body, headers: HTTP::Headers{"X-ApiKey" => @api_key, "X-ApiTenantID" => @tenant_id.to_s, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ unless response.success?
+ self[:error] = "The response returned by the server had a status code of #{response.status_code}, see the logs for the response body"
+ raise "unexpected response #{response.status_code}\n#{response.body}"
+ end
+
+ logger.debug { "response status code: #{response.status_code}" }
+ logger.debug { "response body:\n#{response.body}" }
+
+ unless response.success?
+ self[:error] = "The response returned by the server had a status code of #{response.status_code}, see the logs for the response body"
+ raise "unexpected response #{response.status_code}\n#{response.body}"
+ end
+
+ JSON.parse(response.body)
+ end
+
+ def list_products(car_park_id : Int32?, tenant_id : Int32?)
+ query = [] of String
+
+ query.push("carParkID=#{car_park_id}") unless car_park_id.nil?
+ query.push("tenantID=#{tenant_id}") unless tenant_id.nil?
+
+ url = query.size > 0 ? "/api/payment/productList?#{query.join("&")}" : "/api/payment/productList"
+
+ response = http("GET", url, headers: HTTP::Headers{"X-ApiKey" => @api_key, "X-ApiTenantID" => @tenant_id.to_s, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ logger.debug { "response status code: #{response.status_code}" }
+ logger.debug { "response body:\n#{response.body}" }
+
+ unless response.success?
+ self[:error] = "The response returned by the server had a status code of #{response.status_code}, see the logs for the response body"
+ raise "unexpected response #{response.status_code}\n#{response.body}"
+ end
+
+ JSON.parse(response.body)
+ end
+
+ def list_reasons(tenant_id : Int32?)
+ query = [] of String
+
+ query.push("tenantID=#{tenant_id}") unless tenant_id.nil?
+
+ url = query.size > 0 ? "/api/payment/reasonList?#{query.join("&")}" : "/api/payment/productList"
+
+ response = http("GET", url, headers: HTTP::Headers{"X-ApiKey" => @api_key, "X-ApiTenantID" => @tenant_id.to_s, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ logger.debug { "response status code: #{response.status_code}" }
+ logger.debug { "response body:\n#{response.body}" }
+
+ unless response.success?
+ self[:error] = "The response returned by the server had a status code of #{response.status_code}, see the logs for the response body"
+ raise "unexpected response #{response.status_code}\n#{response.body}"
+ end
+
+ JSON.parse(response.body)
+ end
+
+ def make_payment(payment_id : String, promise_pay_card_name : String, user_id : String, tenant_id : Int32, product_id : String, from_date : String, to_date : String, amount : Float64)
+ raise "amount can't be less than zero" if amount < 0
+
+ body = {
+ "paymentID" => payment_id,
+ "promisePayCardName" => promise_pay_card_name,
+ "userID" => user_id,
+ "tenantID" => tenant_id,
+ "productID" => product_id,
+ "fromDate" => from_date,
+ "toDate" => to_date,
+ "amount" => ("%.2f" % amount).to_f64,
+ }.to_json
+
+ response = post("/api/payment/makepayment", body: body, headers: HTTP::Headers{"X-ApiKey" => @api_key, "X-ApiTenantID" => @tenant_id.to_s, "User-Agent" => @user_agent, "Content-Type" => "application/json"})
+
+ logger.debug { "response status code: #{response.status_code}" }
+ logger.debug { "response body:\n#{response.body}" }
+
+ unless response.success?
+ self[:error] = "The response returned by the server had a status code of #{response.status_code}, see the logs for the response body"
+ raise "unexpected response #{response.status_code}\n#{response.body}"
+ end
+
+ JSON.parse(response.body)
+ end
+ end
+end
diff --git a/drivers/ubipark/api_spec.cr b/drivers/ubipark/api_spec.cr
new file mode 100644
index 00000000000..3453f95a1dd
--- /dev/null
+++ b/drivers/ubipark/api_spec.cr
@@ -0,0 +1,466 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "UbiPark::API" do
+ # Users
+
+ list_users = exec(:list_users, 10, 0, String.new)
+
+ expect_http_request do |request, response|
+ case "#{request.path}"
+ when "/data/export/v1.0/user/list"
+ response.status_code = 200
+ response << %([
+ {
+ "RecordCount": 453,
+ "MoreResultsAvailable": true,
+ "Users": [
+ {
+ "userId": 9717,
+ "firstName": "John",
+ "lastName": "Smith",
+ "phone": "Smith",
+ "email": "johnsmith@ubipark.com",
+ "hasCreditCard": true,
+ "marketing": true,
+ "updated": "true"
+ }
+ ]
+ }
+ ])
+ else
+ response.status_code = 500
+ response << "expected get space details request"
+ end
+ end
+
+ users = list_users.get.not_nil!
+ users.as_a.first.["RecordCount"].as_i.should eq 453
+
+ # User permits
+
+ list_userpermits = exec(:list_userpermits, 0, 0, String.new, 0, 0)
+
+ expect_http_request do |request, response|
+ case "#{request.path}"
+ when "/data/export/v1.0/userpermit/list"
+ response.status_code = 200
+ response << %([
+ {
+ "RecordCount": 453,
+ "MoreResultsAvailable": true,
+ "UserPermits": [
+ {
+ "userPermitId": 10917,
+ "userId": 9717,
+ "email": "string",
+ "emailConfirmed": true,
+ "firstName": "string",
+ "lastName": "string",
+ "phoneNo": "string",
+ "permitId": 0,
+ "permitName": "string",
+ "carParkId": 0,
+ "carParkName": "string",
+ "approvalStatus": 0,
+ "approvedBy": 0,
+ "approved": "2024-04-11T14:48:28.487Z",
+ "message": "string",
+ "notes": "string",
+ "effectiveFrom": "2024-04-11T14:48:28.487Z",
+ "effectiveTo": "2024-04-11T14:48:28.487Z",
+ "emailed": true,
+ "notified": true,
+ "userConfirmationRequired": true,
+ "acknowledged": true,
+ "paidTo": "2024-04-11T14:48:28.487Z",
+ "paidToUTC": "2024-04-11T14:48:28.487Z",
+ "address": "string",
+ "suburb": "string",
+ "stateId": 0,
+ "postcode": "string",
+ "ContactAddress": "string",
+ "licensePlate": "string",
+ "vehicleStateId": 0,
+ "vehicleMake": "string",
+ "vehicleModel": "string",
+ "vehicleColour": "string",
+ "courtesyPeriod": true,
+ "expiryEmailed": true,
+ "expiryNotified": true,
+ "active": true,
+ "inserted": "2024-04-11T14:48:28.487Z",
+ "insertedBy": 0,
+ "updated": "true",
+ "updatedBy": 0,
+ "tenantId": 0,
+ "permitNotes": "string",
+ "editVehicle": true,
+ "editVehicleHours": 0,
+ "editVehicleText": "string",
+ "editVehicleTooltip": "string",
+ "vehicleCountryId": 0,
+ "paymentPostcode": "string",
+ "paymentOccupants": 0,
+ "reminderEmailed": true,
+ "reminderNotified": true,
+ "vehicleStateCode": "string",
+ "permitCreated": "2024-04-11T14:48:28.488Z",
+ "permitModified": "2024-04-11T14:48:28.488Z",
+ "timezoneKey": "string",
+ "permitType": 0,
+ "partPayment": true,
+ "permitExternalRef": "string",
+ "airlineId": 0,
+ "permitReasonId": 0,
+ "externalRef": "string",
+ "externalUserId": "string",
+ "permitState": 0,
+ "stateCode": "string",
+ "permitGroupId": 0,
+ "permitGroupCode": "string",
+ "qRCode": true,
+ "reservedBays": true,
+ "userCancel": true,
+ "userCancelHours1": 0,
+ "userCancelFee1": 0,
+ "userCancelHours2": 0,
+ "userCancelFee2": 0,
+ "Overstay": true,
+ "OverstayEmailed": true,
+ "OverstayNotified": true,
+ "OverstayPayment": true,
+ "StaffId": "string",
+ "userChange": true,
+ "UserChangeHours": 0,
+ "userChangeTooltip": "string",
+ "userChangeText": "string",
+ "staffIdDisplay": true,
+ "staffIdRequired": true,
+ "permitSchedule": true,
+ "schedule": true,
+ "Mom": true,
+ "monFrom": "2024-04-11T14:48:28.488Z",
+ "monTo": "2024-04-11T14:48:28.488Z",
+ "tue": true,
+ "tueFrom": "2024-04-11T14:48:28.488Z",
+ "tueTo": "2024-04-11T14:48:28.488Z",
+ "wed": true,
+ "wedFrom": "2024-04-11T14:48:28.488Z",
+ "wedTo": "2024-04-11T14:48:28.488Z",
+ "thu": true,
+ "thuFrom": "2024-04-11T14:48:28.488Z",
+ "thuTo": "2024-04-11T14:48:28.488Z",
+ "fri": true,
+ "friFrom": "2024-04-11T14:48:28.488Z",
+ "friTo": "2024-04-11T14:48:28.488Z",
+ "sat": true,
+ "satFrom": "2024-04-11T14:48:28.488Z",
+ "satTo": "2024-04-11T14:48:28.488Z",
+ "sun": true,
+ "sunFrom": "2024-04-11T14:48:28.488Z",
+ "sunTo": "2024-04-11T14:48:28.488Z",
+ "versionNo": 0,
+ "reason": "string",
+ "attachment": "string",
+ "fileName": "string",
+ "contentType": "string",
+ "promoCodeId": 0,
+ "promoCodeOneTimeUseId": 0,
+ "promoCode": "string",
+ "captureNumberPlate": true,
+ "numberPlateRequired": true,
+ "confirmLicensePlate": true,
+ "groupPermit": true,
+ "organisationName": "string",
+ "organisationPrincipal": "string",
+ "organiserFirstName": "string",
+ "organiserLastName": "string",
+ "organiserMobileNo": "string",
+ "organiserEmail": "string",
+ "contactPhoneNo": "string",
+ "contactFaxNo": "string",
+ "agencyName": "string",
+ "agencyPhone": "string",
+ "agencyContactName": "string",
+ "agencyEmailAddress": "string",
+ "vehicleTypeId": 0,
+ "noChildren": 0,
+ "NoAdults": 0,
+ "noUnder5": 0,
+ "entryID": 0,
+ "noVehicles": 0,
+ "transportCompanyName": "string",
+ "groupPermitTypeId": 0,
+ "multiDay": true,
+ "customText": "string",
+ "bayLabel": "string",
+ "courtesyPeriodTooltip": "string",
+ "courtesyPeriodText": "string",
+ "courtesyPeriodNotValidText": "string",
+ "zoneCode": "string",
+ "permitAreaCode": "string",
+ "siteCode": "string",
+ "uniqueId": "string",
+ "userCancelDays": 0,
+ "userCancelHours": 0,
+ "vehicleCountryCode": "string",
+ "permitCourtesyPeriod": true,
+ "courtesyPeriodTime": "2024-04-11T14:48:28.488Z",
+ "startGraceDays": 0,
+ "startGraceMins": 0,
+ "endGraceDays": 0,
+ "endGraceMins": 0,
+ "userRefund": true,
+ "userRefundFee": 0,
+ "uploadDocument": true,
+ "uploadDocumentLabel": "string",
+ "documentUploadRequired": true,
+ "documentDeleteAfterApproval": true,
+ "overnight": true,
+ "noSeats": 0,
+ "leaderFirstName": "string",
+ "leaderLastName": "string",
+ "leaderMobileNo": "string",
+ "leaderEmail": "string",
+ "appID": 0,
+ "customAdminValue": "string"
+ }
+ ]
+ }
+ ])
+ else
+ response.status_code = 500
+ response << "expected get space details request"
+ end
+ end
+
+ user_permits = list_userpermits.get.not_nil!
+ user_permits.as_a.first.["RecordCount"].as_i.should eq 453
+
+ # Products
+
+ list_products = exec(:list_products, 1, nil)
+
+ expect_http_request do |request, response|
+ case "#{request.path}"
+ when "/api/payment/productList"
+ response.status_code = 200
+ response << %([
+ {
+ "productID": "VALET",
+ "description": "Premium Valet",
+ "tenantID": 321,
+ "carParkName": "Long Term Car Park",
+ "carParkID": 321,
+ "groupId": 321,
+ "groupCode": "VALET",
+ "groupDescription": "Valet Parking",
+ "default": false,
+ "permitType": 2,
+ "yearType": 0,
+ "yearDate": "2024-04-11T14:54:02.728Z",
+ "monthType": 0,
+ "monthDay": 0,
+ "monthWeek": 0,
+ "monthWeekDay": 0,
+ "weekType": 0,
+ "weekDay": 0,
+ "multiDay": false,
+ "recurring": false,
+ "autoRenew": false,
+ "autoApprove": false,
+ "reminder": true,
+ "reminderDays": true,
+ "daysInAdvance": true,
+ "effectiveFrom": "2020-02-01 00:00",
+ "effectiveTo": "2025-02-01 00:00",
+ "minPurchaseDate": "2025-02-01 00:00",
+ "maxPurchaseDate": "2025-02-01 00:00",
+ "previousDays": 0,
+ "notes": "Billed every month in advance. Must park in speacial section.",
+ "maxAvailable": 40,
+ "addressRequired": false,
+ "contactAddressRequired": false,
+ "confirmLicensePlate": false,
+ "vehicleDetailsRequired": false,
+ "postPaymentRequired": false,
+ "postcodeRequired": false,
+ "occupantsRequired": false,
+ "promoCode": true,
+ "airlineDisplay": true,
+ "airlineRequired": true,
+ "permitReasonDisplay": true,
+ "permitReasonRequired": true,
+ "maxPurchaseDays": 12,
+ "qrCode": true,
+ "reservedBays": true,
+ "overstayCharge": false,
+ "staffIDRequired": false,
+ "schedule": false,
+ "userAccountRequired": false,
+ "captureNumberPlate": false,
+ "numberPlateRequired": false,
+ "groupPermit": false,
+ "paymentMessage": "false",
+ "displayIfZeroAmount": false,
+ "displayTermsAndConditions": false,
+ "displayMarketing": false,
+ "customText": "false",
+ "customTextDisplay": false,
+ "customTextRequired": false,
+ "customWarningDisplay": false,
+ "customWarning": "Details are required.",
+ "eventType": "false",
+ "eventDates": "false",
+ "eventStartDate": "false",
+ "eventEndDate": "false",
+ "timezone": "AUS Eastern Standard Time",
+ "closedDays": false
+ }
+ ])
+ when "/api/payment/productList?#{request.query}"
+ response.status_code = 200
+ response << %([
+ {
+ "productID": "VALET",
+ "description": "Premium Valet",
+ "tenantID": 321,
+ "carParkName": "Long Term Car Park",
+ "carParkID": 321,
+ "groupId": 321,
+ "groupCode": "VALET",
+ "groupDescription": "Valet Parking",
+ "default": false,
+ "permitType": 2,
+ "yearType": 0,
+ "yearDate": "2024-04-11T14:54:02.728Z",
+ "monthType": 0,
+ "monthDay": 0,
+ "monthWeek": 0,
+ "monthWeekDay": 0,
+ "weekType": 0,
+ "weekDay": 0,
+ "multiDay": false,
+ "recurring": false,
+ "autoRenew": false,
+ "autoApprove": false,
+ "reminder": true,
+ "reminderDays": true,
+ "daysInAdvance": true,
+ "effectiveFrom": "2020-02-01 00:00",
+ "effectiveTo": "2025-02-01 00:00",
+ "minPurchaseDate": "2025-02-01 00:00",
+ "maxPurchaseDate": "2025-02-01 00:00",
+ "previousDays": 0,
+ "notes": "Billed every month in advance. Must park in speacial section.",
+ "maxAvailable": 40,
+ "addressRequired": false,
+ "contactAddressRequired": false,
+ "confirmLicensePlate": false,
+ "vehicleDetailsRequired": false,
+ "postPaymentRequired": false,
+ "postcodeRequired": false,
+ "occupantsRequired": false,
+ "promoCode": true,
+ "airlineDisplay": true,
+ "airlineRequired": true,
+ "permitReasonDisplay": true,
+ "permitReasonRequired": true,
+ "maxPurchaseDays": 12,
+ "qrCode": true,
+ "reservedBays": true,
+ "overstayCharge": false,
+ "staffIDRequired": false,
+ "schedule": false,
+ "userAccountRequired": false,
+ "captureNumberPlate": false,
+ "numberPlateRequired": false,
+ "groupPermit": false,
+ "paymentMessage": "false",
+ "displayIfZeroAmount": false,
+ "displayTermsAndConditions": false,
+ "displayMarketing": false,
+ "customText": "false",
+ "customTextDisplay": false,
+ "customTextRequired": false,
+ "customWarningDisplay": false,
+ "customWarning": "Details are required.",
+ "eventType": "false",
+ "eventDates": "false",
+ "eventStartDate": "false",
+ "eventEndDate": "false",
+ "timezone": "AUS Eastern Standard Time",
+ "closedDays": false
+ }
+ ])
+ else
+ response.status_code = 500
+ response << "expected get space details request"
+ end
+ end
+
+ products = list_products.get.not_nil!
+ products.as_a.first.["productID"].as_s.should eq "VALET"
+
+ # Reasons
+
+ list_reasons = exec(:list_reasons, 1)
+
+ expect_http_request do |request, response|
+ case "#{request.path}"
+ when "/api/payment/reasonList"
+ response.status_code = 200
+ response << %([
+ {
+ "tenantID": 12,
+ "reasonID": "HOL",
+ "description": "Holiday"
+ }
+ ])
+ when "/api/payment/reasonList?#{request.query}"
+ response.status_code = 200
+ response << %([
+ {
+ "tenantID": 12,
+ "reasonID": "HOL",
+ "description": "Holiday"
+ }
+ ])
+ else
+ response.status_code = 500
+ response << "expected get space details request"
+ end
+ end
+
+ reasons = list_reasons.get.not_nil!
+ reasons.as_a.first.["reasonID"].as_s.should eq "HOL"
+
+ # Payments
+
+ # payment_id : String, promise_pay_card_name : String, user_id : String, tenant_id : Int32, product_id : String, from_date : String, to_date : String, amount : Float64
+ make_payment = exec(:make_payment, "1", "2", "3", 4, "5", "6", "7", 20.841)
+
+ expect_http_request do |request, response|
+ case "#{request.path}"
+ when "/api/payment/makepayment"
+ response.status_code = 200
+ response << %({
+ "success": true,
+ "errors": [
+ "string"
+ ],
+ "gatewayTimeout": false,
+ "paymentHeld": false,
+ "paymentID": "12345",
+ "receiptNo": "987651",
+ "amount": 20.84
+ })
+ else
+ response.status_code = 500
+ response << "expected get space details request"
+ end
+ end
+
+ payment = make_payment.get.not_nil!
+ payment["success"].as_bool.should eq true
+end
diff --git a/drivers/vecos/releezme.cr b/drivers/vecos/releezme.cr
new file mode 100644
index 00000000000..bb37d9ea44c
--- /dev/null
+++ b/drivers/vecos/releezme.cr
@@ -0,0 +1,353 @@
+require "placeos-driver"
+require "oauth2"
+require "./releezme/*"
+
+# documentation: https://acc-sapi.releezme.net/swagger/ui/index
+
+class Vecos::Releezme < PlaceOS::Driver
+ descriptive_name "Vecos Releezme Gateway"
+ generic_name :ReleezmeLockers
+ uri_base "https://acc-sapi.releezme.net"
+
+ default_settings({
+ client_id: "8537d5c8-a85c-4657-bc6b-7c35b1405464",
+ client_secret: "856b5b85d3eb4697369",
+ username: "admin",
+ password: "admin",
+ releezme_authentication_domain: "acc-identity.releezme.net",
+ })
+
+ def on_update
+ client_id = setting(String, :client_id)
+ client_secret = setting(String, :client_secret)
+ username = setting(String, :username)
+ password = setting(String, :password)
+ releezme_authentication_domain = setting(String, :releezme_authentication_domain)
+
+ transport.before_request do |req|
+ access_token = get_access_token(client_id, client_secret, username, password, releezme_authentication_domain)
+ req.headers["Authorization"] = access_token
+ req.headers["Content-Type"] = "application/json"
+ logger.debug { "requesting #{req.method} #{req.path}?#{req.query}\n#{req.headers}\n#{req.body}" }
+ end
+ end
+
+ @expires : Time = Time.utc
+ @bearer_token : String = ""
+ @access_token : OAuth2::AccessToken? = nil
+
+ protected def get_access_token(client_id, client_secret, username, password, releezme_authentication_domain)
+ return @bearer_token if 1.minute.from_now < @expires
+
+ # check if we are running a spec
+ if config.uri.as(String).includes?("127.0.0.1")
+ uri = URI.parse config.uri.as(String)
+ auth_domain = uri.host.as(String)
+ port = uri.port.as(Int32)
+ scheme = "http"
+ else
+ auth_domain = releezme_authentication_domain
+ scheme = "https"
+ end
+
+ # use the built in crystal oauth client
+ client = OAuth2::Client.new(auth_domain, client_id, client_secret, scheme: scheme, port: port, token_uri: "/connect/token")
+ token = if (access_token = @access_token) && access_token.refresh_token.presence
+ begin
+ client.get_access_token_using_refresh_token(access_token.refresh_token)
+ rescue error : OAuth2::Error
+ logger.warn(exception: error) { "failed to refresh token" }
+ client.get_access_token_using_resource_owner_credentials(username: username, password: password, scope: "Vecos.Releezme.Web.SAPI offline_access")
+ end
+ else
+ client.get_access_token_using_resource_owner_credentials(username: username, password: password, scope: "Vecos.Releezme.Web.SAPI offline_access")
+ end
+ @expires = token.expires_in.as(Int64).seconds.from_now
+ @access_token = token
+ @bearer_token = "Bearer #{token.access_token}"
+ end
+
+ @[Security(Level::Support)]
+ def fetch_pages(location : String) : Array(JSON::Any)
+ append = location.includes?('?') ? '&' : '?'
+ next_page = "#{location}#{append}pageNumber=#{1}"
+ data = [] of JSON::Any
+
+ loop do
+ response = get(next_page)
+ @expires = 1.minute.ago if response.status_code == 401
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+
+ payload = JSON.parse(response.body).as_h
+ pages = if has_paging = payload.delete("Paging")
+ Paging.from_json has_paging.to_json
+ end
+ data.concat payload[payload.keys.first].as_a
+
+ break unless pages && pages.has_next_page
+
+ next_page = "#{location}#{append}pageNumber=#{pages.page_number + 1}"
+ end
+
+ data
+ end
+
+ @[Security(Level::Support)]
+ def fetch_item(location : String) : String
+ response = get(location)
+ @expires = 1.minute.ago if response.status_code == 401
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ logger.debug { "response body:\n#{response.body}" }
+ response.body
+ end
+
+ @[Security(Level::Support)]
+ def bearer_token
+ @bearer_token
+ end
+
+ # ===============
+ # COMPANIES
+ # ===============
+
+ def companies
+ JSON.parse(fetch_item("/api/companies"))["Companies"]
+ end
+
+ # =======================
+ # LOCATIONS / Buildings
+ # =======================
+
+ # typically these are buildings
+ def locations
+ fetch_pages("/api/locations?pageSize=200")
+ end
+
+ def location(location_id : String)
+ Location.from_json fetch_item("/api/locations/#{location_id}")
+ end
+
+ # typically these are floors in the building
+ def location_sections(location_id : String)
+ fetch_pages("/api/locations/#{location_id}/sections?pageSize=200")
+ end
+
+ # ===================
+ # SECTIONS / Levels
+ # ===================
+
+ # all floors from all buildings in one request
+ def sections
+ fetch_pages("/api/sections?pageSize=200")
+ end
+
+ def section(section_id : String)
+ Section.from_json fetch_item("/api/locations/#{section_id}")
+ end
+
+ def section_locker_banks(section_id : String)
+ fetch_pages("/api/sections/#{section_id}/lockerbanks?pageSize=200")
+ end
+
+ # banks and groups in the banks that the user can allocate to themselves
+ def section_banks_allocatable(section_id : String, user_id : String)
+ params = URI::Params.build do |form|
+ form.add "externalUserId", user_id
+ form.add "pageSize", "200"
+ end
+ fetch_pages("/api/sections/#{section_id}/lockerbanklockergroups/allocatable?#{params}")
+ end
+
+ # =====================================
+ # BANKS / lockers physically together
+ # =====================================
+
+ def banks
+ fetch_pages("/api/lockerbanks?pageSize=200")
+ end
+
+ def bank(bank_id : String)
+ LockerBank.from_json fetch_item("/api/lockerbanks/#{bank_id}")
+ end
+
+ def bank_groups(bank_id : String)
+ fetch_pages("/api/lockerbanks/#{bank_id}/lockergroups?pageSize=200")
+ end
+
+ # returns all the lockers in the bank without paging (but paging json is included)
+ def bank_lockers(bank_id : String)
+ fetch_pages("/api/lockerbanks/#{bank_id}/lockers?pageSize=200")
+ end
+
+ def bank_group_lockers_available(bank_id : String, group_id : String)
+ fetch_pages("/api/lockerbanks/#{bank_id}/#{group_id}/availablelockers?pageSize=200")
+ end
+
+ # NOTE:: Only accessible to System Control Clients
+ def bank_locker_allocations(bank_id : String)
+ fetch_pages("/api/lockerbanks/#{bank_id}/allocations?pageSize=200")
+ end
+
+ # ===============================================
+ # GROUPS / lockers assigned to a group of users
+ # ===============================================
+
+ def groups
+ fetch_pages("/api/lockergroups?pageSize=200")
+ end
+
+ def group(group_id : String)
+ Array(LockerGroup).from_json fetch_item("/api/lockergroups/#{group_id}")
+ end
+
+ def group_locker_banks(group_id : String)
+ fetch_pages("/api/lockergroups/#{group_id}/lockerbanks?pageSize=200")
+ end
+
+ # =====================================
+ # BOOKINGS
+ # =====================================
+
+ def bookings(user_id : String)
+ params = URI::Params.build do |form|
+ form.add "externalUserId", user_id
+ form.add "pageSize", "200"
+ end
+ fetch_pages("/api/bookings?#{params}")
+ end
+
+ def bookings_availability(
+ user_id : String,
+ starting : Int64,
+ ending : Int64,
+ section_id : String? = nil,
+ location_id : String? = nil,
+ bank_id : String? = nil,
+ group_id : String? = nil,
+ locker_id : String? = nil
+ )
+ params = URI::Params.build do |form|
+ form.add "externalUserId", user_id
+ form.add "startDateTimeUtc", Time.unix(starting).to_rfc3339
+ form.add "endDateTimeUtc", Time.unix(ending).to_rfc3339
+ form.add "sectionId", section_id.as(String) if section_id.presence
+ form.add "locationId", location_id.as(String) if location_id.presence
+ form.add "lockerBankId", bank_id.as(String) if bank_id.presence
+ form.add "lockerBankId", group_id.as(String) if bank_id.presence && group_id.presence
+ form.add "lockerId", locker_id.as(String) if locker_id.presence
+ form.add "pageSize", "200"
+ end
+ fetch_pages("/api/bookings/availability?#{params}")
+ end
+
+ def book_locker(starting : Int64, ending : Int64, user_id : String, locker_id : String? = nil, group_id : String? = nil, bank_id : String? = nil, timezone : String = "UTC")
+ tz = Time::Location.load(timezone)
+ response = post("/api/bookings", body: {
+ # this seems like a stupid data format? I assume as the locker bank has the timezone?
+ "StartDateTimeUtc" => Time.unix(starting).in(tz).to_s("%m-%d-%Y %H:%M:%S"),
+ "EndDateTimeUtc" => Time.unix(ending).in(tz).to_s("%m-%d-%Y %H:%M:%S"),
+ "LockerGroupId" => group_id,
+ "LockerBankId" => bank_id,
+ "LockerId" => locker_id,
+ "ExternalUserId" => user_id,
+ }.to_json)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ # =====================================
+ # LOCKERS
+ # =====================================
+
+ # the lockers that are currently allocated to the specified user
+ # the user ID is typically email - defined by the client
+ def lockers_allocated_to(user_id : String)
+ params = URI::Params.build do |form|
+ form.add "externalUserId", user_id
+ form.add "pageSize", "200"
+ end
+ fetch_pages("/api/lockers/allocated?#{params}")
+ end
+
+ # check if a user can be allocated a new locker
+ def can_allocate_locker?(user_id : String) : String
+ params = URI::Params.build do |form|
+ form.add "externalUserId", user_id
+ end
+ response = get("/api/lockers/canallocate?#{params}")
+ response.body
+ end
+
+ def locker_allocate(locker_id : String, user_id : String)
+ params = URI::Params.build do |form|
+ form.add "externalUserId", user_id
+ end
+ response = post("/api/lockers/#{locker_id}/allocate?#{params}")
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ def locker_allocate_random(bank_id : String, group_id : String, user_id : String)
+ params = URI::Params.build do |form|
+ form.add "lockerBankId", bank_id
+ form.add "lockerGroupId", group_id
+ form.add "externalUserId", user_id
+ end
+ response = post("/api/lockers/allocate?#{params}")
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ JSON.parse(response.body)
+ end
+
+ def locker_release(locker_id : String, user_id : String? = nil) : Nil
+ params = URI::Params.build do |form|
+ form.add "externalUserId", user_id if user_id.presence
+ end
+ response = post("/api/lockers/#{locker_id}/release?#{params}")
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ end
+
+ def locker_unlock(locker_id : String, pin_code : String? = nil)
+ pin_route = pin_code ? nil : "/withoutpincode"
+ response = post("/api/lockers/#{locker_id}/pincode/unlock#{pin_route}", body: pin_code)
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ end
+
+ # =====================================
+ # SHARING
+ # =====================================
+
+ def share_locker_with(locker_id : String, owner_id : String, user_id : String) : Bool
+ params = URI::Params.build do |form|
+ form.add "externalUserId", owner_id
+ form.add "sharedUserId", user_id
+ end
+ response = post("/api/lockers/#{locker_id}/share?#{params}")
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ true
+ end
+
+ def unshare_locker(locker_id : String, owner_id : String, shared_with_internal_id : String? = nil) : Bool
+ params = URI::Params.build do |form|
+ form.add "externalUserId", owner_id
+ end
+ response = post("/api/lockers/#{locker_id}/unshare/#{shared_with_internal_id}?#{params}")
+ raise "unexpected response #{response.status_code}\n#{response.body}" unless response.success?
+ true
+ end
+
+ def can_share_locker_with?(locker_id : String, owner_id : String, search : String)
+ params = URI::Params.build do |form|
+ form.add "externalUserId", owner_id
+ form.add "searchString", search
+ end
+ Array(LockerUsers).from_json(fetch_item("/api/lockers/#{locker_id}/shareablelockerusers?#{params}"), root: "LockerUsers")
+ end
+
+ def locker_shared_with?(locker_id : String, owner_id : String)
+ params = URI::Params.build do |form|
+ form.add "externalUserId", owner_id
+ end
+ Array(LockerUsers).from_json(fetch_item("/api/lockers/#{locker_id}/shareablelockerusers?#{params}"), root: "LockerUsers")
+ end
+end
diff --git a/drivers/vecos/releezme/allocation.cr b/drivers/vecos/releezme/allocation.cr
new file mode 100644
index 00000000000..6bb593c92fb
--- /dev/null
+++ b/drivers/vecos/releezme/allocation.cr
@@ -0,0 +1,35 @@
+require "json"
+
+module Vecos
+ struct Allocation
+ include JSON::Serializable
+
+ # This is the internal user_id - not the user email etc
+ @[JSON::Field(key: "UserId")]
+ getter user_id : String
+
+ @[JSON::Field(key: "LockerId")]
+ getter locker_id : String
+
+ @[JSON::Field(key: "SelfReleaseAllowed")]
+ getter? self_releasable : Bool
+
+ @[JSON::Field(key: "DynamicAllocated")]
+ getter? dynamically_allocated : Bool
+
+ @[JSON::Field(key: "StartDateTimeUtc")]
+ getter starting : Time
+
+ @[JSON::Field(key: "ExpiresDateTimeUtc")]
+ getter expiring : Time
+
+ @[JSON::Field(key: "SharedToUser")]
+ getter? shared_to_user : Bool
+
+ @[JSON::Field(key: "AllocatedForPackage")]
+ getter? allocated_for_package : Bool
+
+ @[JSON::Field(key: "AllocatedByLockerActionOnRelease")]
+ getter? allocated_by_locker_action_on_release : Bool
+ end
+end
diff --git a/drivers/vecos/releezme/booking.cr b/drivers/vecos/releezme/booking.cr
new file mode 100644
index 00000000000..7a84389616f
--- /dev/null
+++ b/drivers/vecos/releezme/booking.cr
@@ -0,0 +1,28 @@
+require "json"
+
+module Vecos
+ struct Booking
+ include JSON::Serializable
+
+ @[JSON::Field(key: "BookingId")]
+ getter id : String
+
+ @[JSON::Field(key: "LockerId")]
+ getter locker_id : String
+
+ @[JSON::Field(key: "LockerBankId")]
+ getter locker_bank_id : String
+
+ @[JSON::Field(key: "LockerGroupId")]
+ getter locker_group_id : String
+
+ @[JSON::Field(key: "FullDoorNumber")]
+ getter full_door_number : String
+
+ @[JSON::Field(key: "StartDateTimeUtc")]
+ getter starting : Time
+
+ @[JSON::Field(key: "EndDateTimeUtc")]
+ getter ending : Time
+ end
+end
diff --git a/drivers/vecos/releezme/location.cr b/drivers/vecos/releezme/location.cr
new file mode 100644
index 00000000000..ac3671bb9ac
--- /dev/null
+++ b/drivers/vecos/releezme/location.cr
@@ -0,0 +1,16 @@
+require "json"
+
+module Vecos
+ struct Location
+ include JSON::Serializable
+
+ @[JSON::Field(key: "Id")]
+ getter id : String
+
+ @[JSON::Field(key: "Name")]
+ getter name : String
+
+ @[JSON::Field(key: "TimeZoneId")]
+ getter time_zone : String? = nil
+ end
+end
diff --git a/drivers/vecos/releezme/locker.cr b/drivers/vecos/releezme/locker.cr
new file mode 100644
index 00000000000..c5b8236f807
--- /dev/null
+++ b/drivers/vecos/releezme/locker.cr
@@ -0,0 +1,70 @@
+require "json"
+
+module Vecos
+ struct Locker
+ include JSON::Serializable
+
+ @[JSON::Field(key: "Id")]
+ getter id : String
+
+ @[JSON::Field(key: "LockerGroupId")]
+ getter locker_group_id : String
+
+ @[JSON::Field(key: "LockerBankId")]
+ getter locker_bank_id : String
+
+ @[JSON::Field(key: "LockerBrickId")]
+ getter locker_brick_id : String
+
+ @[JSON::Field(key: "Blocked")]
+ getter blocked : Bool
+
+ @[JSON::Field(key: "IsUsable")]
+ getter is_usable : Bool
+
+ @[JSON::Field(key: "IsDetected")]
+ getter is_detected : Bool
+
+ @[JSON::Field(key: "FullDoorNumber")]
+ getter full_door_number : String
+
+ @[JSON::Field(key: "DoorNumberPrefix")]
+ getter door_number_prefix : String
+
+ @[JSON::Field(key: "DoorNumber")]
+ getter door_number : Int32
+
+ @[JSON::Field(key: "SelfReleaseAllowed")]
+ getter self_release_allowed : Bool?
+
+ @[JSON::Field(key: "DynamicAllocated")]
+ getter dynamic_allocated : Bool?
+
+ @[JSON::Field(key: "OpenTime")]
+ getter open_time : Int32
+
+ @[JSON::Field(key: "NrOfAllocations")]
+ getter number_of_allocations : Int32?
+
+ @[JSON::Field(key: "SharedToUser")]
+ getter shared_to_user : Bool?
+
+ @[JSON::Field(key: "IsShared")]
+ getter is_shared : Bool?
+
+ @[JSON::Field(key: "IsShareable")]
+ getter is_shareable : Bool?
+
+ @[JSON::Field(key: "SequenceNumber")]
+ getter sequence_number : Int32
+
+ @[JSON::Field(key: "ExpiresDateTimeUtc")]
+ getter expires_date_time_utc : Time?
+
+ @[JSON::Field(key: "StartDateTimeUtc")]
+ getter start_date_time_utc : Time?
+
+ @[JSON::Field(key: "NumberOfDigitsForDoorNumber")]
+ getter number_of_digits_for_door_number : Int32
+ end
+end
diff --git a/drivers/vecos/releezme/locker_bank.cr b/drivers/vecos/releezme/locker_bank.cr
new file mode 100644
index 00000000000..133de99ea77
--- /dev/null
+++ b/drivers/vecos/releezme/locker_bank.cr
@@ -0,0 +1,31 @@
+require "json"
+
+module Vecos
+ struct LockerBank
+ include JSON::Serializable
+
+ @[JSON::Field(key: "Id")]
+ getter id : String
+
+ @[JSON::Field(key: "Name")]
+ getter name : String
+
+ @[JSON::Field(key: "SectionId")]
+ getter section_id : String
+
+ @[JSON::Field(key: "LocationId")]
+ getter location_id : String?
+
+ @[JSON::Field(key: "Published")]
+ getter published : Bool
+
+ @[JSON::Field(key: "RandomAllocation")]
+ getter random_allocation : Bool?
+
+ @[JSON::Field(key: "ServiceMode")]
+ getter service_mode : Bool
+
+ @[JSON::Field(key: "Description")]
+ getter description : String?
+ end
+end
diff --git a/drivers/vecos/releezme/locker_bank_and_locker_group.cr b/drivers/vecos/releezme/locker_bank_and_locker_group.cr
new file mode 100644
index 00000000000..9002aacacb3
--- /dev/null
+++ b/drivers/vecos/releezme/locker_bank_and_locker_group.cr
@@ -0,0 +1,14 @@
+require "./locker_bank"
+require "./locker_group"
+
+module Vecos
+ struct LockerBankAndLockerGroup
+ include JSON::Serializable
+
+ @[JSON::Field(key: "LockerBank")]
+ getter locker_bank : LockerBank
+
+ @[JSON::Field(key: "LockerGroup")]
+ getter locker_group : LockerGroup
+ end
+end
diff --git a/drivers/vecos/releezme/locker_group.cr b/drivers/vecos/releezme/locker_group.cr
new file mode 100644
index 00000000000..ff3fc7f0db2
--- /dev/null
+++ b/drivers/vecos/releezme/locker_group.cr
@@ -0,0 +1,22 @@
+require "json"
+
+module Vecos
+ struct LockerGroup
+ include JSON::Serializable
+
+ @[JSON::Field(key: "Id")]
+ getter id : String
+
+ @[JSON::Field(key: "Name")]
+ getter name : String
+
+ @[JSON::Field(key: "LockMode")]
+ getter lock_mode : Int32
+
+ @[JSON::Field(key: "LockerBookingFeatureEnabled")]
+ getter locker_booking_feature_enabled : Bool
+
+ @[JSON::Field(key: "PostalServiceFeatureEnabled")]
+ getter postal_service_feature_enabled : Bool
+ end
+end
diff --git a/drivers/vecos/releezme/locker_group_status.cr b/drivers/vecos/releezme/locker_group_status.cr
new file mode 100644
index 00000000000..8f8845c3060
--- /dev/null
+++ b/drivers/vecos/releezme/locker_group_status.cr
@@ -0,0 +1,46 @@
+require "json"
+
+module Vecos
+ struct LockerGroupStatus
+ include JSON::Serializable
+
+ @[JSON::Field(key: "LockerGroupId")]
+ getter locker_group_id : String
+
+ @[JSON::Field(key: "LockerGroupName")]
+ getter locker_group_name : String
+
+ @[JSON::Field(key: "UsableLockers")]
+ getter usable_lockers : Int32
+
+ @[JSON::Field(key: "UnusableLockers")]
+ getter unusable_lockers : Int32
+
+ @[JSON::Field(key: "PublicLockers")]
+ getter public_lockers : Int32
+
+ @[JSON::Field(key: "AvailableDynamicLockers")]
+ getter available_dynamic_lockers : Int32
+
+ @[JSON::Field(key: "AllocatedDynamicLockers")]
+ getter allocated_dynamic_lockers : Int32
+
+ @[JSON::Field(key: "BlockedAllocatedDynamicLockers")]
+ getter blocked_allocated_dynamic_lockers : Int32
+
+ @[JSON::Field(key: "BlockedUnallocatedDynamicLockers")]
+ getter blocked_unallocated_dynamic_lockers : Int32
+
+ @[JSON::Field(key: "AvailableStaticLockers")]
+ getter available_static_lockers : Int32
+
+ @[JSON::Field(key: "AllocatedStaticLockers")]
+ getter allocated_static_lockers : Int32
+
+ @[JSON::Field(key: "BlockedAllocatedStaticLockers")]
+ getter blocked_allocated_static_lockers : Int32
+
+ @[JSON::Field(key: "BlockedUnallocatedStaticLockers")]
+ getter blocked_unallocated_static_lockers : Int32
+ end
+end
diff --git a/drivers/vecos/releezme/locker_users.cr b/drivers/vecos/releezme/locker_users.cr
new file mode 100644
index 00000000000..6d7226fe4ca
--- /dev/null
+++ b/drivers/vecos/releezme/locker_users.cr
@@ -0,0 +1,22 @@
+require "json"
+
+module Vecos
+ struct LockerUsers
+ include JSON::Serializable
+
+ @[JSON::Field(key: "Id")]
+ getter id : String
+
+ @[JSON::Field(key: "FirstName")]
+ getter first_name : String?
+
+ @[JSON::Field(key: "LastName")]
+ getter last_name : String?
+
+ @[JSON::Field(key: "EmailAddress")]
+ getter email : String?
+
+ @[JSON::Field(key: "ExternalUserId")]
+ getter user_id : String
+ end
+end
diff --git a/drivers/vecos/releezme/paging.cr b/drivers/vecos/releezme/paging.cr
new file mode 100644
index 00000000000..7eaa9affe74
--- /dev/null
+++ b/drivers/vecos/releezme/paging.cr
@@ -0,0 +1,37 @@
+require "json"
+
+module Vecos
+ struct Paging
+ include JSON::Serializable
+
+ @[JSON::Field(key: "FirstItemOnPage")]
+ getter first_item_on_page : Int32
+
+ @[JSON::Field(key: "HasNextPage")]
+ getter has_next_page : Bool
+
+ @[JSON::Field(key: "HasPreviousPage")]
+ getter has_previous_page : Bool
+
+ @[JSON::Field(key: "IsFirstPage")]
+ getter is_first_page : Bool
+
+ @[JSON::Field(key: "IsLastPage")]
+ getter is_last_page : Bool
+
+ @[JSON::Field(key: "LastItemOnPage")]
+ getter last_item_on_page : Int32
+
+ @[JSON::Field(key: "PageCount")]
+ getter page_count : Int32
+
+ @[JSON::Field(key: "PageNumber")]
+ getter page_number : Int32
+
+ @[JSON::Field(key: "PageSize")]
+ getter page_size : Int32
+
+ @[JSON::Field(key: "TotalItemCount")]
+ getter total_item_count : Int32
+ end
+end
diff --git a/drivers/vecos/releezme/section.cr b/drivers/vecos/releezme/section.cr
new file mode 100644
index 00000000000..73aca27dbea
--- /dev/null
+++ b/drivers/vecos/releezme/section.cr
@@ -0,0 +1,16 @@
+require "json"
+
+module Vecos
+ struct Section
+ include JSON::Serializable
+
+ @[JSON::Field(key: "Id")]
+ getter id : String
+
+ @[JSON::Field(key: "Name")]
+ getter name : String
+
+ @[JSON::Field(key: "LocationId")]
+ getter location_id : String
+ end
+end
diff --git a/drivers/vecos/releezme_locations.cr b/drivers/vecos/releezme_locations.cr
new file mode 100644
index 00000000000..06f1f0e7f30
--- /dev/null
+++ b/drivers/vecos/releezme_locations.cr
@@ -0,0 +1,307 @@
+require "placeos-driver"
+require "placeos-driver/interface/lockers"
+require "placeos-driver/interface/locatable"
+require "./releezme/*"
+
+class Vecos::ReleezmeLocations < PlaceOS::Driver
+ include Interface::Locatable
+ include Interface::Lockers
+
+ alias PlaceLocker = PlaceOS::Driver::Interface::Lockers::PlaceLocker
+
+ descriptive_name "Vecos Locker Locations"
+ generic_name :LockerLocations
+
+ accessor staff_api : StaffAPI_1
+ accessor releezme : ReleezmeLockers_1
+
+ default_settings({
+ # the users id
+ user_id_key: "email",
+ vecos_floor_mappings: {
+ "placeos_zone_id": {
+ section_id: "level",
+ name: "friendly name for documentation",
+ },
+ },
+ door_number_lookup: false,
+ })
+
+ def on_update
+ @door_number_lookup = setting?(Bool, :door_number_lookup) || false
+ @user_id_key = setting?(String, :user_id_key) || "email"
+ @floor_mappings = setting(Hash(String, Mapping), :vecos_floor_mappings).transform_values(&.section_id)
+ @zone_filter = @floor_mappings.keys
+ @building_id = nil
+
+ if @door_number_lookup
+ schedule.clear
+ schedule.in(rand(10).seconds) do
+ @floor_mappings.each_key do |zone_id|
+ device_locations(zone_id)
+ end
+ end
+ end
+ end
+
+ # place_zone_id => releexme_section_id
+ @floor_mappings : Hash(String, String) = {} of String => String
+ @zone_filter : Array(String) = [] of String
+ @user_id_key : String = "email"
+ @door_number_lookup : Bool = false
+ @last_mapped : Time = 4.hours.ago
+
+ struct Mapping
+ include JSON::Serializable
+ getter section_id : String
+ end
+
+ # Finds the building ID for the current location services object
+ def get_building_id
+ zone_ids = staff_api.zones(tags: "building").get.as_a.map(&.[]("id").as_s)
+ (zone_ids & system.zones).first
+ rescue error
+ logger.warn(exception: error) { "unable to determine building zone id" }
+ raise error
+ end
+
+ getter building_id : String { get_building_id }
+
+ def lookup_id(locker_id : String) : String
+ if @door_number_lookup
+ status?(String, locker_id.downcase) || locker_id
+ else
+ locker_id
+ end
+ end
+
+ # ========================================
+ # Lockers Interface
+ # ========================================
+
+ class PlaceLocker
+ def initialize(
+ locker : Vecos::Locker,
+ allocated : Bool = false,
+ @building = nil,
+ @level = nil
+ )
+ @locker_uid = locker.id
+ @locker_id = locker.full_door_number
+ @bank_id = locker.locker_bank_id
+ @group_id = locker.locker_group_id
+ @locker_name = locker.full_door_number
+ @expires_at = locker.expires_date_time_utc
+ @allocated = if allocations = locker.number_of_allocations
+ (allocations > 0) || allocated
+ else
+ allocated
+ end
+ end
+
+ def initialize(booking : Vecos::Booking)
+ @locker_uid = booking.locker_id
+ @locker_id = booking.full_door_number
+ @bank_id = booking.locker_bank_id
+ @group_id = booking.locker_group_id
+ @locker_name = booking.full_door_number
+ @expires_at = booking.ending
+ @allocated = true
+ @allocation_id = booking.id
+ end
+
+ getter group_id : String? = nil
+ getter locker_uid : String? = nil
+ end
+
+ protected def get_group_id(user_id, bank_id)
+ section_id = releezme.bank(bank_id).get["SectionId"].as_s
+ groups = Array(LockerBankAndLockerGroup).from_json releezme.section_banks_allocatable(section_id, user_id).get.to_json
+ group = groups.find { |group| group.locker_bank.id == bank_id }
+ raise "there are no lockers available to the user in the selected locker bank" unless group
+ group.locker_group.id
+ end
+
+ protected def get_user_key(user_id)
+ return user_id.downcase if @user_id_key == "email" && user_id.includes?("@")
+ user = staff_api.user(user_id).get
+ user[@user_id_key].as_s
+ end
+
+ # allocates a locker now, the allocation may expire
+ @[Security(Level::Administrator)]
+ def locker_allocate(
+ # PlaceOS user id, recommend using email
+ user_id : String,
+
+ # the locker location
+ bank_id : String | Int64,
+
+ # allocates a random locker if this is nil
+ locker_id : String | Int64? = nil,
+
+ # attempts to create a booking that expires at the time specified
+ expires_at : Int64? = nil
+ ) : PlaceLocker
+ user_id = get_user_key(user_id)
+ locker_id = locker_id ? lookup_id(locker_id.to_s) : nil
+
+ if expires_at
+ timezone = system.timezone || "UTC"
+ booking = if locker_id
+ releezme.book_locker(1.minute.ago.to_unix, expires_at, user_id, locker_id, timezone: timezone).get
+ else
+ group_id = get_group_id(user_id, bank_id)
+ releezme.book_locker(1.minute.ago.to_unix, expires_at, user_id, group_id: group_id, bank_id: bank_id, timezone: timezone).get
+ end
+ PlaceLocker.new(Vecos::Booking.from_json booking.to_json)
+ elsif locker_id
+ vlocker = Vecos::Locker.from_json releezme.locker_allocate(locker_id, user_id).get.to_json
+ PlaceLocker.new(vlocker, true)
+ else
+ group_id = get_group_id(user_id, bank_id)
+ vlocker = Vecos::Locker.from_json releezme.locker_allocate_random(bank_id, group_id, user_id).get.to_json
+ PlaceLocker.new(vlocker, true)
+ end
+ end
+
+ # return the locker to the pool
+ @[Security(Level::Administrator)]
+ def locker_release(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+
+ # release / unshare just this user - otherwise release the whole locker
+ owner_id : String? = nil
+ ) : Nil
+ locker_id = lookup_id(locker_id.to_s)
+ owner_id = get_user_key(owner_id) if owner_id
+ releezme.locker_release(locker_id, owner_id).get
+ end
+
+ # a list of lockers that are allocated to the user
+ @[Security(Level::Administrator)]
+ def lockers_allocated_to(user_id : String) : Array(PlaceLocker)
+ user_id = get_user_key user_id
+ lockers = Array(Vecos::Locker).from_json releezme.lockers_allocated_to(user_id).get.to_json
+ lockers.map { |locker| PlaceLocker.new(locker, true) }
+ end
+
+ @[Security(Level::Administrator)]
+ def locker_share(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+ owner_id : String,
+ share_with : String
+ ) : Nil
+ locker_id = lookup_id(locker_id.to_s)
+ releezme.share_locker_with(locker_id, get_user_key(owner_id), get_user_key(share_with)).get
+ end
+
+ @[Security(Level::Administrator)]
+ def locker_unshare(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+ owner_id : String,
+ # the individual you previously shared with
+ shared_with_id : String? = nil
+ ) : Nil
+ owner_id = get_user_key(owner_id)
+ locker_id = lookup_id(locker_id.to_s)
+
+ # we need the internal id if we want to unshare an individual
+ if shared_with_id
+ shared_with_external_id = get_user_key(shared_with_id)
+ shared_with = Array(Vecos::LockerUsers).from_json releezme.locker_shared_with?(locker_id, owner_id).get.to_json
+ shared_user = shared_with.find { |user| user.user_id == shared_with_external_id }
+ return unless shared_user
+ shared_with_id = shared_user.id
+ end
+ releezme.unshare_locker(locker_id, owner_id, shared_with_id).get
+ end
+
+ # a list of user-ids that the locker is shared with.
+ # this can be placeos user ids or emails
+ @[Security(Level::Administrator)]
+ def locker_shared_with(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+ owner_id : String
+ ) : Array(String)
+ owner_id = get_user_key(owner_id)
+ locker_id = lookup_id(locker_id.to_s)
+ shared_with = Array(Vecos::LockerUsers).from_json releezme.locker_shared_with?(locker_id, owner_id).get.to_json
+ shared_with.map { |user| user.email || user.user_id }
+ end
+
+ @[Security(Level::Administrator)]
+ def locker_unlock(
+ bank_id : String | Int64,
+ locker_id : String | Int64,
+
+ # sometimes required by locker systems
+ owner_id : String? = nil,
+ # time in seconds the locker should be unlocked
+ # (can be ignored if not implemented)
+ open_time : Int32 = 60,
+ # optional pin code - if user entered from a kiosk
+ pin_code : String? = nil
+ ) : Nil
+ locker_id = lookup_id(locker_id.to_s)
+ releezme.locker_unlock(locker_id, pin_code).get
+ end
+
+ # ========================================
+ # Locatable Interface
+ # ========================================
+
+ # array of devices and their x, y coordinates, that are associated with this user
+ def locate_user(email : String? = nil, username : String? = nil)
+ logger.debug { "releezme incapable of locating #{email} or #{username}" }
+ [] of Nil
+ end
+
+ # return an array of MAC address strings
+ # lowercase with no seperation characters abcdeffd1234 etc
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ logger.debug { "releezme incapable of tracking #{email} or #{username}" }
+ [] of String
+ end
+
+ # return `nil` or `{"location": "wireless", "assigned_to": "bob123", "mac_address": "abcd"}`
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ logger.debug { "releezme incapable of tracking #{mac_address}" }
+ nil
+ end
+
+ # array of lockers on this level
+ def device_locations(zone_id : String, location : String? = nil)
+ logger.debug { "searching for lockers in zone #{zone_id}" }
+
+ if building_id == zone_id
+ return @zone_filter.flat_map { |level_id| device_locations(level_id, location) }
+ end
+ return [] of Nil unless @zone_filter.includes?(zone_id)
+
+ # grab all the lockers for the current zone_id
+ releexme_section_id = @floor_mappings[zone_id]
+ banks = Array(Vecos::LockerBank).from_json releezme.section_locker_banks(releexme_section_id).get.to_json
+
+ if @door_number_lookup && @last_mapped < 3.hour.ago
+ # periodically save the locker name => id mappings in redis
+ @last_mapped = Time.utc
+ banks.flat_map do |bank|
+ lockers = Array(Vecos::Locker).from_json releezme.bank_lockers(bank.id).get.to_json
+ lockers.map do |locker|
+ self[locker.full_door_number.downcase] = locker.id
+ PlaceLocker.new(locker, building: building_id, level: zone_id)
+ end
+ end
+ else
+ banks.flat_map do |bank|
+ lockers = Array(Vecos::Locker).from_json releezme.bank_lockers(bank.id).get.to_json
+ lockers.map { |locker| PlaceLocker.new(locker, building: building_id, level: zone_id) }
+ end
+ end
+ end
+end
diff --git a/drivers/vecos/releezme_locations_spec.cr b/drivers/vecos/releezme_locations_spec.cr
new file mode 100644
index 00000000000..0ae517777aa
--- /dev/null
+++ b/drivers/vecos/releezme_locations_spec.cr
@@ -0,0 +1,4 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Vecos::ReleezmeLocations" do
+end
diff --git a/drivers/vecos/releezme_spec.cr b/drivers/vecos/releezme_spec.cr
new file mode 100644
index 00000000000..ed059c5da8e
--- /dev/null
+++ b/drivers/vecos/releezme_spec.cr
@@ -0,0 +1,80 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Vecos::Releezme" do
+ resp = exec :locations
+
+ expect_http_request do |request, response|
+ case request.path
+ when "/connect/token"
+ response.status_code = 200
+ response << %({
+ "access_token": "1234",
+ "expires_in": 300
+ })
+ else
+ response.status_code = 500
+ response << "expected token request"
+ end
+ end
+
+ expect_http_request do |request, response|
+ case "#{request.path}?#{request.query}"
+ when "/api/locations?pageSize=200&pageNumber=1"
+ response.status_code = 200
+ response << %({
+ "Locations": [{
+ "Id": "loc-1234",
+ "Name": "Level 2"
+ }],
+ "Paging": {
+ "FirstItemOnPage": 1,
+ "HasNextPage": true,
+ "HasPreviousPage": false,
+ "IsFirstPage": true,
+ "IsLastPage": false,
+ "LastItemOnPage": 1,
+ "PageCount": 2,
+ "PageNumber": 1,
+ "PageSize": 2,
+ "TotalItemCount": 2
+ }
+ })
+ else
+ response.status_code = 500
+ response << "expected locations request"
+ end
+ end
+
+ expect_http_request do |request, response|
+ case "#{request.path}?#{request.query}"
+ when "/api/locations?pageSize=200&pageNumber=2"
+ response.status_code = 200
+ response << %({
+ "Locations": [{
+ "Id": "loc-5678",
+ "Name": "Level 3"
+ }],
+ "Paging": {
+ "FirstItemOnPage": 1,
+ "HasNextPage": false,
+ "HasPreviousPage": true,
+ "IsFirstPage": false,
+ "IsLastPage": true,
+ "LastItemOnPage": 1,
+ "PageCount": 2,
+ "PageNumber": 2,
+ "PageSize": 2,
+ "TotalItemCount": 2
+ }
+ })
+ else
+ response.status_code = 500
+ response << "expected locations request"
+ end
+ end
+
+ resp.get.should eq [
+ {"Id" => "loc-1234", "Name" => "Level 2"},
+ {"Id" => "loc-5678", "Name" => "Level 3"},
+ ]
+end
diff --git a/drivers/vergesense/location_service.cr b/drivers/vergesense/location_service.cr
new file mode 100644
index 00000000000..aceae678728
--- /dev/null
+++ b/drivers/vergesense/location_service.cr
@@ -0,0 +1,258 @@
+require "json"
+require "oauth2"
+require "placeos-driver"
+require "placeos-driver/interface/locatable"
+require "placeos-driver/interface/sensor"
+require "./models"
+
+class Vergesense::LocationService < PlaceOS::Driver
+ include Interface::Locatable
+ include Interface::Sensor
+
+ descriptive_name "Vergesense Location Service"
+ generic_name :VergesenseLocationService
+ description %(collects desk booking data from the staff API and overlays Vergesense data for visualising on a map)
+
+ accessor area_manager : AreaManagement_1
+ accessor vergesense : Vergesense_1
+
+ default_settings({
+ floor_mappings: {
+ "vergesense_building_id-floor_id": {
+ building_id: "zone-building",
+ level_id: "zone-level",
+ name: "friendly name for documentation",
+ },
+ },
+ return_empty_spaces: true,
+ desk_space_types: ["desk"],
+ notify_updates: false,
+ })
+
+ @floor_mappings : Hash(String, NamedTuple(building_id: String?, level_id: String)) = {} of String => NamedTuple(building_id: String?, level_id: String)
+ @zone_filter : Array(String) = [] of String
+ @building_mappings : Hash(String, String?) = {} of String => String?
+ @desk_space_types : Array(String) = ["desk"]
+ @notify_updates : Bool = false
+
+ def on_update
+ @return_empty_spaces = setting?(Bool, :return_empty_spaces) || false
+ @notify_updates = setting?(Bool, :notify_updates) || false
+ @desk_space_types = setting?(Array(String), :desk_space_types) || ["desk"]
+ @floor_mappings = setting(Hash(String, NamedTuple(building_id: String?, level_id: String)), :floor_mappings)
+ @zone_filter = @floor_mappings.values.map do |z|
+ level = z[:level_id]
+ @building_mappings[level] = z[:building_id]
+ level
+ end
+
+ bind_floor_status
+ end
+
+ # ===================================
+ # Bindings into Vergesense data
+ # ===================================
+ protected def bind_floor_status
+ subscriptions.clear
+
+ @floor_mappings.each do |floor_id, details|
+ zone_id = details[:level_id]
+ vergesense.subscribe(floor_id) do |_sub, payload|
+ level_state_change(zone_id, Floor.from_json(payload))
+ end
+ end
+ end
+
+ # Zone_id => Floor
+ @occupancy_mappings : Hash(String, Floor) = {} of String => Floor
+
+ protected def level_state_change(zone_id, floor)
+ @occupancy_mappings[zone_id] = floor
+ area_manager.update_available({zone_id}) if @notify_updates
+ rescue error
+ logger.error(exception: error) { "error updating level #{zone_id} space changes" }
+ end
+
+ # ===================================
+ # Locatable Interface functions
+ # ===================================
+ def locate_user(email : String? = nil, username : String? = nil)
+ logger.debug { "sensor incapable of locating #{email} or #{username}" }
+ [] of Nil
+ end
+
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ logger.debug { "sensor incapable of tracking #{email} or #{username}" }
+ [] of String
+ end
+
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ logger.debug { "sensor incapable of tracking #{mac_address}" }
+ nil
+ end
+
+ def device_locations(zone_id : String, location : String? = nil)
+ logger.debug { "searching locatable in zone #{zone_id}" }
+ return [] of Nil unless @zone_filter.includes?(zone_id)
+
+ floor = @occupancy_mappings[zone_id]?
+ return [] of Nil unless floor
+
+ desk_types = @desk_space_types
+ floor.spaces.compact_map do |space|
+ loc_type = space.space_type.in?(desk_types) ? "desk" : "area"
+ next if location.presence && location != loc_type
+
+ people_count = space.people.try(&.count)
+
+ if @return_empty_spaces || people_count && people_count > 0
+ if env = space.environment
+ humidity = env.humidity.value
+ temperature = env.temperature.value
+ iaq = env.iaq.try &.value
+ end
+
+ {
+ location: loc_type,
+ at_location: people_count || 0,
+ map_id: space.name,
+ level: zone_id,
+ building: @building_mappings[zone_id]?,
+ capacity: space.capacity,
+
+ vergesense_space_id: space.ref_id,
+ vergesense_space_type: space.space_type,
+ area_humidity: humidity,
+ area_temperature: temperature,
+ area_air_quality: iaq,
+ signs_of_life: space.signs_of_life,
+ }
+ end
+ end
+ end
+
+ # ===================================
+ # Sensor Interface functions
+ # ===================================
+ def sensor(mac : String, id : String? = nil) : Detail?
+ logger.debug { "sensor mac: #{mac}, id: #{id} requested" }
+ return nil unless id
+
+ # https://crystal-lang.org/api/1.1.0/String.html#rpartition(search:Char%7CString):Tuple(String,String,String)-instance-method
+ zone_id, _, space_id = mac.rpartition('-')
+ return nil if zone_id.empty? || space_id.empty?
+
+ floor = @occupancy_mappings[zone_id]?
+ return nil unless floor
+
+ floor_space = floor.spaces.find { |space| space.ref_id == space_id }
+ return nil unless floor_space
+
+ case id
+ when "people"
+ build_sensor_details(zone_id, floor, floor_space, :people_count)
+ when "presence"
+ build_sensor_details(zone_id, floor, floor_space, :presence)
+ when "humidity"
+ build_sensor_details(zone_id, floor, floor_space, :humidity)
+ when "temp"
+ build_sensor_details(zone_id, floor, floor_space, :temperature)
+ when "air"
+ build_sensor_details(zone_id, floor, floor_space, :air_quality)
+ end
+ rescue error
+ logger.warn(exception: error) { "checking for sensor" }
+ nil
+ end
+
+ SENSOR_TYPES = {SensorType::PeopleCount, SensorType::Presence, SensorType::Humidity, SensorType::Temperature, SensorType::AirQuality}
+ NO_MATCH = [] of Interface::Sensor::Detail
+
+ def sensors(type : String? = nil, mac : String? = nil, zone_id : String? = nil) : Array(Detail)
+ logger.debug { "sensors of type: #{type}, mac: #{mac}, zone_id: #{zone_id} requested" }
+
+ if type
+ sensor_type = SensorType.parse(type)
+ return NO_MATCH unless SENSOR_TYPES.includes?(sensor_type)
+ end
+
+ if mac
+ level_zone, _, space_id = mac.rpartition('-')
+ return NO_MATCH if zone_id && zone_id != level_zone || space_id.empty?
+ zone_id = level_zone
+ end
+
+ return NO_MATCH if zone_id && !@occupancy_mappings.has_key?(zone_id)
+
+ if space_id
+ floor = @occupancy_mappings[zone_id]
+ floor_space = floor.spaces.find { |space| space.ref_id == space_id }
+ return NO_MATCH unless floor_space
+ spaces = [{zone_id, floor, floor_space}]
+ elsif zone_id
+ floor = @occupancy_mappings[zone_id]
+ spaces = floor.spaces.map { |space| {zone_id, floor, space} }
+ else
+ spaces = @occupancy_mappings.flat_map { |(zone, floor)|
+ floor.spaces.map { |space| {zone, floor, space} }
+ }
+ end
+
+ if sensor_type
+ spaces.compact_map { |(zone, floor, space)| build_sensor_details(zone.not_nil!, floor, space, sensor_type) }
+ else
+ spaces.flat_map { |(zone, floor, space)| space_sensors(zone.not_nil!, floor, space) }.compact
+ end
+ end
+
+ protected def build_sensor_details(zone_id : String, floor : Vergesense::Floor, space : Vergesense::Space, sensor : SensorType) : Detail?
+ time = space.timestamp
+ id = "people"
+ limit_high = nil
+ value = case sensor
+ when .people_count?
+ limit_high = (space.max_capacity || space.capacity).try &.to_f64
+ space.people.try &.count.try &.to_f64
+ when .presence?
+ id = "presence"
+ space.people.try &.count.try { |count| count > 0 ? 1.0 : 0.0 } || 0.0
+ when .humidity?
+ id = "humidity"
+ time = space.environment.try &.timestamp
+ space.environment.try &.humidity.value
+ when .temperature?
+ id = "temp"
+ time = space.environment.try &.timestamp
+ space.environment.try &.temperature.value
+ when .air_quality?
+ id = "air"
+ time = space.environment.try &.timestamp
+ space.environment.try(&.iaq.try(&.value))
+ else
+ raise "sensor type unavailable: #{sensor}"
+ end
+ return nil unless value
+
+ detail = Detail.new(
+ type: sensor,
+ value: value,
+ last_seen: (time || Time.utc).to_unix,
+ mac: "#{zone_id}-#{space.ref_id}",
+ id: id,
+ name: "#{floor.name} #{space.name} (#{space.space_type})",
+ limit_high: limit_high
+ )
+ detail.level = zone_id
+ detail
+ end
+
+ protected def space_sensors(zone_id : String, floor : Vergesense::Floor, space : Vergesense::Space)
+ [
+ build_sensor_details(zone_id, floor, space, :people_count),
+ build_sensor_details(zone_id, floor, space, :presence),
+ build_sensor_details(zone_id, floor, space, :humidity),
+ build_sensor_details(zone_id, floor, space, :temperature),
+ build_sensor_details(zone_id, floor, space, :air_quality),
+ ].compact!
+ end
+end
diff --git a/drivers/vergesense/location_service_spec.cr b/drivers/vergesense/location_service_spec.cr
new file mode 100644
index 00000000000..fed5f031f19
--- /dev/null
+++ b/drivers/vergesense/location_service_spec.cr
@@ -0,0 +1,94 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Vergesense::LocationService" do
+ system({
+ Vergesense: {VergesenseMock},
+ AreaManagement: {AreaManagementMock},
+ })
+
+ resp = exec(:device_locations, "zone-level").get
+ resp.should eq([
+ {
+ "location" => "area",
+ "at_location" => 21,
+ "map_id" => "Conference Room 0721",
+ "level" => "zone-level",
+ "building" => "zone-building",
+ "capacity" => 30,
+ "vergesense_space_id" => "CR_0721",
+ "vergesense_space_type" => "conference_room",
+ "area_humidity" => nil,
+ "area_temperature" => nil,
+ "area_air_quality" => nil,
+ "signs_of_life" => nil,
+ },
+ {
+ "location" => "desk",
+ "at_location" => 1,
+ "map_id" => "desk-1234",
+ "level" => "zone-level",
+ "building" => "zone-building",
+ "capacity" => 1,
+ "vergesense_space_id" => "CR_0722",
+ "vergesense_space_type" => "desk",
+ "area_humidity" => nil,
+ "area_temperature" => nil,
+ "area_air_quality" => nil,
+ "signs_of_life" => nil,
+ },
+ ])
+end
+
+# :nodoc:
+class VergesenseMock < DriverSpecs::MockDriver
+ def on_load
+ self["vergesense_building_id-floor_id"] = {
+ "floor_ref_id" => "floor_id",
+ "name" => "Floor 1",
+ "capacity" => 84,
+ "max_capacity" => 60,
+ "spaces" => [
+ {
+ "building_ref_id" => "vergesense_building_id",
+ "floor_ref_id" => "floor_id",
+ "space_ref_id" => "CR_0721",
+ "space_type" => "conference_room",
+ "name" => "Conference Room 0721",
+ "capacity" => 30,
+ "max_capacity" => 32,
+ "geometry" => {"type" => "Polygon", "coordinates" => [[[93.850772, 44.676952], [93.850739, 44.676929], [93.850718, 44.67695], [93.850751, 44.676973], [93.850772, 44.676952], [93.850772, 44.676952]]]},
+ "people" => {
+ "count" => 21,
+ "coordinates" => [[[2.2673, 4.3891], [6.2573, 1.5303]]],
+ },
+ "timestamp" => "2019-08-21T21:10:25Z",
+ "motion_detected" => true,
+ },
+ {
+ "building_ref_id" => "vergesense_building_id",
+ "floor_ref_id" => "floor_id",
+ "space_ref_id" => "CR_0722",
+ "space_type" => "desk",
+ "name" => "desk-1234",
+ "capacity" => 1,
+ "max_capacity" => 1,
+ "geometry" => {"type" => "Polygon", "coordinates" => [[[93.850772, 44.676952], [93.850739, 44.676929], [93.850718, 44.67695], [93.850751, 44.676973], [93.850772, 44.676952], [93.850772, 44.676952]]]},
+ "people" => {
+ "count" => 1,
+ "coordinates" => [[[2.2673, 4.3891], [6.2573, 1.5303]]],
+ },
+ "timestamp" => "2019-08-21T21:10:25Z",
+ "motion_detected" => true,
+ },
+ ],
+ }
+ end
+end
+
+# :nodoc:
+class AreaManagementMock < DriverSpecs::MockDriver
+ def update_available(zones : Array(String))
+ logger.info { "requested update to #{zones}" }
+ nil
+ end
+end
diff --git a/drivers/vergesense/models.cr b/drivers/vergesense/models.cr
new file mode 100644
index 00000000000..b4053cb02be
--- /dev/null
+++ b/drivers/vergesense/models.cr
@@ -0,0 +1,123 @@
+require "json"
+
+# Vergesense Data Models
+module Vergesense
+ struct Building
+ include JSON::Serializable
+
+ property name : String
+ property building_ref_id : String
+ property address : String?
+ end
+
+ struct BuildingWithFloors
+ include JSON::Serializable
+
+ property building_ref_id : String
+ property floors : Array(Floor)
+ end
+
+ struct Floor
+ include JSON::Serializable
+
+ property floor_ref_id : String
+ property name : String
+ property capacity : UInt32?
+ property max_capacity : UInt32?
+ property spaces : Array(Space)
+ end
+
+ struct Sensor
+ include JSON::Serializable
+
+ property units : String
+ property value : Float64
+ end
+
+ struct Environment
+ include JSON::Serializable
+
+ property sensor : String
+ property timestamp : Time
+
+ property humidity : Sensor
+ property iaq : Sensor?
+ property temperature : Sensor
+ end
+
+ struct Report
+ include JSON::Serializable
+
+ property timestamp : Time
+ property person_count : Int32?
+ property signs_of_life : Bool?
+ end
+
+ struct Pagination
+ include JSON::Serializable
+
+ def initialize
+ @next_page = nil
+ end
+
+ @[JSON::Field(key: "next")]
+ property next_page : String?
+ end
+
+ class Space
+ include JSON::Serializable
+
+ property building_ref_id : String?
+ property floor_ref_id : String?
+ property space_ref_id : String?
+ property space_type : String?
+ property name : String?
+ property capacity : UInt32?
+ property max_capacity : UInt32?
+ # property geometry : Geometry?
+ property people : People?
+ property last_reports : Array(Report)?
+ property environment : Environment?
+ property timestamp : Time?
+ property motion_detected : Bool?
+
+ def signs_of_life? : Bool?
+ if report = last_reports.try &.first?
+ report.signs_of_life if report.timestamp >= 2.hours.ago
+ end
+ end
+
+ def last_report_time? : Time?
+ if report = last_reports.try &.first?
+ report.timestamp
+ elsif env = environment
+ env.timestamp
+ end
+ end
+
+ # NOTE:: not returned by the API, we fill this in
+ property signs_of_life : Bool?
+
+ def floor_key
+ "#{building_ref_id}-#{floor_ref_id}".strip
+ end
+
+ def ref_id
+ self.space_ref_id || self.floor_ref_id || self.space_type
+ end
+ end
+
+ struct Geometry
+ include JSON::Serializable
+
+ property type : String
+ property coordinates : Array(Array(Array(Float64)))
+ end
+
+ struct People
+ include JSON::Serializable
+
+ property count : UInt32?
+ # property coordinates : Array(Array(Float64)?)?
+ end
+end
diff --git a/drivers/vergesense/mqtt_export.cr b/drivers/vergesense/mqtt_export.cr
new file mode 100644
index 00000000000..7b1f12944d9
--- /dev/null
+++ b/drivers/vergesense/mqtt_export.cr
@@ -0,0 +1,64 @@
+require "placeos-driver"
+require "./models"
+
+class Vergesense::MqttExport < PlaceOS::Driver
+ descriptive_name "Vergesense to MQTT Exporter"
+ generic_name :VergesenseToMQTT
+ description %(Export Vergesense people count data to an MQTT consumer)
+
+ accessor vergesense : Vergesense_1
+ accessor mqtt : GenericMQTT_1
+
+ default_settings({
+ mqtt_root_topic: "/t/root-topic/",
+ floors_to_export: [
+ "vergesense_building_id-floor_id",
+ ],
+ debug: false,
+ })
+
+ @mqtt_root_topic : String = "/t/root-topic/"
+ @floors_to_export : Array(String) = [] of String
+ @debug : Bool = false
+
+ @subscriptions : Int32 = 0
+ @previous_counts = Hash(String, UInt32).new
+
+ def on_update
+ @mqtt_root_topic = setting(String, :mqtt_root_topic) || "/t/root-topic"
+ @floors_to_export = setting(Array(String), :floors_to_export) || [] of String
+ @debug = setting(Bool, :debug) || false
+
+ subscriptions.clear
+ @subscriptions = 0
+ @floors_to_export.each do |floor|
+ system.subscribe(:Vergesense_1, floor) do |_subscription, vergesense_floor_json|
+ vergesense_to_mqtt(Floor.from_json(vergesense_floor_json))
+ end
+ @subscriptions += 1
+ end
+ end
+
+ def inspect_state
+ {
+ vergesense_subscriptions: @subscriptions,
+ people_counts: @previous_counts,
+ }
+ end
+
+ private def vergesense_to_mqtt(vergesense_floor : Floor)
+ # Determine which spaces have had their people count change
+ changed_spaces = vergesense_floor.spaces.reject { |s| s.people.try &.count == @previous_counts[s.space_ref_id]? }
+ logger.debug { "#{changed_spaces.size}/#{vergesense_floor.spaces.size} spaces have changed" } if @debug
+ # Publish the new values
+ changed_spaces.each do |s|
+ next unless s.space_ref_id
+ space_id = s.space_ref_id.not_nil!.gsub(/[ \/]/, "")
+ topic = [@mqtt_root_topic, s.building_ref_id, "-", s.floor_ref_id, ".", s.space_type, ".", space_id, ".", "count"].join.downcase
+ # Store the current value, for comparison next time
+ @previous_counts[space_id] = payload = s.people.try &.count || 0_u32
+ mqtt.publish(topic, payload.to_s).get
+ logger.debug { "Published #{payload} to #{topic}" } if @debug
+ end
+ end
+end
diff --git a/drivers/vergesense/room_sensor.cr b/drivers/vergesense/room_sensor.cr
new file mode 100644
index 00000000000..fb3c4ab703d
--- /dev/null
+++ b/drivers/vergesense/room_sensor.cr
@@ -0,0 +1,162 @@
+require "placeos-driver"
+require "placeos-driver/interface/sensor"
+require "./models"
+
+class Vergesense::RoomSensor < PlaceOS::Driver
+ include Interface::Sensor
+
+ # Discovery Information
+ descriptive_name "Vergesense Room Sensor"
+ generic_name :Sensor
+
+ default_settings({
+ space_ref_id: "vergesense-room-id",
+ })
+
+ accessor vergesense : Vergesense_1
+
+ @space_id : String = ""
+ @floor_key : String = ""
+
+ getter! space : Space
+ getter! floor_name : String
+
+ def on_update
+ @space_id = setting(String, :space_ref_id)
+ subscriptions.clear
+ schedule.clear
+
+ # Level sensors
+ system.subscribe(:Vergesense, 1, "init_complete") do |_sub, value|
+ subscribe_to_sensor if value == "true"
+ end
+ end
+
+ protected def subscribe_to_sensor : Nil
+ @floor_key = vergesense.floor_key(@space_id).get.as_s
+ system.subscribe(:Vergesense, 1, @floor_key) { |_sub, floor| update_sensor_state(floor) }
+ self[:floor_key] = @floor_key
+ rescue error
+ schedule.in(15.seconds) { subscribe_to_sensor }
+ logger.warn(exception: error) { "attempting to bind to sensor details" }
+ self[:last_error] = error.message
+ self[:floor_key] = "unknown space_ref_id in settings"
+ end
+
+ protected def update_sensor_state(level : String)
+ floor = Floor.from_json(level)
+ @floor_name = floor.name
+ @space = floor_space = floor.spaces.find { |space| space.space_ref_id == @space_id }
+ raise "space '#{@space_id}' not found" unless floor_space
+
+ self[:last_changed] = Time.utc.to_unix
+
+ people_count = floor_space.people.try &.count
+ if people_count
+ self[:presence] = people_count > 0
+ self[:people] = people_count
+ else
+ self[:presence] = false
+ self[:people] = 0
+ end
+
+ self[:humidity] = floor_space.environment.try &.humidity.value
+ self[:temperature] = floor_space.environment.try &.temperature.value
+ self[:air_quality] = floor_space.environment.try(&.iaq.try(&.value))
+
+ self[:capacity] = floor_space.max_capacity || floor_space.capacity
+ end
+
+ # ======================
+ # Sensor interface
+ # ======================
+
+ SENSOR_TYPES = {SensorType::PeopleCount, SensorType::Presence, SensorType::Humidity, SensorType::Temperature, SensorType::AirQuality}
+ NO_MATCH = [] of Interface::Sensor::Detail
+
+ def sensors(type : String? = nil, mac : String? = nil, zone_id : String? = nil) : Array(Interface::Sensor::Detail)
+ logger.debug { "sensors of type: #{type}, mac: #{mac}, zone_id: #{zone_id} requested" }
+
+ return NO_MATCH if mac && mac != "verg-#{@space_id}"
+ if type
+ sensor_type = SensorType.parse(type)
+ return NO_MATCH unless SENSOR_TYPES.includes?(sensor_type)
+ end
+ return NO_MATCH if zone_id && !system.zones.includes?(zone_id)
+
+ if sensor_type
+ sensor = build_sensor_details(sensor_type)
+ return NO_MATCH unless sensor
+ [sensor]
+ else
+ space_sensors
+ end
+ end
+
+ def sensor(mac : String, id : String? = nil) : Interface::Sensor::Detail?
+ logger.debug { "sensor mac: #{mac}, id: #{id} requested" }
+ return nil unless id
+ return nil unless mac == "verg-#{@space_id}"
+
+ case id
+ when "people"
+ build_sensor_details(:people_count)
+ when "presence"
+ build_sensor_details(:presence)
+ when "humidity"
+ build_sensor_details(:humidity)
+ when "temperature"
+ build_sensor_details(:temperature)
+ when "air_quality"
+ build_sensor_details(:air_quality)
+ end
+ end
+
+ protected def build_sensor_details(sensor : SensorType) : Detail?
+ time = space.timestamp || space.environment.try(&.timestamp) || Time.utc
+ id = "people"
+ limit_high = nil
+ value = case sensor
+ when .people_count?
+ limit_high = (space.max_capacity || space.capacity).try &.to_f64
+ space.people.try &.count.try &.to_f64
+ when .presence?
+ id = "presence"
+ space.people.try &.count.try { |count| count > 0 ? 1.0 : 0.0 } || 0.0
+ when .humidity?
+ id = "humidity"
+ space.environment.try &.humidity.value
+ when .temperature?
+ id = "temperature"
+ space.environment.try &.temperature.value
+ when .air_quality?
+ id = "air_quality"
+ space.environment.try(&.iaq.try(&.value))
+ else
+ raise "sensor type unavailable: #{sensor}"
+ end
+ return nil unless value
+
+ Detail.new(
+ type: sensor,
+ value: value,
+ last_seen: time.to_unix,
+ mac: "verg-#{@space_id}",
+ id: id,
+ name: "#{floor_name} #{space.name} (#{space.space_type})",
+ limit_high: limit_high,
+ module_id: module_id,
+ binding: id
+ )
+ end
+
+ protected def space_sensors
+ [
+ build_sensor_details(:people_count),
+ build_sensor_details(:presence),
+ build_sensor_details(:humidity),
+ build_sensor_details(:temperature),
+ build_sensor_details(:air_quality),
+ ].compact
+ end
+end
diff --git a/drivers/vergesense/room_sensor_spec.cr b/drivers/vergesense/room_sensor_spec.cr
new file mode 100644
index 00000000000..fbe9ece2b75
--- /dev/null
+++ b/drivers/vergesense/room_sensor_spec.cr
@@ -0,0 +1,54 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Vergesense::RoomSensor" do
+ system({
+ Vergesense: {VergesenseMock},
+ })
+
+ sleep 200.milliseconds
+
+ status[:presence].should eq(true)
+ status[:people].should eq(21)
+ status[:capacity].should eq(3)
+
+ sensors = exec(:sensors).get.not_nil!.as_a
+ sensors.size.should eq 2
+
+ sensor = exec(:sensor, sensors[0]["mac"], sensors[0]["id"]).get
+ sensors[0].should eq sensor
+end
+
+# :nodoc:
+class VergesenseMock < DriverSpecs::MockDriver
+ def on_load
+ self[:floor_key] = {
+ "floor_ref_id" => "FL1",
+ "name" => "Floor 1",
+ "capacity" => 84,
+ "max_capacity" => 60,
+ "spaces" => [
+ {
+ "building_ref_id" => "HQ1",
+ "floor_ref_id" => "FL1",
+ "space_ref_id" => "vergesense-room-id",
+ "space_type" => "conference_room",
+ "name" => "Conference Room 0721",
+ "capacity" => 4,
+ "max_capacity" => 3,
+ "geometry" => {"type" => "Polygon", "coordinates" => [[[93.850772, 44.676952], [93.850739, 44.676929], [93.850718, 44.67695], [93.850751, 44.676973], [93.850772, 44.676952], [93.850772, 44.676952]]]},
+ "people" => {
+ "count" => 21,
+ "coordinates" => [[2.2673, 4.3891], [6.2573, 1.5303]],
+ },
+ "timestamp" => "2019-08-21T21:10:25Z",
+ "motion_detected" => true,
+ },
+ ],
+ }
+ self[:init_complete] = true
+ end
+
+ def floor_key(space_id : String)
+ "floor_key"
+ end
+end
diff --git a/drivers/vergesense/vergesense_api.cr b/drivers/vergesense/vergesense_api.cr
new file mode 100644
index 00000000000..b2ae77a15bd
--- /dev/null
+++ b/drivers/vergesense/vergesense_api.cr
@@ -0,0 +1,199 @@
+require "placeos-driver"
+require "./models"
+
+# docs: https://vergesense.readme.io/reference/reference-getting-started
+
+class Vergesense::VergesenseAPI < PlaceOS::Driver
+ # Discovery Information
+ descriptive_name "Vergesense API"
+ generic_name :Vergesense
+ uri_base "https://api.vergesense.com"
+ description "for more information visit: https://vergesense.readme.io/"
+
+ default_settings({
+ vergesense_api_key: "VS-API-KEY",
+ })
+
+ @api_key : String = ""
+
+ getter buildings : Array(Building) = [] of Building
+ getter floors : Hash(String, Floor) = {} of String => Floor
+ getter spaces : Hash(String, String) = {} of String => String
+
+ @debug_payload : Bool = false
+ @poll_every : Time::Span? = nil
+ @sync_lock : Mutex = Mutex.new
+
+ def on_load
+ on_update
+ schedule.in(200.milliseconds) { init_sync }
+ end
+
+ def on_update
+ @api_key = setting(String, :vergesense_api_key)
+ @debug_payload = setting?(Bool, :debug_payload) || false
+
+ @poll_every = setting?(Int32, :poll_every).try &.seconds
+
+ schedule.clear
+ if poll_time = @poll_every
+ schedule.every(poll_time) { init_sync }
+ end
+ end
+
+ # Performs initial sync by loading buildings / floors / spaces
+ def init_sync
+ @sync_lock.synchronize do
+ init_buildings
+
+ if @buildings
+ init_floors
+ init_spaces
+ init_floors_status
+
+ self["init_complete"] = true
+ end
+ end
+ rescue e
+ logger.error { "failed to perform vergesense API sync\n#{e.inspect_with_backtrace}" }
+ end
+
+ EMPTY_HEADERS = {} of String => String
+ SUCCESS_RESPONSE = {HTTP::Status::OK, EMPTY_HEADERS, nil}
+
+ # Webhook endpoint for space_report API, expects version 2
+ def space_report_api(method : String, headers : Hash(String, Array(String)), body : String)
+ logger.debug { "space_report API received: #{method},\nheaders #{headers},\nbody size #{body.size}" }
+ logger.debug { body } if @debug_payload
+
+ # Parse the data posted
+ begin
+ remote_space = Space.from_json(body)
+ logger.debug { "parsed vergesense payload" }
+
+ update_floor_space(remote_space)
+ update_single_floor_status(remote_space.floor_key, @floors[remote_space.floor_key]?)
+ rescue e
+ logger.error { "failed to parse vergesense space_report API payload\n#{e.inspect_with_backtrace}" }
+ logger.debug { "failed payload body was\n#{body}" }
+ end
+
+ # Return a 200 response
+ SUCCESS_RESPONSE
+ end
+
+ def floor_key(space_id : String)
+ @spaces[space_id]
+ end
+
+ private def init_buildings
+ @buildings = Array(Building).from_json(get_request("/buildings"))
+ end
+
+ private def init_floors
+ @buildings.not_nil!.each do |building|
+ building_with_floors = BuildingWithFloors.from_json(get_request("/buildings/#{building.building_ref_id}"))
+ if building_with_floors
+ building_with_floors.floors.each do |floor|
+ floor_key = "#{building.building_ref_id}-#{floor.floor_ref_id}".strip
+ @floors[floor_key] = floor
+ end
+ end
+ end
+ @floors
+ end
+
+ private def init_spaces
+ spaces = Array(Space).from_json(get_request("/spaces"))
+ spaces.each do |remote_space|
+ update_floor_space(remote_space)
+ end
+
+ spaces
+ end
+
+ private def init_floors_status
+ @floors.each do |floor_key, floor|
+ update_single_floor_status(floor_key, floor)
+ end
+ end
+
+ private def update_single_floor_status(floor_key, floor)
+ if floor_key && floor
+ self[floor_key] = floor.not_nil!
+ end
+ end
+
+ # Finds a space on a given floor and updates it in place.
+ private def update_floor_space(remote_space)
+ floor = @floors[remote_space.floor_key]?
+ if floor
+ floor_space = floor.spaces.find { |space| space.ref_id == remote_space.ref_id }
+ if floor_space
+ floor_space.building_ref_id = remote_space.building_ref_id
+ floor_space.floor_ref_id = remote_space.floor_ref_id
+ floor_space.people = remote_space.people
+ floor_space.motion_detected = remote_space.motion_detected
+ floor_space.timestamp = remote_space.last_report_time?
+ floor_space.environment = remote_space.environment
+ floor_space.name = remote_space.name if remote_space.name
+ floor_space.capacity = remote_space.capacity if remote_space.capacity
+ floor_space.max_capacity = remote_space.max_capacity if remote_space.max_capacity
+ floor_space.signs_of_life = remote_space.signs_of_life?
+ else
+ remote_space.signs_of_life = remote_space.signs_of_life?
+ floor.spaces << remote_space
+ end
+
+ # cache the lookups for simple floor discovery
+ if space_ref = remote_space.ref_id
+ @spaces[space_ref] = remote_space.floor_key
+ end
+ end
+ end
+
+ private def check_hardware_state
+ # paginated_request("/hardware/sensors") do |raw_json|
+ # end
+ end
+
+ private def get_request(path)
+ response = get(path,
+ headers: {
+ "vs-api-key" => @api_key,
+ }
+ )
+
+ if response.success?
+ response.body
+ else
+ raise "unexpected response #{response.status_code}\n#{response.body}"
+ end
+ end
+
+ private def paginated_request(path)
+ max_pages = 100
+ loop do
+ response = get(path,
+ headers: {
+ "vs-api-key" => @api_key,
+ }
+ )
+
+ if response.success?
+ body_json = response.body
+ yield body_json
+
+ max_pages -= 1
+ break if max_pages <= 0
+
+ pagination = Pagination.from_json(body_json, "links") rescue Pagination.new
+ next_request = pagination.next_page
+ break unless next_request
+ path = next_request
+ else
+ raise "unexpected response #{response.status_code}\n#{response.body}"
+ end
+ end
+ end
+end
diff --git a/drivers/vergesense/vergesense_api_spec.cr b/drivers/vergesense/vergesense_api_spec.cr
new file mode 100644
index 00000000000..dac15cc826a
--- /dev/null
+++ b/drivers/vergesense/vergesense_api_spec.cr
@@ -0,0 +1,187 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Vergesense::VergesenseAPI" do
+ expect_http_request do |request, response|
+ case request.path
+ when "/buildings"
+ response.status_code = 200
+ response << %([{
+ "name": "HQ 1",
+ "building_ref_id": "HQ1",
+ "address": null
+ }])
+ end
+ end
+
+ puts "SENT BUILDINGS"
+
+ expect_http_request do |request, response|
+ case request.path
+ when "/buildings/HQ1"
+ response.status_code = 200
+ response << %({
+ "building_ref_id": "HQ1",
+ "capacity": 84,
+ "minimum_social_distance": 2.0,
+ "floors": [
+ {
+ "name": "Floor 1",
+ "floor_ref_id": "FL1",
+ "capacity": 84,
+ "max_capacity": 60,
+ "spaces": [
+ {
+ "name": "Conference Room 0721",
+ "space_ref_id": "CR_0721",
+ "space_type": "conference_room",
+ "capacity": 4,
+ "max_capacity": 3,
+ "sensors": [
+ {
+ "id": "L_000018",
+ "partitions": [
+ {
+ "id": "L_000018/321"
+ }
+ ]
+ }
+ ],
+ "geometry": {
+ "type": "Polygon",
+ "coordinates": [
+ [
+ [
+ 93.850772,
+ 44.676952
+ ],
+ [
+ 93.850739,
+ 44.676929
+ ],
+ [
+ 93.850718,
+ 44.67695
+ ],
+ [
+ 93.850751,
+ 44.676973
+ ],
+ [
+ 93.850772,
+ 44.676952
+ ],
+ [
+ 93.850772,
+ 44.676952
+ ]
+ ]
+ ]
+ }
+ }
+ ]
+ }
+ ]
+})
+ end
+ end
+
+ puts "SENT FLOORS"
+
+ expect_http_request do |request, response|
+ case request.path
+ when "/spaces"
+ response.status_code = 200
+ response << %([
+ {
+ "building_ref_id": "HQ1",
+ "floor_ref_id": "FL1",
+ "space_ref_id": "CR_0721",
+ "name": "Conference Room 0721",
+ "space_type": "conference_room",
+ "last_reports": [
+ {
+ "id": "W91-IGI",
+ "person_count": 2,
+ "signs_of_life": null,
+ "motion_detected": null,
+ "timestamp": "2019-07-29T18:42:19Z"
+ }
+ ],
+ "people": {
+ "count": 2,
+ "distances": {
+ "units": "meters",
+ "values": [2.42]
+ }
+ }
+ }
+])
+ end
+ end
+
+ puts "SENT SPACES"
+
+ status["HQ1-FL1"].should eq({
+ "floor_ref_id" => "FL1",
+ "name" => "Floor 1",
+ "capacity" => 84,
+ "max_capacity" => 60,
+ "spaces" => [
+ {
+ "building_ref_id" => "HQ1",
+ "floor_ref_id" => "FL1",
+ "space_ref_id" => "CR_0721",
+ "space_type" => "conference_room",
+ "name" => "Conference Room 0721",
+ "capacity" => 4,
+ "max_capacity" => 3,
+ "people" => {"count" => 2},
+ },
+ ],
+ })
+
+ # Testing webhook save
+ webhook_space_report_event = %({
+ "building_ref_id": "HQ1",
+ "floor_ref_id": "FL1",
+ "space_ref_id": "CR_0721",
+ "sensor_ids": ["VS0-123", "VS1-321"],
+ "person_count": 21,
+ "signs_of_life": null,
+ "motion_detected": true,
+ "event_type": "space_report",
+ "timestamp": "2019-08-21T21:10:25Z",
+ "people": {
+ "count": 21,
+ "distances": {
+ "units": "meters",
+ "values": [1.5]
+ }
+ }
+ })
+
+ exec(:space_report_api, method: "update", headers: {"test" => ["test"]}, body: webhook_space_report_event).get
+
+ status["HQ1-FL1"].should eq({
+ "floor_ref_id" => "FL1",
+ "name" => "Floor 1",
+ "capacity" => 84,
+ "max_capacity" => 60,
+ "spaces" => [
+ {
+ "building_ref_id" => "HQ1",
+ "floor_ref_id" => "FL1",
+ "space_ref_id" => "CR_0721",
+ "space_type" => "conference_room",
+ "name" => "Conference Room 0721",
+ "capacity" => 4,
+ "max_capacity" => 3,
+ "people" => {
+ "count" => 21,
+ },
+ "timestamp" => "2019-08-21T21:10:25Z",
+ "motion_detected" => true,
+ },
+ ],
+ })
+end
diff --git a/drivers/whispir/messages.cr b/drivers/whispir/messages.cr
new file mode 100644
index 00000000000..f2c8cfbd33d
--- /dev/null
+++ b/drivers/whispir/messages.cr
@@ -0,0 +1,55 @@
+require "placeos-driver"
+require "placeos-driver/interface/sms"
+
+# Documentation: https://whispir.github.io/api/#messages
+
+class Whispir::Messages < PlaceOS::Driver
+ include Interface::SMS
+
+ # Discovery Information
+ generic_name :SMS
+ descriptive_name "Whispir messages service"
+ uri_base "https://api.au.whispir.com"
+
+ # For whatever reason, you need both basic auth and an API key
+ default_settings({
+ basic_auth: {
+ username: "username",
+ password: "password",
+ },
+ api_key: "12345",
+ })
+
+ @api_key : String = ""
+
+ def on_update
+ @api_key = setting(String, :api_key)
+ end
+
+ def send_sms(
+ phone_numbers : String | Array(String),
+ message : String,
+ format : String? = "SMS",
+ source : String? = nil
+ )
+ phone_numbers = [phone_numbers] unless phone_numbers.is_a?(Array)
+
+ response = post("/messages?apikey=#{@api_key}", body: {
+ to: phone_numbers.join(";"),
+ # As far as I can tell, this field is not passed to the recipients
+ subject: "PlaceOS Notification",
+ body: message,
+ }.to_json, headers: {
+ "Content-Type" => "application/vnd.whispir.message-v1+json",
+ "Accept" => "application/vnd.whispir.message-v1+json",
+ "x-api-key" => @api_key,
+ })
+
+ raise "request failed with #{response.status_code}" unless response.status_code == 202
+
+ location = response.headers["Location"]?
+ logger.debug { "message sent: #{location}" }
+
+ location
+ end
+end
diff --git a/drivers/whispir/messages_spec.cr b/drivers/whispir/messages_spec.cr
new file mode 100644
index 00000000000..ad58dc179d1
--- /dev/null
+++ b/drivers/whispir/messages_spec.cr
@@ -0,0 +1,32 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Whispir::Messages" do
+ # Send the request
+ retval = exec(:send_sms,
+ phone_numbers: "+61418419954",
+ message: "hello steve"
+ )
+
+ # sms should send a HTTP request
+ expect_http_request do |request, response|
+ headers = request.headers
+ io = request.body
+ if io
+ data = io.gets_to_end
+ request = JSON.parse(data)
+ if request["to"] == "+61418419954" &&
+ headers["x-api-key"]? == "12345" &&
+ headers["Authorization"]? == "Basic #{Base64.strict_encode("username:password")}"
+ response.status_code = 202
+ response.headers["Location"] = "https://api.au.whispir.com/messages/id"
+ else
+ response.status_code = 401
+ end
+ else
+ raise "expected request to include dialing details #{request.inspect}"
+ end
+ end
+
+ # What the sms function should return
+ retval.get.should eq("https://api.au.whispir.com/messages/id")
+end
diff --git a/drivers/wiegand/models.cr b/drivers/wiegand/models.cr
new file mode 100644
index 00000000000..cb2a08b3aa4
--- /dev/null
+++ b/drivers/wiegand/models.cr
@@ -0,0 +1,103 @@
+module Wiegand
+ # Ported from: https://github.com/acaprojects/ruby-engine-drivers/blob/beta/lib/hid/algorithms.rb
+ class Base
+ property wiegand : UInt64
+ property facility : UInt32
+ property card_number : UInt32
+
+ def initialize(wiegand : UInt64, facility : UInt32, card_number : UInt32)
+ @wiegand = wiegand
+ @facility = facility
+ @card_number = card_number
+ end
+
+ def self.count_1s(int : UInt32 | UInt64)
+ int.to_s(2).gsub("0", "").size
+ end
+ end
+
+ class Wiegand26 < Base
+ FAC_PAR_MASK = 0b11111111100000000000000000
+ FACILITY_MASK = 0b01111111100000000000000000
+ CARD_MASK = 0b00000000011111111111111110
+ CARD_PAR_MASK = 0b00000000011111111111111111
+
+ # Convert wiegand 26 card data to components
+ #
+ # Hex card data: 0x21a6616
+ # Card Number: 13067
+ # Card Facility Code: 13
+ def from_wiegand(wiegand : UInt64)
+ card_number = (wiegand & CARD_MASK) >> 1
+ card_1s = count_1s(wiegand & CARD_PAR_MASK)
+
+ facility = (wiegand & FACILITY_MASK) >> 17
+ facility_1s = count_1s(wiegand & FAC_PAR_MASK)
+
+ parity_passed = card_1s.odd? && facility_1s.even?
+ raise "parity check error" unless parity_passed
+
+ Wiegand26.new(wiegand.to_u64, facility, card_number)
+ end
+
+ # Convert components to wiegand 26 card data
+ def self.from_components(facility : UInt32, card_number : UInt32)
+ wiegand = 0
+
+ wiegand += card_number << 1
+ # Build the card parity bit (should be an odd number of ones)
+ wiegand += (FAC_PAR_MASK ^ FACILITY_MASK) if count_1s(card_number).odd?
+
+ wiegand += facility << 17
+ # Build facility parity bit (should be an even number of ones)
+ wiegand += 1 if count_1s(facility).even?
+
+ Wiegand26.new(wiegand.to_u64, facility, card_number)
+ end
+ end
+
+ class Wiegand35 < Base
+ PAR_EVEN_MASK = 0b01101101101101101101101101101101100
+ PAR_ODD_MASK = 0b00110110110110110110110110110110110
+ CARD_MASK = 0b00000000000001111111111111111111100
+ FACILITY_MASK = 0b01111111111110000000000000000000000
+
+ # Outputs the HEX code of what is written to the swipe card
+ #
+ # Hex card data: 0x06F20107F
+ # Card Number: 2540
+ # Card Facility Code: 4033
+ def from_components(facility : UInt32, card_number : UInt32)
+ wiegand = (facility << 22) + (card_number << 2)
+ even_count = count_1s(wiegand & PAR_EVEN_MASK)
+ odd_count = count_1s(wiegand & PAR_ODD_MASK)
+
+ # Even Parity
+ wiegand += (1 << 34) if even_count.odd?
+
+ # Odd Parity
+ wiegand += 2 if odd_count.even?
+ wiegand = wiegand.to_s(2).rjust(35, '0').reverse.to_i(2)
+
+ Wiegand35.new(wiegand.to_u64, facility, card_number)
+ end
+
+ # Convert wiegand 35 card data to components
+ #
+ # 1 + 12 + 20 + 2
+ # 1 + facility + card num + 2
+ def self.from_wiegand(wiegand)
+ str = wiegand.to_s(2).rjust(35, '0').reverse
+ data = str.to_i(2)
+ even_count = count_1s(data & PAR_EVEN_MASK) + (str[0] == '1' ? 1 : 0)
+ odd_count = count_1s(data & PAR_ODD_MASK)
+
+ parity_passed = odd_count.odd? && even_count.even?
+ raise "parity check error" unless parity_passed
+
+ facility = (data & FACILITY_MASK) >> 22
+ card_number = (data & CARD_MASK) >> 2
+ Wiegand35.new(wiegand.to_u64, facility, card_number)
+ end
+ end
+end
diff --git a/drivers/williams_av/wave_cast_fm.cr b/drivers/williams_av/wave_cast_fm.cr
new file mode 100644
index 00000000000..9c7f46ad2a8
--- /dev/null
+++ b/drivers/williams_av/wave_cast_fm.cr
@@ -0,0 +1,281 @@
+require "placeos-driver"
+
+# Documentation: https://aca.im/driver_docs/WilliamsAV/WaveCAST-MAN-262D-WCFM.pdf
+
+class WilliamsAV::WaveCastFM < PlaceOS::Driver
+ # Discovery Information:
+ generic_name :HearingAugmentation
+ descriptive_name "WilliamsAV WaveCast / FM"
+ uri_base "http://192.168.0.1"
+
+ default_settings({
+ # only a single connection can be maintained at a time
+ http_max_requests: 0,
+ # supports 0-7
+ channel_number: 0,
+
+ hearing_notice_text: "Hearing augmentation code:",
+ })
+
+ @hearing_notice_text : String = "Hearing augmentation code:"
+
+ def on_update
+ @channel_number = setting?(Int32, :channel_number)
+ @hearing_notice_text = setting?(String, :hearing_notice_text) || "Hearing augmentation code:"
+ schedule.clear
+
+ # ensure query run at the same time for offset to work
+ schedule.cron("* * * * *") { connected }
+ end
+
+ def channel_offset
+ (3000 * (@channel_number || 0)) + rand(750)
+ end
+
+ def connected
+ schedule.in(channel_offset.milliseconds) { query_state }
+ end
+
+ getter channel_number : Int32? = nil
+
+ enum Command
+ TDU8_REBOOT
+ TDU8_RESTORE_DEFAULTS
+ TDU8_VU_METER_VALUE
+ TDU8_INPUT_GAIN
+ TDU8_INPUT_SOURCE
+ TDU8_PRESET
+ TDU8_HIGH_PASS
+ TDU8_LOW_PASS
+ TDU8_COMPRESSION
+ TDU8_USE_DHCP
+ TDU8_AUDIO_TX_MODE
+ TDU8_TTL
+ TDU8_SECURE_MODE
+ TDU8_PANEL_LOCK
+ TDU32_RF_TIMEOUT
+ TDU8_RF_CHANNEL
+ TDU8_RF_17_CHANNEL_MODE
+ TDU8_RF_POWER
+ TDSTR_SERVER_NAME
+ TDSTR_STATIC_IP_ADDR
+ TDSTR_STATIC_SUBNET_MASK
+ TDSTR_STATIC_GATEWAY_ADDR
+ TDSTR_MULTICAST_ADDR
+ TDSTR_JOIN_CODE
+ end
+
+ enum Type
+ TT_FLOAT # float
+ TT_U8 # uint8
+ TT_U32 # uint32
+ TT_S8 # int8
+ TT_S32 # int32
+ TT_STRING
+ end
+
+ TYPES = {
+ Command::TDU8_REBOOT => Type::TT_U8,
+ Command::TDU8_RESTORE_DEFAULTS => Type::TT_U8,
+ Command::TDU8_VU_METER_VALUE => Type::TT_U8,
+ Command::TDU8_INPUT_GAIN => Type::TT_U8,
+ Command::TDU8_INPUT_SOURCE => Type::TT_U8,
+ Command::TDU8_PRESET => Type::TT_U8,
+ Command::TDU8_HIGH_PASS => Type::TT_U8,
+ Command::TDU8_LOW_PASS => Type::TT_U8,
+ Command::TDU8_COMPRESSION => Type::TT_U8,
+ Command::TDU8_USE_DHCP => Type::TT_U8,
+ Command::TDU8_AUDIO_TX_MODE => Type::TT_U8,
+ Command::TDU8_TTL => Type::TT_U8,
+ Command::TDU8_SECURE_MODE => Type::TT_U8,
+ Command::TDU8_PANEL_LOCK => Type::TT_U8,
+ Command::TDU32_RF_TIMEOUT => Type::TT_U32,
+ Command::TDU8_RF_CHANNEL => Type::TT_U8,
+ Command::TDU8_RF_17_CHANNEL_MODE => Type::TT_U8,
+ Command::TDU8_RF_POWER => Type::TT_U8,
+ Command::TDSTR_SERVER_NAME => Type::TT_STRING,
+ Command::TDSTR_STATIC_IP_ADDR => Type::TT_STRING,
+ Command::TDSTR_STATIC_SUBNET_MASK => Type::TT_STRING,
+ Command::TDSTR_STATIC_GATEWAY_ADDR => Type::TT_STRING,
+ Command::TDSTR_MULTICAST_ADDR => Type::TT_STRING,
+ Command::TDSTR_JOIN_CODE => Type::TT_STRING,
+ }
+
+ def query_state
+ if channel = channel_number
+ body_data = URI::Params.build { |form|
+ form.add "type", "TT_U8"
+ form.add "id", "TDU8_CURRENT_CHANNEL"
+ form.add "value", channel.to_s
+ }.to_s
+
+ logger.debug { "switching current channel to: #{channel}" }
+
+ response = post("/TBL-WRITE", body: body_data)
+ raise "request failed with #{response.status_code}\n#{response.body}" unless response.success?
+ end
+
+ response = get("/TBL-READ?All")
+ raise "request failed with #{response.status_code}\n#{response.body}" unless response.success?
+
+ count = 0
+ response.body.split('\n').each do |line|
+ next unless line.presence
+ parts = line.split(",").map!(&.strip)
+ begin
+ type = Type.parse(parts[0])
+ command = Command.parse?(parts[1]) || parts[1]
+ value_raw = parts[2]
+
+ value = case type
+ in Type::TT_FLOAT
+ value_raw.to_f
+ in Type::TT_U8, Type::TT_U32, Type::TT_S8, Type::TT_S32
+ value_raw.to_i
+ in Type::TT_STRING
+ value_raw
+ end
+
+ set_status(command, value)
+ count += 1
+ rescue error
+ raise "error parsing response line\n#{error.inspect_with_backtrace}"
+ end
+ end
+ "#{count} values updated"
+ end
+
+ protected def set_status(command : Command | String, value)
+ command_str = command.to_s.split('_', 2)[1].downcase
+
+ case command
+ when Command::TDU8_SECURE_MODE
+ command_str = "join_code_enabled"
+ value = value == 1
+ when Command::TDU8_AUDIO_TX_MODE
+ command_str = "transmit_multicast"
+ value = value == 1
+ when Command::TDU8_PANEL_LOCK
+ value = value == 1
+ when Command::TDU8_INPUT_SOURCE
+ value = InputSource.from_value?(value.to_i) || value
+ when Command::TDU8_PRESET
+ value = Preset.from_value?(value.to_i) || value
+ when Command::TDSTR_JOIN_CODE
+ self[:hearing_notice_text] = "#{@hearing_notice_text} #{value}"
+ end
+
+ self[command_str] = value
+ end
+
+ @[Security(Level::Administrator)]
+ def write(command : Command, value : UInt8 | UInt32 | String)
+ body_data = URI::Params.build { |form|
+ if channel = channel_number
+ form.add "type", "TT_U8"
+ form.add "id", "TDU8_CURRENT_CHANNEL"
+ form.add "value", channel.to_s
+ end
+ form.add "type", TYPES[command].to_s
+ form.add "id", command.to_s
+ form.add "value", value.to_s
+ }.to_s
+
+ logger.debug { "updating setting: #{body_data}" }
+
+ response = post("/TBL-WRITE", body: body_data)
+ raise "request failed with #{response.status_code}\n#{response.body}" unless response.success?
+
+ set_status(command, value)
+ end
+
+ @[Security(Level::Support)]
+ def enable_join_code(state : Bool)
+ write(Command::TDU8_SECURE_MODE, state ? 1_u8 : 0_u8)
+ end
+
+ @[Security(Level::Support)]
+ def set_join_code(pin : String)
+ write(Command::TDSTR_JOIN_CODE, pin)
+ end
+
+ # creates a numeric pin size digits long
+ @[Security(Level::Support)]
+ def set_random_join_code(size : Int32 = 4)
+ pin = String.build do |str|
+ size.times do
+ rand(9).to_s(str)
+ end
+ end
+ set_join_code(pin)
+ end
+
+ @[Security(Level::Support)]
+ def reboot
+ write(Command::TDU8_REBOOT, 1_u8)
+ end
+
+ @[Security(Level::Administrator)]
+ def restore_defaults
+ write(Command::TDU8_RESTORE_DEFAULTS, 1_u8)
+ end
+
+ @[Security(Level::Administrator)]
+ def set_vu_meter(value : UInt8, overload : Bool = false)
+ value = value.clamp(0_u8, 9_u8) unless overload
+ write(Command::TDU8_VU_METER_VALUE, value)
+ end
+
+ @[Security(Level::Support)]
+ def input_gain(value : UInt8)
+ value = value.clamp(0_u8, 50_u8)
+ write(Command::TDU8_INPUT_GAIN, value)
+ end
+
+ enum InputSource
+ AnalogLineIn = 1
+ Mic = 2
+ PhantomMic = 3
+ AES = 4
+ S_PDIF = 5
+ TestTone = 6
+ end
+
+ @[Security(Level::Support)]
+ def input_source(value : InputSource)
+ write(Command::TDU8_INPUT_SOURCE, value.to_u8)
+ end
+
+ enum Preset
+ Voice = 1
+ Music = 2
+ HearingAssist = 3
+ Custom = 4
+ end
+
+ @[Security(Level::Support)]
+ def preset(value : Preset)
+ write(Command::TDU8_PRESET, value.to_u8)
+ end
+
+ @[Security(Level::Administrator)]
+ def transmit_multicast(state : Bool)
+ write(Command::TDU8_AUDIO_TX_MODE, state ? 1_u8 : 0_u8)
+ end
+
+ @[Security(Level::Administrator)]
+ def set_ttl(value : UInt8)
+ value = value.clamp(0_u8, 30_u8)
+ write(Command::TDU8_TTL, value)
+ end
+
+ @[Security(Level::Support)]
+ def lock_front_panel(state : Bool)
+ write(Command::TDU8_PANEL_LOCK, state ? 1_u8 : 0_u8)
+ end
+
+ @[Security(Level::Administrator)]
+ def set_multicast_address(ip_address : String)
+ write(Command::TDSTR_MULTICAST_ADDR, ip_address)
+ end
+end
diff --git a/drivers/williams_av/wave_cast_fm_spec.cr b/drivers/williams_av/wave_cast_fm_spec.cr
new file mode 100644
index 00000000000..fedbe773ab8
--- /dev/null
+++ b/drivers/williams_av/wave_cast_fm_spec.cr
@@ -0,0 +1,89 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "MessageMedia::SMS" do
+ # select channel
+ expect_http_request do |request, response|
+ data = request.body.try(&.gets_to_end)
+ if data == "type=TT_U8&id=TDU8_CURRENT_CHANNEL&value=0"
+ response.status_code = 201
+ else
+ response.status_code = 400
+ response << "badly formatted"
+ end
+ end
+
+ # request state
+ expect_http_request do |request, response|
+ response.status_code = 200
+ response << %(TT_FLOAT, FLOAT_DATA_0, 0.0000
+TT_U32, TDU32_DANTE_LINK_STATE, 0
+TT_U32, TDU32_DANTE_SAMPLE_RATE, 0
+TT_U32, TDU32_RF_TIMEOUT, 1800000
+TT_U32, TDU32_RTC_UNIX_TIME, 981868966
+TT_S32, S32_DATA_0, 0
+TT_U8, TDU8_VU_METER_VALUE, 0
+TT_U8, TDU8_INPUT_GAIN, 10
+TT_U8, TDU8_INPUT_SOURCE, 1
+TT_U8, TDU8_PRESET, 3
+TT_U8, TDU8_HIGH_PASS, 1
+TT_U8, TDU8_LOW_PASS, 8
+TT_U8, TDU8_COMPRESSION, 1
+TT_U8, TDU8_USE_DHCP, 1
+TT_U8, TDU8_AUDIO_TX_MODE, 1
+TT_U8, TDU8_TTL, 1
+TT_U8, TDU8_SECURE_MODE, 0
+TT_U8, TDU8_PANEL_LOCK, 0
+TT_U8, TDU8_REBOOT, 0
+TT_U8, TDU8_RESTORE_DEFAULTS, 0
+TT_U8, TDU8_DANTE_PRESENT, 0
+TT_U8, TDU8_RF_CHANNEL, 1
+TT_U8, TDU8_RF_17_CHANNEL_MODE, 1
+TT_U8, TDU8_RF_POWER, 3
+TT_S8, TDS8_SERVER_CHANNEL_NO, 0
+TT_STRING, TDSTR_SERVER_NAME, Exemplar Room
+TT_STRING, TDSTR_CURRENT_IP_ADDR, 138.80.96.228
+TT_STRING, TDSTR_STATIC_IP_ADDR, 10.0.0.2
+TT_STRING, TDSTR_STATIC_SUBNET_MASK, 255.0.0.0
+TT_STRING, TDSTR_STATIC_GATEWAY_ADDR,
+TT_STRING, TDSTR_CURRENT_MC_ADDR,
+TT_STRING, TDSTR_MULTICAST_ADDR, 0.0.0.0
+TT_STRING, TDSTR_JOIN_CODE, 000000
+TT_STRING, TDSTR_USER_NAME, cduadmin
+TT_STRING, TDSTR_DANTE_DEVICE_NAME,
+TT_STRING, TDSTR_DANTE_DEFAULT_NAME,
+TT_STRING, TDSTR_DANTE_IP_ADDR,
+TT_STRING, TDSTR_DANTE_SUBNET_MASK,
+TT_STRING, TDSTR_DANTE_GATEWAY,
+TT_STRING, TDSTR_DANTE_MAC_ADDR,
+TT_STRING, TDSTR_WEBSERVER_VERSION, 2.2.0
+TT_STRING, TDSTR_293_FIRMWARE_VERSION, 2.4.0
+TT_STRING, TDSTR_DEVICE_MODEL_NAME, WF_T5
+TT_STRING, TDSTR_LAST_LOGGED_ERROR, 981868965 ERR_WEB_404_RESPONSE
+
+)
+ end
+
+ sleep 1.second
+
+ # check the status updated
+ status["join_code_enabled"]?.should eq false
+ status["panel_lock"]?.should eq false
+ status["transmit_multicast"]?.should eq true
+ status["reboot"]?.should eq 0
+ status["rf_power"]?.should eq 3
+ status["input_source"]?.should eq "AnalogLineIn"
+ status["preset"]?.should eq "HearingAssist"
+
+ # check the various methods work
+ retval = exec(:reboot)
+ expect_http_request do |request, response|
+ data = request.body.try(&.gets_to_end)
+ if data == "type=TT_U8&id=TDU8_CURRENT_CHANNEL&value=0&type=TT_U8&id=TDU8_REBOOT&value=1"
+ response.status_code = 201
+ else
+ response.status_code = 400
+ response << "badly formatted"
+ end
+ end
+ retval.get.should eq(1)
+end
diff --git a/drivers/winmate/led_light_bar.cr b/drivers/winmate/led_light_bar.cr
new file mode 100644
index 00000000000..7867d269bfa
--- /dev/null
+++ b/drivers/winmate/led_light_bar.cr
@@ -0,0 +1,182 @@
+require "placeos-driver"
+
+# Documentation: https://aca.im/driver_docs/Winmate/LED%20Light%20Bar%20SDK.pdf
+
+class Winmate::LedLightBar < PlaceOS::Driver
+ # Discovery Information
+ descriptive_name "Winmate PC - LED Light Bar"
+ generic_name :StatusLight
+ tcp_port 8000
+
+ def on_load
+ queue.delay = 100.milliseconds
+ on_update
+ end
+
+ DEFAULT_COLOURS = {
+ "red" => {
+ red: 255_u8,
+ green: 0_u8,
+ blue: 0_u8,
+ },
+ "green" => {
+ red: 0_u8,
+ green: 255_u8,
+ blue: 0_u8,
+ },
+ "blue" => {
+ red: 0_u8,
+ green: 0_u8,
+ blue: 255_u8,
+ },
+ "orange" => {
+ red: 200_u8,
+ green: 0_u8,
+ blue: 0_u8,
+ },
+ "off" => {
+ red: 0_u8,
+ green: 0_u8,
+ blue: 0_u8,
+ },
+ }
+
+ alias Colours = Hash(String, NamedTuple(red: UInt8, green: UInt8, blue: UInt8))
+
+ @colours : Colours = Colours.new
+
+ def on_update
+ colours = setting?(Colours, :colours) || Colours.new
+ @colours = colours.merge(DEFAULT_COLOURS)
+ end
+
+ def connected
+ @buffer = String.new
+
+ transport.tokenizer = Tokenizer.new do |io|
+ bytes = io.peek # for demonstration purposes
+ bytes[0].to_i
+ end
+
+ do_poll
+ schedule.every(50.seconds) do
+ logger.debug { "-- Polling Winmate LED" }
+ do_poll
+ end
+ end
+
+ def disconnected
+ schedule.clear
+ end
+
+ def colour(colour : String)
+ colours = @colours[colour]
+ self[:colour_name] = colour
+ colours.each do |component, intensity|
+ led = Led.parse(component.to_s)
+ set led, intensity
+ end
+ end
+
+ enum Led
+ Red
+ Green
+ Blue
+ end
+
+ COLOURS = {
+ Led::Red => 0x10_u8,
+ Led::Green => 0x11_u8,
+ Led::Blue => 0x12_u8,
+ }
+
+ COLOUR_LOOKUP = {
+ 0x10 => Led::Red,
+ 0x11 => Led::Green,
+ 0x12 => Led::Blue,
+ }
+
+ COMMANDS = {
+ set: 0x61_u8,
+ get: 0x60_u8,
+ }
+
+ def query(led : Led, **options)
+ do_send(**options.merge({
+ command: :get,
+ colour: led,
+ }))
+ end
+
+ def set(led : Led, value : UInt8, **options)
+ self[led.to_s.downcase] = value
+
+ do_send(**options.merge({
+ command: :set,
+ colour: led,
+ value: value,
+ }))
+ end
+
+ def do_poll
+ query(:red, priority: 0)
+ query(:green, priority: 0)
+ query(:blue, priority: 0)
+ end
+
+ def received(bytes, task)
+ logger.debug { "received: #{bytes.hexstring}" }
+
+ unless check_checksum(bytes)
+ logger.warn { "Error processing response. Possibly incorrect baud rate configured" }
+ return task.try(&.abort)
+ end
+
+ # first byte is the message length, so we can ignore that
+ indicator = bytes[1]
+ colour = COLOUR_LOOKUP[indicator]?
+ if colour
+ self[colour.to_s.downcase] = bytes[2]
+ task.try(&.success(bytes[2]))
+ else
+ return task.try(&.abort) unless indicator == 0x0C
+ task.try(&.success)
+ end
+ end
+
+ # 2’s complement, &+ operators ignore overflows
+ protected def build_checksum(data : Array(UInt8))
+ result = data.reduce(0_u8) { |sum, byte| sum &+= byte }
+ ((~(result & 0xFF_u8)) &+ 1_u8)
+ end
+
+ protected def check_checksum(data : Bytes)
+ check = data.to_a
+ result = check.pop
+ result == build_checksum(check)
+ end
+
+ protected def do_send(command : Symbol, colour : Led, value : UInt8? = nil, **options)
+ cmd = COMMANDS[command]
+ led = COLOURS[colour]
+
+ # Build core request
+ req = [cmd, led]
+ req << value if value
+
+ # Add length indicator
+ len = (req.size + 2).to_u8
+ req.unshift len
+
+ # Calculate checksum
+ req << build_checksum(req)
+ bytes = Slice.new(req.to_unsafe, req.size)
+ logger.debug { "requesting #{bytes}" }
+
+ options = options.merge({
+ name: "#{command}_#{colour}_#{!!value}",
+ })
+
+ send(bytes, **options)
+ end
+end
diff --git a/drivers/winmate/led_light_bar_spec.cr b/drivers/winmate/led_light_bar_spec.cr
new file mode 100644
index 00000000000..dfc812313b1
--- /dev/null
+++ b/drivers/winmate/led_light_bar_spec.cr
@@ -0,0 +1,15 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Winmate::LedLightBar" do
+ should_send(Bytes[0x04, 0x60, 0x10, 140]).responds Bytes[0x04, 0x10, 0xFF, 0xED]
+ should_send(Bytes[0x04, 0x60, 0x11, 139]).responds Bytes[0x04, 0x11, 0xFF, 0xEC]
+ should_send(Bytes[0x04, 0x60, 0x12, 138]).responds Bytes[0x04, 0x12, 0xFF, 0xEB]
+ status[:red].should eq 0xFF
+ status[:green].should eq 0xFF
+ status[:blue].should eq 0xFF
+
+ resp = exec(:set, "red", 100)
+ should_send(Bytes[0x05, 0x61, 0x10, 0x64, 0x26]).responds Bytes[0x03, 0x0C, 0xF1]
+ resp.get
+ status[:red].should eq 100
+end
diff --git a/drivers/xovis/sensor_api.cr b/drivers/xovis/sensor_api.cr
new file mode 100644
index 00000000000..6b67ecce884
--- /dev/null
+++ b/drivers/xovis/sensor_api.cr
@@ -0,0 +1,279 @@
+require "placeos-driver"
+require "placeos-driver/interface/sensor"
+require "xml"
+
+# Documentation: https://aca.im/driver_docs/Xovis/Xovis-REST-API.pdf
+
+class Xovis::SensorAPI < PlaceOS::Driver
+ include Interface::Sensor
+
+ # Discovery Information
+ generic_name :XovisSensor
+ descriptive_name "Xovis Flow Sensor"
+
+ uri_base "https://192.168.0.1"
+
+ default_settings({
+ basic_auth: {
+ username: "account",
+ password: "password!",
+ },
+ poll_rate: 15,
+ })
+
+ @poll_rate : Time::Span = 15.seconds
+ @mac : String = ""
+ @state : Hash(String, Array(SensorDetail)) = {} of String => Array(SensorDetail)
+
+ def on_update
+ @poll_rate = (setting?(Int32, :poll_rate) || 15).seconds
+ @mac = URI.parse(config.uri.not_nil!).hostname.not_nil!
+
+ query_capacity = setting?(Bool, :query_capacity)
+ query_counts = setting?(Bool, :query_counts)
+
+ schedule.clear
+ schedule.every(@poll_rate) do
+ capacity_data unless query_capacity == false
+ count_data unless query_counts == false
+ end
+ schedule.every(5.minutes) { device_status }
+ schedule.in(@poll_rate / 3) do
+ device_status
+ capacity_data unless query_capacity == false
+ count_data unless query_counts == false
+ end
+ end
+
+ class SensorDetail < Interface::Sensor::Detail
+ property capacity : Int32? = nil
+ property first_entry : Int64? = nil
+ property last_entry : Int64? = nil
+ end
+
+ def sensor(mac : String, id : String? = nil) : Interface::Sensor::Detail?
+ logger.debug { "sensor mac: #{mac}, id: #{id} requested" }
+
+ return nil unless @mac == mac
+ return nil unless id
+
+ # https://crystal-lang.org/api/1.1.0/String.html#rpartition(search:Char%7CString):Tuple(String,String,String)-instance-method
+ sensor, _, index_str = id.rpartition('-')
+ return nil if sensor.empty?
+ index = index_str.to_i
+
+ if sensors = @state["#{sensor}-counts"]?
+ sensors[index]?
+ end
+ rescue error
+ logger.warn(exception: error) { "checking for sensor" }
+ nil
+ end
+
+ TYPES = {
+ "line-counts" => SensorType::QueueSize,
+ "zone-occupancy-counts" => SensorType::PeopleCount,
+ "zone-in-out-counts" => SensorType::Counter,
+ }
+
+ NO_MATCH = [] of Interface::Sensor::Detail
+
+ def sensors(type : String? = nil, mac : String? = nil, zone_id : String? = nil) : Array(Interface::Sensor::Detail)
+ logger.debug { "sensors of type: #{type}, mac: #{mac}, zone_id: #{zone_id} requested" }
+ return NO_MATCH if mac && mac != @mac
+ return @state.values.flatten.map &.as(Interface::Sensor::Detail) unless type
+
+ sensor_type = SensorType.parse(type)
+ matches = [] of Array(Interface::Sensor::Detail)
+ TYPES.each { |key, key_type| matches << @state[key].map &.as(Interface::Sensor::Detail) if key_type == sensor_type }
+
+ matches.flatten
+ rescue error
+ logger.warn(exception: error) { "searching for sensors" }
+ NO_MATCH
+ end
+
+ # Alternative to using basic auth, but here really only for testing with postman
+ @[Security(Level::Support)]
+ def get_token
+ response = get("/api/auth/token", headers: {"Accept" => "text"})
+ raise "issue obtaining token: #{response.status_code}\n#{response.body}" unless response.success?
+ response.body
+ end
+
+ @[Security(Level::Support)]
+ def get_logs
+ response = get("/api/info/log", headers: {"Accept" => "text"})
+ raise "issue obtaining logs: #{response.status_code}\n#{response.body}" unless response.success?
+ response.body
+ end
+
+ @[Security(Level::Support)]
+ def reset_count
+ response = get("/api/count-data/reset", headers: {"Accept" => "text/xml"})
+ check_success(response)
+ true
+ end
+
+ def is_alive?
+ response = get("/api/info/alive", headers: {"Accept" => "text/xml"})
+ check_success(response)
+ true
+ rescue
+ false
+ end
+
+ def count_data
+ response = get("/api/count-data", headers: {"Accept" => "text/xml"})
+ document = check_success(response)
+
+ lines = {} of String => NamedTuple(name: String, id: String, type: String, sensor: String, data: Hash(String, String | Int32 | Float32))
+ lines_xml = document.xpath_nodes("//lines/line")
+
+ self[:lines] = lines_xml.map do |line|
+ attrs = {} of String => String | Hash(String, Int32)
+ counts = {} of String => Int32
+ line.attributes.each { |attr| attrs[attr.name] = attr.content }
+ line.children.each { |child|
+ next if child.name == "text"
+ counts[child.name] = child.text.to_i
+ }
+ attrs["counts"] = counts
+ attrs
+ end
+ end
+
+ def capacity_data
+ response = get("/api/info/persistence", headers: {"Accept" => "text/xml"})
+ document = check_success(response)
+
+ last_checked = Time.utc.to_unix
+
+ {"line", "zone-occupancy", "zone-in-out"}.each do |count_name|
+ xml_key_name = "//count-#{count_name}-storage"
+ if count_data = document.xpath_nodes(xml_key_name).first?
+ count_type = count_name.split("-", 2)[0]
+ capacity = xpath_text(document, "#{xml_key_name}/capacity", &.to_i)
+
+ key = "#{count_name}-counts"
+ @state[key] = self[key] = document.xpath_nodes("#{xml_key_name}/count-#{count_type}s/count-#{count_type}").map_with_index { |zone, index|
+ attrs = {} of String => String | Int32 | Int64 | Nil
+
+ zone.children.each do |child|
+ content = child.text.strip
+ attrs[child.name] = case child.name
+ when "entry-count"
+ content.to_i
+ when "first-entry", "last-entry"
+ content.empty? ? nil : Time.parse!(content, "%Y-%m-%dT%H:%M:%S%z").to_unix
+ when "text"
+ next
+ else
+ content
+ end
+ end
+
+ last_entry = attrs["last-entry"].as(Int64?)
+ sensor = case count_name
+ when "line"
+ SensorDetail.new(SensorType::QueueSize, attrs["entry-count"].as(Int32).to_f, last_entry || last_checked, @mac, "line-#{index}", attrs["name"].as(String))
+ when "zone-occupancy"
+ SensorDetail.new(SensorType::PeopleCount, attrs["entry-count"].as(Int32).to_f, last_entry || last_checked, @mac, "zone-occupancy-#{index}", "Occupancy #{attrs["name"].as(String)}")
+ when "zone-in-out"
+ SensorDetail.new(SensorType::Counter, attrs["entry-count"].as(Int32).to_f, last_entry || last_checked, @mac, "zone-in-out-#{index}", "In Out #{attrs["name"].as(String)}")
+ else
+ next
+ end
+ sensor.capacity = capacity
+ sensor.last_entry = last_entry
+ sensor.first_entry = attrs["first-entry"].as(Int64?)
+ sensor
+ }.compact
+ end
+ end
+ true
+ end
+
+ # Combined `/info` and `/info/status`
+ def device_status
+ response = get("/api/info/sensor-status", headers: {"Accept" => "text/xml"})
+ document = check_success(response)
+
+ parse_type_info(document, "version")
+ parse_type_info(document, "temperature")
+
+ if sensor = parse_text_info(document, "sensor")
+ @mac = sensor["serial-number"]? || @mac
+ end
+ parse_text_info(document, "illumination")
+ parse_text_info(document, "configuration")
+ parse_text_info(document, "operation")
+
+ true
+ end
+
+ protected def xpath_text(document, path)
+ document.xpath_nodes(path).first?.try(&.text.strip)
+ end
+
+ protected def xpath_text(document, path)
+ if node = document.xpath_nodes(path).first?
+ yield node.text.strip
+ end
+ end
+
+ protected def parse_type_info(document, xpath_key) : Nil
+ ver_data = document.xpath_nodes("//#{xpath_key}s/#{xpath_key}")
+ attrs = {} of String => String
+ ver_data.each do |data|
+ key = data.attributes.find(&.name.==("type")).try &.content
+ next unless key
+ attrs[key] = data.text.strip
+ end
+ self[xpath_key] = attrs.empty? ? nil : attrs
+ end
+
+ protected def parse_text_info(document, status) : Hash(String, String)?
+ if keys = document.xpath_nodes("//#{status}").first?.try(&.children)
+ attrs = {} of String => String
+ keys.each do |data|
+ key = data.name
+ next if key == "text"
+ attrs[key.underscore] = data.text.strip
+ end
+ self[status] = attrs.empty? ? nil : attrs
+ else
+ self[status] = nil
+ end
+ end
+
+ protected def check_success(response)
+ raise "issue with request: #{response.status_code}\n#{response.body}" unless response.success?
+ document = parse_without_namespaces(response.body)
+ status = document.xpath_nodes("//request-status/status").first?.try &.text.strip
+ raise "request failed with #{status}\n#{response.body}" unless status == "OK"
+ sensor_time(document)
+ document
+ end
+
+ protected def sensor_time(document) : Time?
+ if time_text = document.xpath_nodes("//sensor-time").first?.try &.text
+ self[:sensor_time] = Time.parse!(time_text, "%Y-%m-%dT%H:%M:%S%z")
+ end
+ end
+
+ protected def parse_without_namespaces(xml : String)
+ xml = xml.strip
+ document = XML.parse(xml)
+ namespace_node = document.children[0].name == "xml" ? document.children[1].name : document.children[0].name
+ namespaces = document.children[0].namespaces.keys.compact_map { |name| name.starts_with?("xmlns:") ? "#{name[6..-1]}\\:" : nil }
+
+ # Clean up namespaces from node names
+ xml = xml.gsub(Regex.new(namespaces.join("|")), "")
+ # Replace namespace node
+ xml = xml.sub(Regex.new("<#{namespace_node}.+>"), "<#{namespace_node}>")
+
+ # Return the parsed document
+ XML.parse(xml)
+ end
+end
diff --git a/drivers/xovis/sensor_api_spec.cr b/drivers/xovis/sensor_api_spec.cr
new file mode 100644
index 00000000000..3674d7b8e37
--- /dev/null
+++ b/drivers/xovis/sensor_api_spec.cr
@@ -0,0 +1,278 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Xovis::SensorAPI" do
+ # =========================
+ # GET TOKEN
+ # =========================
+ retval = exec(:get_token)
+
+ # We should request a new token from Floorsense
+ expect_http_request do |request, response|
+ auth = request.headers["Authorization"]
+ if auth == "Basic YWNjb3VudDpwYXNzd29yZCE="
+ response.status_code = 200
+ response.output << "jwt_token"
+ else
+ response.status_code = 401
+ puts "invalid auth header #{auth}"
+ end
+ end
+
+ # What the function should return (for use in making further requests)
+ retval.get.should eq("jwt_token")
+
+ # =========================
+ # RESET COUNT
+ # =========================
+ retval = exec(:reset_count)
+
+ # We should request a new token from Floorsense
+ expect_http_request do |_request, response|
+ response.status_code = 200
+ response.output << %(
+
+ 2020-05-04T12:34:46Z
+
+ OK
+
+ )
+ end
+
+ # What the function should return (for use in making further requests)
+ retval.get.should eq(true)
+ status["sensor_time"].should eq("2020-05-04T12:34:46Z")
+
+ # =========================
+ # COUNT DATA
+ # =========================
+ retval = exec(:count_data)
+
+ # We should request a new token from Floorsense
+ expect_http_request do |_request, response|
+ response.status_code = 200
+ response.output << %(
+
+
+
+
+ 0
+ 0
+
+
+
+ 2020-05-05T11:20:47+02:00
+
+ OK
+
+ )
+ end
+
+ # What the function should return (for use in making further requests)
+ line_data = [{
+ "name" => "Line 0",
+ "id" => "0",
+ "sensor-type" => "SINGLE_SENSOR",
+ "counts" => {
+ "fw-count" => 0,
+ "bw-count" => 0,
+ },
+ }]
+ retval.get.should eq(line_data)
+ status["lines"].should eq(line_data)
+
+ # =========================
+ # DEVICE INFO
+ # =========================
+ retval = exec(:device_status)
+
+ # We should request a new token from Floorsense
+ expect_http_request do |_request, response|
+ response.status_code = 200
+ response.output << <<-XML
+
+
+ OK
+ 2020-05-05T13:11:38+02:00 81551360
+
+ 5
+ AB E
+ B
+ 1.2.12 4.3.1 (5b57718)
+
+ 80:1F:12:73:2F:A4 192.168.1.115
+ S01
+ Test
+ PC2S
+ PC2S
+
+ 49.0
+ 46.0
+
+ 8.0 1.20166 0.0 0.0139272 true
+
+ true 85.823784 8.23138
+ 0.143171 0.98707 0.0720739
+
+ false
+
+ false 492810AF623279442C87D2D65D4A6240 2020-05-05T12:22:10+02:00 false
+
+ tracking 1018951 1 true Europe/Zurich
+
+ OK
+
+ XOVIS-PC
+ 192.168.1.115 255.255.255.0 192.168.1.1
+ 192.168.1.1
+
+ false
+ false
+
+ true 2020-05-05T13:06:58+02:00 91 false
+
+
+ sensor-support.xovis.com:443 true
+ true true true true 2020-05-05T02:11:07+02:002020-05-05T02:02:53+02:00false
+
+
+ XML
+ end
+
+ # What the function should return (for use in making further requests)
+ retval.get.should eq(true)
+ status["version"].should eq({
+ "HW" => "5",
+ "PROD" => "AB",
+ "BOM" => "E",
+ "PCB" => "B",
+ "FW" => "1.2.12",
+ "SW" => "4.3.1 (5b57718)",
+ })
+ status["temperature"].should eq({
+ "die" => "49.0",
+ "housing" => "46.0",
+ })
+ status["sensor"].should eq({
+ "serial-number" => "80:1F:12:73:2F:A4",
+ "ip-address" => "192.168.1.115",
+ "name" => "S01",
+ "group" => "Test",
+ "type" => "PC2S",
+ "device-type" => "PC2S",
+ })
+
+ # =========================
+ # ALIVE CHECK
+ # =========================
+ retval = exec(:is_alive?)
+
+ # We should request a new token from Floorsense
+ expect_http_request do |_request, response|
+ response.status_code = 200
+ response.output << %(
+
+ 2020-05-04T12:34:46Z
+
+ OK
+
+ )
+ end
+
+ # What the function should return (for use in making further requests)
+ retval.get.should eq(true)
+
+ # =========================
+ # CAPACITY DATA
+ # =========================
+ retval = exec(:capacity_data)
+
+ # We should request a new token from Floorsense
+ expect_http_request do |_request, response|
+ response.status_code = 200
+ response.output << %(
+
+ 2020-05-05T13:06:06+02:00
+
+ OK
+
+
+ 100
+
+
+ Line 0
+ 0
+ 2020-04-27T11:40:00+02:00
+ 2020-05-05T13:05:00+02:00
+ 9
+
+
+
+
+ 80
+
+
+ Zone 0
+ 0
+ 2020-05-05T12:22:00+02:00
+ 2020-05-05T13:05:00+02:00
+ 1
+
+
+
+
+ 80
+
+
+ Zone 0
+ 0
+ 2020-05-05T12:22:00+02:00
+ 2020-05-05T13:05:00+02:00
+ 1
+
+
+
+ )
+ end
+
+ # What the function should return (for use in making further requests)
+ retval.get.should eq(true)
+ status["line-counts"].should eq([{
+ "status" => "normal",
+ "type" => "queue_size",
+ "value" => 9.0,
+ "last_seen" => 1588676700,
+ "mac" => "80:1F:12:73:2F:A4",
+ "id" => "line-0",
+ "name" => "Line 0",
+ "location" => "sensor",
+ "capacity" => 100,
+ "first_entry" => 1587980400,
+ "last_entry" => 1588676700,
+ }])
+ status["zone-occupancy-counts"].should eq([{
+ "status" => "normal",
+ "type" => "people_count",
+ "value" => 1.0,
+ "last_seen" => 1588676700,
+ "mac" => "80:1F:12:73:2F:A4",
+ "id" => "zone-occupancy-0",
+ "name" => "Occupancy Zone 0",
+ "location" => "sensor",
+ "capacity" => 80,
+ "first_entry" => 1588674120,
+ "last_entry" => 1588676700,
+ }])
+ status["zone-in-out-counts"].should eq([{
+ "status" => "normal",
+ "type" => "counter",
+ "value" => 1.0,
+ "last_seen" => 1588676700,
+ "mac" => "80:1F:12:73:2F:A4",
+ "id" => "zone-in-out-0",
+ "name" => "In Out Zone 0",
+ "location" => "sensor",
+ "capacity" => 80,
+ "first_entry" => 1588674120,
+ "last_entry" => 1588676700,
+ }])
+end
diff --git a/drivers/xy_sense/location_service.cr b/drivers/xy_sense/location_service.cr
new file mode 100644
index 00000000000..c67cf9097d9
--- /dev/null
+++ b/drivers/xy_sense/location_service.cr
@@ -0,0 +1,233 @@
+require "json"
+require "oauth2"
+require "placeos-driver"
+require "placeos-driver/interface/locatable"
+
+class XYSense::LocationService < PlaceOS::Driver
+ include Interface::Locatable
+
+ descriptive_name "XY Sense Locations"
+ generic_name :XYLocationService
+ description %(collects desk booking data from the staff API and overlays XY Sense data for visualising on a map)
+
+ accessor area_manager : AreaManagement_1
+ accessor xy_sense : XYSense_1
+ bind XYSense_1, :floors, :floor_details_changed
+
+ default_settings({
+ floor_mappings: {
+ "xy-sense-floor-id": {
+ zone_id: "placeos-zone-id",
+ name: "friendly name for documentation",
+ },
+ },
+ })
+
+ @floor_mappings : Hash(String, NamedTuple(zone_id: String)) = {} of String => NamedTuple(zone_id: String)
+ @zone_filter : Array(String) = [] of String
+
+ def on_update
+ @floor_mappings = setting(Hash(String, NamedTuple(zone_id: String)), :floor_mappings)
+ @zone_filter = @floor_mappings.map { |_, detail| detail[:zone_id] }
+
+ schedule.clear
+ schedule.every(30.minutes) { sync_floor_states }
+ end
+
+ # ===================================
+ # Bindings into xy-sense data
+ # ===================================
+ class FloorDetails
+ include JSON::Serializable
+
+ property floor_id : String
+ property floor_name : String
+ property location_id : String
+ property location_name : String
+
+ property spaces : Array(SpaceDetails)
+ end
+
+ class SpaceDetails
+ include JSON::Serializable
+
+ property id : String
+ property name : String?
+ property capacity : Int32
+ property category : String
+ end
+
+ class Occupancy
+ include JSON::Serializable
+
+ property status : String
+ property headcount : Int32
+ property space_id : String
+
+ @[JSON::Field(converter: Time::Format.new("%FT%T", Time::Location::UTC))]
+ property collected : Time
+
+ @[JSON::Field(ignore: true)]
+ property! details : SpaceDetails
+ end
+
+ # Floor id => subscription
+ @floor_subscriptions = {} of String => PlaceOS::Driver::Subscriptions::Subscription
+ @space_details = {} of String => SpaceDetails
+ @change_lock = Mutex.new
+
+ def update_space_details
+ @change_lock.synchronize do
+ # Get the floor details from either the status push event or module update
+ floors = xy_sense.status(Hash(String, FloorDetails), :floors)
+ space_details = {} of String => SpaceDetails
+
+ floors.each do |floor_id, floor|
+ mapping = @floor_mappings[floor_id]?
+ next unless mapping
+
+ # track space data
+ floor.spaces.each { |space| space_details[space.id] = space }
+ end
+
+ # update to new space details
+ @space_details = space_details
+ end
+ end
+
+ protected def floor_details_changed(_sub = nil, payload = nil)
+ @change_lock.synchronize do
+ # Get the floor details from either the status push event or module update
+ floors = payload ? Hash(String, FloorDetails).from_json(payload) : xy_sense.status(Hash(String, FloorDetails), :floors)
+ space_details = {} of String => SpaceDetails
+
+ # work out what we should be watching
+ monitor = {} of String => String
+ floors.each do |floor_id, floor|
+ mapping = @floor_mappings[floor_id]?
+ next unless mapping
+
+ monitor[floor_id] = mapping[:zone_id]
+
+ # track space data
+ floor.spaces.each { |space| space_details[space.id] = space }
+ end
+
+ # unsubscribe from floors we're not interested in
+ existing = @floor_subscriptions.keys
+ desired = monitor.keys
+ (existing - desired).each { |sub| subscriptions.unsubscribe @floor_subscriptions.delete(sub).not_nil! }
+
+ # update to new space details
+ @space_details = space_details
+
+ # Subscribe to new data
+ (desired - existing).each { |floor_id|
+ zone_id = monitor[floor_id]
+ @floor_subscriptions[floor_id] = xy_sense.subscribe(floor_id) do |_sub, message|
+ level_state_change(zone_id, Array(Occupancy).from_json(message))
+ end
+ }
+ end
+ end
+
+ def floor_subscriptions
+ @floor_subscriptions.keys
+ end
+
+ def sync_floor_states
+ logger.debug { "-- updating space details..." }
+ details = update_space_details
+ logger.debug { "-- details:\n#{details}" }
+
+ logger.debug { "-- grabbing floor details..." }
+ xy = xy_sense
+ @change_lock.synchronize do
+ floor_subscriptions.each do |zone_id|
+ level_state_change(zone_id, xy.status(Array(Occupancy), zone_id))
+ end
+ end
+ logger.debug { "-- floor states synced!" }
+ @occupancy_mappings
+ end
+
+ # Zone_id => area => occupancy details
+ @occupancy_mappings : Hash(String, Hash(String, Occupancy)) = {} of String => Hash(String, Occupancy)
+
+ def level_state_change(zone_id : String, spaces : Array(Occupancy))
+ area_occupancy = {} of String => Occupancy
+ spaces.each do |space|
+ space.details = @space_details[space.space_id]
+ space_name = space.details.name
+ unless space_name
+ logger.warn { "missing space name for id #{space.details.id}" }
+ next
+ end
+ area_occupancy[space_name] = space
+ end
+ @occupancy_mappings[zone_id] = area_occupancy
+ area_manager.update_available({zone_id})
+ rescue error
+ logger.error(exception: error) { "error updating level #{zone_id} space changes" }
+ end
+
+ # ===================================
+ # Locatable Interface functions
+ # ===================================
+ def locate_user(email : String? = nil, username : String? = nil)
+ logger.debug { "sensor incapable of locating #{email} or #{username}" }
+ [] of Nil
+ end
+
+ def macs_assigned_to(email : String? = nil, username : String? = nil) : Array(String)
+ logger.debug { "sensor incapable of tracking #{email} or #{username}" }
+ [] of String
+ end
+
+ def check_ownership_of(mac_address : String) : OwnershipMAC?
+ logger.debug { "sensor incapable of tracking #{mac_address}" }
+ nil
+ end
+
+ def device_locations(zone_id : String, location : String? = nil)
+ logger.debug { "searching locatable in zone #{zone_id}" }
+ return [] of Nil unless @zone_filter.includes?(zone_id)
+
+ @occupancy_mappings[zone_id].compact_map do |space_name, space|
+ # Assume this means we're looking at a desk
+ capacity = space.details.capacity
+ if capacity == 1
+ next unless space.headcount > 0
+ next if location.presence && location != "desk"
+
+ {
+ location: :desk,
+ at_location: space.headcount,
+ map_id: space_name,
+ level: zone_id,
+ capacity: capacity,
+
+ xy_sense_space_id: space.space_id,
+ xy_sense_status: space.status,
+ xy_sense_collected: space.collected.to_unix,
+ xy_sense_category: space.details.category,
+ }
+ else
+ next if location.presence && location != "area"
+
+ {
+ location: :area,
+ at_location: space.headcount,
+ map_id: space_name,
+ level: zone_id,
+ capacity: capacity,
+
+ xy_sense_space_id: space.space_id,
+ xy_sense_status: space.status,
+ xy_sense_collected: space.collected.to_unix,
+ xy_sense_category: space.details.category,
+ }
+ end
+ end
+ end
+end
diff --git a/drivers/xy_sense/location_service_spec.cr b/drivers/xy_sense/location_service_spec.cr
new file mode 100644
index 00000000000..3a1142ed47f
--- /dev/null
+++ b/drivers/xy_sense/location_service_spec.cr
@@ -0,0 +1,80 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "XYSense::LocationService" do
+ system({
+ XYSense: {XYSenseMock},
+ AreaManagement: {AreaManagementMock},
+ })
+
+ now = Time.local
+ start = now.at_beginning_of_day.to_unix
+ ending = now.at_end_of_day.to_unix
+
+ resp = exec(:device_locations, "placeos-zone-id").get
+ puts resp
+ resp.should eq([
+ {"location" => "desk", "at_location" => 1, "map_id" => "desk-456", "level" => "placeos-zone-id", "capacity" => 1, "xy_sense_space_id" => "xysense-desk-456-id", "xy_sense_status" => "recentlyOccupied", "xy_sense_collected" => 1605088820, "xy_sense_category" => "Workpoint"},
+ {"location" => "area", "at_location" => 8, "map_id" => "area-567", "level" => "placeos-zone-id", "capacity" => 20, "xy_sense_space_id" => "xysense-area-567-id", "xy_sense_status" => "currentlyOccupied", "xy_sense_collected" => 1605088820, "xy_sense_category" => "Lobby"},
+ ])
+end
+
+# :nodoc:
+class XYSenseMock < DriverSpecs::MockDriver
+ def on_load
+ self[:floors] = {
+ "xy-sense-floor-id" => {
+ floor_id: "xy-sense-floor-id",
+ floor_name: "Fancy floor",
+ location_id: "xysense-building",
+ location_name: "Fancy building",
+ spaces: [{
+ id: "xysense-desk-123-id",
+ name: "desk-123",
+ capacity: 1,
+ category: "Workpoint",
+ },
+ {
+ id: "xysense-desk-456-id",
+ name: "desk-456",
+ capacity: 1,
+ category: "Workpoint",
+ },
+ {
+ id: "xysense-area-567-id",
+ name: "area-567",
+ capacity: 20,
+ category: "Lobby",
+ }],
+ },
+ }
+
+ self["xy-sense-floor-id"] = [
+ {
+ status: "notOccupied",
+ headcount: 0,
+ space_id: "xysense-desk-123-id",
+ collected: "2020-11-11T10:00:20",
+ },
+ {
+ status: "recentlyOccupied",
+ headcount: 1,
+ space_id: "xysense-desk-456-id",
+ collected: "2020-11-11T10:00:20",
+ },
+ {
+ status: "currentlyOccupied",
+ headcount: 8,
+ space_id: "xysense-area-567-id",
+ collected: "2020-11-11T10:00:20",
+ },
+ ]
+ end
+end
+
+# :nodoc:
+class AreaManagementMock < DriverSpecs::MockDriver
+ def update_available(zones : Array(String))
+ logger.info { "requested update to #{zones}" }
+ nil
+ end
+end
diff --git a/drivers/zencontrol/advanced_tpi.cr b/drivers/zencontrol/advanced_tpi.cr
new file mode 100644
index 00000000000..540a5948a5e
--- /dev/null
+++ b/drivers/zencontrol/advanced_tpi.cr
@@ -0,0 +1,226 @@
+require "placeos-driver"
+require "placeos-driver/interface/lighting"
+require "bindata"
+
+# Documentation: https://aca.im/driver_docs/zencontrol/Advanced_Third_Party_Interface_API_Document.pdf
+
+class Zencontrol::AdvancedTPI < PlaceOS::Driver
+ include Interface::Lighting::Scene
+ include Interface::Lighting::Level
+ alias Area = Interface::Lighting::Area
+
+ generic_name :Lighting
+ descriptive_name "Zencontrol Advanced Lighting API"
+ description "Uses the advanced zencontrol third party interface UDP or TCP API"
+
+ # NOTE:: Multicast update events are sent on address: 239.255.90.67 port: 6969
+ udp_port 5108
+
+ default_settings({
+ api_version: 4,
+ })
+
+ def on_load
+ # size is the 3rd byte
+ transport.tokenizer = Tokenizer.new do |io|
+ bytes = io.peek
+ # Ensure message indicator is well-formed
+ logger.debug { "Received: #{bytes.hexstring}" }
+ # [type, sequence, length, [data], checksum]
+ # return 0 if the message is incomplete
+ bytes.size < 3 ? 0 : (bytes[2].to_i + 4)
+ end
+
+ on_update
+ end
+
+ def on_update
+ @version = setting?(UInt8, :api_version) || 4_u8
+ end
+
+ @version : UInt8 = 4_u8
+ @sequence : UInt8 = 0_u8
+
+ protected def next_sequence_num
+ seq = @sequence
+ if seq == 255_u8
+ @sequence = 0_u8
+ else
+ @sequence = seq + 1_u8
+ end
+ seq
+ end
+
+ # Using indirect commands
+ def trigger(area : UInt32, scene : UInt32)
+ area = Area.new(area)
+ set_lighting_scene(scene, area)
+ end
+
+ # Using direct command
+ def light_level(area : UInt32, level : Float64)
+ area = Area.new(area)
+ set_lighting_level(level, area)
+ end
+
+ # ==================
+ # Lighting Interface
+ # ==================
+
+ def set_lighting_scene(scene : UInt32, area : Area? = nil, fade_time : UInt32 = 1000_u32)
+ # Most likely you just want to call a scene on a paricular group by adding 64 to the group number for Address.
+ area = area.as(Area)
+ area_id = area.id.as(UInt32)
+ area_id = area_id.clamp(0, 191) + 64 unless area_id == 0xFF_u32
+
+ # DALI_SCENE
+ self[area.to_s] = scene
+ basic_request(0xA1_u8, area_id.to_u8, scene)
+ end
+
+ def lighting_scene?(area : Area? = nil)
+ # DALI_QUERY_LAST_SCENE
+ area_id = area.as(Area).id.as(UInt32).clamp(0, 191) + 64
+ basic_request(0xAD_u8, area_id.to_u8)
+ end
+
+ LEVEL_PERCENTAGE = 0xFF / 100
+
+ def set_lighting_level(level : Float64, area : Area? = nil, fade_time : UInt32 = 1000_u32)
+ # Levels can be called on groups by adding 64 to the group number
+ area = area.as(Area)
+ area_id = area.id.as(UInt32)
+ area_id = area_id.clamp(0, 191) + 64 unless area_id == 0xFF_u32
+
+ # Levels are percentage based (on the PlaceOS side)
+ level = level.clamp(0.0, 100.0)
+ level_actual = (level * LEVEL_PERCENTAGE).round.to_u32
+
+ # DALI_ARC_LEVEL
+ basic_request(0xA2_u8, area_id.to_u8, level_actual)
+ end
+
+ def lighting_level?(area : Area? = nil)
+ # DALI_QUERY_LEVEL
+ area_id = area.as(Area).id.as(UInt32).clamp(0, 191) + 64
+ basic_request(0xAA_u8, area_id.to_u8)
+ end
+
+ # ==================
+ # Request Building
+ # ==================
+
+ class BasicRequest < BinData
+ endian big
+
+ uint8 :version
+ uint8 :sequence
+ uint8 :command
+ uint8 :address
+ bit_field do
+ bits 24, :data
+ end
+ uint8 :checksum, value: ->{
+ version ^ sequence ^ command ^ address ^ (data >> 16 & 0xFF).to_u8 ^ (data >> 8 & 0xFF).to_u8 ^ (data & 0xFF).to_u8
+ }
+ end
+
+ class ::PlaceOS::Driver::Task
+ property request_payload : Zencontrol::AdvancedTPI::BasicRequest? = nil
+ end
+
+ protected def basic_request(command : UInt8, address : UInt8, data : UInt32 = 0_u32, **options)
+ # build the message
+ request = BasicRequest.new
+ request.version = @version
+ request.sequence = next_sequence_num
+ request.command = command
+ request.address = address
+ request.data = data
+
+ # send the request
+ send(request, **options)
+ end
+
+ # ====================
+ # RESPONSE PROCESSING
+ # ====================
+
+ ERROR_CODES = {
+ 0x01_u8 => "The checksum check failed",
+ 0x02_u8 => "A short on the DALI line was detected",
+ 0x03_u8 => "A receive error occured",
+ 0x04_u8 => "The command in the request is unrecognised",
+ 0xB0_u8 => "The command requested relies on a paid feature that hasn't been purchsed",
+ 0xB1_u8 => "Invalid arguments supplied for the given command in the re quest",
+ 0xB2_u8 => "The command couldn't be processed",
+ 0xB3_u8 => "The queue or buffer that's required to process the command in the request
+ is full or broken",
+ 0xB4_u8 => "The command in the request may stream multiple responses back, but this
+ feature isn't available for some reason",
+ 0xB5_u8 => "The DALI related request couldn't be processed due to an error",
+ 0xB6_u8 => "There are an insufficient number of the required resource remaining service
+ the request",
+ 0xB7_u8 => "An unexpected result occurred",
+ }
+
+ enum ResponseType
+ Okay = 0xA0
+ Answer = 0xA1
+ NoAnswer = 0xA2
+ Error = 0xA3
+ end
+
+ class ResponseFrame < BinData
+ endian big
+
+ enum_field UInt8, type : ResponseType = ResponseType::Error
+ uint8 :sequence
+ uint8 :size
+ bytes :bytes, length: ->{ size }
+ uint8 :checksum, verify: ->{
+ sum = type.to_u8 ^ sequence ^ size
+ checksum == bytes.reduce(sum) { |acc, i| i ^ acc }
+ }
+ end
+
+ def received(data, task)
+ logger.debug { "Zencontrol sent: #{data.hexstring}" }
+
+ io = IO::Memory.new(data)
+ response = io.read_bytes ResponseFrame
+
+ case response.type
+ when .okay?, .no_answer?
+ # no processing required
+ when .answer?
+ if (request = task.try(&.request_payload)) && request.sequence == response.sequence
+ case request.command
+ when 0xAD_u8 # DALI_QUERY_LAST_SCENE
+ area = Area.new((request.address - 64_u8).to_u32)
+ self[area.to_s] = response.bytes[0]
+ when 0xAA_u8 # DALI_QUERY_LEVEL
+ area = Area.new((request.address - 64_u8).to_u32)
+ self[area.append("level").to_s] = response.bytes[0]
+ else
+ logger.debug { "unknown answer for #{request.command.to_s(16)}\n - req: #{request.to_slice.hexstring}\n - resp: #{response.to_slice.hexstring}" }
+ end
+ end
+ when .error?
+ error_code = response.bytes[0]
+ error_message = ERROR_CODES[error_code]?
+ logger.error { "request failed with code #{error_code}, message: #{error_message}" }
+ return task.try &.abort(error_message)
+ end
+
+ # check if we are expecting a frame
+ if request = task.try(&.request_payload)
+ if request.sequence == response.sequence
+ return task.try &.success
+ else # ignore this packet
+ return
+ end
+ end
+ task.try &.success
+ end
+end
diff --git a/drivers/zencontrol/advanced_tpi_spec.cr b/drivers/zencontrol/advanced_tpi_spec.cr
new file mode 100644
index 00000000000..64ffdaca7de
--- /dev/null
+++ b/drivers/zencontrol/advanced_tpi_spec.cr
@@ -0,0 +1,13 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Zencontrol::AdvancedTPI" do
+ exec(:trigger, 0xFF, 1)
+ should_send Bytes[0x04, 0x00, 0xA1, 0xFF, 0x00, 0x00, 0x01, 0x5B]
+ responds Bytes[0xA0, 0x00, 0x00, 0xA0]
+ status["area255"].should eq(1)
+
+ exec(:lighting_scene?, {id: 2})
+ should_send Bytes[0x04, 0x01, 0xAD, 66, 0x00, 0x00, 0x00, 0xea]
+ responds Bytes[0xA1, 0x01, 0x01, 4, 0xA5]
+ status["area2"].should eq(4)
+end
diff --git a/drivers/zencontrol/classic_tpi.cr b/drivers/zencontrol/classic_tpi.cr
new file mode 100644
index 00000000000..4e91eba5fb1
--- /dev/null
+++ b/drivers/zencontrol/classic_tpi.cr
@@ -0,0 +1,105 @@
+require "placeos-driver"
+require "placeos-driver/interface/lighting"
+
+# this is the original third party interface
+# Documentation: https://aca.im/driver_docs/zencontrol/lighting_udp.pdf
+
+class Zencontrol::ClassicTPI < PlaceOS::Driver
+ include Interface::Lighting::Scene
+ include Interface::Lighting::Level
+ alias Area = Interface::Lighting::Area
+
+ generic_name :Lighting
+ descriptive_name "Zencontrol Classic Lighting API"
+ description "Uses the classic zencontrol third party interface UDP API"
+
+ udp_port 5108
+
+ default_settings({
+ version: 1,
+ controller_id: "ffffffffffff",
+ })
+
+ def on_load
+ # Communication settings
+ queue.wait = false
+ on_update
+ end
+
+ BROADCAST = Bytes[0xff, 0xff, 0xff, 0xff, 0xff, 0xff]
+
+ @version : UInt8 = 1_u8
+ @controller : Bytes = BROADCAST
+
+ def on_update
+ @version = setting?(UInt8, :version) || 1_u8
+ controller = setting?(String, :controller_id)
+
+ if controller
+ @controller = controller.rjust(12, '0').hexbytes
+ else
+ @controller = BROADCAST
+ end
+ end
+
+ # Using indirect commands
+ def trigger(area : UInt32, scene : UInt32)
+ area = Area.new(area)
+ set_lighting_scene(scene, area)
+ end
+
+ # Using direct command
+ def light_level(area : UInt32, level : Float64)
+ area = Area.new(area)
+ set_lighting_level(level, area)
+ end
+
+ # ==================
+ # Lighting Interface
+ # ==================
+
+ def set_lighting_scene(scene : UInt32, area : Area? = nil, fade_time : UInt32 = 1000_u32)
+ area = area.as(Area)
+ scene = scene.clamp(0, 15) + 16
+ area_id = area.id.as(UInt32).clamp(0, 127) + 128
+
+ self[area.to_s] = scene
+ do_send(area_id.to_u8, scene.to_u8)
+ end
+
+ def lighting_scene?(area : Area? = nil)
+ self[area.to_s]? if area
+ end
+
+ LEVEL_PERCENTAGE = 0xFF / 100
+
+ def set_lighting_level(level : Float64, area : Area? = nil, fade_time : UInt32 = 1000_u32)
+ area = area.as(Area)
+
+ # Levels are percentage based (on the PlaceOS side)
+ level = level.clamp(0.0, 100.0)
+ level_actual = (level * LEVEL_PERCENTAGE).round.to_u8
+ area_id = area.id.as(UInt32).clamp(0, 127).to_u8
+
+ self[area.append("level").to_s] = level
+ do_send(area_id, level_actual)
+ end
+
+ def lighting_level?(area : Area? = nil)
+ self[area.append("level").to_s]? if area
+ end
+
+ protected def do_send(address : UInt8, command : UInt8, **options)
+ io = IO::Memory.new
+ io.write_byte @version
+ io.write @controller
+ io.write_byte address
+ io.write_byte command
+ send(io.to_slice, **options)
+ end
+
+ def received(data, task)
+ logger.debug { "Zencontrol sent: #{data.hexstring}" }
+ task.try &.success
+ end
+end
diff --git a/drivers/zencontrol/classic_tpi_spec.cr b/drivers/zencontrol/classic_tpi_spec.cr
new file mode 100644
index 00000000000..89ff035421e
--- /dev/null
+++ b/drivers/zencontrol/classic_tpi_spec.cr
@@ -0,0 +1,7 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Zencontrol::ClassicTPI" do
+ exec(:light_level, 0x4F, 94.2)
+ should_send("\x01\xFF\xFF\xFF\xFF\xFF\xFF\x4F\xF0")
+ status["area79_level"].should eq(94.2)
+end
diff --git a/drivers/zoom/booking_converter.cr b/drivers/zoom/booking_converter.cr
new file mode 100644
index 00000000000..566ca9ec81b
--- /dev/null
+++ b/drivers/zoom/booking_converter.cr
@@ -0,0 +1,96 @@
+require "placeos-driver"
+require "place_calendar"
+
+class Zoom::BookingConverter < PlaceOS::Driver
+ descriptive_name "Convert Zoom Bookings to PlaceOS Calendar Events"
+ generic_name :Bookings
+ description %(Retrieves bookings from Zoom CSAPI Module and exposes them as PlaceOS Calendar events)
+
+ # default_settings({
+ # })
+
+ accessor zoom_csapi : ZoomCSAPI_1
+
+ def on_load
+ on_update
+ end
+
+ def on_update
+ subscriptions.clear
+ subscription = system.subscribe(:ZoomCSAPI_1, :BookingsListResult) do |_subscription, new_data|
+ zoom_bookings_list = Array(JSON::Any).from_json(new_data)
+ logger.debug { "Detected changed in Zoom Bookings List: : #{zoom_bookings_list.inspect}" }
+ expose_bookings(zoom_bookings_list)
+ end
+ # ensure current booking is updated at the start of every minute
+ # rand spreads the load placed on redis
+ schedule.cron("* * * * *") do
+ schedule.in(rand(1000).milliseconds) do
+ if list = self[:bookings]?
+ determine_current_booking(list.as_a)
+ determine_next_booking(list.as_a)
+ end
+ end
+ end
+ end
+
+ private def expose_bookings(zoom_bookings_list : Array(JSON::Any))
+ placeos_bookings = [] of Hash(String, Array(Bool) | Bool | Int64 | String | Nil)
+ zoom_bookings_list.each do |zoom_booking|
+ placeos_bookings << convert_booking(zoom_booking)
+ end
+ self[:bookings] = placeos_bookings
+ end
+
+ private def convert_booking(zoom_booking : JSON::Any)
+ {
+ "title" => zoom_booking["meetingName"].as_s,
+ "body" => zoom_booking["location"].as_s,
+ "location" => zoom_booking["location"].as_s,
+ "event_start" => Time.parse_rfc3339(zoom_booking["startTime"].as_s).to_unix,
+ "event_end" => Time.parse_rfc3339(zoom_booking["endTime"].as_s).to_unix,
+ "id" => zoom_booking["meetingNumber"].as_s,
+
+ "recurring_event_id" => nil,
+ "attendees" => [] of Bool,
+ "attachments" => [] of Bool,
+ "timezone" => nil,
+ "recurring" => false,
+ "created" => nil,
+ "updated" => nil,
+ "recurrence" => nil,
+ "status" => nil,
+ "creator" => nil,
+ "ical_uid" => nil,
+ "private" => false,
+ "all_day" => false
+ }
+ end
+
+ private def determine_current_booking(bookings : Array(JSON::Any))
+ if bookings.empty?
+ self[:current_booking] = nil
+ self[:booking_in_progress] = false
+ return
+ end
+ current_time = Time.utc.to_unix
+ current_booking = bookings.find do |booking|
+ booking["event_start"].as_i64 <= current_time && booking["event_end"].as_i64 > current_time
+ end
+ self[:current_booking] = current_booking || nil
+ self[:booking_in_progress] = !current_booking.nil?
+ end
+
+ # This assumes the Zoom bookings are sorted by start time, which is still TBD
+ private def determine_next_booking(bookings : Array(JSON::Any))
+ if bookings.empty?
+ self[:next_booking] = nil
+ return
+ end
+ current_time = Time.utc.to_unix
+ next_booking = bookings.find do |booking|
+ booking["event_start"].as_i64 > current_time
+ end
+ self[:next_booking] = next_booking || nil
+ end
+end
diff --git a/drivers/zoom/booking_converter_spec.cr b/drivers/zoom/booking_converter_spec.cr
new file mode 100644
index 00000000000..301371b2962
--- /dev/null
+++ b/drivers/zoom/booking_converter_spec.cr
@@ -0,0 +1 @@
+require "placeos-driver/spec"
diff --git a/drivers/zoom/rooms_api.cr b/drivers/zoom/rooms_api.cr
new file mode 100644
index 00000000000..93724d890b1
--- /dev/null
+++ b/drivers/zoom/rooms_api.cr
@@ -0,0 +1,550 @@
+require "placeos-driver"
+require "base64"
+require "json"
+require "jwt"
+
+# Documentation: https://developers.zoom.us/docs/api/rooms/
+
+class Zoom::RoomsApi < PlaceOS::Driver
+ descriptive_name "Zoom Rooms Cloud REST API"
+ generic_name :ZoomAPI
+ description %(
+ Zoom Rooms Cloud REST API Control driver for managing and controlling Zoom Room devices.
+
+ Requirements:
+ - OAuth 2.0 authentication (Server-to-Server OAuth app recommended)
+ - Required scopes: room:read:admin, room:write:admin, zoom_rooms:update:room_control:admin
+ - Calendar API access (Microsoft Exchange or Google Calendar) for room check-in/out features
+ )
+
+ uri_base "https://api.zoom.us"
+
+ default_settings({
+ account_id: "your_account_id",
+ client_id: "your_client_id",
+ client_secret: "your_client_secret",
+
+ sdk_client_id: "your_client_id",
+ sdk_client_secret: "your_client_secret",
+ })
+
+ def on_update
+ # Read settings
+ @account_id = setting(String, :account_id)
+ @client_id = setting(String, :client_id)
+ @client_secret = setting(String, :client_secret)
+ @sdk_client_id = setting?(String, :sdk_client_id) || @client_id
+ @sdk_client_secret = setting?(String, :sdk_client_secret) || @client_secret
+ end
+
+ getter client_id : String = ""
+ getter sdk_client_id : String = ""
+
+ @auth_token : AccessToken? = nil
+ @account_id : String = ""
+ @client_secret : String = ""
+ @sdk_client_secret : String = ""
+
+ record AccessToken, access_token : String, token_type : String, expires_in : Int32, scope : String?, api_url : String do
+ include JSON::Serializable
+
+ @[JSON::Field(ignore: true)]
+ getter! expiry : Time
+
+ def after_initialize
+ @expiry = Time.utc + expires_in.seconds
+ end
+
+ def expired?
+ 1.minute.from_now > expiry
+ end
+ end
+
+ # Authentication
+ private def authenticate : String
+ auth_token = @auth_token
+ if auth_token.nil? || (auth_token && auth_token.expired?)
+ token_url = "https://zoom.us/oauth/token"
+ http_uri_override = "https://zoom.us"
+ body = URI::Params.build do |form|
+ form.add("grant_type", "account_credentials")
+ form.add("account_id", @account_id)
+ end
+ response = post(
+ "/oauth/token",
+ headers: HTTP::Headers{
+ "Authorization" => "Basic #{Base64.strict_encode("#{@client_id}:#{@client_secret}")}",
+ "Content-Type" => "application/x-www-form-urlencoded",
+ },
+ body: body
+ )
+
+ if response.success?
+ logger.debug { "Successfully authenticated with Zoom API:\n#{response.body}" }
+ @auth_token = auth_token = AccessToken.from_json(response.body)
+
+ # TODO:: fix this, needs to be against the transport
+ http_uri_override = auth_token.api_url
+ else
+ logger.error { "Failed to authenticate: #{response.status_code}\n#{response.body}" }
+ raise "Authentication failed: #{response.status_code}, response: #{response.body}"
+ end
+ end
+ @auth_token.as(AccessToken).access_token
+ end
+
+ enum Role
+ Participant = 0
+ Host
+ end
+
+ @[Security(Level::Administrator)]
+ def generate_jwt(meeting_number : String, issued_at : Int64? = nil, expires_at : Int64? = nil, role : Role? = nil)
+ iat = issued_at || 2.minutes.ago.to_unix # issued at time, 2 minutes earlier to avoid clock skew
+ exp = expires_at || 2.hours.from_now.to_unix # token expires after 2 hours
+
+ # https://developers.zoom.us/docs/meeting-sdk/auth/
+ payload = {
+ "appKey" => @sdk_client_id,
+ # "sdkKey" => @client_id, # no longer needed
+ "mn" => meeting_number,
+ "role" => (role || Role::Participant).to_i,
+ "iat" => iat,
+ "exp" => exp,
+ "tokenExp" => exp,
+ }
+
+ JWT.encode(payload, @sdk_client_secret, JWT::Algorithm::HS256)
+ end
+
+ private def api_request(method : String, resource : String, body = nil, params : Hash(String, String)? = nil)
+ token = authenticate
+
+ headers = {
+ "Authorization" => "Bearer #{token}",
+ "Content-Type" => "application/json",
+ }
+ resource = "/v2#{resource}"
+ response = case method.downcase
+ when "get"
+ params ? get(resource, headers: headers, params: params) : get(resource, headers: headers)
+ when "post"
+ post(resource, headers: headers, body: body.try(&.to_json))
+ when "patch"
+ patch(resource, headers: headers, body: body.try(&.to_json))
+ when "delete"
+ delete(resource, headers: headers)
+ else
+ raise "Unsupported HTTP method: #{method}"
+ end
+
+ unless response.success?
+ logger.error { "API request failed: #{method} #{resource} - #{response.status_code} - #{response.body}" }
+ raise "API request failed: #{response.status_code}, response: #{response.body}"
+ end
+
+ JSON.parse(response.body) unless (response.body.nil? || response.body.empty?)
+ end
+
+ # List Zoom Rooms
+ def list_rooms(
+ status : String? = nil,
+ type : String? = nil,
+ location_id : String? = nil,
+ page_size : Int32 = 30,
+ next_page_token : String? = nil,
+ )
+ params = {
+ "status" => status,
+ "type" => type,
+ "location_id" => location_id,
+ "page_size" => page_size.to_s,
+ "next_page_token" => next_page_token,
+ }.compact
+
+ api_request("GET", "/rooms", params: params)
+ end
+
+ # Get specific room details
+ # the user_id in this response can be used to get the upcoming meetings
+ # https://developers.zoom.us/docs/api/rooms/#tag/zoom-rooms/GET/rooms/{roomId}
+ def get_room(room_id : String)
+ api_request("GET", "/rooms/#{room_id}")
+ end
+
+ enum MeetingType
+ Scheduled # All valid previous (unexpired) meetings, live meetings, and upcoming scheduled meetings.
+ Live # All the ongoing meetings
+ Upcoming # All upcoming meetings, including live meetings.
+ UpcomingMeetings # All upcoming meetings, including live meetings.
+ PreviousMeetings # All the previous meetings.
+ end
+
+ # list the meetings in the room
+ # https://developers.zoom.us/docs/api/meetings/#tag/meetings/get/users/{userId}/meetings
+ def list_user_meetings(room_user_id : String, type : MeetingType = MeetingType::Scheduled)
+ params = {
+ "type" => type.to_s.underscore,
+ }
+ api_request("GET", "/users/#{room_user_id}/meetings", params: params)
+ end
+
+ # List calendar events
+ def list_calendar_events(
+ calendar_id : String,
+ from : String? = nil,
+ to : String? = nil,
+ page_size : Int32 = 30,
+ next_page_token : String? = nil,
+ )
+ api_request("GET", "/calendars/#{calendar_id}/events", params: {
+ "from" => from,
+ "to" => to,
+ "page_size" => page_size.to_s,
+ "next_page_token" => next_page_token,
+ }.compact)
+ end
+
+ # List Zoom Room locations
+ def list_locations(
+ parent_location_id : String? = nil,
+ type : String? = nil,
+ page_size : Int32 = 30,
+ next_page_token : String? = nil,
+ )
+ params = {
+ "parent_location_id" => parent_location_id,
+ "type" => type,
+ "page_size" => page_size.to_s,
+ "next_page_token" => next_page_token,
+ }.compact
+
+ api_request("GET", "/rooms/locations", params: params)
+ end
+
+ # List Zoom Room devices
+ def list_devices(room_id : String)
+ api_request("GET", "/rooms/#{room_id}/devices")
+ end
+
+ # Get device information
+ def get_device_info(room_id : String)
+ api_request("GET", "/rooms/#{room_id}/device_profiles")
+ end
+
+ # List device profiles
+ def list_device_profiles(room_id : String)
+ api_request("GET", "/rooms/#{room_id}/device_profiles")
+ end
+
+ # Get Zoom Room sensor data
+ def get_sensor_data(room_id : String, from : String? = nil, to : String? = nil)
+ api_request("GET", "/rooms/#{room_id}/sensor_data", params: {
+ "from" => from,
+ "to" => to,
+ }.compact)
+ end
+
+ # Get Zoom Room settings
+ def get_room_settings(room_id : String)
+ api_request("GET", "/rooms/#{room_id}/settings")
+ end
+
+ # ==============================
+ # in-meeting controls
+ # ==============================
+
+ enum Recording
+ Start
+ Stop
+ Pause
+ Resume
+ end
+
+ def meeting_recording(meeting_id : String | Int64, command : Recording) : Nil
+ body = {
+ method: "recording.#{command.to_s.downcase}",
+ }
+ api_request("PATCH", "/live_meetings/#{meeting_id}/events", body: body)
+ logger.debug { "Updated recording state: #{command}" }
+ end
+
+ def meeting_call_phone(
+ meeting_id : String | Int64,
+ invitee_name : String,
+ phone_number : String,
+ require_greeting : Bool = true,
+ require_pressing_one : Bool = true,
+ ) : Nil
+ body = {
+ method: "participant.invite.callout",
+ params: {
+ invitee_name: invitee_name,
+ phone_number: phone_number,
+ invite_options: {
+ require_greeting: require_greeting,
+ require_pressing_one: require_pressing_one,
+ },
+ },
+ }
+
+ api_request("PATCH", "/live_meetings/#{meeting_id}/events", body: body)
+ logger.debug { "Calling: #{invitee_name} => #{phone_number}" }
+ end
+
+ def meeting_invite_contacts(meeting_id : String | Int64, email : String | Array(String)) : Nil
+ email = email.is_a?(String) ? [email] : email
+ emails = email.map { |address| {email: address} }
+ body = {
+ method: "participant.invite",
+ params: {
+ contacts: emails,
+ },
+ }
+
+ api_request("PATCH", "/live_meetings/#{meeting_id}/events", body: body)
+ logger.debug { "Inviting: #{email}" }
+ end
+
+ def meeting_waiting_room(meeting_id : String | Int64, title : String, description : String) : Nil
+ body = {
+ method: "waiting_room.update",
+ params: {
+ waiting_room_title: title,
+ waiting_room_description: description,
+ },
+ }
+
+ api_request("PATCH", "/live_meetings/#{meeting_id}/events", body: body)
+ logger.debug { "Waiting room update: #{title}\n#{description}" }
+ end
+
+ # ==============================
+ # Zoom Room Controls
+ # ==============================
+
+ # Room Controls - Mute/Unmute microphone
+ def mute(room_id : String, state : Bool = true) : Nil
+ method = state ? "zoomroom.mute" : "zoomroom.unmute"
+ api_request("PATCH", "/rooms/#{room_id}/events", body: {method: method})
+ logger.debug { "Microphone #{state ? "muted" : "unmuted"} in #{room_id}" }
+ end
+
+ def unmute(room_id : String)
+ mute(room_id, false)
+ end
+
+ def meeting_accept(room_id : String) : Nil
+ api_request("PATCH", "/rooms/#{room_id}/events", body: {method: "zoomroom.meeting_accept"})
+ logger.debug { "Zoom Room meeting accept in #{room_id}" }
+ end
+
+ def meeting_decline(room_id : String) : Nil
+ api_request("PATCH", "/rooms/#{room_id}/events", body: {method: "zoomroom.meeting_decline"})
+ logger.debug { "Zoom Room meeting decline in #{room_id}" }
+ end
+
+ # Video mute/unmute
+ def video_mute(room_id : String, state : Bool = true) : Nil
+ method = state ? "zoomroom.video_mute" : "zoomroom.video_unmute"
+ api_request("PATCH", "/rooms/#{room_id}/events", body: {method: method})
+ logger.debug { "Video #{state ? "muted" : "unmuted"} in #{room_id}" }
+ end
+
+ def video_unmute(room_id : String)
+ video_mute(room_id, false)
+ end
+
+ # Restart Zoom Room
+ def restart_room(room_id : String) : Nil
+ api_request("PATCH", "/rooms/#{room_id}/events", body: {method: "zoomroom.restart"})
+ logger.info { "Zoom Room restart initiated in #{room_id}" }
+ end
+
+ # Meeting controls
+ def meeting_leave(room_id : String) : Nil
+ api_request("PATCH", "/rooms/#{room_id}/events", body: {method: "zoomroom.meeting_leave"})
+ logger.info { "Left meeting in #{room_id}" }
+ end
+
+ def meeting_end(room_id : String) : Nil
+ api_request("PATCH", "/rooms/#{room_id}/events", body: {method: "zoomroom.meeting_end"})
+ logger.info { "Ended meeting in #{room_id}" }
+ end
+
+ def meeting_schedule(room_id : String, meeting_topic : String, start_time : Int64, duration_min : Int32, passcode : String? = nil, join_before_host : Bool = true) : Nil
+ body = {
+ method: "zoomroom.meeting_schedule",
+ params: {
+ "passcode" => passcode,
+ "meeting_topic" => meeting_topic,
+ "start_time" => Time.unix(start_time).to_rfc3339,
+ "duration" => duration_min,
+ "settings" => {
+ "join_before_host" => join_before_host,
+ },
+ }.compact,
+ }
+
+ api_request("PATCH", "/rooms/#{room_id}/events", body: body)
+ logger.info { "Meeting #{meeting_topic} scheduled in #{room_id}" }
+ end
+
+ def meeting_join_thirdparty(room_id : String, join_url : String) : Nil
+ if join_url =~ /https:\/\/(?:[\w.-]*teams\.microsoft\.com|teams\.live\.com)\/[^\s>"]+/i
+ meeting_source_type = "MS_TEAMS"
+ elsif join_url =~ /https:\/\/meet\.google\.com\/[^\s>"]+/i
+ meeting_source_type = "GOOGLE_MEET"
+ else
+ raise "only supports Google Meet or MS Teams"
+ end
+
+ body = {
+ method: "zoomroom.thirdparty_meeting_join",
+ params: {
+ "join_type" => "url",
+ "meeting_source_type" => meeting_source_type,
+ "join_url" => join_url,
+ }.compact,
+ }
+
+ api_request("PATCH", "/rooms/#{room_id}/events", body: body)
+ logger.debug { "Joining 3rd party meeting #{join_url} in #{room_id}" }
+ end
+
+ def meeting_join(room_id : String, meeting_number : String | Int64, password : String? = nil, host : Bool = false) : Nil
+ body = {
+ method: "zoomroom.meeting_join",
+ params: {
+ "meeting_number" => meeting_number.to_s,
+ "password" => password,
+ "force_accept" => true,
+ "make_zoom_room_host" => host,
+ }.compact,
+ }
+
+ api_request("PATCH", "/rooms/#{room_id}/events", body: body)
+ logger.info { "Joined meeting #{meeting_number} in #{room_id}" }
+ end
+
+ # Device switching
+ def switch_camera(room_id : String, camera_id : String) : Nil
+ body = {
+ method: "zoomroom.switch_camera",
+ params: {
+ cameraId: camera_id,
+ },
+ }
+
+ api_request("PATCH", "/rooms/#{room_id}/events", body: body)
+ logger.debug { "Switched to camera #{camera_id} in #{room_id}" }
+ end
+
+ def switch_microphone(room_id : String, microphone_id : String) : Nil
+ body = {
+ method: "zoomroom.switch_microphone",
+ params: {
+ microphoneId: microphone_id,
+ },
+ }
+ api_request("PATCH", "/rooms/#{room_id}/events", body: body)
+ logger.debug { "Switched to microphone #{microphone_id} in #{room_id}" }
+ end
+
+ def switch_speaker(room_id : String, speaker_id : String) : Nil
+ body = {
+ method: "zoomroom.switch_speaker",
+ params: {
+ "speakerId" => speaker_id,
+ },
+ }
+
+ api_request("PATCH", "/rooms/#{room_id}/events", body: body)
+ logger.debug { "Switched to speaker #{speaker_id} in #{room_id}" }
+ end
+
+ # Content sharing
+ def share_content(room_id : String, state : Bool = true) : Nil
+ method = state ? "zoomroom.share_content_start" : "zoomroom.share_content_stop"
+ api_request("PATCH", "/rooms/#{room_id}/events", body: {method: method})
+ logger.debug { "Content sharing #{state ? "started" : "stopped"} in #{room_id}" }
+ end
+
+ def stop_share_content(room_id : String)
+ share_content(room_id, false)
+ end
+
+ # Volume control
+ def set_volume(room_id : String, level : Int32) : Int32
+ # Ensure volume is within valid range (0-100)
+ level = level.clamp(0, 100)
+
+ body = {
+ method: "zoomroom.volume_level",
+ params: {
+ volume_level: level,
+ },
+ }
+
+ api_request("PATCH", "/rooms/#{room_id}/events", body: body)
+ logger.debug { "Volume set to #{level} in #{room_id}" }
+ level
+ end
+
+ # Room check-in/out
+ def check_in(
+ room_id : String,
+ # The unique identifier of the calendar event associated with the Zoom Room.
+ event_id : String,
+ # This field is only required for Microsoft Exchange / Office 365 Calendar
+ resource_email : String? = nil,
+ # This field is required only for Microsoft Exchange or Office 365 calendar
+ change_key : String? = nil,
+ # only required if using Google Calendar
+ calendar_id : String? = nil,
+ ) : Nil
+ params = {
+ "calendar_id" => calendar_id,
+ "event_id" => event_id,
+ "resource_email" => resource_email,
+ "change_key" => change_key,
+ }.compact
+
+ body = {
+ method: "zoomroom.check_in",
+ params: params,
+ }
+
+ api_request("PATCH", "/rooms/#{room_id}/events", body: body)
+ logger.info { "Checked in to room #{room_id}" }
+ end
+
+ def check_out(
+ room_id : String,
+ # The unique identifier of the calendar event associated with the Zoom Room.
+ event_id : String,
+ # This field is only required for Microsoft Exchange / Office 365 Calendar
+ resource_email : String? = nil,
+ # This field is required only for Microsoft Exchange or Office 365 calendar
+ change_key : String? = nil,
+ # only required if using Google Calendar
+ calendar_id : String? = nil,
+ ) : Nil
+ params = {
+ "calendar_id" => calendar_id,
+ "event_id" => event_id,
+ "resource_email" => resource_email,
+ "change_key" => change_key,
+ }.compact
+
+ body = {
+ method: "zoomroom.check_in",
+ params: params,
+ }
+
+ api_request("PATCH", "/rooms/#{room_id}/events", body: body)
+ logger.info { "Checked out of room #{room_id}" }
+ end
+
+ # ==============================
+end
diff --git a/drivers/zoom/rooms_api_spec.cr b/drivers/zoom/rooms_api_spec.cr
new file mode 100644
index 00000000000..96c9895851b
--- /dev/null
+++ b/drivers/zoom/rooms_api_spec.cr
@@ -0,0 +1,315 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Zoom::RoomsApi" do
+ # Mock settings
+ settings({
+ account_id: "test_account_id",
+ client_id: "test_client_id",
+ client_secret: "test_client_secret",
+ })
+
+ room_id = "qMOLddnySIGGVycz8aX_JQ"
+
+ retval = exec(:list_rooms, room_id)
+ # Mock authentication response
+ expect_http_request do |request, response|
+ if request.path == "/oauth/token"
+ response.status_code = 200
+ response.output.puts %({
+ "access_token": "test_access_token_123",
+ "token_type": "bearer",
+ "expires_in": 3600,
+ "scope": "room:read:admin room:write:admin",
+ "api_url": "https://api.zoom.us"
+ })
+ else
+ response.status_code = 500
+ end
+ end
+
+ # Mock list rooms request with authentication
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms"
+ response.status_code = 200
+ response.output.puts %({
+ "page_size": 30,
+ "rooms": [
+ {
+ "id": "qMOLddnySIGGVycz8aX_JQ",
+ "name": "Conference Room A",
+ "type": "ZoomRoom",
+ "location_id": "49D7a0xPQvGQ2DCMZgSe7w",
+ "status": "Available"
+ }
+ ]
+ })
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+
+ retval.get.try &.as_h["rooms"].should eq([{
+ "id" => "qMOLddnySIGGVycz8aX_JQ",
+ "name" => "Conference Room A",
+ "type" => "ZoomRoom",
+ "location_id" => "49D7a0xPQvGQ2DCMZgSe7w",
+ "status" => "Available",
+ }])
+
+ retval = exec(:mute, room_id)
+
+ # Mock mute request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/events"
+ body = JSON.parse(request.body.not_nil!)
+ body["method"].should eq("zoomroom.mute")
+ response.status_code = 202
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+
+ retval.get
+
+ retval = exec(:unmute, room_id)
+ # Mock unmute request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/events"
+ body = JSON.parse(request.body.not_nil!)
+ body["method"].should eq("zoomroom.unmute")
+ response.status_code = 202
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+
+ retval.get
+
+ retval = exec(:video_mute, room_id)
+ # Mock video mute request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/events"
+ body = JSON.parse(request.body.not_nil!)
+ body["method"].should eq("zoomroom.video_mute")
+ response.status_code = 202
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+ retval.get
+
+ retval = exec(:meeting_join, room_id, "123456789", "abc123")
+ # Mock join meeting request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/events"
+ body = JSON.parse(request.body.not_nil!)
+ body["method"].should eq("zoomroom.meeting_join")
+ body["params"]["meeting_number"].should eq("123456789")
+ body["params"]["password"].should eq("abc123")
+ response.status_code = 202
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+ retval.get
+
+ retval = exec(:meeting_leave, room_id)
+ # Mock leave meeting request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/events"
+ body = JSON.parse(request.body.not_nil!)
+ body["method"].should eq("zoomroom.meeting_leave")
+ response.status_code = 202
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+
+ retval.get
+
+ retval = exec(:set_volume, room_id, 75)
+ # Mock volume control request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/events"
+ body = JSON.parse(request.body.not_nil!)
+ body["method"].should eq("zoomroom.volume_level")
+ body["params"]["volume_level"].should eq(75)
+ response.status_code = 202
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+ retval.get.should eq(75)
+
+ retval = exec(:switch_camera, room_id, "camera_123")
+ # Mock switch camera request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/events"
+ body = JSON.parse(request.body.not_nil!)
+ body["method"].should eq("zoomroom.switch_camera")
+ body["params"]["cameraId"].should eq("camera_123")
+ response.status_code = 202
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+
+ retval.get
+
+ retval = exec(:share_content, room_id)
+ # Mock content sharing request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/events"
+ body = JSON.parse(request.body.not_nil!)
+ body["method"].should eq("zoomroom.share_content_start")
+ response.status_code = 202
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+ retval.get
+
+ retval = exec(:get_room, room_id)
+ # Mock get room request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ"
+ response.status_code = 200
+ response.output.puts %({
+ "id": "qMOLddnySIGGVycz8aX_JQ",
+ "name": "Conference Room A",
+ "type": "ZoomRoom",
+ "location_id": "49D7a0xPQvGQ2DCMZgSe7w",
+ "status": "Available",
+ "health": "healthy"
+ })
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+
+ result = retval.get
+ result.should eq({
+ "id" => "qMOLddnySIGGVycz8aX_JQ",
+ "name" => "Conference Room A",
+ "type" => "ZoomRoom",
+ "location_id" => "49D7a0xPQvGQ2DCMZgSe7w",
+ "status" => "Available",
+ "health" => "healthy",
+ })
+
+ retval = exec(:list_devices, room_id)
+ # Mock list devices request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/devices"
+ response.status_code = 200
+ response.output.puts %({
+ "devices": [
+ {
+ "id": "device_123",
+ "room_name": "Conference Room A",
+ "device_type": "ZoomRoomsComputer",
+ "app_version": "5.8.0",
+ "device_system": "Win 10",
+ "status": "Online"
+ }
+ ]
+ })
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+
+ retval.get["devices"].should eq([{
+ "id" => "device_123",
+ "room_name" => "Conference Room A",
+ "device_type" => "ZoomRoomsComputer",
+ "app_version" => "5.8.0",
+ "device_system" => "Win 10",
+ "status" => "Online",
+ }])
+
+ retval = exec(:get_sensor_data, room_id)
+ # Mock sensor data request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/sensor_data"
+ response.status_code = 200
+ response.output.puts %({
+ "sensor_data": {
+ "temperature": {
+ "value": 22.5,
+ "unit": "celsius"
+ },
+ "humidity": {
+ "value": 45,
+ "unit": "percentage"
+ },
+ "people_count": 3
+ }
+ })
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+
+ result = retval.get.not_nil!.as_h
+ result["sensor_data"]["temperature"]["value"].should eq(22.5)
+ result["sensor_data"]["people_count"].should eq(3)
+
+ retval = exec(:check_in, room_id, "event_123", "room@example.com", nil, "mycalendar@example.com")
+ # Mock check-in request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/events"
+ body = JSON.parse(request.body.not_nil!)
+ body["method"].should eq("zoomroom.check_in")
+ body["params"]["calendar_id"].should eq("mycalendar@example.com")
+ body["params"]["event_id"].should eq("event_123")
+ body["params"]["resource_email"].should eq("room@example.com")
+ response.status_code = 202
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+
+ retval.get
+
+ retval = exec(:restart_room, room_id)
+ # Mock restart request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/qMOLddnySIGGVycz8aX_JQ/events"
+ body = JSON.parse(request.body.not_nil!)
+ body["method"].should eq("zoomroom.restart")
+ response.status_code = 202
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+
+ retval.get
+
+ retval = exec(:list_locations)
+ # Mock list locations request
+ expect_http_request do |request, response|
+ if request.path == "/v2/rooms/locations"
+ response.status_code = 200
+ response.output.puts %({
+ "locations": [
+ {
+ "id": "49D7a0xPQvGQ2DCMZgSe7w",
+ "name": "Building A",
+ "type": "building",
+ "parent_location_id": "parent_123"
+ }
+ ]
+ })
+ else
+ raise "unexpected request #{request.path}"
+ end
+ end
+
+ retval.get["locations"].should eq([{
+ "id" => "49D7a0xPQvGQ2DCMZgSe7w",
+ "name" => "Building A",
+ "type" => "building",
+ "parent_location_id" => "parent_123",
+ }])
+end
diff --git a/drivers/zoom/zoom_meeting.cr b/drivers/zoom/zoom_meeting.cr
new file mode 100644
index 00000000000..43320165521
--- /dev/null
+++ b/drivers/zoom/zoom_meeting.cr
@@ -0,0 +1,246 @@
+require "placeos-driver"
+require "place_calendar"
+require "jwt"
+require "uri"
+
+# https://developers.zoom.us/docs/meeting-sdk/auth/
+
+class Zoom::Meeting < PlaceOS::Driver
+ descriptive_name "Zoom Room"
+ generic_name :Zoom
+
+ default_settings({
+ zoom_domain: "x.zoom.us",
+ zoom_room_id: "room_id",
+ _zoom_api_system: "sys-management",
+ })
+
+ accessor bookings : Bookings_1
+ bind Bookings_1, :current_booking, :current_booking_changed
+
+ @zoom_api_system : String? = nil
+
+ getter zoom_domain : String = "x.zoom.us"
+ getter room_id : String = ""
+
+ def on_update
+ @zoom_domain = setting(String, :zoom_domain).downcase
+ @room_id = setting(String, :zoom_room_id)
+ @zoom_api_system = setting?(String, :zoom_api_system).presence
+ end
+
+ private def zoom_api
+ if zoom_system = @zoom_api_system
+ system(zoom_system)["ZoomAPI"]
+ else
+ system["ZoomAPI"]
+ end
+ end
+
+ struct Meeting
+ include JSON::Serializable
+
+ @[JSON::Field(ignore: true)]
+ getter uri : URI
+ getter url : String
+ getter title : String?
+ getter event_start : Int64
+ getter? is_zoom : Bool
+ getter? can_host : Bool
+
+ def id
+ uri.path.split('/')[2] if is_zoom?
+ end
+
+ def password
+ uri.query_params["pwd"]?.try(&.presence) if is_zoom?
+ end
+
+ def token
+ uri.query_params["tk"]?.try(&.presence) if is_zoom?
+ end
+
+ def initialize(@title, @event_start, @is_zoom, @uri, host_domain : String)
+ @url = @uri.to_s
+ @can_host = @is_zoom ? @url.starts_with?("https://#{host_domain}") : false
+ end
+ end
+
+ getter current_meeting : Meeting? = nil
+ getter joined_meeting : Meeting? = nil
+
+ def join_meeting(start_time : Int64? = nil)
+ if start_time
+ if event = bookings.status(Array(PlaceCalendar::Event), :bookings).find { |event| event.event_start.to_unix == start_time }
+ meeting = extract_meeting(event)
+ end
+ elsif @current_meeting
+ meeting = @current_meeting
+ elsif event = bookings.status?(PlaceCalendar::Event, :current_booking)
+ meeting = extract_meeting(event)
+ end
+
+ if meeting.nil?
+ logger.debug { "no meeting found @ #{start_time.inspect}" }
+ return
+ end
+
+ @joined_meeting = nil
+
+ # process the meeting body for the zoom link
+ logger.debug { "found matching meeting: #{meeting.title} - starting #{meeting.event_start}" }
+
+ if meeting.is_zoom?
+ logger.debug { "found zoom meeting uri: #{meeting.url} (can host: #{meeting.can_host?})" }
+
+ control_sys = config.control_system.not_nil!
+ role = meeting.can_host? ? "host" : "participant"
+ meeting_id = meeting.id.as(String)
+ password = meeting.password
+
+ zoom_api.meeting_join(room_id, meeting_id, password, meeting.can_host?).get
+ @joined_meeting = meeting
+ self[:meeting_joined] = meeting.event_start
+ spawn { setup_room }
+
+ # https://developers.zoom.us/docs/meeting-sdk/web/component-view/meetings/
+ {
+ "meetingNumber" => meeting_id,
+ "signature" => zoom_api.generate_jwt(meeting_id, role: role).get.as_s,
+ "userEmail" => control_sys.email,
+ "userName" => control_sys.display_name.presence || control_sys.name,
+ "password" => password || "",
+ # sdkKey: client_id.as_s, # now pulled from the JWT
+ "tk" => meeting.token,
+ }.compact!
+ else
+ logger.debug { "found 3rd party meeting uri: #{meeting.url}" }
+ zoom_api.meeting_join_thirdparty(room_id, meeting.url).get
+ self[:meeting_joined] = meeting.event_start
+ nil
+ end
+ end
+
+ protected def setup_room
+ mic_mute false
+ camera_mute false
+ share_content false
+ self[:recording] = Recording::Stop
+ end
+
+ def leave_meeting : Nil
+ zoom_api.meeting_leave(room_id).get
+ @joined_meeting = nil
+ self[:meeting_joined] = nil
+ end
+
+ def end_meeting : Nil
+ zoom_api.meeting_end(room_id).get
+ @joined_meeting = nil
+ self[:meeting_joined] = nil
+ end
+
+ def mic_mute(state : Bool = true) : Bool
+ zoom_api.mute(room_id, state).get
+ self[:mic_mute] = state
+ end
+
+ def camera_mute(state : Bool = true) : Bool
+ zoom_api.video_mute(room_id, state).get
+ self[:camera_mute] = state
+ end
+
+ def share_content(state : Bool = true) : Bool
+ zoom_api.share_content(room_id, state).get
+ self[:share_content] = state
+ end
+
+ def volume(level : Int32) : Int32
+ level = level.clamp(0, 100)
+ zoom_api.set_volume(room_id, level).get
+ self[:volume] = level
+ end
+
+ enum Recording
+ Start
+ Stop
+ Pause
+ Resume
+ end
+
+ def recording(command : Recording) : Recording
+ if command.start? && status?(Recording, :recording).try(&.pause?)
+ command = Recording::Resume
+ end
+
+ in_meeting = joined_meeting || current_meeting
+ raise "no live meetings" unless in_meeting
+ zoom_api.meeting_recording(in_meeting.id, command).get
+ self[:recording] = command.resume? ? Recording::Start : command
+ end
+
+ def call_phone(invitee_name : String, phone_number : String) : Nil
+ in_meeting = joined_meeting || current_meeting
+ raise "no live meetings" unless in_meeting
+ zoom_api.meeting_call_phone(in_meeting.id, invitee_name, phone_number).get
+ end
+
+ def invite_contacts(emails : String | Array(String)) : Nil
+ in_meeting = joined_meeting || current_meeting
+ raise "no live meetings" unless in_meeting
+ zoom_api.meeting_invite_contacts(in_meeting.id, emails).get
+ end
+
+ # Stub for adding sensor data retrieval and exposure
+ # def get_sensor_data(from : String? = nil, to : String? = nil) : Nil
+ # sensor_data = zoom_api.get_sensor_data(@room_id, from, to).get
+ # end
+
+ protected def extract_meeting_links(mail_body : String) : Tuple(Bool, URI)?
+ zoom = true
+ link = extract_zoom_link(mail_body)
+
+ if link.nil?
+ zoom = false
+ link = extract_teams_link(mail_body) || extract_meet_link(mail_body)
+ end
+
+ return nil unless link
+ {zoom, URI.parse(URI.decode(link))}
+ end
+
+ def extract_zoom_link(body : String) : String?
+ body.scan(/https:\/\/[\w.-]+\.zoom\.us\/[jw]\/\d+[^\s>"]*/i).first?.to_s
+ end
+
+ def extract_meet_link(body : String) : String?
+ body.scan(/https:\/\/meet\.google\.com\/[^\s>"]+/i).map(&.[0]).first?.to_s
+ end
+
+ def extract_teams_link(body : String) : String?
+ body.scan(/https:\/\/(?:[\w.-]*teams\.microsoft\.com|teams\.live\.com)\/[^\s>"]+/i).map(&.[0]).first?.to_s
+ end
+
+ private def current_booking_changed(_subscription, new_event)
+ logger.debug { "current booking changed!" }
+ event = (PlaceCalendar::Event?).from_json(new_event)
+
+ if event
+ meeting_link = extract_meeting(event)
+ end
+
+ @current_meeting = meeting_link
+ self[:meeting_in_progress] = meeting_link.try(&.event_start)
+ rescue e
+ logger.warn(exception: e) { "failed to parse event" }
+ self[:meeting_in_progress] = nil
+ end
+
+ private def extract_meeting(event : PlaceCalendar::Event) : Meeting?
+ if body = event.body
+ if extracted = extract_meeting_links(body)
+ Meeting.new(event.title, event.event_start.to_unix, *extracted, @zoom_domain)
+ end
+ end
+ end
+end
diff --git a/drivers/zoom/zoom_meeting.md b/drivers/zoom/zoom_meeting.md
new file mode 100644
index 00000000000..8cb59a3e924
--- /dev/null
+++ b/drivers/zoom/zoom_meeting.md
@@ -0,0 +1,65 @@
+# Zoom Meeting Driver overview
+
+## Meeting Joining
+
+Related state
+
+```crystal
+# Int64 | Nil - is the start time of the current meeting with a zoom link
+meeting_in_progress
+
+# Int64 | Nil - timestamp of the last meeting joined
+# if different from meeting_in_progress then make sure to show buttons to `join_meeting`
+meeting_joined
+```
+
+related functions
+
+* `Zoom.join_meeting(start_time : Int64? = nil)` - start_time is optional, if not specified will use the `meeting_in_progress` status value
+ * if this function returns a hash, the touch panel can use it to join the meeting for additional controls via the JS SDK
+ * if this function returns nil and `meeting_joined` updated to match `meeting_in_progress` or the start_time you passed in, then a 3rd party meeting is in progress (teams or meet) - but the touch panel doesn't need to join as it won't be able to control the meeting.
+* `Zoom.leave_meeting` - leaves the meeting, without ending the meeting
+* `Zoom.end_meeting` - ends the meeting for everyone
+ * both these set `meeting_joined` to `nil`
+
+## Meeting Recording
+
+```crystal
+# "stop" | "start" | "pause" - the current state of cloud recordings
+# if equal to "pause" then you can "resume" the recording
+recording
+```
+
+related functions
+
+* `Zoom.recording(command : Recording) : Recording` - command is one of "stop", "start" or "pause"
+
+## Meeting Controls
+
+Status for binding
+
+```crystal
+# Bool - is the local mic audio muted
+mic_mute
+
+# Bool - is the local camera video muted
+camera_mute
+
+# Bool - are we sharing content locally
+share_content
+
+# Int32 - the room volume, 0-100
+volume
+```
+
+related functions
+
+* `Zoom.mic_mute(state : Bool = true) : Bool`
+* `Zoom.camera_mute(state : Bool = true) : Bool`
+* `Zoom.share_content(state : Bool = true) : Bool`
+* `Zoom.volume(level : Int32) : Int32`
+
+## Adding additional people to the current call
+
+* `Zoom.call_phone(invitee_name : String, phone_number : String)`
+* `Zoom.invite_contacts(emails : String | Array(String))`
diff --git a/drivers/zoom/zoom_meeting_spec.cr b/drivers/zoom/zoom_meeting_spec.cr
new file mode 100644
index 00000000000..7a79380cb46
--- /dev/null
+++ b/drivers/zoom/zoom_meeting_spec.cr
@@ -0,0 +1,119 @@
+require "placeos-driver/spec"
+require "place_calendar"
+require "jwt"
+
+# :nodoc:
+class BookingsMock < DriverSpecs::MockDriver
+ START_TIME = 1.hour.ago
+
+ BOOKINGS = [
+ PlaceCalendar::Event.new(
+ id: "12345",
+ host: "steve@place.com",
+ event_start: START_TIME,
+ event_end: 2.hours.from_now,
+ title: "Booking 1",
+ body: "Some content\nmeeting: https://x.zoom.us/j/123456789?pwd=password\nwhat new line",
+ location: "meeting 1",
+ attendees: [PlaceCalendar::Event::Attendee.new(
+ name: "Steve",
+ email: "steve@place.com",
+ response_status: "accepted",
+ resource: false,
+ organizer: true
+ )],
+ private: false,
+ all_day: false,
+ timezone: "Australia/Darwin",
+ recurrence: nil,
+ status: "confirmed",
+ creator: "steve@place.com",
+ recurring_event_id: nil,
+ ical_uid: "some id",
+ created: 3.days.ago,
+ updated: 3.days.ago
+ ),
+ ]
+
+ def on_load
+ self[:bookings] = BOOKINGS
+ self[:current_booking] = BOOKINGS[0]
+ end
+end
+
+# :nodoc:
+class ZoomAPIMock < DriverSpecs::MockDriver
+ def meeting_join(room_id : String, meeting_number : String | Int64, password : String? = nil, host : Bool = false) : Nil
+ logger.debug { "joining meeting #{meeting_number} in #{room_id}" }
+ end
+
+ def mute(room_id : String, state : Bool = true) : Nil
+ logger.debug { "muting audio #{state} in #{room_id}" }
+ end
+
+ def video_mute(room_id : String, state : Bool = true) : Nil
+ logger.debug { "muting video #{state} in #{room_id}" }
+ end
+
+ def share_content(room_id : String, state : Bool = true) : Nil
+ logger.debug { "sharing content #{state} in #{room_id}" }
+ end
+
+ enum Role
+ Participant = 0
+ Host
+ end
+
+ def generate_jwt(meeting_number : String, issued_at : Int64? = nil, expires_at : Int64? = nil, role : Role? = nil)
+ iat = issued_at || 2.minutes.ago.to_unix # issued at time, 2 minutes earlier to avoid clock skew
+ exp = expires_at || 2.hours.from_now.to_unix # token expires after 2 hours
+
+ client_id = "key"
+ payload = {
+ "appKey" => client_id,
+ "mn" => meeting_number,
+ "role" => (role || Role::Participant).to_i,
+ "tokenExp" => exp,
+ "iat" => iat,
+ "exp" => exp,
+ }
+
+ JWT.encode(payload, "secret", JWT::Algorithm::HS256)
+ end
+end
+
+DriverSpecs.mock_driver "Zoom::Meeting" do
+ system({
+ Bookings: {BookingsMock},
+ ZoomAPI: {ZoomAPIMock},
+ })
+
+ # ====
+ # example generated at https://developers.zoom.us/docs/meeting-sdk/auth/
+ # jwt = exec(:generate_jwt, "1234567", 1751266556_i64, 1751270156_i64, "host").get
+ # jwt.should eq "eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJhcHBLZXkiOiJrZXkiLCJzZGtLZXkiOiJrZXkiLCJtbiI6IjEyMzQ1NjciLCJyb2xlIjoxLCJ0b2tlbkV4cCI6MTc1MTI3MDE1NiwiaWF0IjoxNzUxMjY2NTU2LCJleHAiOjE3NTEyNzAxNTZ9.lbTc6uvEnxMBEq7WiJw9EnzXNdSU32qBAigXAvaIQ5I"
+
+ # ====
+ # join a meeting
+ payload = exec(:join_meeting).get.not_nil!
+ payload["password"]?.should eq "password"
+ payload["meetingNumber"]?.should eq "123456789"
+ payload["userEmail"]?.should eq "spec@acaprojects.com"
+ payload["userName"]?.should eq "Spec Runner"
+
+ jwt, header = JWT.decode(payload["signature"].as_s, "secret", JWT::Algorithm::HS256)
+ jwt["appKey"].should eq "key"
+ jwt["role"].should eq 1
+ jwt["mn"].should eq "123456789"
+
+ # ====
+ # test link extraction
+ ms_meeting = %(Join the meeting now Meeting ID: xxxxxxxxx5)
+ exec(:extract_teams_link, ms_meeting).get.should eq "https://teams.microsoft.com/l/meetup-join/19%3ameeting_YzE1NzI3N2MtM200MGIxLWFhYTEtM2ViZTNlYjM5ZmY5%40thread.v2/0?context=%7b%22Tid%22%3a%225294a0-3e20-41b2-a970-6d0bf1546fa%22%2c%22Oid%22%3a%2257fc4f0c-fd53-4b12-8ca7-79ef698167f6%22%7d"
+
+ google_meeting = %(Video call link: https://meet.google.com/sfq-nqpp-iqx Or)
+ exec(:extract_meet_link, google_meeting).get.should eq "https://meet.google.com/sfq-nqpp-iqx"
+
+ zoom_meeting = %(Join Zoom Meeting One tap mobile:)
+ exec(:extract_zoom_link, zoom_meeting).get.should eq "https://ucla.zoom.us/j/93640805?pwd=P1BO3Il84TipdBd5Q.1&from=addon"
+end
diff --git a/drivers/zoom/zr_csapi.cr b/drivers/zoom/zr_csapi.cr
new file mode 100644
index 00000000000..b5b4185f025
--- /dev/null
+++ b/drivers/zoom/zr_csapi.cr
@@ -0,0 +1,776 @@
+require "placeos-driver"
+
+# Driver for Zoom Room ZR-CSAPI (Legacy SSH Control System API)
+# Connects to Zoom Room machines via SSH on port 2244
+# API Documentation: https://developers.zoom.us/docs/rooms/cli/
+class Zoom::ZrCSAPI < PlaceOS::Driver
+ descriptive_name "Zoom Room ZR-CSAPI"
+ generic_name :ZoomCSAPI
+ description "Legacy SSH-based API for Zoom Rooms. Requires SSH credentials configured on the Zoom Room."
+
+ tcp_port 2244
+
+ default_settings({
+ ssh: {
+ username: "zoom",
+ password: "",
+ },
+ enable_debug_logging: false,
+ milliseconds_until_response: 500,
+ })
+
+ getter? ready : Bool = false
+ @debug_enabled : Bool = false
+ @response_delay : Int32 = 500
+ @current_time : Int64 = Time.utc.to_unix
+
+ def on_load
+ queue.wait = false
+ queue.delay = 10.milliseconds
+ self[:ready] = @ready = false
+ on_update
+ end
+
+ def on_update
+ @debug_enabled = setting?(Bool, :enable_debug_logging) || false
+ @response_delay = setting?(Int32, :milliseconds_until_response) || 500
+ end
+
+ def connected
+ reset_connection_flags
+ # schedule.in(5.seconds) do
+ # initialize_tokenizer unless @ready || @init_called
+ # end
+ # we need to disconnect if we don't see welcome message
+ schedule.in(9.seconds) do
+ if !ready?
+ logger.error { "ZR-CSAPI connection failed to be ready after 9 seconds." }
+ disconnect
+ end
+ end
+ logger.debug { "Connected to Zoom Room ZR-CSAPI" }
+ self[:connected] = true
+ end
+
+ def disconnected
+ reset_connection_flags
+ queue.clear abort_current: true
+ schedule.clear
+ logger.debug { "Disconnected from Zoom Room ZR-CSAPI" }
+ self[:connected] = false
+ end
+
+ def fetch_initial_state
+ update_current_time
+ bookings_update
+ call_status
+ end
+
+ # =================
+ # zCommand Methods - Meeting Control
+ # =================
+
+ # Get today's meetings scheduled for this room
+ def bookings_list
+ do_send("zCommand Bookings List", name: "bookings_list")
+ sleep @response_delay.milliseconds
+ expose_custom_bookings_list
+ self["BookingsListResult"]
+ end
+
+ def update_current_time
+ @current_time = Time.utc.to_unix;
+ self[:meeting_started_time] = @current_time
+ end
+
+ # Expose custom booking JSON, filter meetings whose meetingNumber == 0 (invalid)
+ # filter meetings whose endTime has already passed (completely finished)
+ private def expose_custom_bookings_list
+ bookings = self["BookingsListResult"]?
+ return unless bookings
+
+ # Get current time as unix timestamp for filtering
+ update_current_time
+
+ self[:Bookings] = bookings.as_a.compact_map { |b|
+ booking_hash = b.as_h
+
+ # Parse ISO 8601 times and convert to unix timestamps
+ start_time_iso = booking_hash["startTime"]?.try(&.as_s)
+ end_time_iso = booking_hash["endTime"]?.try(&.as_s)
+
+ next unless start_time_iso && end_time_iso
+
+ begin
+ start_time_unix = Time.parse_iso8601(start_time_iso).to_unix
+ end_time_unix = Time.parse_iso8601(end_time_iso).to_unix
+
+ # Filter out bookings whose start time has already elapsed
+ next if end_time_unix < @current_time
+
+ # Filter out entries whose meeting number is "0"
+ meeting_number = booking_hash["meetingNumber"]?
+ next if meeting_number == "0"
+
+ # Return booking with converted unix timestamps
+ {
+ "creatorName" => booking_hash["creatorName"]?,
+ "startTime" => start_time_unix,
+ "endTime" => end_time_unix,
+ "meetingName" => booking_hash["meetingName"]?,
+ "meetingNumber" => booking_hash["meetingNumber"]?
+ }
+ rescue Time::Format::Error
+ # Skip bookings with invalid time formats
+ next
+ end
+ }.compact
+ end
+
+ # Update/refresh the meeting list from calendar
+ def bookings_update
+ do_send("zCommand Bookings Update", name: "bookings_update")
+ sleep @response_delay.milliseconds
+ bookings_list
+ end
+
+ # Start or join a meeting
+ def dial_start(meeting_number : String)
+ command = "zCommand Dial Start meetingNumber: #{meeting_number}"
+ do_send(command, name: "dial_start")
+ sleep @response_delay.milliseconds
+ self["Call"]
+ bookings_list
+ end
+
+ # Join a meeting
+ def dial_join(meeting_number : String)
+ command = "zCommand Dial Join meetingNumber: #{meeting_number}"
+ do_send(command, name: "dial_join")
+ sleep @response_delay.milliseconds
+ self["Call"]
+ bookings_list
+ end
+
+ # Join meeting via SIP
+ def dial_join_sip(sip_address : String, protocol : String = "Auto")
+ do_send("zCommand Dial Join meetingAddress: #{sip_address} protocol: #{protocol}", name: "dial_join_sip")
+ sleep @response_delay.milliseconds
+ self["Call"]
+ bookings_list
+ end
+
+ # Start PMI meeting
+ def dial_start_pmi(duration_minutes : Int32 = 15)
+ command = "zCommand Dial StartPmi Duration: #{duration_minutes}"
+ do_send(command, name: "dial_start_pmi")
+ sleep @response_delay.milliseconds
+ self["Call"]
+ bookings_list
+ end
+
+ # Input meeting password
+ def input_password(password : String)
+ do_send("zCommand Input Meeting Password: #{password}", name: "input_password")
+ end
+
+ # Leave current meeting
+ def call_disconnect
+ do_send("zCommand Call Disconnect", name: "call_disconnect")
+ end
+
+ # Invite participant to meeting
+ def call_invite(user : String)
+ do_send("zCommand Call Invite user: #{user}", name: "call_invite")
+ end
+
+ # Mute/unmute specific participant audio
+ def call_mute_participant_audio (mute : Bool, participant_id : String)
+ state = mute ? "on" : "off"
+ do_send("zCommand Call MuteParticipant mute: #{state} Id: #{participant_id}", name: "call_mute_participant_audio")
+ end
+
+ # Mute/unmute specific participant video
+ def call_mute_participant_video (mute : Bool, participant_id : String)
+ state = mute ? "on" : "off"
+ do_send("zCommand Call MuteParticipantVideo mute: #{state} Id: #{participant_id}", name: "call_mute_participant_video")
+ end
+
+ # Mute/unmute all participants
+ def call_mute_all(mute : Bool)
+ state = mute ? "on" : "off"
+ do_send("zCommand Call MuteAll mute: #{state}", name: "call_mute_all")
+ end
+
+ # Mute/unmute self (room microphone)
+ def call_mute_self(mute : Bool)
+ state = mute ? "on" : "off"
+ do_send("zConfiguration Call Microphone Mute: #{state}", name: "call_mute_self")
+ end
+
+ # Mute/unmute self (camera)
+ def call_mute_camera(mute : Bool)
+ state = mute ? "on" : "off"
+ do_send("zConfiguration Call Camera Mute: #{state}", name: "call_mute_camera")
+ sleep @response_delay.milliseconds
+ self["Call"]
+ end
+
+ # Start/stop recording
+ def call_record(enable : Bool)
+ state = enable ? "on" : "off"
+ do_send("zCommand Call Record Enable: #{state}", name: "call_record")
+ end
+
+ # Change meeting host
+ def call_make_host(participant_id : String)
+ do_send("zCommand Call MakeHost Id: #{participant_id}", name: "call_make_host")
+ end
+
+ # Pin participant video
+ def call_pin_participant(pin : Bool, participant_id : String)
+ state = pin ? "on" : "off"
+ do_send("zCommand Call PinParticipant Pin: #{state} Id: #{participant_id}", name: "call_pin_participant")
+ end
+
+ # Spotlight participant
+ def call_spotlight_participant(spotlight : Bool, participant_id : String)
+ state = spotlight ? "on" : "off"
+ do_send("zCommand Call SpotlightParticipant Spotlight: #{state} Id: #{participant_id}", name: "call_spotlight_participant")
+ end
+
+ # Lock/unlock meeting
+ def call_lock(lock : Bool)
+ state = lock ? "on" : "off"
+ do_send("zCommand Call Lock Enable: #{state}", name: "call_lock")
+ end
+
+ # Enable/disable waiting room
+ def call_waiting_room(enable : Bool)
+ state = enable ? "on" : "off"
+ do_send("zCommand Call WaitingRoom Enable: #{state}", name: "call_waiting_room")
+ end
+
+ # Admit participant from waiting room
+ def call_admit_participant(participant_id : String)
+ do_send("zCommand Call Admit Participant: #{participant_id}", name: "call_admit_participant")
+ end
+
+ # Expel participant from meeting
+ def call_expel_participant(participant_id : String)
+ do_send("zCommand Call Expel Id: #{participant_id}", name: "call_expel_participant")
+ end
+
+ # Change video layout
+ def call_layout(layout_style : String, layout_size : String? = nil, layout_position : String? = nil)
+ command = "zCommand Call Layout LayoutStyle: #{layout_style}"
+ command += " LayoutSize: #{layout_size}" if layout_size
+ command += " LayoutPosition: #{layout_position}" if layout_position
+ do_send(command, name: "call_layout")
+ end
+
+ # List phonebook contacts
+ def phonebook_list
+ do_send("zCommand Phonebook List", name: "phonebook_list")
+ end
+
+ # Search phonebook
+ def phonebook_search(search_string : String)
+ do_send("zCommand Phonebook Search SearchString: #{search_string}", name: "phonebook_search")
+ end
+
+ # =================
+ # zCommand Methods - Sharing Control
+ # =================
+
+ # Start/stop HDMI sharing
+ def sharing_start_hdmi
+ do_send("zCommand Call Sharing HDMI Start", name: "sharing_start_hdmi")
+ sleep @response_delay.milliseconds
+ self["SharingState"]
+ end
+
+ def sharing_stop
+ do_send("zCommand Call Sharing HDMI Stop", name: "sharing_stop_hdmi")
+ sleep @response_delay.milliseconds
+ self["SharingState"]
+ end
+
+ # Stop sharing Wireless
+ def sharing_stop_wireless
+ do_send("zCommand Call Sharing Disconnect", name: "sharing_stop_wireless")
+ sleep @response_delay.milliseconds
+ self["Sharing"]
+ end
+
+ # Share camera
+ def sharing_start_camera(camera_id : String, enable : Bool)
+ state = enable ? "on" : "off"
+ do_send("zCommand Call ShareCamera id: #{camera_id} Status: #{state}", name: "sharing_camera")
+ end
+
+ # =================
+ # zCommand Methods - Device Testing
+ # =================
+
+ # Test microphone
+ def test_microphone_start(device_id : String? = nil)
+ command = "zCommand Test Microphone Start"
+ command += " Id: #{device_id}" if device_id
+ do_send(command, name: "test_microphone_start")
+ end
+
+ def test_microphone_stop
+ do_send("zCommand Test Microphone Stop", name: "test_microphone_stop")
+ end
+
+ # Test speakers
+ def test_speakers_start(device_id : String? = nil)
+ command = "zCommand Test Speakers Start"
+ command += " Id: #{device_id}" if device_id
+ do_send(command, name: "test_speakers_start")
+ end
+
+ def test_speakers_stop
+ do_send("zCommand Test Speakers Stop", name: "test_speakers_stop")
+ end
+
+ # Test camera
+ def test_camera_start(device_id : String? = nil)
+ command = "zCommand Test Camera Start"
+ command += " Id: #{device_id}" if device_id
+ do_send(command, name: "test_camera_start")
+ end
+
+ def test_camera_stop
+ do_send("zCommand Test Camera Stop", name: "test_camera_stop")
+ end
+
+ # =================
+ # zStatus Methods
+ # =================
+
+ def system_unit?
+ do_send("zStatus SystemUnit", name: "status_system_unit")
+ sleep @response_delay.milliseconds
+ self["SystemUnit"]
+ end
+
+ # Get call status
+ def call_status
+ do_send("zStatus Call Status", name: "call_status")
+ sleep @response_delay.milliseconds
+ self["Call"]
+ end
+
+ # Get call stats information
+ def call_stats
+ do_send("zStatus Call Stats", name: "call_stats")
+ end
+
+ # Get participant list
+ def call_list_participants
+ logger.debug { "=== CALLING call_list_participants ===" }
+ do_send("zCommand Call ListParticipants", name: "call_participants")
+ sleep @response_delay.milliseconds
+ self["ListParticipantsResult"]
+ end
+
+ #Expose ListParticipantsResult in a more easily read and usable format
+ private def expose_custom_participant_list
+ participants = self["ListParticipantsResult"]?
+ return unless participants
+
+ participants_array = participants.as_a
+ self[:number_of_participants] = participants_array.size
+
+ # selected participants
+ selected_participants = participants_array.map { |p| p.as_h.select(
+ "user_id",
+ "user_name",
+ "audio_status state",
+ "video_status has_source",
+ "video_status is_sending",
+ "isCohost",
+ "is_host",
+ "is_in_waiting_room",
+ "hand_status"
+ )}
+
+ # transform
+ self[:Participants] = selected_participants.map do |participant|
+ {
+ "user_id" => participant["user_id"],
+ "user_name" => participant["user_name"],
+ "audio_state" => participant["audio_status state"],
+ "video_has_source" => participant["video_status has_source"],
+ "video_is_sending" => participant["video_status is_sending"],
+ "isCohost" => participant["isCohost"],
+ "is_host" => participant["is_host"],
+ "is_in_waiting_room" => participant["is_in_waiting_room"],
+ "hand_status" => participant["hand_status"]
+ }
+ end
+ end
+
+ private def expose_custom_call_state
+ return unless call = self[:Call]
+
+ call_state = call.dig?("Status")
+ self[:in_call] = call_state.as_s? == "IN_MEETING" if call_state
+
+ mic_state = call.dig?("Microphone", "Mute")
+ self[:mic_mute] = mic_state.as_bool? if mic_state
+
+ cam_state = call.dig?("Camera", "Mute")
+ self[:cam_mute] = cam_state.as_bool? if cam_state
+
+ end
+
+ # Get audio input devices
+ def audio_input_line
+ do_send("zStatus Audio Input Line", name: "audio_input_line")
+ end
+
+ # Get audio output devices
+ def audio_output_line
+ do_send("zStatus Audio Output Line", name: "audio_output_line")
+ end
+
+ # Get video camera devices
+ def video_camera_line
+ do_send("zStatus Video Camera Line", name: "video_camera_line")
+ end
+
+ # Get system capabilities
+ def capabilities
+ do_send("zStatus Capabilities", name: "capabilities")
+ end
+
+ # Get sharing status
+ def sharing_status
+ do_send("zStatus Sharing", name: "sharing_status")
+ end
+
+ # Get room info
+ def room_info
+ do_send("zStatus RoomInfo", name: "room_info")
+ end
+
+ # Get peripherals
+ def peripherals
+ do_send("zStatus Peripherals", name: "peripherals")
+ end
+
+ # =================
+ # zConfiguration Methods
+ # =================
+
+ # Audio Configuration
+ def config_audio_input(device_id : String? = nil)
+ if device_id
+ do_send("zConfiguration Audio Input selectedDevice: #{device_id}", name: "config_audio_input")
+ else
+ do_send("zConfiguration Audio Input selectedDevice", name: "config_audio_input")
+ end
+ end
+
+ def config_audio_output(device_id : String? = nil)
+ if device_id
+ do_send("zConfiguration Audio Output selectedDevice: #{device_id}", name: "config_audio_output")
+ else
+ do_send("zConfiguration Audio Output selectedDevice", name: "config_audio_output")
+ end
+ end
+
+ def config_audio_volume(volume : Int32)
+ if volume
+ do_send("zConfiguration Audio Output volume: #{volume}", name: "config_audio_volume")
+ else
+ do_send("zConfiguration Audio Output volume", name: "config_audio_volume")
+ end
+ end
+
+ def config_audio_reduce_reverb(enable : Bool? = nil)
+ if enable.nil?
+ do_send("zConfiguration Audio Input ReduceReverb", name: "config_audio_reduce_reverb")
+ else
+ state = enable ? "on" : "off"
+ do_send("zConfiguration Audio Input ReduceReverb: #{state}", name: "config_audio_reduce_reverb")
+ end
+ end
+
+ def config_audio_software_processing(enable : Bool? = nil)
+ if enable.nil?
+ do_send("zConfiguration Audio Input SoftwareAudioProcessing", name: "config_audio_software_processing")
+ else
+ state = enable ? "on" : "off"
+ do_send("zConfiguration Audio Input SoftwareAudioProcessing: #{state}", name: "config_audio_software_processing")
+ end
+ end
+
+ # Video Configuration
+ def config_video_camera(device_id : String? = nil)
+ if device_id
+ do_send("zConfiguration Video Camera selectedDevice: #{device_id}", name: "config_video_camera")
+ else
+ do_send("zConfiguration Video Camera selectedDevice", name: "config_video_camera")
+ end
+ end
+
+ def config_video_self_view(hide : Bool? = nil)
+ if hide.nil?
+ do_send("zConfiguration Video selfViewHide", name: "config_video_self_view")
+ else
+ state = hide ? "on" : "off"
+ do_send("zConfiguration Video selfViewHide: #{state}", name: "config_video_self_view")
+ end
+ end
+
+ def config_video_mirror_mode(enable : Bool? = nil)
+ if enable.nil?
+ do_send("zConfiguration Video Camera mirrorMode", name: "config_video_mirror_mode")
+ else
+ state = enable ? "on" : "off"
+ do_send("zConfiguration Video Camera mirrorMode: #{state}", name: "config_video_mirror_mode")
+ end
+ end
+
+ # Call Configuration
+ def config_call_mute_on_entry(enable : Bool? = nil)
+ if enable.nil?
+ do_send("zConfiguration Call muteUserOnEntry", name: "config_call_mute_on_entry")
+ else
+ state = enable ? "on" : "off"
+ do_send("zConfiguration Call muteUserOnEntry: #{state}", name: "config_call_mute_on_entry")
+ end
+ end
+
+ def config_call_lock_enable(enable : Bool? = nil)
+ if enable.nil?
+ do_send("zConfiguration Call Lock enable", name: "config_call_lock")
+ else
+ state = enable ? "on" : "off"
+ do_send("zConfiguration Call Lock enable: #{state}", name: "config_call_lock")
+ end
+ end
+
+ def config_call_layout(layout_style : String? = nil, layout_size : String? = nil, layout_position : String? = nil)
+ if layout_style
+ command = "zConfiguration Call Layout LayoutStyle: #{layout_style}"
+ command += " LayoutSize: #{layout_size}" if layout_size
+ command += " LayoutPosition: #{layout_position}" if layout_position
+ do_send(command, name: "config_call_layout")
+ else
+ do_send("zConfiguration Call Layout", name: "config_call_layout")
+ end
+ end
+
+ def config_call_share_thumb(size : String? = nil, position : String? = nil)
+ if size || position
+ command = "zConfiguration Call Layout ShareThumb"
+ command += " Size: #{size}" if size
+ command += " Position: #{position}" if position
+ do_send(command, name: "config_call_share_thumb")
+ else
+ do_send("zConfiguration Call Layout ShareThumb", name: "config_call_share_thumb")
+ end
+ end
+
+ # Closed Caption Configuration
+ def config_call_closed_caption_visible(enable : Bool? = nil)
+ if enable.nil?
+ do_send("zConfiguration Call ClosedCaption Visible", name: "config_closed_caption_visible")
+ else
+ state = enable ? "on" : "off"
+ do_send("zConfiguration Call ClosedCaption Visible: #{state}", name: "config_closed_caption_visible")
+ end
+ end
+
+ def config_call_closed_caption_font_size(size : Int32? = nil)
+ if size
+ do_send("zConfiguration Call ClosedCaption FontSize: #{size}", name: "config_closed_caption_font_size")
+ else
+ do_send("zConfiguration Call ClosedCaption FontSize", name: "config_closed_caption_font_size")
+ end
+ end
+
+ # Client Information
+ def config_client_app_version
+ do_send("zConfiguration Client appVersion", name: "config_client_app_version")
+ end
+
+ def config_client_device_system
+ do_send("zConfiguration Client deviceSystem", name: "config_client_device_system")
+ end
+
+ # Sharing Configuration
+ def config_sharing_participant(enable : Bool? = nil)
+ if enable.nil?
+ do_send("zConfiguration Sharing Participant", name: "config_sharing_participant")
+ else
+ state = enable ? "on" : "off"
+ do_send("zConfiguration Sharing Participant: #{state}", name: "config_sharing_participant")
+ end
+ end
+
+ def config_sharing_optimize_video(enable : Bool? = nil)
+ if enable.nil?
+ do_send("zConfiguration Sharing optimizeVideo", name: "config_sharing_optimize_video")
+ else
+ state = enable ? "on" : "off"
+ do_send("zConfiguration Sharing optimizeVideo: #{state}", name: "config_sharing_optimize_video")
+ end
+ end
+
+ def send_command(command : String)
+ transport.send "#{command}\r\n"
+ end
+
+ protected def reset_connection_flags
+ self[:ready] = @ready = false
+ @init_called = false
+ transport.tokenizer = nil
+ end
+
+ # Regexp's for tokenizing the ZR-CSAPI response structure.
+ INVALID_COMMAND = /(?<=onUnsupported Command)[\r\n]+/
+ SUCCESS = /(?<=OK)[\r\n]+/
+ COMMAND_RESPONSE = Regex.union(INVALID_COMMAND, SUCCESS)
+
+ private def initialize_tokenizer
+ @init_called = true
+ transport.tokenizer = Tokenizer.new do |io|
+ raw = io.gets_to_end
+ data = raw.lstrip
+ index = if data.includes?("{")
+ count = 0
+ pos = 0
+ data.each_char_with_index do |char, i|
+ pos = i
+ count += 1 if char == '{'
+ count -= 1 if char == '}'
+ break if count.zero?
+ end
+ pos if count.zero?
+ else
+ data =~ COMMAND_RESPONSE
+ end
+ if index
+ message = data[0..index]
+ index += raw.byte_index_to_char_index(raw.byte_index(message).not_nil!).not_nil!
+ index = raw.char_index_to_byte_index(index + 1)
+ end
+ index || -1
+ end
+ self[:ready] = @ready = true
+ rescue error
+ @init_called = false
+ logger.warn(exception: error) { "error configuring zrcsapi transport" }
+ end
+
+ def received(data, task)
+ response = String.new(data).strip.delete &.in?('\r', '\n')
+ logger.debug { "Received: #{response.inspect}" } if @debug_enabled
+
+ unless ready?
+ if response.includes?("ZAAPI") # Initial connection message
+ queue.clear abort_current: true
+ do_send("echo off", name: "echo_off")
+ schedule.clear
+ do_send("format json", name: "set_format")
+ schedule.clear
+ initialize_tokenizer unless @init_called
+ fetch_initial_state
+ else
+ return task.try(&.abort)
+ end
+ end
+
+ # Ignore non-JSON messages
+ if response[0] == '{'
+ task.try &.success(response)
+ else
+ return
+ end
+
+ json_response = JSON.parse(response)
+ response_type : String = json_response["type"].as_s
+ response_topkey : String = json_response["topKey"].as_s
+ if @debug_enabled
+ logger.debug { "type: #{response_type}, topkey: #{response_topkey}" }
+ end
+
+ # Expose new data as status variables
+ begin
+ old_data = self[response_topkey]
+ new_data = json_response[response_topkey].as_h
+ logger.debug { "Merging new data into existing data" } if @debug_enabled
+ self[response_topkey] = old_data.as_h.merge(new_data)
+ rescue exception
+ logger.debug { "Replacing existing data" } if @debug_enabled
+ self[response_topkey] = json_response[response_topkey]
+ end
+
+ case response_topkey
+ when "Call"
+ expose_custom_call_state
+ when "ListParticipantsResult"
+ begin
+ list = json_response["ListParticipantsResult"]
+ event = nil
+
+ # Handle different data structures correctly
+ if list.as_a?
+ # It's an array (manual query response) - get event from first participant
+ first_participant = list.as_a.first?
+ if first_participant && first_participant.as_h?
+ event_value = first_participant.as_h["event"]?
+ event = event_value.try(&.as_s) if event_value
+ end
+ elsif list.as_h?
+ # It's a single hash (automatic event) - get event directly
+ event_value = list.as_h["event"]?
+ event = event_value.try(&.as_s) if event_value
+ end
+
+ logger.info { "Final event: #{event}" }
+
+ # Handle the event properly
+ if event == "None" && list.as_a?
+ # Manual query response - process the participant list
+ logger.info { "Processing manual query response" }
+ expose_custom_participant_list
+ elsif event && event.starts_with?("ZRCUserChangedEvent")
+ # Automatic event - trigger fresh query
+ logger.info { "Triggering auto-refresh for: #{event}" }
+ call_list_participants
+ end
+
+ rescue ex
+ logger.error { "Error processing ListParticipantsResult: #{ex.message}" }
+ end
+ end
+
+ # Perform additional actions
+ case response_type
+ when "zEvent"
+ case response_topkey
+ when "Bookings Updated"
+ bookings_list
+ end
+ when "zStatus"
+ case response_topkey
+ when "Call"
+ expose_custom_call_state
+ end
+ when "zConfiguration"
+ when "zCommand"
+ end
+ end
+
+ private def do_send(command, **options)
+ logger.debug { "requesting #{command}" }
+ send "#{command}\r\n", **options
+ end
+end
diff --git a/drivers/zoom/zr_csapi_spec.cr b/drivers/zoom/zr_csapi_spec.cr
new file mode 100644
index 00000000000..db315f2203e
--- /dev/null
+++ b/drivers/zoom/zr_csapi_spec.cr
@@ -0,0 +1,131 @@
+require "placeos-driver/spec"
+
+DriverSpecs.mock_driver "Zoom::ZrCSAPI" do
+ settings({
+ enable_debug_logging: true
+ })
+
+ # Initial connection sequence
+ transmit "Welcome to ZAAPI\r\n"
+ should_send "echo off\r\n"
+ responds "OK\r\n"
+ should_send "format json\r\n"
+ responds "OK\r\n"
+
+ exec(:bookings_list)
+ should_send "zCommand Bookings List\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"BookingsListResult\",\"BookingsListResult\":{\"meetings\":[]}}\r\n"
+
+ exec(:bookings_update)
+ should_send "zCommand Bookings Update\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"BookingsUpdateResult\",\"BookingsUpdateResult\":{\"status\":\"success\"}}\r\n"
+
+ exec(:call_disconnect)
+ should_send "zCommand Call Disconnect\r\n"
+ responds "{\r\n \"Call\": {\r\n \"Status\": \"NOT_IN_MEETING\"\r\n },\r\n \"Status\": {\r\n \"message\": \"\",\r\n \"state\": \"OK\"\r\n },\r\n \"Sync\": false,\r\n \"topKey\": \"Call\",\r\n \"type\": \"zStatus\"\r\n}"
+
+ exec(:dial_start, "1234567890")
+ should_send "zCommand Dial Start meetingNumber: 1234567890\r\n"
+ responds "{\r\n \"Call\": {\r\n \"Status\": \"IN_MEETING\"\r\n },\r\n \"Status\": {\r\n \"message\": \"\",\r\n \"state\": \"OK\"\r\n },\r\n \"Sync\": false,\r\n \"topKey\": \"Call\",\r\n \"type\": \"zStatus\"\r\n}"
+ transmit "{\r\n \"Call\": {\r\n \"Microphone\": {\r\n \"Mute\": false\r\n }\r\n },\r\n \"Status\": {\r\n \"message\": \"\",\r\n \"state\": \"OK\"\r\n },\r\n \"Sync\": false,\r\n \"topKey\": \"Call\",\r\n \"type\": \"zConfiguration\"\r\n}"
+ transmit "{\r\n \"Call\": {\r\n \"Lock\": {\r\n \"Enable\": false\r\n }\r\n },\r\n \"Status\": {\r\n \"message\": \"\",\r\n \"state\": \"OK\"\r\n },\r\n \"Sync\": false,\r\n \"topKey\": \"Call\",\r\n \"type\": \"zConfiguration\"\r\n}"
+ transmit "{\r\n \"Call\": {\r\n \"Layout\": {\r\n \"Size\": \"Size1\"\r\n }\r\n },\r\n \"Status\": {\r\n \"message\": \"\",\r\n \"state\": \"OK\"\r\n },\r\n \"Sync\": false,\r\n \"topKey\": \"Call\",\r\n \"type\": \"zConfiguration\"\r\n}"
+ transmit "{\r\n \"Call\": {\r\n \"ClosedCaption\": {\r\n \"CanDisable\": false\r\n }\r\n },\r\n \"Status\": {\r\n \"message\": \"\",\r\n \"state\": \"OK\"\r\n },\r\n \"Sync\": false,\r\n \"topKey\": \"Call\",\r\n \"type\": \"zStatus\"\r\n}"
+ transmit "{\r\n \"Call\": {\r\n \"Share\": {\r\n \"Setting\": \"MULTI_SHARE\"\r\n }\r\n },\r\n \"Status\": {\r\n \"message\": \"\",\r\n \"state\": \"OK\"\r\n },\r\n \"Sync\": false,\r\n \"topKey\": \"Call\",\r\n \"type\": \"zConfiguration\"\r\n}"
+
+ exec(:dial_join_sip, "test@example.com", "SIP")
+ should_send "zCommand Dial Join meetingAddress: test@example.com protocol: SIP\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"DialResult\",\"DialResult\":{\"status\":\"connecting\"}}\r\n"
+
+ exec(:call_invite, "user@example.com")
+ should_send "zCommand Call Invite user: user@example.com\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"CallResult\",\"CallResult\":{\"status\":\"invited\"}}\r\n"
+
+ exec(:call_mute_participant, true, "12345")
+ should_send "zCommand Call MuteParticipant mute: on Id: 12345\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"CallResult\",\"CallResult\":{\"status\":\"muted\"}}\r\n"
+
+ exec(:call_mute_all, true)
+ should_send "zCommand Call MuteAll mute: on\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"CallResult\",\"CallResult\":{\"status\":\"all_muted\"}}\r\n"
+
+ exec(:call_mute_self, false)
+ should_send "zCommand Audio Microphone Mute: off\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"CallResult\",\"CallResult\":{\"status\":\"unmuted\"}}\r\n"
+
+ exec(:call_record, true)
+ should_send "zCommand Call Record Enable: on\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"CallResult\",\"CallResult\":{\"status\":\"recording\"}}\r\n"
+
+ exec(:call_make_host, "67890")
+ should_send "zCommand Call MakeHost Id: 67890\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"CallResult\",\"CallResult\":{\"status\":\"host_changed\"}}\r\n"
+
+ exec(:call_layout, "Gallery", "Large", "Top")
+ should_send "zCommand Call Layout LayoutStyle: Gallery LayoutSize: Large LayoutPosition: Top\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"CallResult\",\"CallResult\":{\"status\":\"layout_changed\"}}\r\n"
+
+ # Test sharing control methods
+ exec(:sharing_start_hdmi)
+ should_send "zCommand Sharing Start source: hdmi\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"SharingResult\",\"SharingResult\":{\"status\":\"sharing_started\"}}\r\n"
+
+ exec(:sharing_stop)
+ should_send "zCommand Sharing Stop\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"SharingResult\",\"SharingResult\":{\"status\":\"sharing_stopped\"}}\r\n"
+
+ exec(:sharing_start_camera)
+ should_send "zCommand Sharing Start source: camera\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"SharingResult\",\"SharingResult\":{\"status\":\"camera_sharing_started\"}}\r\n"
+
+ # Test device testing methods
+ exec(:test_microphone_start, "Device123")
+ should_send "zCommand Test Microphone Start Id: Device123\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"TestResult\",\"TestResult\":{\"status\":\"test_started\"}}\r\n"
+
+ exec(:test_microphone_stop)
+ should_send "zCommand Test Microphone Stop\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"TestResult\",\"TestResult\":{\"status\":\"test_stopped\"}}\r\n"
+
+ exec(:test_speakers_start)
+ should_send "zCommand Test Speakers Start\r\n"
+ responds "{\"type\":\"zCommand\",\"topKey\":\"TestResult\",\"TestResult\":{\"status\":\"test_started\"}}\r\n"
+
+ # Test zStatus methods
+ exec(:system_unit?)
+ should_send "zStatus SystemUnit\r\n"
+ responds "{\"type\":\"zStatus\",\"topKey\":\"SystemUnit\",\"SystemUnit\":{\"platform\":\"windows\",\"version\":\"5.8.0\"}}\r\n"
+
+ exec(:call_status)
+ should_send "zStatus Call Status\r\n"
+ responds "{\"type\":\"zStatus\",\"topKey\":\"Call\",\"Call\":{\"Status\":\"NOT_IN_MEETING\"}}\r\n"
+
+ exec(:capabilities)
+ should_send "zStatus Capabilities\r\n"
+ responds "{\"type\":\"zStatus\",\"topKey\":\"Capabilities\",\"Capabilities\":{\"HardwareEncryption\":true}}\r\n"
+
+ # Test zConfiguration methods
+ exec(:config_audio_volume, 75)
+ should_send "zConfiguration Audio Output volume: 75\r\n"
+ responds "{\"type\":\"zConfiguration\",\"topKey\":\"Audio\",\"Audio\":{\"Output\":{\"volume\":75}}}\r\n"
+
+ exec(:config_audio_volume)
+ should_send "zConfiguration Audio Output volume\r\n"
+ responds "{\"type\":\"zConfiguration\",\"topKey\":\"Audio\",\"Audio\":{\"Output\":{\"volume\":50}}}\r\n"
+
+ exec(:config_video_camera, "Camera001")
+ should_send "zConfiguration Video Camera selectedDevice: Camera001\r\n"
+ responds "{\"type\":\"zConfiguration\",\"topKey\":\"Video\",\"Video\":{\"Camera\":{\"selectedDevice\":\"Camera001\"}}}\r\n"
+
+ exec(:config_call_mute_on_entry, true)
+ should_send "zConfiguration Call muteUserOnEntry: on\r\n"
+ responds "{\"type\":\"zConfiguration\",\"topKey\":\"Call\",\"Call\":{\"muteUserOnEntry\":true}}\r\n"
+
+ # Check that status values are properly set
+ status[:system_unit]?.should_not be_nil
+ status[:call_status]?.should_not be_nil
+ status[:capabilities]?.should_not be_nil
+ status[:audio_config]?.should_not be_nil
+ status[:video_config]?.should_not be_nil
+ status[:call_config]?.should_not be_nil
+end
diff --git a/harness b/harness
new file mode 100755
index 00000000000..8934361abc5
--- /dev/null
+++ b/harness
@@ -0,0 +1,142 @@
+#! /usr/bin/env bash
+
+# `e`: fail script if a command's exitcode is non-zero
+# `u`: fail script if a variable is unset (unitialized)
+set -eu
+
+say_done() {
+ printf "░░░ Done.\n"
+}
+
+fail() {
+ echo "${@}" >&2
+ exit 1
+}
+
+# Called when Ctrl-C is sent
+function trap_ctrlc ()
+{
+ echo ">~"
+ echo "░░░ Cleaning up..."
+ down
+ exit 2
+}
+
+trap "trap_ctrlc" 2
+
+up() {
+ echo '░░░ PlaceOS Driver Harness'
+ echo '░░░ -> Pulling latest code...'
+ git pull
+ echo '░░░ -> Pulling latest images...'
+ docker compose pull
+ echo '░░░ -> Starting environment...'
+ docker compose up -d
+ printf "░░░ The harness can be found at http://localhost:8085/index.html\n"
+ echo '░░░ Stop the harness with `harness down`'
+ say_done
+}
+
+down() {
+ echo '░░░ Stopping PlaceOS Driver Harness...'
+ docker compose down --remove-orphans &> /dev/null
+ say_done
+}
+
+format() {
+ echo '░░░ Running `crystal tool format` over `drivers` and `repositories`'
+ docker compose run \
+ -v "${PWD}/drivers:/wd/drivers" \
+ -v "${PWD}/repositories:/wd/repositories" \
+ --no-deps \
+ --rm \
+ install-shards \
+ crystal tool format
+ say_done
+}
+
+report() {
+ echo '░░░ PlaceOS Driver Compilation Report'
+ echo '░░░ Pulling images...'
+ docker compose pull &> /dev/null
+
+ # Ensure shards are satisfied before running the report
+ echo '░░░ Installing shards...'
+ docker compose run \
+ --rm \
+ install-shards > /dev/null
+
+ echo '░░░ Starting environment...'
+ docker compose up -d &> /dev/null
+
+ exit_code=0
+
+ echo '░░░ Starting report...'
+ docker exec placeos-drivers report $@ || exit_code=$?
+
+ down
+ exit ${exit_code}
+}
+
+build() {
+ docker compose run \
+ --rm \
+ --no-deps \
+ -v "${PWD}/repositories:/app/repositories" \
+ -v "${PWD}/drivers:/app/repositories/drivers" \
+ --entrypoint="/app/scripts/entrypoint.sh" \
+ build build $@
+}
+
+usage() {
+ cat < 0.6.0
+
+ bindata:
+ github: spider-gazelle/bindata
+ version: ~> 2.0
+
+ placeos-models:
+ github: placeos/models
+ version: ">= 9.37"
+
+ inactive-support:
+ github: spider-gazelle/inactive-support
+
+ jwt:
+ github: crystal-community/jwt
+
+ pinger:
+ github: spider-gazelle/pinger
+
+ ntlm:
+ github: spider-gazelle/ntlm
+
+ link-header:
+ github: spider-gazelle/link-header
+
+ place_calendar:
+ github: PlaceOS/calendar
+
+ office365:
+ github: PlaceOS/office365
+
+ placeos-compiler:
+ github: placeos/compiler
+
+ placeos-driver:
+ github: placeos/driver
+ version: ~> 7.1
+
+ # The PlaceOS API client
+ placeos:
+ github: placeos/crystal-client
+ version: ">= 2.10"
+
+ # HTTP Client helper
+ responsible:
+ github: place-labs/responsible
+
+ rwlock:
+ github: spider-gazelle/readers-writer
+
+ # Driver deps:
+ telnet:
+ github: spider-gazelle/telnet.cr
+
+ pars:
+ github: spider-gazelle/pars
+
+ # For lat lon location indexing
+ s2_cells:
+ github: spider-gazelle/s2_cells
+
+ # TODO:: deprecated, we should aim to remove at some point
+ qr-code:
+ github: spider-gazelle/qr-code
+
+ # A faster and better QR code implementation
+ goban:
+ github: soya-daizu/goban
+ branch: master
+
+ # For QR .png file export
+ stumpy_png:
+ github: stumpycr/stumpy_png
+
+ # the STOMP protocol
+ stomp:
+ github: spider-gazelle/stomp
+
+ # KNX protocol
+ knx:
+ github: spider-gazelle/knx
+
+ # MQTT protocol
+ mqtt:
+ github: spider-gazelle/crystal-mqtt
+
+ # XML to JSON convertor
+ oq:
+ github: blacksmoke16/oq
+ version: ~> 1.2
+
+ # signed requests to AWS APIs
+ awscr-signer:
+ github: taylorfinnell/awscr-signer
+ version: ~> 0.8
+
+ # BACnet protocol support
+ bacnet:
+ github: spider-gazelle/crystal-bacnet
+ version: ~> 0.10
+
+ # HTTP client
+ halite:
+ github: icyleaf/halite
+
+ # token bucket algorithm for rate limiting
+ rate_limiter:
+ github: lbarasti/rate_limiter
+ version: ~> 1.0
+
+ # fake data for mocks
+ faker:
+ github: askn/faker
+
+ # SOAP client
+ sabo:
+ github: place-technology/sabo
+
+ # AxiomXa client
+ axio:
+ github: place-technology/axio
+
+ # Lutron Quantum protocol
+ quantum:
+ github: place-technology/quantum
+
+ # Stripe API wrapper
+ stripetease:
+ github: place-technology/stripetease
+
+ # Siemens Desigo API wrapper
+ desigo:
+ github: place-technology/desigo
+
+ # Protobuf
+ protobuf:
+ github: jeromegn/protobuf.cr
+
+ # debugging drivers
+ perf_tools:
+ github: crystal-lang/perf-tools
+
\ No newline at end of file
diff --git a/spec/spec_helper.cr b/spec/spec_helper.cr
deleted file mode 100644
index e008dcfd222..00000000000
--- a/spec/spec_helper.cr
+++ /dev/null
@@ -1,7 +0,0 @@
-require "spec"
-
-# Your application config
-require "../src/config"
-
-# Helper methods for testing controllers (curl, with_server, context)
-require "../lib/action-controller/spec/curl_context"
diff --git a/spec/welcome_spec.cr b/spec/welcome_spec.cr
deleted file mode 100644
index 5666e9ad6e3..00000000000
--- a/spec/welcome_spec.cr
+++ /dev/null
@@ -1,25 +0,0 @@
-require "./spec_helper"
-
-describe Welcome do
- # ==============
- # Unit Testing
- # ==============
- it "should generate a date string" do
- # instantiate the controller you wish to unit test
- welcome = Welcome.new(context("GET", "/"))
-
- # Test the instance methods of the controller
- welcome.time_now.should contain("GMT")
- end
-
- # ==============
- # Test Responses
- # ==============
- with_server do
- it "should welcome you" do
- result = curl("GET", "/")
- result.body.should eq("\n\nWelcome\nYou're riding on Spider-Gazelle!\n\n")
- result.headers["Date"]?.nil?.should eq(false)
- end
- end
-end
diff --git a/src b/src
new file mode 120000
index 00000000000..86e5b5e04d4
--- /dev/null
+++ b/src
@@ -0,0 +1 @@
+./drivers
\ No newline at end of file
diff --git a/src/app.cr b/src/app.cr
deleted file mode 100644
index 4a6e7bbdbb3..00000000000
--- a/src/app.cr
+++ /dev/null
@@ -1,46 +0,0 @@
-require "option_parser"
-require "./config"
-
-# Server defaults
-port = 3000
-host = "127.0.0.1"
-
-# Command line options
-OptionParser.parse! do |parser|
- parser.banner = "Usage: #{PROGRAM_NAME} [arguments]"
-
- parser.on("-b HOST", "--bind=HOST", "Specifies the server host") { |h| host = h }
- parser.on("-p PORT", "--port=PORT", "Specifies the server port") { |p| port = p.to_i }
-
- parser.on("-r", "--routes", "List the application routes") do
- ActionController::Server.print_routes
- exit 0
- end
-
- parser.on("-v", "--version", "Display the application version") do
- puts "#{APP_NAME} v#{VERSION}"
- exit 0
- end
-
- parser.on("-h", "--help", "Show this help") do
- puts parser
- exit 0
- end
-end
-
-# Load the routes
-puts "Launching #{APP_NAME} v#{VERSION}"
-server = ActionController::Server.new(port, host)
-
-# Detect ctr-c to shutdown gracefully
-Signal::INT.trap do
- puts " > terminating gracefully"
- server.close
-end
-
-# Start the server
-puts "Listening on tcp://#{host}:#{port}"
-server.run
-
-# Shutdown message
-puts "#{APP_NAME} leaps through the veldt\n"
diff --git a/src/config.cr b/src/config.cr
deleted file mode 100644
index f48255a4f35..00000000000
--- a/src/config.cr
+++ /dev/null
@@ -1,21 +0,0 @@
-# Application dependencies
-require "action-controller"
-require "active-model"
-
-# Application code
-require "./controllers/application"
-require "./controllers/*"
-require "./models/*"
-
-# Server required after application controllers
-require "action-controller/server"
-
-# Configure session cookies
-# NOTE:: Change these from defaults
-ActionController::Session.configure do
- settings.key = "_spider_gazelle_"
- settings.secret = "4f74c0b358d5bab4000dd3c75465dc2c"
-end
-
-APP_NAME = "Spider-Gazelle"
-VERSION = "1.0.0"
diff --git a/src/controllers/application.cr b/src/controllers/application.cr
deleted file mode 100644
index 9bdbc79b557..00000000000
--- a/src/controllers/application.cr
+++ /dev/null
@@ -1,15 +0,0 @@
-# Require kilt for template support
-require "kilt"
-
-abstract class Application < ActionController::Base
- before_action :set_date_header
-
- # https://developer.mozilla.org/en-US/docs/Web/HTTP/Headers/Date
- def time_now
- Time.utc_now.to_s("%a, %d %b %Y %H:%M:%S GMT")
- end
-
- def set_date_header
- response.headers["Date"] = time_now
- end
-end
diff --git a/src/controllers/welcome.cr b/src/controllers/welcome.cr
deleted file mode 100644
index 7695e78845b..00000000000
--- a/src/controllers/welcome.cr
+++ /dev/null
@@ -1,18 +0,0 @@
-class Welcome < Application
- base "/"
-
- def index
- welcome_text = "You're riding on Spider-Gazelle!"
-
- respond_with do
- html Kilt.render("src/views/welcome.ecr")
- text "Welcome, #{welcome_text}"
- json({welcome: welcome_text})
- xml do
- XML.build(indent: " ") do |xml|
- xml.element("welcome") { xml.text welcome_text }
- end
- end
- end
- end
-end
diff --git a/src/views/welcome.ecr b/src/views/welcome.ecr
deleted file mode 100644
index 69f2e46c394..00000000000
--- a/src/views/welcome.ecr
+++ /dev/null
@@ -1,5 +0,0 @@
-
-
-Welcome
-<%= welcome_text %>
-